Asymmetric Cryptography part 1 2 Haya Shulman Many
- Slides: 41
Asymmetric Cryptography part 1 & 2 Haya Shulman Many thanks to Amir Herzberg who donated some of the slides from http: //www. cs. biu. ac. il/~herzbea/89 -690/index. html
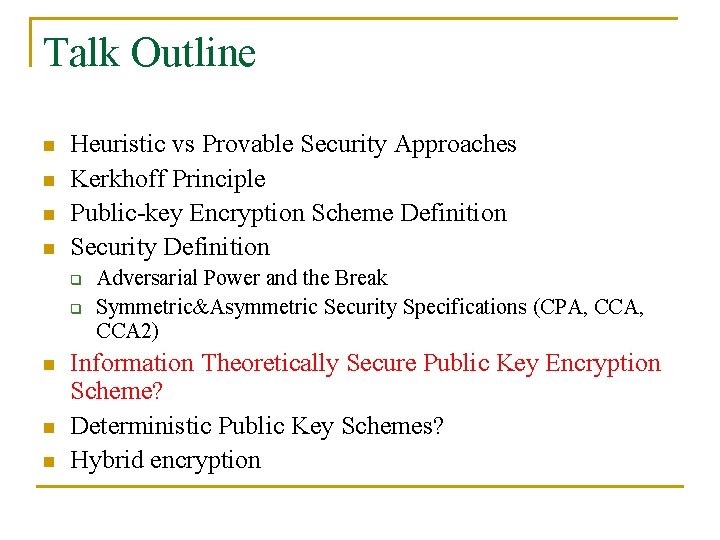
Talk Outline n n Heuristic vs Provable Security Approaches Kerkhoff Principle Public-key Encryption Scheme Definition Security Definition q q n n n Adversarial Power and the Break Symmetric&Asymmetric Security Specifications (CPA, CCA 2) Information Theoretically Secure Public Key Encryption Scheme? Deterministic Public Key Schemes? Hybrid encryption
Heuristic vs Provable Security Approaches n The heuristic approach n n n The provable security q q n Build-break-fix paradigm Failed cryptanalysis Reductions to hardness assumptions Reduction is a basic cryptographic technique The information theoretic security
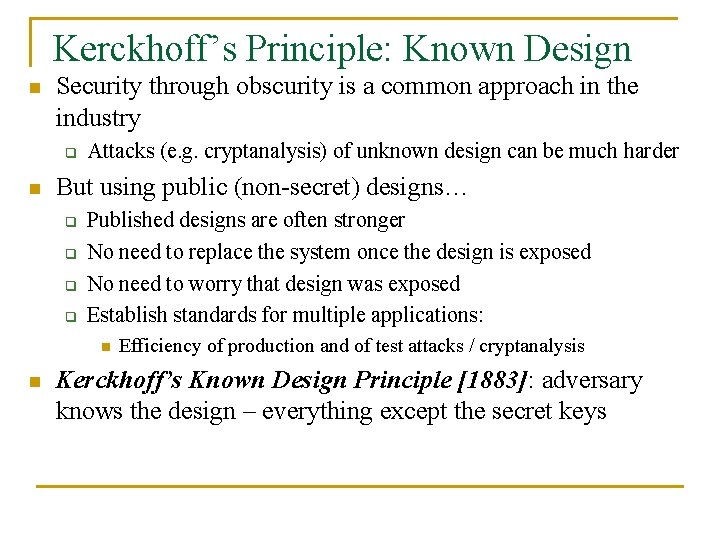
Kerckhoff’s Principle: Known Design n Security through obscurity is a common approach in the industry q n Attacks (e. g. cryptanalysis) of unknown design can be much harder But using public (non-secret) designs… q q Published designs are often stronger No need to replace the system once the design is exposed No need to worry that design was exposed Establish standards for multiple applications: n n Efficiency of production and of test attacks / cryptanalysis Kerckhoff’s Known Design Principle [1883]: adversary knows the design – everything except the secret keys
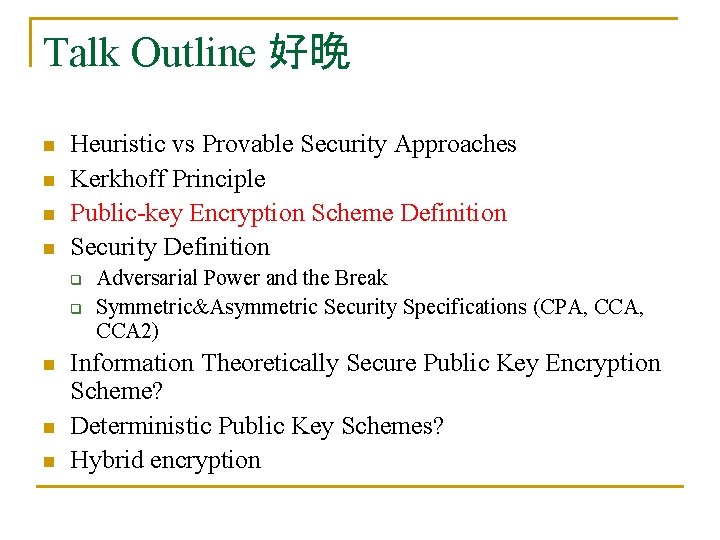
Talk Outline 好晚 n n Heuristic vs Provable Security Approaches Kerkhoff Principle Public-key Encryption Scheme Definition Security Definition q q n n n Adversarial Power and the Break Symmetric&Asymmetric Security Specifications (CPA, CCA 2) Information Theoretically Secure Public Key Encryption Scheme? Deterministic Public Key Schemes? Hybrid encryption
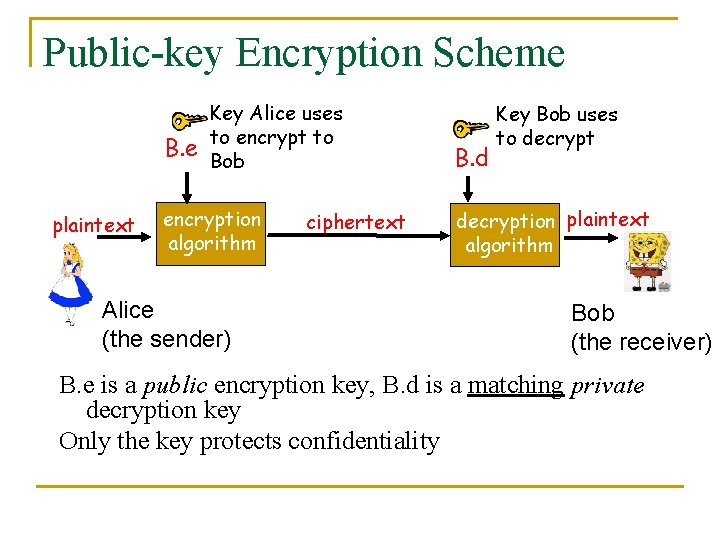
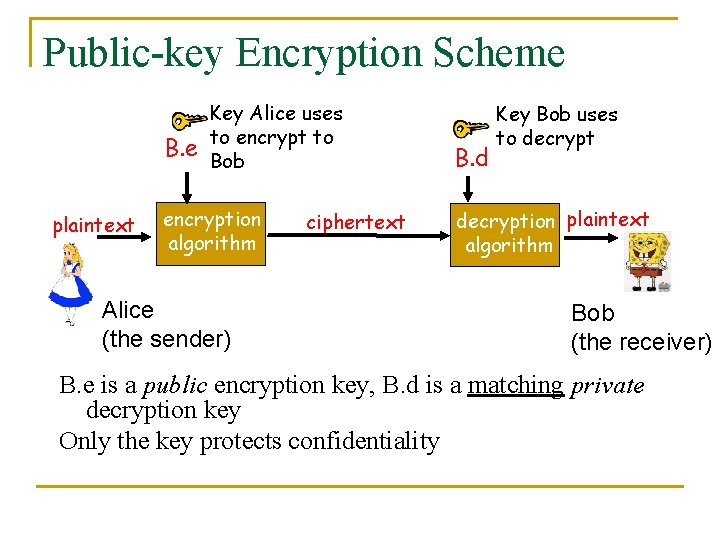
Public-key Encryption Scheme B. e plaintext Key Alice uses to encrypt to Bob encryption algorithm Alice (the sender) ciphertext B. d Key Bob uses to decryption plaintext algorithm Bob (the receiver) B. e is a public encryption key, B. d is a matching private decryption key Only the key protects confidentiality
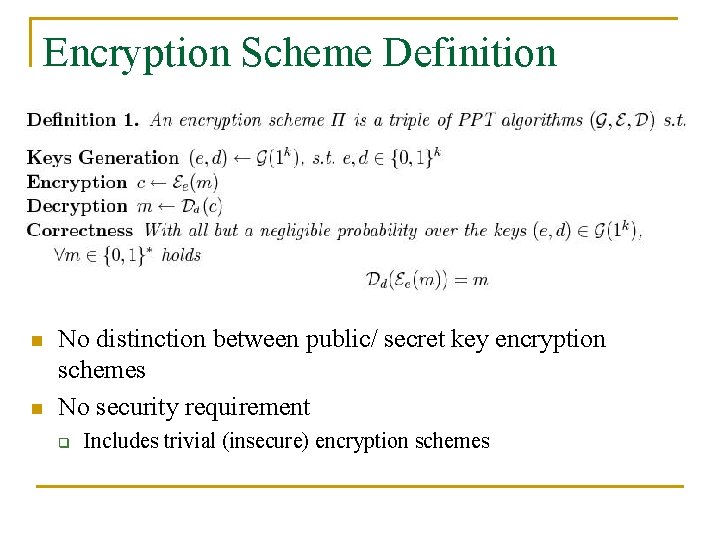
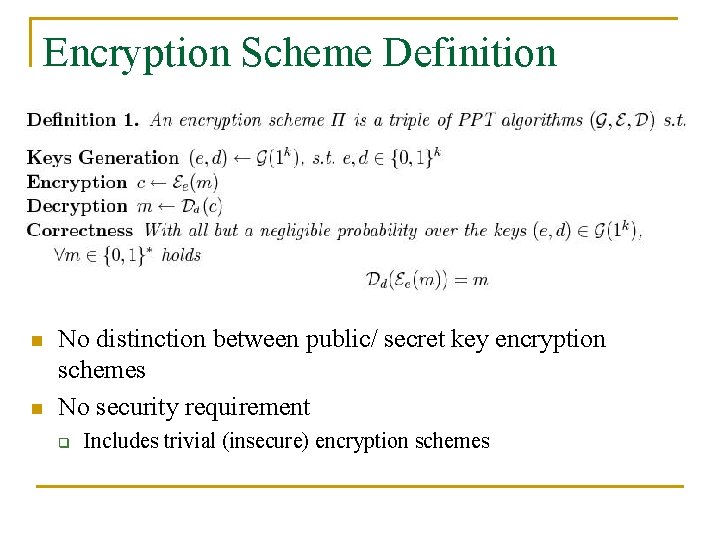
Encryption Scheme Definition n n No distinction between public/ secret key encryption schemes No security requirement q Includes trivial (insecure) encryption schemes
Talk Outline n n Heuristic vs Provable Security Approaches Kerkhoff Principle Public-key Encryption Scheme Definition Security Definition q q n n n Adversarial Power and the Break Symmetric&Asymmetric Security Specifications (CPA, CCA 2) Information Theoretically Secure Public Key Encryption Scheme? Deterministic Public Key Schemes? Hybrid encryption
Defining Adversarial Power n Computational power q q n Computational bounds on its running time Uniform/ non-uniform What actions can it take? q q Passive, eavesdropping Active, can obtain encryptions/ decryptions
Defining the Break n Define the successful break of the scheme q q q n Recovering the secret key Decrypting the challenge Learning some partial information about the encrypted message! Simulating reality using experiments q Indistinguishability (CPA, CCA, adaptive-CCA)
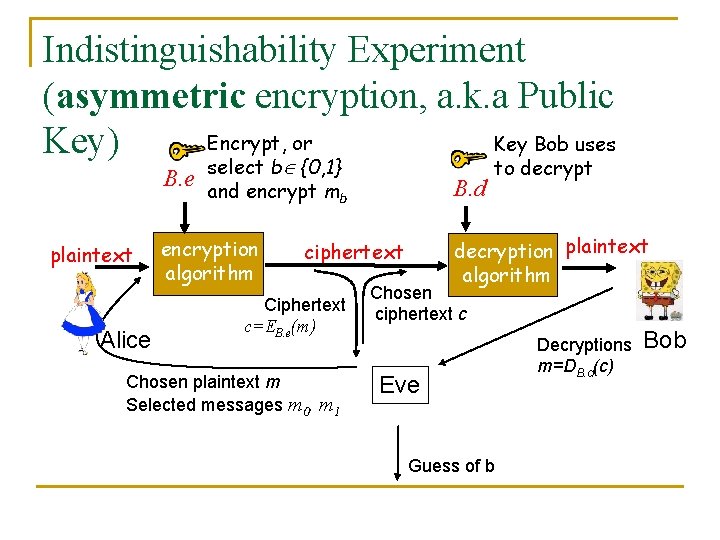
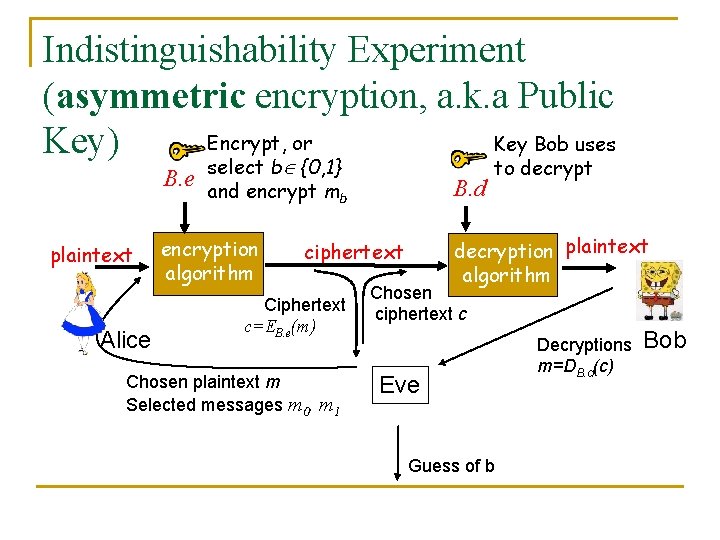
Indistinguishability Experiment (asymmetric encryption, a. k. a Public Encrypt, or Key Bob uses Key) B. e select b {0, 1} B. d and encrypt mb plaintext Alice encryption algorithm decryption plaintext algorithm ciphertext Ciphertext c=EB. e(m) Chosen plaintext m Selected messages m 0, m 1 to decrypt Chosen ciphertext c Eve Guess of b Decryptions m=DB. d(c) Bob
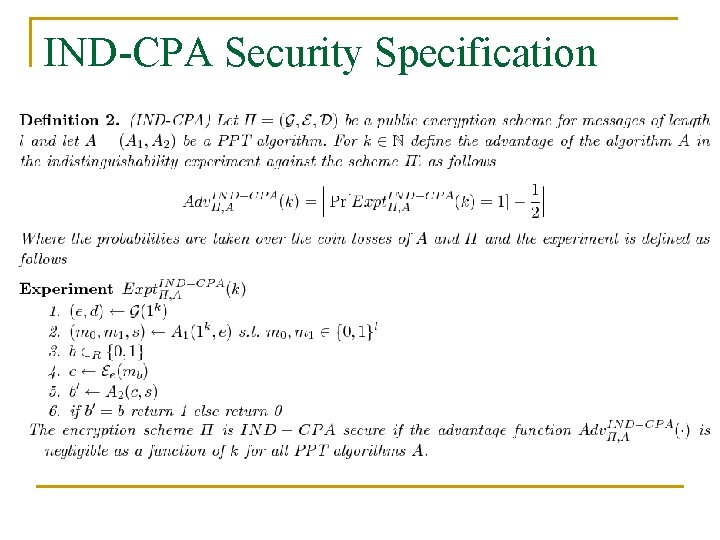
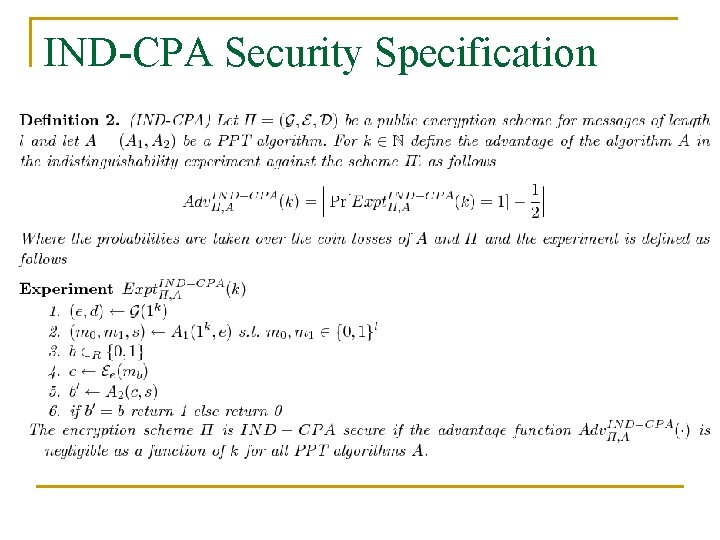
IND-CPA Security Specification
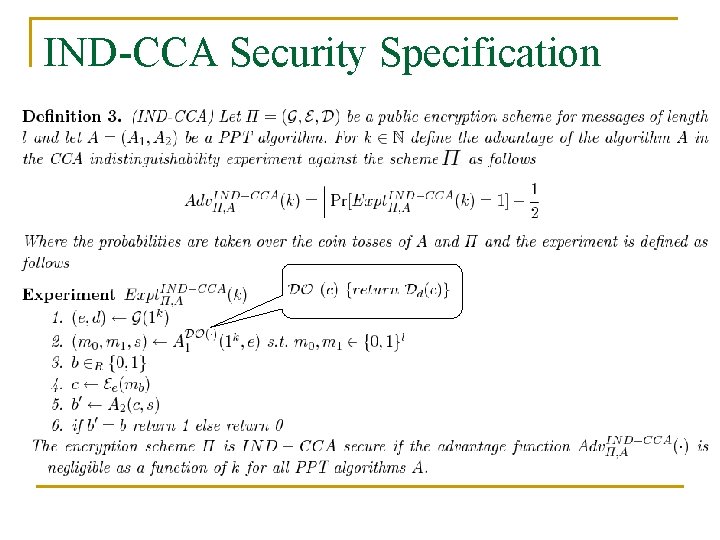
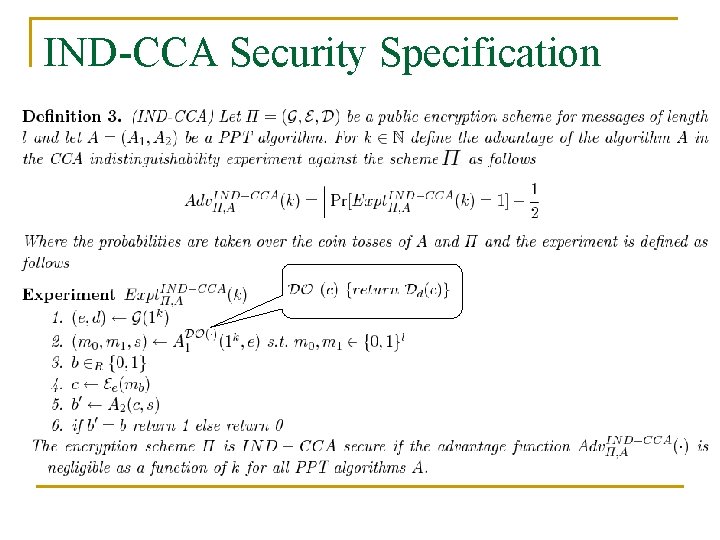
IND-CCA Security Specification
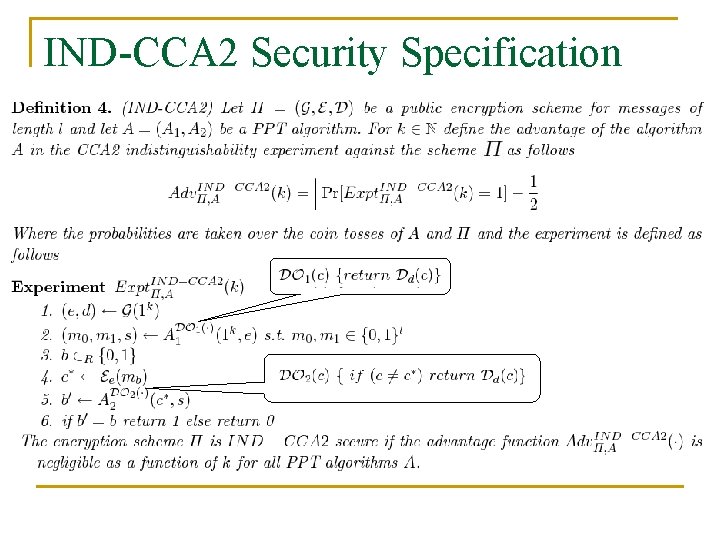
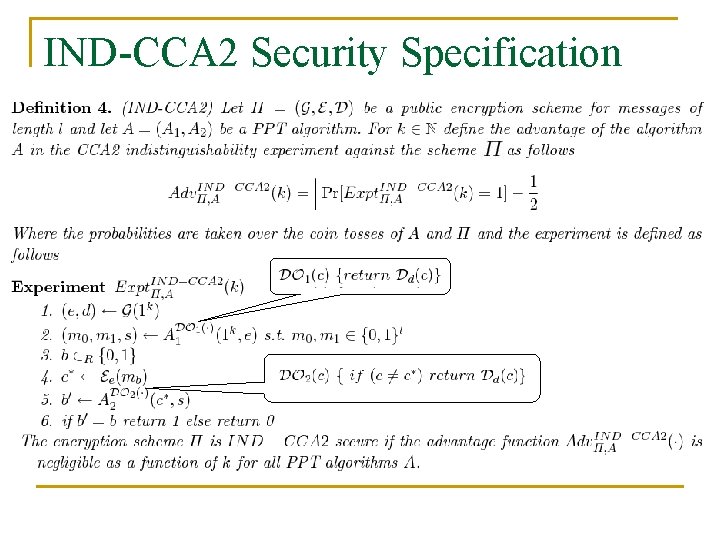
IND-CCA 2 Security Specification
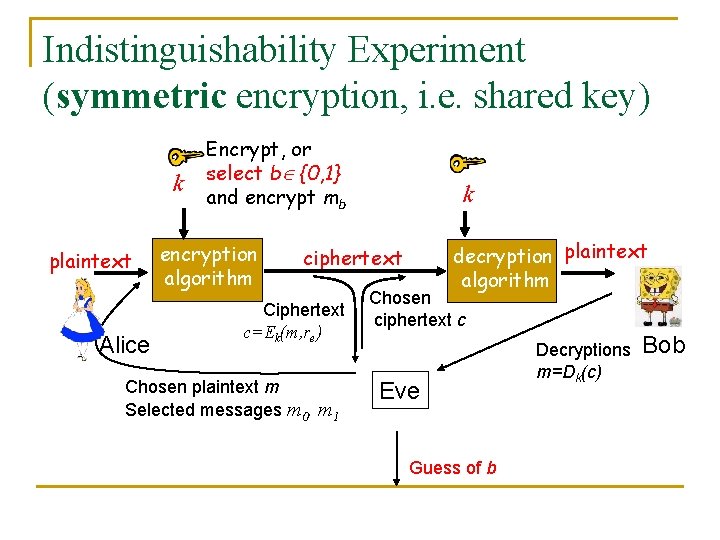
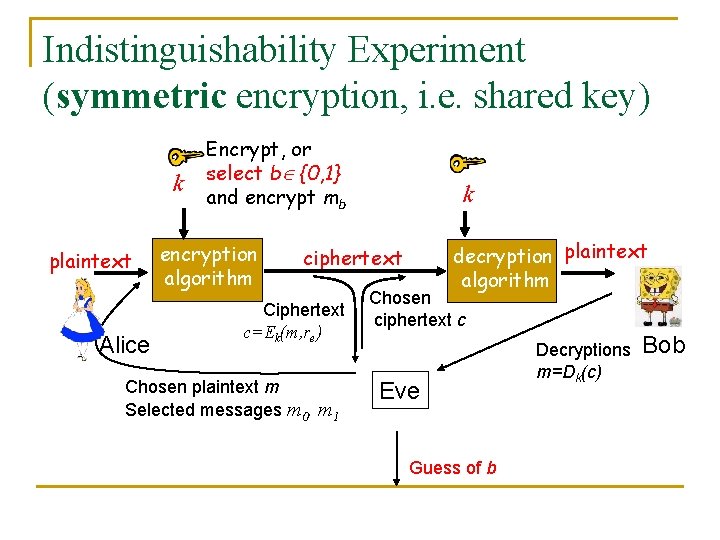
Indistinguishability Experiment (symmetric encryption, i. e. shared key) k plaintext Alice Encrypt, or select b {0, 1} and encrypt mb encryption algorithm k decryption plaintext algorithm ciphertext Ciphertext c=Ek(m, re) Chosen plaintext m Selected messages m 0, m 1 Chosen ciphertext c Eve Guess of b Decryptions m=Dk(c) Bob
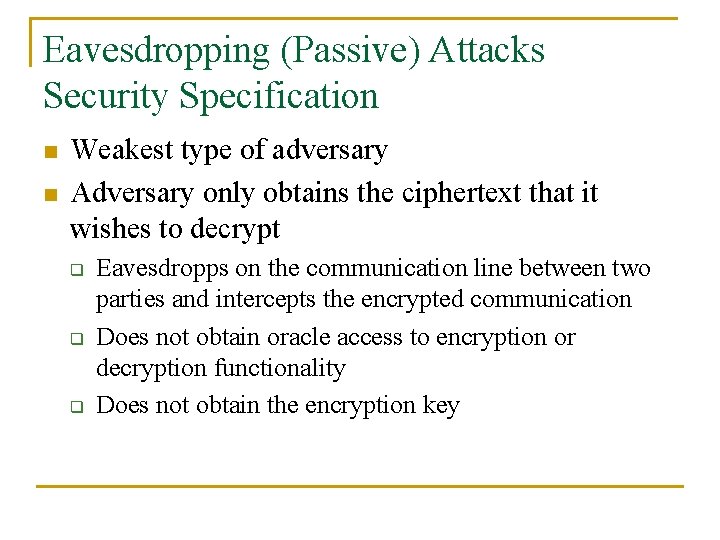
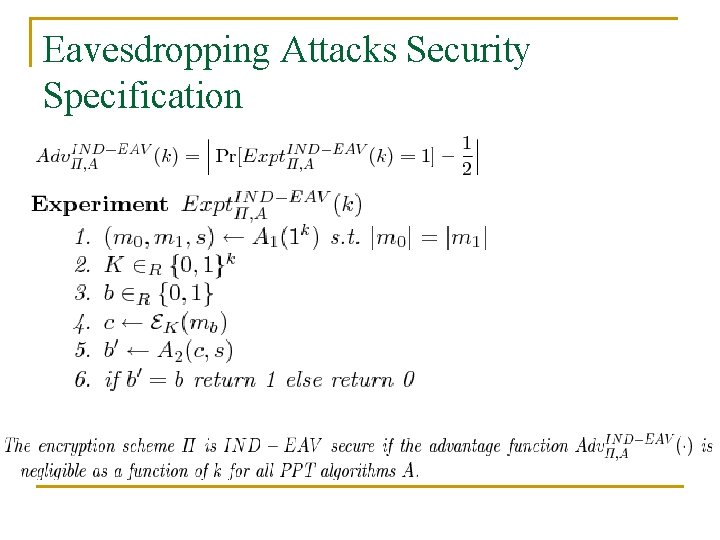
Eavesdropping (Passive) Attacks Security Specification n n Weakest type of adversary Adversary only obtains the ciphertext that it wishes to decrypt q q q Eavesdropps on the communication line between two parties and intercepts the encrypted communication Does not obtain oracle access to encryption or decryption functionality Does not obtain the encryption key
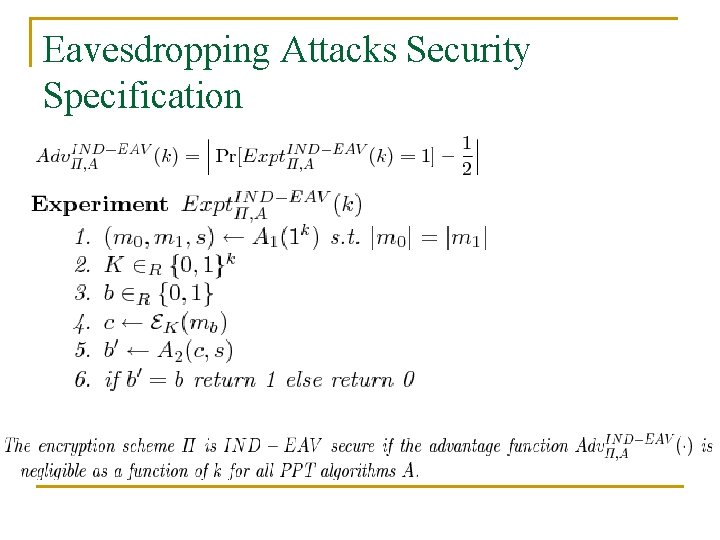
Eavesdropping Attacks Security Specification
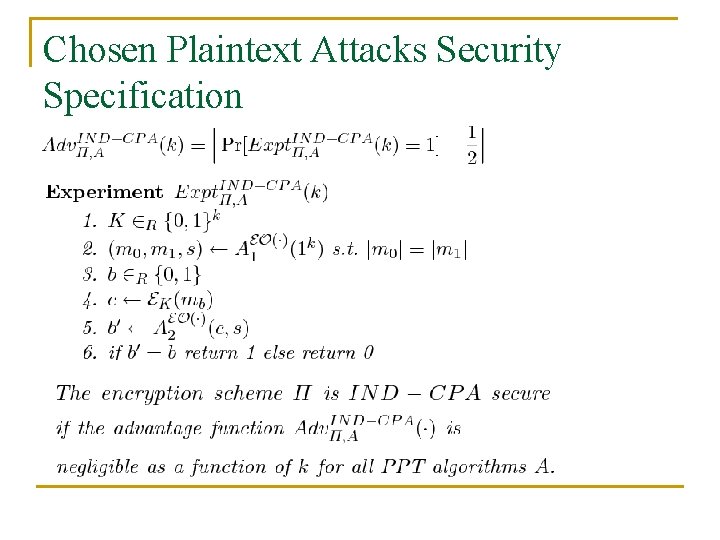
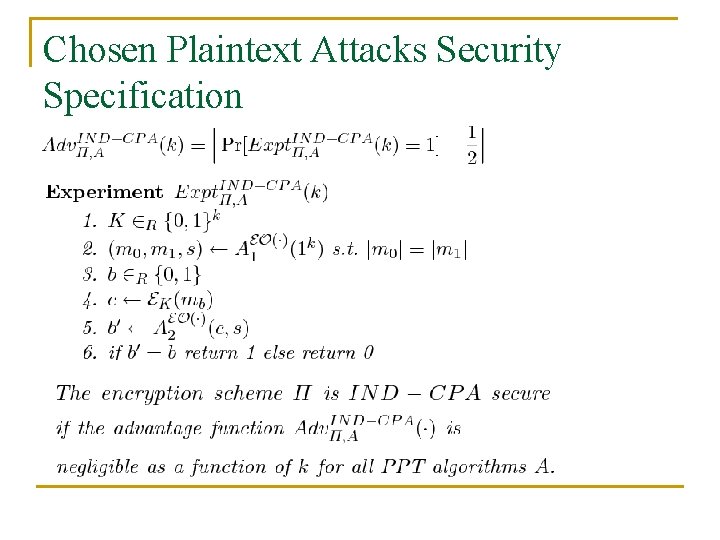
Chosen Plaintext Attacks Security Specification
Talk Outline n n Heuristic vs Provable Security Approaches Kerkhoff Principle Public-key Encryption Scheme Definition Security Definition q q n n n Adversarial Power and the Break Symmetric&Asymmetric Security Specifications (CPA, CCA 2) Information Theoretically Secure Public Key Encryption Scheme? Deterministic Public Key Schemes? Hybrid encryption
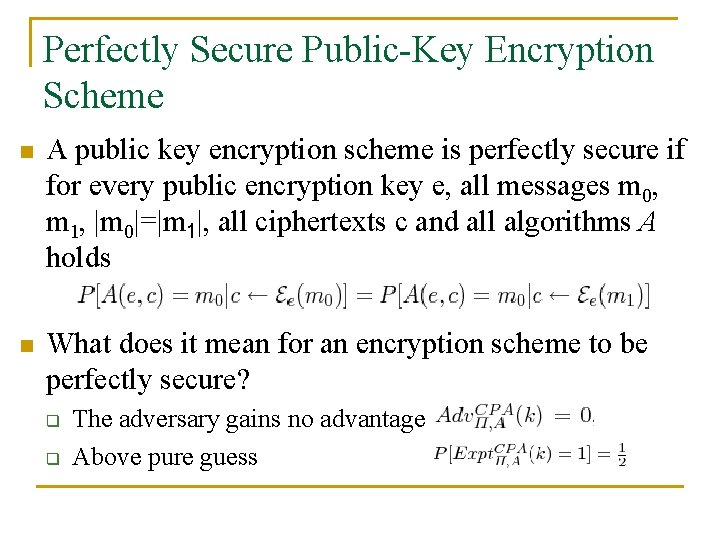
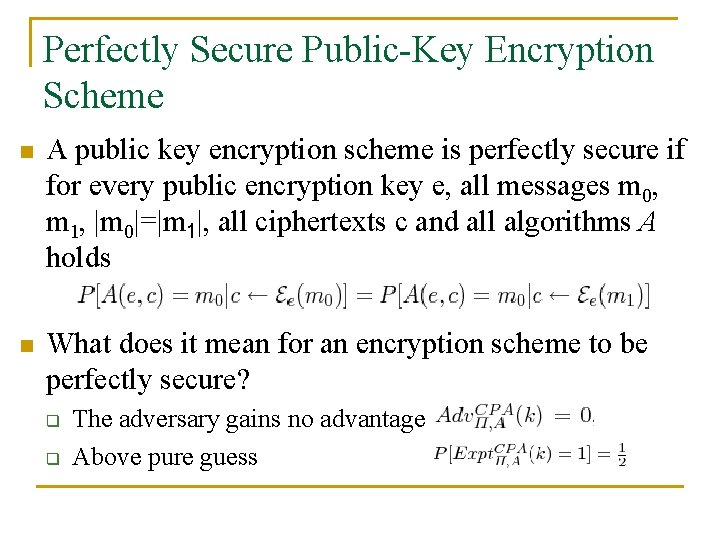
Perfectly Secure Public-Key Encryption Scheme n A public key encryption scheme is perfectly secure if for every public encryption key e, all messages m 0, m 1, |m 0|=|m 1|, all ciphertexts c and all algorithms A holds n What does it mean for an encryption scheme to be perfectly secure? q q The adversary gains no advantage Above pure guess
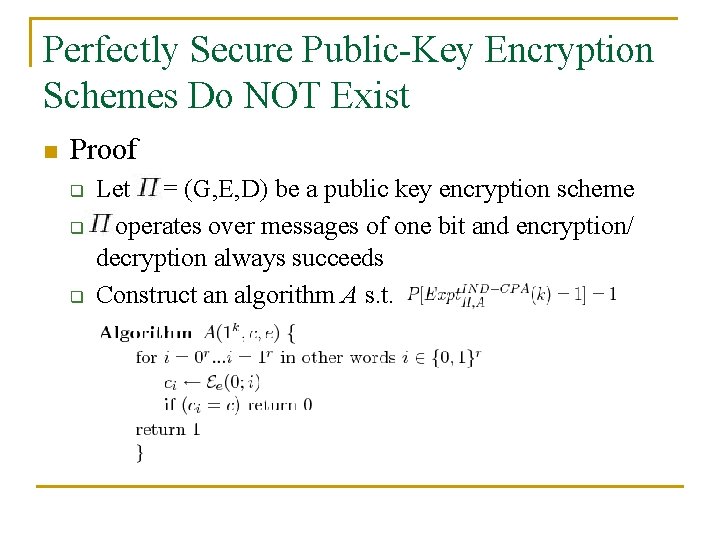
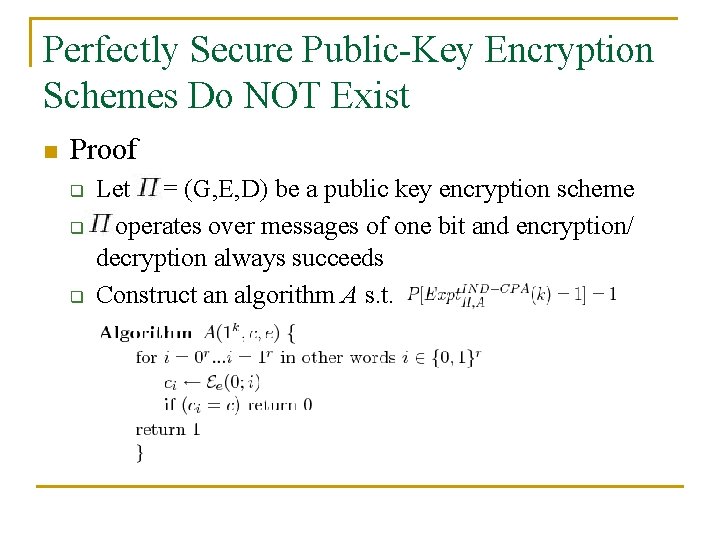
Perfectly Secure Public-Key Encryption Schemes Do NOT Exist n Proof q q q Let = (G, E, D) be a public key encryption scheme operates over messages of one bit and encryption/ decryption always succeeds Construct an algorithm A s. t.
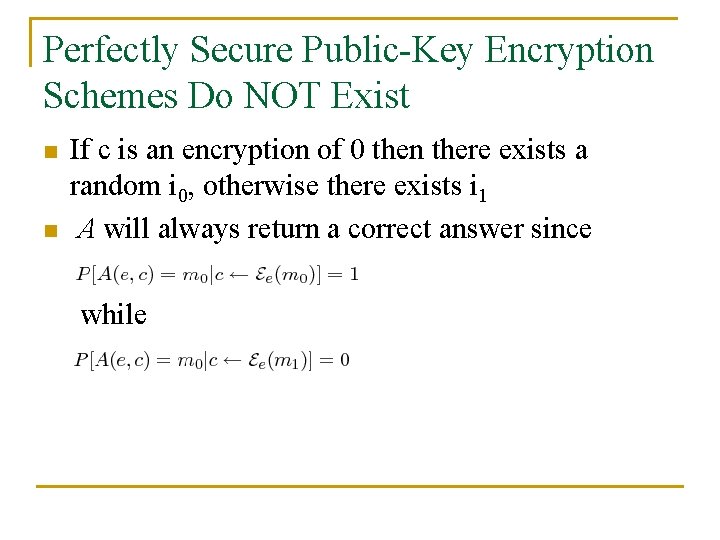
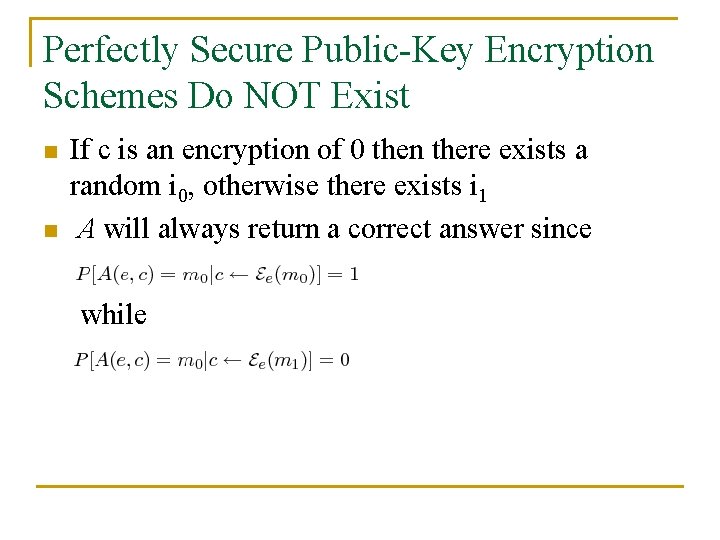
Perfectly Secure Public-Key Encryption Schemes Do NOT Exist n n If c is an encryption of 0 then there exists a random i 0, otherwise there exists i 1 A will always return a correct answer since while
Talk Outline n n Heuristic vs Provable Security Approaches Kerkhoff Principle Public-key Encryption Scheme Definition Security Definition q q n n n Adversarial Power and the Break Symmetric&Asymmetric Specifications (CPA, CCA 2) Information Theoretically Secure Public Key Encryption Scheme? Deterministic Public Key Schemes? Hybrid encryption
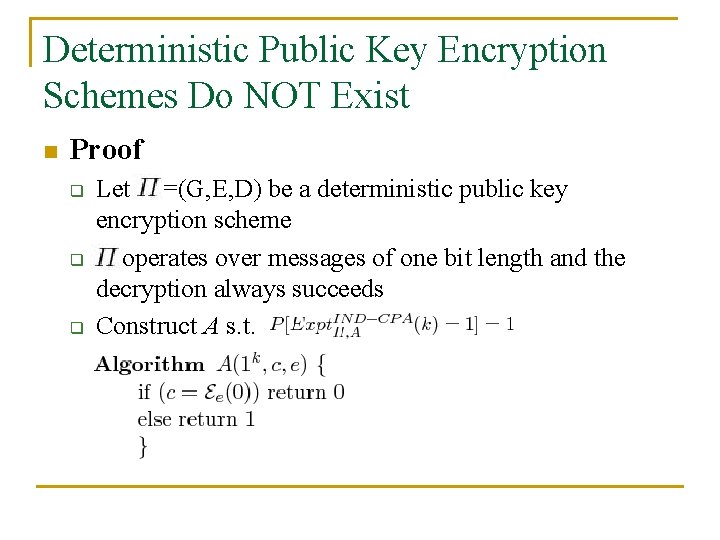
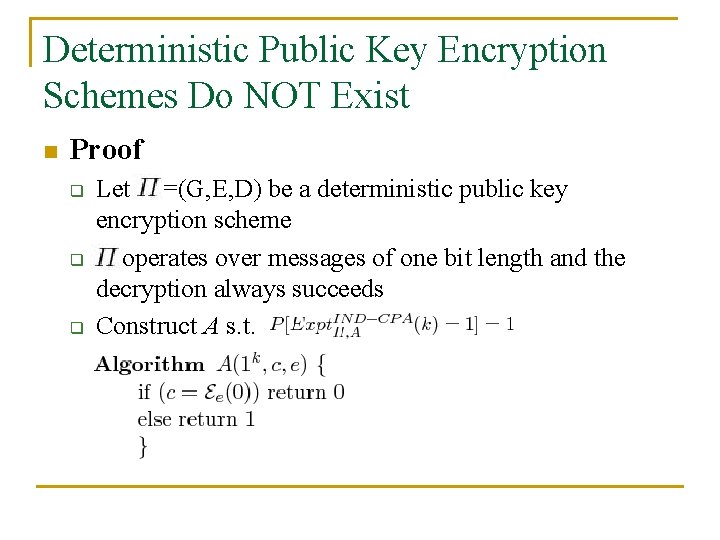
Deterministic Public Key Encryption Schemes Do NOT Exist n Proof q q q Let =(G, E, D) be a deterministic public key encryption scheme operates over messages of one bit length and the decryption always succeeds Construct A s. t.
Talk Outline n n Heuristic vs Provable Security Approaches Kerkhoff Principle Public-key Encryption Scheme Definition Security Definition q q n n n Adversarial Power and the Break Symmetric&Asymmetric Security Specifications (CPA, CCA 2) Information Theoretically Secure Public Key Encryption Scheme? Deterministic Public Key Schemes? Hybrid encryption
Symmetric vs. Asymmetric n n Is there a perfectly secure private key encryption scheme? Is there a secure deterministic private key encryption scheme? q n Depends on the attack model Why not define the strongest security for any scheme? q There is a price for being overly conservative
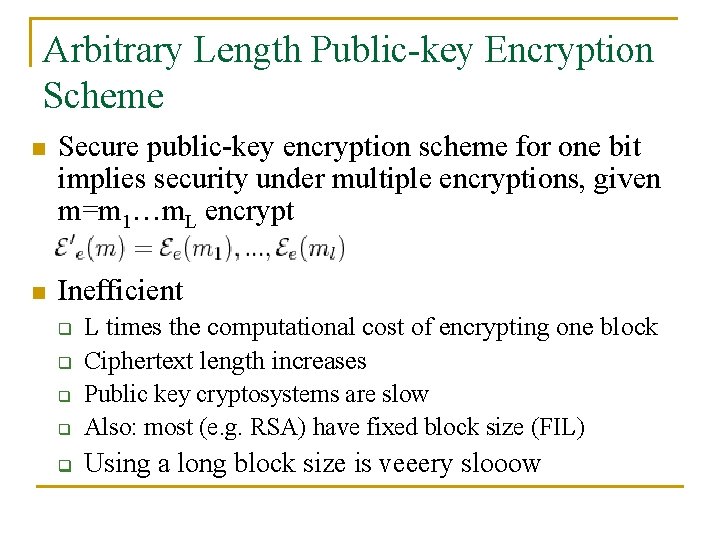
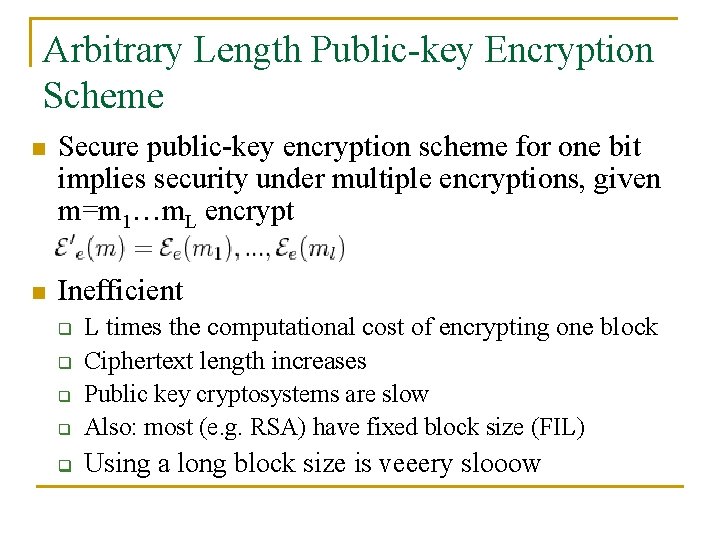
Arbitrary Length Public-key Encryption Scheme n Secure public-key encryption scheme for one bit implies security under multiple encryptions, given m=m 1…m. L encrypt n Inefficient q L times the computational cost of encrypting one block Ciphertext length increases Public key cryptosystems are slow Also: most (e. g. RSA) have fixed block size (FIL) q Using a long block size is veeery slooow q q q
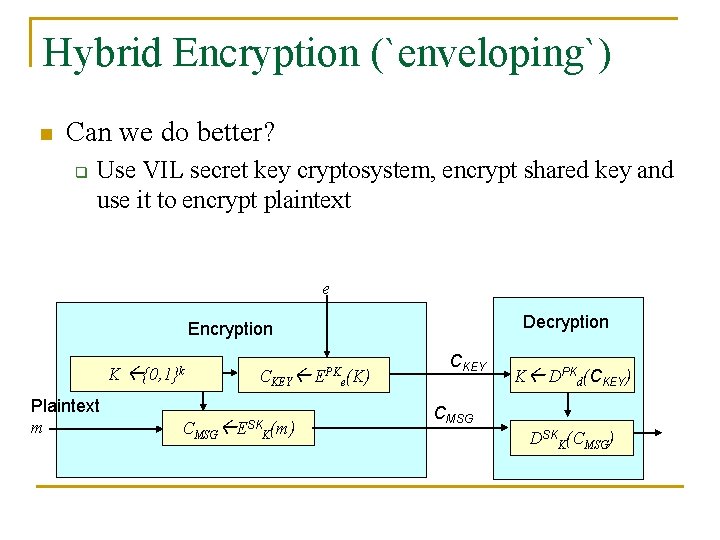
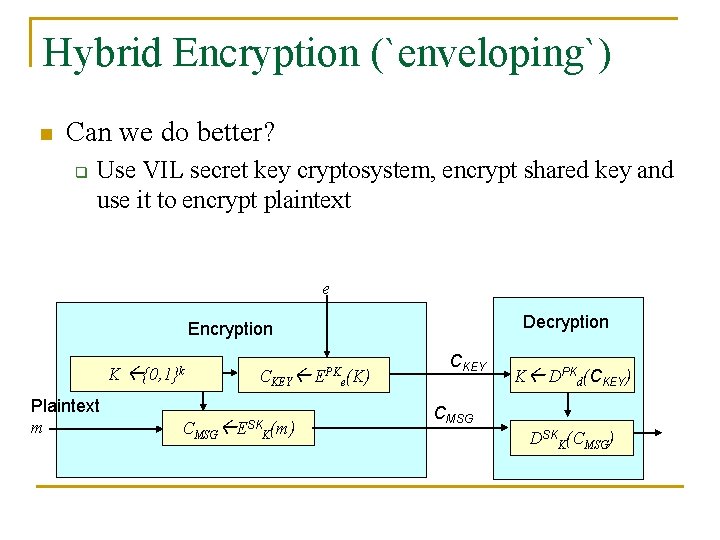
Hybrid Encryption (`enveloping`) n Can we do better? q Use VIL secret key cryptosystem, encrypt shared key and use it to encrypt plaintext e Decryption Encryption K Plaintext m {0, 1}k CMSG CKEY ESKK(m) EPKe(K) CKEY K DPKd(CKEY) CMSG DSKK(CMSG)
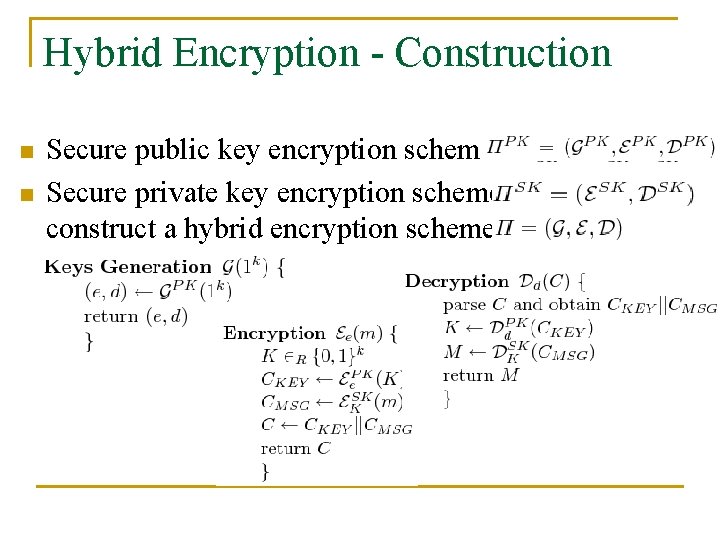
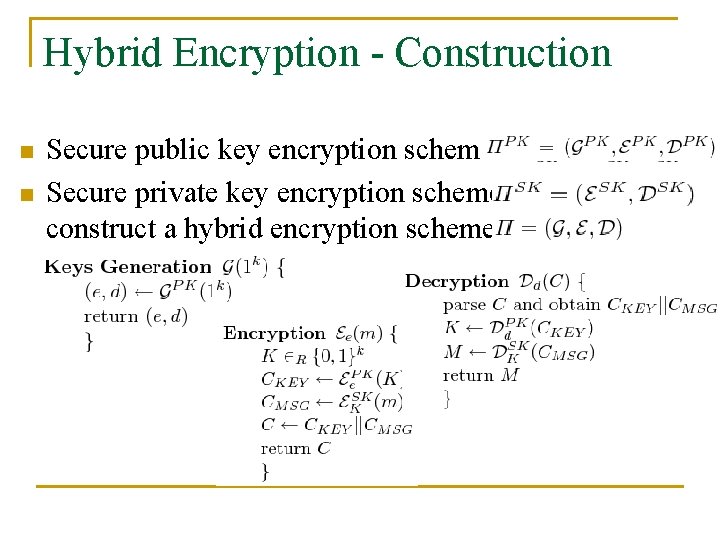
Hybrid Encryption - Construction n n Secure public key encryption scheme Secure private key encryption scheme construct a hybrid encryption scheme
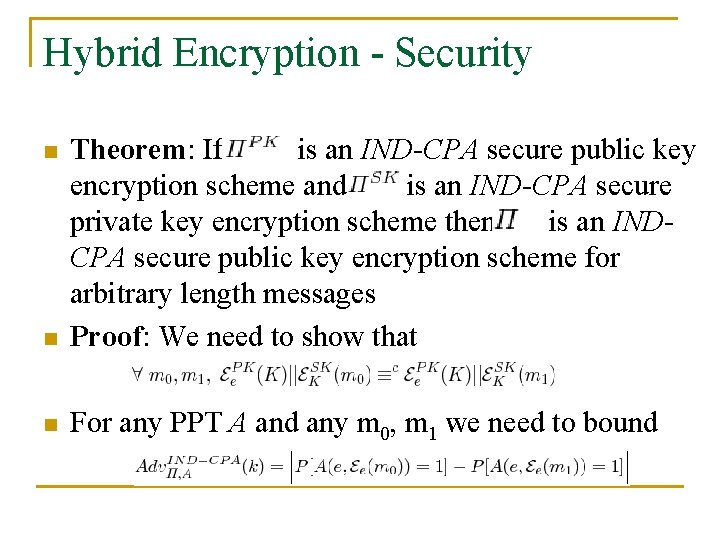
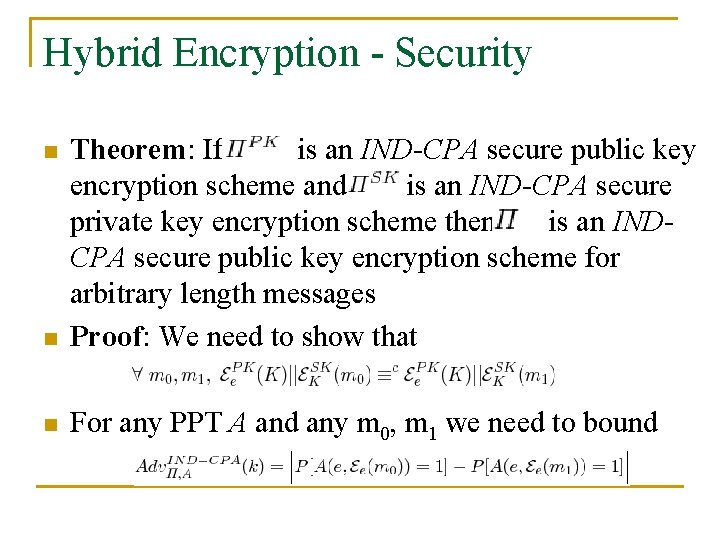
Hybrid Encryption - Security n Theorem: If is an IND-CPA secure public key encryption scheme and is an IND-CPA secure private key encryption scheme then is an INDCPA secure public key encryption scheme for arbitrary length messages Proof: We need to show that n For any PPT A and any m 0, m 1 we need to bound n
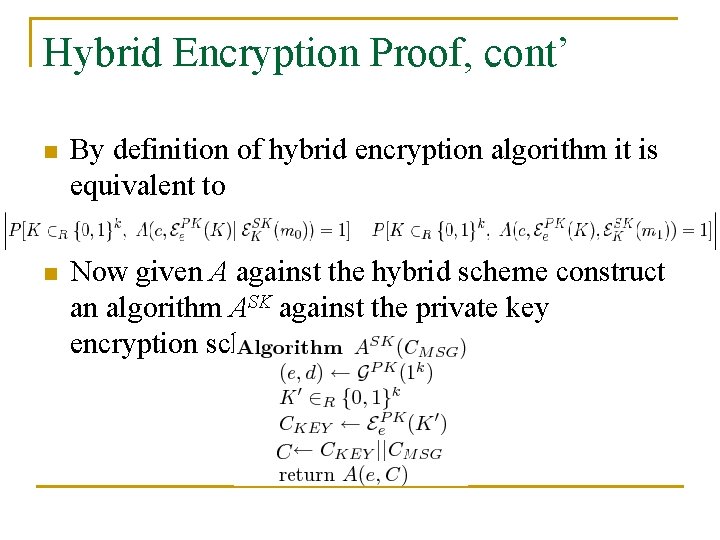
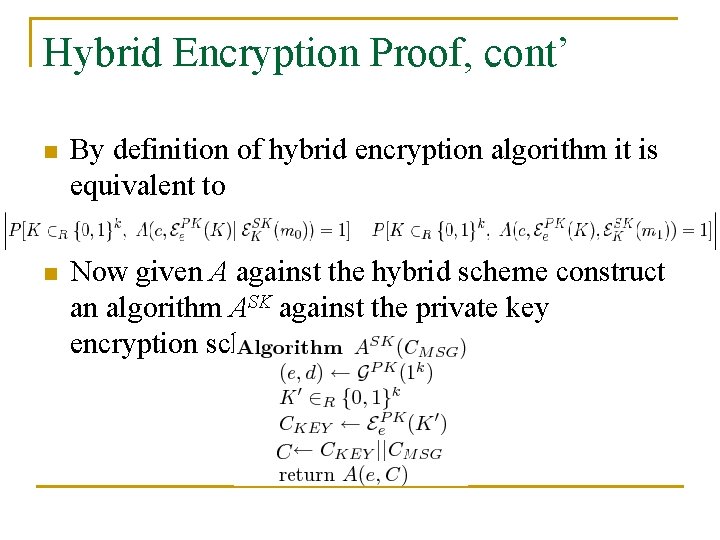
Hybrid Encryption Proof, cont’ n By definition of hybrid encryption algorithm it is equivalent to n Now given A against the hybrid scheme construct an algorithm ASK against the private key encryption scheme
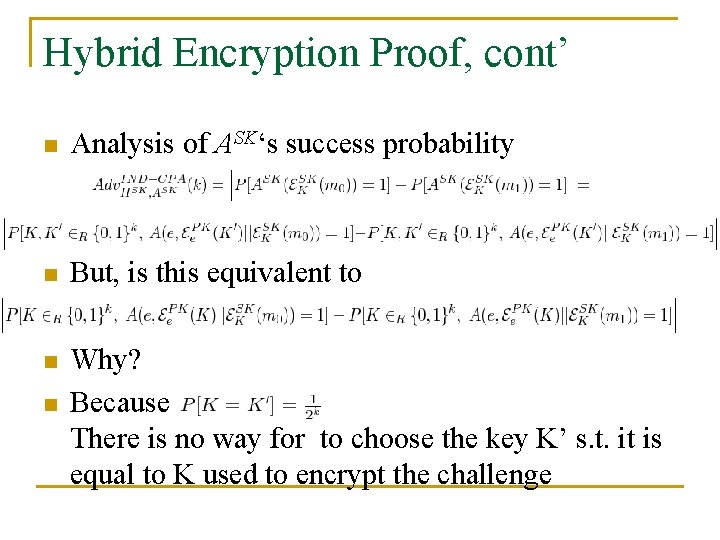
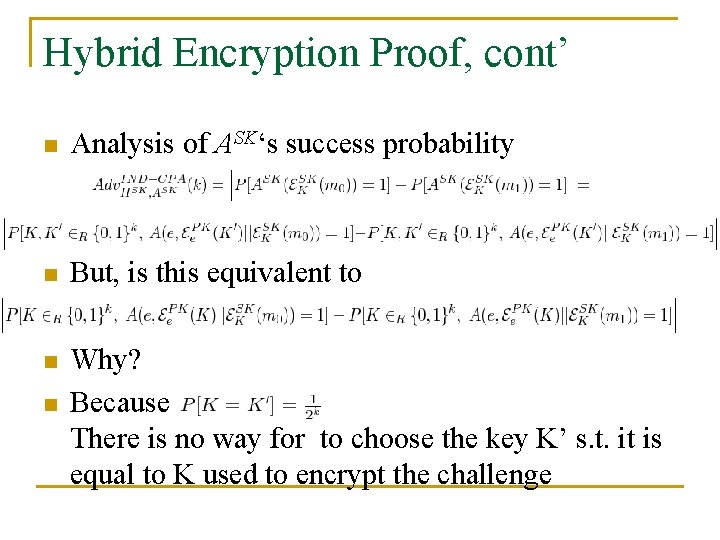
Hybrid Encryption Proof, cont’ n Analysis of ASK‘s success probability n But, is this equivalent to n Why? Because There is no way for to choose the key K’ s. t. it is equal to K used to encrypt the challenge n
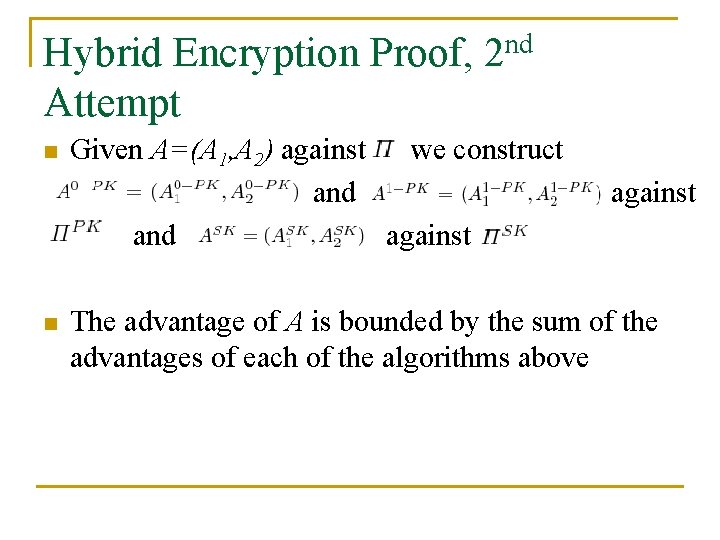
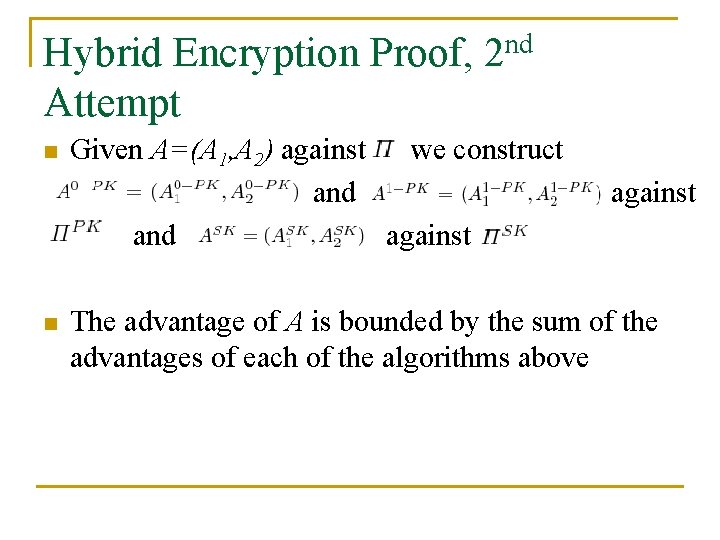
Hybrid Encryption Proof, 2 nd Attempt n n Given A=(A 1, A 2) against we construct and against The advantage of A is bounded by the sum of the advantages of each of the algorithms above
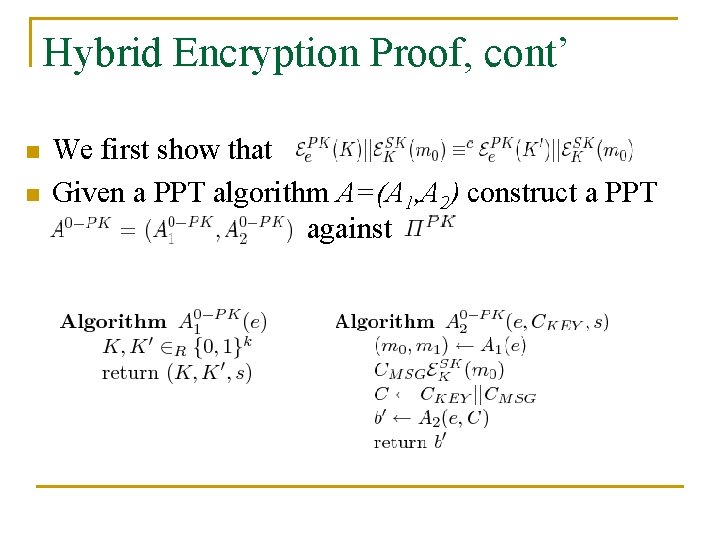
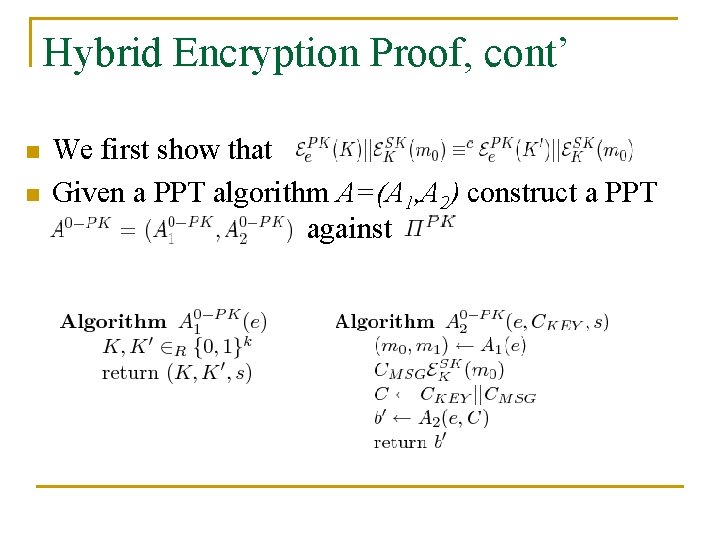
Hybrid Encryption Proof, cont’ n n We first show that Given a PPT algorithm A=(A 1, A 2) construct a PPT against
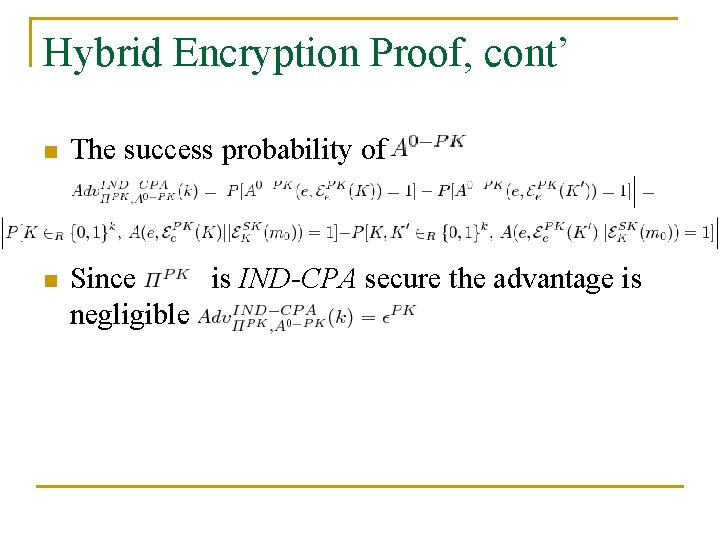
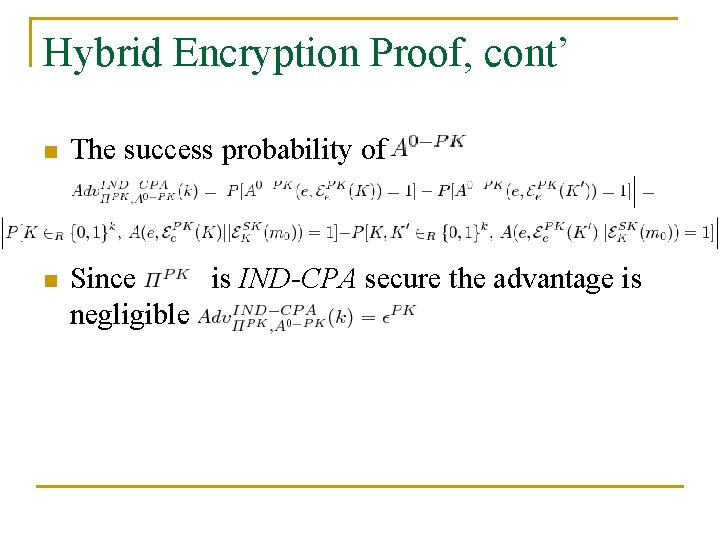
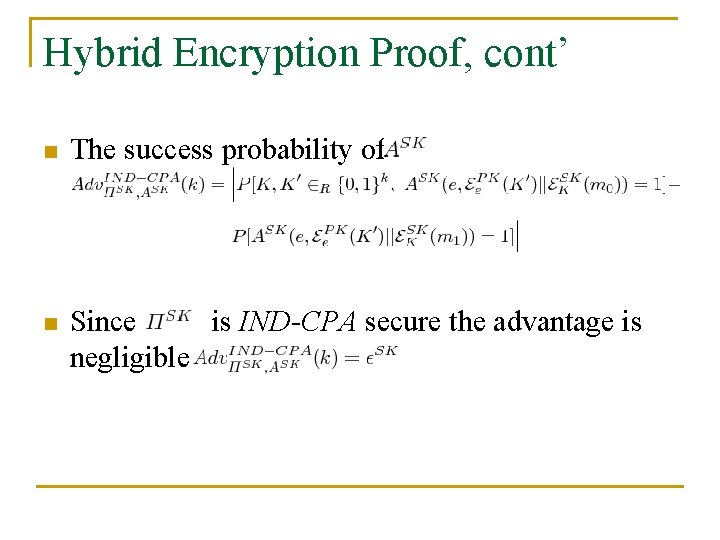
Hybrid Encryption Proof, cont’ n The success probability of n Since is IND-CPA secure the advantage is negligible
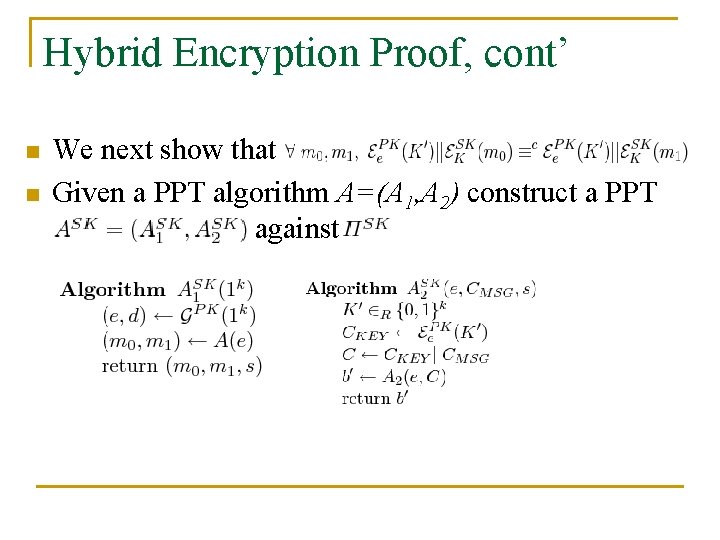
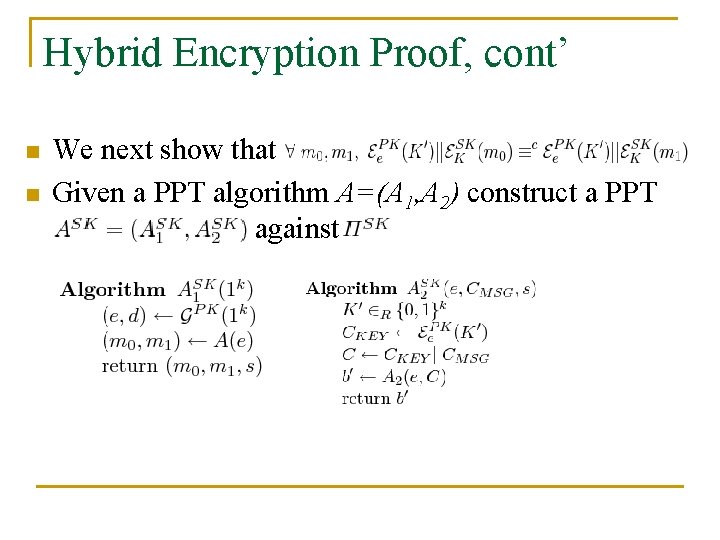
Hybrid Encryption Proof, cont’ n n We next show that Given a PPT algorithm A=(A 1, A 2) construct a PPT against
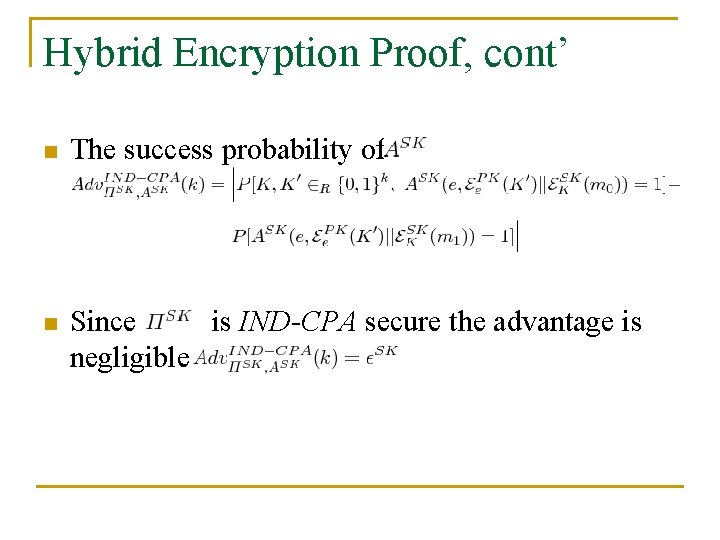
Hybrid Encryption Proof, cont’ n The success probability of n Since is IND-CPA secure the advantage is negligible
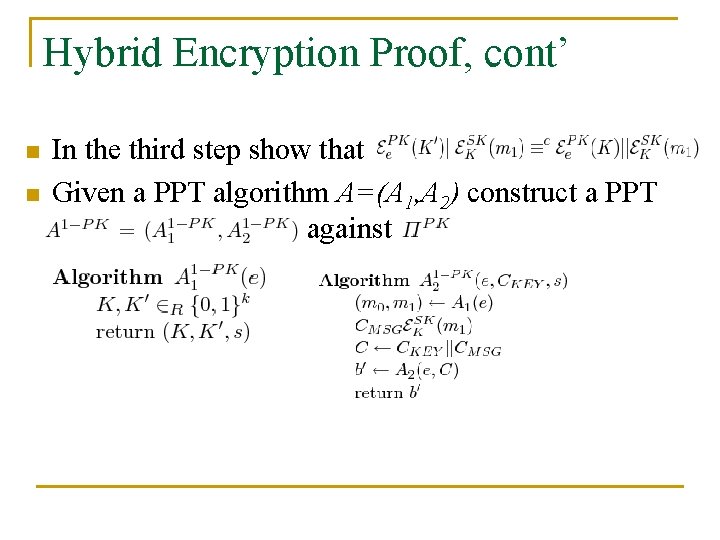
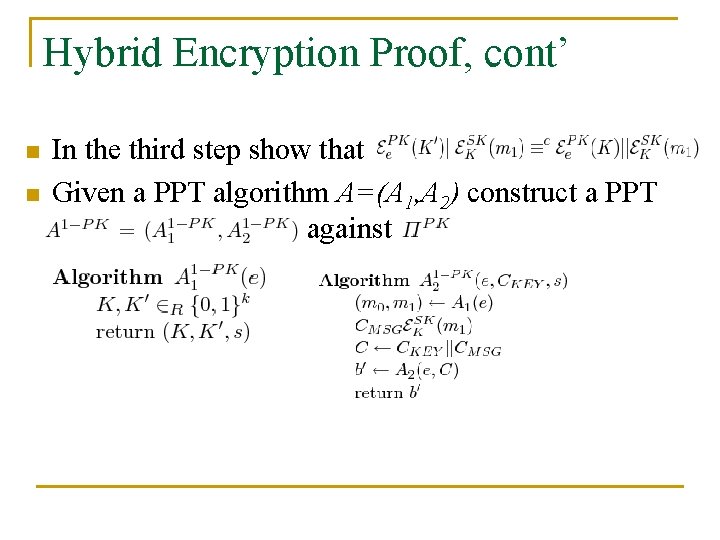
Hybrid Encryption Proof, cont’ n n In the third step show that Given a PPT algorithm A=(A 1, A 2) construct a PPT against
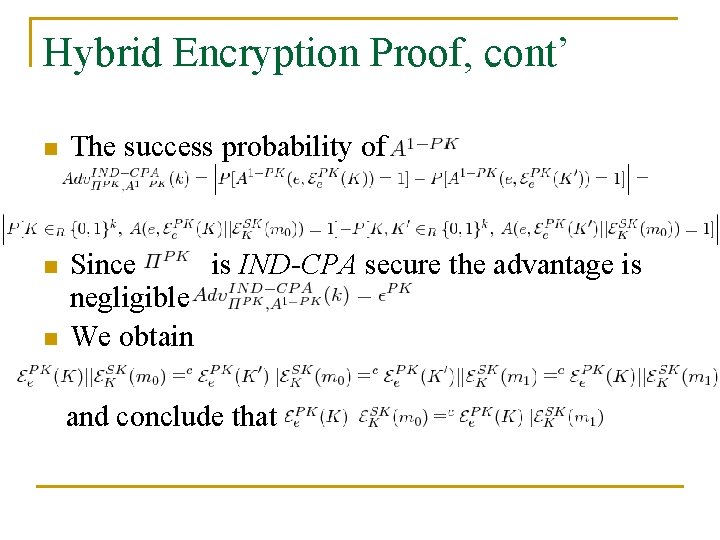
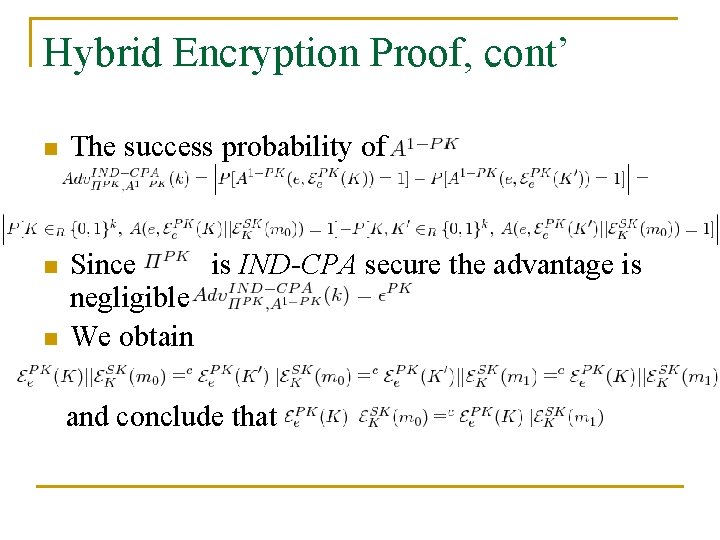
Hybrid Encryption Proof, cont’ n The success probability of n Since is IND-CPA secure the advantage is negligible We obtain n and conclude that
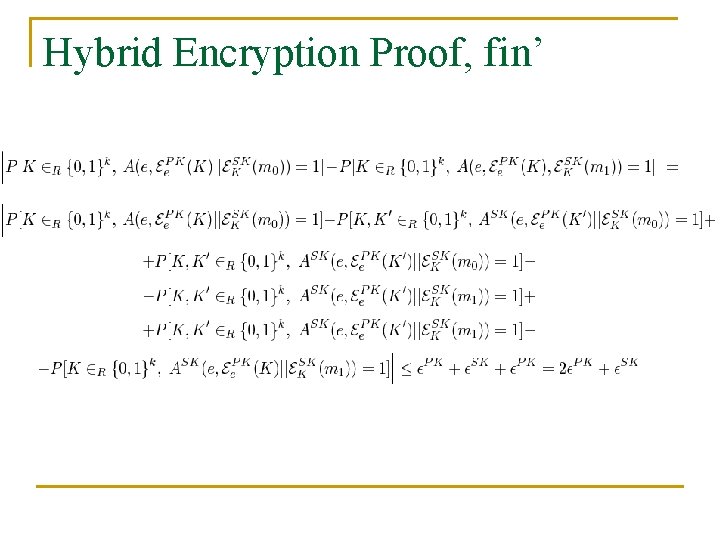
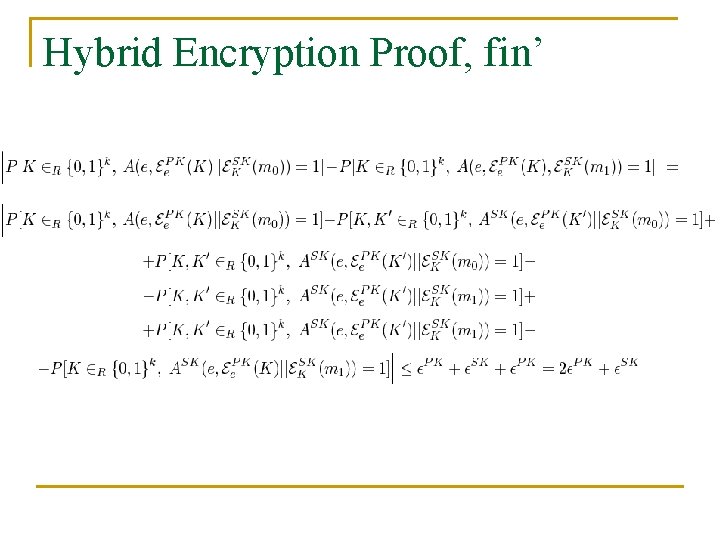
Hybrid Encryption Proof, fin’
Asymmetric Encryption n End of part 1 and 2 Questions? Thank you.