Analysis of Algorithms Input 2014 Goodrich Tamassia Goldwasser
![Summary O(g(n)) [upper bound] Original function f(n) [time, space] (g(n)) [lower bound] © 2014 Summary O(g(n)) [upper bound] Original function f(n) [time, space] (g(n)) [lower bound] © 2014](https://slidetodoc.com/presentation_image_h2/800b35371d4f53208cd441a5b3bf4e62/image-52.jpg)
- Slides: 52
Analysis of Algorithms Input © 2014 Goodrich, Tamassia, Goldwasser Algorithm Analysis of Algorithms Output 1
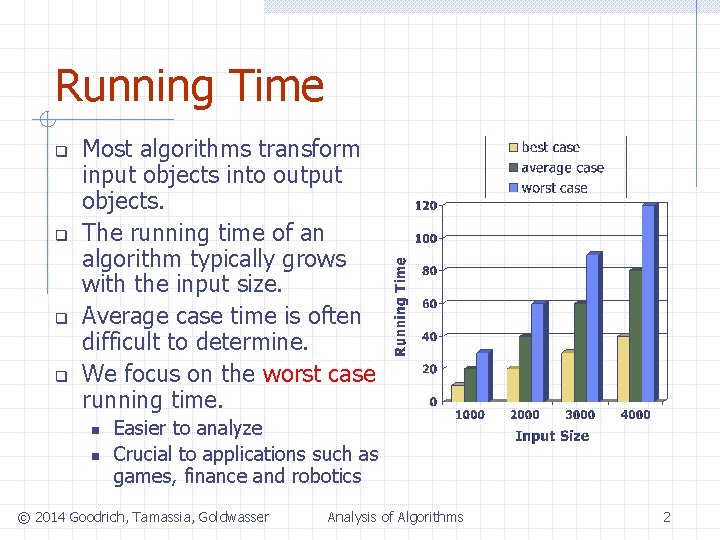
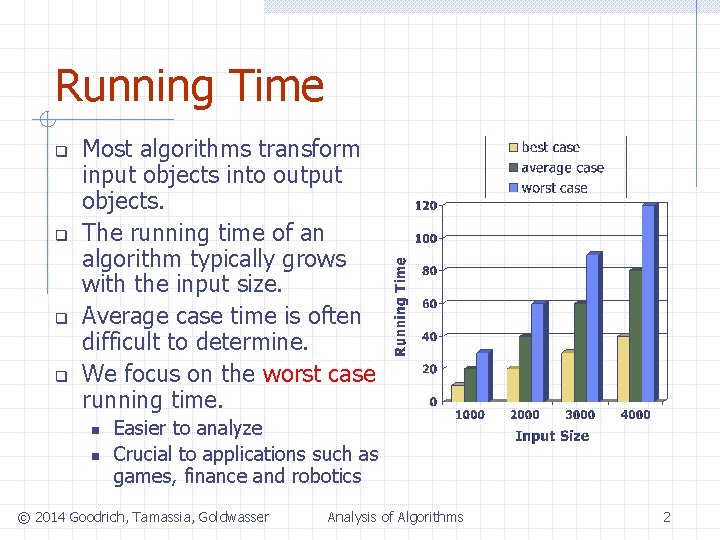
Running Time q q Most algorithms transform input objects into output objects. The running time of an algorithm typically grows with the input size. Average case time is often difficult to determine. We focus on the worst case running time. n n Easier to analyze Crucial to applications such as games, finance and robotics © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 2
2 lines at the grocery store q Line A: n q Line B: n q The wait is at least 10 seconds The wait is at most one minute Which line would you choose? © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 3
2 lines at the grocery store q Line A: n The wait is at least 10 seconds (best case) w Could be a few hours q Line B: n The wait is at most one minute (worst case) w Could be a few seconds © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 4
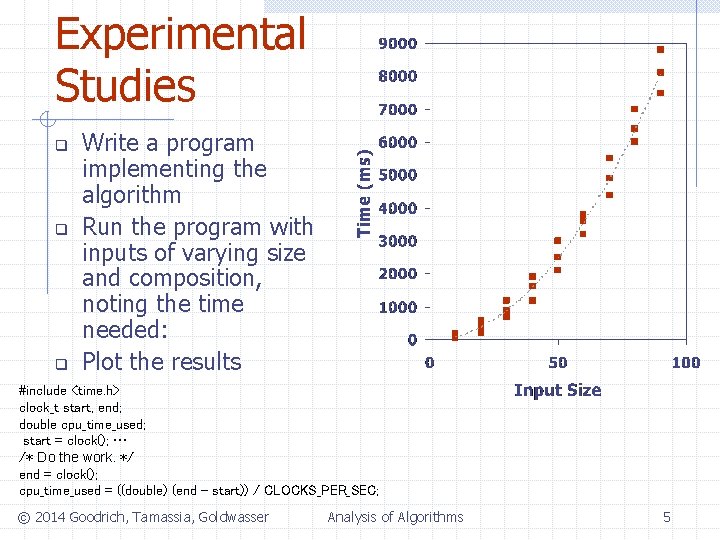
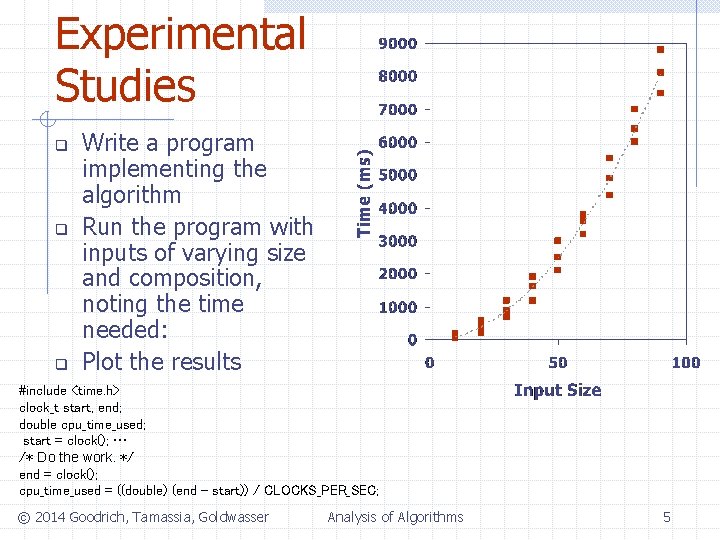
Experimental Studies q q q Write a program implementing the algorithm Run the program with inputs of varying size and composition, noting the time needed: Plot the results #include <time. h> clock_t start, end; double cpu_time_used; start = clock(); … /* Do the work. */ end = clock(); cpu_time_used = ((double) (end - start)) / CLOCKS_PER_SEC; © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 5
Limitations of Experiments implement the algorithm, which may be difficult q results may not be indicative of the running time on other inputs not included in the experiment. q compare two algorithms--same hardware and software environments must be used q © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 6
Theoretical Analysis Uses a high-level description of the algorithm instead of an implementation q Characterizes running time as a function of the input size, n q Takes into account all possible inputs q independent of the hardware/software environment q © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 7
Pseudocode High-level description of an algorithm q More structured than English prose q Less detailed than a program q Preferred notation for describing algorithms q Hides program design issues q © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 8
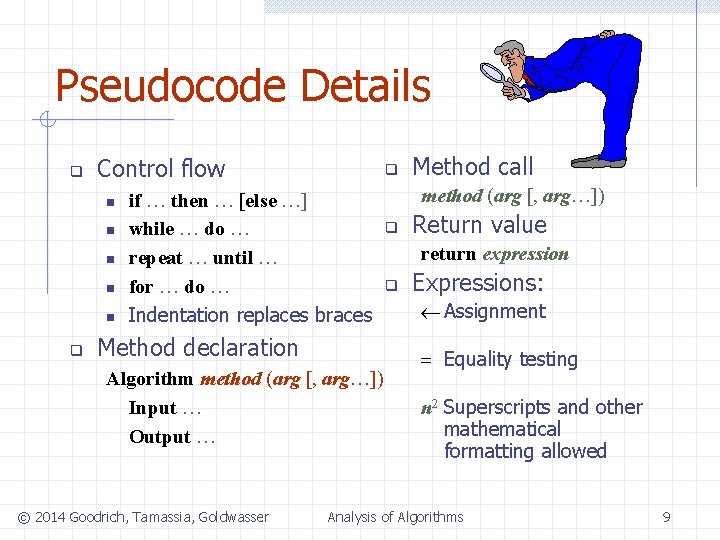
Pseudocode Details q Control flow n n n q q if … then … [else …] while … do … repeat … until … for … do … Indentation replaces braces Method declaration Algorithm method (arg [, arg…]) Input … Output … © 2014 Goodrich, Tamassia, Goldwasser Method call method (arg [, arg…]) q Return value return expression q Expressions: ¬ Assignment = Equality testing n 2 Superscripts and other mathematical formatting allowed Analysis of Algorithms 9
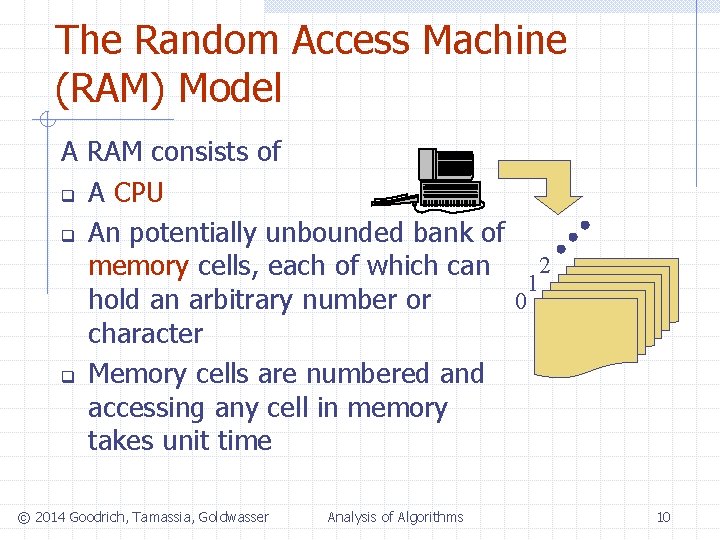
The Random Access Machine (RAM) Model A RAM consists of q A CPU q An potentially unbounded bank of 2 memory cells, each of which can 1 0 hold an arbitrary number or character q Memory cells are numbered and accessing any cell in memory takes unit time © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 10
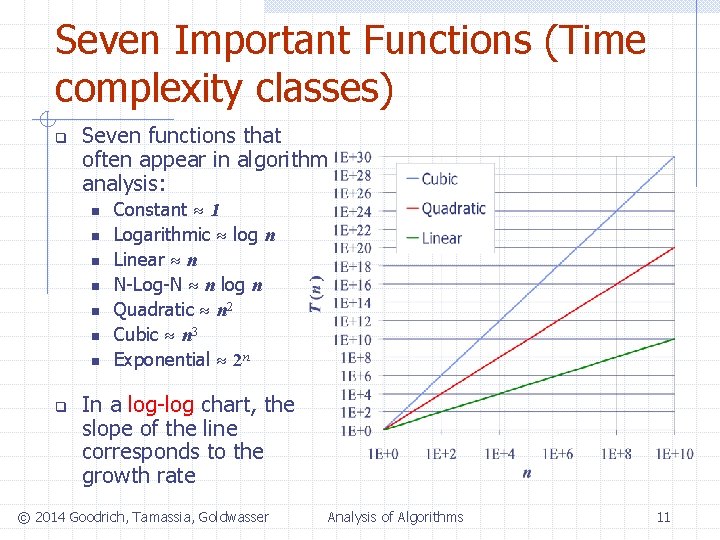
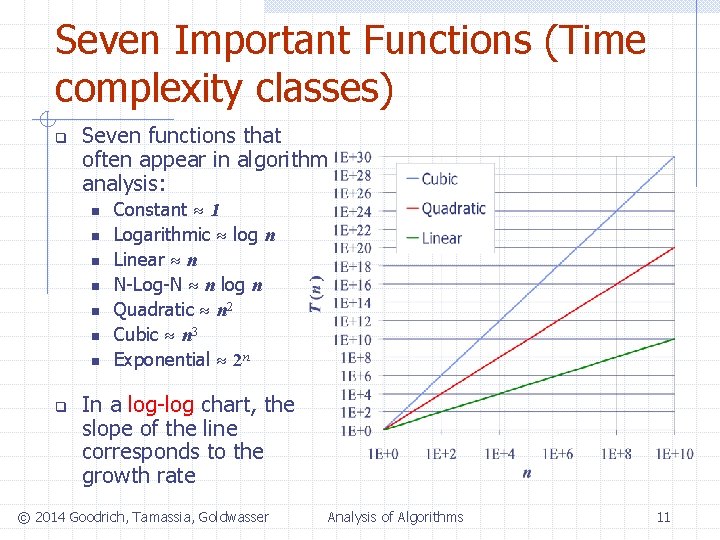
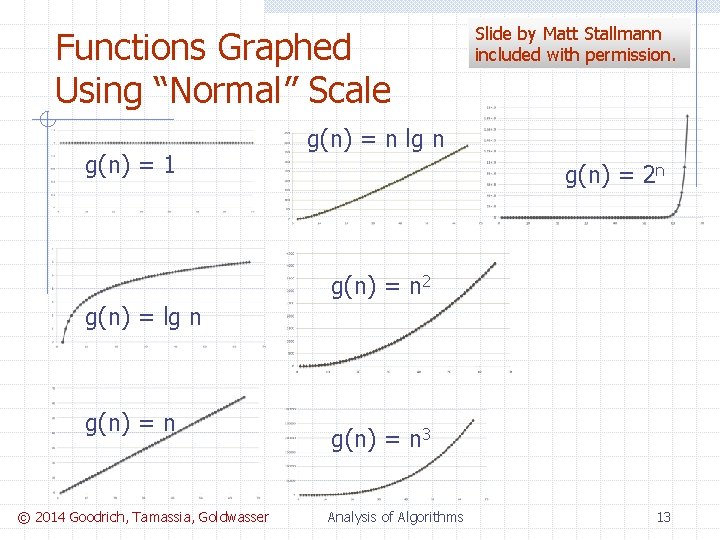
Seven Important Functions (Time complexity classes) q Seven functions that often appear in algorithm analysis: n n n n q Constant 1 Logarithmic log n Linear n N-Log-N n log n Quadratic n 2 Cubic n 3 Exponential 2 n In a log-log chart, the slope of the line corresponds to the growth rate © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 11
Log-log chart/plot y = xa q log y = a log x q q Slope is a © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 12
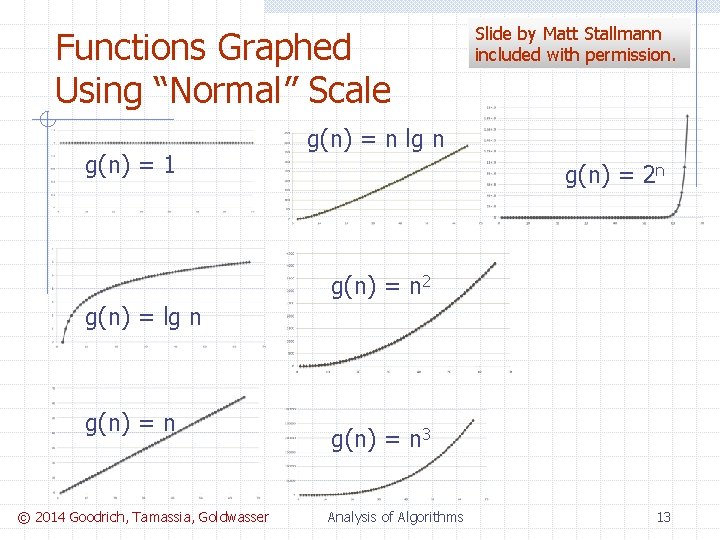
Functions Graphed Using “Normal” Scale g(n) = 1 Slide by Matt Stallmann included with permission. g(n) = n lg n g(n) = 2 n g(n) = n 2 g(n) = lg n g(n) = n © 2014 Goodrich, Tamassia, Goldwasser g(n) = n 3 Analysis of Algorithms 13
Primitive Operations q q q Basic computations performed by an algorithm Identifiable in pseudocode Largely independent from the programming language Exact definition not important (we will see why later) Assumed to take a constant amount of time in the RAM model © 2014 Goodrich, Tamassia, Goldwasser q Analysis of Algorithms Examples: n n n Evaluating an expression Assigning a value to a variable Indexing into an array Calling a method Returning from a method 14
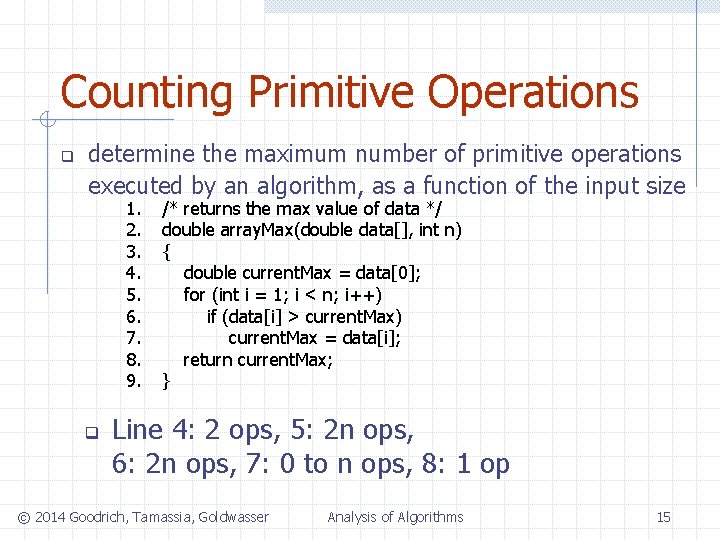
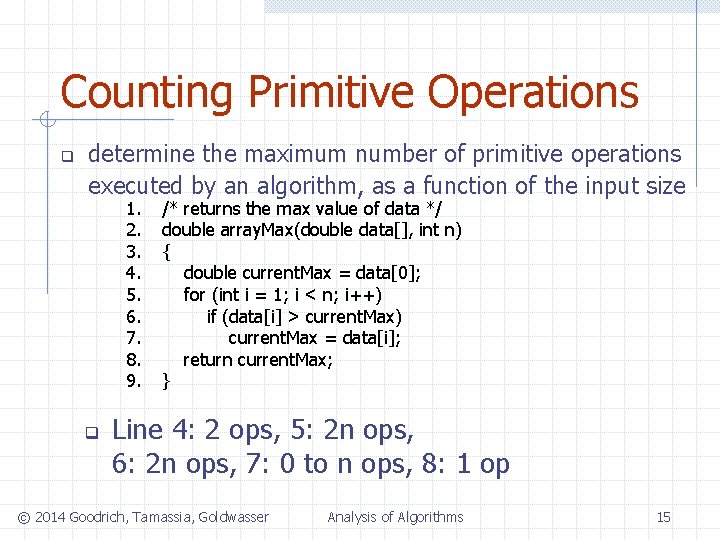
Counting Primitive Operations q determine the maximum number of primitive operations executed by an algorithm, as a function of the input size 1. 2. 3. 4. 5. 6. 7. 8. 9. q /* returns the max value of data */ double array. Max(double data[], int n) { double current. Max = data[0]; for (int i = 1; i < n; i++) if (data[i] > current. Max) current. Max = data[i]; return current. Max; } Line 4: 2 ops, 5: 2 n ops, 6: 2 n ops, 7: 0 to n ops, 8: 1 op © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 15
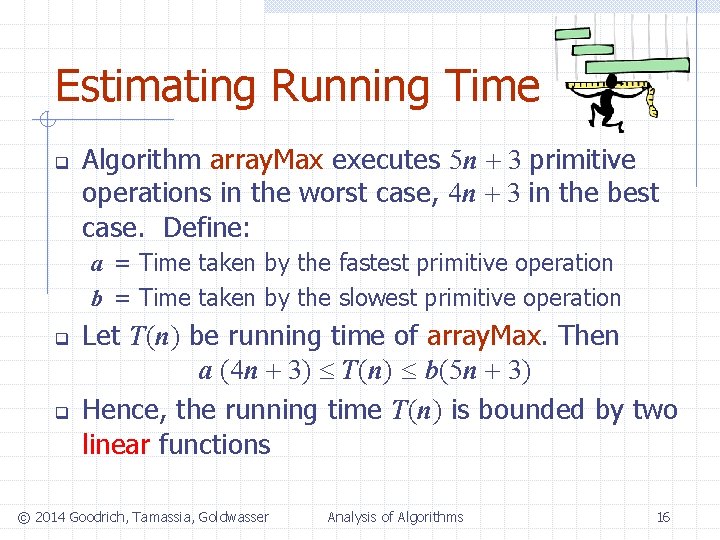
Estimating Running Time q Algorithm array. Max executes 5 n + 3 primitive operations in the worst case, 4 n + 3 in the best case. Define: a = Time taken by the fastest primitive operation b = Time taken by the slowest primitive operation q q Let T(n) be running time of array. Max. Then a (4 n + 3) T(n) b(5 n + 3) Hence, the running time T(n) is bounded by two linear functions © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 16
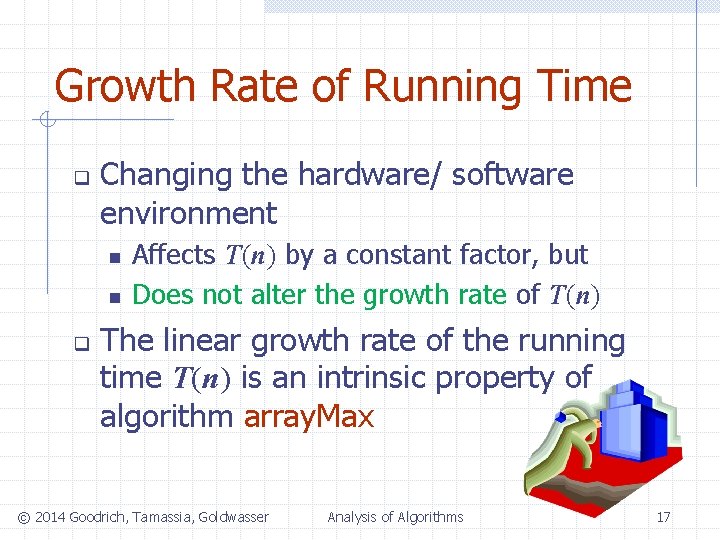
Growth Rate of Running Time q Changing the hardware/ software environment n n q Affects T(n) by a constant factor, but Does not alter the growth rate of T(n) The linear growth rate of the running time T(n) is an intrinsic property of algorithm array. Max © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 17
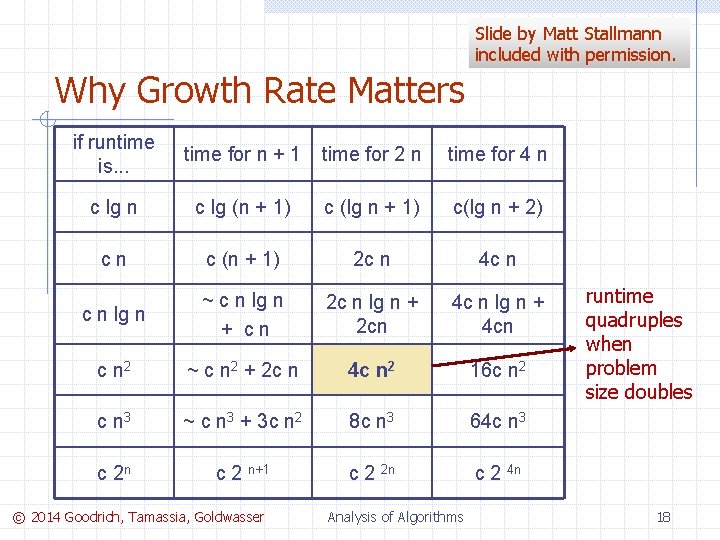
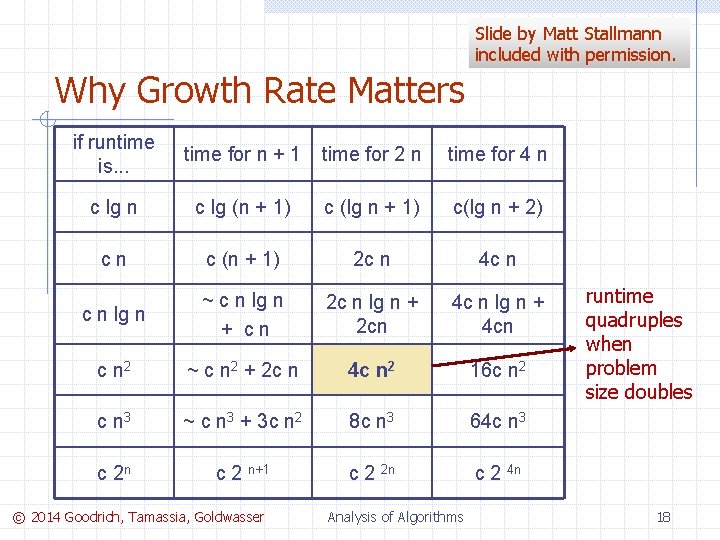
Slide by Matt Stallmann included with permission. Why Growth Rate Matters if runtime is. . . time for n + 1 time for 2 n time for 4 n c lg (n + 1) c (lg n + 1) c(lg n + 2) cn c (n + 1) 2 c n 4 c n lg n ~ c n lg n + cn 2 c n lg n + 2 cn 4 c n lg n + 4 cn c n 2 ~ c n 2 + 2 c n 4 c n 2 16 c n 2 c n 3 ~ c n 3 + 3 c n 2 8 c n 3 64 c n 3 c 2 n c 2 n+1 c 2 2 n c 2 4 n © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms runtime quadruples when problem size doubles 18
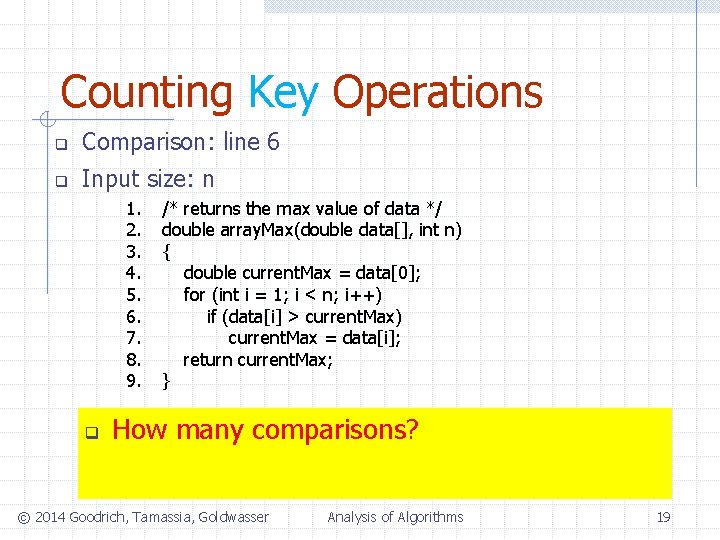
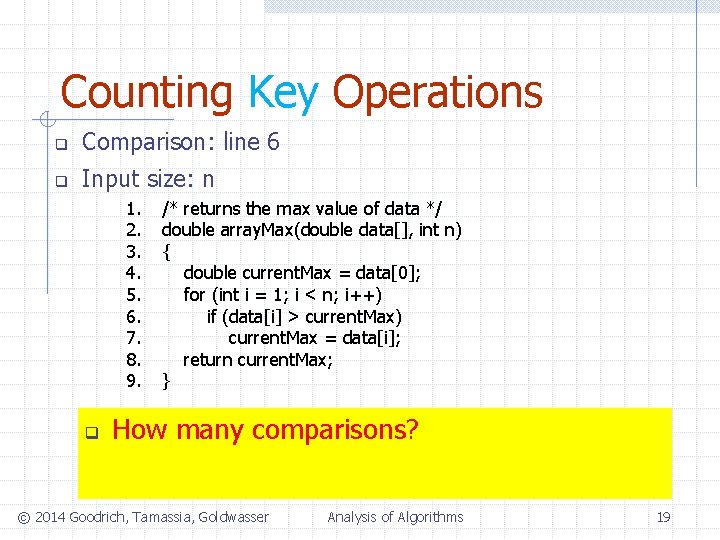
Counting Key Operations q Comparison: line 6 q Input size: n 1. 2. 3. 4. 5. 6. 7. 8. 9. q /* returns the max value of data */ double array. Max(double data[], int n) { double current. Max = data[0]; for (int i = 1; i < n; i++) if (data[i] > current. Max) current. Max = data[i]; return current. Max; } How many comparisons? © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 19
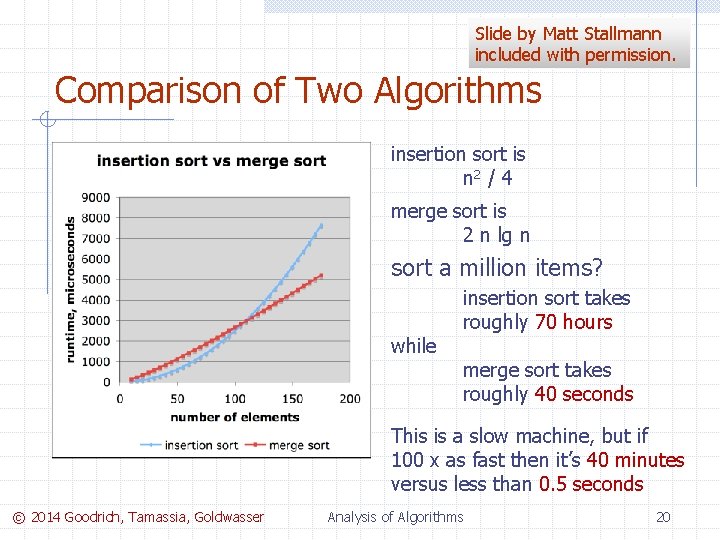
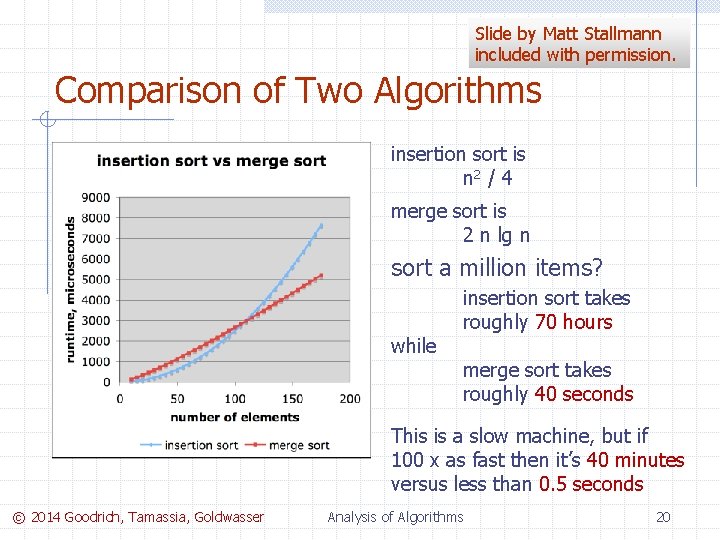
Slide by Matt Stallmann included with permission. Comparison of Two Algorithms insertion sort is n 2 / 4 merge sort is 2 n lg n sort a million items? while insertion sort takes roughly 70 hours merge sort takes roughly 40 seconds This is a slow machine, but if 100 x as fast then it’s 40 minutes versus less than 0. 5 seconds © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 20
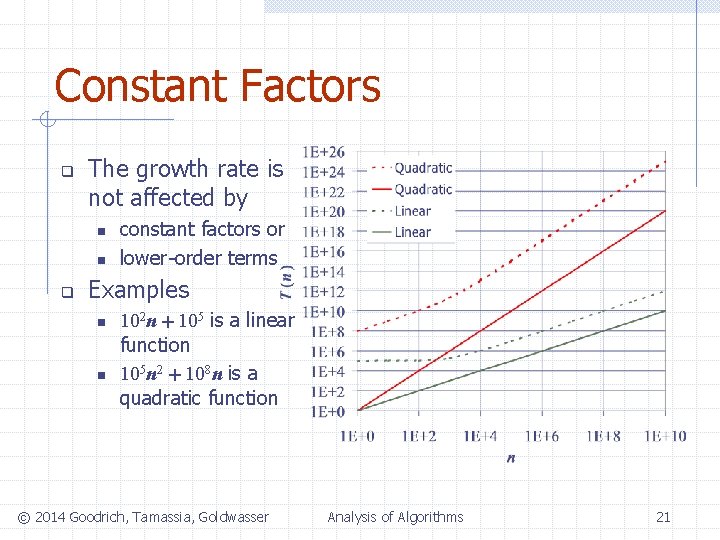
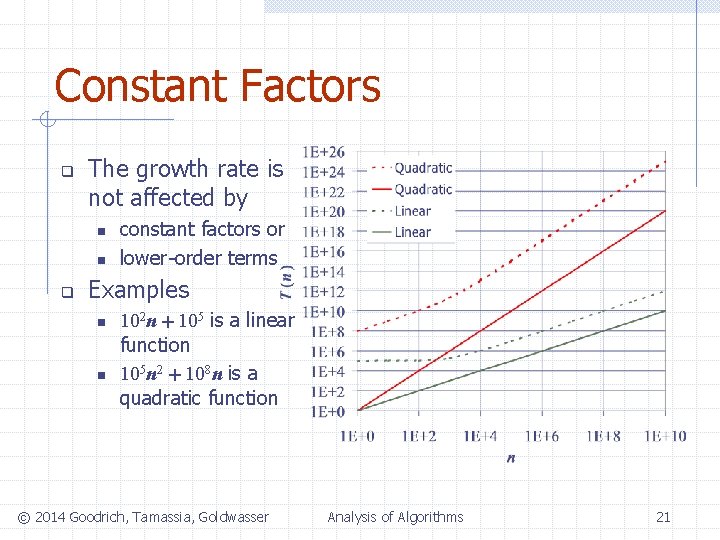
Constant Factors q The growth rate is not affected by n n q constant factors or lower-order terms Examples n n 102 n + 105 is a linear function 105 n 2 + 108 n is a quadratic function © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 21
Big-Oh Notation q Given functions f(n) and g(n), we say that f(n) is O(g(n)) if there are positive constants K and n 0 such that f(n) Kg(n) for n n 0 © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 22
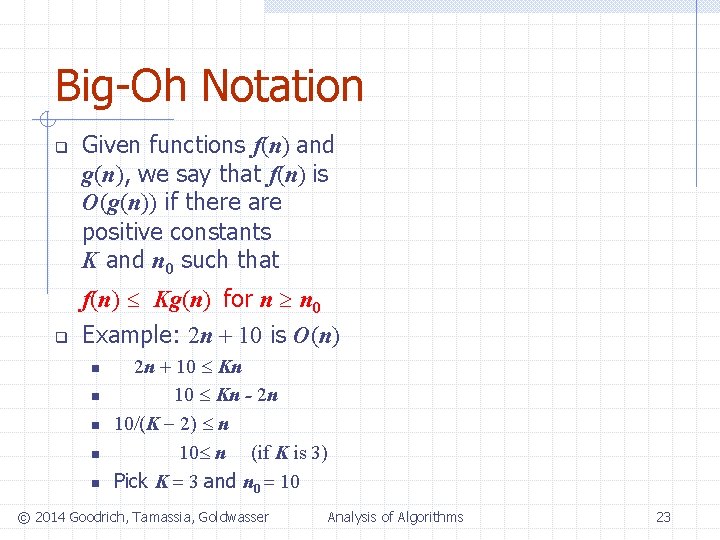
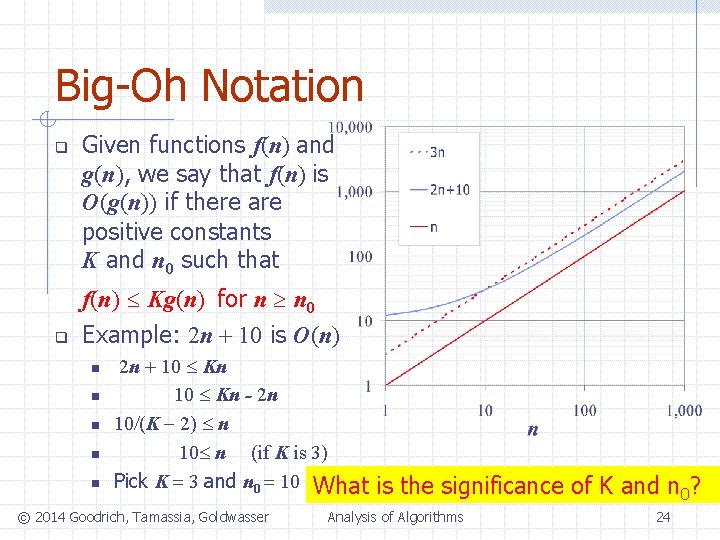
Big-Oh Notation q q Given functions f(n) and g(n), we say that f(n) is O(g(n)) if there are positive constants K and n 0 such that f(n) Kg(n) for n n 0 Example: 2 n + 10 is O(n) n n n 2 n + 10 Kn - 2 n 10/(K 2) n 10 n (if K is 3) Pick K = 3 and n 0 = 10 © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 23
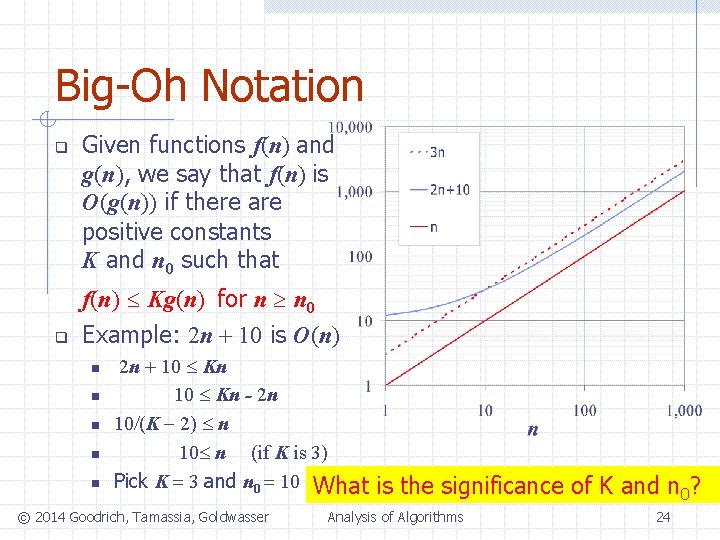
Big-Oh Notation q q Given functions f(n) and g(n), we say that f(n) is O(g(n)) if there are positive constants K and n 0 such that f(n) Kg(n) for n n 0 Example: 2 n + 10 is O(n) n n n 2 n + 10 Kn - 2 n 10/(K 2) n 10 n (if K is 3) Pick K = 3 and n 0 = 10 What © 2014 Goodrich, Tamassia, Goldwasser is the significance of K and n 0? Analysis of Algorithms 24
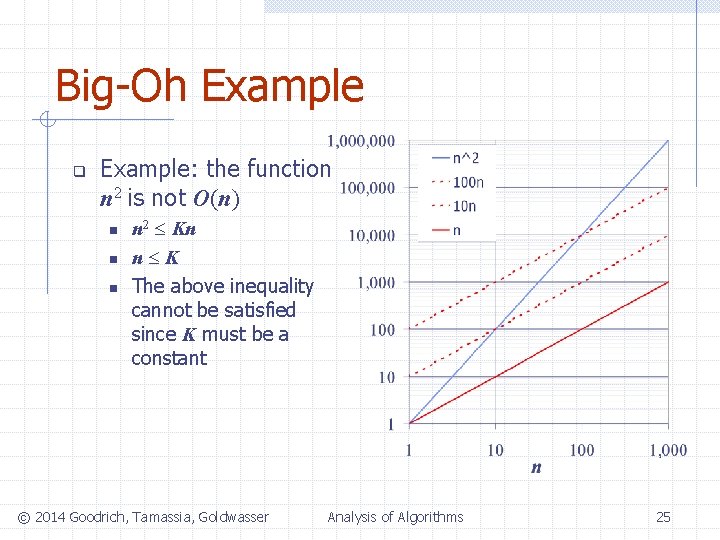
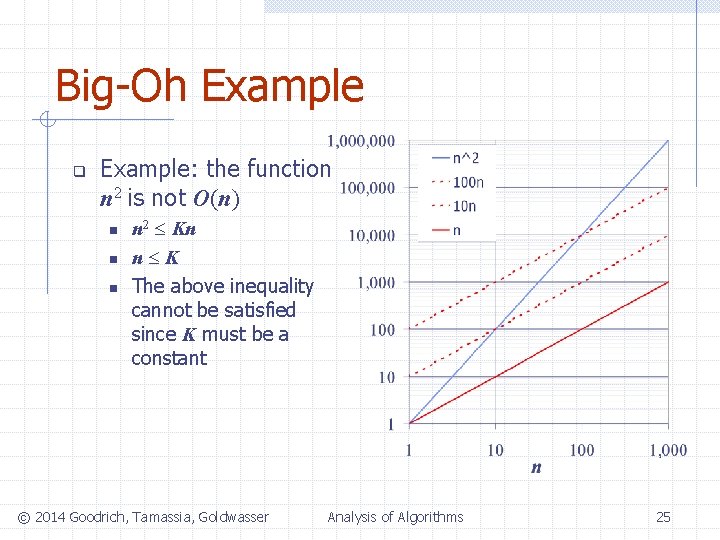
Big-Oh Example q Example: the function n 2 is not O(n) n n 2 Kn n K The above inequality cannot be satisfied since K must be a constant © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 25
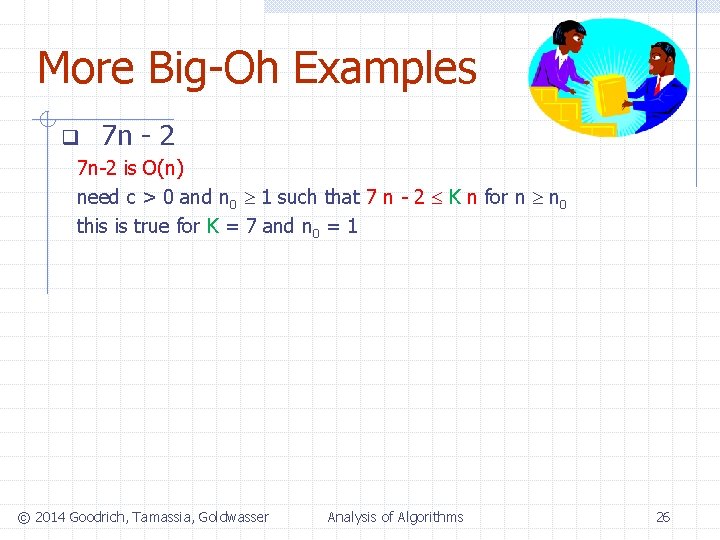
More Big-Oh Examples q 7 n - 2 7 n-2 is O(n) need c > 0 and n 0 1 such that 7 n - 2 K n for n n 0 this is true for K = 7 and n 0 = 1 © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 26
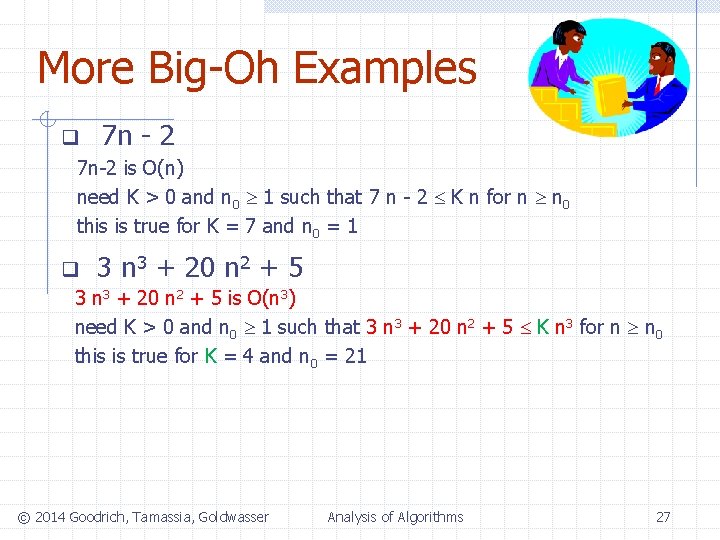
More Big-Oh Examples q 7 n - 2 7 n-2 is O(n) need K > 0 and n 0 1 such that 7 n - 2 K n for n n 0 this is true for K = 7 and n 0 = 1 q 3 n 3 + 20 n 2 + 5 is O(n 3) need K > 0 and n 0 1 such that 3 n 3 + 20 n 2 + 5 K n 3 for n n 0 this is true for K = 4 and n 0 = 21 © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 27
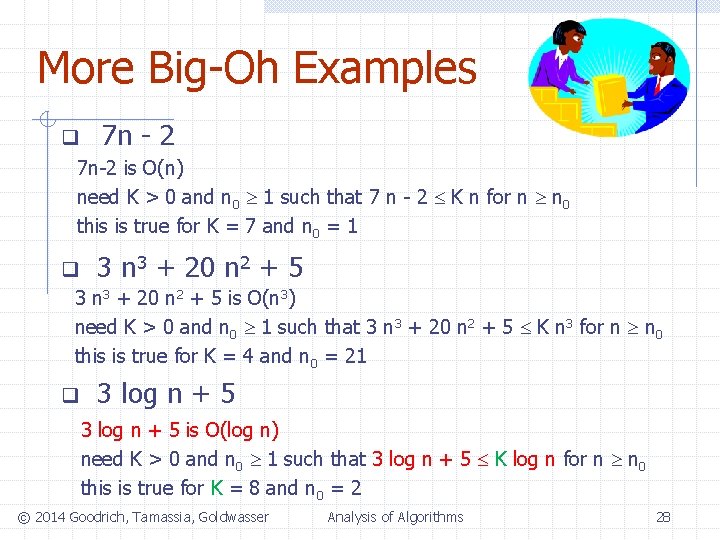
More Big-Oh Examples q 7 n - 2 7 n-2 is O(n) need K > 0 and n 0 1 such that 7 n - 2 K n for n n 0 this is true for K = 7 and n 0 = 1 q 3 n 3 + 20 n 2 + 5 is O(n 3) need K > 0 and n 0 1 such that 3 n 3 + 20 n 2 + 5 K n 3 for n n 0 this is true for K = 4 and n 0 = 21 q 3 log n + 5 is O(log n) need K > 0 and n 0 1 such that 3 log n + 5 K log n for n n 0 this is true for K = 8 and n 0 = 2 © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 28
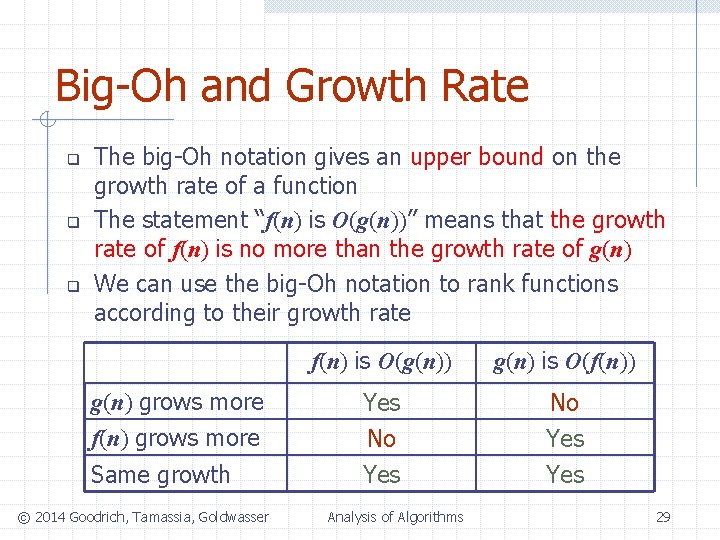
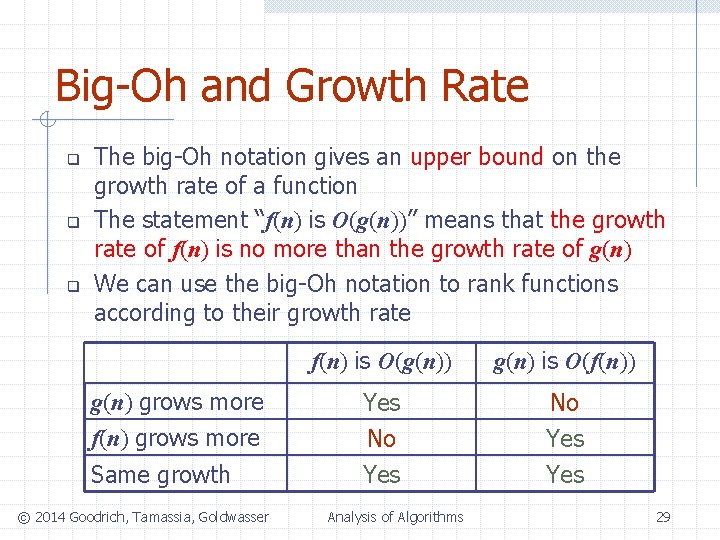
Big-Oh and Growth Rate q q q The big-Oh notation gives an upper bound on the growth rate of a function The statement “f(n) is O(g(n))” means that the growth rate of f(n) is no more than the growth rate of g(n) We can use the big-Oh notation to rank functions according to their growth rate g(n) grows more f(n) grows more Same growth © 2014 Goodrich, Tamassia, Goldwasser f(n) is O(g(n)) g(n) is O(f(n)) Yes No Yes Analysis of Algorithms 29
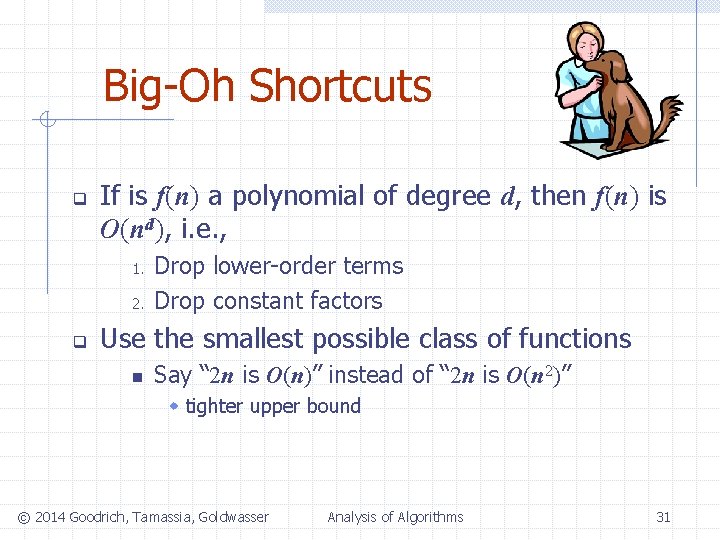
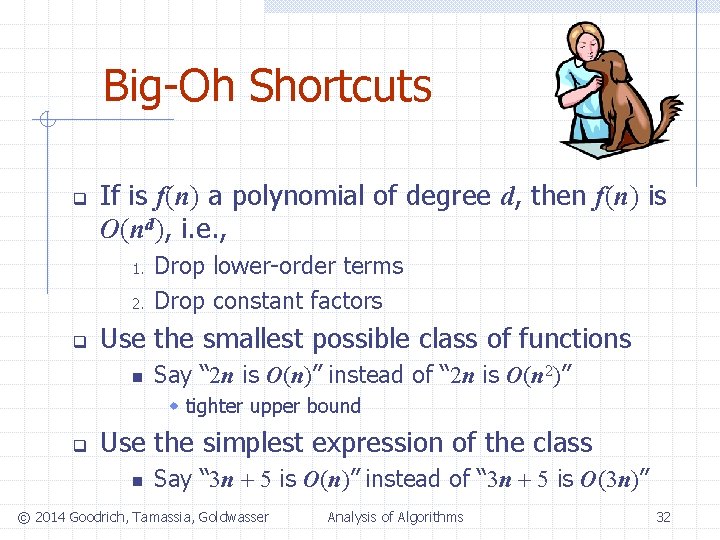
Big-Oh Shortcuts q If is f(n) a polynomial of degree d, then f(n) is O(nd), i. e. , 1. 2. Drop lower-order terms Drop constant factors © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 30
Big-Oh Shortcuts q If is f(n) a polynomial of degree d, then f(n) is O(nd), i. e. , 1. 2. q Drop lower-order terms Drop constant factors Use the smallest possible class of functions n Say “ 2 n is O(n)” instead of “ 2 n is O(n 2)” w tighter upper bound © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 31
Big-Oh Shortcuts q If is f(n) a polynomial of degree d, then f(n) is O(nd), i. e. , 1. 2. q Drop lower-order terms Drop constant factors Use the smallest possible class of functions n Say “ 2 n is O(n)” instead of “ 2 n is O(n 2)” w tighter upper bound q Use the simplest expression of the class n Say “ 3 n + 5 is O(n)” instead of “ 3 n + 5 is O(3 n)” © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 32
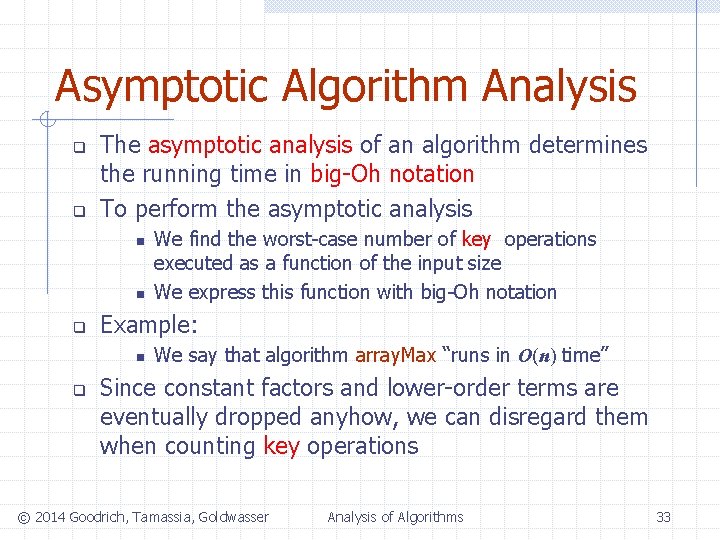
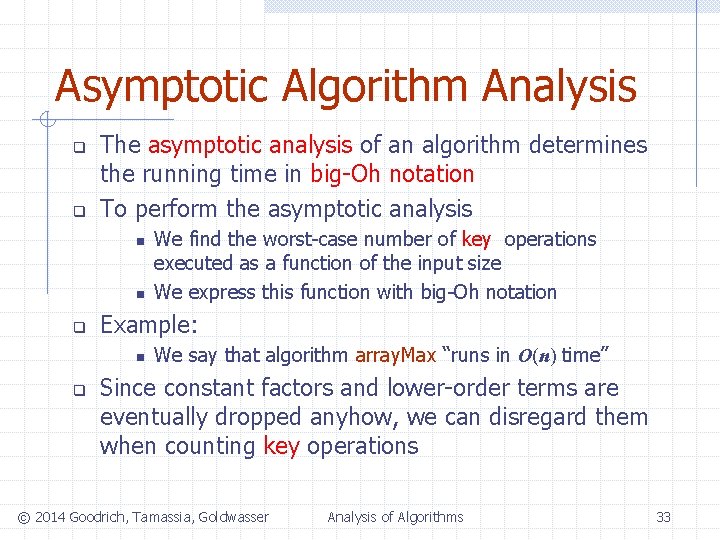
Asymptotic Algorithm Analysis q q The asymptotic analysis of an algorithm determines the running time in big-Oh notation To perform the asymptotic analysis n n q Example: n q We find the worst-case number of key operations executed as a function of the input size We express this function with big-Oh notation We say that algorithm array. Max “runs in O(n) time” Since constant factors and lower-order terms are eventually dropped anyhow, we can disregard them when counting key operations © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 33
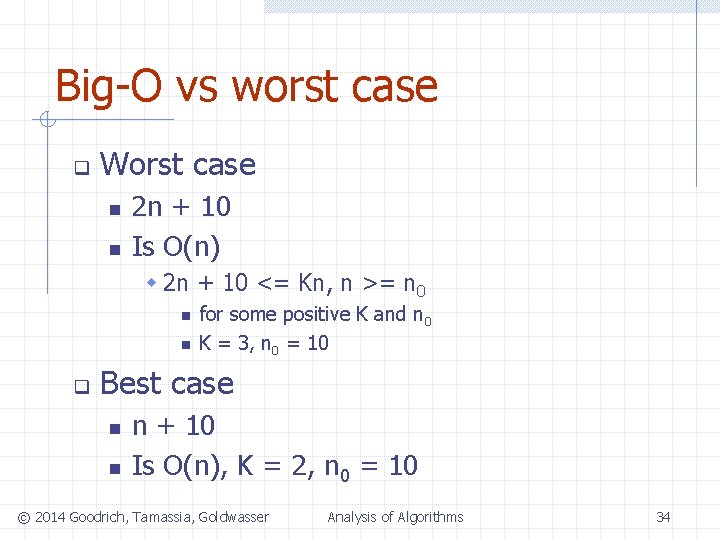
Big-O vs worst case q Worst case n n 2 n + 10 Is O(n) w 2 n + 10 <= Kn, n >= n 0 n n q for some positive K and n 0 K = 3, n 0 = 10 Best case n n n + 10 Is O(n), K = 2, n 0 = 10 © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 34
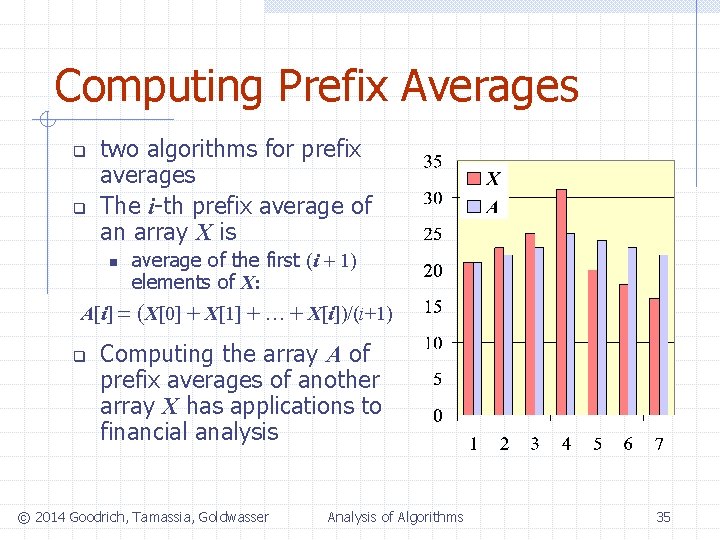
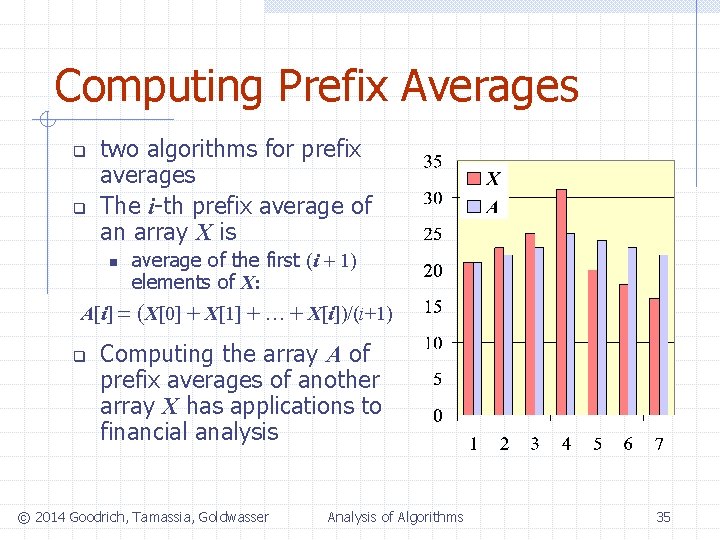
Computing Prefix Averages q q two algorithms for prefix averages The i-th prefix average of an array X is n average of the first (i + 1) elements of X: A[i] = (X[0] + X[1] + … + X[i])/(i+1) q Computing the array A of prefix averages of another array X has applications to financial analysis © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 35
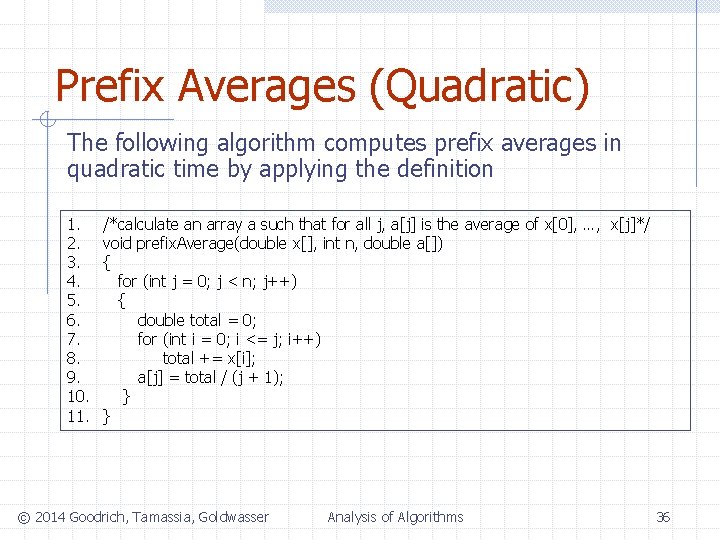
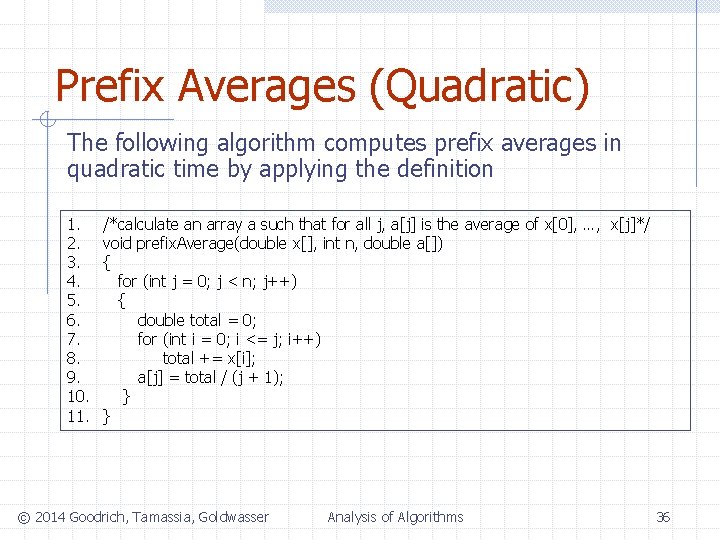
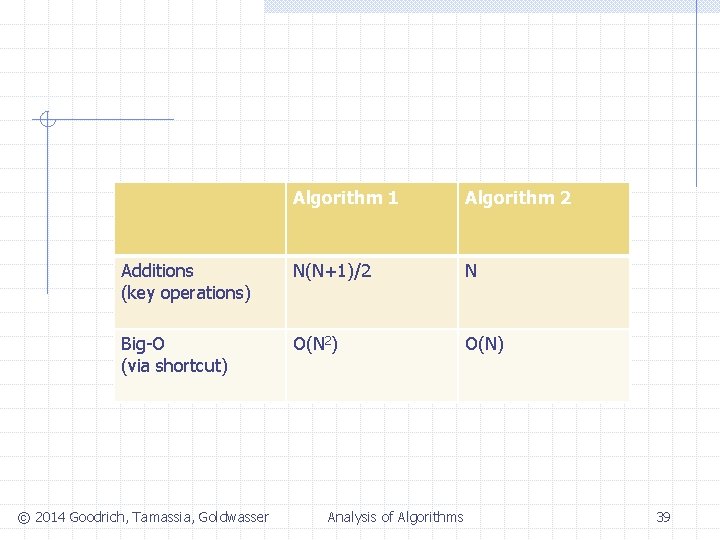
Prefix Averages (Quadratic) The following algorithm computes prefix averages in quadratic time by applying the definition 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. /*calculate an array a such that for all j, a[j] is the average of x[0], …, x[j]*/ void prefix. Average(double x[], int n, double a[]) { for (int j = 0; j < n; j++) { double total = 0; for (int i = 0; i <= j; i++) total += x[i]; a[j] = total / (j + 1); } } © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 36
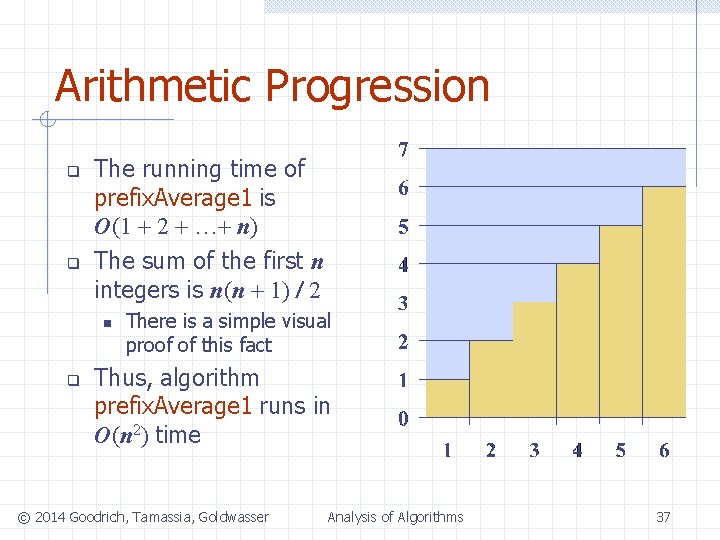
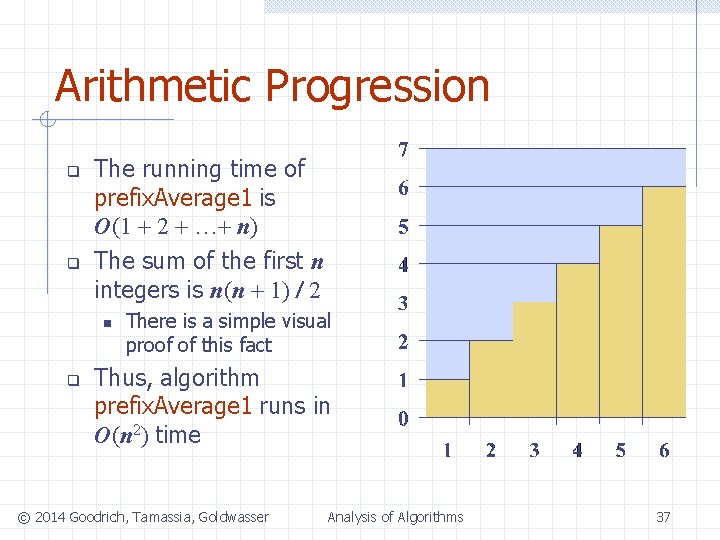
Arithmetic Progression q q The running time of prefix. Average 1 is O(1 + 2 + …+ n) The sum of the first n integers is n(n + 1) / 2 n q There is a simple visual proof of this fact Thus, algorithm prefix. Average 1 runs in O(n 2) time © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 37
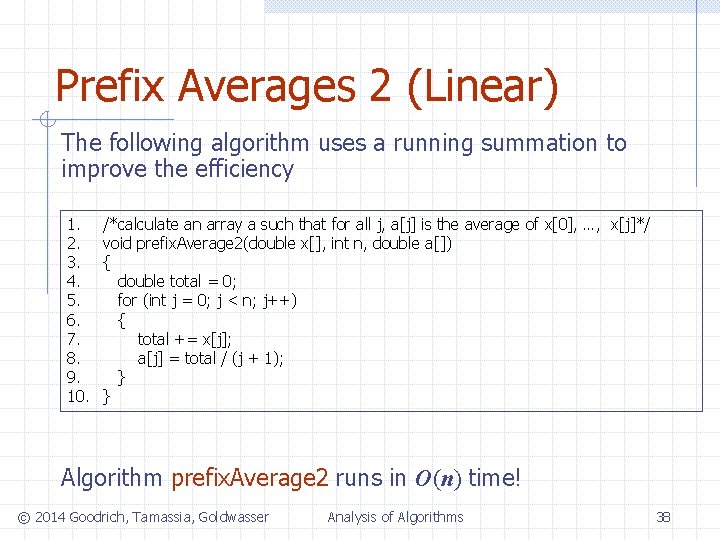
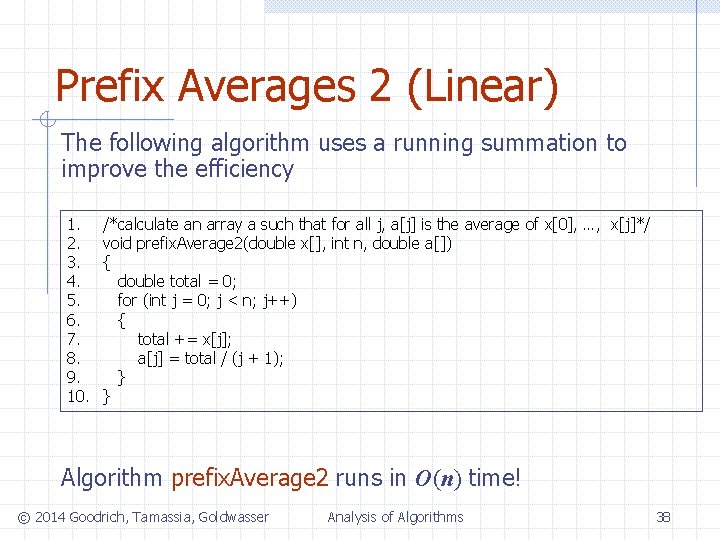
Prefix Averages 2 (Linear) The following algorithm uses a running summation to improve the efficiency 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. /*calculate an array a such that for all j, a[j] is the average of x[0], …, x[j]*/ void prefix. Average 2(double x[], int n, double a[]) { double total = 0; for (int j = 0; j < n; j++) { total += x[j]; a[j] = total / (j + 1); } } Algorithm prefix. Average 2 runs in O(n) time! © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 38
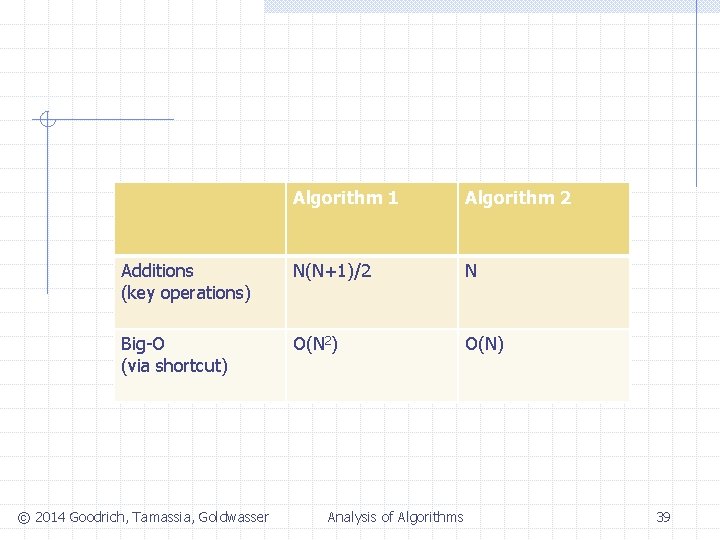
Algorithm 1 Algorithm 2 Additions (key operations) N(N+1)/2 N Big-O (via shortcut) O(N 2) O(N) © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 39
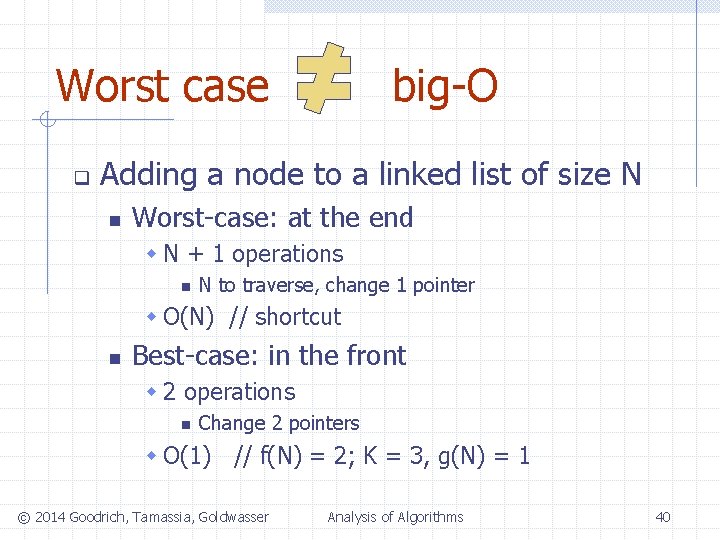
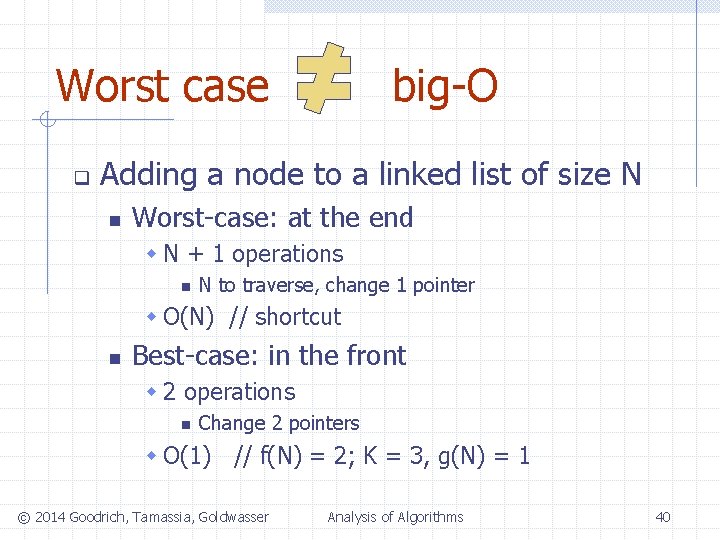
Worst case q big-O Adding a node to a linked list of size N n Worst-case: at the end w N + 1 operations n N to traverse, change 1 pointer w O(N) // shortcut n Best-case: in the front w 2 operations n Change 2 pointers w O(1) // f(N) = 2; K = 3, g(N) = 1 © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 40
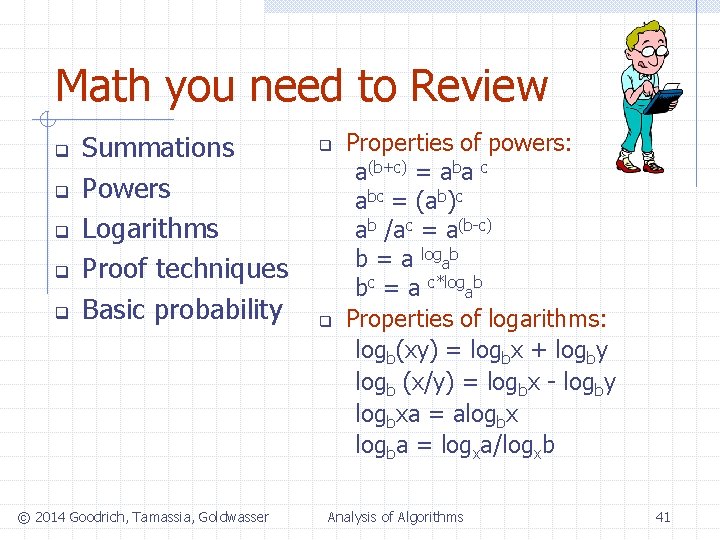
Math you need to Review q q q Summations Powers Logarithms Proof techniques Basic probability © 2014 Goodrich, Tamassia, Goldwasser q q Properties of powers: a(b+c) = aba c abc = (ab)c ab /ac = a(b-c) b = a logab bc = a c*logab Properties of logarithms: logb(xy) = logbx + logby logb (x/y) = logbx - logby logbxa = alogbx logba = logxa/logxb Analysis of Algorithms 41
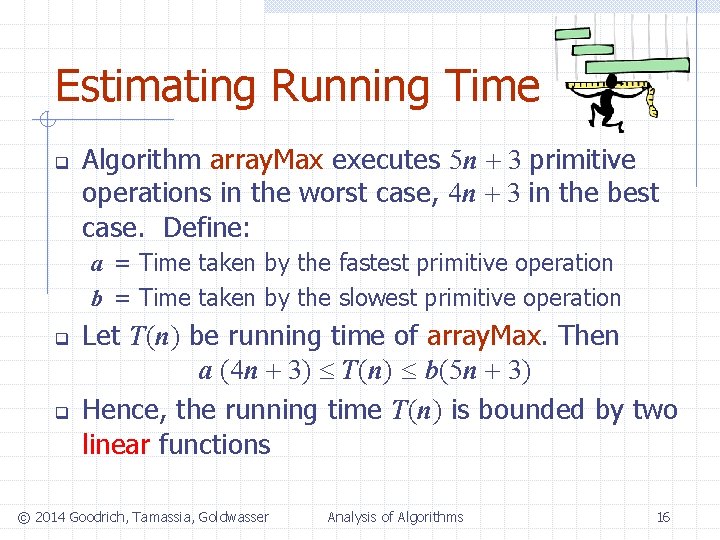
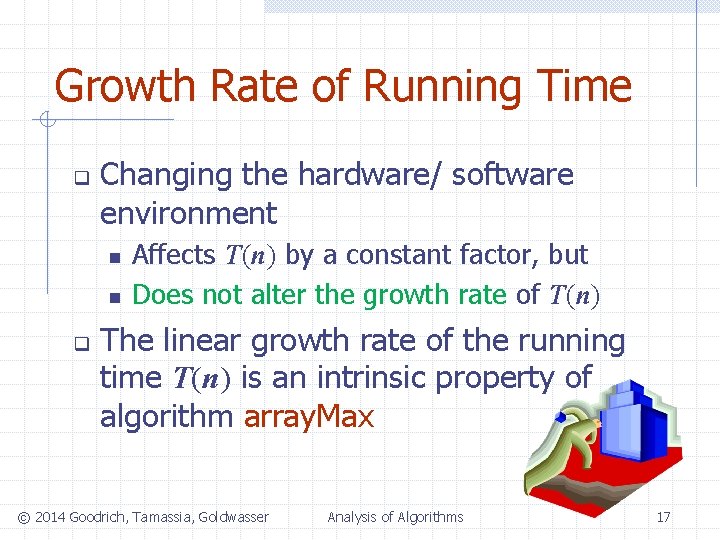
Relatives of Big-Oh big-Omega n f(n) is (g(n)) if there is a constant K > 0 and an integer constant n 0 1 such that f(n) K g(n) for n n 0 © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 42
Relatives of Big-Oh big-Omega n f(n) is (g(n)) if there is a constant K > 0 and an integer constant n 0 1 such that f(n) K g(n) for n n 0 big-Theta n f(n) is (g(n)) if there are constants K’ > 0 and K’’ > 0 and an integer constant n 0 1 such that K’g(n) f(n) K’’g(n) for n n 0 © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 43
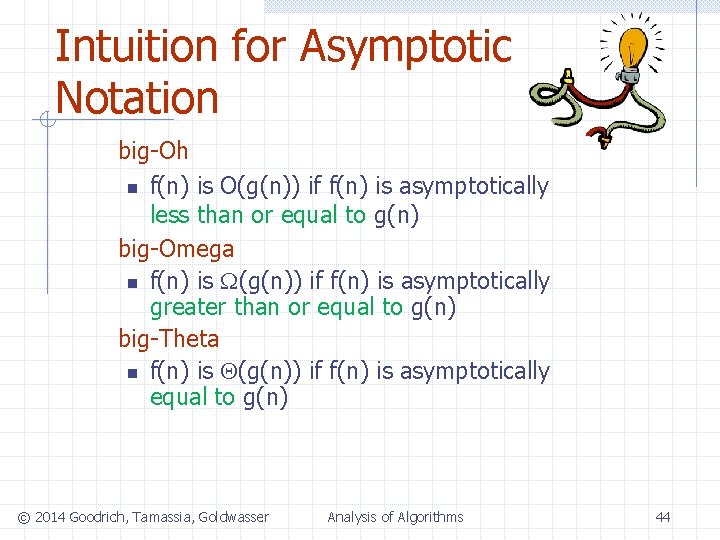
Intuition for Asymptotic Notation big-Oh n f(n) is O(g(n)) if f(n) is asymptotically less than or equal to g(n) big-Omega n f(n) is (g(n)) if f(n) is asymptotically greater than or equal to g(n) big-Theta n f(n) is (g(n)) if f(n) is asymptotically equal to g(n) © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 44
Example of Big-Oh and Relatives q 2 n + 10 is O(n) n n n 2 n + 10 Kn - 2 n 10/(K 2) n 10 n (let K be 3) K = 3 and n 0 = 10 © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 45
Example of Big-Oh and Relatives q 2 n + 10 is O(n) n n n q 2 n + 10 Kn - 2 n 10/(K 2) n 10 n (let K be 3) K = 3 and n 0 = 10 2 n + 10 is (n) n n n 2 n + 10 K’n (2 -K’)n + 10 0 (let K’ be 1) n -10 K’ = 1 and n 0 = 1 © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 46
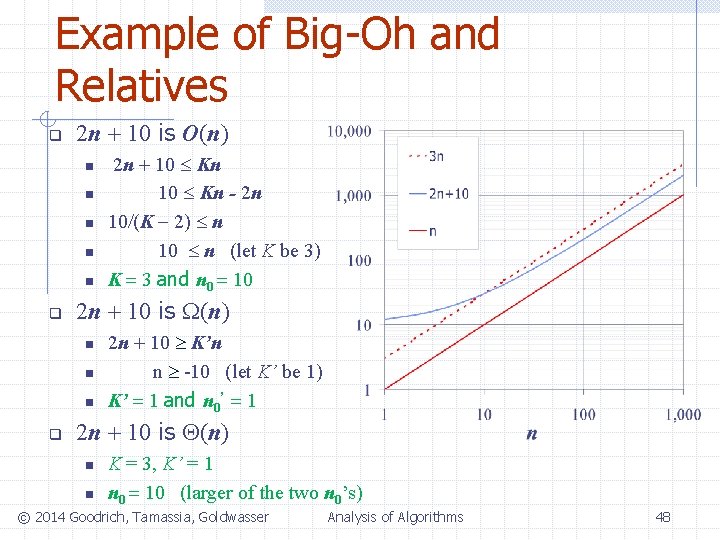
Example of Big-Oh and Relatives q 2 n + 10 is O(n) n n n q 2 n + 10 is (n) n n n q 2 n + 10 Kn - 2 n 10/(K 2) n 10 n (let K be 3) K = 3 and n 0 = 10 2 n + 10 K’n n -10 (let K’ be 1) K’ = 1 and n 0’ = 1 2 n + 10 is (n) n n K = 3, K’ = 1 n 0 = 10 (larger of the two n 0’s) © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 47
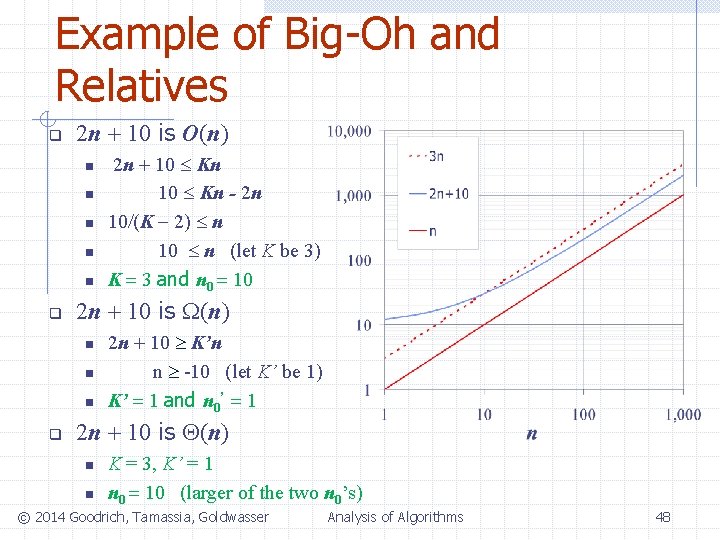
Example of Big-Oh and Relatives q 2 n + 10 is O(n) n n n q 2 n + 10 is (n) n n n q 2 n + 10 Kn - 2 n 10/(K 2) n 10 n (let K be 3) K = 3 and n 0 = 10 2 n + 10 K’n n -10 (let K’ be 1) K’ = 1 and n 0’ = 1 2 n + 10 is (n) n n K = 3, K’ = 1 n 0 = 10 (larger of the two n 0’s) © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 48
Example Uses of the Relatives of Big-Oh n 5 n 2 is (n 2) if there is a constant K > 0 and an integer constant n 0 1 such that 5 n 2 K n 2 for n n 0 let K = 5 and n 0 = 1 © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 49
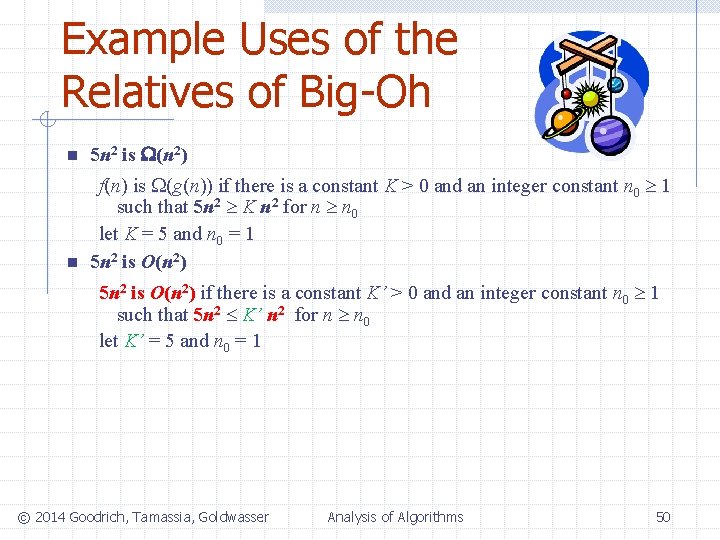
Example Uses of the Relatives of Big-Oh n 5 n 2 is (n 2) n f(n) is (g(n)) if there is a constant K > 0 and an integer constant n 0 1 such that 5 n 2 K n 2 for n n 0 let K = 5 and n 0 = 1 5 n 2 is O(n 2) if there is a constant K’ > 0 and an integer constant n 0 1 such that 5 n 2 K’ n 2 for n n 0 let K’ = 5 and n 0 = 1 © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 50
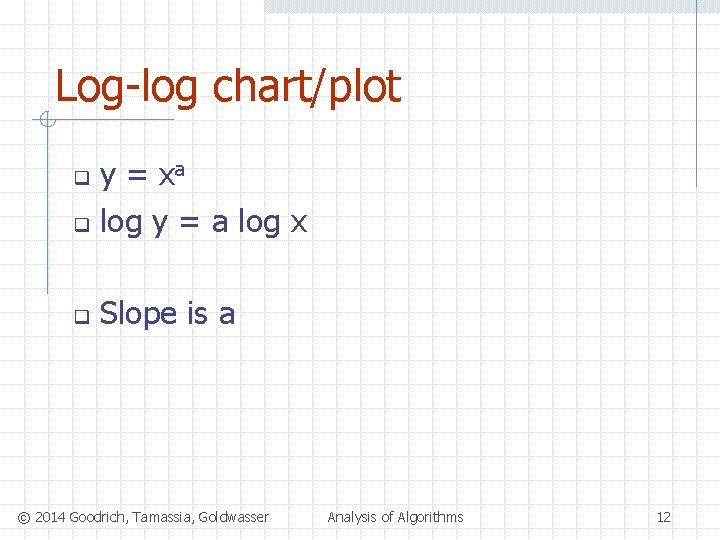
Example Uses of the Relatives of Big-Oh n 5 n 2 is (n 2) n f(n) is (g(n)) if there is a constant K > 0 and an integer constant n 0 1 such that 5 n 2 K n 2 for n n 0 let K = 5 and n 0 = 1 5 n 2 is O(n 2) 5 n 2 is O(n) if there is a constant k > 0 and an integer constant n 0 1 such that 5 n 2 K’ n 2 for n n 0 let K’ = 5 and n 0 = 1 n 5 n 2 is (n 2) if 5 n 2 is (n 2) and O(n 2). let K = 5, K’ = 5 and n 0 = 1 © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 51
![Summary Ogn upper bound Original function fn time space gn lower bound 2014 Summary O(g(n)) [upper bound] Original function f(n) [time, space] (g(n)) [lower bound] © 2014](https://slidetodoc.com/presentation_image_h2/800b35371d4f53208cd441a5b3bf4e62/image-52.jpg)
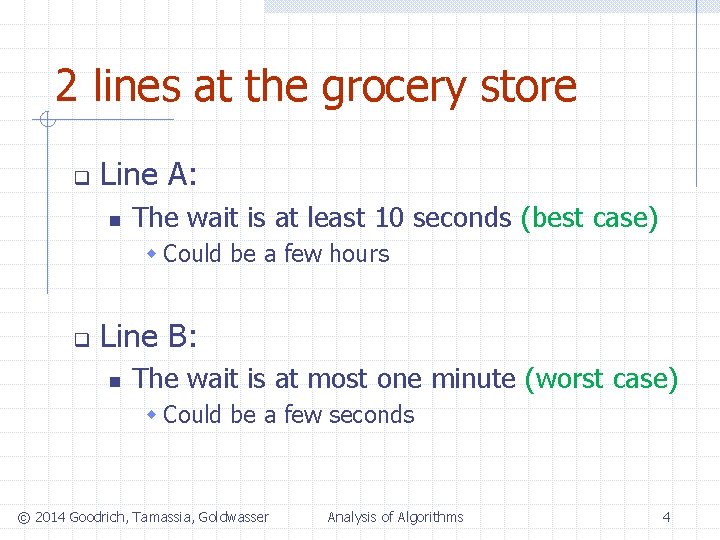
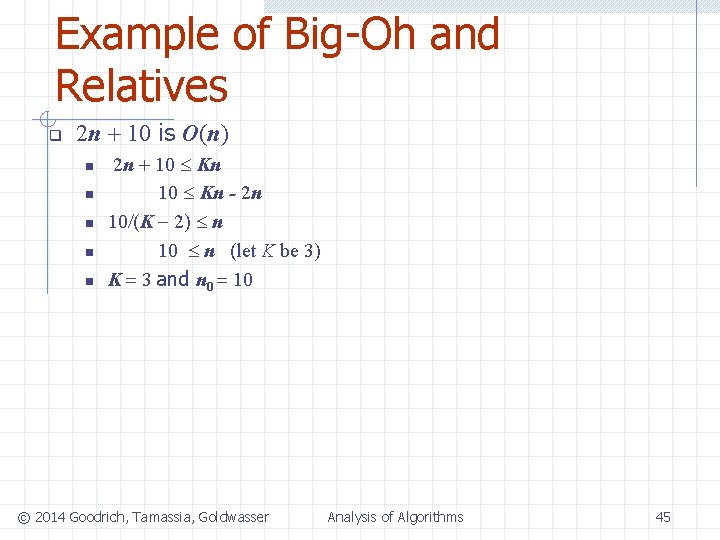
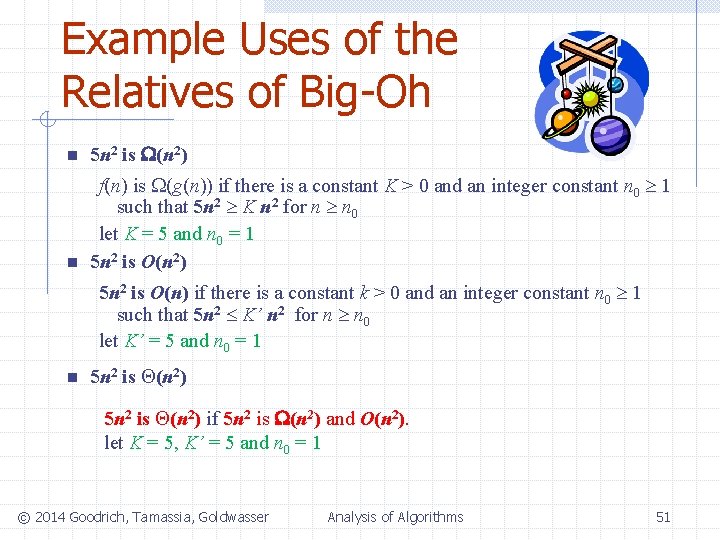
Summary O(g(n)) [upper bound] Original function f(n) [time, space] (g(n)) [lower bound] © 2014 Goodrich, Tamassia, Goldwasser Analysis of Algorithms 52