ARP Cache Poisoning Attack Dr Neminath Hubballi IIT
ARP Cache Poisoning Attack Dr. Neminath Hubballi IIT Indore © Neminath Hubballi
Outline ARP Cache Poisoning Defense mechanisms IIT Indore © Neminath Hubballi
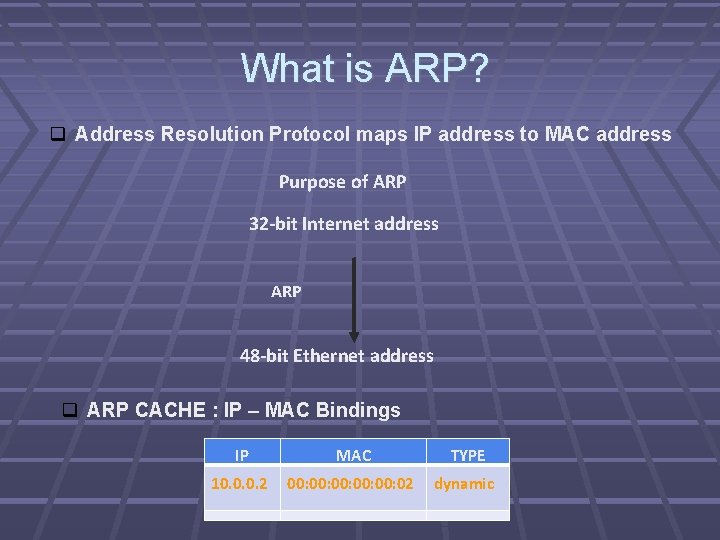
What is ARP? Address Resolution Protocol maps IP address to MAC address Purpose of ARP 32 -bit Internet address ARP 48 -bit Ethernet address ARP CACHE : IP – MAC Bindings IP MAC TYPE 10. 0. 0. 2 00: 00: 00: 02 dynamic IIT Indore © Neminath Hubballi
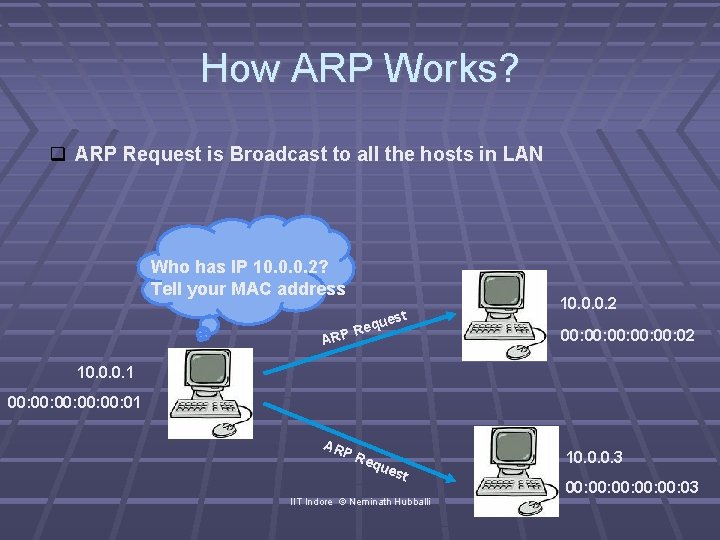
How ARP Works? ARP Request is Broadcast to all the hosts in LAN Who has IP 10. 0. 0. 2? Tell your MAC address t ues eq R ARP 10. 0. 0. 2 00: 00: 00: 02 10. 0. 0. 1 00: 00: 00: 01 AR PR equ est IIT Indore © Neminath Hubballi 10. 0. 0. 3 00: 00: 00: 03
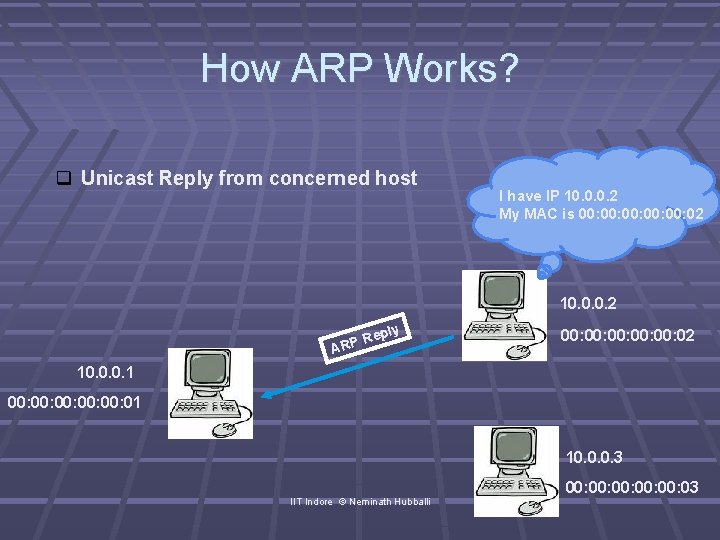
How ARP Works? Unicast Reply from concerned host I have IP 10. 0. 0. 2 My MAC is 00: 00: 00: 02 10. 0. 0. 2 ply Re ARP 00: 00: 00: 02 10. 0. 0. 1 00: 00: 00: 01 10. 0. 0. 3 IIT Indore © Neminath Hubballi 00: 00: 00: 03
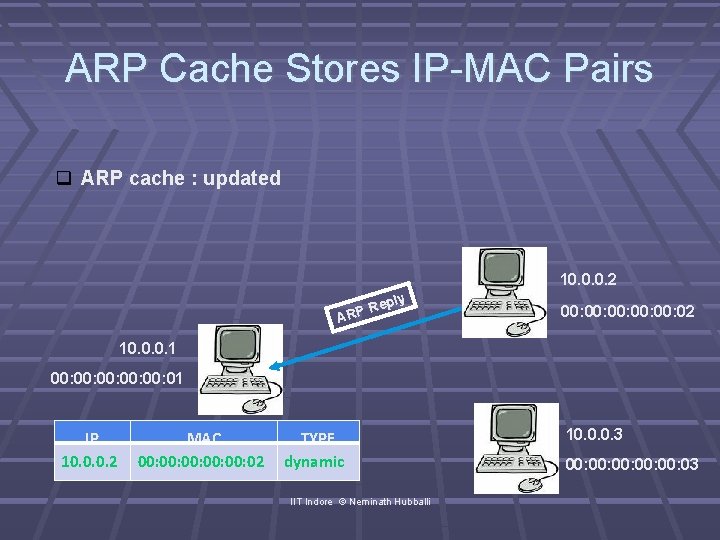
ARP Cache Stores IP-MAC Pairs ARP cache : updated 10. 0. 0. 2 ply Re ARP 00: 00: 00: 02 10. 0. 0. 1 00: 00: 00: 01 IP 10. 0. 0. 2 MAC 00: 00: 00: 02 TYPE dynamic IIT Indore © Neminath Hubballi 10. 0. 0. 3 00: 00: 00: 03
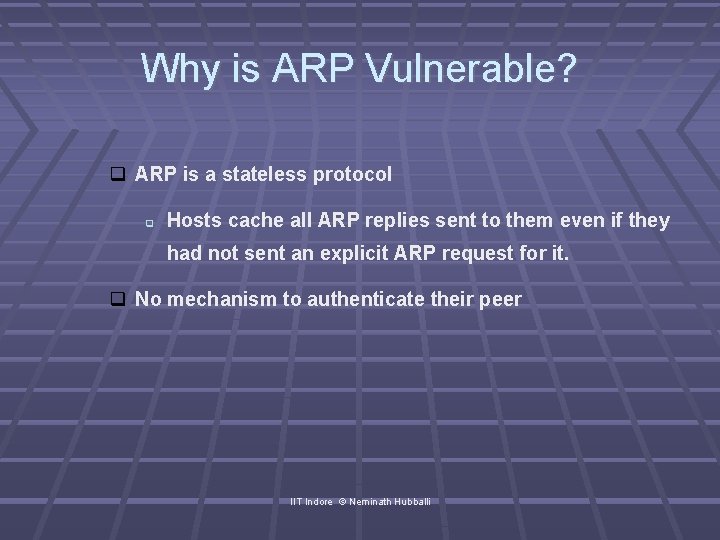
Why is ARP Vulnerable? ARP is a stateless protocol Hosts cache all ARP replies sent to them even if they had not sent an explicit ARP request for it. No mechanism to authenticate their peer IIT Indore © Neminath Hubballi
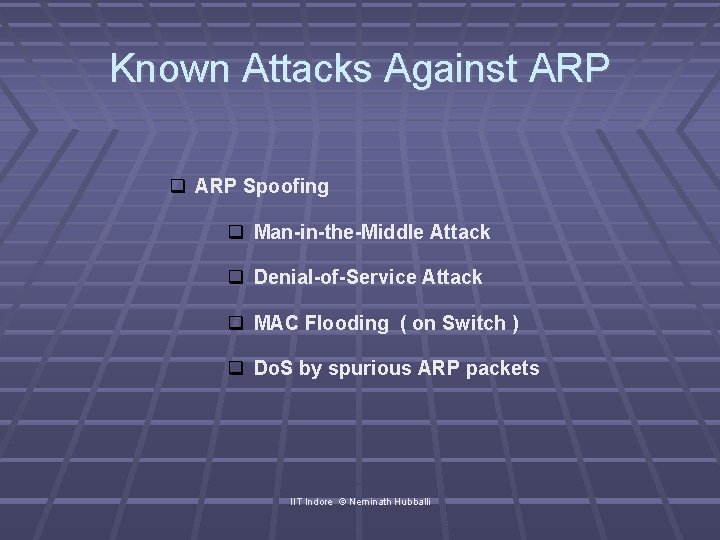
Known Attacks Against ARP Spoofing Man-in-the-Middle Attack Denial-of-Service Attack MAC Flooding ( on Switch ) Do. S by spurious ARP packets IIT Indore © Neminath Hubballi
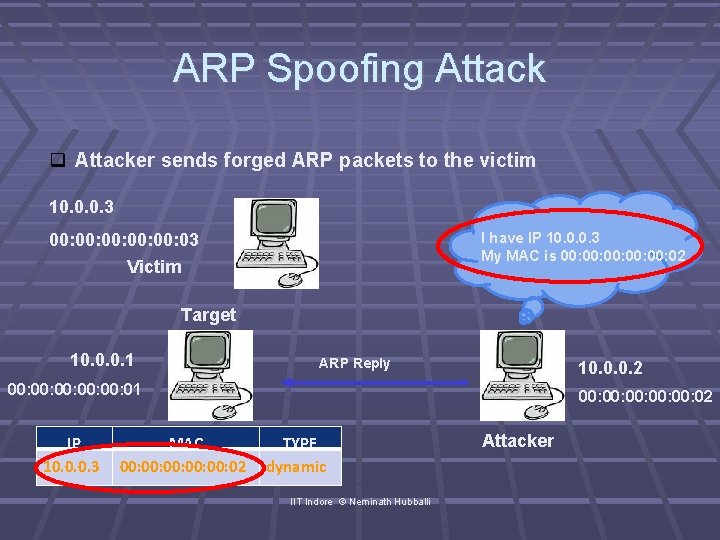
ARP Spoofing Attacker sends forged ARP packets to the victim 10. 0. 0. 3 I have IP 10. 0. 0. 3 My MAC is 00: 00: 00: 02 00: 00: 00: 03 Victim Target 10. 0. 0. 1 ARP Reply 10. 0. 0. 2 00: 00: 00: 01 IP 10. 0. 0. 3 MAC 00: 00: 00: 02 TYPE dynamic IIT Indore © Neminath Hubballi Attacker
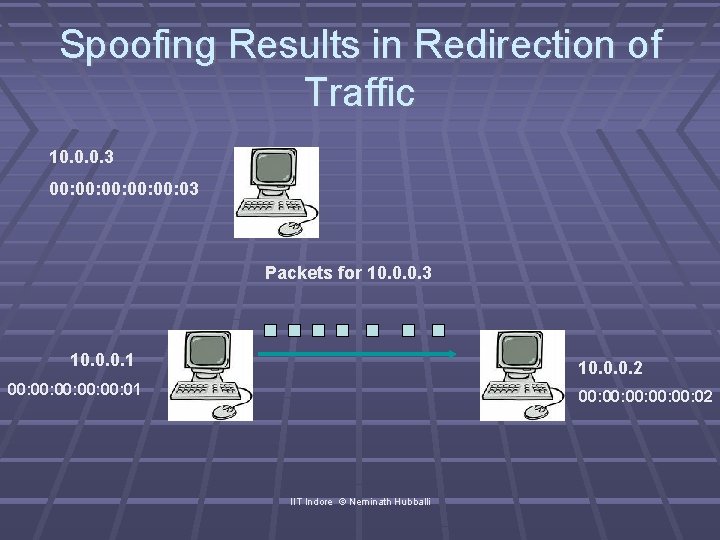
Spoofing Results in Redirection of Traffic 10. 0. 0. 3 00: 00: 00: 03 Packets for 10. 0. 0. 3 10. 0. 0. 1 10. 0. 0. 2 00: 00: 00: 01 00: 00: 00: 02 IIT Indore © Neminath Hubballi
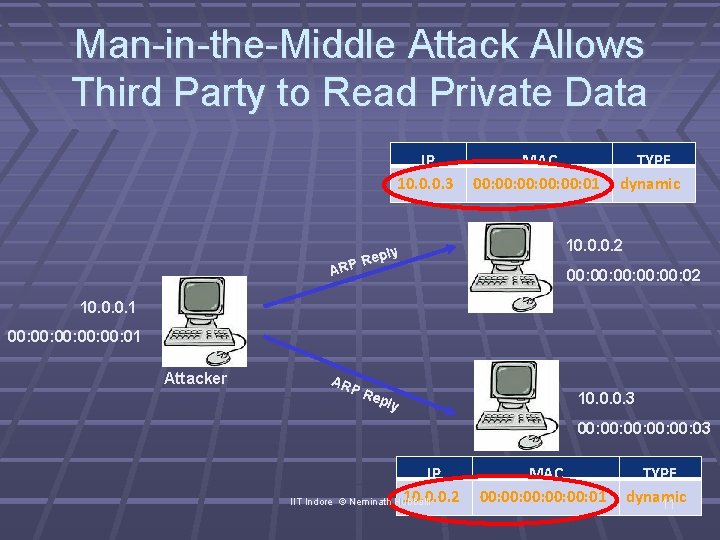
Man-in-the-Middle Attack Allows Third Party to Read Private Data IP 10. 0. 0. 3 ply P Re AR MAC 00: 00: 00: 01 TYPE dynamic 10. 0. 0. 2 00: 00: 00: 02 10. 0. 0. 1 00: 00: 00: 01 Attacker AR PR epl y 10. 0. 0. 3 00: 00: 00: 03 IIT Indore IP 10. 0. 0. 2 © Neminath Hubballi MAC 00: 00: 00: 01 TYPE dynamic 11
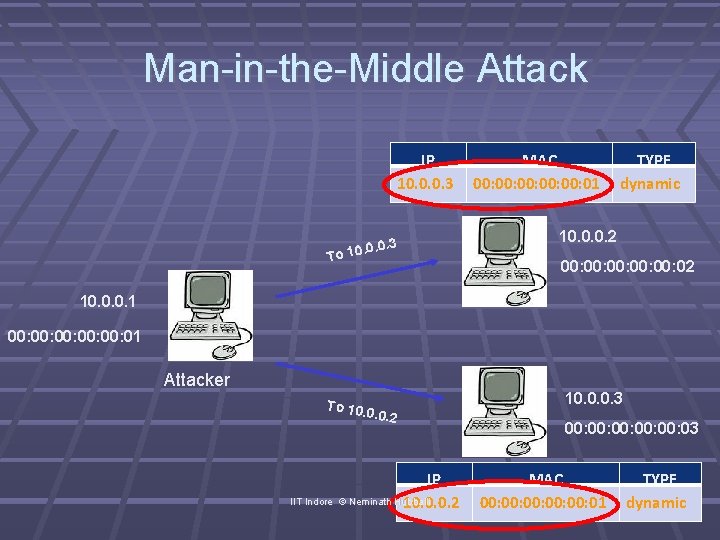
Man-in-the-Middle Attack IP 10. 0. 0. 3 To 10 MAC 00: 00: 00: 01 TYPE dynamic 10. 0. 0. 2 00: 00: 00: 02 10. 0. 0. 1 00: 00: 00: 01 Attacker To 10. 0. 0. 2 IIT Indore IP © Neminath Hubballi 10. 0. 0. 2 10. 0. 0. 3 00: 00: 00: 03 MAC 00: 00: 00: 01 TYPE dynamic
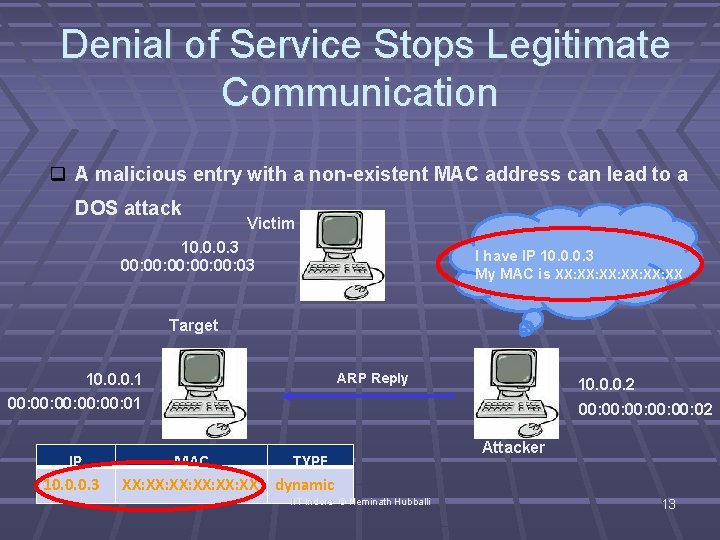
Denial of Service Stops Legitimate Communication A malicious entry with a non-existent MAC address can lead to a DOS attack Victim 10. 0. 0. 3 00: 00: 00: 03 I have IP 10. 0. 0. 3 My MAC is XX: XX: XX: XX Target ARP Reply 10. 0. 0. 1 00: 00: 00: 01 IP 10. 0. 0. 3 10. 0. 0. 2 00: 00: 00: 02 MAC TYPE XX: XX: XX: XX dynamic IIT Indore © Neminath Hubballi Attacker 13
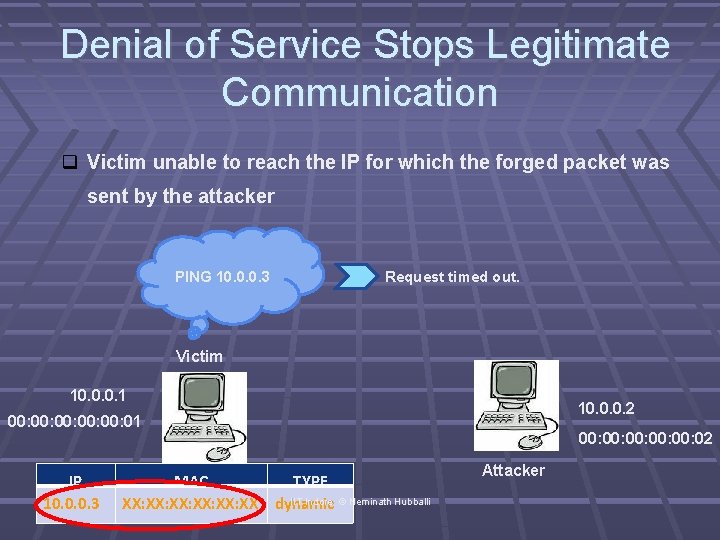
Denial of Service Stops Legitimate Communication Victim unable to reach the IP for which the forged packet was sent by the attacker PING 10. 0. 0. 3 Request timed out. Victim 10. 0. 0. 1 10. 0. 0. 2 00: 00: 00: 01 IP 10. 0. 0. 3 MAC TYPE IIT Indore © Neminath Hubballi XX: XX: XX: XX dynamic 00: 00: 00: 02 Attacker
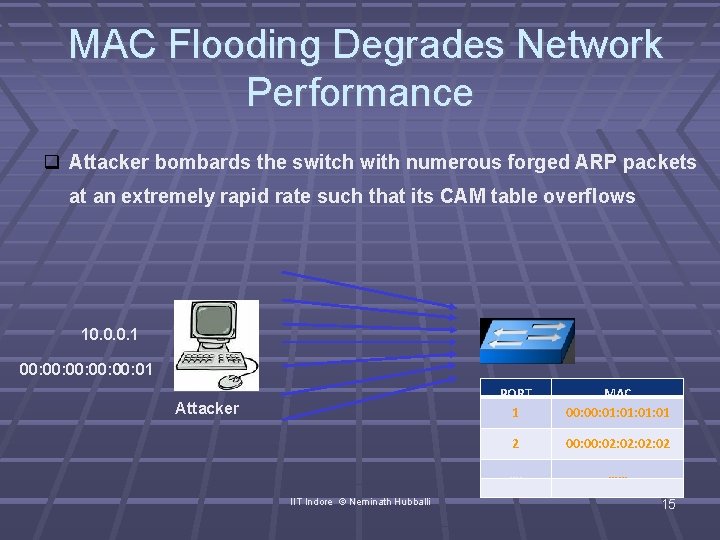
MAC Flooding Degrades Network Performance Attacker bombards the switch with numerous forged ARP packets at an extremely rapid rate such that its CAM table overflows 10. 0. 0. 1 00: 00: 00: 01 Attacker IIT Indore © Neminath Hubballi PORT 1 MAC 00: 01: 01: 01 2 00: 02: 02: 02 …. …. . …… ……. 15
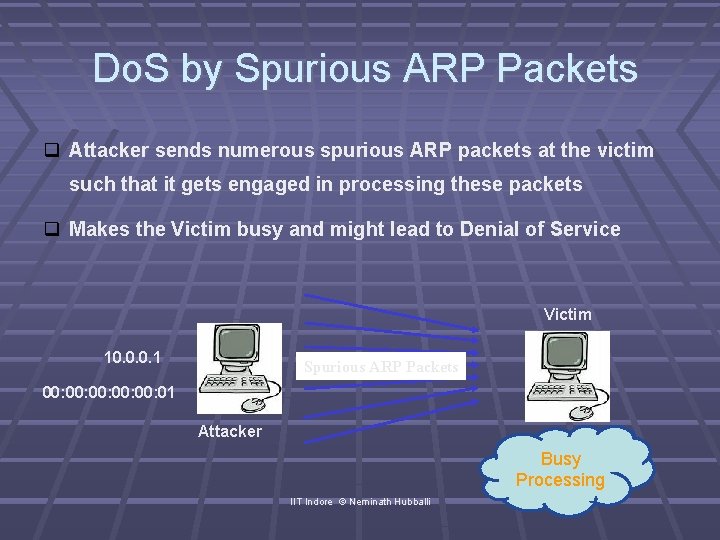
Do. S by Spurious ARP Packets Attacker sends numerous spurious ARP packets at the victim such that it gets engaged in processing these packets Makes the Victim busy and might lead to Denial of Service Victim 10. 0. 0. 1 Spurious ARP Packets 00: 00: 00: 01 Attacker Busy Processing IIT Indore © Neminath Hubballi
Detection and Mitigation Techniques Static ARP Cache entries—Fixed IP-MAC pairs ARPWATCH /COLOSOFT CAPSA/ARP-Guard- Maintains a database with IPMAC mappings and any change detected is reported to administrator Count the imbalance in number of requests and responses Evaded Cryptographic Techniques: Secure ARP – use cryptographic algorithms to authenticate TARP- ticket based IIT Indore © Neminath Hubballi
- Slides: 17