Attacking and Crashing Io T devices via Bluetooth
Attacking and Crashing Io. T devices via Bluetooth LE Protocol Ajay Pratap Singh & Pratap Chandra
Agenda • BLE in Io. T devices • Bluetooth Low Energy Protocol Stack • Functionality of Protocol Layers in BLE • BLE Pairing Mechanisms • Attacking Io. T Devices – Case Studies
Internet of Things • What The internet of things (Io. T) is the network of physical devices, vehicles, buildings and other items—embedded with electronics, software, sensors, actuators, and network connectivity that enable these objects to collect and exchange data. Source : Wikipedia
IOT Devices Smart Homes Connected Camera Wearable devices Tooth brush Automobile Industry More devices can be found at: http: //iotlist. co
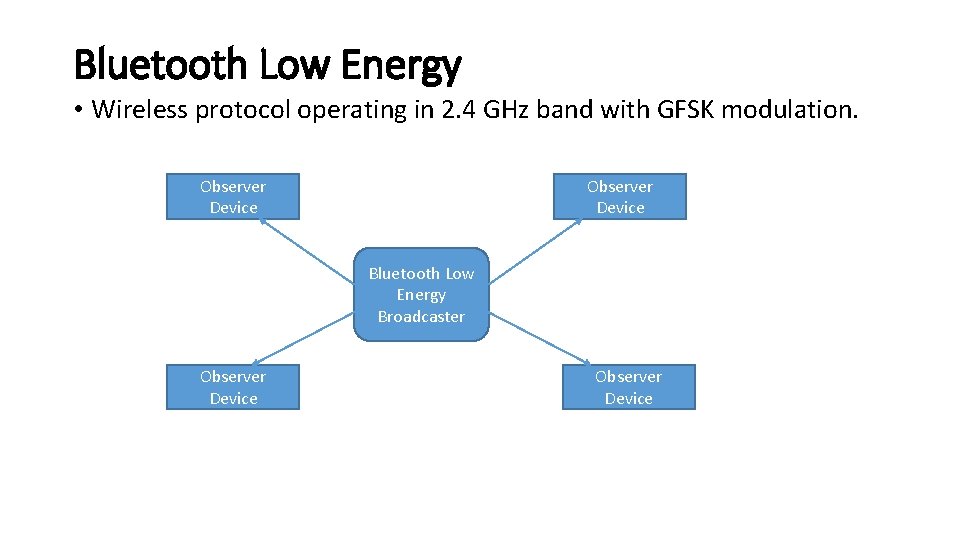
Bluetooth Low Energy • Wireless protocol operating in 2. 4 GHz band with GFSK modulation. Observer Device Bluetooth Low Energy Broadcaster Observer Device
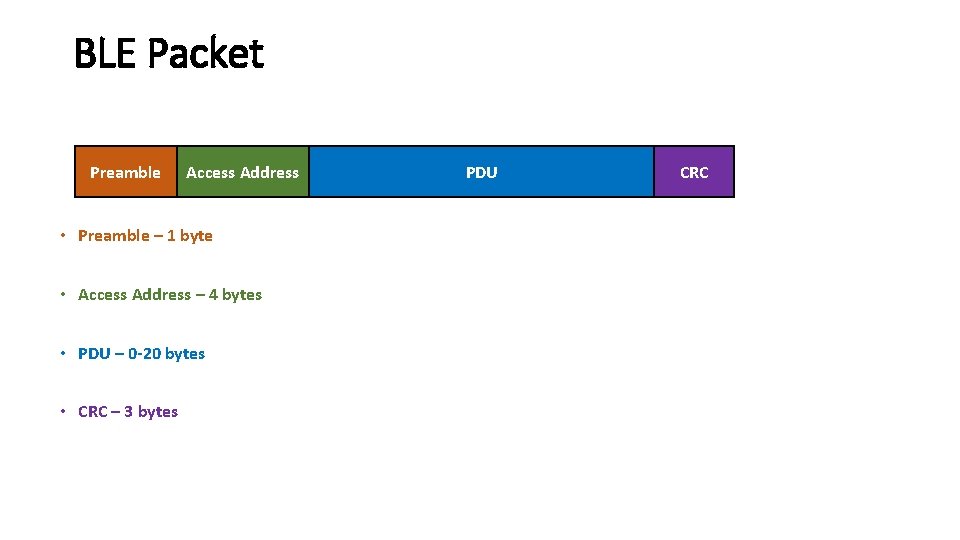
BLE Packet Preamble Access Address • Preamble – 1 byte • Access Address – 4 bytes • PDU – 0 -20 bytes • CRC – 3 bytes PDU CRC
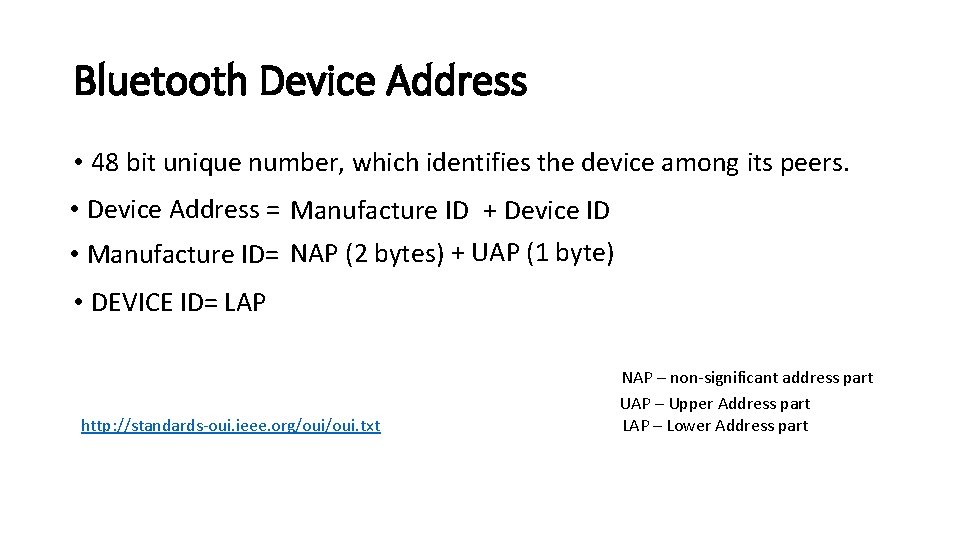
Bluetooth Device Address • 48 bit unique number, which identifies the device among its peers. • Device Address = Manufacture ID + Device ID • Manufacture ID= NAP (2 bytes) + UAP (1 byte) • DEVICE ID= LAP http: //standards-oui. ieee. org/oui. txt NAP – non-significant address part UAP – Upper Address part LAP – Lower Address part
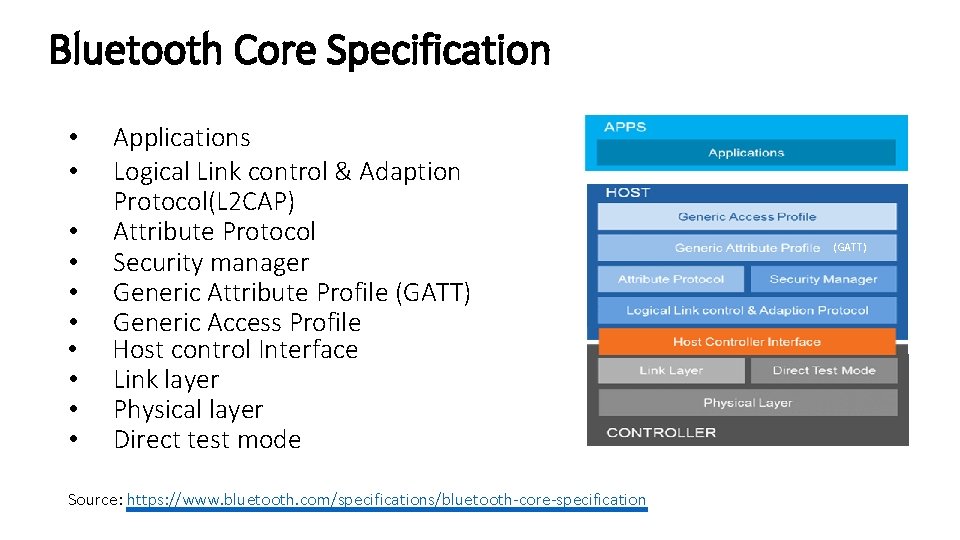
Bluetooth Core Specification • • • Applications Logical Link control & Adaption Protocol(L 2 CAP) Attribute Protocol Security manager Generic Attribute Profile (GATT) Generic Access Profile Host control Interface Link layer Physical layer Direct test mode Source: https: //www. bluetooth. com/specifications/bluetooth-core-specification (GATT)
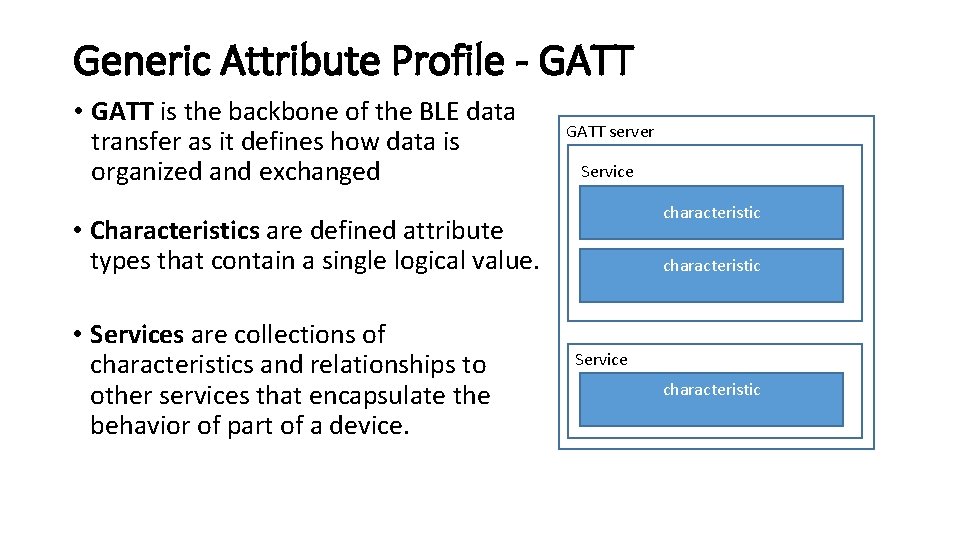
Generic Attribute Profile - GATT • GATT is the backbone of the BLE data transfer as it defines how data is organized and exchanged GATT server Service characteristic • Characteristics are defined attribute types that contain a single logical value. • Services are collections of characteristics and relationships to other services that encapsulate the behavior of part of a device. characteristic Service characteristic
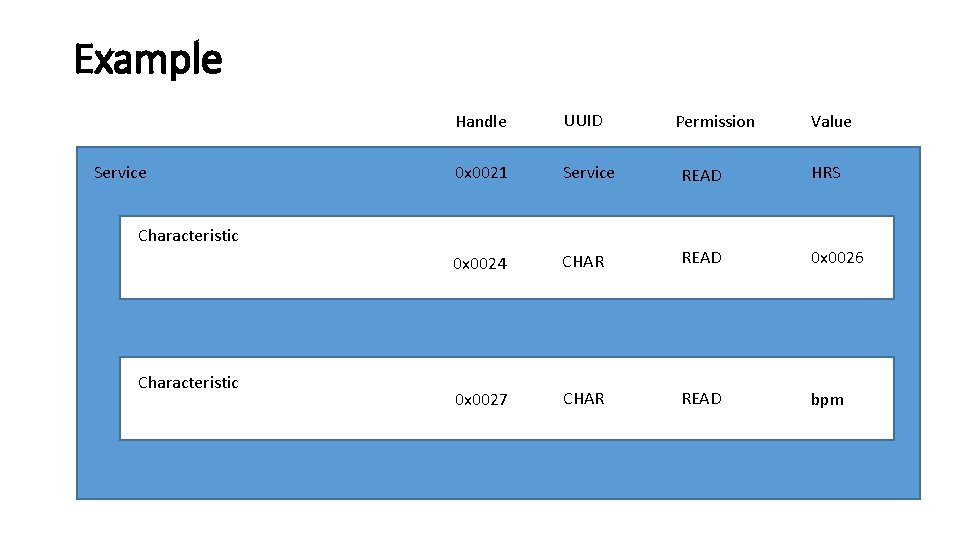
Example Service Handle UUID 0 x 0021 Service READ HRS 0 x 0024 CHAR READ 0 x 0026 0 x 0027 CHAR READ bpm Characteristic Permission Value
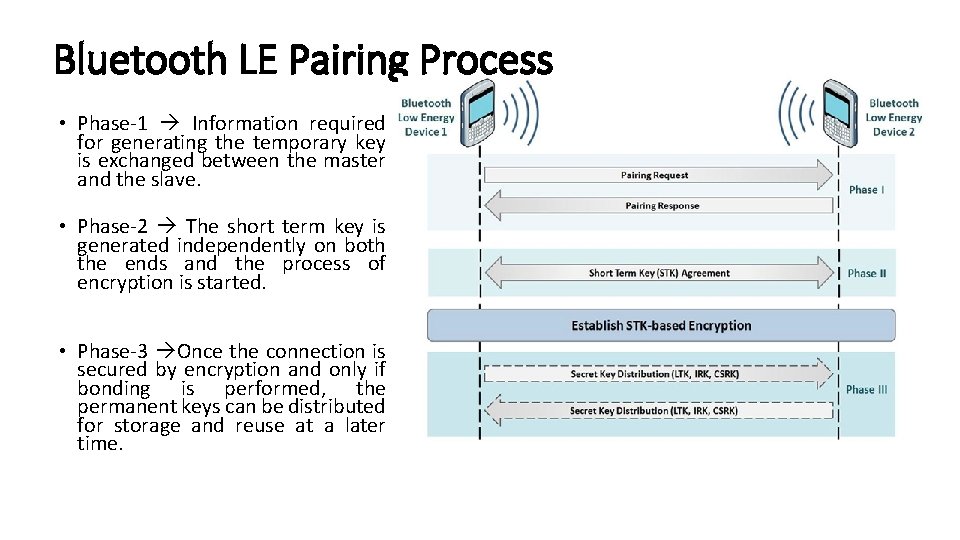
Bluetooth LE Pairing Process • Phase-1 Information required for generating the temporary key is exchanged between the master and the slave. • Phase-2 The short term key is generated independently on both the ends and the process of encryption is started. • Phase-3 Once the connection is secured by encryption and only if bonding is performed, the permanent keys can be distributed for storage and reuse at a later time.
CASE STUDIES
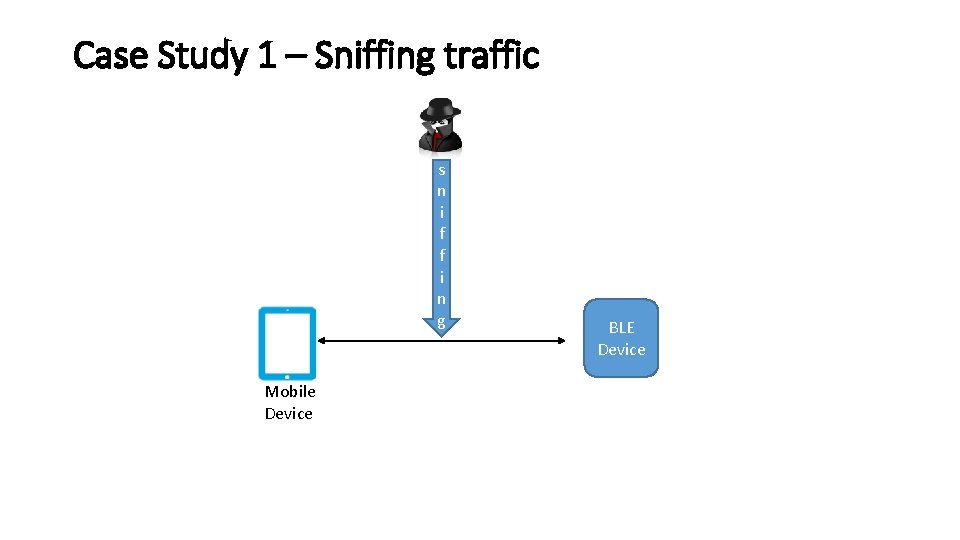
Case Study 1 – Sniffing traffic s n i f f i n g Mobile Device BLE Device
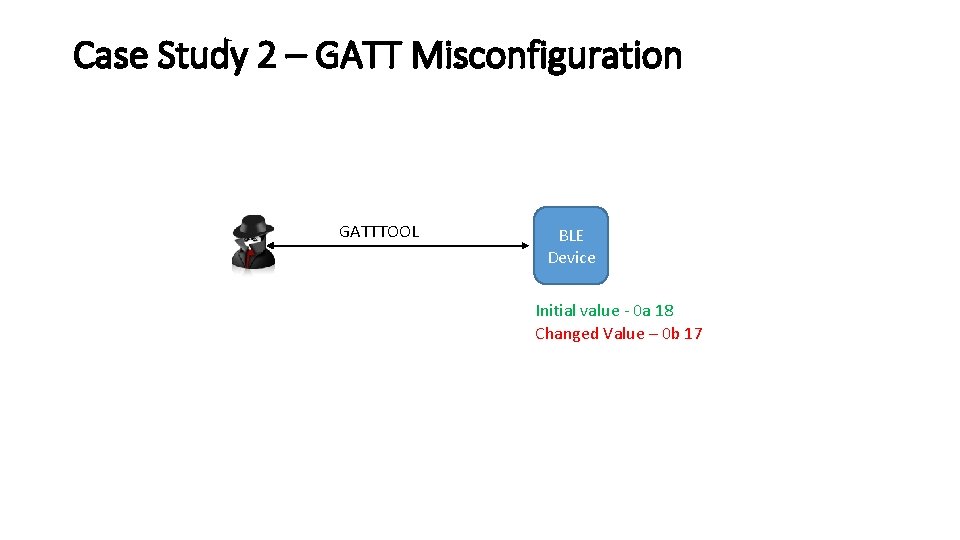
Case Study 2 – GATT Misconfiguration GATTTOOL BLE Device Initial value - 0 a 18 Changed Value – 0 b 17
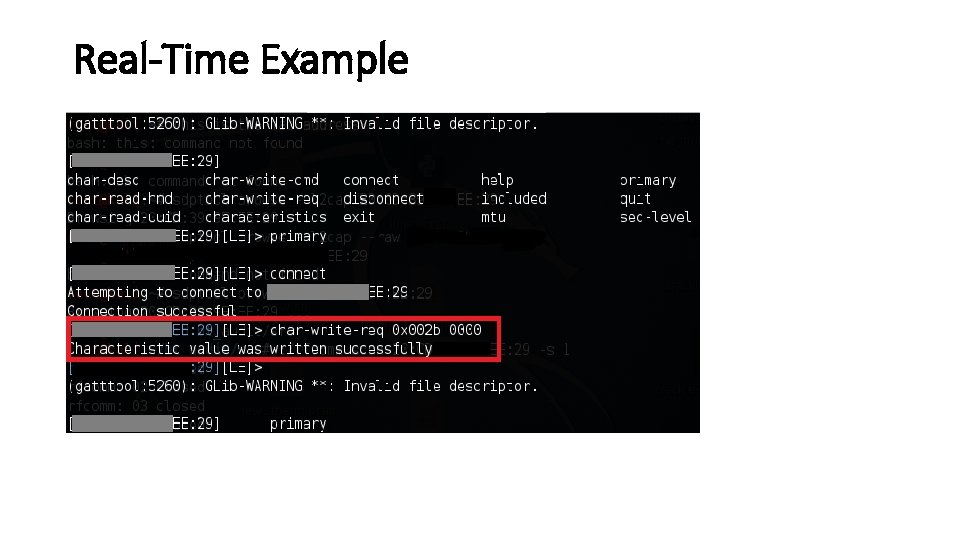
Real-Time Example
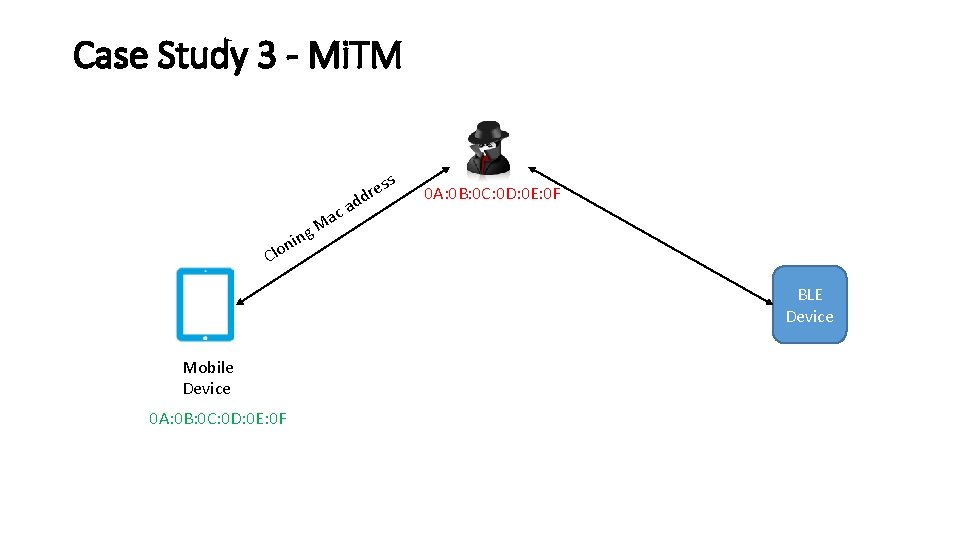
Case Study 3 - Mi. TM s ac M g res d ad 0 A: 0 B: 0 C: 0 D: 0 E: 0 F in n lo C BLE Device Mobile Device 0 A: 0 B: 0 C: 0 D: 0 E: 0 F
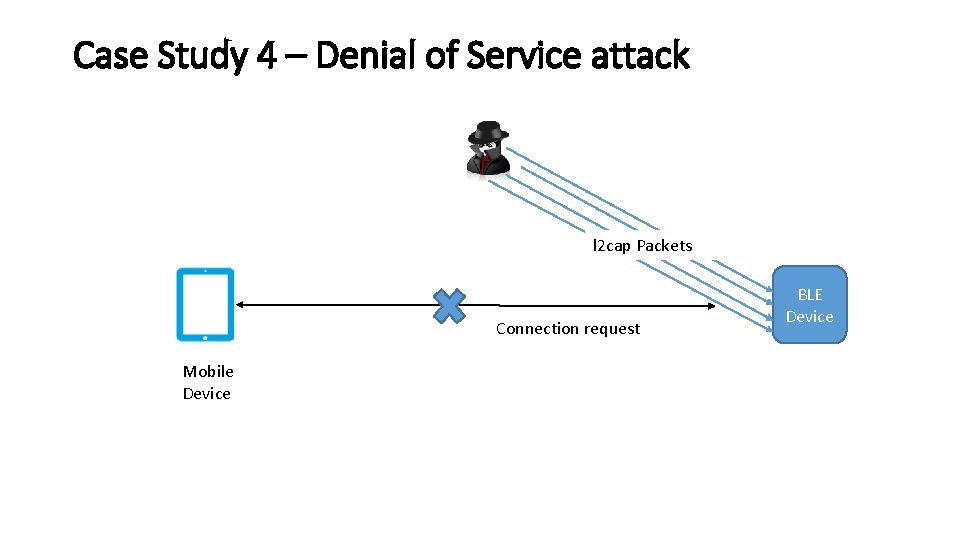
Case Study 4 – Denial of Service attack l 2 cap Packets Connection request Mobile Device BLE Device
Thank you Michael Mcneil Maheshan Pardhiv Reddy Sagar Popat Swaroop Yermalkar Chandrakant Nial Ben Kokx Neelesh swami Sanjog Panda Jiggyasu Sharma Kartik Lalan Audience Minatee Mishra Anirudh Duggal Archita Narendra Makkena Abhishikt
QUESTIONS
- Slides: 19