ASIACRYPT 2010 December 6 2010 LINEARCOMPLEXITY PRIVATE SET
ASIACRYPT 2010 December 6, 2010 LINEAR-COMPLEXITY PRIVATE SET INTERSECTION PROTOCOLS SECURE IN MALICIOUS MODEL Emiliano De Cristofaro 1, Jihye Kim 2, and Gene Tsudik 1 1 University of California, Irvine 2 Seoul National University 1
Outline n n n Motivation Private Set Intersection Primitives 1. Authorized Private Set Intersection (APSI) construct 2. Plain Private Set Intersection (PSI) construct • Linear-complexity constructions secure in the malicious model n n Performance Comparison Future Work 2
Privacy n Privacy and society (Image from geekologie. com) • Basic individual right & desire • Relevant to entities, e. g. , corporations & governments • Recently increased awareness n Privacy and technology • Information disclosed (mostly on the Internet) • Handling and transfer of sensitive information • Need to combine Privacy and Accountability n Goal: Design protocols allowing to “share” only what needs to be shared and nothing else (or as little as possible). 3
Private Set Intersection IRS <--- Foreign Bank n • Learn if suspected tax evaders have bank accounts Governmental Agency <--- Industrial Contractor n • Learn if any employee has criminal records CIA <---> MI 5 n • Compare databases of terrorist suspects DHS <--- Airline Company n • Check if any passenger is on the DHS Terrorist Watch List 4
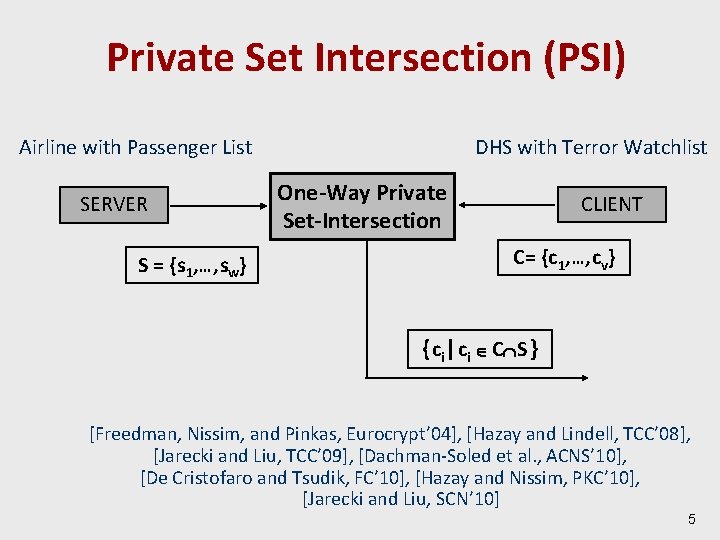
Private Set Intersection (PSI) Airline with Passenger List SERVER S = {s 1, … , sw} DHS with Terror Watchlist One-Way Private Set-Intersection CLIENT C= {c 1, … , cv} { c i | c i C S } [Freedman, Nissim, and Pinkas, Eurocrypt’ 04], [Hazay and Lindell, TCC’ 08], [Jarecki and Liu, TCC’ 09], [Dachman-Soled et al. , ACNS’ 10], [De Cristofaro and Tsudik, FC’ 10], [Hazay and Nissim, PKC’ 10], [Jarecki and Liu, SCN’ 10] 5
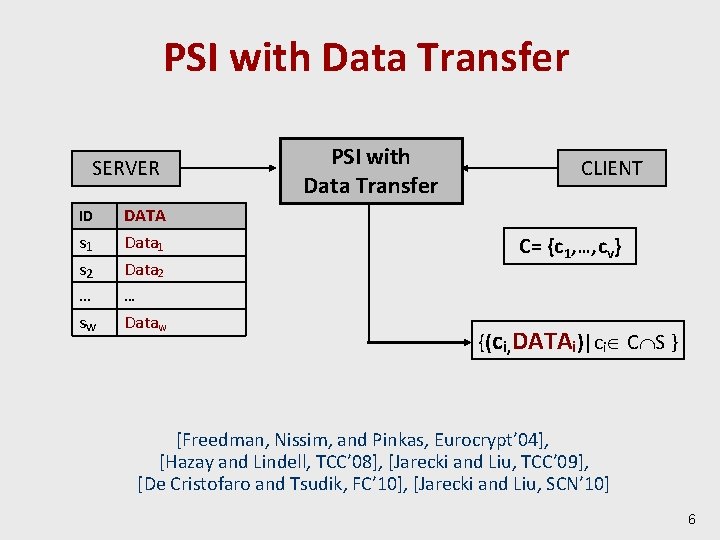
PSI with Data Transfer SERVER ID s 1 s 2 … sw DATA Data 1 Data 2 PSI with Data Transfer CLIENT C= {c 1, … , cv} … Dataw {(ci, DATAi)|ci C S } [Freedman, Nissim, and Pinkas, Eurocrypt’ 04], [Hazay and Lindell, TCC’ 08], [Jarecki and Liu, TCC’ 09], [De Cristofaro and Tsudik, FC’ 10], [Jarecki and Liu, SCN’ 10] 6
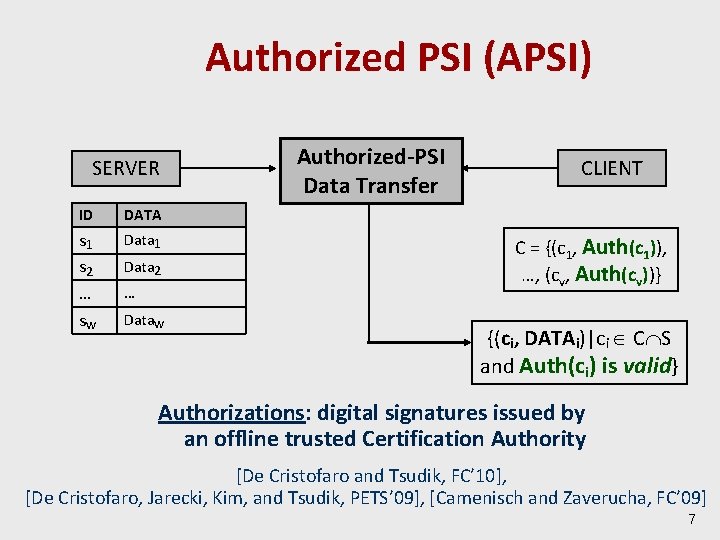
Authorized PSI (APSI) SERVER ID DATA s 1 s 2 … sw Data 1 Data 2 … Dataw Authorized-PSI Data Transfer CLIENT C = {(c 1, Auth(c 1)), …, (cv, Auth(cv))} {(ci, DATAi)|ci C S and Auth(ci) is valid} Authorizations: digital signatures issued by an offline trusted Certification Authority [De Cristofaro and Tsudik, FC’ 10], [De Cristofaro, Jarecki, Kim, and Tsudik, PETS’ 09], [Camenisch and Zaverucha, FC’ 09] 7
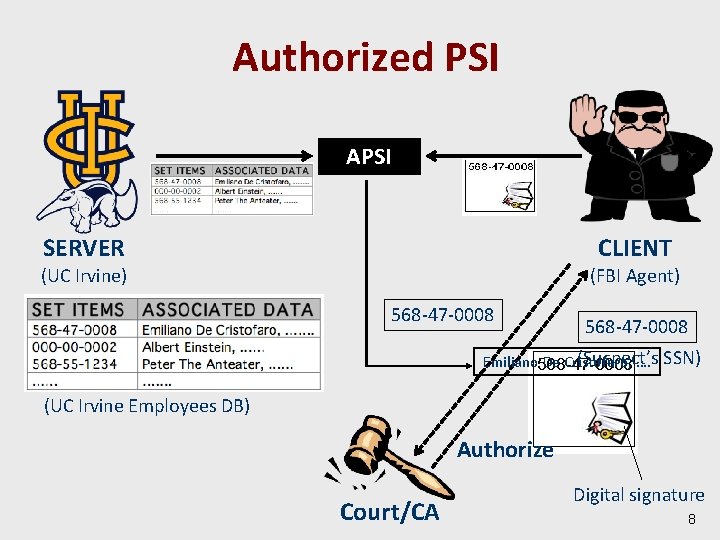
Authorized PSI APSI SERVER CLIENT (UC Irvine) (FBI Agent) 568 -47 -0008 (Suspect’s Emiliano De Cristofaro, …. SSN) (UC Irvine Employees DB) Authorize Court/CA Digital signature 8
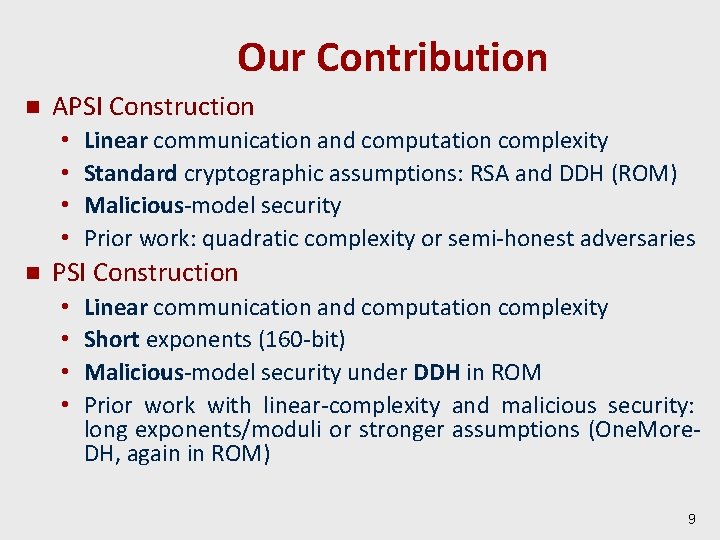
Our Contribution n APSI Construction • • n Linear communication and computation complexity Standard cryptographic assumptions: RSA and DDH (ROM) Malicious-model security Prior work: quadratic complexity or semi-honest adversaries PSI Construction • • Linear communication and computation complexity Short exponents (160 -bit) Malicious-model security under DDH in ROM Prior work with linear-complexity and malicious security: long exponents/moduli or stronger assumptions (One. More. DH, again in ROM) 9
Outline n n n Motivation Private Set Intersection Primitives 1. Authorized Private Set Intersection (APSI) construct 2. Plain Private Set Intersection (PSI) construct Performance Comparison Future Work 10
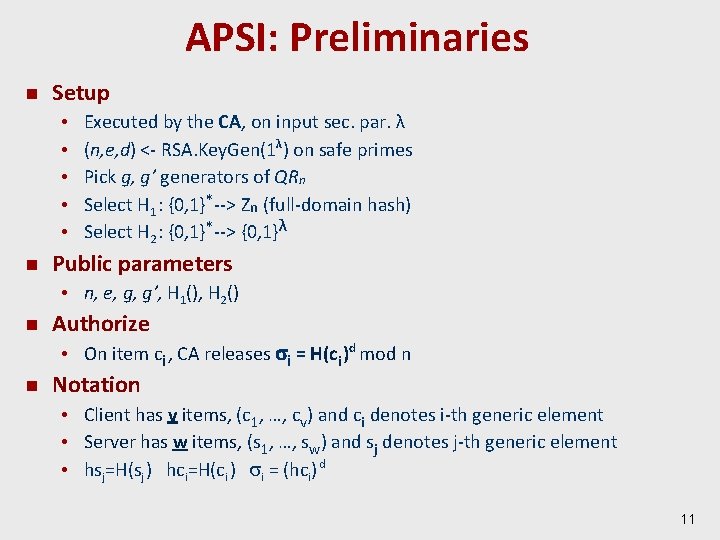
APSI: Preliminaries n Setup • • • n Executed by the CA, on input sec. par. λ (n, e, d) <- RSA. Key. Gen(1λ) on safe primes Pick g, g’ generators of QRn Select H 1 : {0, 1}*--> Zn (full-domain hash) Select H 2 : {0, 1}*--> {0, 1}λ Public parameters • n, e, g, g’, H 1(), H 2() n Authorize • On item ci , CA releases i = H(ci )d mod n n Notation • Client has v items, (c 1, …, cv) and ci denotes i-th generic element • Server has w items, (s 1, …, sw) and sj denotes j-th generic element • hsj=H(sj ) hci=H(ci ) i = (hci) d 11
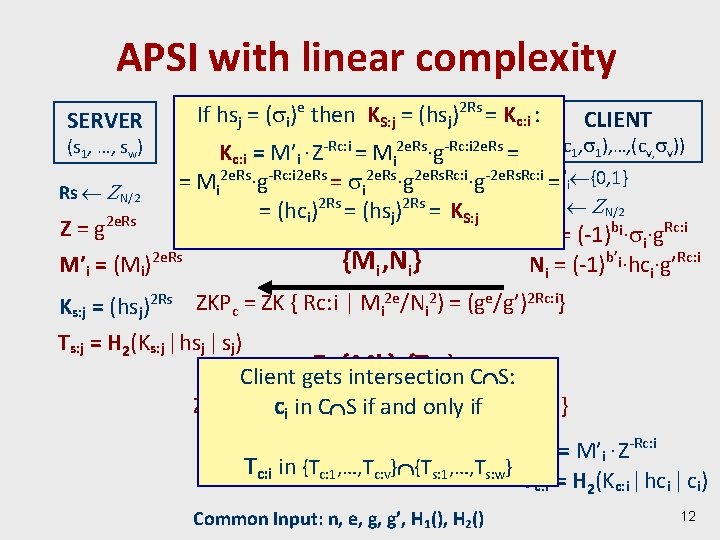
APSI with linear complexity SERVER If hsj = ( icomputation )e then KS: j mod = (hsnj)2 Rs = Kc: i : CLIENT Kc: i = M’i · Z-Rc: i = Mi 2 e. Rs·g-Rc: i 2 e. Rs = ((c 1, 1), …, (cv, v)) 2 e. Rs -Rc: i 2 e. Rs. Rc: i -2 e. Rs. Rc: i bi, b’ = M ·g = ·g ·g = i {0, 1} i i Rs N/2 2 Rs Rc: i N/2 = (hc ) = (hs ) = KS: j i j 2 e. Rs Z=g Mi = (-1)bi· i·g. Rc: i {Mi , Ni} M’i = (Mi)2 e. Rs Ni = (-1)b’i·hci·g’Rc: i (s 1, …, sw) Ks: j = (hsj)2 Rs ZKPc = ZK { Rc: i | Mi 2 e/Ni 2) = (ge/g’)2 Rc: i} Ts: j = H 2(Ks: j | hsj | sj) Z, {intersection M’i}, {Ts: j} C S: Client gets 2 e. Rs, M’ =(M )2 e. Rs } ZKPs = ZKci{in Rs. C| ZS =if (g) and only ifi i KC: i = M’i · Z-Rc: i Tc: i in {Tc: 1, …, Tc: v} {Ts: 1, …, Ts: w} Tc: i = H 2(Kc: i | hci | ci) Common Input: n, e, g, g’, H 1(), H 2() 12
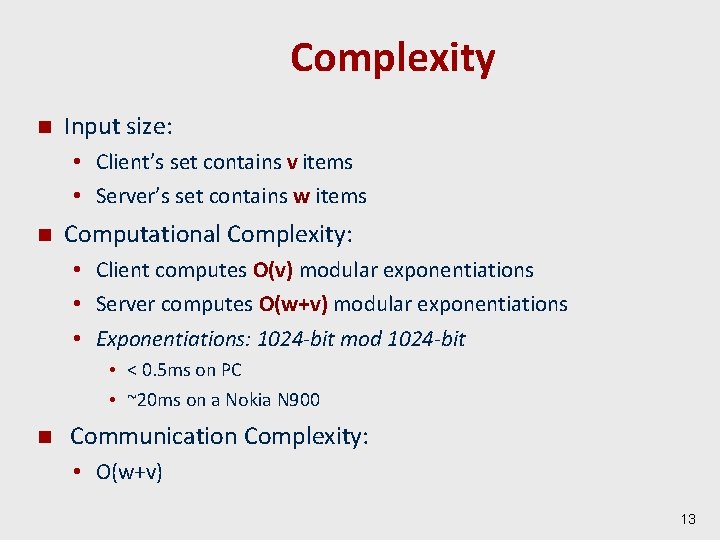
Complexity n Input size: • Client’s set contains v items • Server’s set contains w items n Computational Complexity: • Client computes O(v) modular exponentiations • Server computes O(w+v) modular exponentiations • Exponentiations: 1024 -bit mod 1024 -bit • < 0. 5 ms on PC • ~20 ms on a Nokia N 900 n Communication Complexity: • O(w+v) 13
Outline n n n Motivation Private Set Intersection Primitives 1. Authorized Private Set Intersection (APSI) construct 2. Plain Private Set Intersection (PSI) construct Performance Comparison Future Work 14
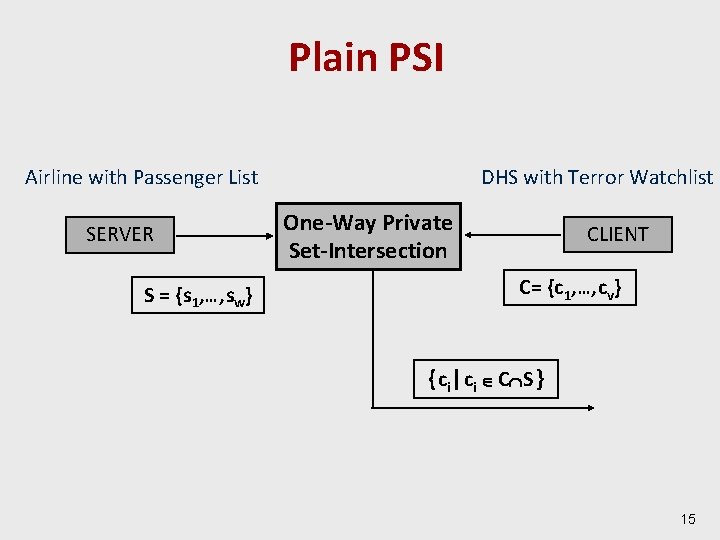
Plain PSI Airline with Passenger List SERVER S = {s 1, … , sw} DHS with Terror Watchlist One-Way Private Set-Intersection CLIENT C= {c 1, … , cv} { c i | c i C S } 15
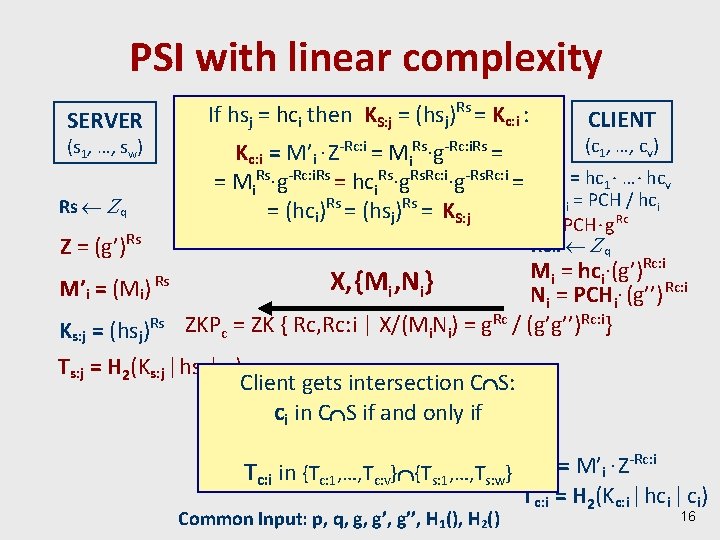
PSI with linear complexity SERVER (s 1, …, sw) Rs q Z = (g’)Rs M’i = (Mi) Rs Ks: j = (hsj)Rs If hsj = hccomputation (hspj)Rs = Kc: i : mod i then KS: j = CLIENT (c 1, …, cv) Kc: i = M’i · Z-Rc: i = Mi. Rs·g-Rc: i. Rs = hci. Rs·g. Rs. Rc: i·g-Rs. Rc: i = PCH = hc 1 · … · hcv PCHi = PCH / hci = (hci)Rs = (hsj)Rs = KS: j Rc X = PCH · g Rc: i q Rc: i M = hc ·(g’) i i X, {Mi , Ni} Ni = PCHi· (g’’) Rc: i ZKPc = ZK { Rc, Rc: i | X/(Mi. Ni) = g. Rc / (g’g’’)Rc: i} Ts: j = H 2(Ks: j | hsj | sj) Client gets Z, {intersection M’i}, {Ts: j} C S: ci in C S if and only if ZKPs = ZK { Rs | Z = (g’)Rs, M’i=(Mi)Rs } -Rc: i K = M’ · Z i Tc: i in {Tc: 1, …, Tc: v} {Ts: 1, …, Ts: w} C: i Tc: i = H 2(Kc: i | hci | ci) Common Input: p, q, g, g’’, H 1(), H 2() 16
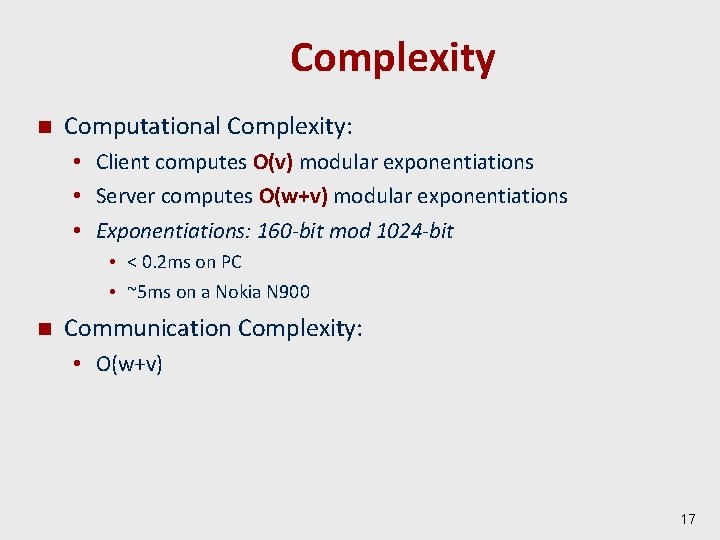
Complexity n Computational Complexity: • Client computes O(v) modular exponentiations • Server computes O(w+v) modular exponentiations • Exponentiations: 160 -bit mod 1024 -bit • < 0. 2 ms on PC • ~5 ms on a Nokia N 900 n Communication Complexity: • O(w+v) 17
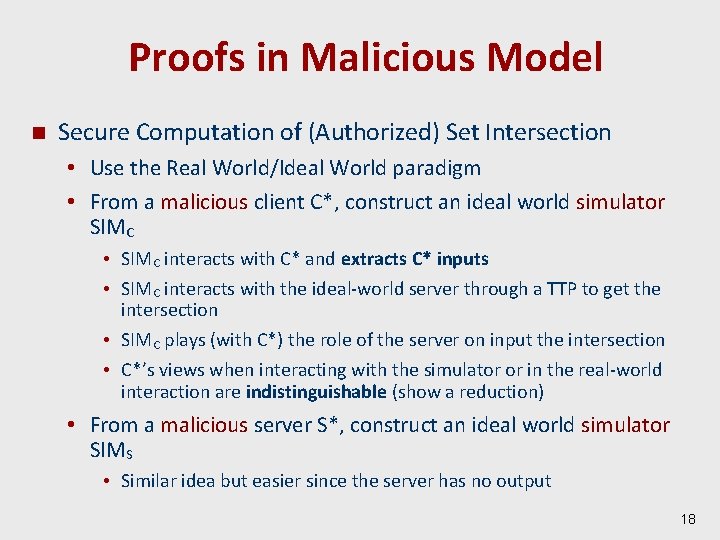
Proofs in Malicious Model n Secure Computation of (Authorized) Set Intersection • Use the Real World/Ideal World paradigm • From a malicious client C*, construct an ideal world simulator SIMC • SIMC interacts with C* and extracts C* inputs • SIMC interacts with the ideal-world server through a TTP to get the intersection • SIMC plays (with C*) the role of the server on input the intersection • C*’s views when interacting with the simulator or in the real-world interaction are indistinguishable (show a reduction) • From a malicious server S*, construct an ideal world simulator SIMS • Similar idea but easier since the server has no output 18
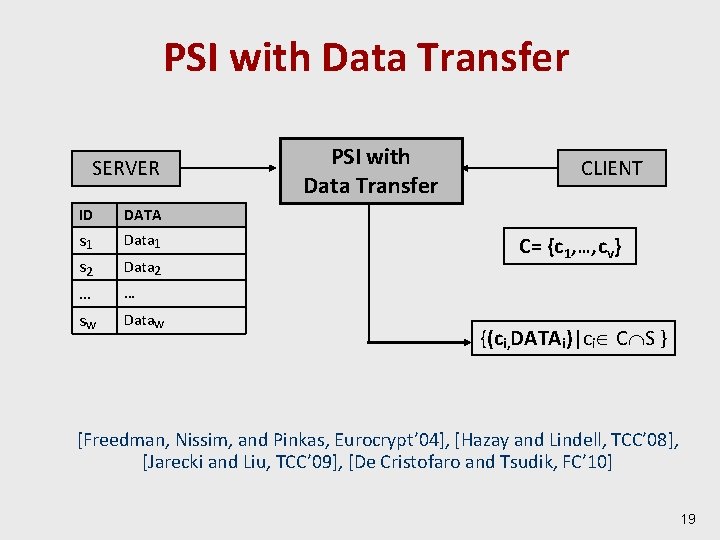
PSI with Data Transfer SERVER ID DATA s 1 s 2 … sw Data 1 Data 2 PSI with Data Transfer CLIENT C= {c 1, … , cv} … Dataw {(ci, DATAi)|ci C S } [Freedman, Nissim, and Pinkas, Eurocrypt’ 04], [Hazay and Lindell, TCC’ 08], [Jarecki and Liu, TCC’ 09], [De Cristofaro and Tsudik, FC’ 10] 19
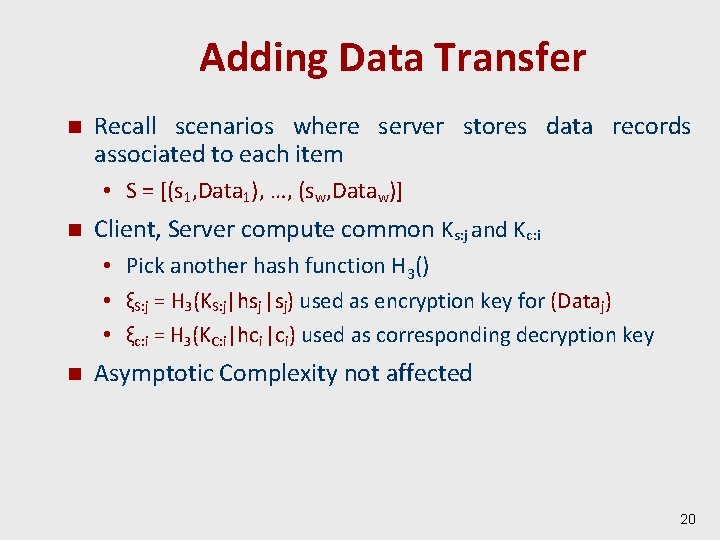
Adding Data Transfer n Recall scenarios where server stores data records associated to each item • S = [(s 1, Data 1), …, (sw, Dataw)] n Client, Server compute common Ks: j and Kc: i • Pick another hash function H 3() • ξS: j = H 3(KS: j|hsj |sj) used as encryption key for (Dataj) • ξc: i = H 3(KC: i|hci |ci) used as corresponding decryption key n Asymptotic Complexity not affected 20
![Comparison (APSI) Tools Model Comm Server Op Client Op Camenisch and Zaverucha [FC 09] Comparison (APSI) Tools Model Comm Server Op Client Op Camenisch and Zaverucha [FC 09]](http://slidetodoc.com/presentation_image/e99525b1136ed6e9b8e0d17592e1d1fa/image-21.jpg)
Comparison (APSI) Tools Model Comm Server Op Client Op Camenisch and Zaverucha [FC 09] (Certified Sets) SRSA Std Mal O(w·v) O(v·w) exps O(v+w) exps De Cristofaro et al. [PETS 09] (PPIT) RSA ROM Hb. C O(w·v) O(v+w) exps, O(v·w) mults O(v) exps De Cristofaro. Tsudik [FC 10] RSA ROM Hb. C O(w+v) O(v+w) exps O(v) exps Our APSI [Asiacrypt 10] RSA ROM Mal O(w+v) O(v+w) exps O(v) exps 21
![Comparison (PSI) Tools Model Adv Server Op Client Op Freedman et al. [Eurocr. 04] Comparison (PSI) Tools Model Adv Server Op Client Op Freedman et al. [Eurocr. 04]](http://slidetodoc.com/presentation_image/e99525b1136ed6e9b8e0d17592e1d1fa/image-22.jpg)
Comparison (PSI) Tools Model Adv Server Op Client Op Freedman et al. [Eurocr. 04] Oblivious Poly Eval Standard/ ROM Hb. C/ Malicious O(wlglg(v)) 160 -bit mod 1024 exps O(w+v) 160 -bit mod 1024 exps Kissner-Song [Crypto’ 05] Oblivious Poly Eval Standard Hb. C Malicious* O(w·v) m-bit mod 2048 exps O(w+v) m-bit mod 2048 exps Hazay-Lindell [TCC 08] DDH Standard Covert O(w+v) 160 -bit mod 1024 exps O(v) 160 -bit mod 1024 exps Jarecki-Liu [TCC 09] OPRF q-DDH (*) Standard CRS Malicious O(w) m-bit mod 2048 exps O(v) m-bit mod 2048 exps Hazay-Nissim [PKC 10] DDH Std Malicious O(wlglg(v)) 160 mod 1024 -bit exps O(w+v) 160 -bit mod 1024 exps Jarecki-Liu [SCN 10] One. More. DH ROM Malicious O(w+v) 160 -bit mod 1024 exps O(v) 160 -bit mod 1024 exps De Cristofaro. Tsudik [FC 10] One. More. RSA ROM Hb. C O(w+v) 1024 -bit mod 1024 exps O(v) mod mults Our PSI [Asiacrypt] DDH ROM Malicious O(w+v) 160 -bit mod 1024 exps O(v) 160 -bit mod 1024 exps 22
Conclusions n Motivated APSI and PSI applications n First linear-complexity APSI secure in malicious model • Security in ROM under the RSA and DDH assumptions n Linear-complexity PSI secure in malicious model • Security in ROM under the DDH assumptions • Enjoy short exponents n Current Work • • Removing ROM assumption (journal version) Extension to groups Size-Hiding PSI: hiding the size of client’s set Cardinality-only Private Set Intersection 23

Thank you! Image from truthdig. com 24
- Slides: 24