Auditable Privacy On TamperEvident Mix Networks Jong Youl

Auditable Privacy: On Tamper-Evident Mix Networks Jong Youl Choi Philippe Golle Markus Jakobsson jychoi@cs. indiana. edu pgolle@parc. com markus@indiana. edu Dept. of Computer Science Palo Alto Indiana University at Research Center Bloomington School of Informatics Indiana University at Bloomington
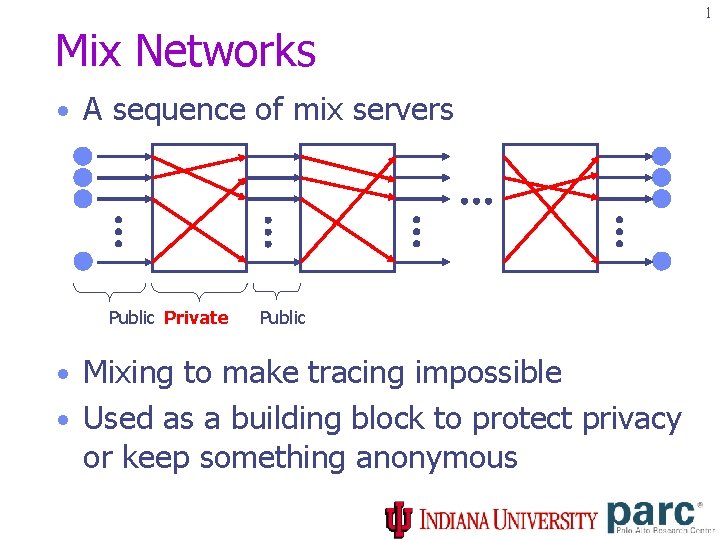
1 Mix Networks • A sequence of mix servers Public Private Public • Mixing to make tracing impossible • Used as a building block to protect privacy or keep something anonymous
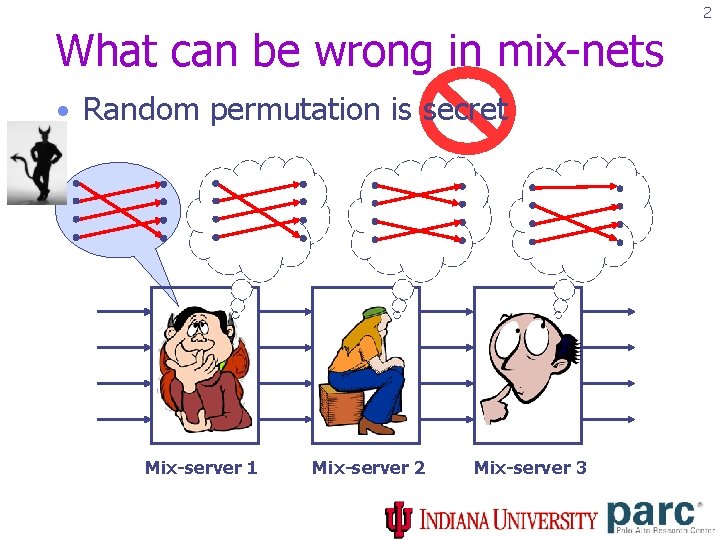
2 What can be wrong in mix-nets • Random permutation is secret Mix-server 1 Mix-server 2 Mix-server 3
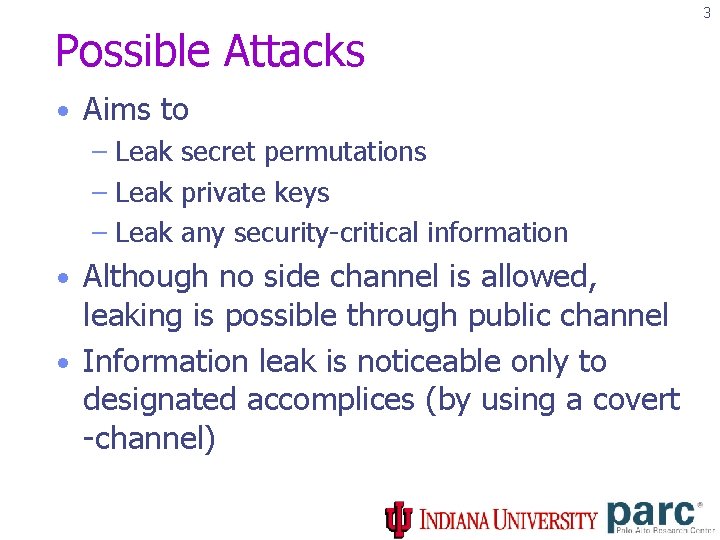
3 Possible Attacks • Aims to – Leak secret permutations – Leak private keys – Leak any security-critical information • Although no side channel is allowed, leaking is possible through public channel • Information leak is noticeable only to designated accomplices (by using a covert -channel)
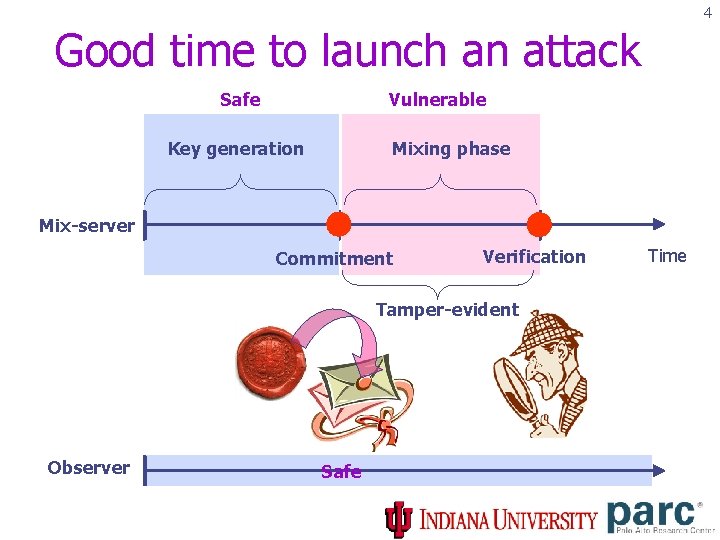
4 Good time to launch an attack Vulnerable Safe Key generation Mixing phase Mix-server Commitment Verification Tamper-evident Observer Safe Time
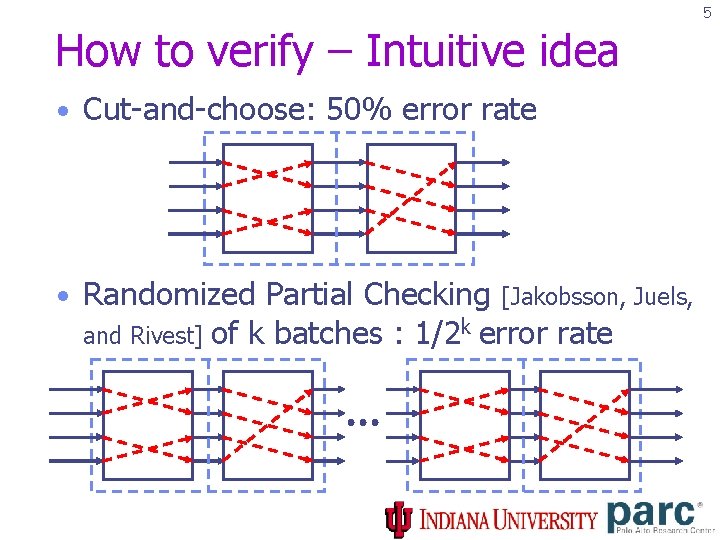
5 How to verify – Intuitive idea • Cut-and-choose: 50% error rate • Randomized Partial Checking [Jakobsson, Juels, and Rivest] of k batches : 1/2 k error rate
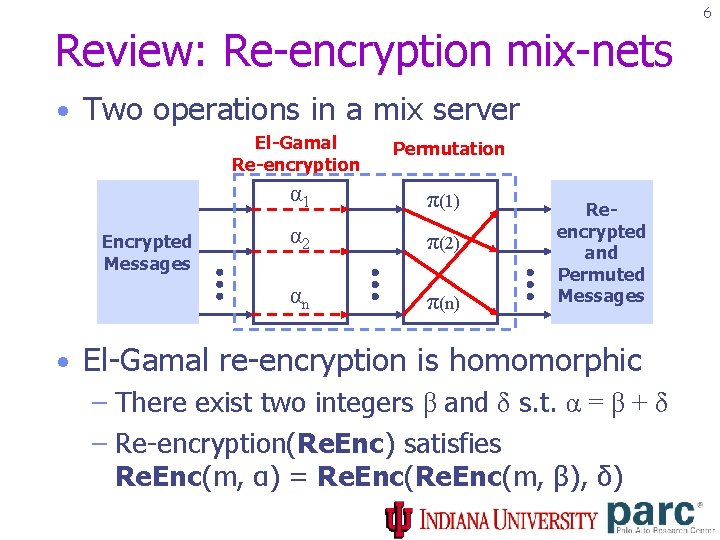
6 Review: Re-encryption mix-nets • Two operations in a mix server El-Gamal Re-encryption Encrypted Messages Permutation α 1 π(1) α 2 π(2) αn π(n) Reencrypted and Permuted Messages • El-Gamal re-encryption is homomorphic – There exist two integers β and δ s. t. α = β + δ – Re-encryption(Re. Enc) satisfies Re. Enc(m, α) = Re. Enc(m, β), δ)
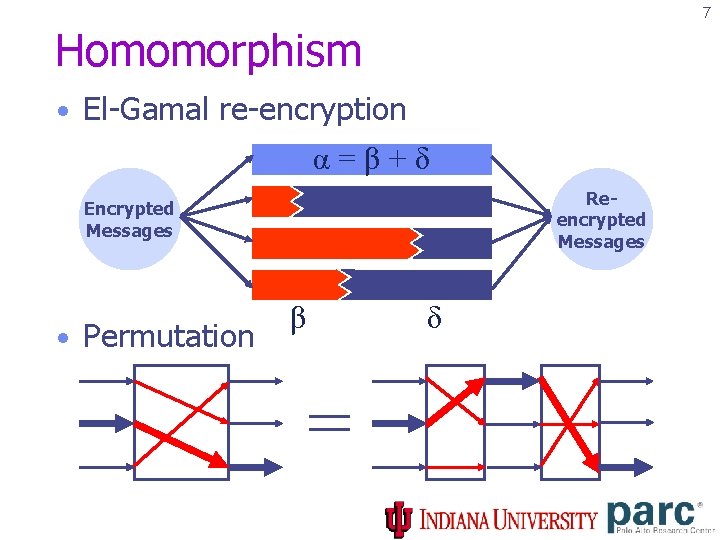
7 Homomorphism • El-Gamal re-encryption α=β+δ Reencrypted Messages Encrypted Messages • Permutation β δ =
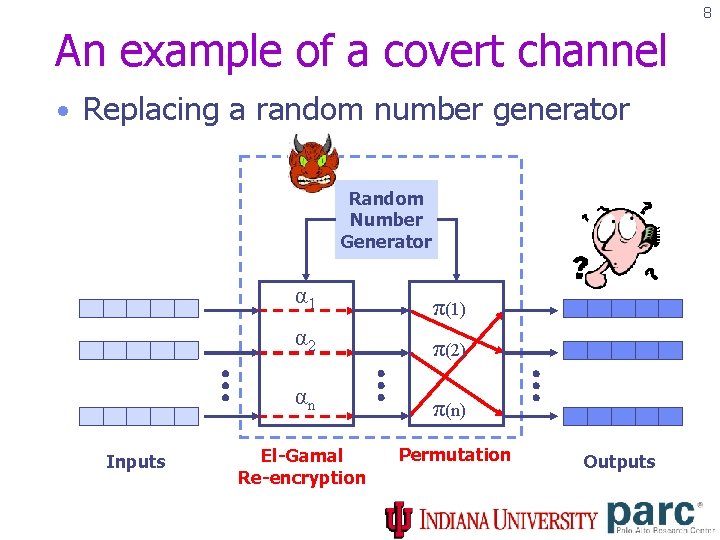
8 An example of a covert channel • Replacing a random number generator Random Number Generator Inputs α 1 π(1) α 2 π(2) αn π(n) El-Gamal Re-encryption Permutation Outputs
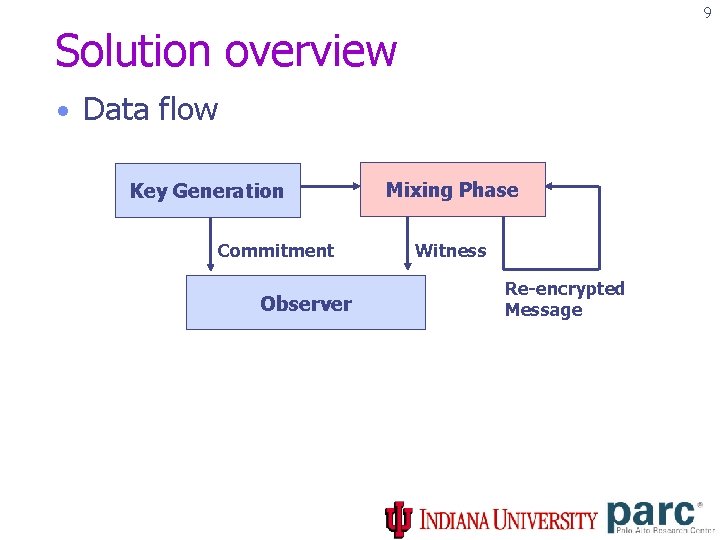
9 Solution overview • Data flow Key Generation Commitment Observer Mixing Phase Witness Re-encrypted Message
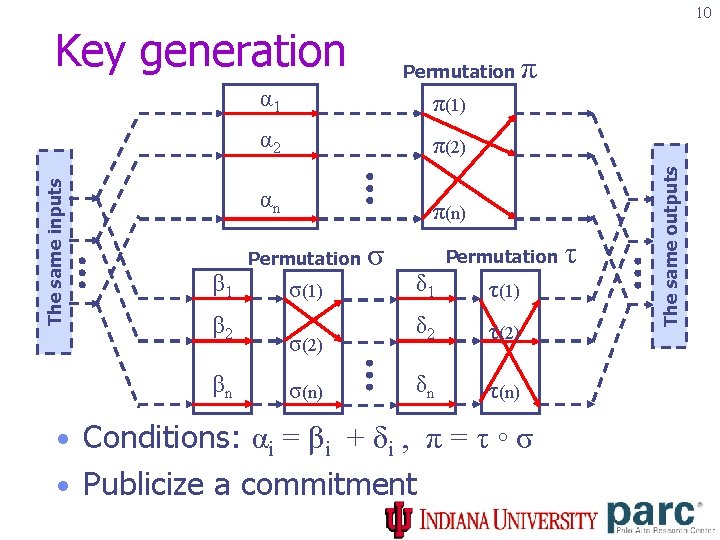
10 α 1 π(1) α 2 π(2) αn π(n) Permutation β 1 β 2 βn Permutation σ(1) σ(2) σ(n) σ π Permutation δ 1 τ(1) δ 2 τ(2) δn τ(n) • Conditions: αi = βi + δi , π = τ ◦ σ • Publicize a commitment τ The same outputs The same inputs Key generation
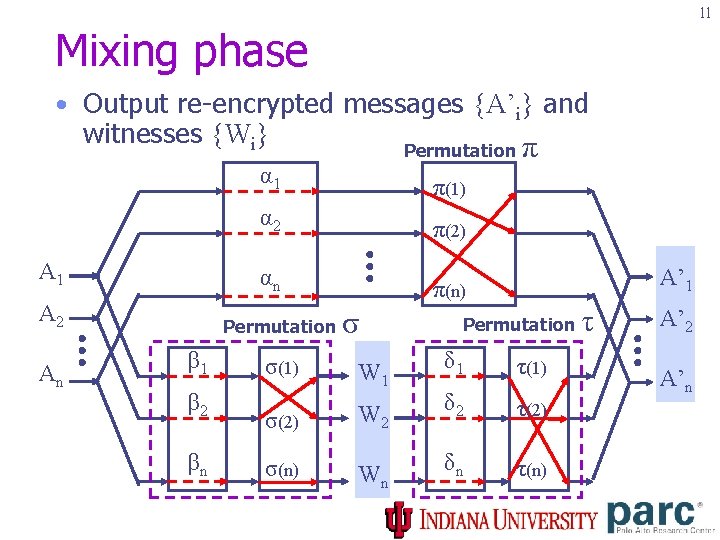
11 Mixing phase • Output re-encrypted messages {A’i} and witnesses {Wi} A 1 A 2 An α 1 π(1) α 2 π(2) αn π(n) Permutation β 1 β 2 βn Permutation σ π A’ 1 Permutation δ 1 τ(1) σ(2) W 2 δ 2 τ(2) σ(n) Wn δn τ(n) σ(1) W 1 τ A’ 2 A’n
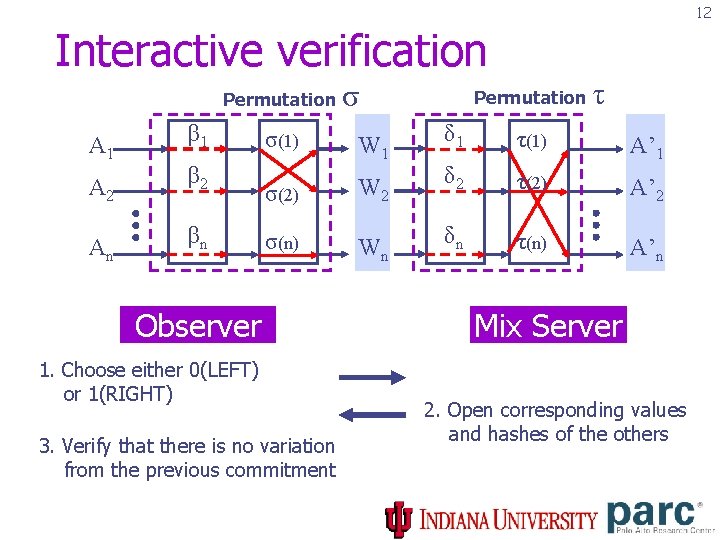
12 Interactive verification Permutation A 1 β 1 A 2 β 2 An βn σ Permutation τ δ 1 τ(1) σ(2) W 2 δ 2 A’ 1 τ(2) A’ 2 σ(n) Wn δn τ(n) A’n σ(1) W 1 Observer 1. Choose either 0(LEFT) or 1(RIGHT) 3. Verify that there is no variation from the previous commitment Mix Server 2. Open corresponding values and hashes of the others
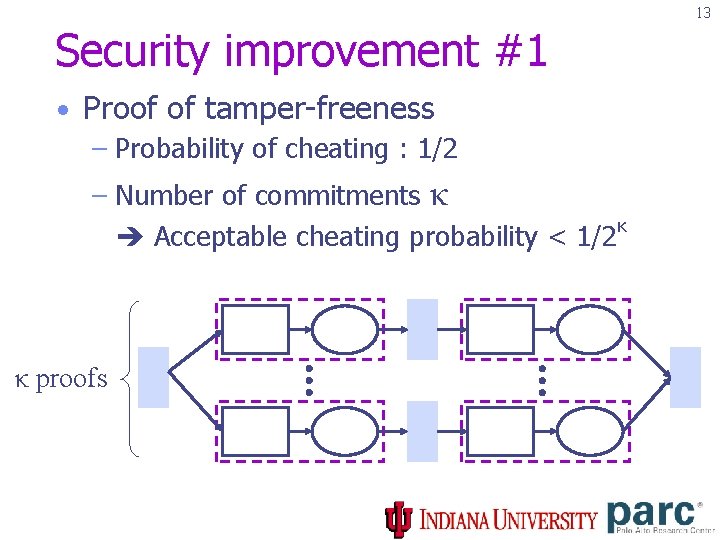
13 Security improvement #1 • Proof of tamper-freeness – Probability of cheating : 1/2 – Number of commitments κ κ Acceptable cheating probability < 1/2 κ proofs
14 Security improvement #2 • Undercover observer – Challenges are automatically chosen from κ bits of output hash({A’i}) – Non-interactive proof Stealthy observation – Attackers are hard to find non-interactive observers. Thus we called undercover observers Key Generation Commitment Mixing Phase Witness
15 Conclusion • A covert-channel in mix networks threatens privacy • New notion of security : Tamper-evidence, detecting variations from prescribed commitments • Stealthy operation of non-interactive observer Or, Send me an email : jychoi@cs. indiana. edu
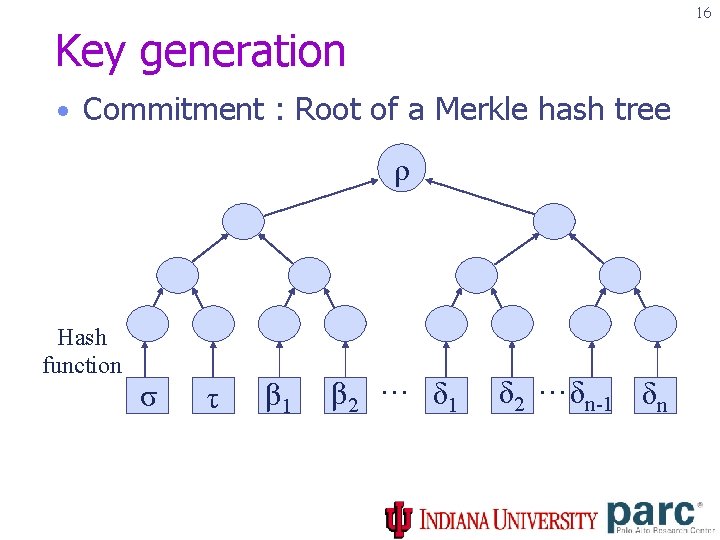
16 Key generation • Commitment : Root of a Merkle hash tree ρ Hash function σ τ β 1 β 2 … δ 1 δ 2 … δn-1 δn
- Slides: 17