Analyzing and Testing justified Prime Numbers Concrete Mathematics
Analyzing and Testing justified Prime Numbers Concrete Mathematics Final Presentation 20032047 Jeong-Kyu YANG 2003 Seok-Kyu Kang
OUTLINE Introduction The Primality Testing Algorithms Ø Probabilistic Algorithms Ø Deterministic Algorithms Analyzing Ø Solovay-Strassen Algorithm Ø Miller-Rabin Algorithm Ø AKS Algorithm Implements & Experiments Conclusion & Future Works References Information Security Group 2

Introduction What is Prime Number & Primality Testing? Prime Number Primality Test The importance of testing primality Applications in cryptography § RSA, etc. uses primality testing algorithm in the part of key generation. How fast and efficient? Brief History 200 BC: Eratosthenes Sieve 1976: NP(Nondeterministic Polynomial-time), Pratt 1977: co. RP(Complementary Randomized Polynomial-time), Solovay and Strassen 1987: RP(Randomized Polynomial-time), adleman and Huang 1992: UP(Unambiguous Polynomial-time), Fellows and Koblitz 2002: PRIMES is in P(Polynomial-time), Agrawal et al. Information Security Group 3
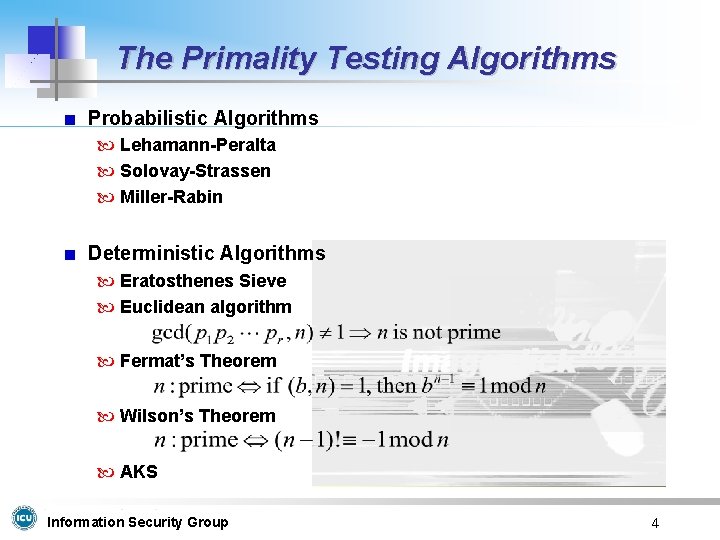
The Primality Testing Algorithms Probabilistic Algorithms Lehamann-Peralta Solovay-Strassen Miller-Rabin Deterministic Algorithms Eratosthenes Sieve Euclidean algorithm Fermat’s Theorem Wilson’s Theorem AKS Information Security Group 4
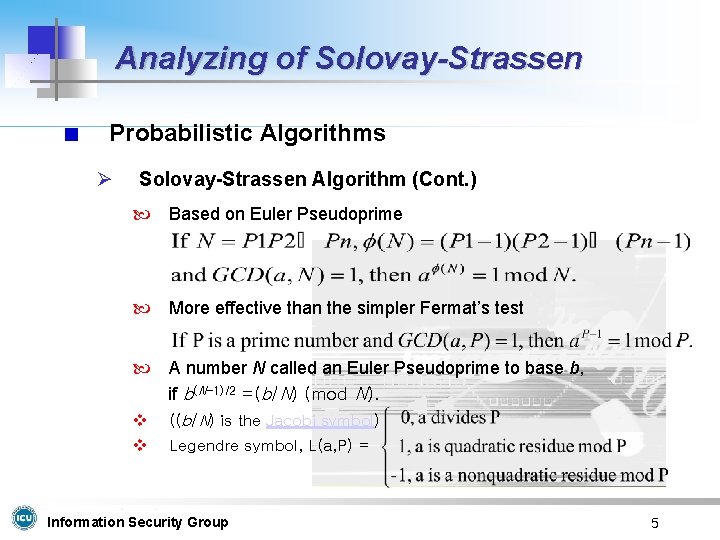
Analyzing of Solovay-Strassen Probabilistic Algorithms Ø Solovay-Strassen Algorithm (Cont. ) Based on Euler Pseudoprime More effective than the simpler Fermat’s test A number N called an Euler Pseudoprime to base b, if b(N-1)/2 =(b/N) (mod N). v ((b/N) is the Jacobi symbol) v Legendre symbol, L(a, P) = Information Security Group 5
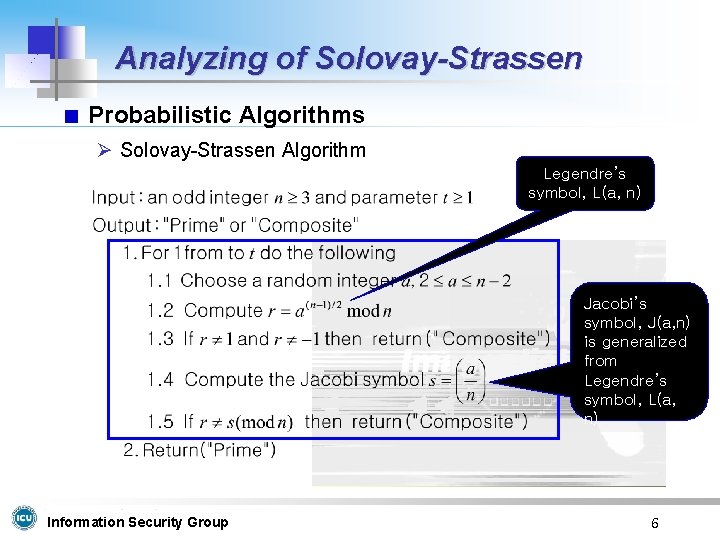
Analyzing of Solovay-Strassen Probabilistic Algorithms Ø Solovay-Strassen Algorithm Legendre’s symbol, L(a, n) Jacobi’s symbol, J(a, n) is generalized from Legendre’s symbol, L(a, n) Information Security Group 6
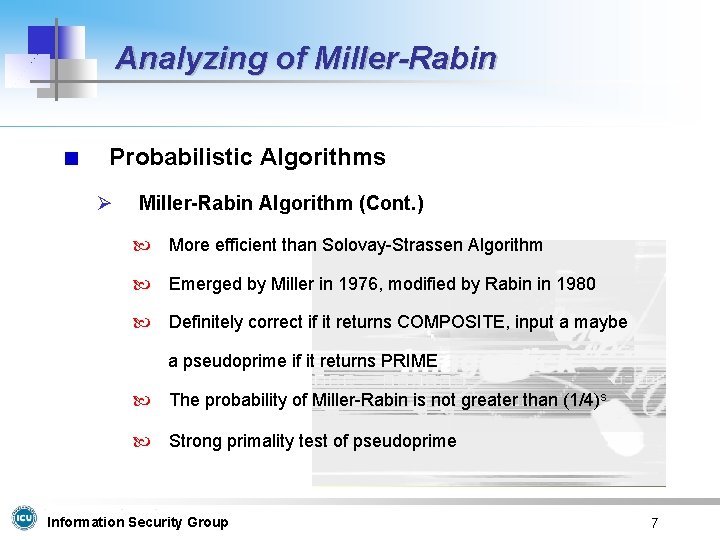
Analyzing of Miller-Rabin Probabilistic Algorithms Ø Miller-Rabin Algorithm (Cont. ) More efficient than Solovay-Strassen Algorithm Emerged by Miller in 1976, modified by Rabin in 1980 Definitely correct if it returns COMPOSITE, input a maybe a pseudoprime if it returns PRIME The probability of Miller-Rabin is not greater than (1/4)s Strong primality test of pseudoprime Information Security Group 7
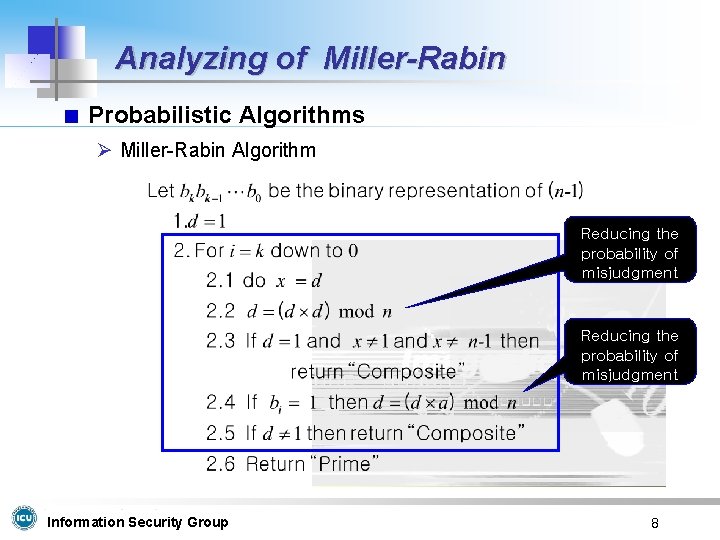
Analyzing of Miller-Rabin Probabilistic Algorithms Ø Miller-Rabin Algorithm Reducing the probability of misjudgment Information Security Group 8
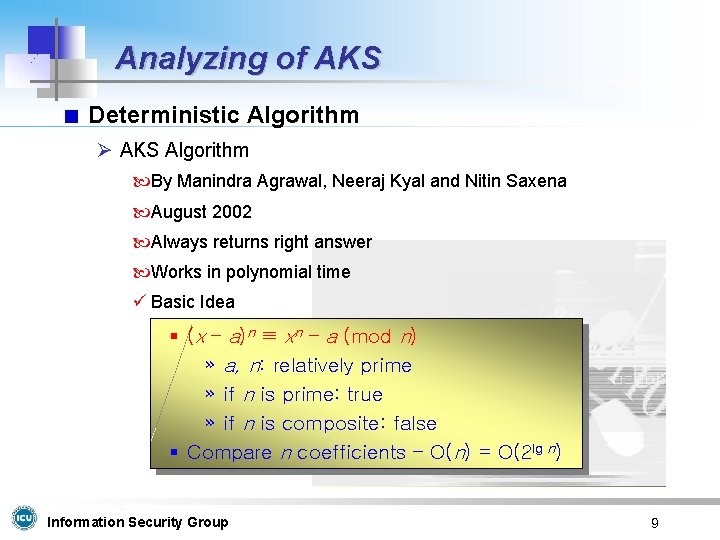
Analyzing of AKS Deterministic Algorithm Ø AKS Algorithm By Manindra Agrawal, Neeraj Kyal and Nitin Saxena August 2002 Always returns right answer Works in polynomial time ü Basic Idea § (x – a)n ≡ xn – a (mod n) » a, n: relatively prime » if n is prime: true » if n is composite: false § Compare n coefficients – O(n) = O(2 lg n) Information Security Group 9

Analyzing of AKS Deterministic Algorithm Ø AKS Algorithm Find Useful Prime Brute force can be used Set of congruence Information Security Group 10
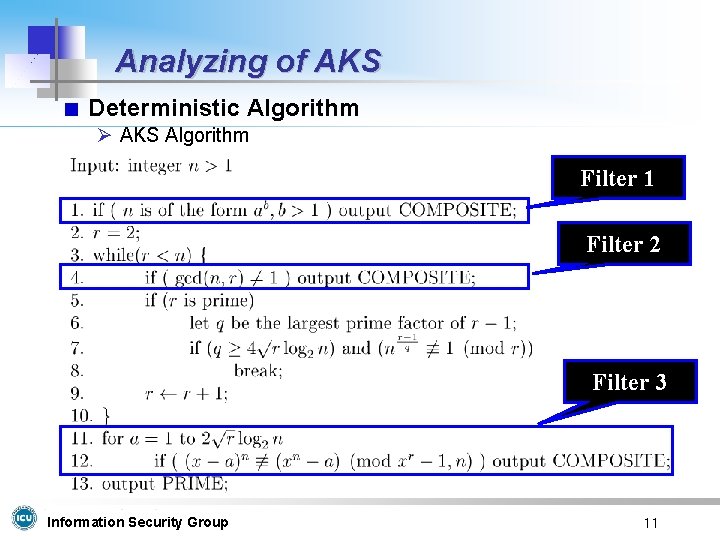
Analyzing of AKS Deterministic Algorithm Ø AKS Algorithm Filter 1 Filter 2 Filter 3 Information Security Group 11
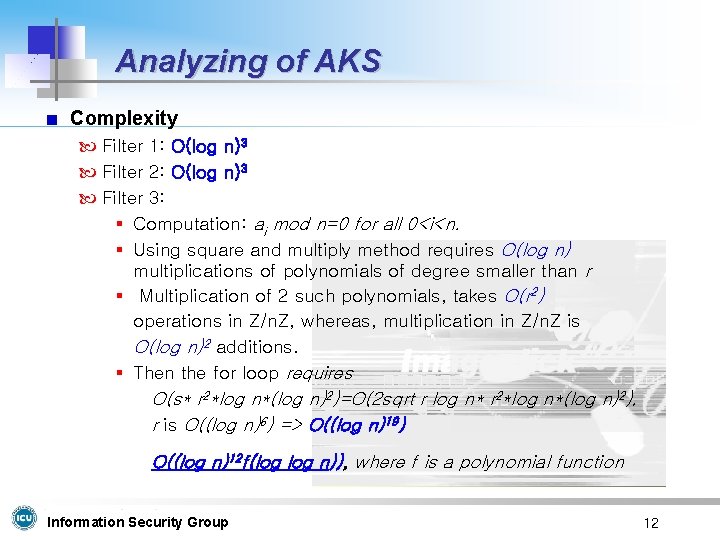
Analyzing of AKS Complexity Filter 1: O(log n)3 Filter 2: O(log n)3 Filter 3: § Computation: ai mod n=0 for all 0<i<n. § Using square and multiply method requires O(log n) multiplications of polynomials of degree smaller than r § Multiplication of 2 such polynomials, takes O(r 2) operations in Z/n. Z, whereas, multiplication in Z/n. Z is O(log n)2 additions. § Then the for loop requires O(s* r 2*log n*(log n)2)=O(2 sqrt r log n* r 2*log n*(log n)2), r is O((log n)6) => O((log n)19) O((log n)12 f(log n)), where f is a polynomial function Information Security Group 12
Implementations – SS, MR and AKS Environment Hardware § Pentium III 550 mhz, 384 RAM Language: Java (j 2 sdk 1. 4. 0_02), Boland Jbuilder 6. 0 The way to implement Solovay-Strassen & Miller-Rabin § § Run simultaneously with a same random number generator Same iterations to check better performance Same bit lengths Demo Program-1 AKS § Testing with far smaller lengths (Long integer operation is for further works) § Testing for polynomial time of AKS § Demo Program-2, Program-3 Information Security Group 13
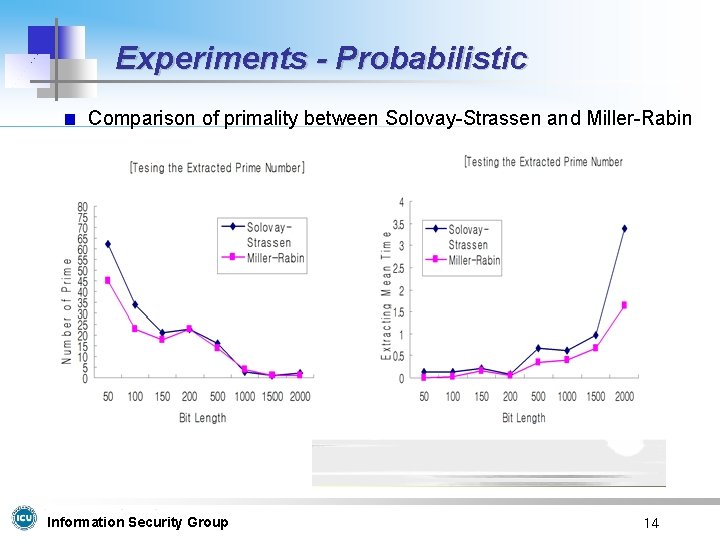
Experiments - Probabilistic Comparison of primality between Solovay-Strassen and Miller-Rabin Information Security Group 14
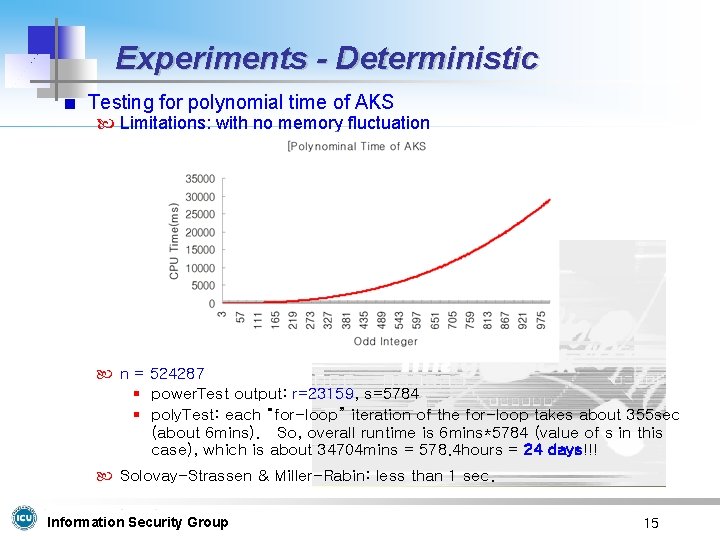
Experiments - Deterministic Testing for polynomial time of AKS Limitations: with no memory fluctuation n = 524287 § power. Test output: r=23159, s=5784 § poly. Test: each “for-loop” iteration of the for-loop takes about 355 sec (about 6 mins). So, overall runtime is 6 mins*5784 (value of s in this case), which is about 34704 mins = 578. 4 hours = 24 days!!! Solovay-Strassen & Miller-Rabin: less than 1 sec. Information Security Group 15
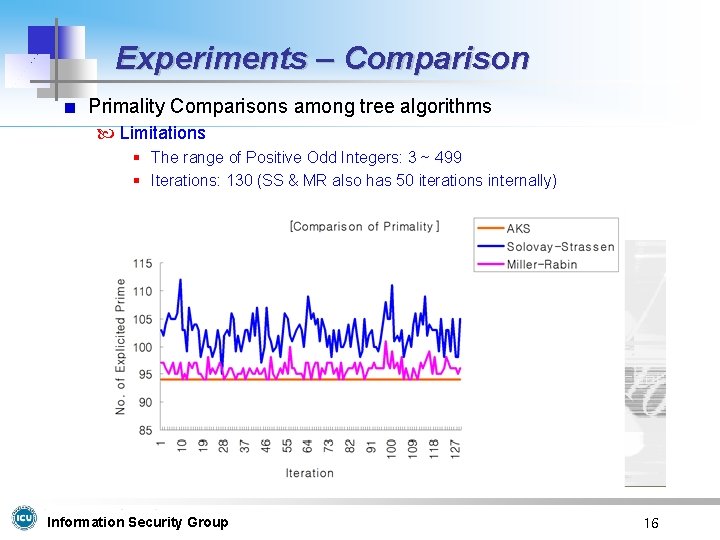
Experiments – Comparison Primality Comparisons among tree algorithms Limitations § The range of Positive Odd Integers: 3 ~ 499 § Iterations: 130 (SS & MR also has 50 iterations internally) Information Security Group 16
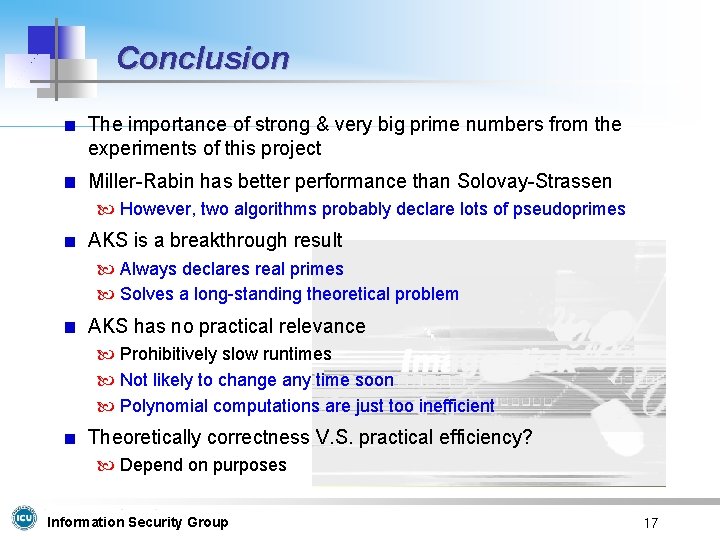
Conclusion The importance of strong & very big prime numbers from the experiments of this project Miller-Rabin has better performance than Solovay-Strassen However, two algorithms probably declare lots of pseudoprimes AKS is a breakthrough result Always declares real primes Solves a long-standing theoretical problem AKS has no practical relevance Prohibitively slow runtimes Not likely to change any time soon Polynomial computations are just too inefficient Theoretically correctness V. S. practical efficiency? Depend on purposes Information Security Group 17
Future Works More analysis of complexity for each algorithms Further Experiments for AKS Find useful prime numbers and analyze its characteristics Further Implementation for AKS Try to get over inefficiency of AKS Algorithm Improving to handle very long integers Continue to compare results of each algorithms Information Security Group 18
![References [1] M. Agrawal, N. Kayal and N. Saxena, “PRIMES is in P”, August References [1] M. Agrawal, N. Kayal and N. Saxena, “PRIMES is in P”, August](http://slidetodoc.com/presentation_image_h2/c6883950dd9dccbaca8dfa37780882ff/image-19.jpg)
References [1] M. Agrawal, N. Kayal and N. Saxena, “PRIMES is in P”, August 6, 2002 [2] William Stallings, “Cryptography and Network security”, second edition. Prentice Hall, 1998 [3] J. Menezes, C. vaz Oorschot and A. Vanstone, “Handbook of Applied Cryptography” CRC, 1977 [4] Takeshi Aoyama, “Polynomial Time Primality Testing Algorithm”, 2003 [5] Frontline. “Volume 19 -Issue 17”, August 17 -30. 2002 [6] http: //www. javastudy. co. kr/docs/techtips/020821. html [7] http: //www-fs. informatik. uni-uebingen. de/~reinhard/krypto/primzt. html [8] http: //www. cse. iitk. ac. in/news/primality. html [9] http: //random. mat. sbg. ac. at/generators/ Information Security Group 19
- Slides: 19