Auditing Payment Systemss Cyberserurity A maturity model based
Auditing Payment Systems´s Cyberserurity: A maturity model based in NIST Cybersecurity Framework 29 th WGITA meeting Roberto Hernandez Rojas Valderrama, SAI Mexico
Agenda • • • Objective Payment Systems architecture and risks Cybersecurity frameworks Audit Results Conclusions
Objective • Audit cybersecurity conditions in Mexican development banking payment systems, including • Regulation • Supervisors • Central operator
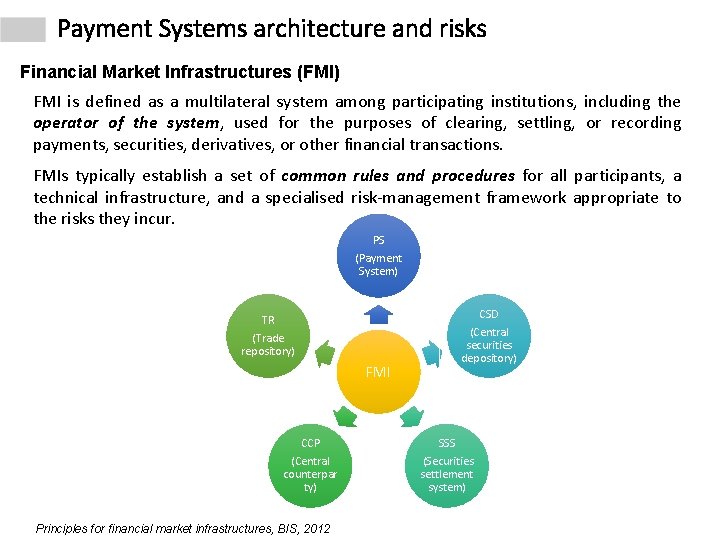
Payment Systems architecture and risks Financial Market Infrastructures (FMI) FMI is defined as a multilateral system among participating institutions, including the operator of the system, used for the purposes of clearing, settling, or recording payments, securities, derivatives, or other financial transactions. FMIs typically establish a set of common rules and procedures for all participants, a technical infrastructure, and a specialised risk-management framework appropriate to the risks they incur. PS (Payment System) TR (Trade repository) FMI CCP (Central counterpar ty) Principles for financial market infrastructures, BIS, 2012 CSD (Central securities depository) SSS (Securities settlement system)
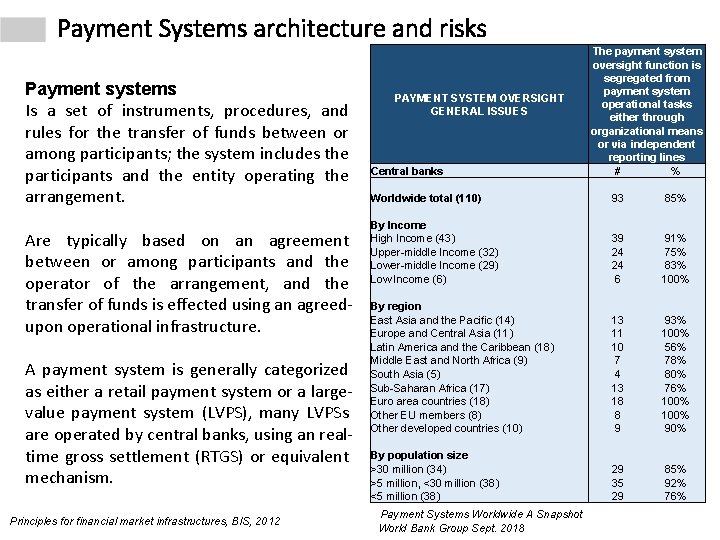
Payment Systems architecture and risks Payment systems Is a set of instruments, procedures, and rules for the transfer of funds between or among participants; the system includes the participants and the entity operating the arrangement. Are typically based on an agreement between or among participants and the operator of the arrangement, and the transfer of funds is effected using an agreedupon operational infrastructure. A payment system is generally categorized as either a retail payment system or a largevalue payment system (LVPS), many LVPSs are operated by central banks, using an realtime gross settlement (RTGS) or equivalent mechanism. Principles for financial market infrastructures, BIS, 2012 PAYMENT SYSTEM OVERSIGHT GENERAL ISSUES Central banks The payment system oversight function is segregated from payment system operational tasks either through organizational means or via independent reporting lines # % Worldwide total (110) 93 85% By Income High Income (43) Upper-middle Income (32) Lower-middle Income (29) Low Income (6) 39 24 24 6 91% 75% 83% 100% By region East Asia and the Pacific (14) Europe and Central Asia (11) Latin America and the Caribbean (18) Middle East and North Africa (9) South Asia (5) Sub-Saharan Africa (17) Euro area countries (18) Other EU members (8) Other developed countries (10) 13 11 10 7 4 13 18 8 9 93% 100% 56% 78% 80% 76% 100% 90% By population size >30 million (34) >5 million, <30 million (38) <5 million (38) 29 35 29 85% 92% 76% Payment Systems Worldwide A Snapshot World Bank Group Sept. 2018
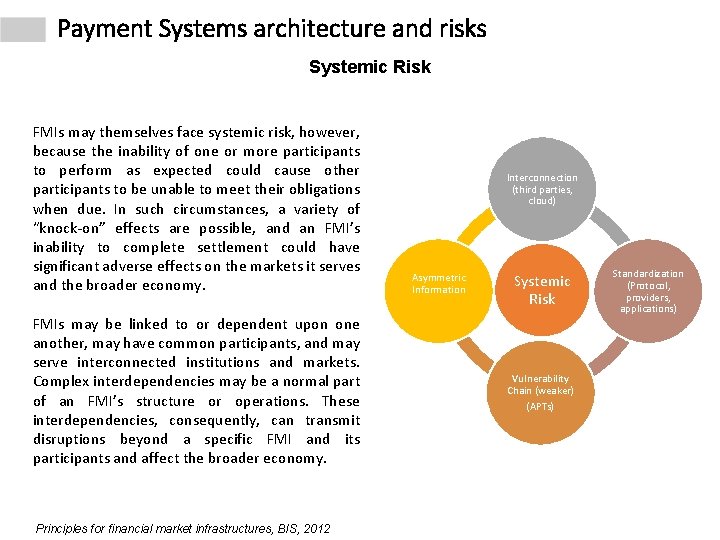
Payment Systems architecture and risks Systemic Risk FMIs may themselves face systemic risk, however, because the inability of one or more participants to perform as expected could cause other participants to be unable to meet their obligations when due. In such circumstances, a variety of “knock-on” effects are possible, and an FMI’s inability to complete settlement could have significant adverse effects on the markets it serves and the broader economy. FMIs may be linked to or dependent upon one another, may have common participants, and may serve interconnected institutions and markets. Complex interdependencies may be a normal part of an FMI’s structure or operations. These interdependencies, consequently, can transmit disruptions beyond a specific FMI and its participants and affect the broader economy. Principles for financial market infrastructures, BIS, 2012 Interconnection (third parties, cloud) Asymmetric Information Systemic Risk Vulnerability Chain (weaker) (APTs) Standardization (Protocol, providers, applications)
Payment Systems architecture and risks Mexico Payment System SPEI is an electronic funds transfer system owned and operated by Banco de México, Mexico’s central bank. Developed to facilitate payments between financial institutions, in addition to enabling them to offer safe and efficient retail payment services to the public. SPEI’s participants can transfer Mexican pesos by own account and on behalf of their accountholders, in near realtime, 24 hours per day, every day of the year. At the core of the legal framework in which SPEI operates is the Payments Systems Law, SPEI’s governance arrangements are subject to Banco de México’s regulatory framework and policies. Principles for financial market infrastructures, BIS, 2012

Payment Systems architecture and risks Mexico Payment System SPEI • 101 participants (financial and non financial institutions) operates SPEI in Mexico • Almost 270 trillions pesos are transferred by SPEI (26 trillions by development bank during 2018 -2019) Mexico Development Banks Financial Institution Core business BANJERCITO Armed Forces Personal BANOBRAS Infrastructure NAFIN Local Commerce BANCOMEXET External Commerce BIENESTAR Social programs TESOFE (Operated by central bank BANXICO) Treasury
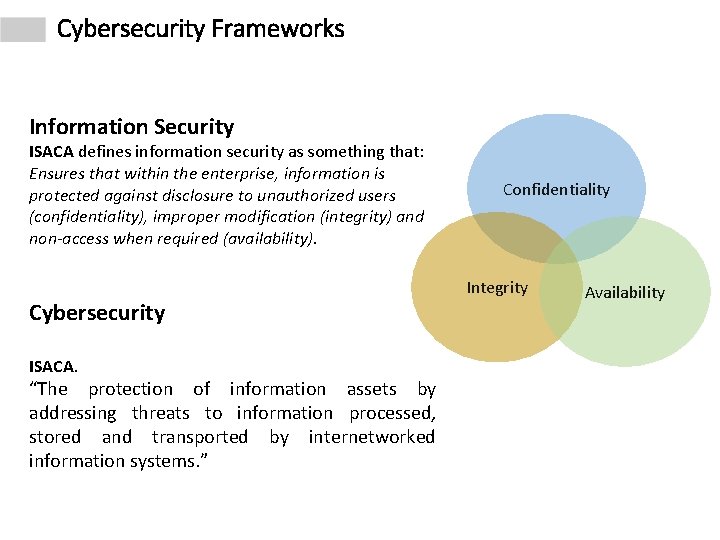
Cybersecurity Frameworks Information Security ISACA defines information security as something that: Ensures that within the enterprise, information is protected against disclosure to unauthorized users (confidentiality), improper modification (integrity) and non-access when required (availability). Cybersecurity ISACA. “The protection of information assets by addressing threats to information processed, stored and transported by internetworked information systems. ” Confidentiality Integrity Availability
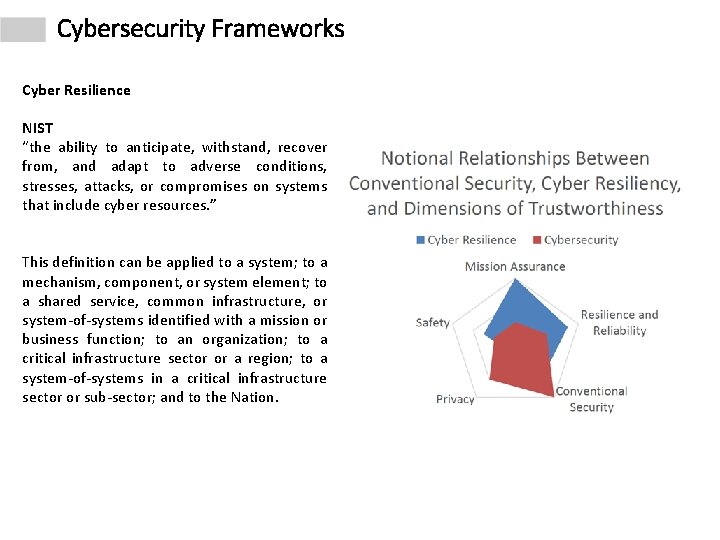
Cybersecurity Frameworks Cyber Resilience NIST “the ability to anticipate, withstand, recover from, and adapt to adverse conditions, stresses, attacks, or compromises on systems that include cyber resources. ” This definition can be applied to a system; to a mechanism, component, or system element; to a shared service, common infrastructure, or system-of-systems identified with a mission or business function; to an organization; to a critical infrastructure sector or a region; to a system-of-systems in a critical infrastructure sector or sub-sector; and to the Nation.
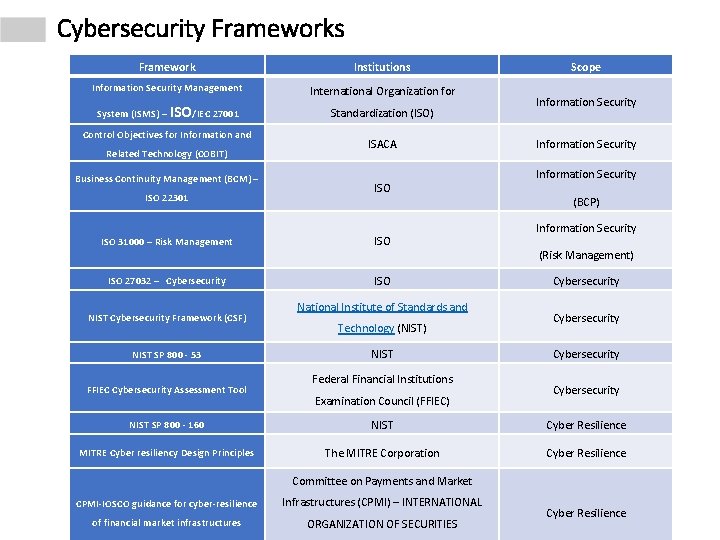
Cybersecurity Frameworks Framework Institutions Information Security Management International Organization for System (ISMS) – ISO/IEC 27001 Standardization (ISO) Control Objectives for Information and Related Technology (COBIT) Business Continuity Management (BCM) – ISO 22301 ISO 31000 – Risk Management ISO 27032 – Cybersecurity NIST Cybersecurity Framework (CSF) NIST SP 800 - 53 FFIEC Cybersecurity Assessment Tool ISACA ISO ISO National Institute of Standards and Technology (NIST) NIST Federal Financial Institutions Examination Council (FFIEC) Scope Information Security (BCP) Information Security (Risk Management) Cybersecurity NIST SP 800 - 160 NIST Cyber Resilience MITRE Cyber resiliency Design Principles The MITRE Corporation Cyber Resilience Committee on Payments and Market CPMI-IOSCO guidance for cyber-resilience Infrastructures (CPMI) – INTERNATIONAL of financial market infrastructures ORGANIZATION OF SECURITIES Cyber Resilience
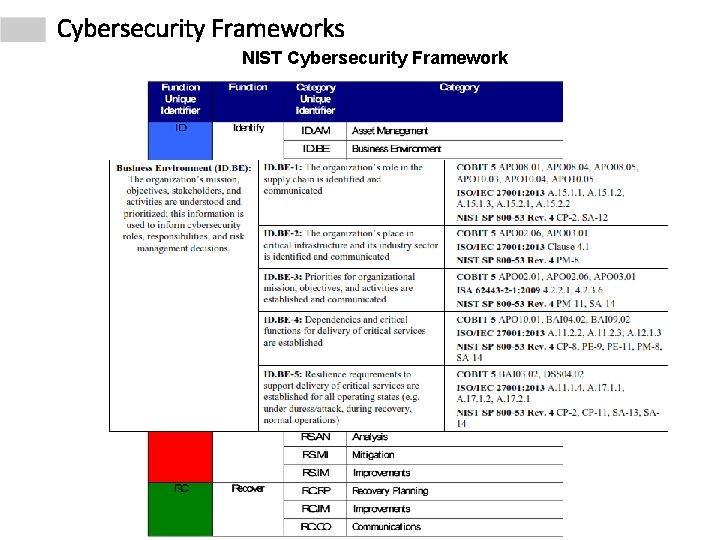
Cybersecurity Frameworks NIST Cybersecurity Framework
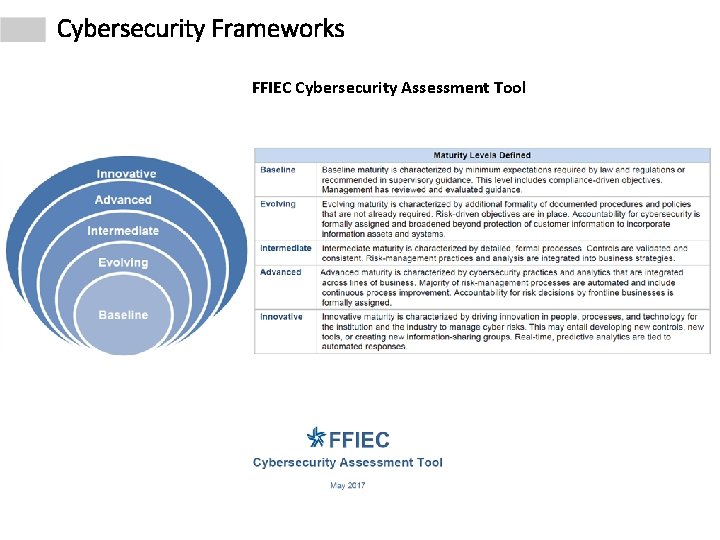
Cybersecurity Frameworks FFIEC Cybersecurity Assessment Tool
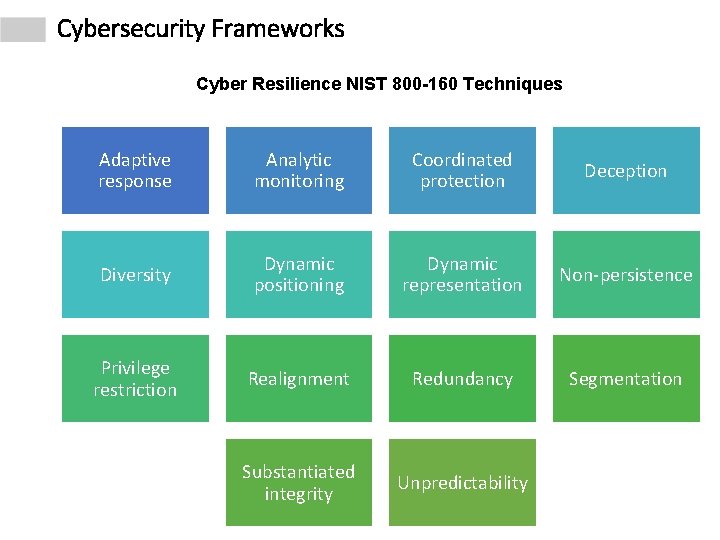
Cybersecurity Frameworks Cyber Resilience NIST 800 -160 Techniques Adaptive response Analytic monitoring Coordinated protection Deception Diversity Dynamic positioning Dynamic representation Non-persistence Privilege restriction Realignment Redundancy Segmentation Substantiated integrity Unpredictability
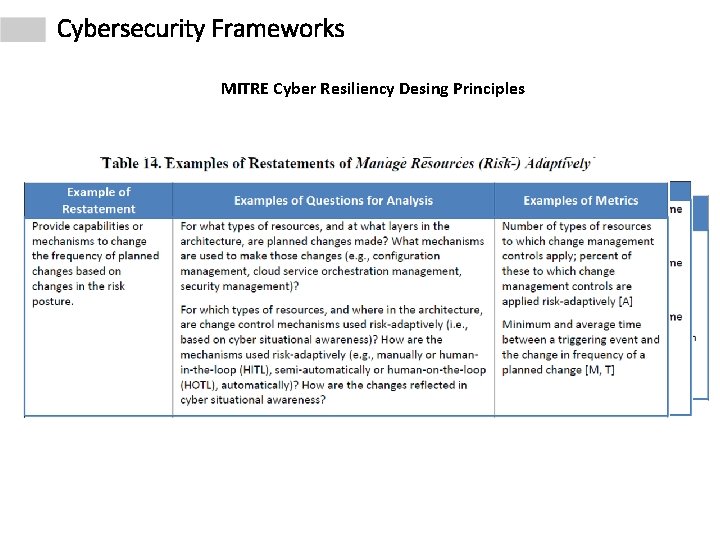
Cybersecurity Frameworks MITRE Cyber Resiliency Desing Principles
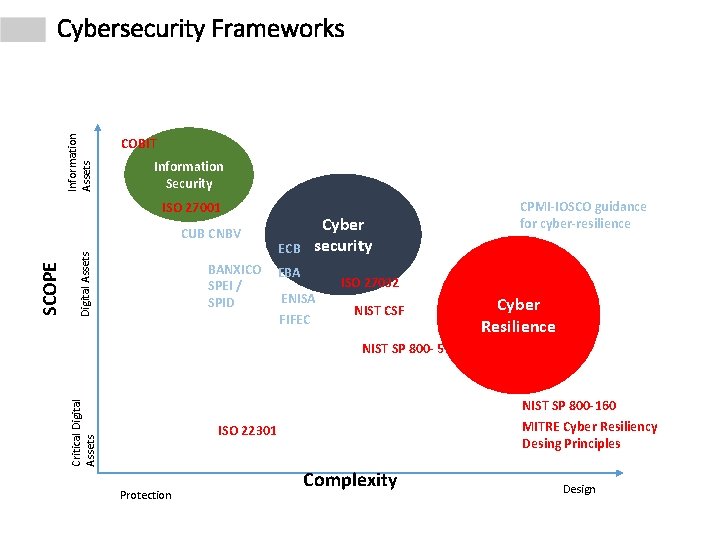
Information Assets Cybersecurity Frameworks COBIT Information Security ISO 27001 Digital Assets BANXICO SPEI / SPID Cyber security ECB EBA ENISA FIFEC ISO 27032 NIST CSF Cyber Resilience NIST SP 800 - 53 Critical Digital Assets SCOPE CUB CNBV CPMI-IOSCO guidance for cyber-resilience NIST SP 800 -160 MITRE Cyber Resiliency Desing Principles ISO 22301 Protection Complexity Design
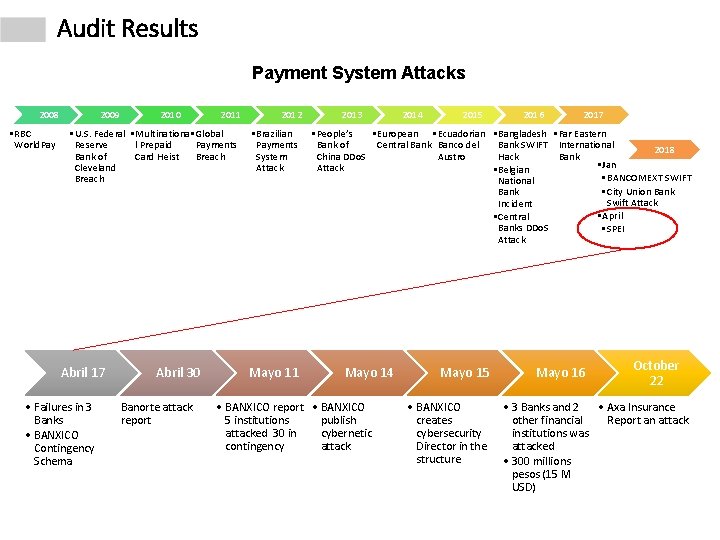
Audit Results Payment System Attacks 2008 • RBC World. Pay 2009 2010 2011 • U. S. Federal • Multinationa • Global Reserve l Prepaid Payments Bank of Card Heist Breach Cleveland Breach Abril 17 • Failures in 3 Banks • BANXICO Contingency Schema Abril 30 Banorte attack report 2012 • Brazilian Payments System Attack Mayo 11 2013 2014 2015 2016 2017 • People’s • European • Ecuadorian • Bangladesh • Far Eastern Bank of Central Bank Banco del Bank SWIFT International 2018 China DDo. S Austro Hack Bank • Jan Attack • Belgian • BANCOMEXT SWIFT National • City Union Bank Swift Attack Incident • April • Central Banks DDo. S • SPEI Attack Mayo 14 • BANXICO report • BANXICO 5 institutions publish attacked 30 in cybernetic contingency attack Mayo 15 • BANXICO creates cybersecurity Director in the structure Mayo 16 October 22 • 3 Banks and 2 • Axa Insurance other financial Report an attack institutions was attacked • 300 millions pesos (15 M USD)
Audit Results Cyber security incidents on Mexican financial system in 2018 In the referred cybersecurity incident, BANJERCITO had no mechanisms for the identification, notification, containment, attention, resolution and mitigation of security incidents in critical systems like SPEI. As well, they did not carry out a chain of custody that ensure the integrity of all the components involved in the cybersecurity incident. Derived from the cybersecurity incidents of the SPEI that occurred in some banks, the SAI of Mexico recommended BANXICO to apply mechanisms to opportunely identify risk to cyber threat that allow them to take actions to mitigate possible systemic risks on SPEI.
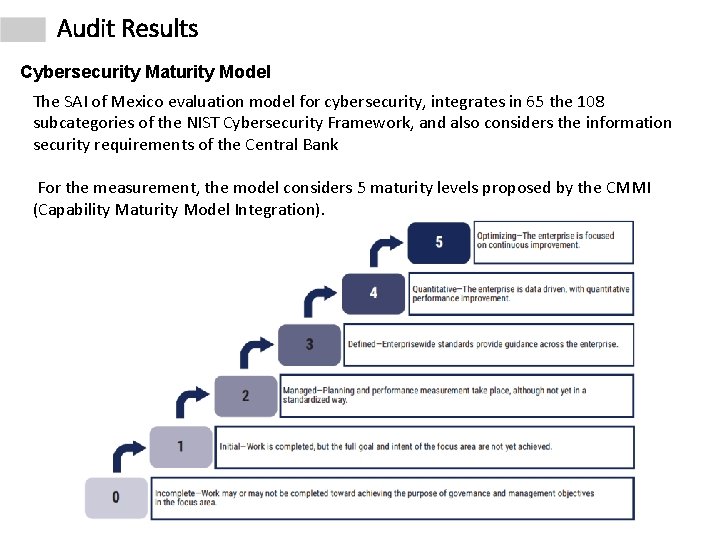
Audit Results Cybersecurity Maturity Model The SAI of Mexico evaluation model for cybersecurity, integrates in 65 the 108 subcategories of the NIST Cybersecurity Framework, and also considers the information security requirements of the Central Bank For the measurement, the model considers 5 maturity levels proposed by the CMMI (Capability Maturity Model Integration).
Audit Results Cybersecurity Maturity Evaluation This audit consider an initial evaluation for 7 entities of Mexico development banking, in this evaluation it was observed that two entities showed very low maturity levels, the other five, low levels. It is important to note that these low maturity levels imply some breaches on some information security controls required by Payment System normative from Central Bank (BANXICO). The result of the analysis was delivered to each entity with a report that contains the findings details and specific recommendations to initiate the necessary actions, to increase their maturity levels in each of the 65 categories reviewed. The entities provided new evidence, which led to a second evaluation by the SAI of Mexico.
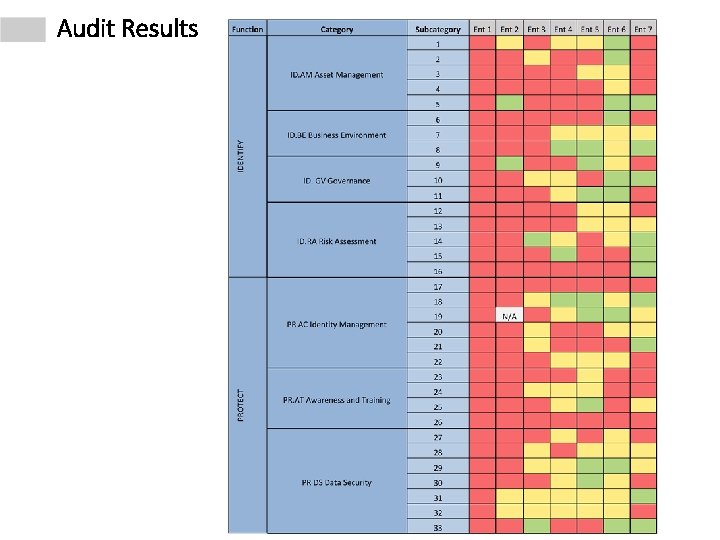
Audit Results
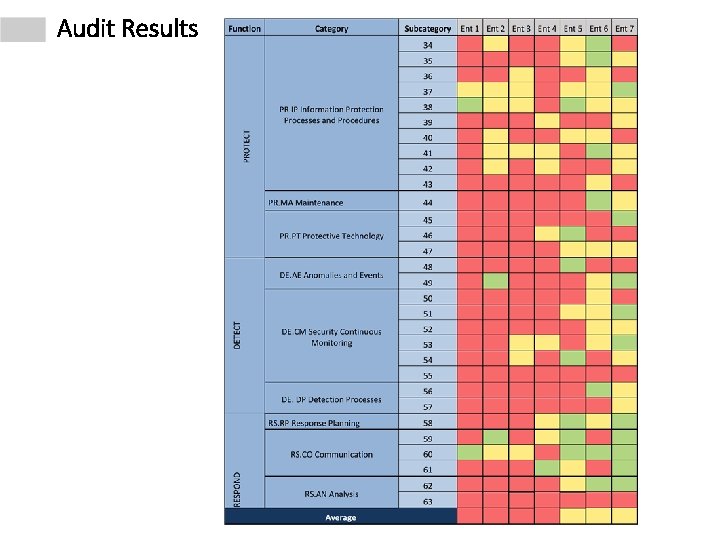
Audit Results
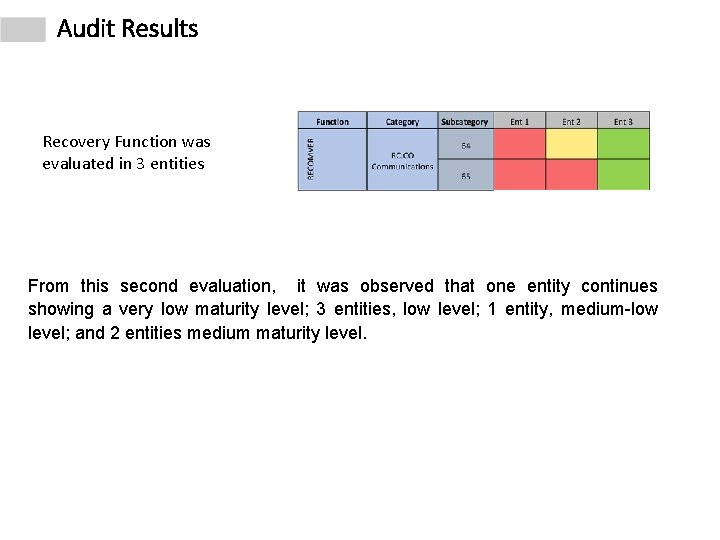
Audit Results Recovery Function was evaluated in 3 entities From this second evaluation, it was observed that one entity continues showing a very low maturity level; 3 entities, low level; 1 entity, medium-low level; and 2 entities medium maturity level.
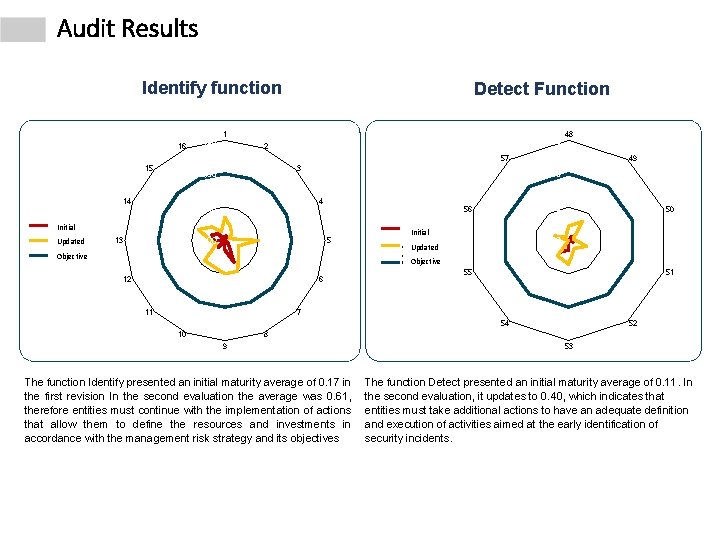
Audit Results Identify function 16 3, 00 Detect Function 1 3, 00 2 48 57 15 3 2, 00 14 2, 00 4 1, 00 56 Inicial Initial Actualizado Updated 49 50 Inicial 0, 00 13 5 Objetivo Objective 12 6 11 Initial 0, 00 Actualiz Updated ado Objective Objetivo 55 51 7 54 10 52 8 9 The function Identify presented an initial maturity average of 0. 17 in the first revision In the second evaluation the average was 0. 61, therefore entities must continue with the implementation of actions that allow them to define the resources and investments in accordance with the management risk strategy and its objectives 53 The function Detect presented an initial maturity average of 0. 11. In the second evaluation, it updates to 0. 40, which indicates that entities must take additional actions to have an adequate definition and execution of activities aimed at the early identification of security incidents.

Audit Results Protect function 46, 00 45, 00 47, 00 44, 00 42, 00 Updated Actualizado Objective Objetivo 3, 00 18, 00 19, 00 20, 00 22, 00 63 23, 00 1, 00 41, 00 24, 00 0, 00 40, 00 58 2, 50 21, 00 2, 00 43, 00 Inicial Initial 17, 00 Respond Function 25, 00 59 1, 00 Inicial Initial 0, 50 Actualizado Updated 0, 00 Objective Objetivo 39, 00 1, 50 26, 00 38, 00 27, 00 37, 00 28, 00 36, 00 35, 00 34, 00 29, 00 33, 00 32, 00 62 60 30, 00 31, 00 61 The function Protect presented an initial maturity average of 0. 28. In the second evaluation, it updates to 0. 59, which indicates that they have to increase the actions to protect the processes and organization assets. The function Respond presented an initial maturity average of 0. 21. In the second evaluation, it updates to 0. 86, which indicates that they have to continue with the definition and execution of appropriated activities to take decisions in case of detection of a security event.
Conclusions • Cybersecurity audit takes 1 year (2019) to SAI Mexico • For the development of the audit, SAI Mexico conducted cybersecurity training for ten IT auditors. • Due to the confidentiality of the information (security architecture of BANXICO), the evidence was stored in the Central Bank with a process that ensure confidentiality (SAI Mexico access), and integrity of the information. • The final report was elaborated with restrictions such as non disclose of evaluation rates, name of entities, and name of cybersecurity subcategories to minimize the risk of possible cyber attacks.
- Slides: 26