Andes Embedded Processors WWW ANDESTECH COM v Andes
Andes Embedded Processors WWW. ANDESTECH. COM

v. Andes Embedded Processors Page 2 ANDES Confidential
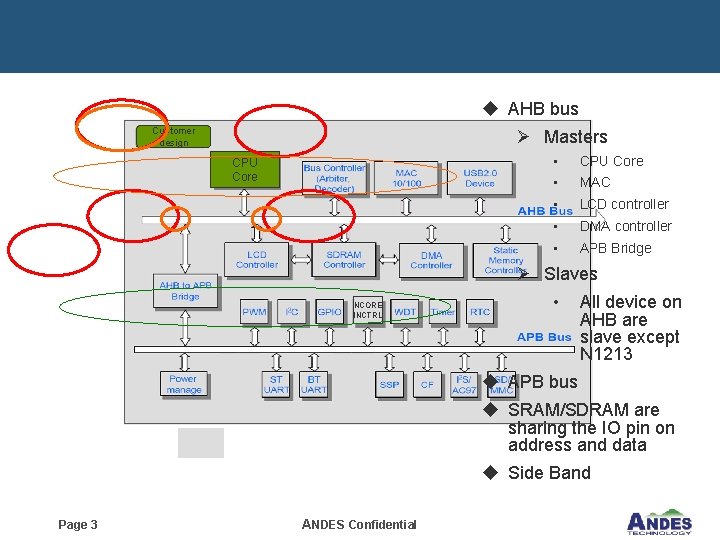
u AHB bus Customer design Ø Masters CPU Core • MAC • LCD controller • DMA controller • APB Bridge Ø Slaves NCORE INCTRL • All device on AHB are slave except N 1213 u APB bus u SRAM/SDRAM are sharing the IO pin on address and data u Side Band Page 3 ANDES Confidential
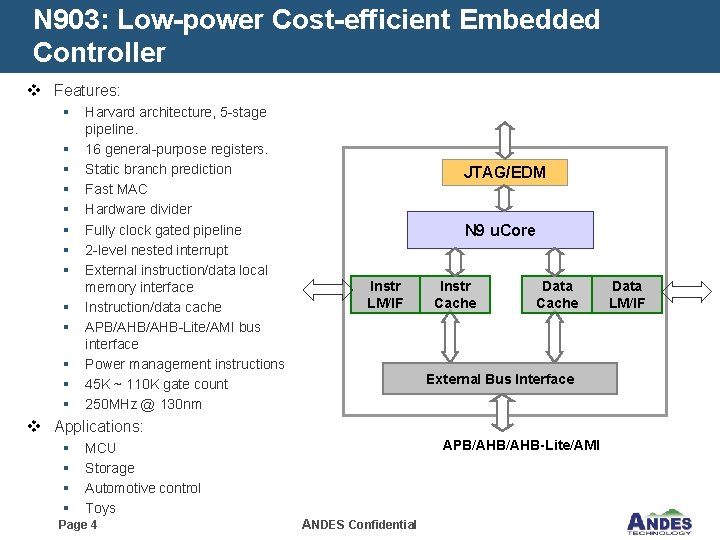
N 903: Low-power Cost-efficient Embedded Controller v Features: § § § § Harvard architecture, 5 -stage pipeline. 16 general-purpose registers. Static branch prediction Fast MAC Hardware divider Fully clock gated pipeline 2 -level nested interrupt External instruction/data local memory interface Instruction/data cache APB/AHB-Lite/AMI bus interface Power management instructions 45 K ~ 110 K gate count 250 MHz @ 130 nm JTAG/EDM N 9 u. Core Instr LM/IF Instr Cache Data Cache External Bus Interface v Applications: § § APB/AHB-Lite/AMI MCU Storage Automotive control Toys Page 4 ANDES Confidential Data LM/IF

N 903 Competition Core’s Features N 903 ARM 7 TDMI Cortex-M 3 Harvard Von Neumann Harvard Pipeline Stages 5 3 3 Instruction Set 16 -/32 -bit mixable Thumb/ARM 16 -/32 -bit mixable 16 16 16 Static None Static 10 24 -42 12 Big and Little APB/AHB/AMI 1 AHB 3 AHB Lite Yes None Yes (external) Architecture General-purpose register # Branch prediction Interrupt latency (Cycle) Data endian support Bus Sleep Mode Vectored interrupt support Yes (internal/external) DMIPS/Mhz 1. 38 0. 95 1. 25 Core Area (mm 2) (TSMC 0. 13 G) *0. 42 0. 26 0. 43/0. 21 Core Power (m. W/MHz) (TSMC 0. 13 G) *0. 06 0. 165/0. 084 Max Frequency (Mhz) (TSMC 0. 13 G) *204 133 135/50 DMIPS (TSMC 0. 13 G) 281. 52 126. 35 168. 75/62. 5 Cost Performance (DMIPS/mm 2) 670. 3 486 393/298 *TSMC free library with max speed synthesis constraint Page 5 ANDES Confidential
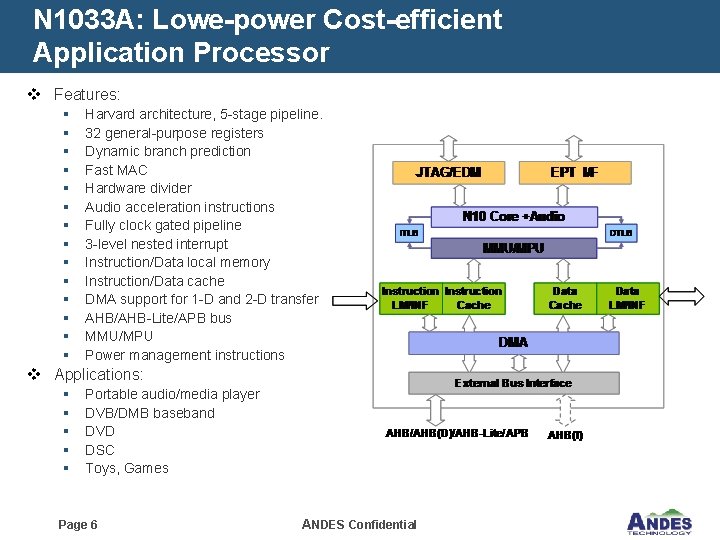
N 1033 A: Lowe-power Cost-efficient Application Processor v Features: § § § § Harvard architecture, 5 -stage pipeline. 32 general-purpose registers Dynamic branch prediction Fast MAC Hardware divider Audio acceleration instructions Fully clock gated pipeline 3 -level nested interrupt Instruction/Data local memory Instruction/Data cache DMA support for 1 -D and 2 -D transfer AHB/AHB-Lite/APB bus MMU/MPU Power management instructions v Applications: § § § Portable audio/media player DVB/DMB baseband DVD DSC Toys, Games Page 6 ANDES Confidential

N 1033 A Competition Core’s Features N 1033 A ARM 926 EJ Pipeline Stages 5 5 Instruction Set 16 -/32 -bit mixable 16 or 32 General-purpose register# 32 16 Dynamic branch prediction 32/64 -Entry BTB No 1 D and 2 D No Physical tag Virtual tag Yes (64 addresses) No 3 No AHB/2 AHB/AHB-Lite/APB 2 AHB > 40 dedicated Few general DSP *280 276/238 1. 6 1. 1 Core Power (m. W/MHz) (TSMC 0. 13 G) *0. 12 0. 36 Core area (mm 2) (TSMC 0. 13 G) *1. 4 1. 61/1. 45 DMIPS (TSMC 0. 13 G) 448 303. 6 Cost Performance (DMIPS/MHz) 320 189 DMA support Cache tag index Vectored interrupt support Nested interruption level Bus Audio DSP instructions Max frequency (Mhz) (TSMC 0. 13 G) Performance (DMIPS/MHz) *TSMC free library with max speed synthesis constraint Page 7 ANDES Confidential

N 1213 – High Performance Application Processor v Features: JTAG/EDM § § EPT I/F N 12 Execution Core § § § DTLB ITLB MMU Instruction Cache LM Data Cache v Applications: § § § DMA External Bus Interface AHB Page 8 Harvard architecture, 8 -stage pipeline. 32 general-purpose registers Dynamic branch prediction. Multiply-add and multiply-subtract instructions. Divide instructions. Instruction/Data local memory. Instruction/Data cache. MMU AHB or HSMP(AXI like) bus Power management instructions HSMP ANDES Confidential Portable media player MFP Networking Gateway/Router Home entertainment Smartphone/Mobile phone
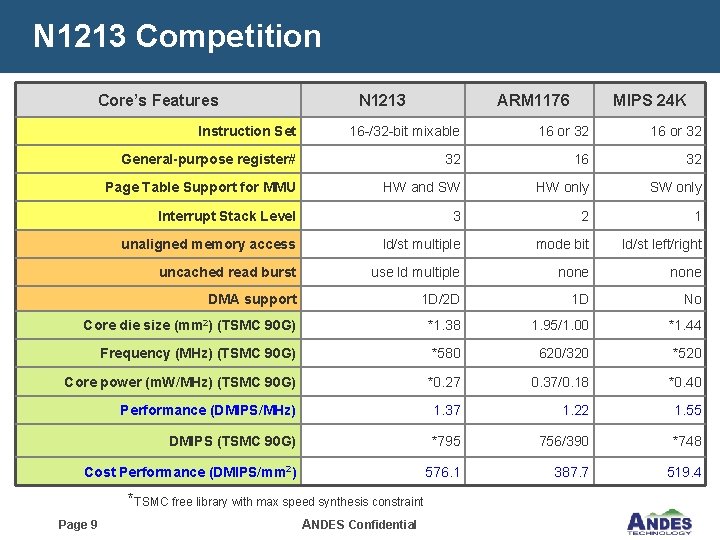
N 1213 Competition Core’s Features N 1213 ARM 1176 MIPS 24 K Instruction Set 16 -/32 -bit mixable 16 or 32 General-purpose register# 32 16 32 Page Table Support for MMU HW and SW HW only SW only Interrupt Stack Level 3 2 1 unaligned memory access ld/st multiple mode bit ld/st left/right uncached read burst use ld multiple none DMA support 1 D/2 D 1 D No Core die size (mm 2) (TSMC 90 G) *1. 38 1. 95/1. 00 *1. 44 Frequency (MHz) (TSMC 90 G) *580 620/320 *520 Core power (m. W/MHz) (TSMC 90 G) *0. 27 0. 37/0. 18 *0. 40 Performance (DMIPS/MHz) 1. 37 1. 22 1. 55 DMIPS (TSMC 90 G) *795 756/390 *748 Cost Performance (DMIPS/mm 2) 576. 1 387. 7 519. 4 *TSMC free library with max speed synthesis constraint Page 9 ANDES Confidential
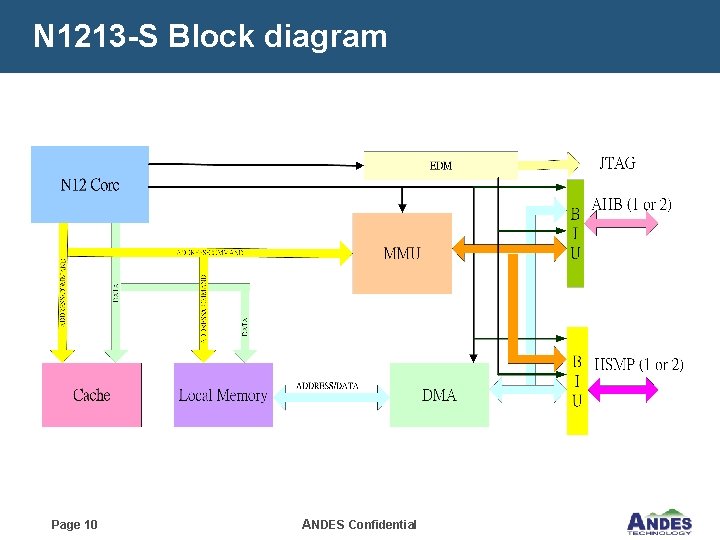
N 1213 -S Block diagram Page 10 ANDES Confidential
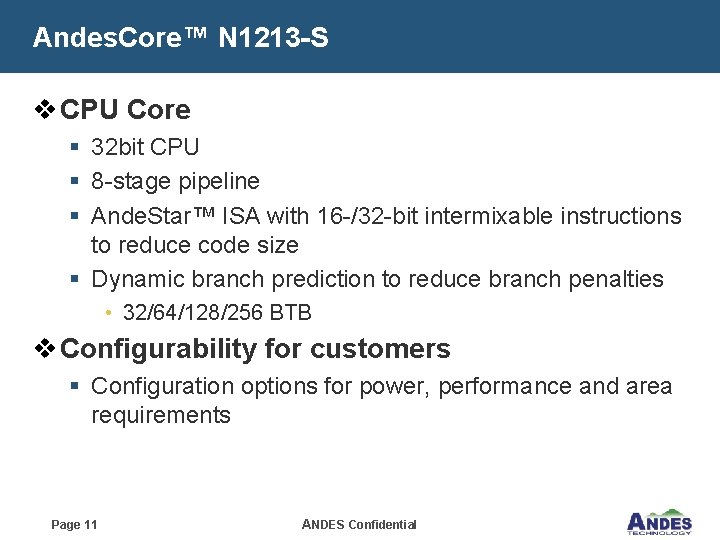
Andes. Core™ N 1213 -S v CPU Core § 32 bit CPU § 8 -stage pipeline § Ande. Star™ ISA with 16 -/32 -bit intermixable instructions to reduce code size § Dynamic branch prediction to reduce branch penalties • 32/64/128/256 BTB v Configurability for customers § Configuration options for power, performance and area requirements Page 11 ANDES Confidential
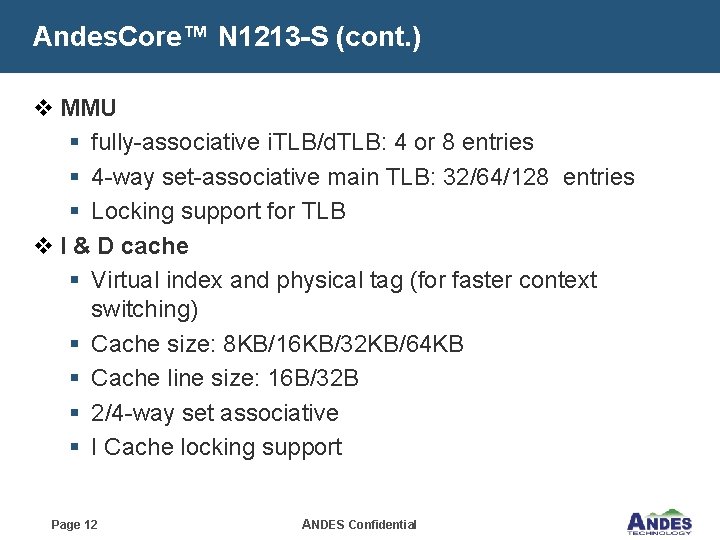
Andes. Core™ N 1213 -S (cont. ) v MMU § fully-associative i. TLB/d. TLB: 4 or 8 entries § 4 -way set-associative main TLB: 32/64/128 entries § Locking support for TLB v I & D cache § Virtual index and physical tag (for faster context switching) § Cache size: 8 KB/16 KB/32 KB/64 KB § Cache line size: 16 B/32 B § 2/4 -way set associative § I Cache locking support Page 12 ANDES Confidential

Andes. Core™ N 1213 -S (cont. ) v I & D Local memory § wide range support for internal /external local memory • 4 KB~1024 KB § Provide fixed access latencies for internal local memory § Double buffer mode for D local memory § Optional external local memory interface v Bus § Synchronous/Asynchronous AHB • 1 or 2 port configuration § Synchronous HSMP • AXI like • 1 or 2 port configuration Page 13 ANDES Confidential

Andes. Core™ N 1213 -S (cont. ) v For performance § Improved memory accesses: • 1 D/2 D DMA, load/store multiple § Efficient synchronization without locking the whole bus • Load lock, store conditional instructions § Vectored interrupt to improve real-time performance • 6 interrupt signals § MMU • Optional HW page table walker • TLB management instructions v For flexibility § § § Memory-mapped IO space JTAG-based debug support Optional embedded program trace interface Performance monitors for performance tuning Bi-endian modes to support flexible data input Page 14 ANDES Confidential
Andes. Core™ N 1213 -S (cont. ) v For power Management § § Clock-gated Low-power mode support instructions Redundant memory access reduction Many CPU/bus frequency ratio support Page 15 ANDES Confidential
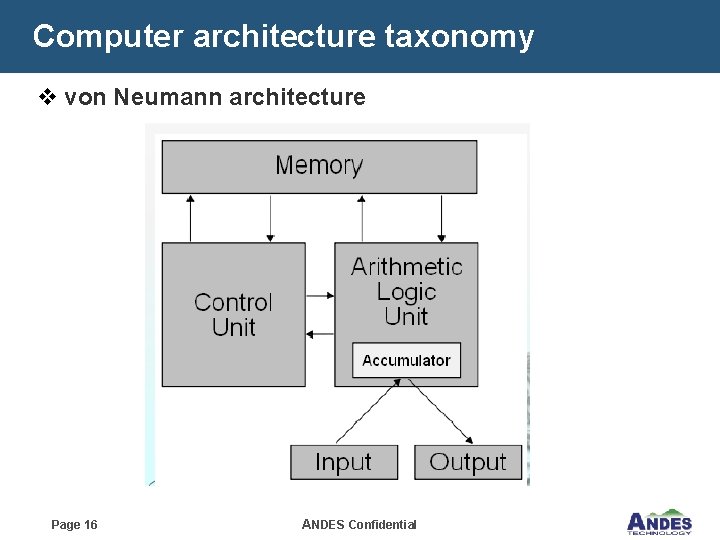
Computer architecture taxonomy v von Neumann architecture Page 16 ANDES Confidential
Computer architecture taxonomy v von Neumann architecture § Features of each: • Execution in multiple cycles § Serial fetch instructions & data § Single memory structure • Can get data/program mixed • Data/instructions same size § Examples, von Neumann: PCs (Intel 80 x 86/Pentium, Motorola 68000, Mot 68 xx u. C families Page 17 ANDES Confidential
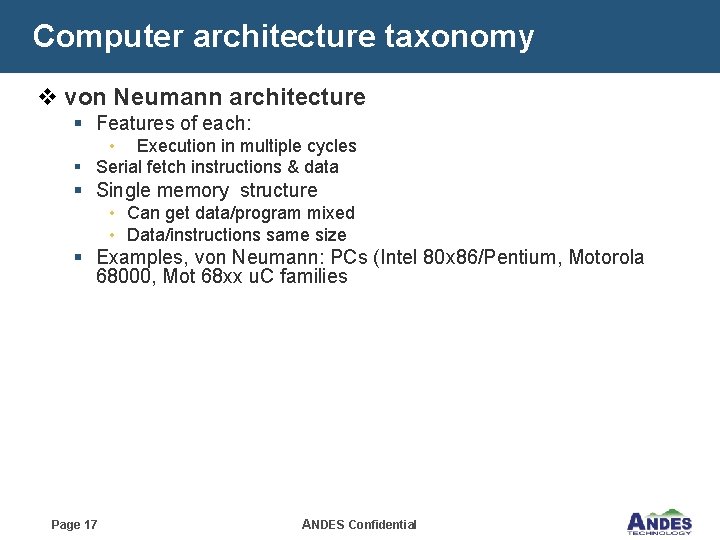
Computer architecture taxonomy (cont. ) v Harvard architecture address data memory data address program memory Page 18 data ANDES Confidential PC CPU
Computer architecture taxonomy (cont. ) v Harvard architecture § Features of each: Execution in 1 cycle § Parallel fetch instructions & data § More Complex H/W • Instructions and data always separate • Different code/data path widths (E. G. 14 bit instructions, 8 bit data) § Harvard: 8051, Microchip PIC families, Atmel AVR, Ande. Score Page 19 ANDES Confidential
Architectures: CISC vs. RISC v. CISC - Complex Instruction Set Computers: § § § Emphasis on hardware Includes multi-clock complex instructions Memory-to-memory Sophisticated arithmetic (multiply, divide, trigonometry etc. ). Special instructions are added to optimize performance with particular compilers. Page 20 ANDES Confidential
Architectures: CISC vs. RISC (cont. ) v. RISC - Reduced Instruction Set Computers: § § § A very small set of primitive instructions Fixed instruction format Emphasis on software All instructions execute in one cycle (Fast!). Register to register (except Load/Store instructions) Pipline architecture Page 21 ANDES Confidential
Pipeline Overview Page 22 ANDES Confidential
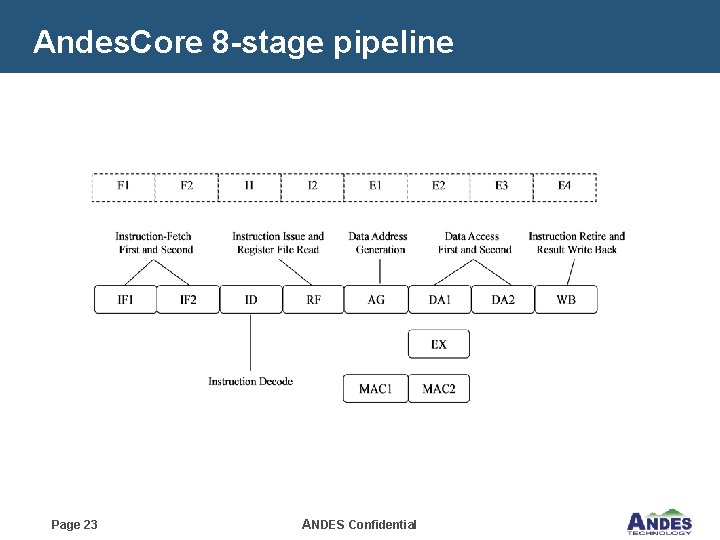
Andes. Core 8 -stage pipeline Page 23 ANDES Confidential

Instruction Fetch Stage v F 1 – Instruction Fetch First § § § Instruction Tag/Data Arrays ITLB Address Translation Branch Target Buffer Prediction v F 2 – Instruction Fetch Second § § § IF 1 Instruction Cache Hit Detection Cache Way Selection Instruction Alignment IF 2 ID RF AG DA 1 EX MAC 1 Page 24 MAC 2 ANDES Confidential DA 2 WB

Instruction Issue Stage v I 1 – Instruction Issue First / Instruction Decode § § 32/16 -Bit Instruction Decode Return Address Stack prediction v I 2 – Instruction Issue Second / Register File Access § § IF 1 Instruction Issue Logic Register File Access IF 2 ID RF AG DA 1 EX MAC 1 Page 25 MAC 2 ANDES Confidential DA 2 WB
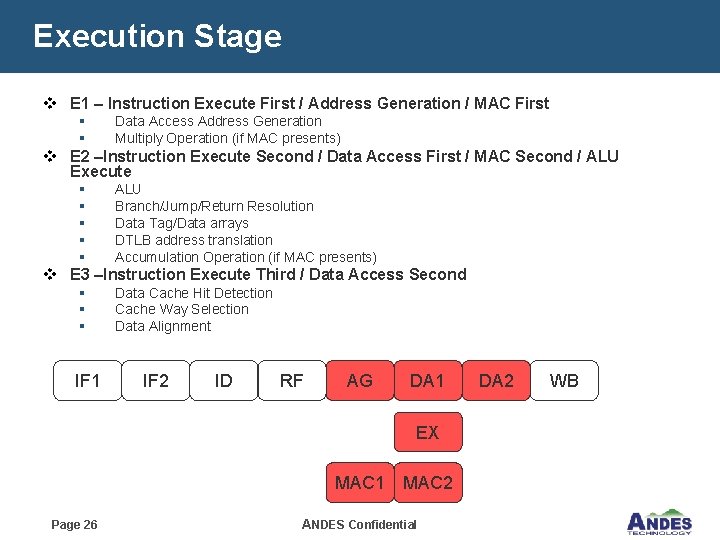
Execution Stage v E 1 – Instruction Execute First / Address Generation / MAC First § § Data Access Address Generation Multiply Operation (if MAC presents) v E 2 –Instruction Execute Second / Data Access First / MAC Second / ALU Execute § § § ALU Branch/Jump/Return Resolution Data Tag/Data arrays DTLB address translation Accumulation Operation (if MAC presents) v E 3 –Instruction Execute Third / Data Access Second § § § IF 1 Data Cache Hit Detection Cache Way Selection Data Alignment IF 2 ID RF AG DA 1 EX MAC 1 Page 26 MAC 2 ANDES Confidential DA 2 WB
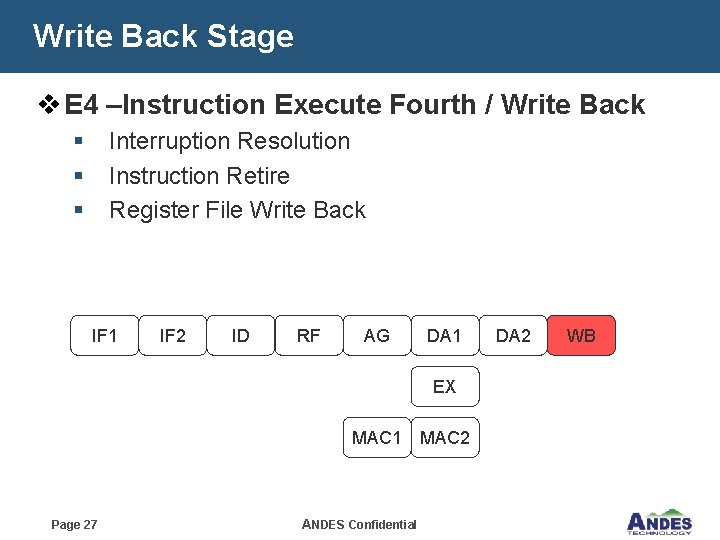
Write Back Stage v E 4 –Instruction Execute Fourth / Write Back § § § Interruption Resolution Instruction Retire Register File Write Back IF 1 IF 2 ID RF AG DA 1 EX MAC 1 Page 27 ANDES Confidential MAC 2 DA 2 WB
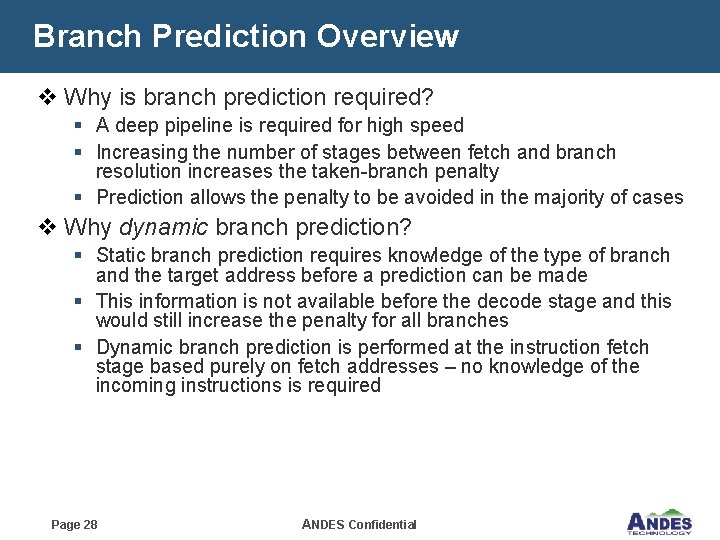
Branch Prediction Overview v Why is branch prediction required? § A deep pipeline is required for high speed § Increasing the number of stages between fetch and branch resolution increases the taken-branch penalty § Prediction allows the penalty to be avoided in the majority of cases v Why dynamic branch prediction? § Static branch prediction requires knowledge of the type of branch and the target address before a prediction can be made § This information is not available before the decode stage and this would still increase the penalty for all branches § Dynamic branch prediction is performed at the instruction fetch stage based purely on fetch addresses – no knowledge of the incoming instructions is required Page 28 ANDES Confidential
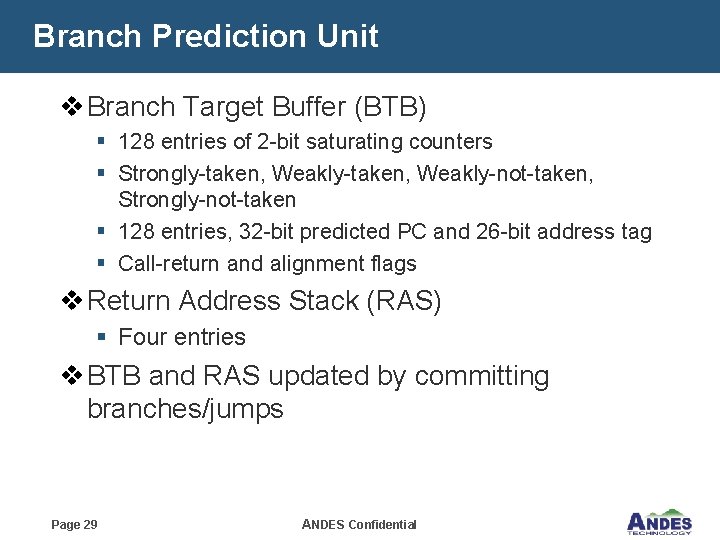
Branch Prediction Unit v Branch Target Buffer (BTB) § 128 entries of 2 -bit saturating counters § Strongly-taken, Weakly-not-taken, Strongly-not-taken § 128 entries, 32 -bit predicted PC and 26 -bit address tag § Call-return and alignment flags v Return Address Stack (RAS) § Four entries v BTB and RAS updated by committing branches/jumps Page 29 ANDES Confidential

BTB Instruction Prediction v BTB predictions are performed based on the previous PC instead of the actual instruction decoding information, BTB may make the following two mistakes § Wrongly predicts the non-branch/jump instructions as branch/jump instructions § Wrongly predicts the instruction boundary (32 -bit -> 16 -bit) v If these cases are detected, IFU will trigger a BTB instruction misprediction in the I 1 stage and re-start the program sequence from the recovered PC. There will be a 2 -cycle penalty introduced here Page 30 ANDES Confidential
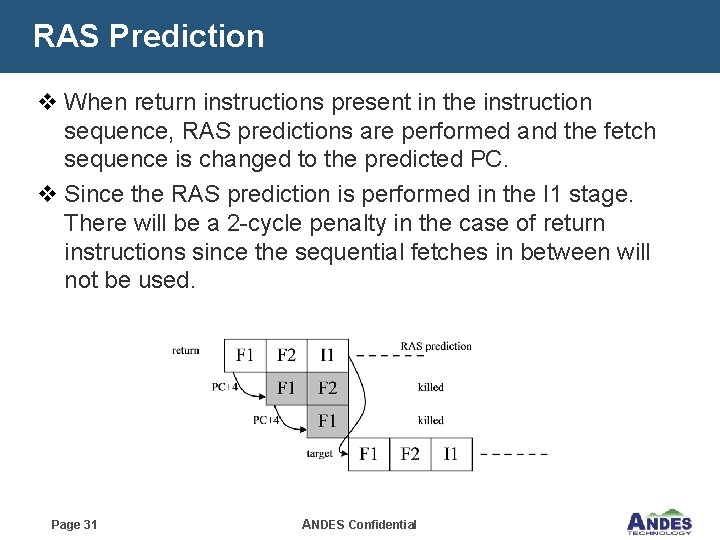
RAS Prediction v When return instructions present in the instruction sequence, RAS predictions are performed and the fetch sequence is changed to the predicted PC. v Since the RAS prediction is performed in the I 1 stage. There will be a 2 -cycle penalty in the case of return instructions since the sequential fetches in between will not be used. Page 31 ANDES Confidential
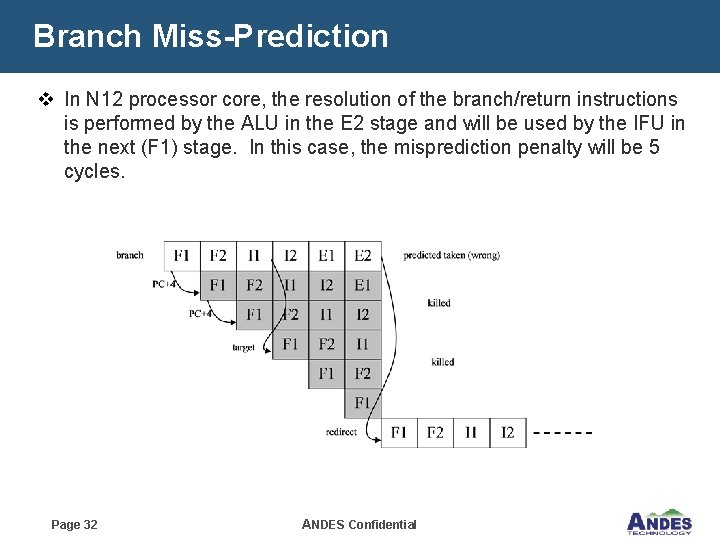
Branch Miss-Prediction v In N 12 processor core, the resolution of the branch/return instructions is performed by the ALU in the E 2 stage and will be used by the IFU in the next (F 1) stage. In this case, the misprediction penalty will be 5 cycles. Page 32 ANDES Confidential
Cache Page 33 ANDES Confidential
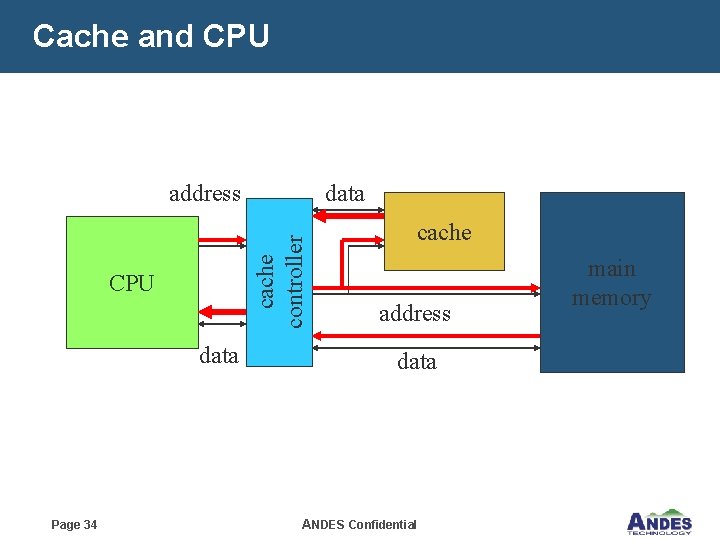
Cache and CPU data Page 34 data cache controller address cache address data ANDES Confidential main memory
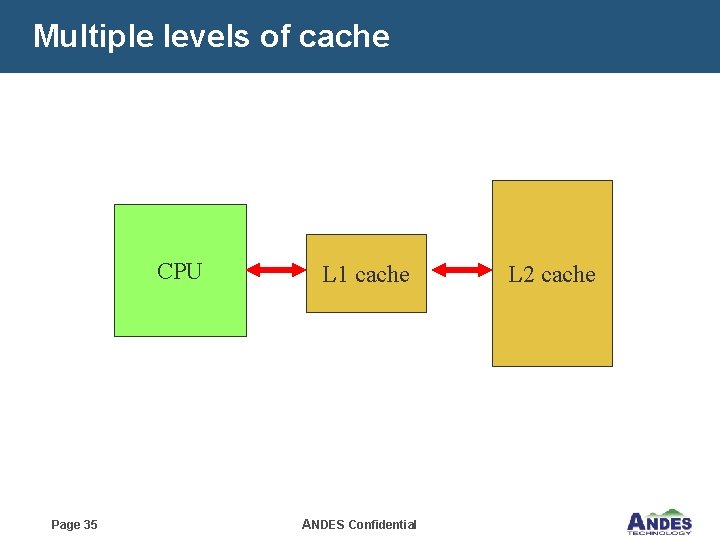
Multiple levels of cache CPU Page 35 L 1 cache ANDES Confidential L 2 cache
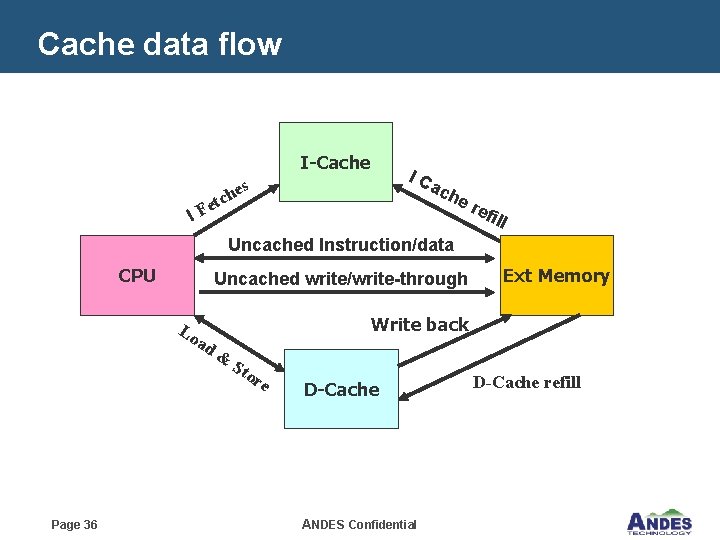
Cache data flow I-Cache IC ac s e h c he r I t Fe efi ll Uncached Instruction/data CPU Uncached write/write-through Lo ad Write back & Sto re Page 36 Ext Memory D-Cache ANDES Confidential D-Cache refill
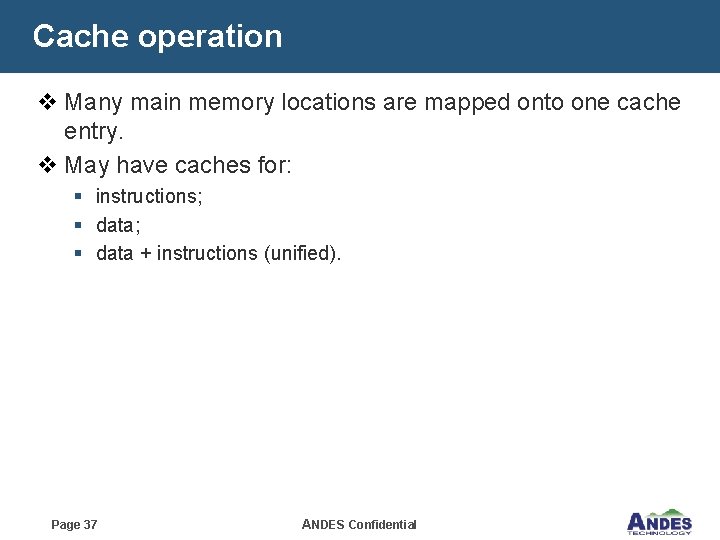
Cache operation v Many main memory locations are mapped onto one cache entry. v May have caches for: § instructions; § data + instructions (unified). Page 37 ANDES Confidential
Replacement policy v Replacement policy: strategy for choosing which cache entry to throw out to make room for a new memory location. v Two popular strategies: § Random. § Least-recently used (LRU). Page 38 ANDES Confidential
Write operations v Write-through: immediately copy write to main memory. v Write-back: write to main memory only when location is removed from cache. Page 39 ANDES Confidential
Improving Cache Performance v Goal: reduce the Average Memory Access Time (AMAT) § AMAT = Hit Time + Miss Rate * Miss Penalty v Approaches § Reduce Hit Time § Reduce or Miss Penalty § Reduce Miss Rate v Notes § There may be conflicting goals § Keep track of clock cycle time, area, and power consumption Page 40 ANDES Confidential

Tuning Cache Parameters v Size: § Must be large enough to fit working set (temporal locality) § If too big, then hit time degrades v Associativity § Need large to avoid conflicts, but 4 -8 way is as good a FA § If too big, then hit time degrades v Block § Need large to exploit spatial locality & reduce tag overhead § If too large, few blocks ⇒ higher misses & miss penalty Configurable architecture allows designers to make the best performance/cost trade-offs Page 41 ANDES Confidential

Cache configuration v Cache line per way § 128/256/512/1024 v Cache ways § 2/4 ways v Cache line size § 16 B/32 B v Cache size combination § 8 KB/16 KB/32 KB/64 KB v Replacement policy § Pseudo LRU (default) • 3 -BIT per cache line § Random • 2 -bit pre cache line Page 42 ANDES Confidential
Cache control— CCTL instruction v I cache control § § § Fill and lock Unlock Invalidate Read/write tag Read/write word data v D cache control § § Invalidate Write back Read/write tag Read/write word data Page 43 ANDES Confidential
Memory Management Units (MMU) Page 44 ANDES Confidential
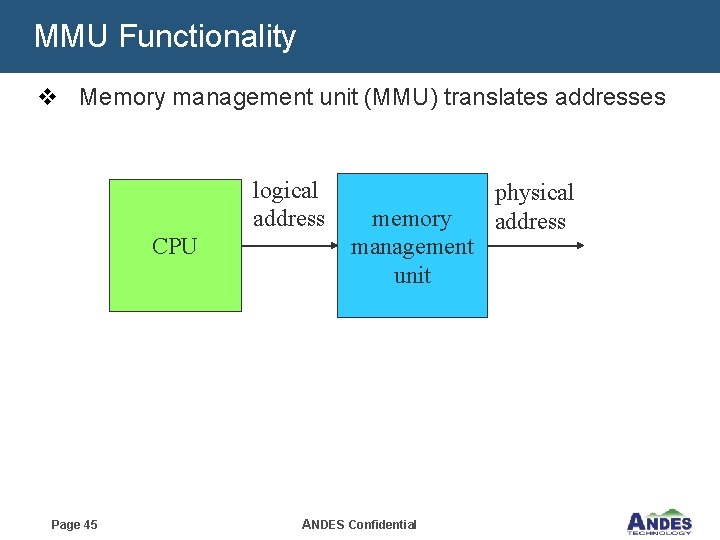
MMU Functionality v Memory management unit (MMU) translates addresses logical address CPU Page 45 memory management unit ANDES Confidential physical address

MMU Architecture IFU M-TLB entry index LSU N(=32) sets k(=4) ways =128 -entry 4/8 I-u. TLB 4/8 D-u. TLB 6 Way number Log 2(N*K)-1 5 4 Set number 0 Log 2(N)-1 M-TLB arbiter M-TLB Tag M-TLB data 32 x 4 M-TLB HPTWK M-TLB Tag Bus interface unit Page 46 ANDES Confidential M-TLB data 0
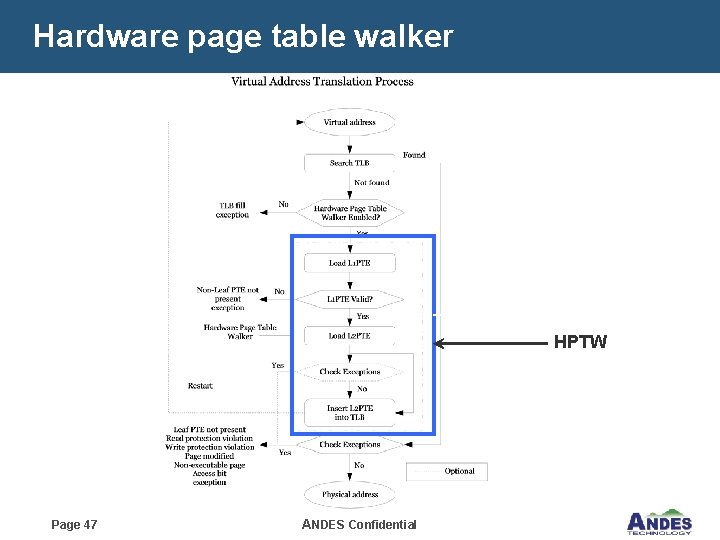
Hardware page table walker HPTW Page 47 ANDES Confidential
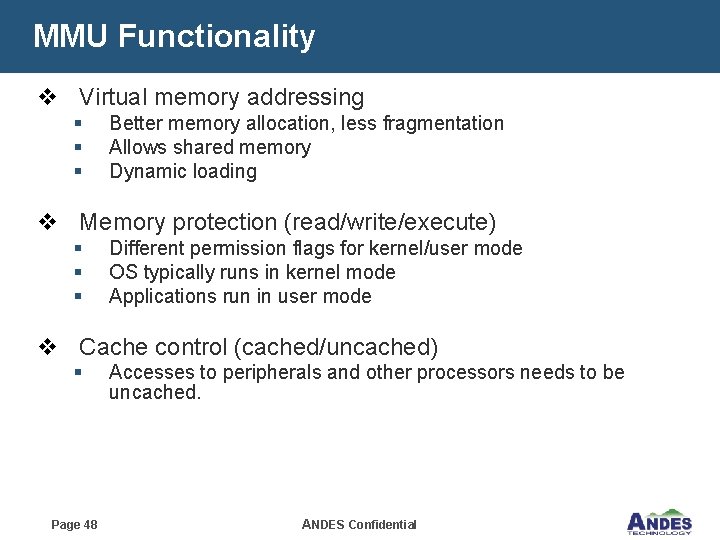
MMU Functionality v Virtual memory addressing § § § Better memory allocation, less fragmentation Allows shared memory Dynamic loading v Memory protection (read/write/execute) § § § Different permission flags for kernel/user mode OS typically runs in kernel mode Applications run in user mode v Cache control (cached/uncached) § Page 48 Accesses to peripherals and other processors needs to be uncached. ANDES Confidential
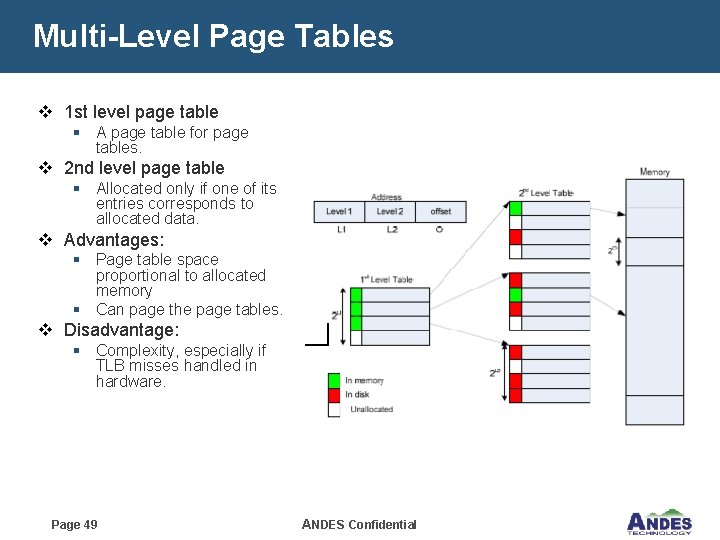
Multi-Level Page Tables v 1 st level page table § A page table for page tables. v 2 nd level page table § Allocated only if one of its entries corresponds to allocated data. v Advantages: § Page table space proportional to allocated memory § Can page the page tables. v Disadvantage: § Complexity, especially if TLB misses handled in hardware. Page 49 ANDES Confidential
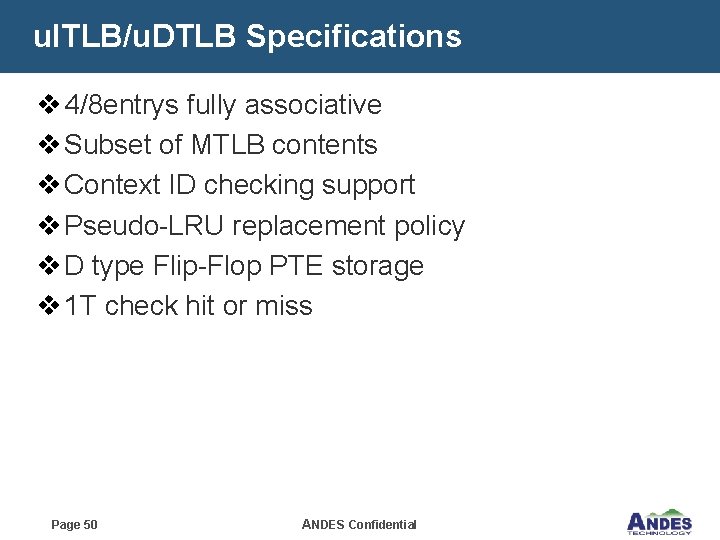
u. ITLB/u. DTLB Specifications v 4/8 entrys fully associative v Subset of MTLB contents v Context ID checking support v Pseudo-LRU replacement policy v D type Flip-Flop PTE storage v 1 T check hit or miss Page 50 ANDES Confidential

MTLB (Main TLB) Specifications v 32/64/128 -entry 4 -way set-associative v Support 4 K/8 K/1 M page VA size v TLB locking support v Pseudo-LRU replacement policy v SRAM base PTE storage Page 51 ANDES Confidential
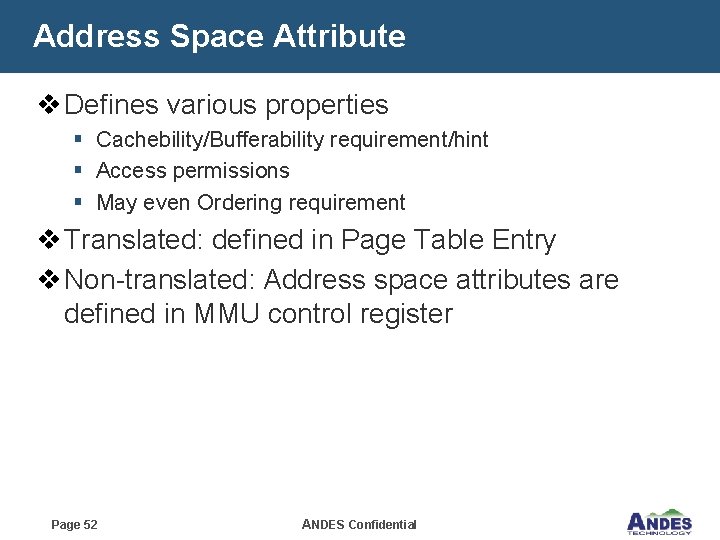
Address Space Attribute v Defines various properties § Cachebility/Bufferability requirement/hint § Access permissions § May even Ordering requirement v Translated: defined in Page Table Entry v Non-translated: Address space attributes are defined in MMU control register Page 52 ANDES Confidential
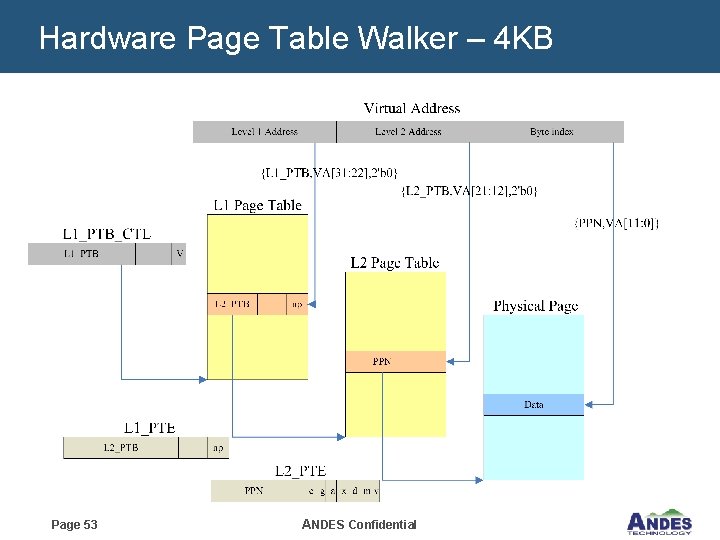
Hardware Page Table Walker – 4 KB Page 53 ANDES Confidential

Hardware Page Table Walker v Responsible for reading TLB entry located in system memory under Main TLB miss condition. v Less flexible than software, handles only one or may be two page table format. But it speeds up the TLB refill time v 2 Level address for looking up PTE in external memory v Use physical address to access memory Page 54 ANDES Confidential
Local Memory (LM) Page 55 ANDES Confidential
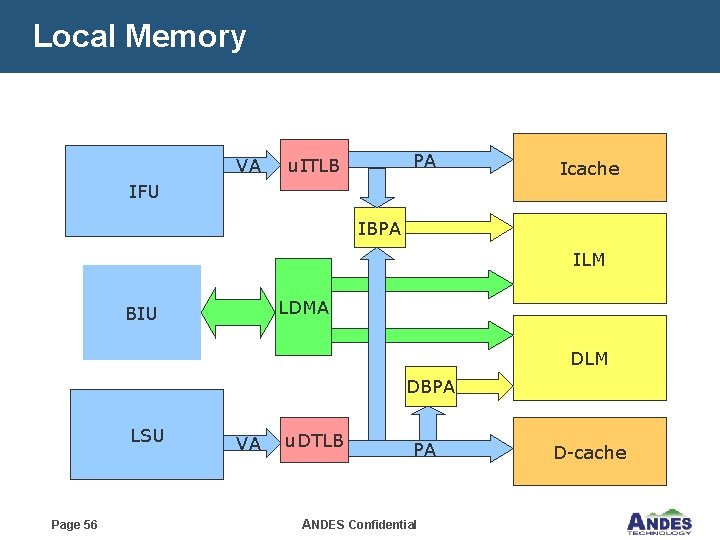
Local Memory VA PA u. ITLB Icache IFU IBPA ILM LDMA BIU DLM DBPA LSU Page 56 VA u. DTLB PA ANDES Confidential D-cache
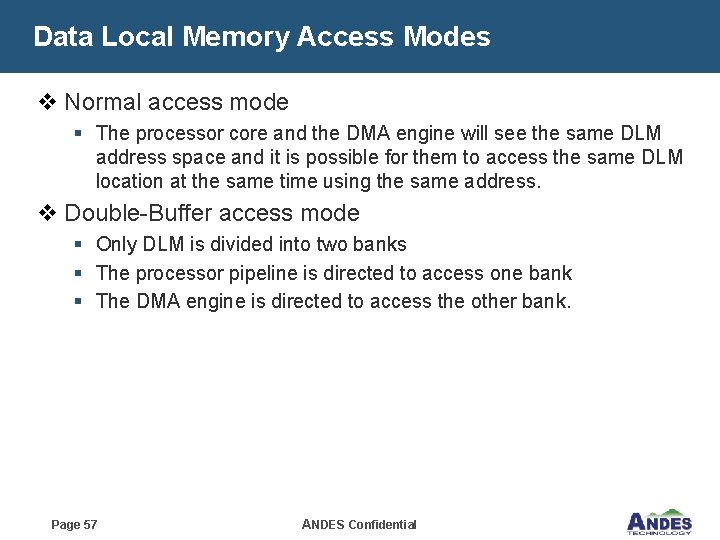
Data Local Memory Access Modes v Normal access mode § The processor core and the DMA engine will see the same DLM address space and it is possible for them to access the same DLM location at the same time using the same address. v Double-Buffer access mode § Only DLM is divided into two banks § The processor pipeline is directed to access one bank § The DMA engine is directed to access the other bank. Page 57 ANDES Confidential
Local memory constraint v Base physical address has to be aligned on 1 MB boundary for any smaller than or equal to 1 MB. v Any access outside of the local memory within the allocated 1 MB region will cause a “Nonexistent local memory address” exception. v The local memory needs to be mapped onto an uncacheable region; otherwise, UPREDICTABLE behavior may happen to the local memory content. Page 58 ANDES Confidential
Direct Memory Access (DMA) Page 59 ANDES Confidential
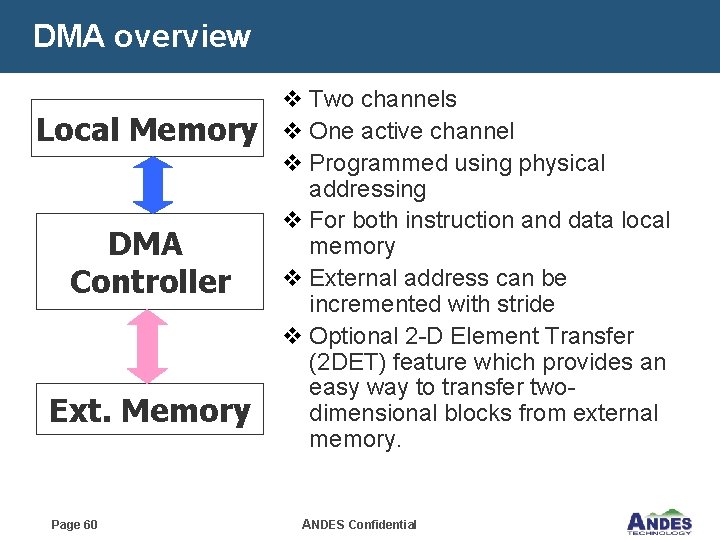
DMA overview Local Memory DMA Controller Ext. Memory Page 60 v Two channels v One active channel v Programmed using physical addressing v For both instruction and data local memory v External address can be incremented with stride v Optional 2 -D Element Transfer (2 DET) feature which provides an easy way to transfer twodimensional blocks from external memory. ANDES Confidential
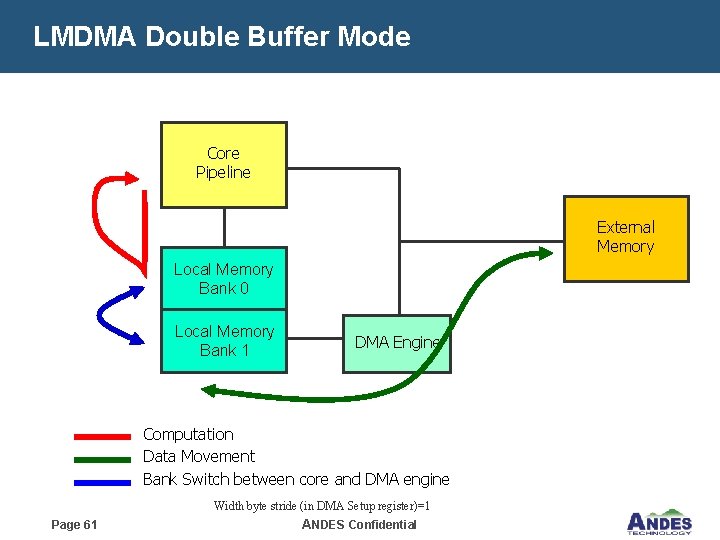
LMDMA Double Buffer Mode Core Pipeline External Memory Local Memory Bank 0 Local Memory Bank 1 DMA Engine Computation Data Movement Bank Switch between core and DMA engine Width byte stride (in DMA Setup register)=1 Page 61 ANDES Confidential
Bus Interface Unit (BIU) Page 62 ANDES Confidential
BIU introduction v Bus Interface unit is responsible for off-CPU memory access which includes § System memory access § Instruction/data local memory access § Memory-mapped register access in devices. Page 63 ANDES Confidential
Bus Interface v Compliance to AHB/AHB-Lite/APB v High Speed Memory Port v Andes Memory Interface v External LM Interface Page 64 ANDES Confidential
HSMP – High speed memory port v N 12 also provides a high speed memory port interface which has higher bus protocol efficiency and can run at a higher frequency to connect to a memory controller. v The high speed memory port will be AMBA 3. 0 (AXI) protocol compliant, but with reduced I/O requirements. Page 65 ANDES Confidential

v. Andes. Core Instruction Set Architecture Page 66 ANDES Confidential
Data Types v Data Types § § § Bit (1 -bit, b) Byte (8 -bit, B) Halfword (16 -bit, H) Word (32 -bit, W) Double Word (64 -bit, D) Page 67 ANDES Confidential
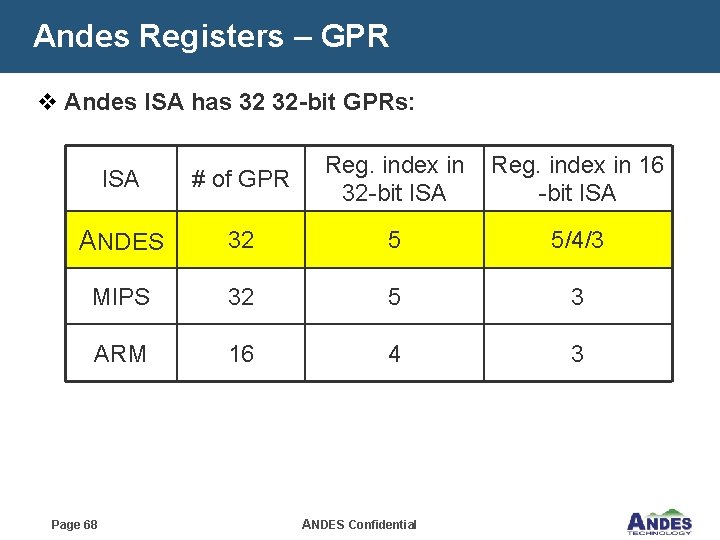
Andes Registers – GPR v Andes ISA has 32 32 -bit GPRs: Reg. index in 16 32 -bit ISA ISA # of GPR ANDES 32 5 5/4/3 MIPS 32 5 3 ARM 16 4 3 Page 68 ANDES Confidential
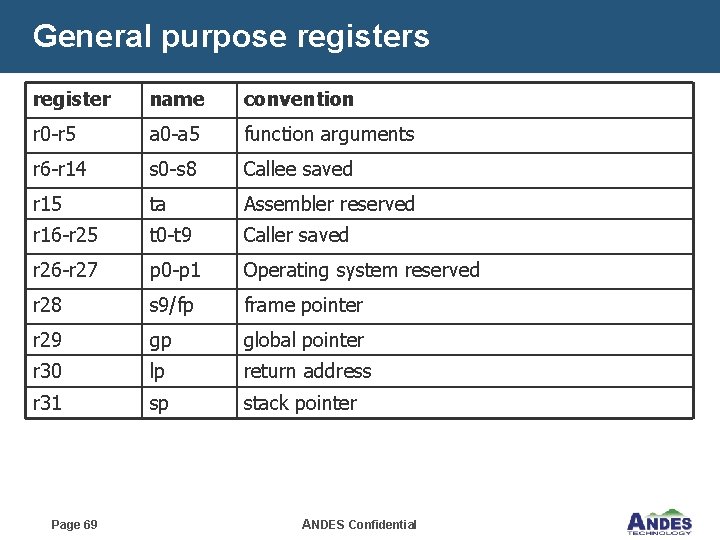
General purpose registers register name convention r 0 -r 5 a 0 -a 5 function arguments r 6 -r 14 s 0 -s 8 Callee saved r 15 ta Assembler reserved r 16 -r 25 t 0 -t 9 Caller saved r 26 -r 27 p 0 -p 1 Operating system reserved r 28 s 9/fp frame pointer r 29 gp global pointer r 30 lp return address r 31 sp stack pointer Page 69 ANDES Confidential
32 -Bit Baseline Instruction 1. Data-processing instructions 2. Load and Store Instructions 3. Jump and Branch Instructions 4. Miscellaneous Instructions Page 70 ANDES Confidential
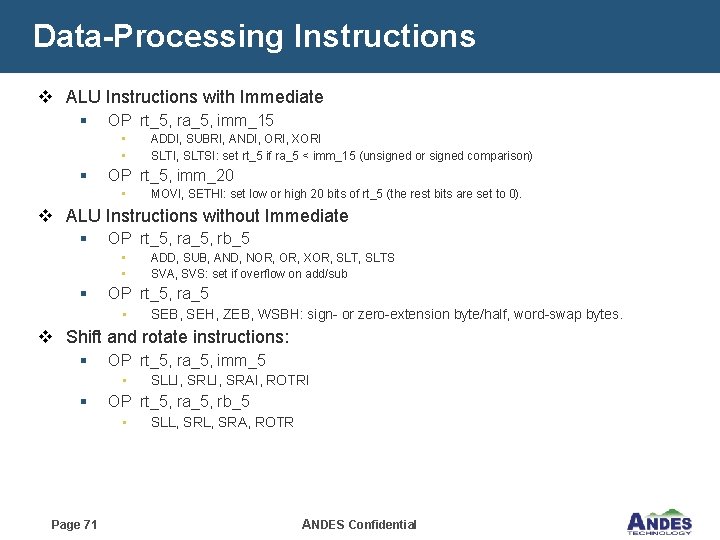
Data-Processing Instructions v ALU Instructions with Immediate § OP rt_5, ra_5, imm_15 • • § ADDI, SUBRI, ANDI, ORI, XORI SLTI, SLTSI: set rt_5 if ra_5 < imm_15 (unsigned or signed comparison) OP rt_5, imm_20 • MOVI, SETHI: set low or high 20 bits of rt_5 (the rest bits are set to 0). v ALU Instructions without Immediate § OP rt_5, ra_5, rb_5 • • § ADD, SUB, AND, NOR, XOR, SLTS SVA, SVS: set if overflow on add/sub OP rt_5, ra_5 • SEB, SEH, ZEB, WSBH: sign- or zero-extension byte/half, word-swap bytes. v Shift and rotate instructions: § OP rt_5, ra_5, imm_5 • § OP rt_5, ra_5, rb_5 • Page 71 SLLI, SRAI, ROTRI SLL, SRA, ROTR ANDES Confidential

Data-Processing Instructions (cont. ) v Multiplication-related Instructions § OP rt_5, ra_5, rb_5 32 -bit results of ra_5 x rb_5 to rt_5 • MUL § OP d_1, ra_5, rb_5 32 -bit or 64 -bit results to “d” registers • MULTS 64, MULT 64, MADDS 64, MADD 64, MSUBS 64, MSUB 64, MULT 32, MADD 32, MSUB 32 § OP rt_5, d_1. {hi, lo} • MFUSR, MTUSR: move-from or move-to a USR register v Example: mult 64 d 0, r 1 mfusr r 2, d 0. hi mfusr r 3, d 0. lo Page 72 ANDES Confidential
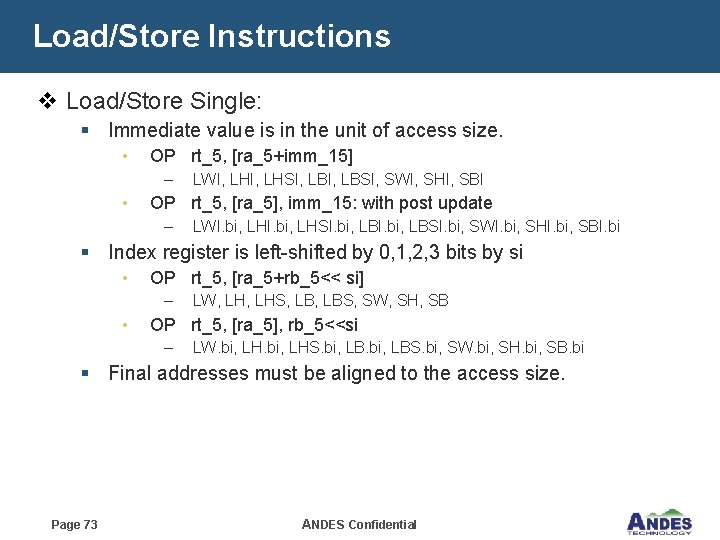
Load/Store Instructions v Load/Store Single: § Immediate value is in the unit of access size. • OP rt_5, [ra_5+imm_15] – • LWI, LHSI, LBSI, SWI, SHI, SBI OP rt_5, [ra_5], imm_15: with post update – LWI. bi, LHSI. bi, LBSI. bi, SWI. bi, SHI. bi, SBI. bi § Index register is left-shifted by 0, 1, 2, 3 bits by si • OP rt_5, [ra_5+rb_5<< si] – • LW, LHS, LBS, SW, SH, SB OP rt_5, [ra_5], rb_5<<si – LW. bi, LHS. bi, LBS. bi, SW. bi, SH. bi, SB. bi § Final addresses must be aligned to the access size. Page 73 ANDES Confidential
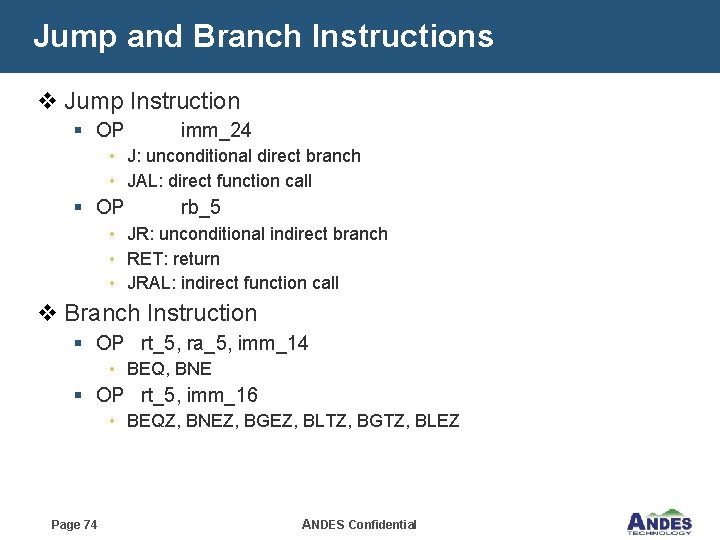
Jump and Branch Instructions v Jump Instruction § OP imm_24 • J: unconditional direct branch • JAL: direct function call § OP rb_5 • JR: unconditional indirect branch • RET: return • JRAL: indirect function call v Branch Instruction § OP rt_5, ra_5, imm_14 • BEQ, BNE § OP rt_5, imm_16 • BEQZ, BNEZ, BGEZ, BLTZ, BGTZ, BLEZ Page 74 ANDES Confidential
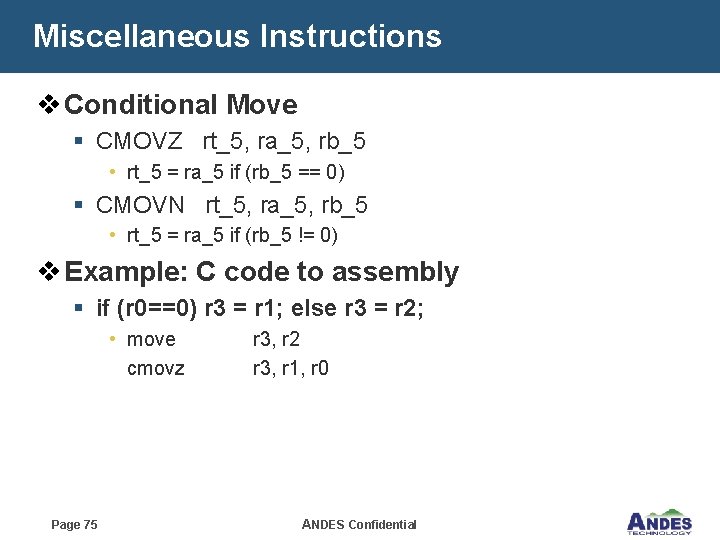
Miscellaneous Instructions v Conditional Move § CMOVZ rt_5, ra_5, rb_5 • rt_5 = ra_5 if (rb_5 == 0) § CMOVN rt_5, ra_5, rb_5 • rt_5 = ra_5 if (rb_5 != 0) v Example: C code to assembly § if (r 0==0) r 3 = r 1; else r 3 = r 2; • move r 3, r 2 cmovz r 3, r 1, r 0 Page 75 ANDES Confidential
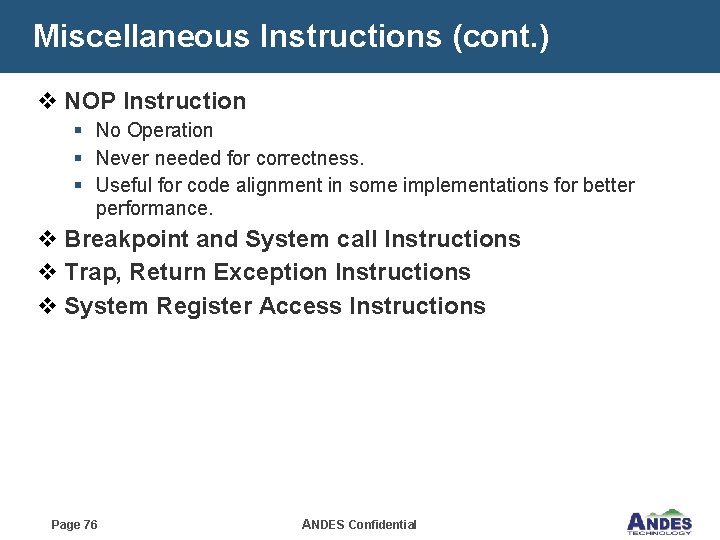
Miscellaneous Instructions (cont. ) v NOP Instruction § No Operation § Never needed for correctness. § Useful for code alignment in some implementations for better performance. v Breakpoint and System call Instructions v Trap, Return Exception Instructions v System Register Access Instructions Page 76 ANDES Confidential
Strength of Andes ISA v Mixed-length ISA with flexible 16 b instructions. v Efficient constant-setting instructions (up to 20 bits) v PC-relative jumps for position independent code. v Bi-endian modes to support flexible data input. v Performance instruction extensions for greater performance. v Immediate values of load/store word/halfword are in the corresponding access size to address wider range. v Load/store with post-update mode. . v Plenty space for custom extensions. Page 77 ANDES Confidential
v. Interruption Page 78 ANDES Confidential
Interruption Introduction v An Interruption is a control flow change of normal instruction execution generated by an Interrupt or an Exception v An interrupt is a control flow change event generated by an asynchronous internal or external source v An exception is a control flow change event generated as a by-product of instruction execution v Two Interruption stack level : 2 -level or 3 -level Page 79 ANDES Confidential

Interruption Stack Level v 4 “Interruption Stack Level” (ISL), ISL 0 means no interruption. v Hardware update interruption states on “Interruption Stack Level Transition” (ISLT). v ISLT 01, ISLT 12 updates Interruption Register Stack. v ISLT 23 updates limited states for server error condition. v Stack level can only be up to level 2 in 2 -level configured interruption Page 80 ANDES Confidential
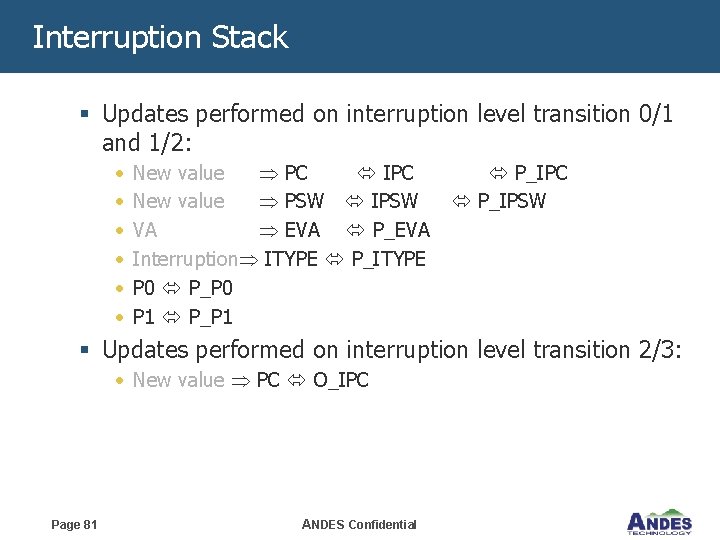
Interruption Stack § Updates performed on interruption level transition 0/1 and 1/2: • • • New value PC IPC New value PSW IPSW VA EVA P_EVA Interruption ITYPE P_ITYPE P 0 P_P 0 P 1 P_IPC P_IPSW § Updates performed on interruption level transition 2/3: • New value PC O_IPC Page 81 ANDES Confidential

Interruption Behavior v Transition to Superuser mode v Disable interrupt v Disable I/D address translation v Use default Endian v ISLT 0 1/ISLT 1 2 achieves these behavior by updating corresponding PSW states while ISLT 2 3 achieves these behavior by assumption. Page 82 ANDES Confidential
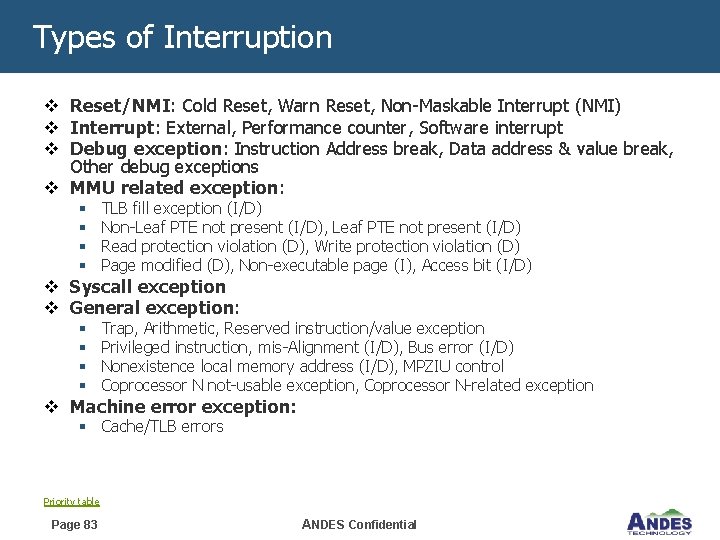
Types of Interruption v Reset/NMI: Cold Reset, Warn Reset, Non-Maskable Interrupt (NMI) v Interrupt: External, Performance counter, Software interrupt v Debug exception: Instruction Address break, Data address & value break, Other debug exceptions v MMU related exception: § § TLB fill exception (I/D) Non-Leaf PTE not present (I/D), Leaf PTE not present (I/D) Read protection violation (D), Write protection violation (D) Page modified (D), Non-executable page (I), Access bit (I/D) § § Trap, Arithmetic, Reserved instruction/value exception Privileged instruction, mis-Alignment (I/D), Bus error (I/D) Nonexistence local memory address (I/D), MPZIU control Coprocessor N not-usable exception, Coprocessor N-related exception v Syscall exception v General exception: v Machine error exception: § Cache/TLB errors Priority table Page 83 ANDES Confidential
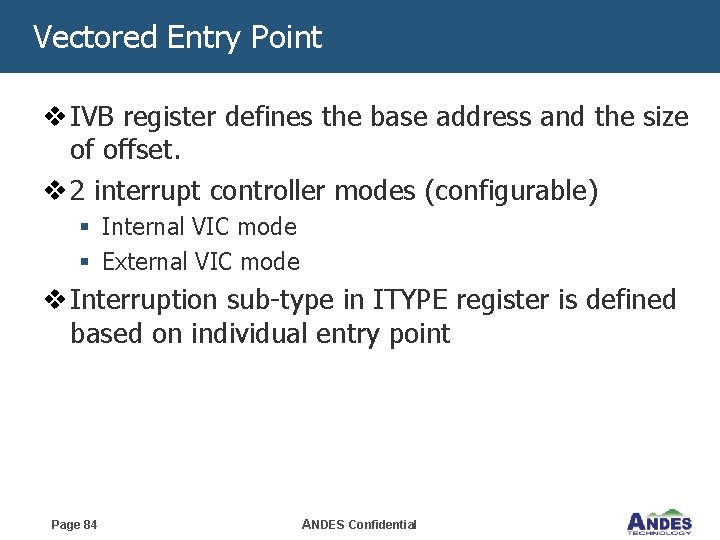
Vectored Entry Point v IVB register defines the base address and the size of offset. v 2 interrupt controller modes (configurable) § Internal VIC mode § External VIC mode v Interruption sub-type in ITYPE register is defined based on individual entry point Page 84 ANDES Confidential
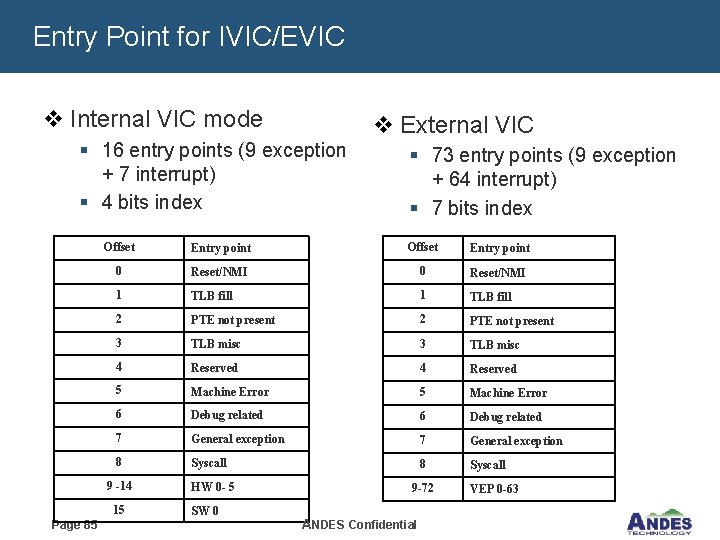
Entry Point for IVIC/EVIC v Internal VIC mode v External VIC § 16 entry points (9 exception + 7 interrupt) § 4 bits index Offset Entry point 0 Reset/NMI 1 TLB fill 2 PTE not present 3 TLB misc 4 Reserved 5 Machine Error 6 Debug related 7 General exception 8 Syscall 9 -14 15 Page 85 § 73 entry points (9 exception + 64 interrupt) § 7 bits index HW 0 - 5 SW 0 9 -72 ANDES Confidential VEP 0 -63

Thank You!!! WWW. ANDESTECH. COM
- Slides: 86