Attacks on TLS Douglas Stebila Last updated June
Attacks on TLS Douglas Stebila Last updated June 6, 2019
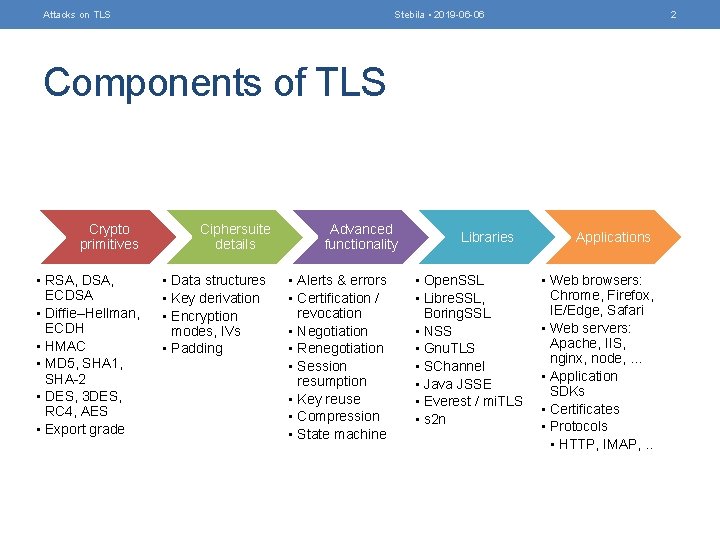
Attacks on TLS Stebila • 2019 -06 -06 2 Components of TLS Crypto primitives • RSA, DSA, ECDSA • Diffie–Hellman, ECDH • HMAC • MD 5, SHA 1, SHA-2 • DES, 3 DES, RC 4, AES • Export grade Ciphersuite details • Data structures • Key derivation • Encryption modes, IVs • Padding Advanced functionality • Alerts & errors • Certification / revocation • Negotiation • Renegotiation • Session resumption • Key reuse • Compression • State machine Libraries • Open. SSL • Libre. SSL, Boring. SSL • NSS • Gnu. TLS • SChannel • Java JSSE • Everest / mi. TLS • s 2 n Applications • Web browsers: Chrome, Firefox, IE/Edge, Safari • Web servers: Apache, IIS, nginx, node, … • Application SDKs • Certificates • Protocols • HTTP, IMAP, . .
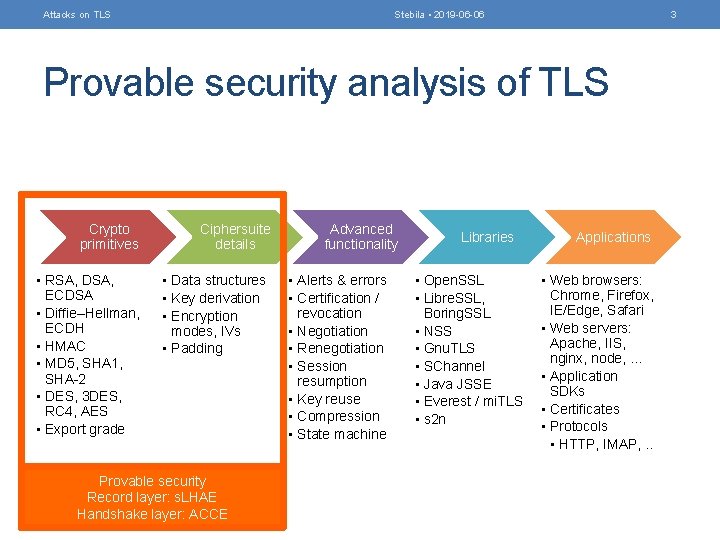
Attacks on TLS Stebila • 2019 -06 -06 3 Provable security analysis of TLS Crypto primitives • RSA, DSA, ECDSA • Diffie–Hellman, ECDH • HMAC • MD 5, SHA 1, SHA-2 • DES, 3 DES, RC 4, AES • Export grade Ciphersuite details • Data structures • Key derivation • Encryption modes, IVs • Padding Provable security Record layer: s. LHAE Handshake layer: ACCE Advanced functionality • Alerts & errors • Certification / revocation • Negotiation • Renegotiation • Session resumption • Key reuse • Compression • State machine Libraries • Open. SSL • Libre. SSL, Boring. SSL • NSS • Gnu. TLS • SChannel • Java JSSE • Everest / mi. TLS • s 2 n Applications • Web browsers: Chrome, Firefox, IE/Edge, Safari • Web servers: Apache, IIS, nginx, node, … • Application SDKs • Certificates • Protocols • HTTP, IMAP, . .
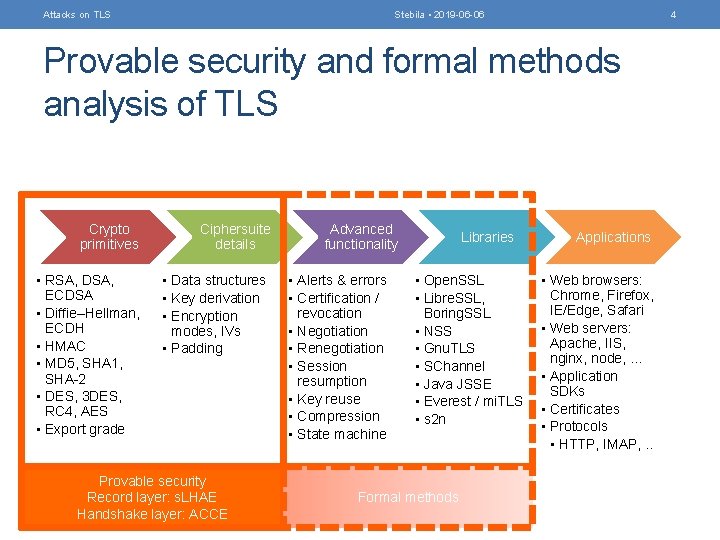
Attacks on TLS Stebila • 2019 -06 -06 4 Provable security and formal methods analysis of TLS Crypto primitives • RSA, DSA, ECDSA • Diffie–Hellman, ECDH • HMAC • MD 5, SHA 1, SHA-2 • DES, 3 DES, RC 4, AES • Export grade Ciphersuite details • Data structures • Key derivation • Encryption modes, IVs • Padding Provable security Record layer: s. LHAE Handshake layer: ACCE Advanced functionality • Alerts & errors • Certification / revocation • Negotiation • Renegotiation • Session resumption • Key reuse • Compression • State machine Libraries • Open. SSL • Libre. SSL, Boring. SSL • NSS • Gnu. TLS • SChannel • Java JSSE • Everest / mi. TLS • s 2 n Formal methods Applications • Web browsers: Chrome, Firefox, IE/Edge, Safari • Web servers: Apache, IIS, nginx, node, … • Application SDKs • Certificates • Protocols • HTTP, IMAP, . .
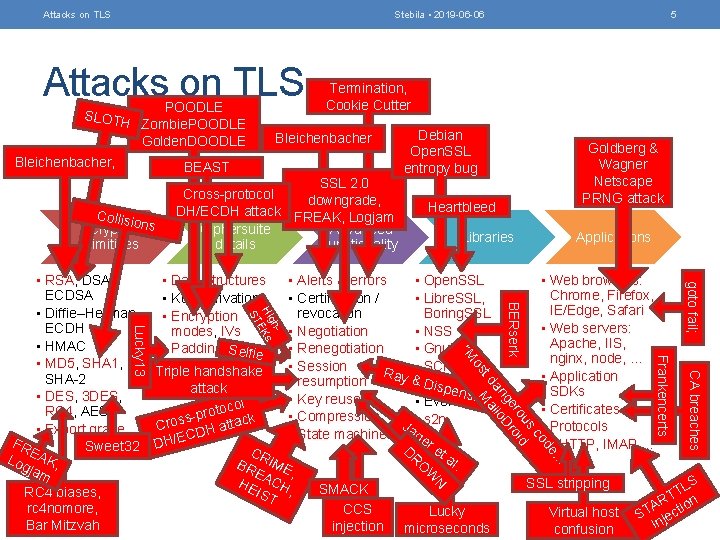
Attacks on TLS Stebila • 2019 -06 -06 Attacks on TLS SLOTH POODLE Zombie. POODLE Golden. DOODLE Bleichenbacher, Termination, Cookie Cutter Bleichenbacher BEAST Collisi o Crypto ns primitives 5 SSL 2. 0 Cross-protocol downgrade, DH/ECDH attack FREAK, Logjam Ciphersuite Advanced details functionality Debian Open. SSL entropy bug Goldberg & Wagner Netscape PRNG attack Heartbleed Libraries Applications goto fail; CA breaches Frankencerts “M e od c us ro oid BERserk ge Dr an llo t d Ma os gh Hi Ks E ST Lucky 13 • RSA, DSA, • Data structures • Alerts & errors • Open. SSL • Web browsers: ECDSA Chrome, Firefox, • Key derivation • Certification / • Libre. SSL, IE/Edge, Safari • Diffie–Hellman, • Encryption revocation Boring. SSL ECDH • Web servers: modes, IVs • Negotiation • NSS Apache, IIS, • HMAC • Padding Selfie • Renegotiation • Gnu. TLS nginx, node, … • MD 5, SHA 1, • Session • SChannel Triple handshake Ray • Application SHA-2 & • D resumption Java JSSE ispen attack SDKs sa • DES, 3 DES, • Key reuse • Everest / mi. TLS l o c • Certificates RC 4, AES proto ck • Compression s • s 2 n s o a J tt Cr • Protocols • Export grade DH a • State machine age C E / FR • HTTP, IMAP, . . Sweet 32 DH D r et EA CR R a Log K, l O BR IME jam W. EA , N HE CH S SSL stripping L SMACK , T IST RC 4 biases, RT ion A rc 4 nomore, CCS Lucky Virtual host ST ject in Bar Mitzvah injection microseconds confusion ” …
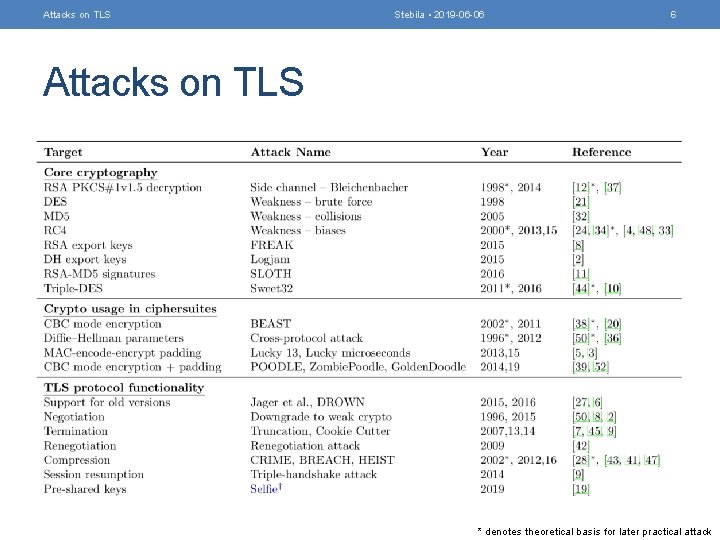
Attacks on TLS Stebila • 2019 -06 -06 6 Attacks on TLS * denotes theoretical basis for later practical attack
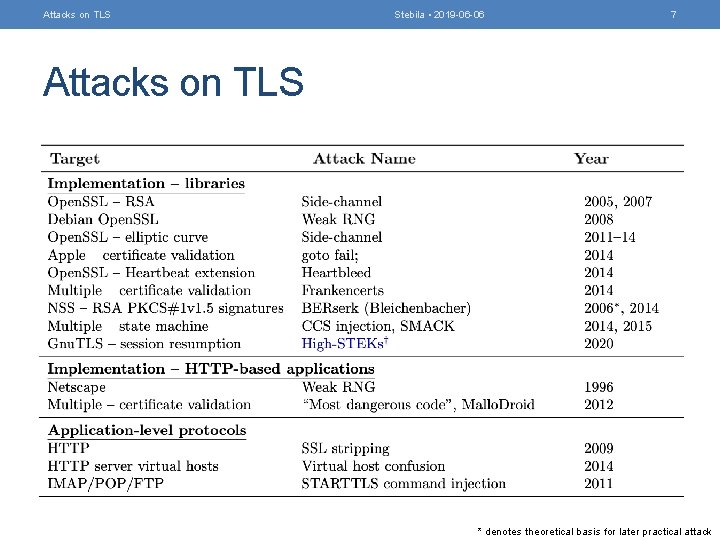
Attacks on TLS Stebila • 2019 -06 -06 7 Attacks on TLS * denotes theoretical basis for later practical attack
- Slides: 7