Attacker Overview Incident Response Defense Meets Offense To

- Slides: 16

Attacker Overview Incident Response
Defense Meets Offense • To find an attacker, you must think like an attacker • Know how they operate • Know their techniques • Know their tools • Know what they are looking for • Essentially, know what they look like If you know they have a capability for initial compromise with an infected USB drive… Emails might not be the best place to start looking for evidence of compromise Incident Response What steps do they take? 2
Threats, vulnerabilities, and risk • Threat Attack source or actor that may cause harm • Vulnerability Weakness in systems or processes Risk Likelihood and impact of attack based on threats and vulnerabilities • Threat x Vulnerability = Risk Incident Response • 3
• In order to prepare for an incident, we must know what is out there • Wide range of malicious Botnets Phishers Ransomware Insider Threats (elevation of privilege, data theft, unauthorized access, etc) Hackers "APT’s” Malware outbreak Etc. . . • Consider as many vectors as possible when preparing Incident Response Threat 4
• Software bugs • Broken processes • Ineffective controls • Hardware flaws • Legacy systems • Human error Incident Response Vulnerabilities 5
• Business disruptions • Financial losses • Privacy loss • Reputation loss • Impaired growth • Loss of life • Others? Incident Response Risk 6
Attacker Methodology • “Cyber Kill Chain” (CKC) • It seems like everyone is coming up with these kill chains • Many have different components to them • But they all have a theme… • Let’s look at a few Incident Response Describes how an adversary works, the steps they take 7
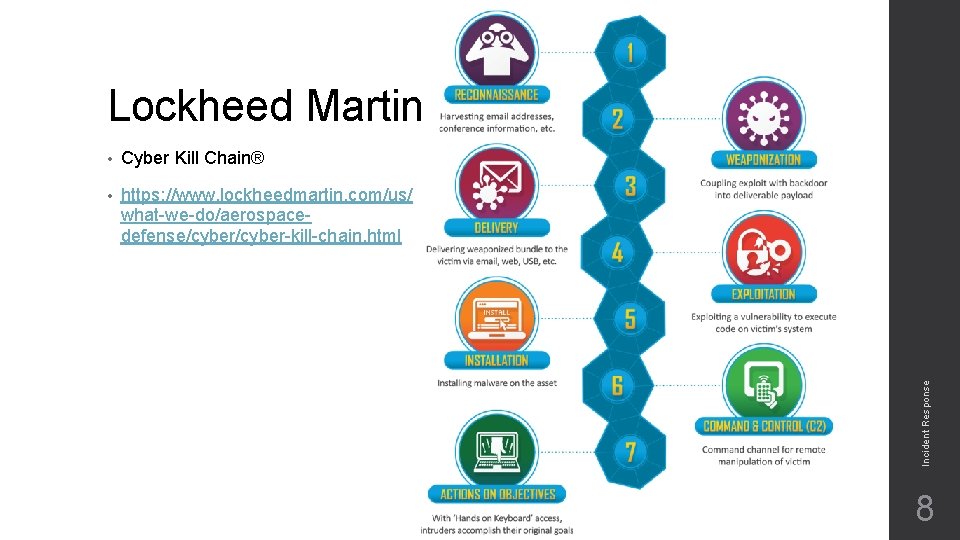
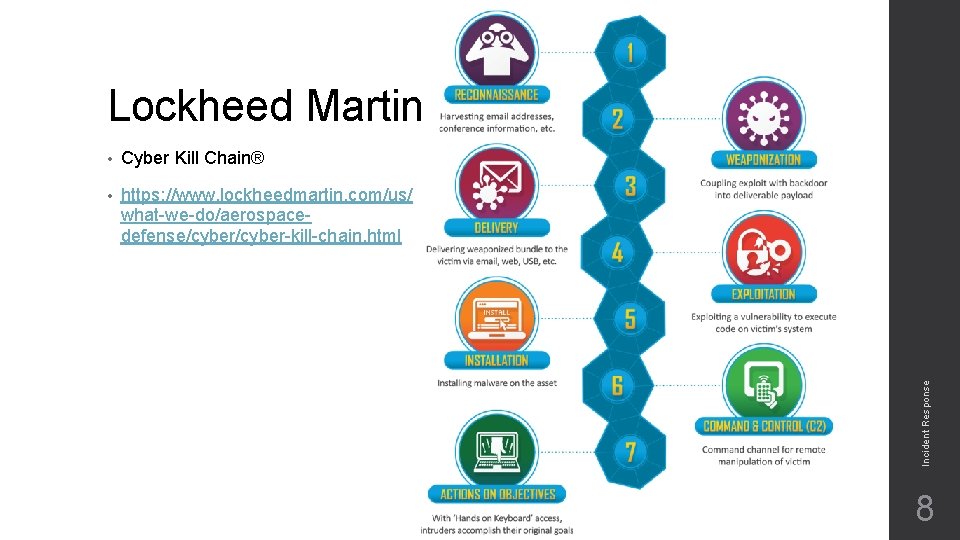
• Cyber Kill Chain® • https: //www. lockheedmartin. com/us/ what-we-do/aerospacedefense/cyber-kill-chain. html Incident Response Lockheed Martin 8
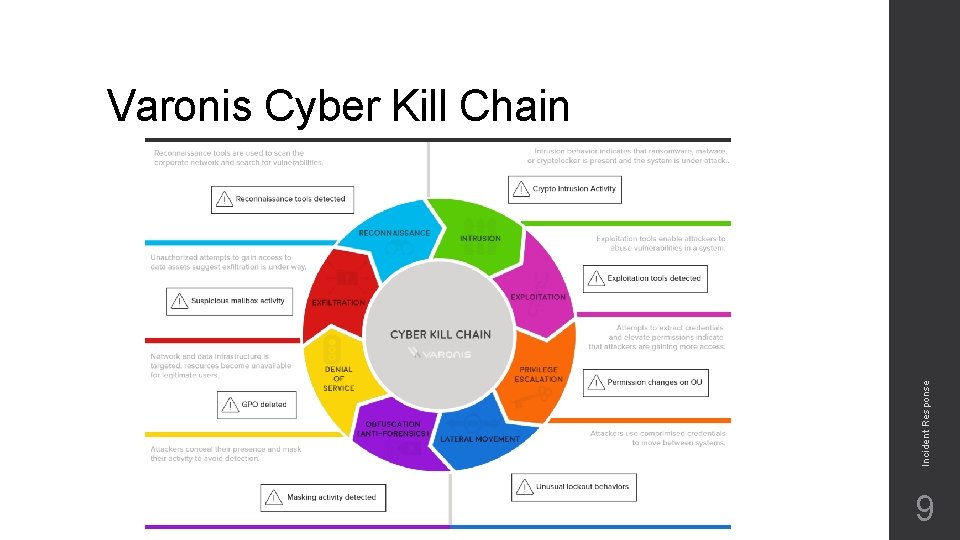
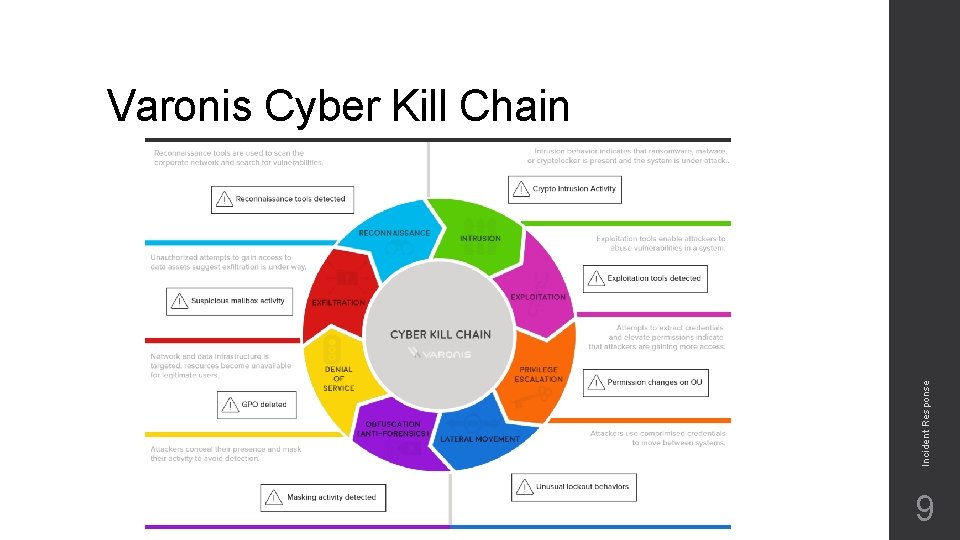
Incident Response Varonis Cyber Kill Chain 9
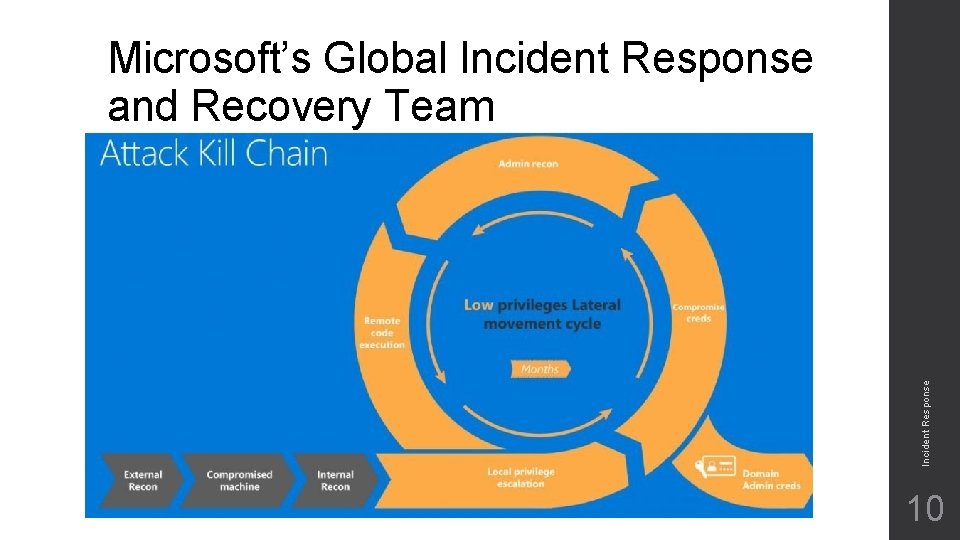
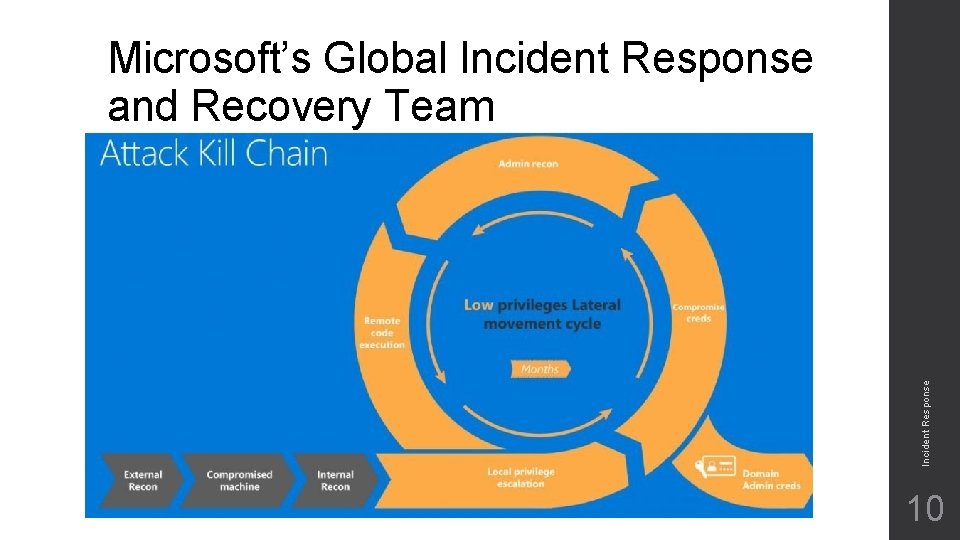
Incident Response Microsoft’s Global Incident Response and Recovery Team 10
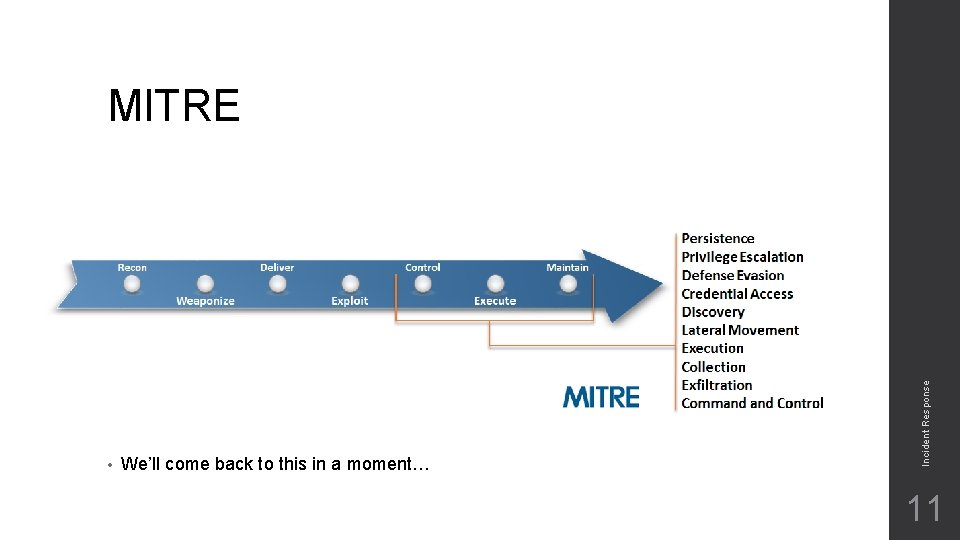
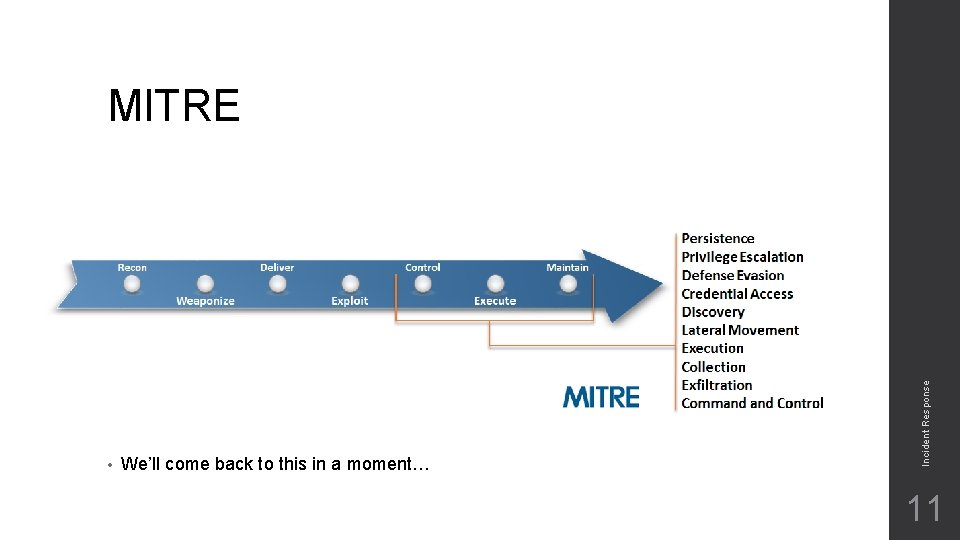
• We’ll come back to this in a moment… Incident Response MITRE 11
Information Gathering • Adversary is gathering information about your network • Passive Recon Never touching the customer Customer should have no idea you’re gathering info on them • Active Recon • Enumeration Scans! Incident Response Touching the customer/equipment Customer could (should) know you’re gathering info on them. 12
• Adversary is mapping vulnerabilities to exploits • This is really done on their side • Nothing that you’re going to see in your systems • …Except maybe determining vulnerable systems Incident Response Threat Modeling/Vulnerability Analysis 13
Exploitation • Exploits traversing the network or hitting the border • Sometimes easy to see them IDS’s may catch them Signatures Anomalies • Newer exploits or custom exploits may not get caught No signatures for them Some exploits just take advantage of poor configuration Probably looks like mostly normal or legit traffic Incident Response • 14
Post-Exploitation • Three P’s Privilege Escalation Pivoting Persistence • Command Control (C 2) • Things can become difficult here • Who’s connecting to who? Is it anomalous? There’s so much of this data on modern networks… Incident Response Covert Channels Encryption 15
• Adversarial Tactics, Techniques, and Common Knowledge • Model for adversarial behaviors • https: //attack. mitre. org/wiki/Main_Page • Categories include… Initial Access Execution Persistence Privilege Escalation Defense Evasion Credential Access Discovery Lateral Movement Collection Exfiltration Command Control Incident Response MITRE ATT&CK 16