Applications of Geometric Programming in Information Security Chris
- Slides: 9
Applications of Geometric Programming in Information Security Chris Ware University of Victoria
Outline Kelly Betting Channel Capacity Reformulated Kelly Purpose What's Next June 27, 2009 Information Security 2
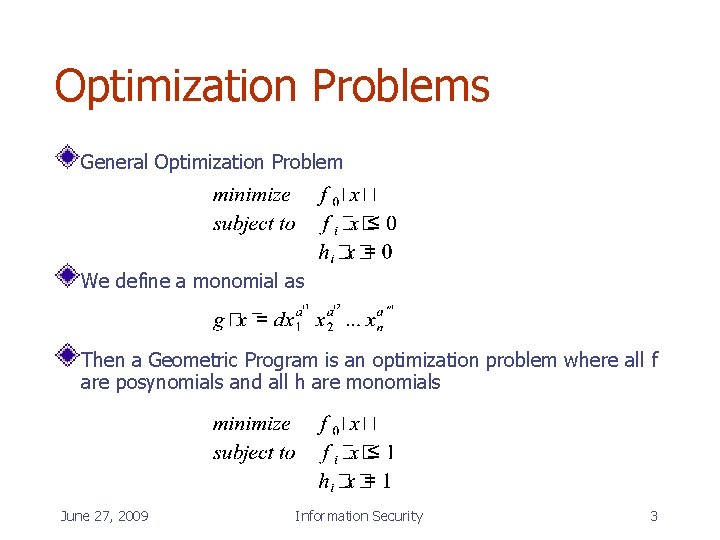
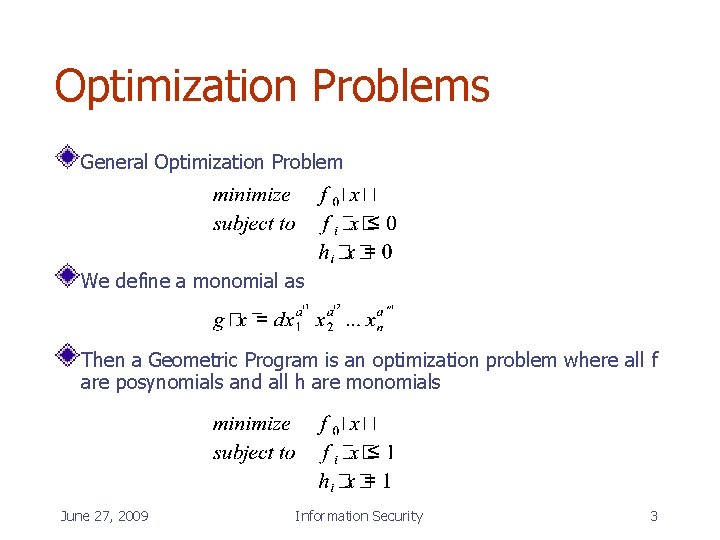
Optimization Problems General Optimization Problem We define a monomial as Then a Geometric Program is an optimization problem where all f are posynomials and all h are monomials June 27, 2009 Information Security 3
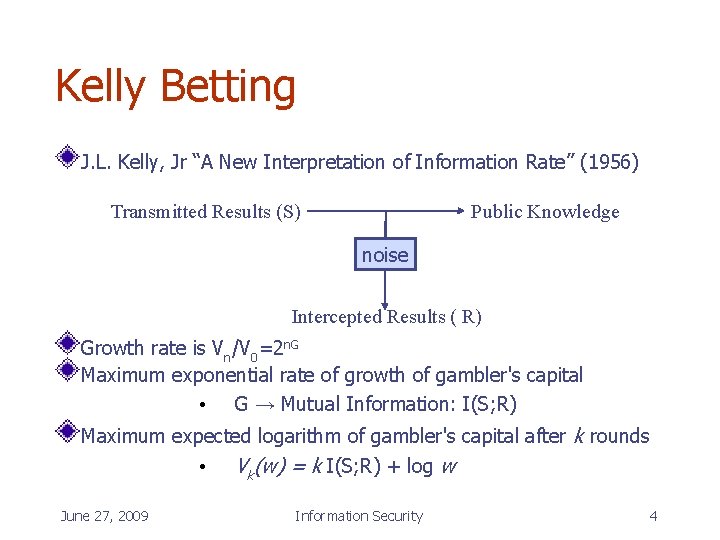
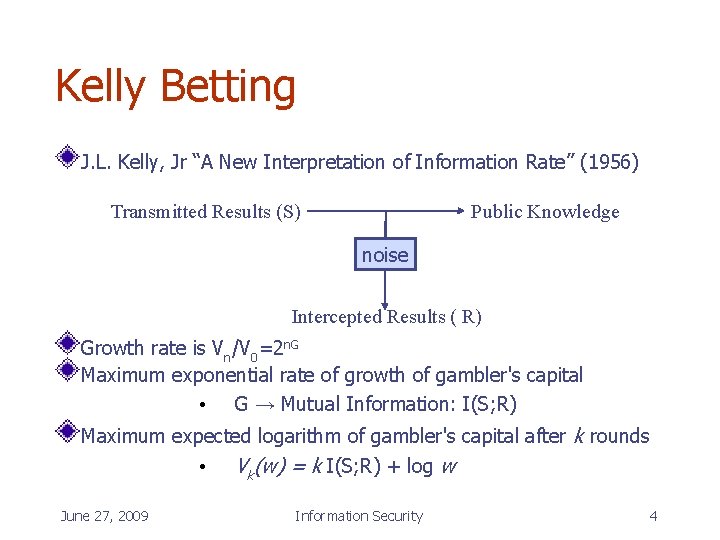
Kelly Betting J. L. Kelly, Jr “A New Interpretation of Information Rate” (1956) Transmitted Results (S) Public Knowledge noise Intercepted Results ( R) Growth rate is Vn/V 0=2 n. G Maximum exponential rate of growth of gambler's capital • G → Mutual Information: I(S; R) Maximum expected logarithm of gambler's capital after k rounds • Vk(w) = k I(S; R) + log w June 27, 2009 Information Security 4
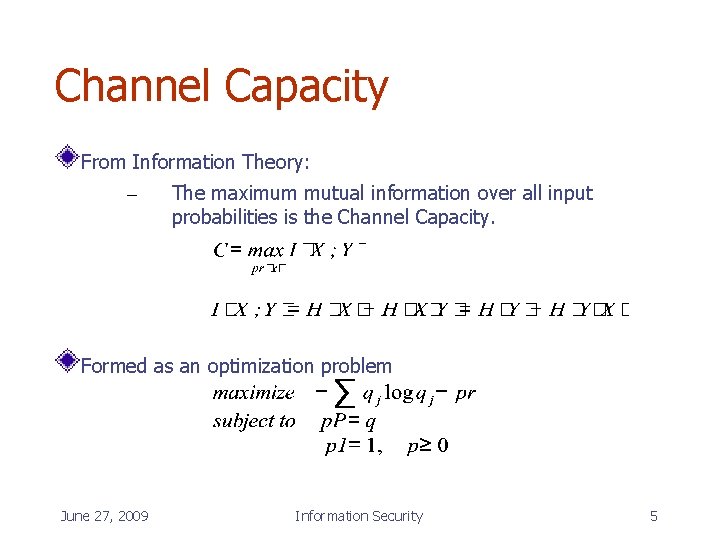
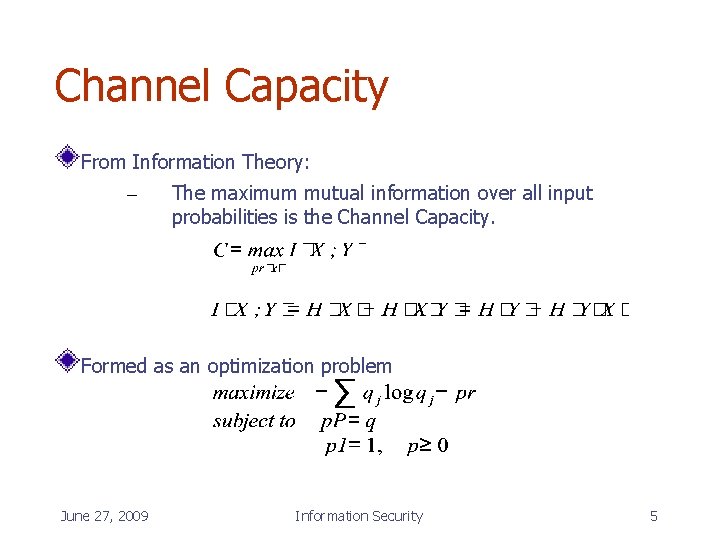
Channel Capacity From Information Theory: – The maximum mutual information over all input probabilities is the Channel Capacity. Formed as an optimization problem June 27, 2009 Information Security 5
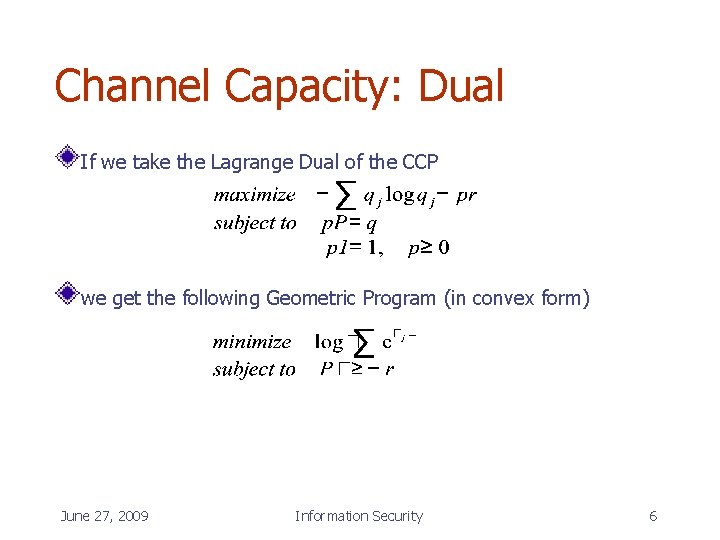
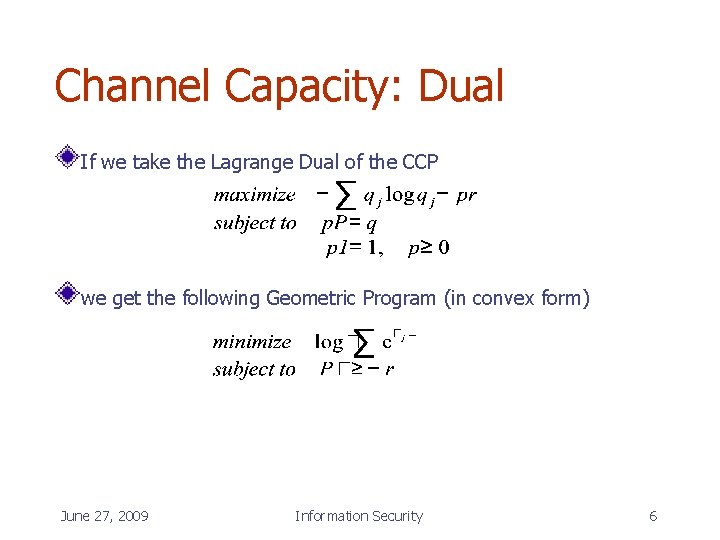
Channel Capacity: Dual If we take the Lagrange Dual of the CCP we get the following Geometric Program (in convex form) June 27, 2009 Information Security 6
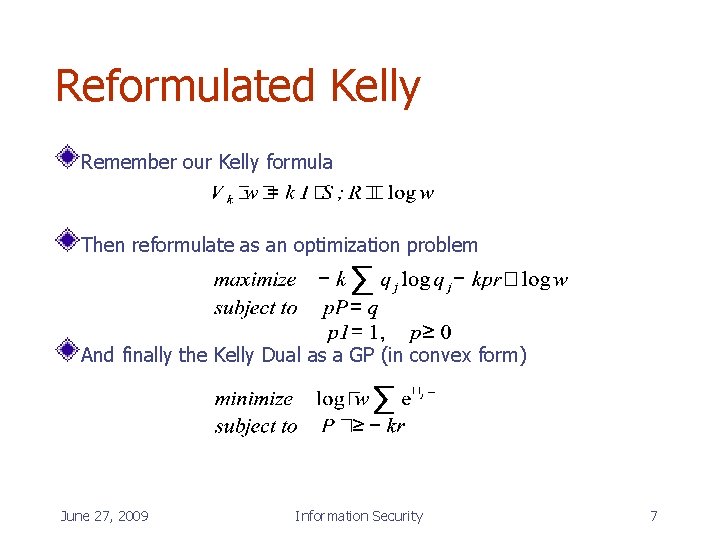
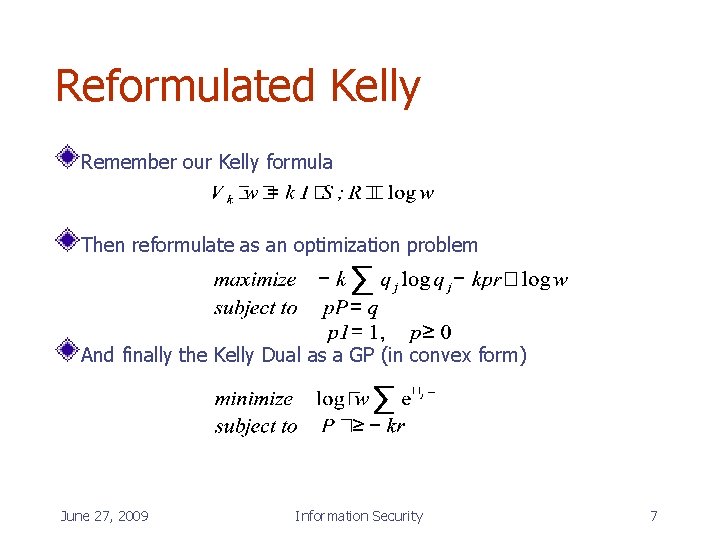
Reformulated Kelly Remember our Kelly formula Then reformulate as an optimization problem And finally the Kelly Dual as a GP (in convex form) June 27, 2009 Information Security 7
Benefits of CCP as a GP Weak Duality: any feasible solution produces an upper bound on channel capacity Strong Duality: the optimal solution is the channel capacity Both primal and dual problems can be simultaneously and efficiently solved through the primal-dual interior point method June 27, 2009 Information Security 8
What's Next Variations on source data distributions – Input costs – Encoding / Noise To create a more general version of Kelly June 27, 2009 Information Security 9