Are You Thinking About Cybersecurity The Wrong Way
Are You Thinking About Cybersecurity The Wrong Way? Darin R. Haines, SVP Global Consulting
Supply Chain VP CIO/CFO IT Consultant We know a lot, because we’ve seen a lot.

Are you thinking about cybersecurity the WRONG WAY?

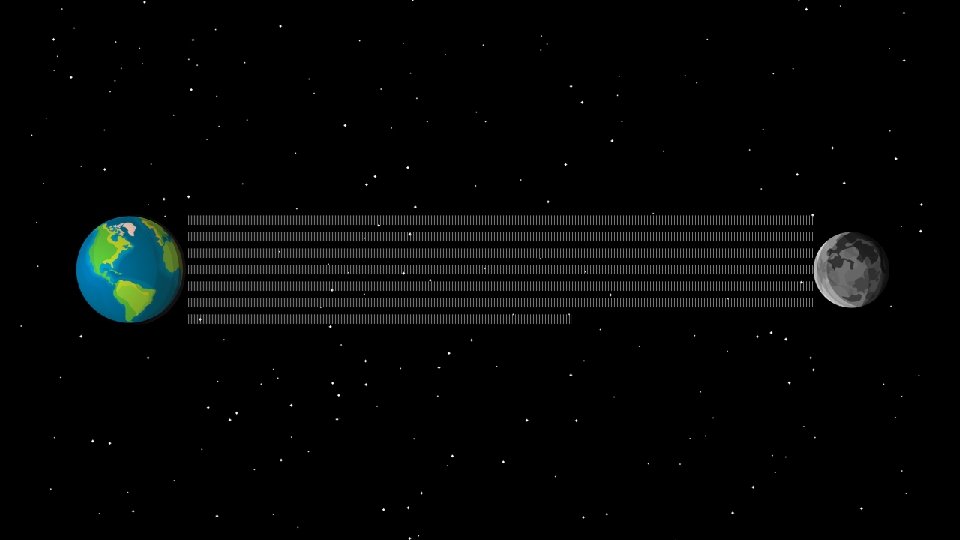
Data is the NEW OIL.
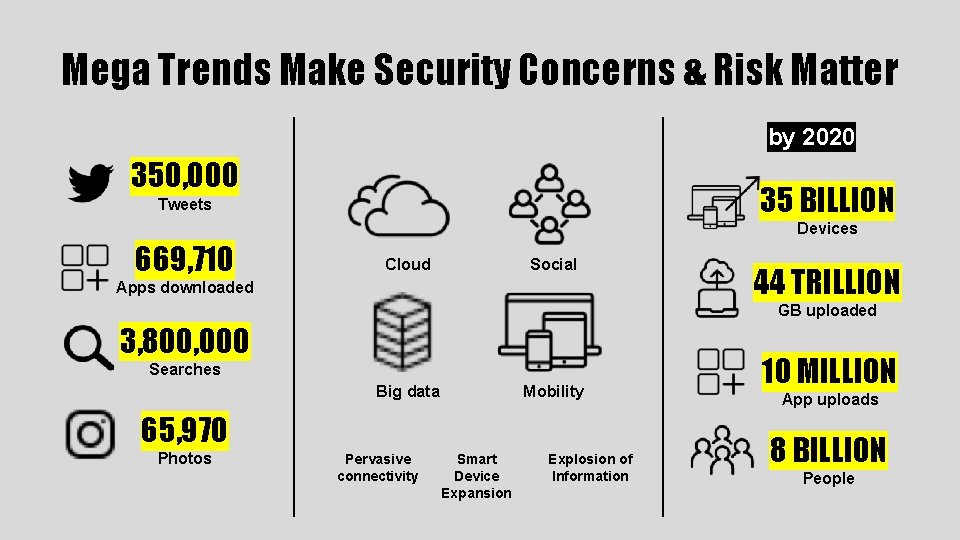
Mega Trends Make Security Concerns & Risk Matter by 2020 350, 000 35 BILLION Tweets Devices 669, 710 Cloud Social Apps downloaded 44 TRILLION GB uploaded 3, 800, 000 Searches Big data Mobility 65, 970 Photos Pervasive connectivity Smart Device Expansion Explosion of Information 10 MILLION App uploads 8 BILLION People
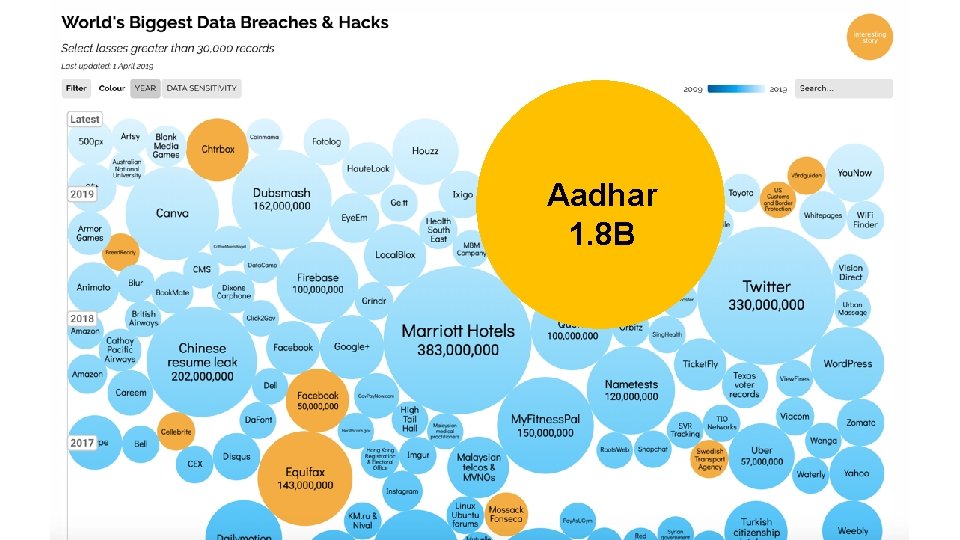
Aadhar 1. 8 B

191 days

69 days

>$1, 000 30 days vs more than 30 days

>200, 000 Computers 150 Countries $4, 000, 000



THREAT VECTORS BRUTE FORCE RANSOMWARE CREDENTIAL THEFT SOCIAL ENGINEERING/ PHISHING WEB DRIVE-BY
EVERY ENDPOINT… IS AN ENTRY POINT.

Employer And Employee Owned Devices
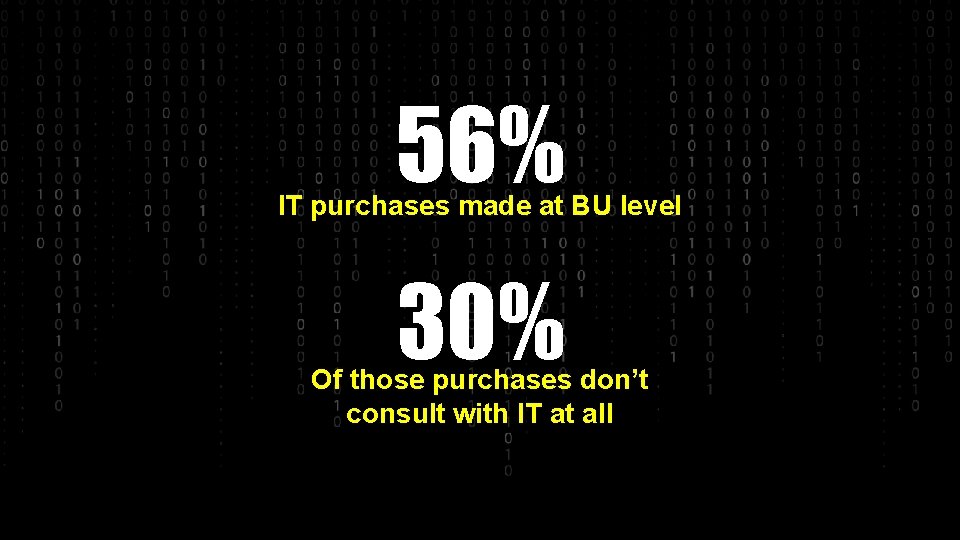
56% IT purchases made at BU level 30% Of those purchases don’t consult with IT at all
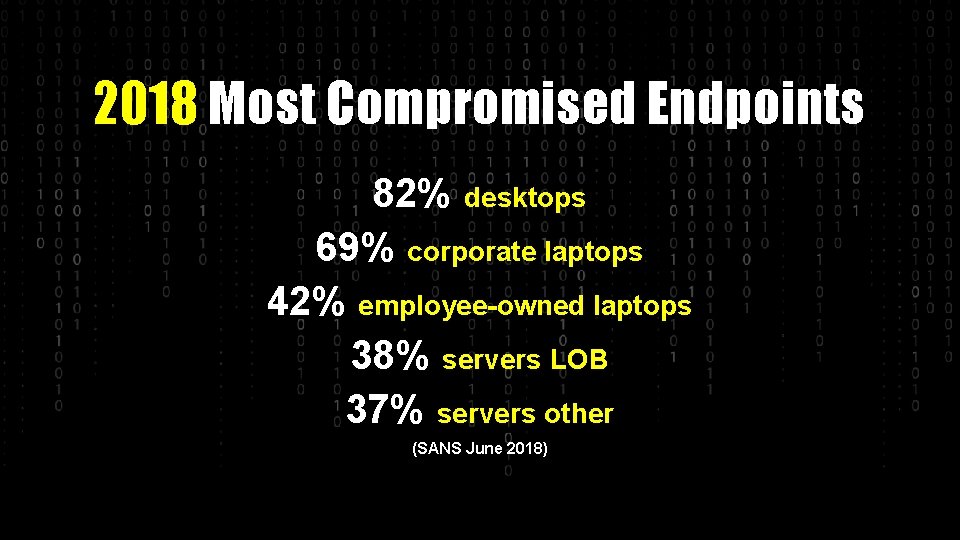
2018 Most Compromised Endpoints 82% desktops 69% corporate laptops 42% employee-owned laptops 38% servers LOB 37% servers other (SANS June 2018)

90% 75% 50% 25% Yikes!

OK – Good – Better – Best The 99% Solution

430 AIRCRAFT WOULD FALL
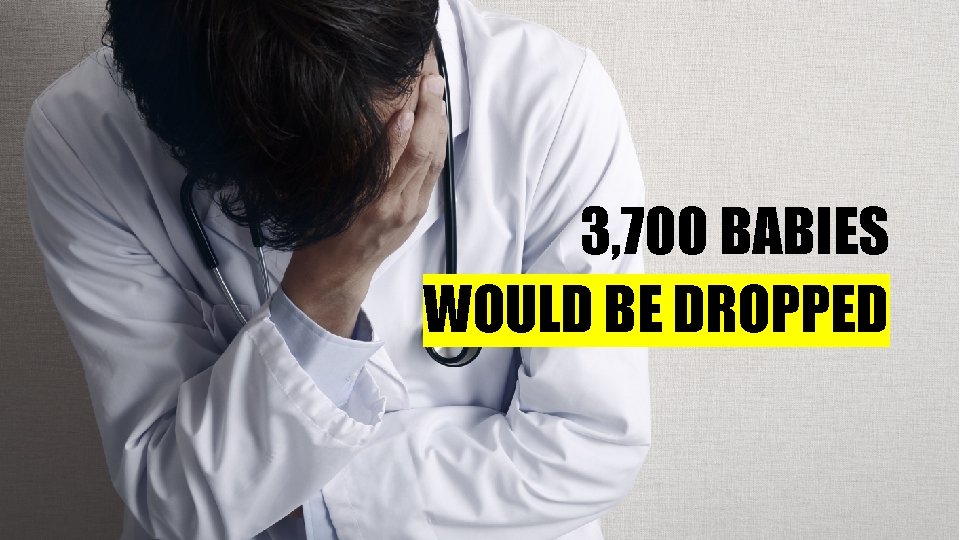
3, 700 BABIES WOULD BE DROPPED

BETTER SECURITY = LESS PAIN
STRATEGY
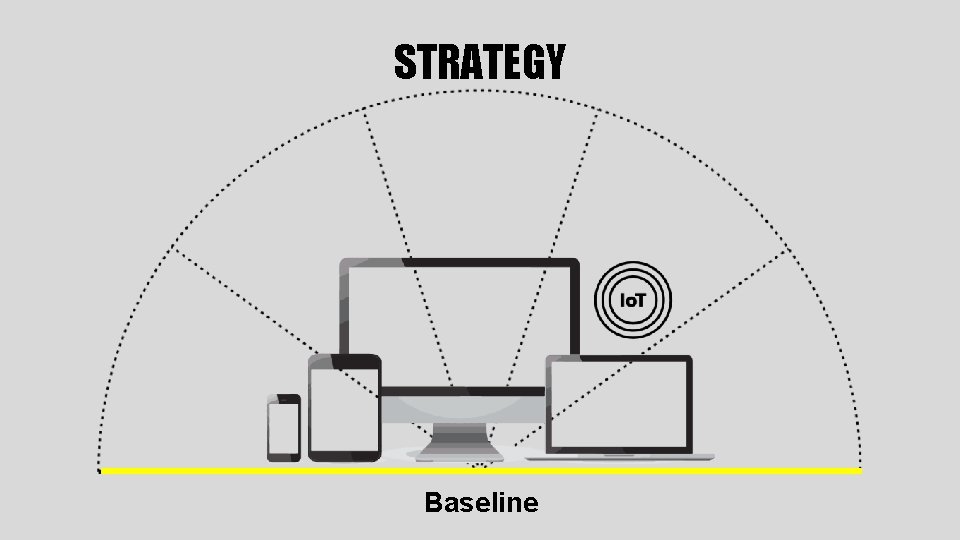
STRATEGY Baseline
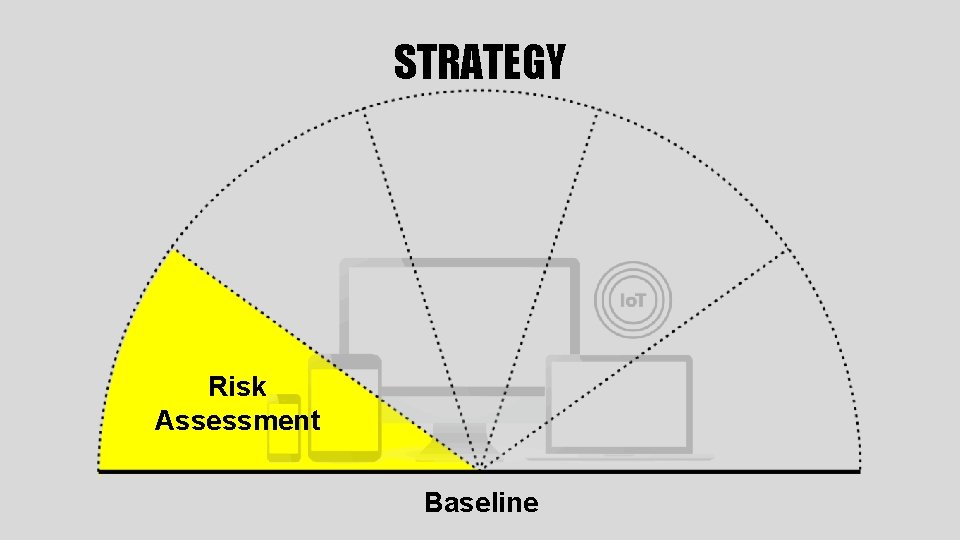
STRATEGY Risk Assessment Baseline
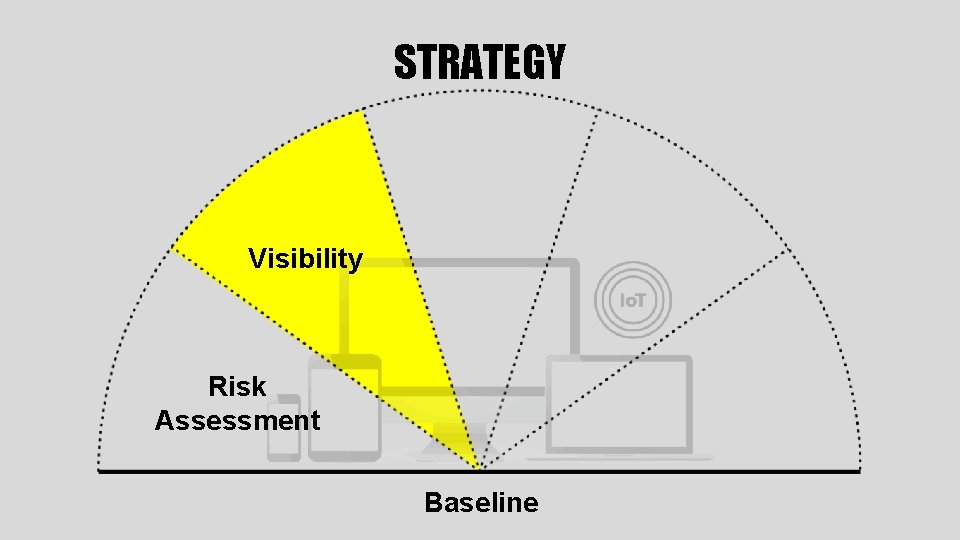
STRATEGY Visibility Risk Assessment Baseline
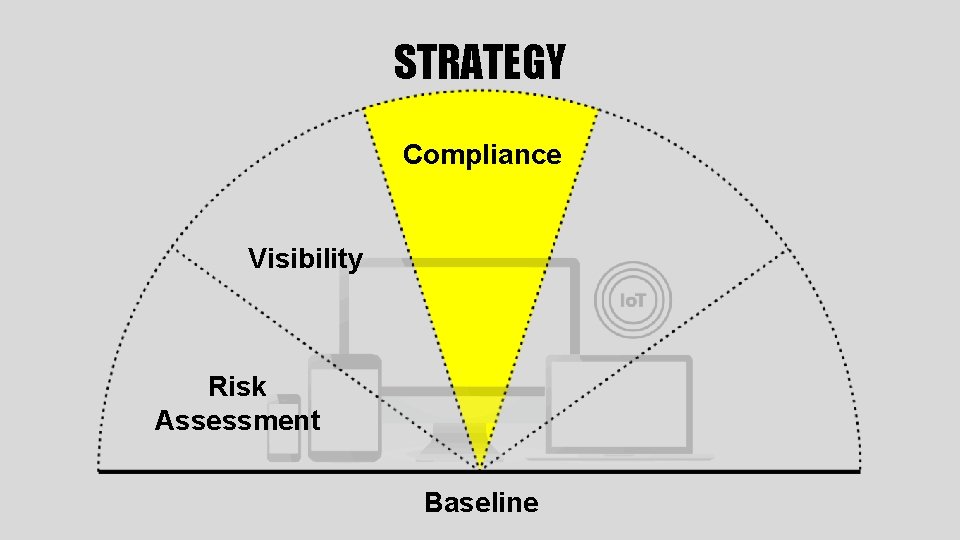
STRATEGY Compliance Visibility Risk Assessment Baseline
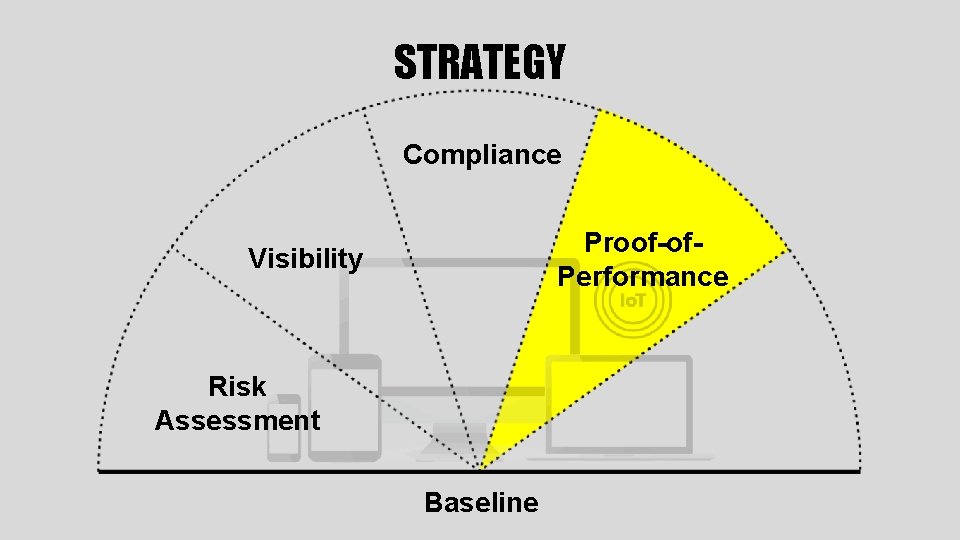
STRATEGY Compliance Proof-of. Performance Visibility Risk Assessment Baseline
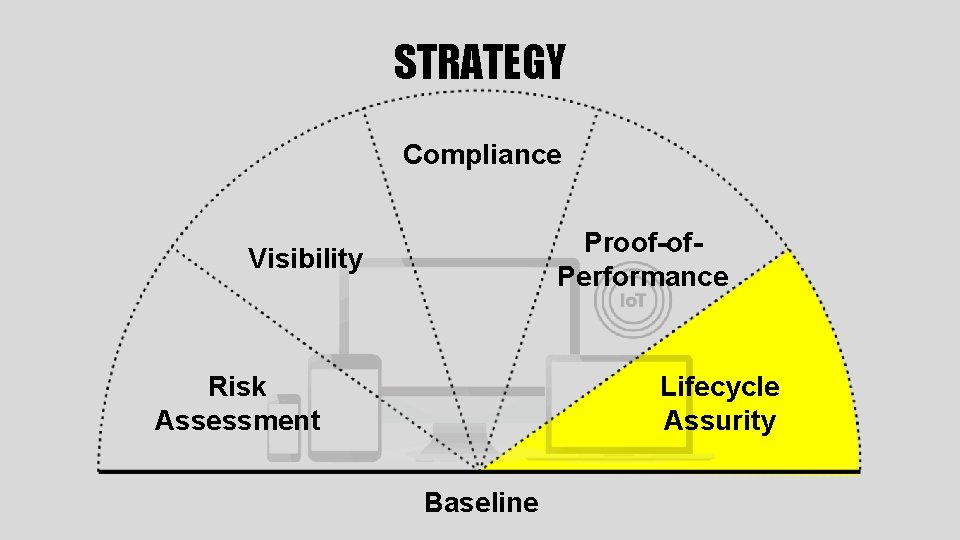
STRATEGY Compliance Proof-of. Performance Visibility Risk Assessment Lifecycle Assurity Baseline



SEE. MEASURE. IMPROVE.
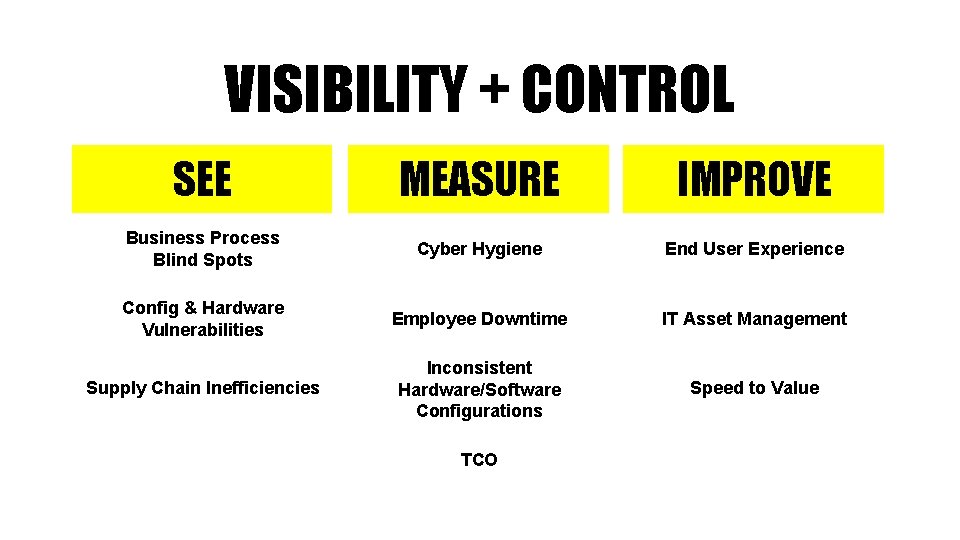
VISIBILITY + CONTROL SEE MEASURE IMPROVE Business Process Blind Spots Cyber Hygiene End User Experience Config & Hardware Vulnerabilities Employee Downtime IT Asset Management Supply Chain Inefficiencies Inconsistent Hardware/Software Configurations Speed to Value TCO

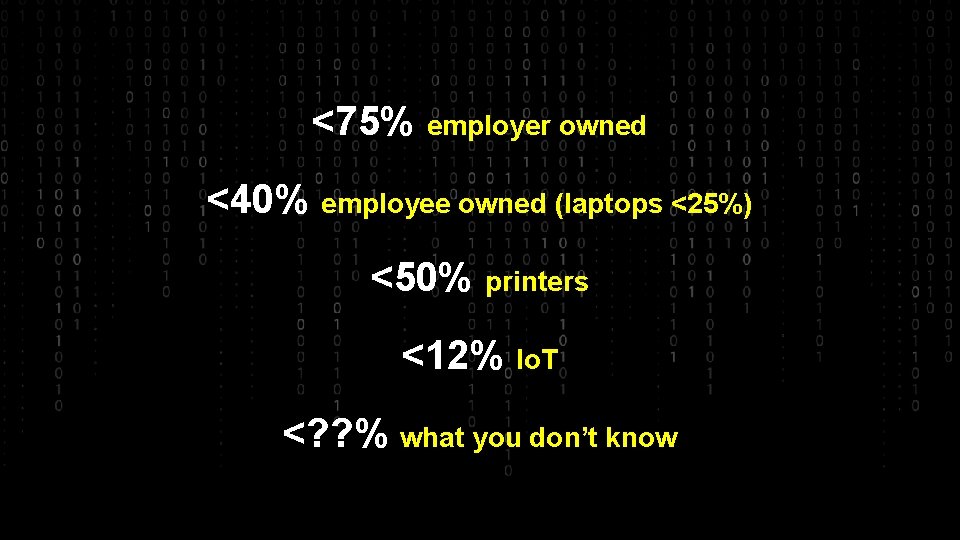
<75% employer owned <40% employee owned (laptops <25%) <50% printers <12% Io. T <? ? % what you don’t know
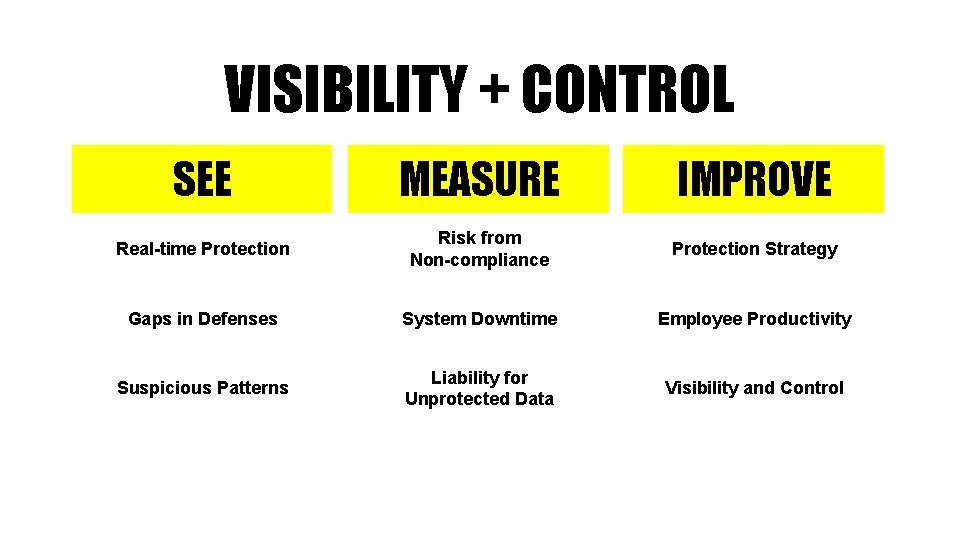
VISIBILITY + CONTROL SEE MEASURE IMPROVE Real-time Protection Risk from Non-compliance Protection Strategy Gaps in Defenses System Downtime Employee Productivity Suspicious Patterns Liability for Unprotected Data Visibility and Control
VISIBILITY + CONTROL SEE Global Program in Real-time Proof of Performance
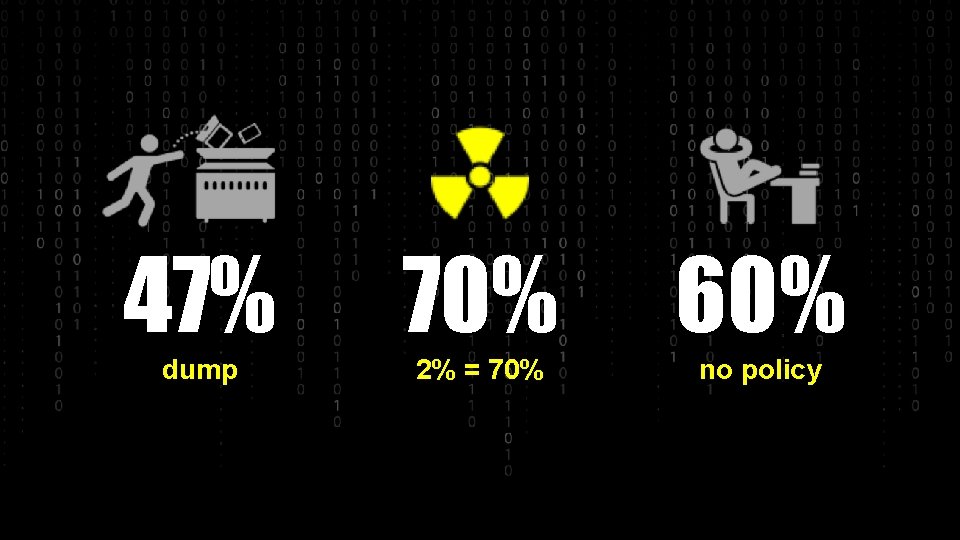
47% 70% 60% dump 2% = 70% no policy
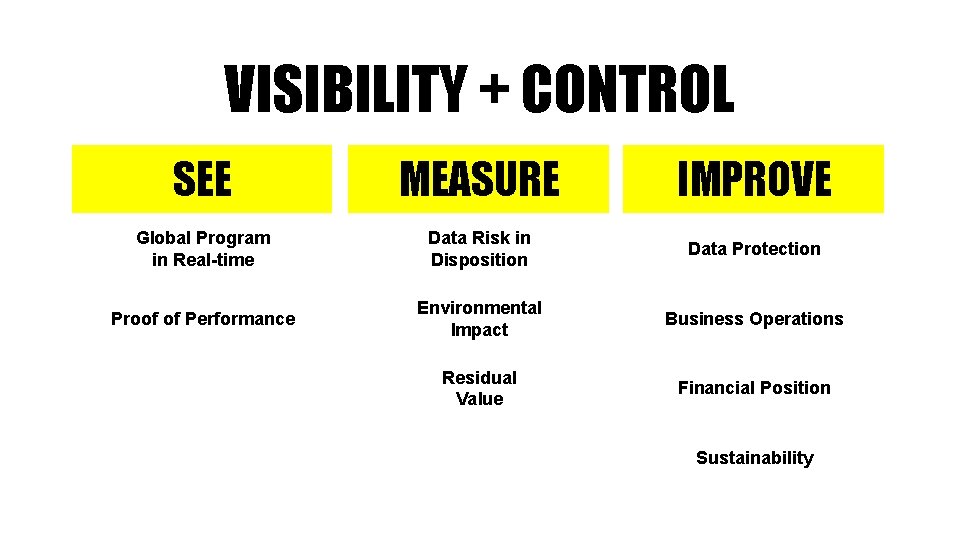
VISIBILITY + CONTROL SEE MEASURE IMPROVE Global Program in Real-time Data Risk in Disposition Data Protection Proof of Performance Environmental Impact Business Operations Residual Value Financial Position Sustainability
Completeness of Vision Ability to Execute
MY CYBER MATURITY SCORE 1 Do you provide proof of performance to deliver hardened endpoints?

MY CYBER MATURITY SCORE 2 Do you have a data protection strategy with centralized control?
MY CYBER MATURITY SCORE 3 Do you have visibility to all locations where sensitive data resides?
MY CYBER MATURITY SCORE 4 Can you perform risk data discovery for PII, PCI, HIPPA?
MY CYBER MATURITY SCORE 5 Do you have a security baseline and measure for drift?
MY CYBER MATURITY SCORE 6 Do you have a discipline to measure and remediate data risk due to missed security updates, insecure network configs, and outof-date antivirus?
MY CYBER MATURITY SCORE 7 It’s 10 o’clock – do you know where your devices are and who has access?
MY CYBER MATURITY SCORE 8 Do you have a process to maintain visibility and control through the life-cycle of your devices?
MY CYBER MATURITY SCORE 9 Do you have proof-ofperformance for data destruction at the retirement stage of your devices?
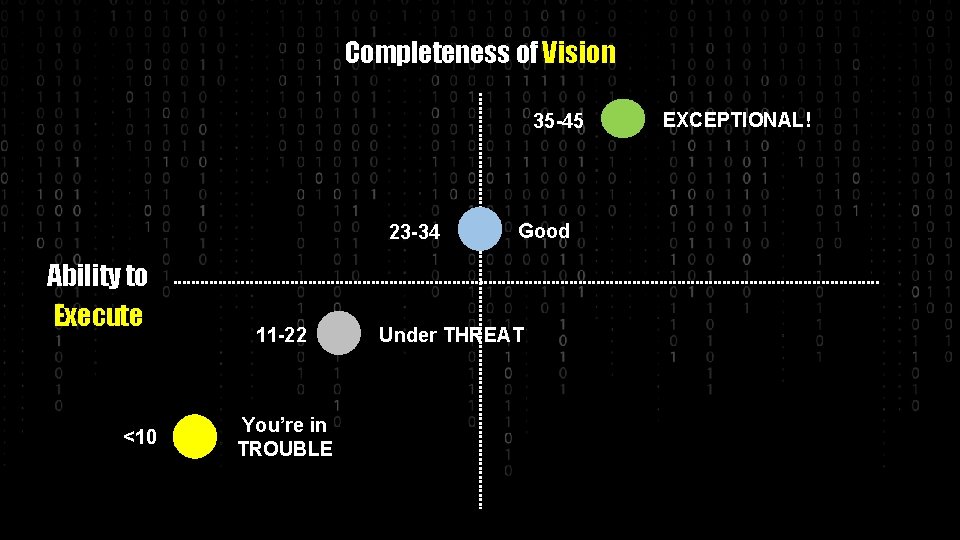
Completeness of Vision 35 -45 23 -34 Ability to Execute <10 11 -22 You’re in TROUBLE Good Under THREAT EXCEPTIONAL!

THANK YOU!

QUESTIONS?
- Slides: 61