Assuring Identities in an Open Trust Framework The


- Slides: 21
Assuring Identities in an Open Trust Framework The Identity Assurance Framework Kantara Initiative 10 -22 -2009 Presentation to the Kantara Healthcare Identity Assurance Work Group
Identity in the Physical World
Today’s Collection of Identity Silos Joe’s Fish Market. Com Tropical, Fresh Water, Shell Fish, Lobster, Frogs, Whales, Seals, Clams
What the User wants… l Simplified online experience l Get rid of the need for multiple user-ids and passwords l Fewer clicks l Protected personal information l Reduce my risk from fraud l Better product & service offerings l Web 2. 0 and/or “smart phone” data service integration
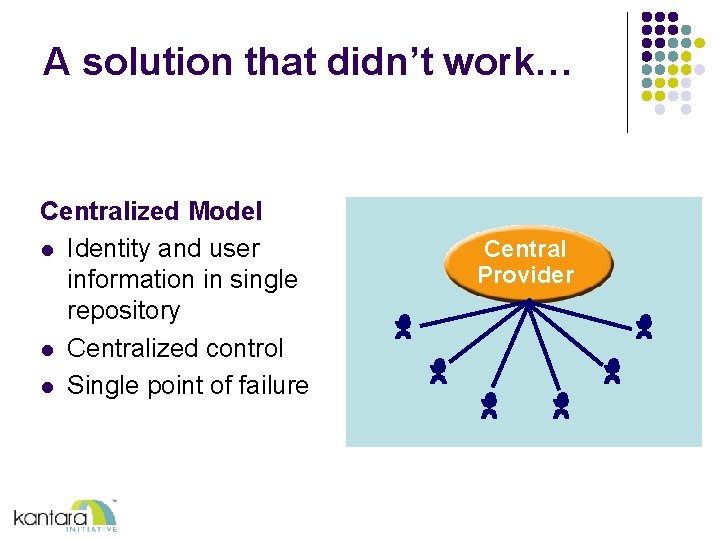
A solution that didn’t work… Centralized Model l Identity and user information in single repository l Centralized control l Single point of failure Central Provider
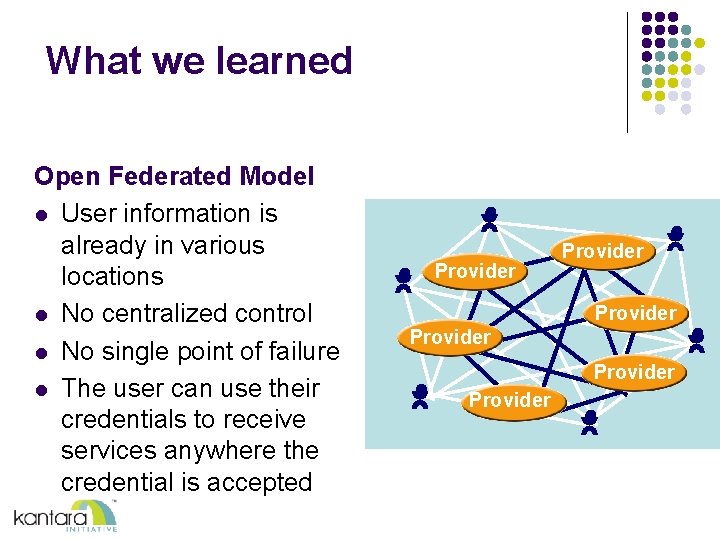
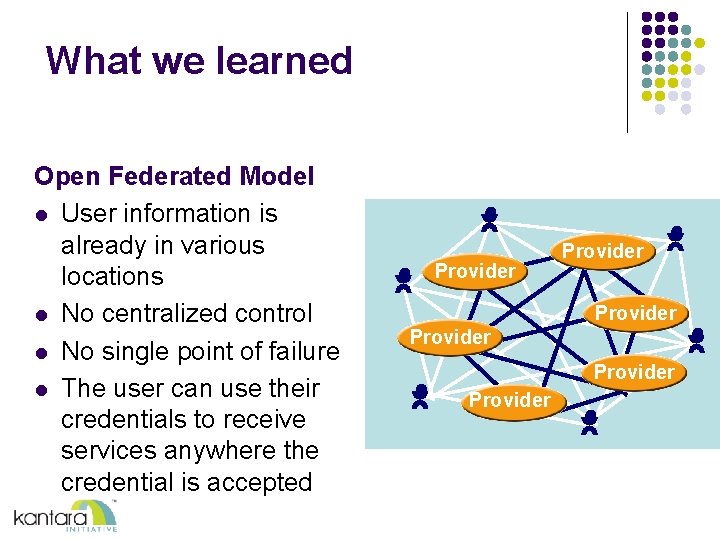
What we learned Open Federated Model l User information is already in various locations l No centralized control l No single point of failure l The user can use their credentials to receive services anywhere the credential is accepted Provider Provider
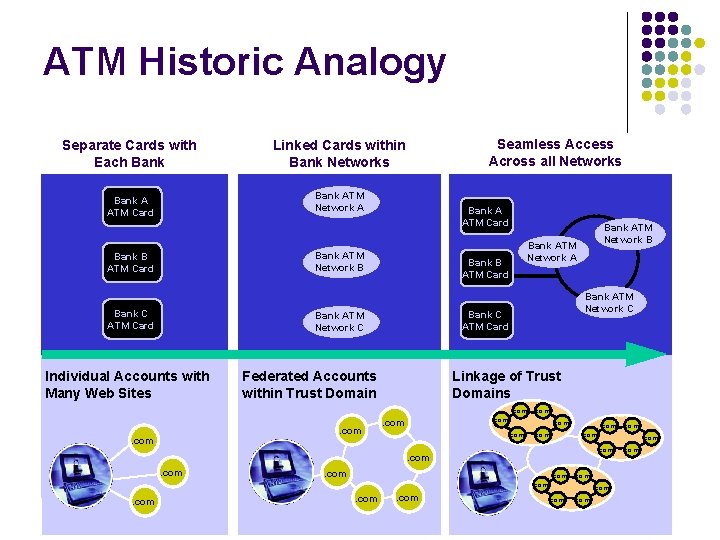
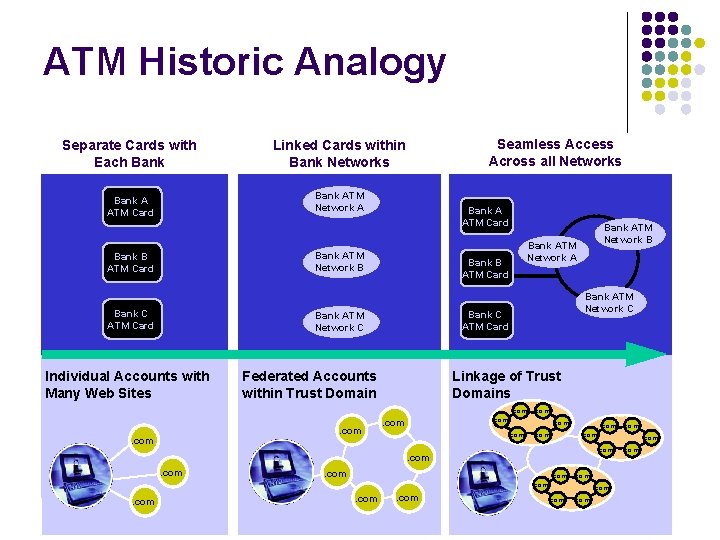
ATM Historic Analogy Separate Cards with Each Bank Linked Cards within Bank Networks Bank A ATM Card Bank ATM Network A Seamless Access Across all Networks Bank A ATM Card Bank ATM Network B Bank B ATM Card Bank C ATM Card Individual Accounts with Many Web Sites Bank ATM Network A Bank B ATM Card Bank ATM Network C Bank C ATM Card Bank ATM Network C Federated Accounts within Trust Domain Bank ATM Network B Linkage of Trust Domains. com . com
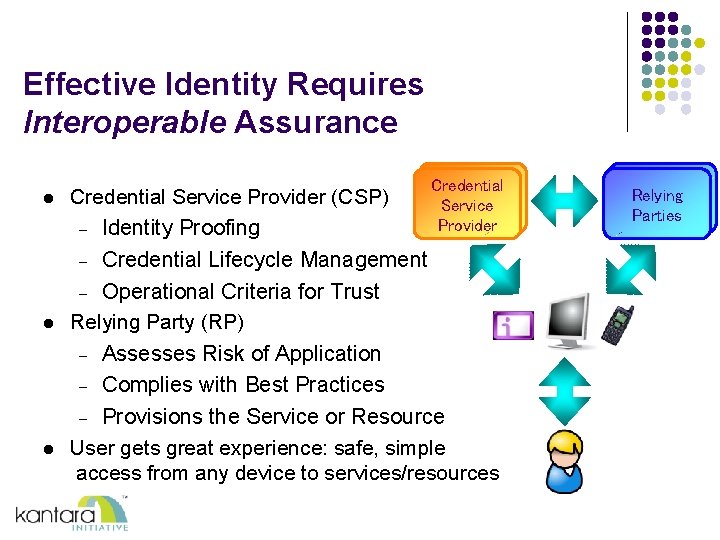
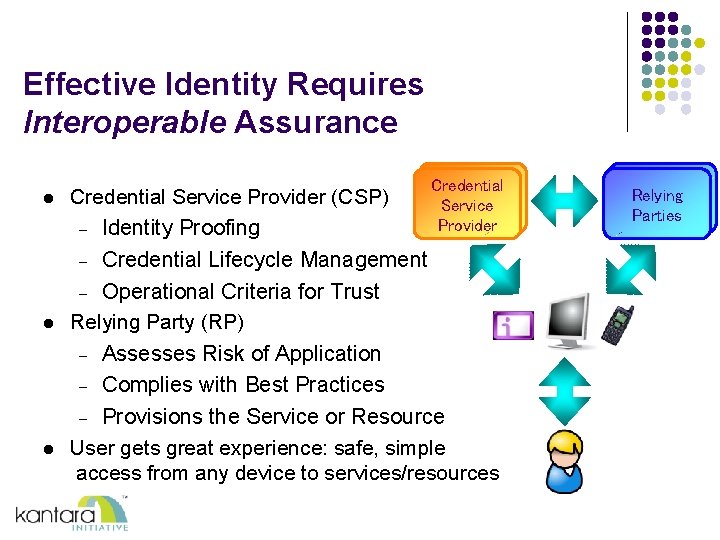
Effective Identity Requires Interoperable Assurance l Credential Service Provider (CSP) – Identity Proofing Credential Service Provider Credential Lifecycle Management – Operational Criteria for Trust Relying Party (RP) – Assesses Risk of Application – Complies with Best Practices – Provisions the Service or Resource User gets great experience: safe, simple access from any device to services/resources Relying Parties – l l 8
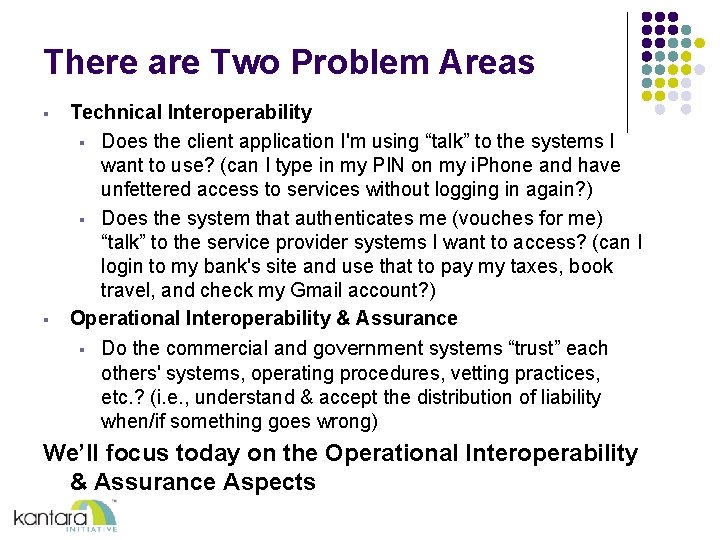
There are Two Problem Areas § § Technical Interoperability § Does the client application I'm using “talk” to the systems I want to use? (can I type in my PIN on my i. Phone and have unfettered access to services without logging in again? ) § Does the system that authenticates me (vouches for me) “talk” to the service provider systems I want to access? (can I login to my bank's site and use that to pay my taxes, book travel, and check my Gmail account? ) Operational Interoperability & Assurance § Do the commercial and government systems “trust” each others' systems, operating procedures, vetting practices, etc. ? (i. e. , understand & accept the distribution of liability when/if something goes wrong) We’ll focus today on the Operational Interoperability & Assurance Aspects
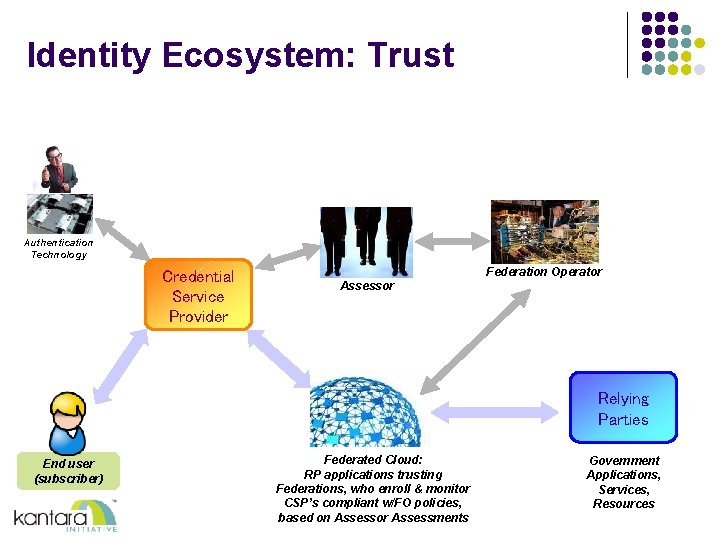
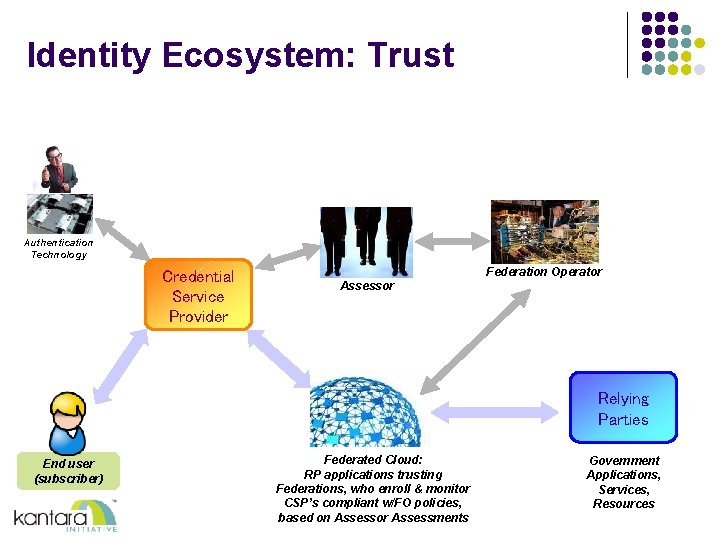
Identity Ecosystem: Trust Authentication Technology Credential Service Provider Federation Operator Assessor Relying Parties End user (subscriber) Federated Cloud: RP applications trusting Federations, who enroll & monitor CSP’s compliant w/FO policies, based on Assessor Assessments Government Applications, Services, Resources

…so why the need for a common standard? Identity Assurance Framework
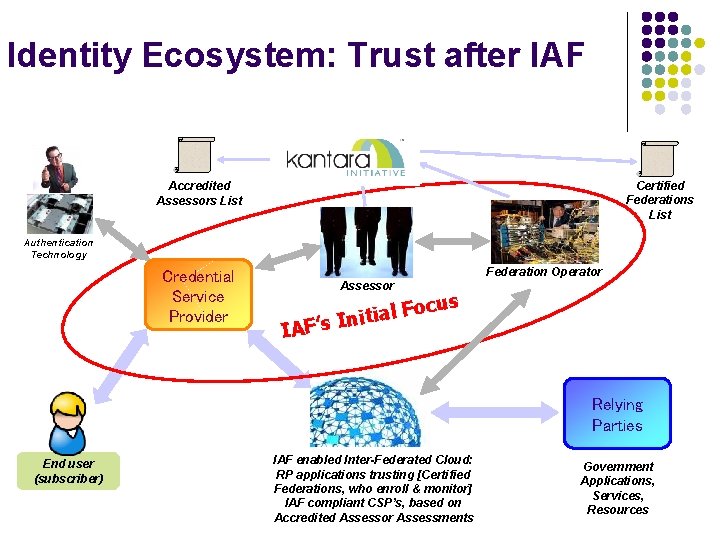
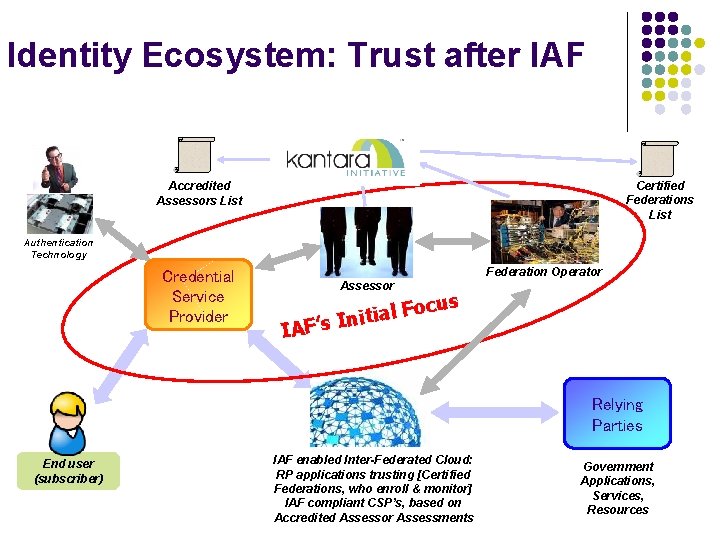
Identity Ecosystem: Trust after IAF Certified Federations List Accredited Assessors List Authentication Technology Credential Service Provider Federation Operator Assessor Foc l a i t i n ’s I IAF us Relying Parties End user (subscriber) IAF enabled Inter-Federated Cloud: RP applications trusting [Certified Federations, who enroll & monitor] IAF compliant CSP’s, based on Accredited Assessor Assessments Government Applications, Services, Resources
End Goal The end goal of this activity is to provide public and private sector organizations with a uniform means of relying on digital credentials issued by a variety of identity assurance providers (credential service providers) in order to advance trusted identity and facilitate public access to online services and information. Interoperability of e-authentication systems, mutual acceptance of rules, policies and supporting business processes is critical to the cost-effective operation of safe and secure systems that perform essential electronic transactions 13 and tasks across industry lines.
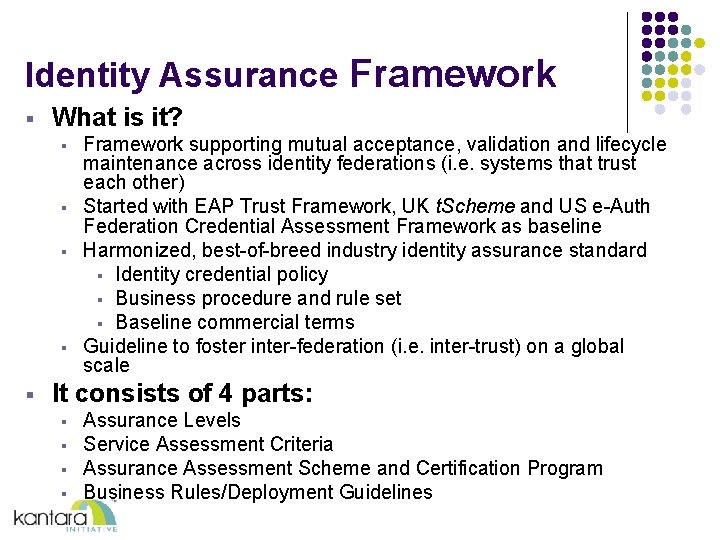
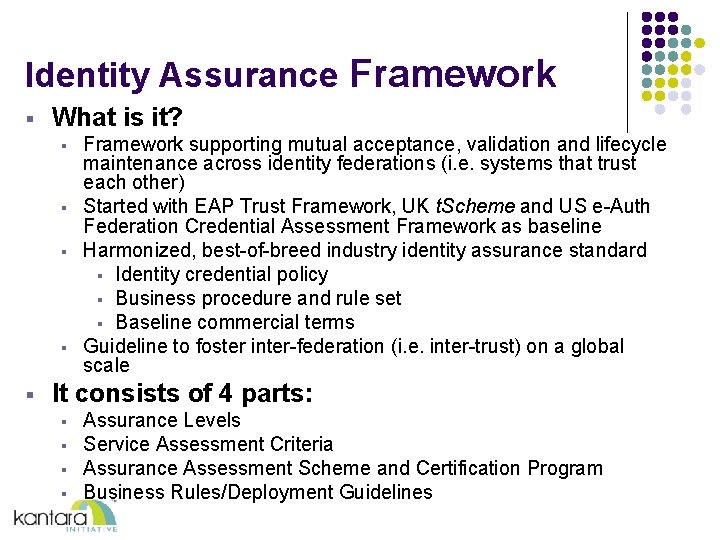
Identity Assurance Framework § What is it? § § § Framework supporting mutual acceptance, validation and lifecycle maintenance across identity federations (i. e. systems that trust each other) Started with EAP Trust Framework, UK t. Scheme and US e-Auth Federation Credential Assessment Framework as baseline Harmonized, best-of-breed industry identity assurance standard § Identity credential policy § Business procedure and rule set § Baseline commercial terms Guideline to foster inter-federation (i. e. inter-trust) on a global scale It consists of 4 parts: § § Assurance Levels Service Assessment Criteria Assurance Assessment Scheme and Certification Program Business Rules/Deployment Guidelines
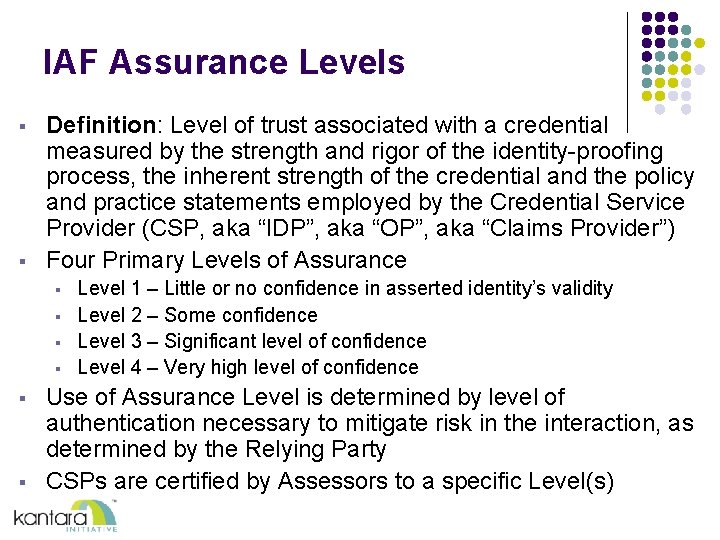
IAF Assurance Levels § § Definition: Level of trust associated with a credential measured by the strength and rigor of the identity-proofing process, the inherent strength of the credential and the policy and practice statements employed by the Credential Service Provider (CSP, aka “IDP”, aka “OP”, aka “Claims Provider”) Four Primary Levels of Assurance § § § Level 1 – Little or no confidence in asserted identity’s validity Level 2 – Some confidence Level 3 – Significant level of confidence Level 4 – Very high level of confidence Use of Assurance Level is determined by level of authentication necessary to mitigate risk in the interaction, as determined by the Relying Party CSPs are certified by Assessors to a specific Level(s)
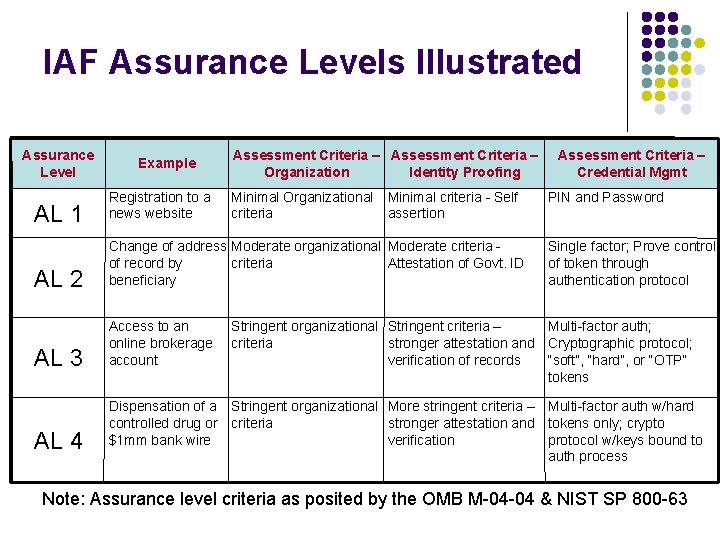
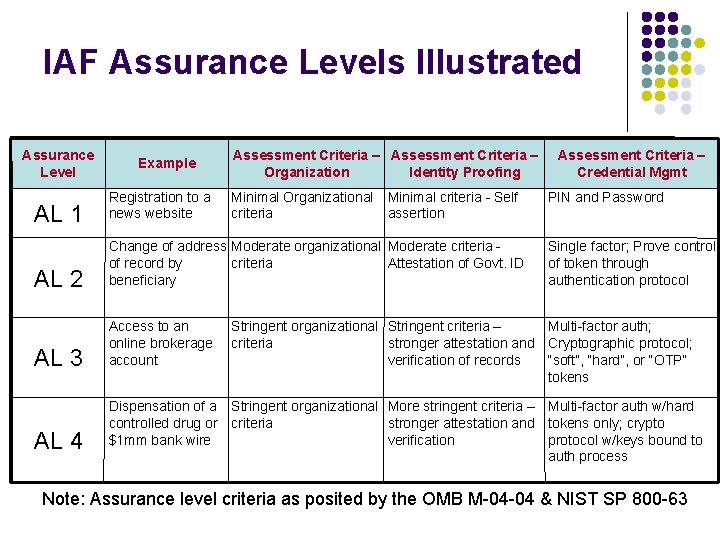
IAF Assurance Levels Illustrated Assurance Level Example Assessment Criteria – Organization Identity Proofing AL 1 Registration to a news website AL 2 Change of address Moderate organizational Moderate criteria of record by criteria Attestation of Govt. ID beneficiary AL 3 Access to an online brokerage account AL 4 Minimal Organizational criteria Minimal criteria - Self assertion Assessment Criteria – Credential Mgmt PIN and Password Single factor; Prove control of token through authentication protocol Stringent organizational Stringent criteria – Multi-factor auth; criteria stronger attestation and Cryptographic protocol; verification of records “soft”, “hard”, or “OTP” tokens Dispensation of a Stringent organizational More stringent criteria – Multi-factor auth w/hard controlled drug or criteria stronger attestation and tokens only; crypto $1 mm bank wire verification protocol w/keys bound to auth process Note: Assurance level criteria as posited by the OMB M-04 -04 & NIST SP 800 -63
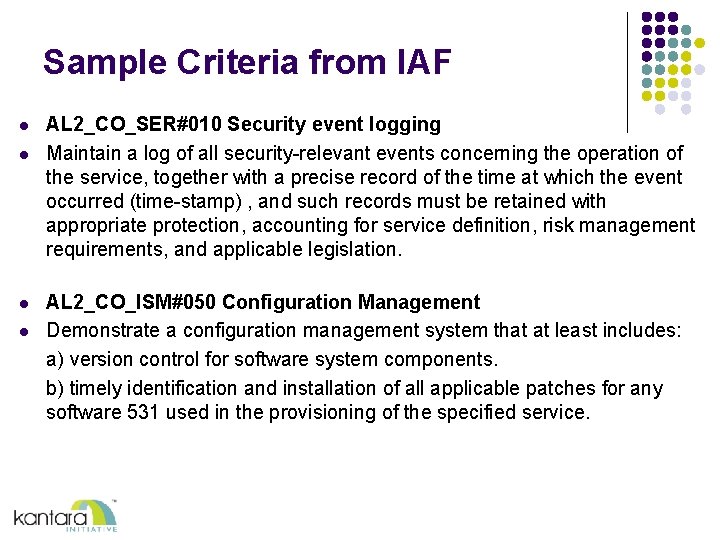
Sample Criteria from IAF l l AL 2_CO_SER#010 Security event logging Maintain a log of all security-relevant events concerning the operation of the service, together with a precise record of the time at which the event occurred (time-stamp) , and such records must be retained with appropriate protection, accounting for service definition, risk management requirements, and applicable legislation. AL 2_CO_ISM#050 Configuration Management Demonstrate a configuration management system that at least includes: a) version control for software system components. b) timely identification and installation of all applicable patches for any software 531 used in the provisioning of the specified service.
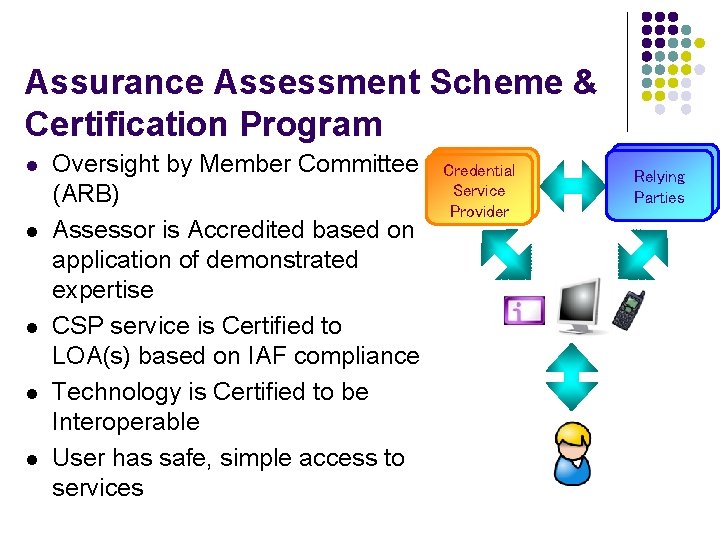
Assurance Assessment Scheme & Certification Program l l l Oversight by Member Committee (ARB) Assessor is Accredited based on application of demonstrated expertise CSP service is Certified to LOA(s) based on IAF compliance Technology is Certified to be Interoperable User has safe, simple access to services Credential Service Provider Relying Parties
Assurance Review Board l l l Assurance Review Board (ARB): effects oversight and processes all applications Comprised of representatives of the identity marketplace ecosystem, and currently includes representatives from the following communities: l Credential Service Provider (CSPs) l Relying Party (RP) l Auditor l Federation Operator l “Interested Party”—ie. an entity that stands to benefit from such a program, but does not have an offering to put through the program Current ARB appointees include Mark Coderre, Aetna; Nigel Tedeschi, BT; David Temoshok, GSA; Nathan Faut, KPMG; and Leif Johansson, SUNET/NORDUnet
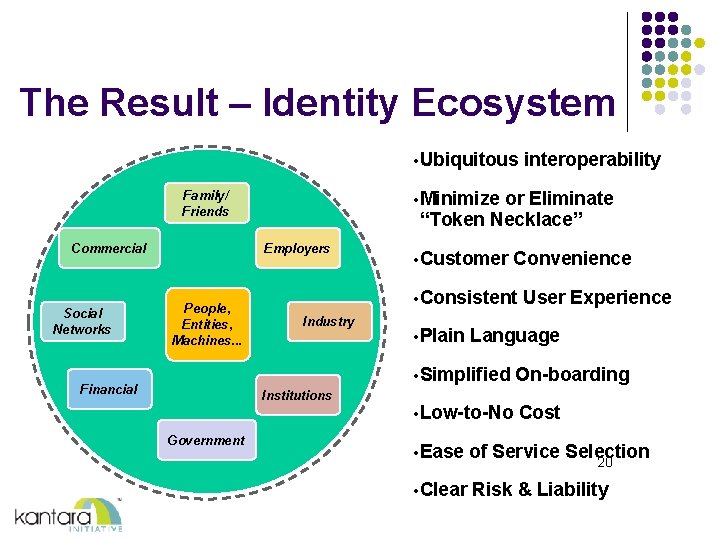
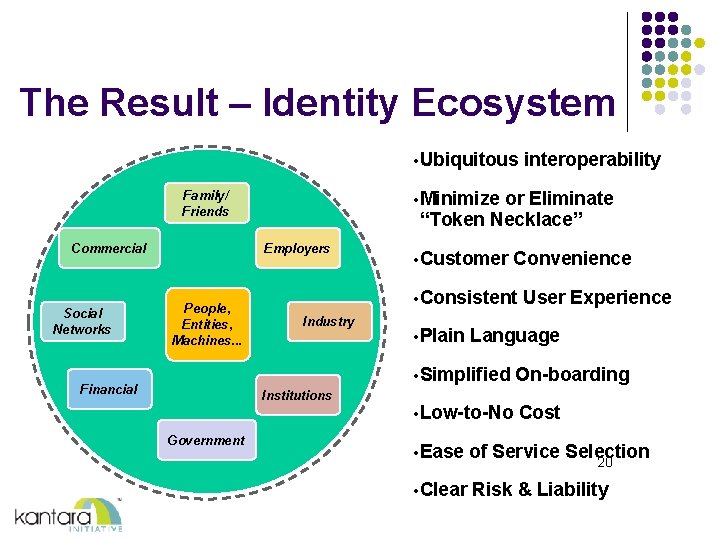
The Result – Identity Ecosystem • Ubiquitous • Minimize or Eliminate “Token Necklace” Family/ Friends Commercial Social Networks Employers People, Entities, Machines. . . Financial • Customer Convenience • Consistent Industry Institutions Government interoperability • Plain User Experience Language • Simplified On-boarding • Low-to-No Cost • Ease of Service Selection • Clear Risk & Liability 20

More Information on IAF and the Assurance Certification Program http: //kantarainitiative. org/confluence/display/ certification/Identity+Assurance+Certification +Program If you are interested in participating in the Certification pilot, please contact Britta Glade (britta@kantarainitiative. org)