An Overview of Common Criteria Protection Profiles Mara
![References • [NIST, 2003] “Common Criteria for IT Security Evaluation: Common Language to Express References • [NIST, 2003] “Common Criteria for IT Security Evaluation: Common Language to Express](https://slidetodoc.com/presentation_image_h2/1d019c409cd81bcbe96a8f728285e4a3/image-25.jpg)
- Slides: 25
An Overview of Common Criteria Protection Profiles María M. Larrondo Petrie, Ph. D March 26, 2004
Overview • Common Criteria CC • Information Assurance IATFF • CC Protection Profiles – Structure – Development Tools • Case Study – Role Based Access Control • References
Common Criteria • Common Criteria (CC) – replaces security criteria and processes used in the (14) common criteria countries with the goal that product evaluations conducted in one country would be accepted in other countries • US entities involved in CC is National Information Assurance Partnership NIAP, a partnership between – National Institute of Standards and Technology NIST – National Security Agency NSA
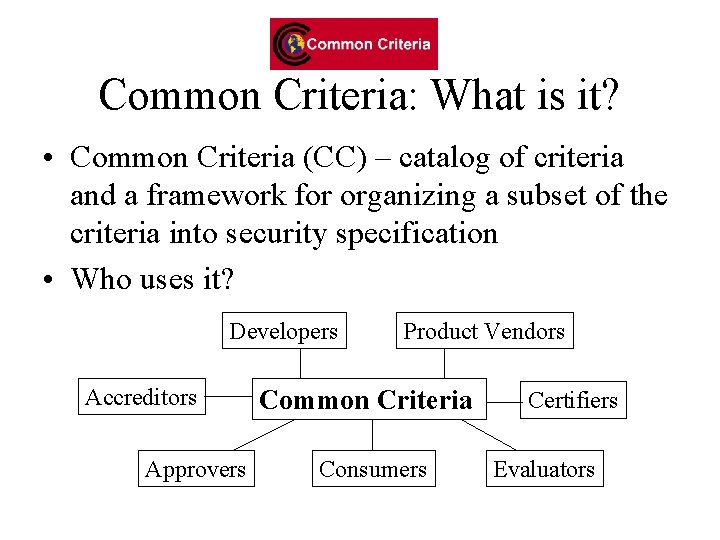
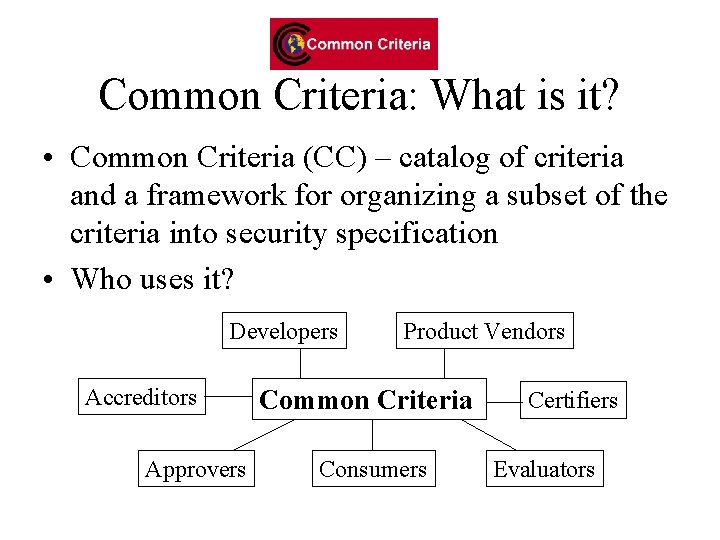
Common Criteria: What is it? • Common Criteria (CC) – catalog of criteria and a framework for organizing a subset of the criteria into security specification • Who uses it? Developers Accreditors Approvers Product Vendors Common Criteria Consumers Certifiers Evaluators
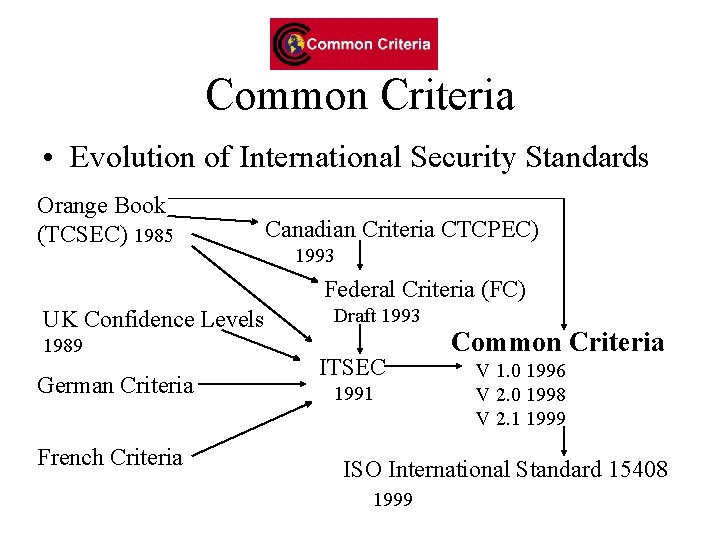
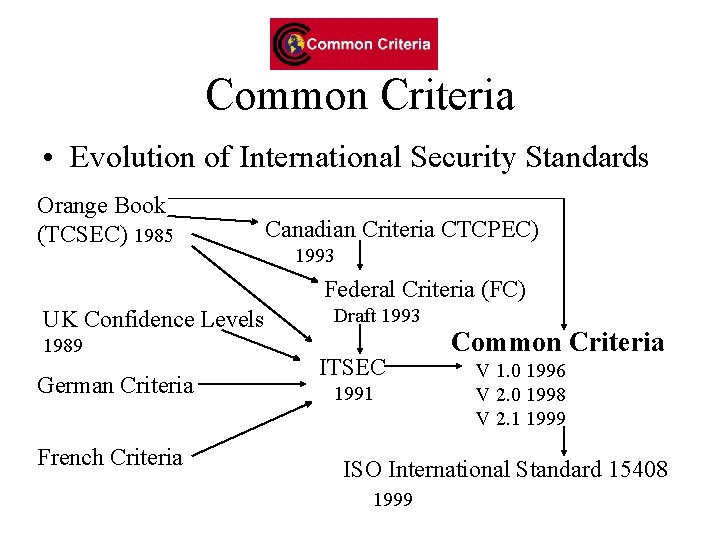
Common Criteria • Evolution of International Security Standards Orange Book (TCSEC) 1985 Canadian Criteria CTCPEC) 1993 Federal Criteria (FC) UK Confidence Levels 1989 German Criteria French Criteria Draft 1993 ITSEC 1991 Common Criteria V 1. 0 1996 V 2. 0 1998 V 2. 1 1999 ISO International Standard 15408 1999
Common Criteria - Terminology • PP - Protection Profile– implementation independent criteria • SP - Security Profile– implementation dependent criteria • TOE – Target of Evaluation – what you are describing – your product • EAL – Evaluation Assurance Level – CC assurance levels – 7 hierarchical – EAL 1 thru EAL 7 – EAL 1 (least amount) • CEM – Common Evaluation Method – set of steps for validating assurance requirements in an SP – Only addresses levels EAL 1 through EAL 4.
CC Protection Profile (PP) • High-level expression of desired security properties (i. e. security environment, security objectives and security requirements) • A mechanism to provide Consumers the ability to specify their security requirements • Generic so multiple implementations may meet the stated requirements • PP represents “I want” from giles. ppt
CC Security Target (ST) • High-level expression of claimed security properties • A mechanism to provide Vendors the ability to make claims regarding their security products • Specific to an implementation • ST represents “I provide”
IATFF • What? A security guidance document developed by NSA’s ISSO organization with support from security advocates in government and industry • Constraints? – Unclassified – Published on the Internet • Primary Coordination forum? Information Assurance Technical Framework Forum (IATFF)
IATF • Help government users become wiser consumers of implementing security solutions • Assist industry in understanding the government’s needs and the nature of the desired solutions to these needs • Focus Government and Industry investment resources on the security technology gaps
How does the Framework help Government Users? • By describing their needs to the industry providers • By “suggesting” the important characteristics of security solutions to different classes of problems • By providing an assessment of the security technology available on the open market
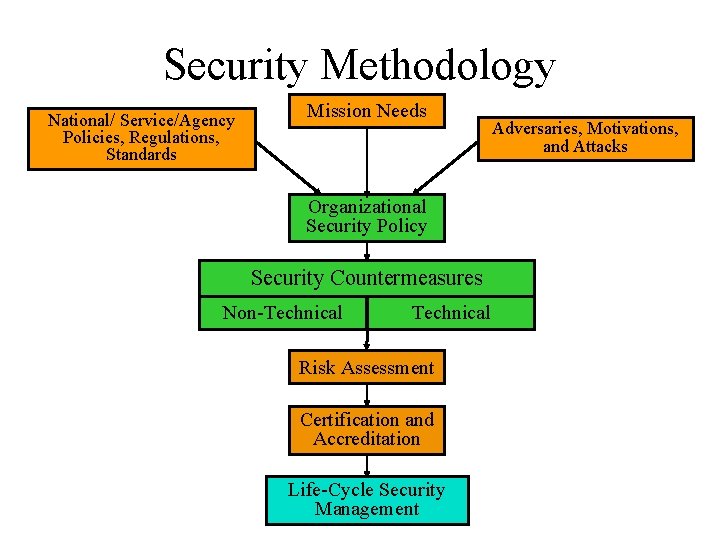
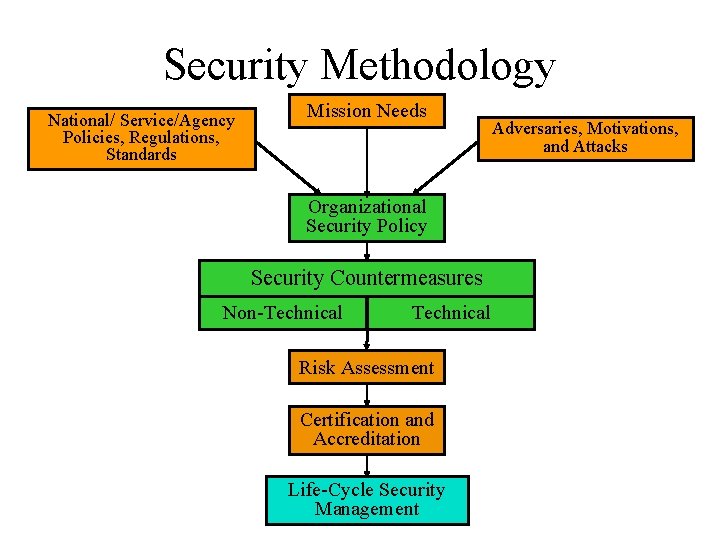
Security Methodology National/ Service/Agency Policies, Regulations, Standards Mission Needs Organizational Security Policy Security Countermeasures Non-Technical Risk Assessment Certification and Accreditation Life-Cycle Security Management Adversaries, Motivations, and Attacks
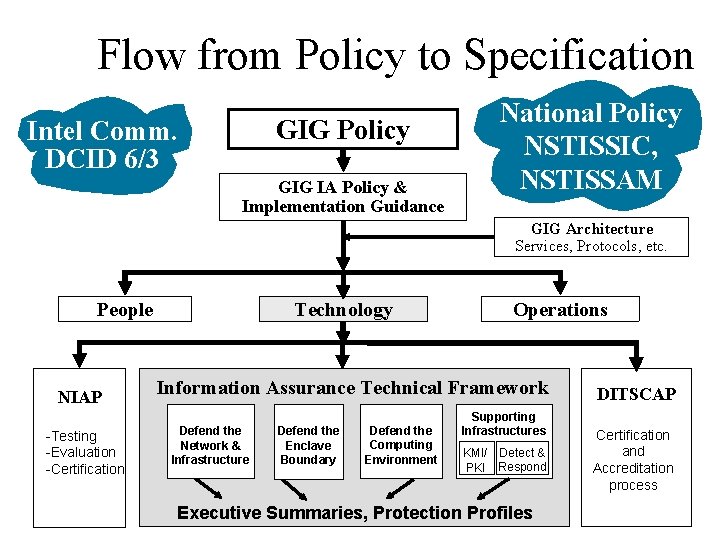
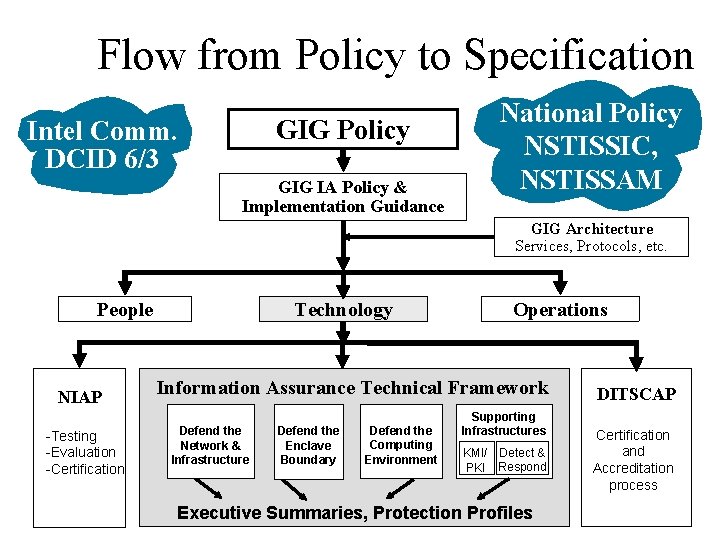
Flow from Policy to Specification GIG Policy Intel Comm. DCID 6/3 GIG IA Policy & Implementation Guidance National Policy NSTISSIC, NSTISSAM GIG Architecture Services, Protocols, etc. People NIAP -Testing -Evaluation -Certification Technology Operations Information Assurance Technical Framework Defend the Network & Infrastructure Defend the Enclave Boundary Defend the Computing Environment Supporting Infrastructures KMI/ Detect & PKI Respond Executive Summaries, Protection Profiles DITSCAP Certification and Accreditation process
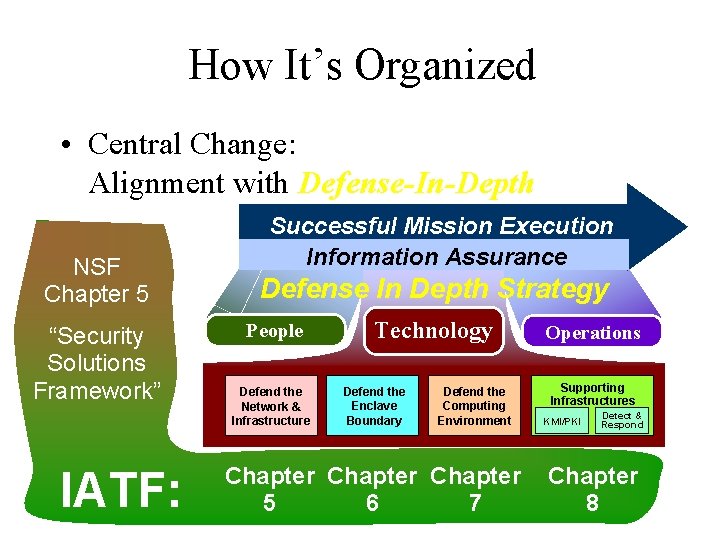
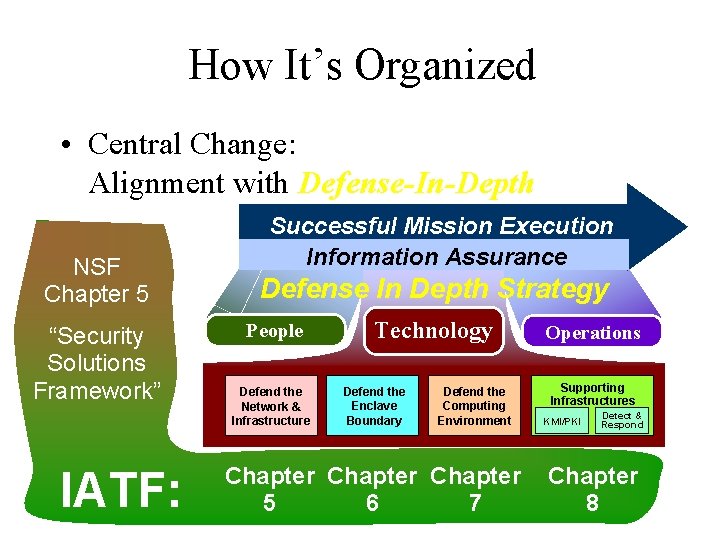
How It’s Organized • Central Change: Alignment with Defense-In-Depth NSF Chapter 5 “Security Solutions Framework” IATF: Successful Mission Execution Information Assurance Defense In Depth Strategy People Defend the Network & Infrastructure Technology Defend the Enclave Boundary Defend the Computing Environment Chapter 5 6 7 Operations Supporting Infrastructures KMI/PKI Detect & Respond Chapter 8
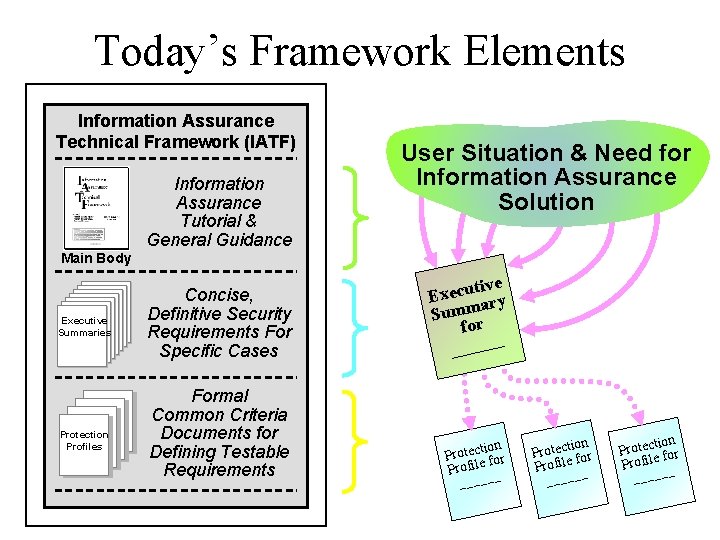
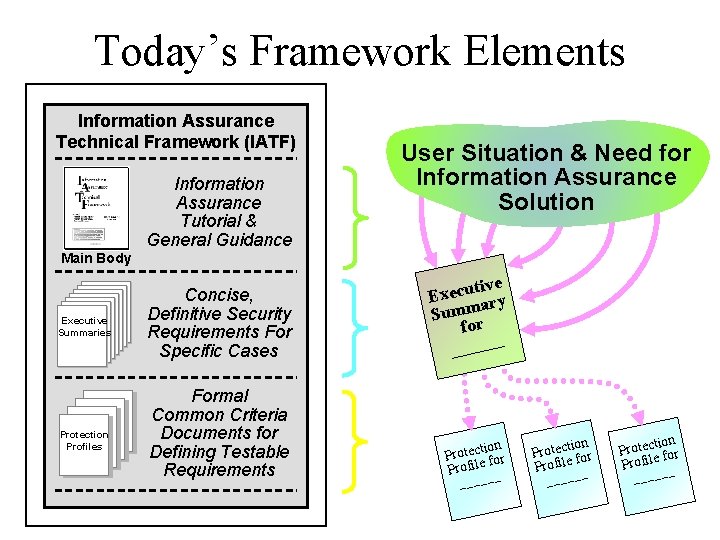
Today’s Framework Elements Information Assurance Technical Framework (IATF) Information Assurance Tutorial & General Guidance IATF Release 2. 0, Figure 1 -2, Composition of the IATF User Situation & Need for Information Assurance Solution The “Document” Main Body Executive Summaries Protection Profiles Concise, Definitive Security Requirements For Specific Cases Formal Common Criteria Documents for Defining Testable Requirements e ecutiv y Ex. Appendix F: ar Summ for Case Specific Guidance _ _____ (aka “executive summaries”) Appendix G: n otectioor tion ection r t c o P e r t o P r P f for Protection Profile __ rofile _ PProfiles Profile __ ____ _ __
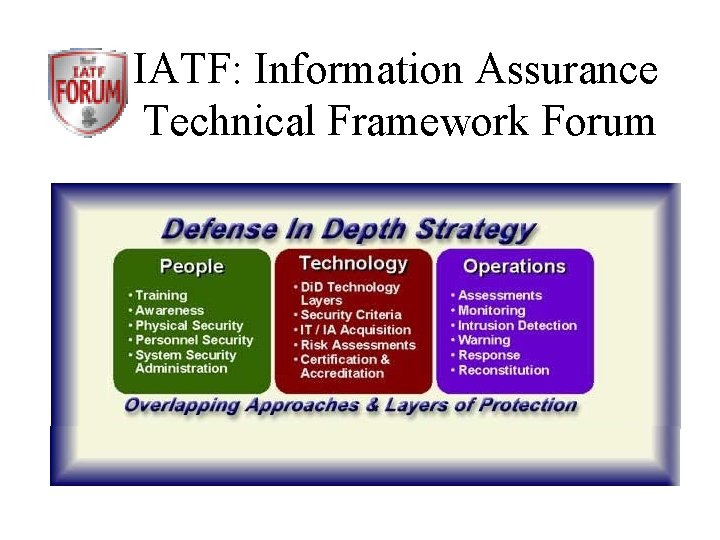
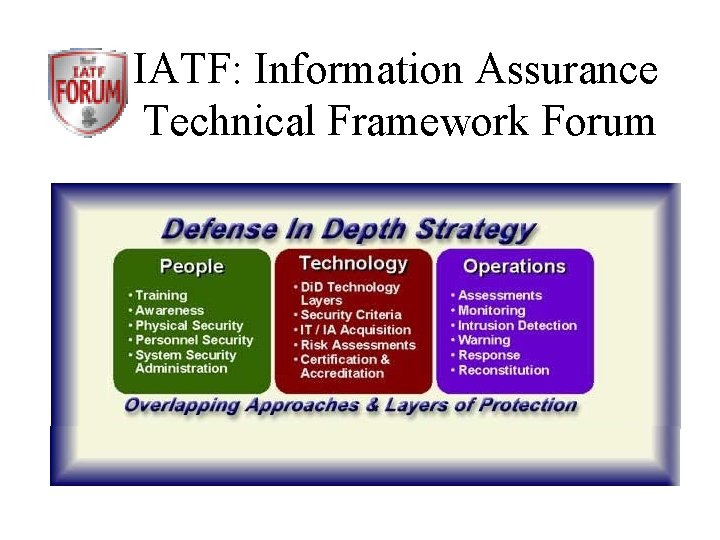
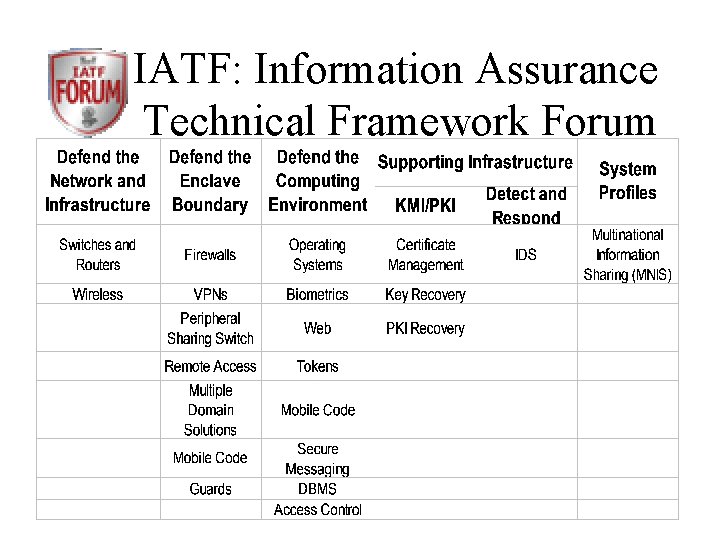
IATF: Information Assurance Technical Framework Forum • • http: //www. iatf. net/protection_profiles/profiles. cfm
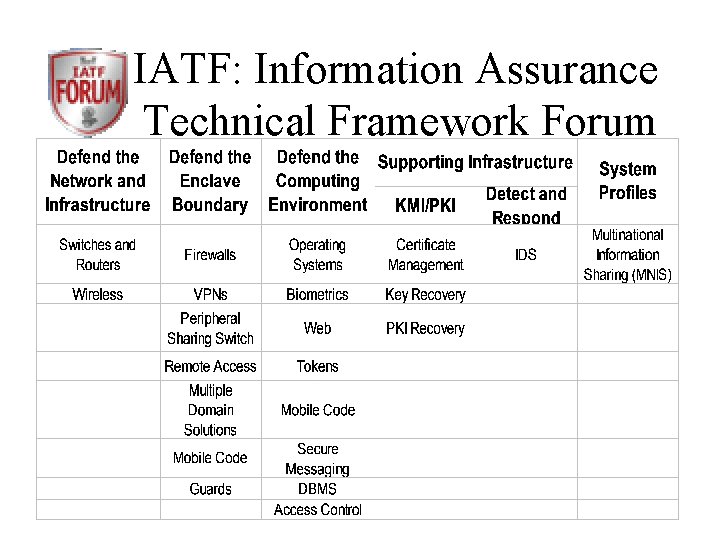
IATF: Information Assurance Technical Framework Forum
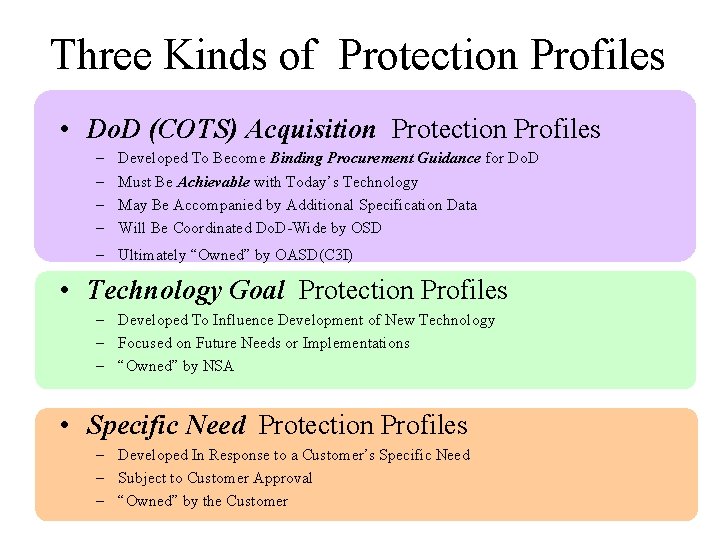
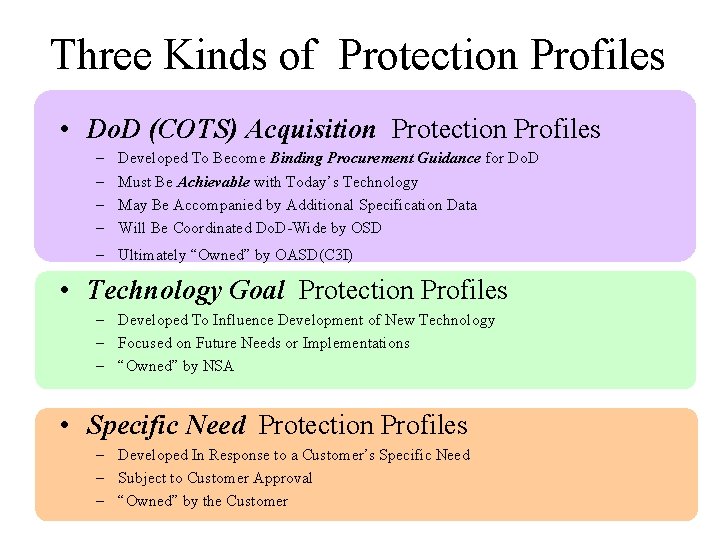
Three Kinds of Protection Profiles • Do. D (COTS) Acquisition Protection Profiles – – Developed To Become Binding Procurement Guidance for Do. D Must Be Achievable with Today’s Technology May Be Accompanied by Additional Specification Data Will Be Coordinated Do. D-Wide by OSD – Ultimately “Owned” by OASD(C 3 I) • Technology Goal Protection Profiles – Developed To Influence Development of New Technology – Focused on Future Needs or Implementations – “Owned” by NSA • Specific Need Protection Profiles – Developed In Response to a Customer’s Specific Need – Subject to Customer Approval – “Owned” by the Customer
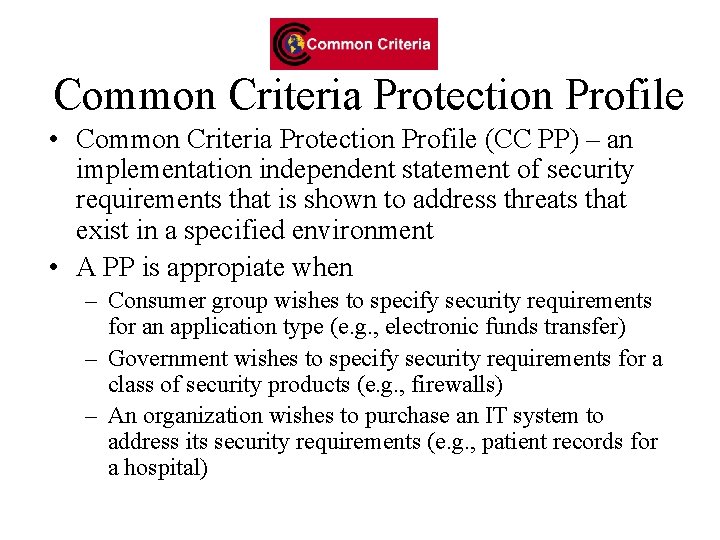
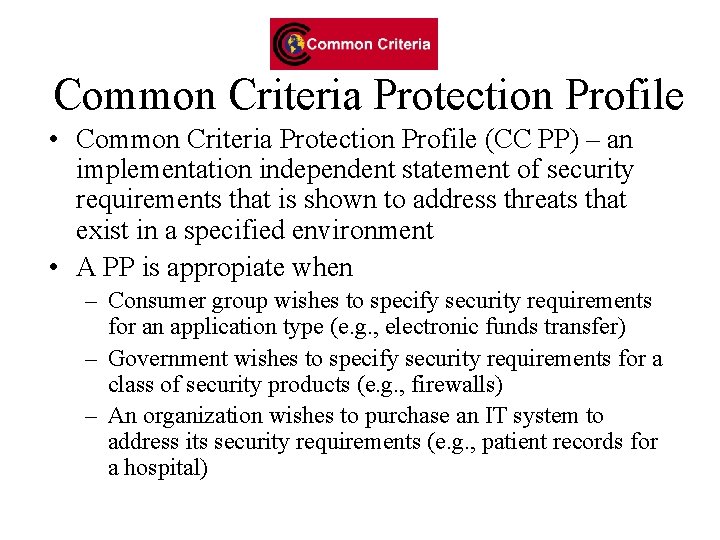
Common Criteria Protection Profile • Common Criteria Protection Profile (CC PP) – an implementation independent statement of security requirements that is shown to address threats that exist in a specified environment • A PP is appropiate when – Consumer group wishes to specify security requirements for an application type (e. g. , electronic funds transfer) – Government wishes to specify security requirements for a class of security products (e. g. , firewalls) – An organization wishes to purchase an IT system to address its security requirements (e. g. , patient records for a hospital)
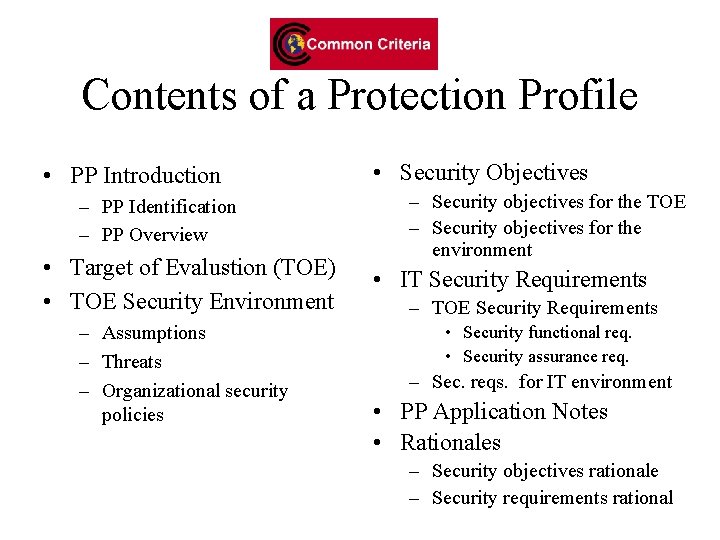
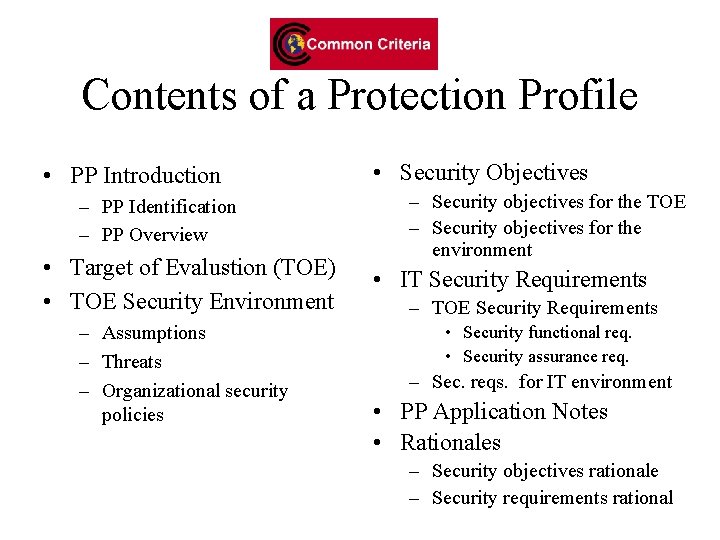
Contents of a Protection Profile • PP Introduction – PP Identification – PP Overview • Target of Evalustion (TOE) • TOE Security Environment – Assumptions – Threats – Organizational security policies • Security Objectives – Security objectives for the TOE – Security objectives for the environment • IT Security Requirements – TOE Security Requirements • Security functional req. • Security assurance req. – Sec. reqs. for IT environment • PP Application Notes • Rationales – Security objectives rationale – Security requirements rational
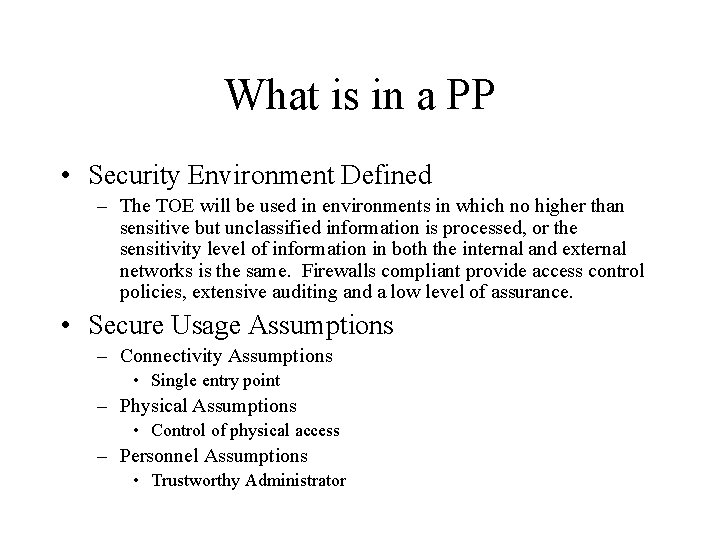
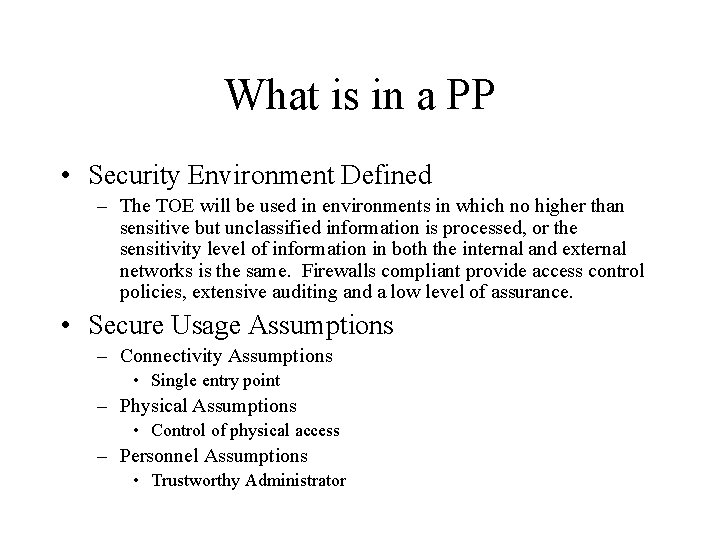
What is in a PP • Security Environment Defined – The TOE will be used in environments in which no higher than sensitive but unclassified information is processed, or the sensitivity level of information in both the internal and external networks is the same. Firewalls compliant provide access control policies, extensive auditing and a low level of assurance. • Secure Usage Assumptions – Connectivity Assumptions • Single entry point – Physical Assumptions • Control of physical access – Personnel Assumptions • Trustworthy Administrator
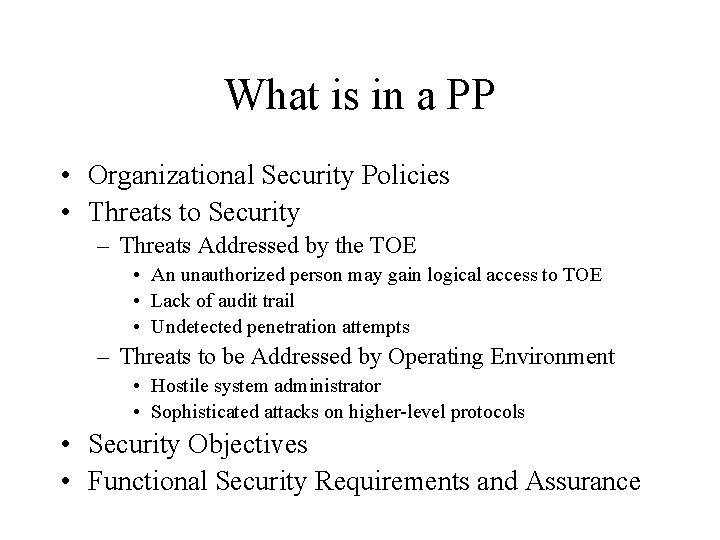
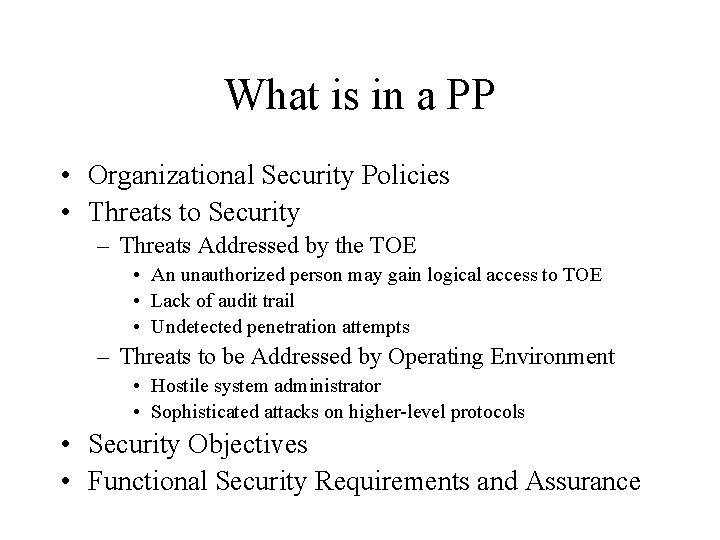
What is in a PP • Organizational Security Policies • Threats to Security – Threats Addressed by the TOE • An unauthorized person may gain logical access to TOE • Lack of audit trail • Undetected penetration attempts – Threats to be Addressed by Operating Environment • Hostile system administrator • Sophisticated attacks on higher-level protocols • Security Objectives • Functional Security Requirements and Assurance
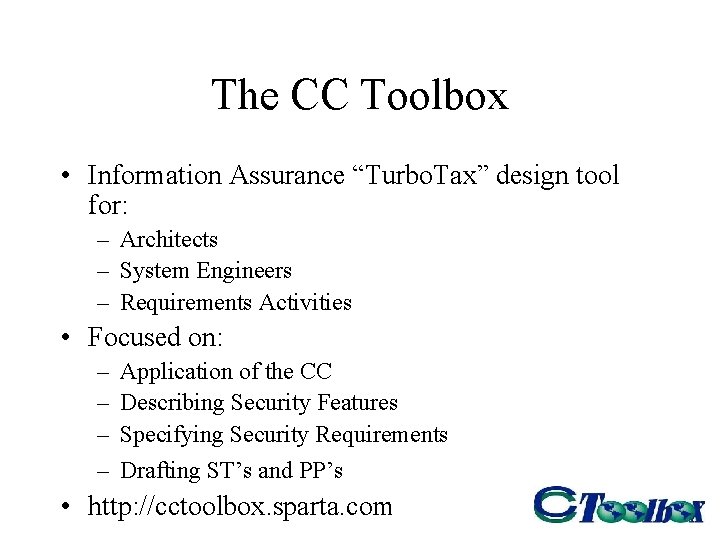
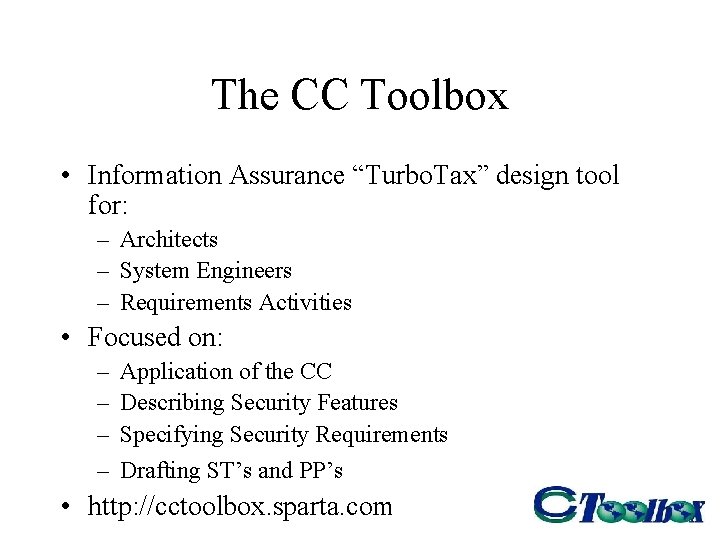
The CC Toolbox • Information Assurance “Turbo. Tax” design tool for: – Architects – System Engineers – Requirements Activities • Focused on: – – Application of the CC Describing Security Features Specifying Security Requirements Drafting ST’s and PP’s • http: //cctoolbox. sparta. com
Registered Protection Profiles • Sets of registered Protection Profiles exist at the following locations: – http: //www. radium. ncsc. mil/tpep/protection_profiles/i ndex. html – http: //www. cesg. gov. uk/cchtml/ippr/list_by_type. html – http: //csrc. nist. gov/cc/pp/pplist. htm – (currently being updated so I could not look up the list to see if it including what we are trying to propose) – http: //www. scssi. gouv. fr/present/si/ccsti/pp. html
![References NIST 2003 Common Criteria for IT Security Evaluation Common Language to Express References • [NIST, 2003] “Common Criteria for IT Security Evaluation: Common Language to Express](https://slidetodoc.com/presentation_image_h2/1d019c409cd81bcbe96a8f728285e4a3/image-25.jpg)
References • [NIST, 2003] “Common Criteria for IT Security Evaluation: Common Language to Express Common Needs”, Computer Security Resource Center (CSRC), National Institute of Standards and Technology, created 12 November 2002, last updated 19 May 2003, http: //csrc. nist. gov/cc/ • “Common Criteria for Information Technology Security Evaluation, User Guide, CESG, UK and NIST, USA, Syntegra, October 2999. • [Towns and Britton, 1999] Towns, M. and K. Britton. Protection Profile Development Workshop: Student Handbook, Ver. 2. 0, NIAP/NIST, 2000. [Grainger 2000] Granger, G. Common Criteria Tools, Mitretek Systems, May 25, 2000.