Attacking Networks Types of Attacks Broadly speaking there
Attacking Networks Types of Attacks • Broadly speaking, there are two types of attacks: • External Attacks. – These come from computers outside of the local network. • Internal Attacks. – These come from computers inside the local network.
Attacking Networks Types of Attacks • Both internal and external attacks use the same exploits.
Attacking Networks Types of Attacks • But, it is worthwhile treating external and internal attacks separately – Because network security measures tend to concentrate on watching for and stopping attacks coming into a network from the outside.
Attacking Networks Types of Attacks • This is especially true for attacks coming from networks outside of an organization.
Attacking Networks Types of Attacks • Both external and internal attacks can take the following form. – Intrusion-based attacks – Service interruption-based attacks – Resource-based attacks. – Data-based attacks.
Attacking Networks Intrusion-based Attacks • Intrusion-based attacks are attempts to gain access to a system. • The goal is to gain system administrator access to the computer system.
Attacking Networks Service Interruption-based Attacks • The second major class of attacks are Service Interruption-based Attacks. • The goal of these attacks are to prevent the computers from doing their job. • Some examples, – Making them so busy they crash, or cannot respond to requests from clients. – Sending them so many packets that they are inaccessible for potential clients.
Attacking Networks Service Interruption-based Attacks • These attacks are specifically designed to limit access to these computers. – Particularly customers and employees of online companies and organizations.
Attacking Networks Service Interruption-based Attacks • Popular attack of this type are – Denial of Service (DOS) attacks - Flooding the computers or the network itself with packets to make the servers inaccessible. – Web page corruption attacks - Break in to a site’s web servers and change the web pages they host.
Attacking Networks Service Interruption-based Attacks • DOS attacks do not require an attacker to break in to a computer – Just keep others from accessing it.
Attacking Networks Service Interruption-based Attacks • A web page defacement does require that an attacker gain at least partial access to a computer – In order to change the web pages it serves.
Denial of Service
Attacking Networks Denial of Service • A classic DOS attack was the SYN flood – The attacker computer sends a stream of TCP SYN messages to the victim’s computer. – The victim computer responds to all of the SYN messages, starting up a connection for each one. – The attacker does not respond to the victim’s ACK/SYN messages with ACKs. – The overhead from maintaining all of these open connections slows down the victim computer, disabling it or perhaps even causing it to crash.
Attacking Networks Denial of Service • There are many variations of the DOS attack. • They exploit different weaknesses of the network protocols.

The Ping of Death
Attacking Networks ICMP • The Internet Control Message Protocol (ICMP) allows routers to send error and control messages to other computers, especially routers, on the network. • ICMP operates at the network (routing) layer of the TCP/IP stack.
Attacking Networks Ping • The most widely used ICMP message is the ping. • Basically, ping is used to see if packets are reaching a particular computer. • The client sends a ping request, and when it receives it, the server responds with a reply.
Attacking Networks Ping • The ping of death uses the ICMP ping to DOS a computer by crashing it. • It does this by sending an illegally large ping packet. – In this case, more than 65, 536 bytes. • The packet causes a buffer overflow that crashes the computer.
Attacking Networks Ping • Modern versions of all major operating systems have fixed this vulnerability, and now check incoming ICMP packets to prevent a buffer overflow of this type.
The Smurf Attack
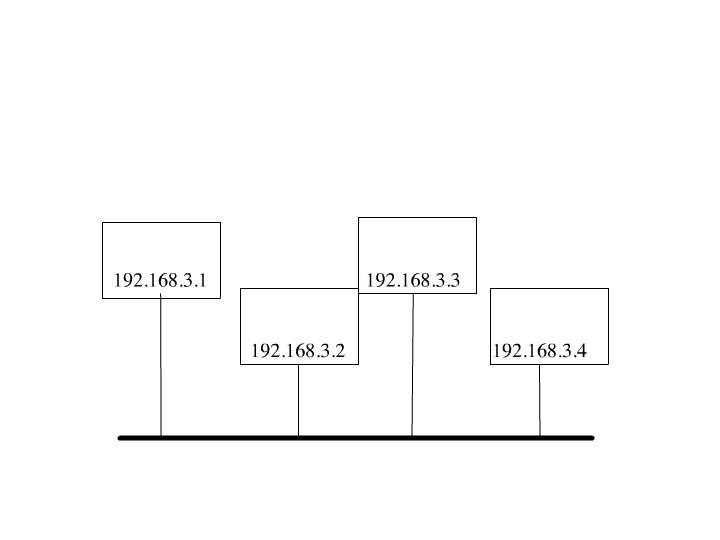
Attacking Networks Broadcast • Normally, packets are sent to a single recipient. • But, they can be broadcast - sent to all computers on the local network.
Attacking Networks Smurf • The Smurf attack broadcasts a ping to all of the machines on a local network. • It forges (spoofs) the return address of the ping packet to be that of the victim. • All of the machines receiving the broadcast ping then send reply packets to the victim.
Attacking Networks Smurf • If enough computers (possibly thousands) receive the forged ping request, the sheer number of reply packets can crash the victim computer, or clog the network.
Attacking Networks Smurf • There is really no way for a potential victim to harden their computer against this attack.
Attacking Networks Smurf • Computers and networks can help prevent themselves from being used as intermediaries in the attack. – Computers do not reply to broadcast pings. – Block broadcast packets at the router. • This can help the potential intermediary, as they can also be a victim if the reply packets swamp their local network.

Traffic Redirection
Attacking Networks Denial of Service • Traffic redirection DOS attacks make it impossible for packets to reach a server by altering information in routing tables. – In essence giving bad directions for routing packets.
Attacking Networks Denial of Service • DNS attack DOS attacks make a server’s site inaccessible by keeping client computers from getting a server’s IP address. • This is done by either – attacking and co-opting a DNS server, or – having clients access a fake DNS server controlled by the attacker. • The malicious DNS server then gives bad translations for the victim’s server.
Attacking Networks Denial of Service • As networks and server computers become faster and more robust, it is more difficult for an attacker to mount classic DOS attacks on an Internet site.
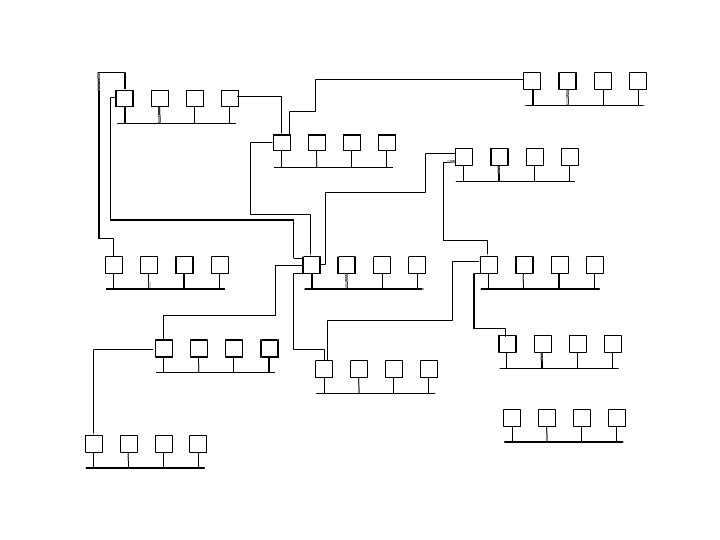
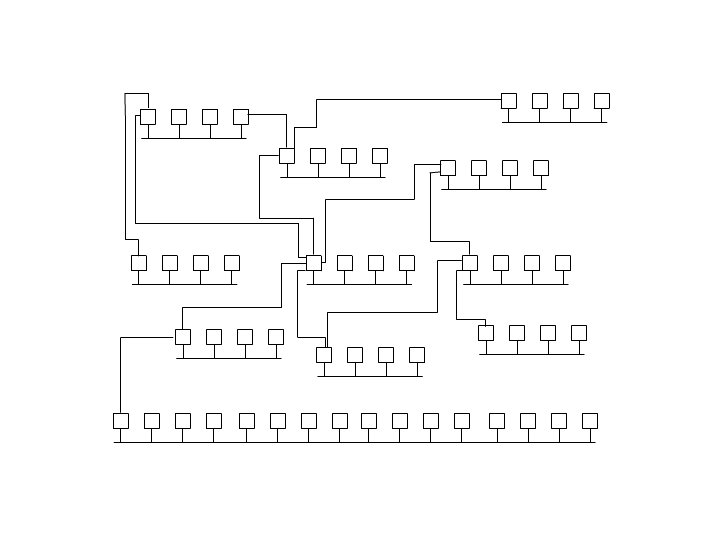
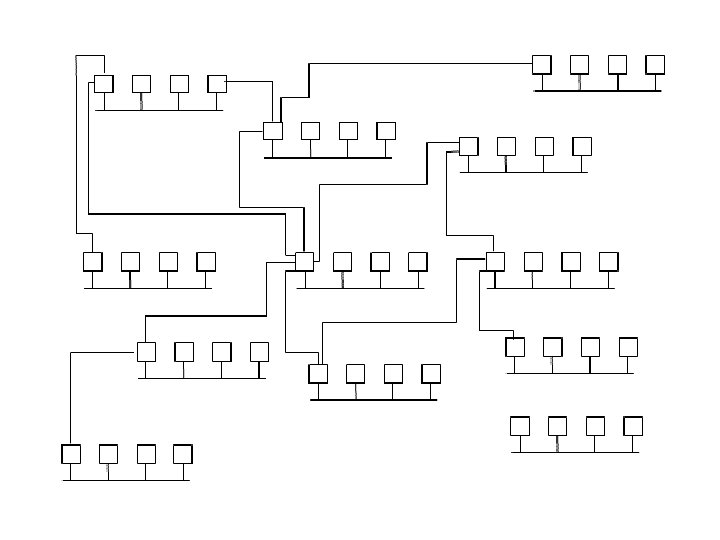
Attacking Networks Denial of Service • To counter this, attackers have taken to using Distributed Denial of Service (DDOS) attacks. • In a DDOS attack, large numbers of computers simultaneously connect to or otherwise attack a victim’s site.
Attacking Networks Denial of Service • Attackers get the large numbers of computers necessary for a DDOS attack by using large numbers of zombie computers that have been previously attacked and take over using viruses, worms, etc. • These zombies are given commands to take part in the DDOS attack.

Session Hijacking
Attacking Networks Session Hijacking • A DOS attack that keeps a victim computer from responding over the network may allow the attacker to do a session hijacking attack to the victim.
Attacking Networks Session Hijacking • In a session hijacking attack, the attacker disables a computer in the middle of a network connection, and then impersonates the disabled computer.
Attacking Networks Session Hijacking • The computer at the other end of the hijacked connection still thinks it is connected to the original, disabled computer. • This may allow the attacker to access valuable information from the computer at the other end of the connection it has hijacked.

Resource-based Attacks
Attacking Networks Resource-Based Attacks • Resource-based attacks are designed to gain access to additional resources for the attacker. • Basically, taking over machines in order to set up illicit servers on them.
Attacking Networks Resource-Based Attacks • Some resource-based attack examples -
Attacking Networks Resource-Based Attacks • Data storage (ftp) servers to store files (e. g. illicit copies of software and media). – Warez.
Attacking Networks Resource-Based Attacks • Message (IRC) servers to host chat sessions.
Attacking Networks Resource-Based Attacks • Mail servers to send spam.
Attacking Networks Resource-Based Attacks • Computers from which to launch subsequent attacks (zombies, bots).
Attacking Networks Resource-Based Attacks • Resource-based attacks typically are intrusion attacks. • That is, the attacker gains control of the computer in order to set up their desired illicit server(s).

Data-based Attacks
Attacking Networks Data-Based Attacks • Data-based attacks are designed to steal or modify data. • Basically, high-tech theft and fraud. • These are also intrusion-based attacks, so the attacker can gain access to the data to steal or alter it.
Attacking Networks Data-Based Attacks • Recent thefts of credit card data from a credit card purchase processing firm are high profile data-based attacks. • The attackers stole large number of credit card numbers, and possibly other data that can be used for fraudulent purchases or possibly identity theft.

Reconnaissance
Attacking Networks Reconnaissance • Before mounting an exploit, an attacker needs reconnaissance - they need to know what attacks will work on their intended targets. – Or, viewed alternately, which servers are vulnerable to their chosen attack(s).
Attacking Networks Port Scanning • Port scanning is part of that reconnaissance. • The purpose of port scanning is to see which, if any, services a computer is offering.
Attacking Networks Port Scanning • In port scanning, 1. the attacker runs a program that attempts to open a connection on each of the ports of a potential victim machine. 2. The program sees which ports respond.
Attacking Networks Port Scanning • Those ports that respond represent services that the computer is offering over the network.
Attacking Networks Port Scanning • By knowing what services a potential victim machine is offering, that attacker can then determine potential vulnerabilities that they can exploit. • For example, perhaps they are running a version of the IIS web server that has a buffer -overrun vulnerability.

Sniffing
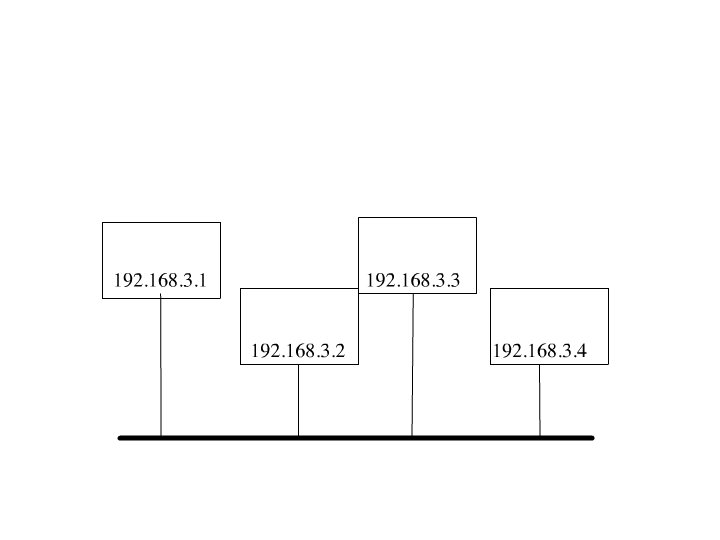
Attacking Networks Sniffing • One major security vulnerability is the digital network equivalent of eavesdropping or wiretapping - sniffing. • On many common types of networks, all of the computers on the local network see all of the packets on that network. • Ethernet, the most common type of non-wireless network, can have this property.
Attacking Networks Sniffing • A computer on the local network can engage in sniffing. • Sniffing is capturing a copy of the packets that are on the local network. • The packets can then be analyzed for useful data, – User IDs and passwords, – Technical information that might be useful for an attack – Other valuable information, e. g. credit card numbers, keys for access to software.
Module Eight Worms
Worms • As discussed previously, worms are malicious software that is used to attack computers. • Although a worm can be spread in other manners, they are most at home on computer networks.
Worms Sniffing • Many modern worms install sniffers once they have taken over a victim computer.
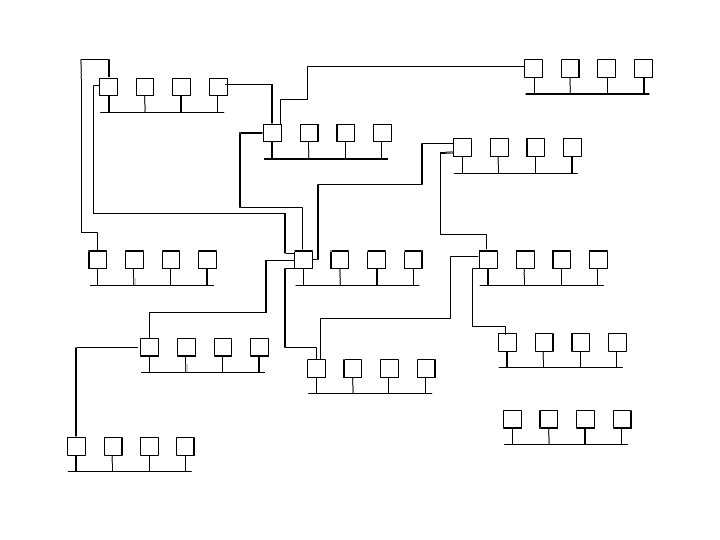
Worms Infecting New Machines • They can find other machines to infect, either – By targeting IP addresses at random, or – Attacking specific machines or networks. • The speed of modern computers and networks allow worms to target very large numbers of potential victims.
- Slides: 65