An Image Fragile Watermark Scheme Based on Chaotic
An Image Fragile Watermark Scheme Based on Chaotic Image Pattern and Pixel-pairs Source: Applied Mathematics and Computation, article in press, 2006 Author: Shao-Hui Liu, Hong-Xun Yao, Wen Gao and Yong. Liang Liu Speaker: Yung-Chen Chou Date: Nov. 16, 2006 Yung-Chen Chou
Outline n n n Introduction Two typical attacks The watermarking algorithm Experiments Conclusions Yung-Chen Chou 2
Introduction n Robust watermarking n n n Copyright protection Anti general image processing Fragile watermarking n n Semi fragile soft authentication Complete fragile hard authentication Yung-Chen Chou 3
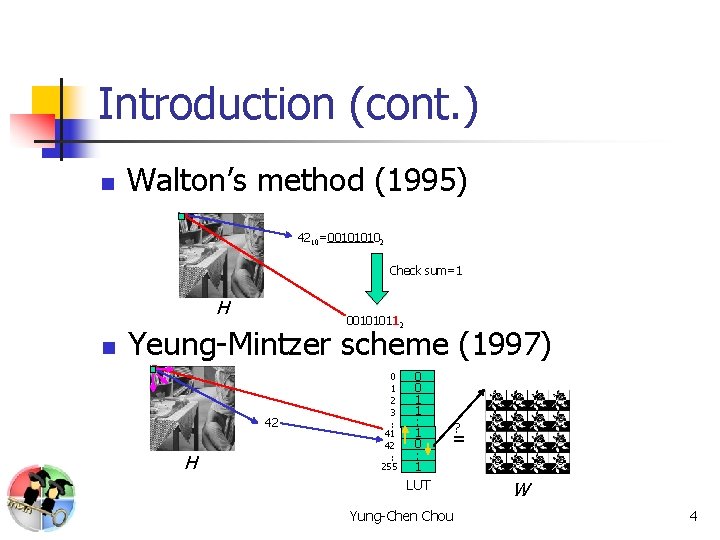
Introduction (cont. ) n Walton’s method (1995) 4210=001010102 Check sum=1 H n 001010112 Yeung-Mintzer scheme (1997) 42 H 0 1 2 3 : 41 42 : 255 0 0 1 1 : 1 0 : 1 ? = LUT Yung-Chen Chou W 4
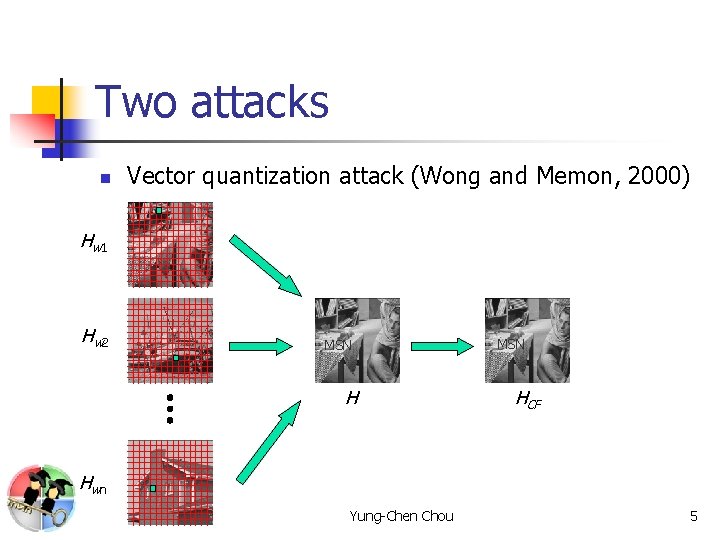
Two attacks n Vector quantization attack (Wong and Memon, 2000) Hw 1 Hw 2 MSN HCF Hw n Yung-Chen Chou 5
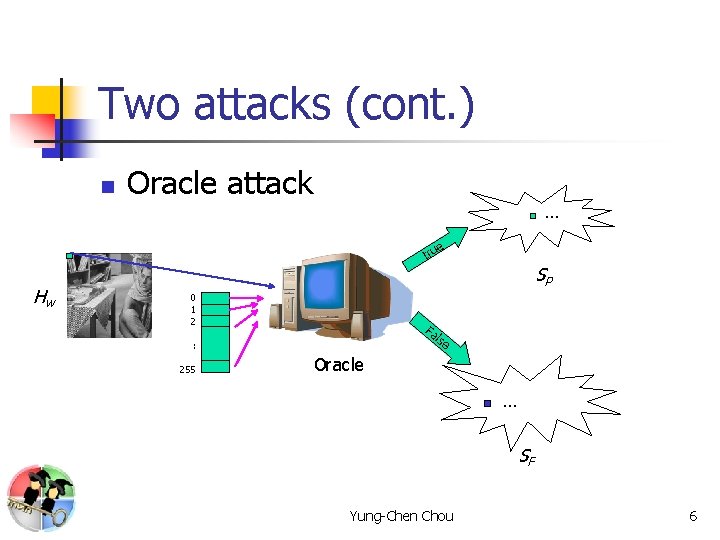
Two attacks (cont. ) n Oracle attack … e tru Hw SP 0 1 2 Fa lse : 255 Oracle … SF Yung-Chen Chou 6
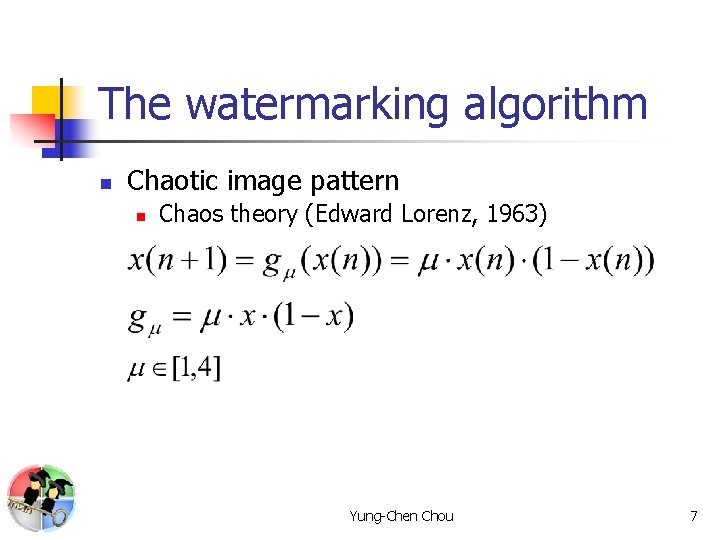
The watermarking algorithm n Chaotic image pattern n Chaos theory (Edward Lorenz, 1963) Yung-Chen Chou 7
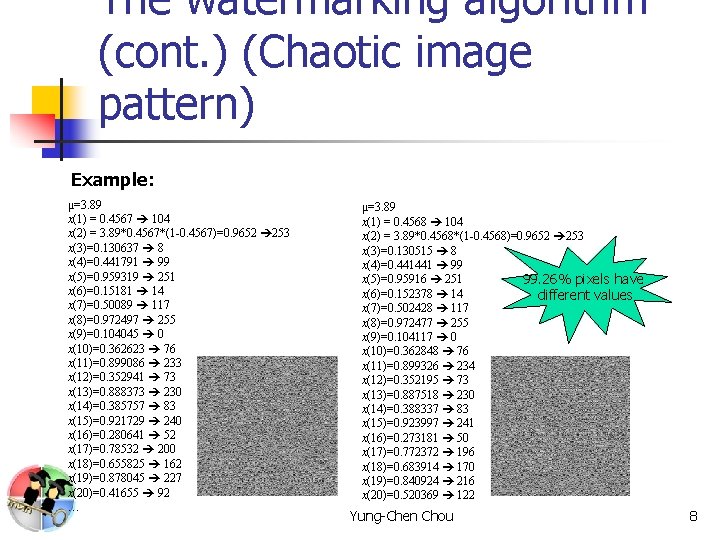
The watermarking algorithm (cont. ) (Chaotic image pattern) Example: μ=3. 89 x(1) = 0. 4567 104 x(2) = 3. 89*0. 4567*(1 -0. 4567)=0. 9652 253 x(3)=0. 130637 8 x(4)=0. 441791 99 x(5)=0. 959319 251 x(6)=0. 15181 14 x(7)=0. 50089 117 x(8)=0. 972497 255 x(9)=0. 104045 0 x(10)=0. 362623 76 x(11)=0. 899086 233 x(12)=0. 352941 73 x(13)=0. 888373 230 x(14)=0. 385757 83 x(15)=0. 921729 240 x(16)=0. 280641 52 x(17)=0. 78532 200 x(18)=0. 655825 162 x(19)=0. 878045 227 x(20)=0. 41655 92 … μ=3. 89 x(1) = 0. 4568 104 x(2) = 3. 89*0. 4568*(1 -0. 4568)=0. 9652 253 x(3)=0. 130515 8 x(4)=0. 441441 99 x(5)=0. 95916 251 99. 26% pixels have x(6)=0. 152378 14 different values x(7)=0. 502428 117 x(8)=0. 972477 255 x(9)=0. 104117 0 x(10)=0. 362848 76 x(11)=0. 899326 234 x(12)=0. 352195 73 x(13)=0. 887518 230 x(14)=0. 388337 83 x(15)=0. 923997 241 x(16)=0. 273181 50 x(17)=0. 772372 196 x(18)=0. 683914 170 x(19)=0. 840924 216 x(20)=0. 520369 122 … Yung-Chen Chou 8
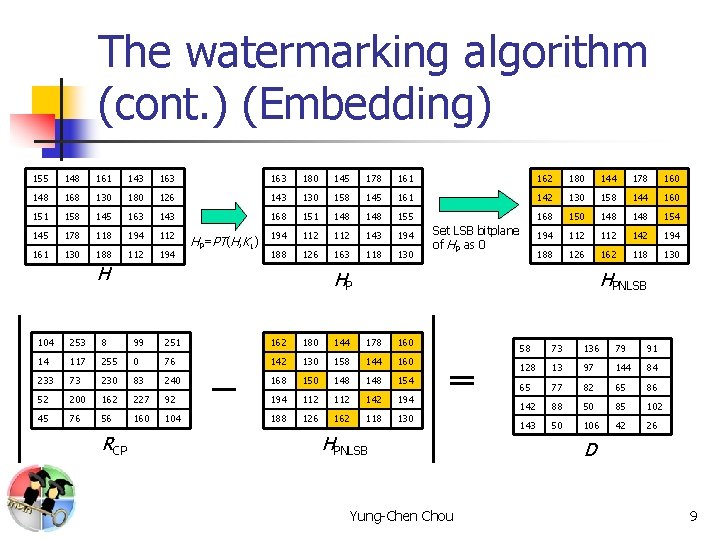
The watermarking algorithm (cont. ) (Embedding) 155 148 161 143 163 180 145 178 161 162 180 144 178 160 148 168 130 180 126 143 130 158 145 161 142 130 158 144 160 151 158 145 163 143 168 151 148 155 168 150 148 154 145 178 118 194 112 112 143 194 112 142 194 161 130 188 112 194 188 126 163 118 130 188 126 162 118 130 HP=PT(H, K 1) H HP HPNLSB 104 253 8 99 251 162 180 144 178 160 14 117 255 0 76 142 130 158 144 160 233 73 230 83 240 168 150 148 154 52 200 162 227 92 194 112 142 194 45 76 56 160 104 188 126 162 118 130 RCP Set LSB bitplane of HP as 0 HPNLSB Yung-Chen Chou 58 73 136 79 91 128 13 97 144 84 65 77 82 65 86 142 88 50 85 102 143 50 106 42 26 D 9
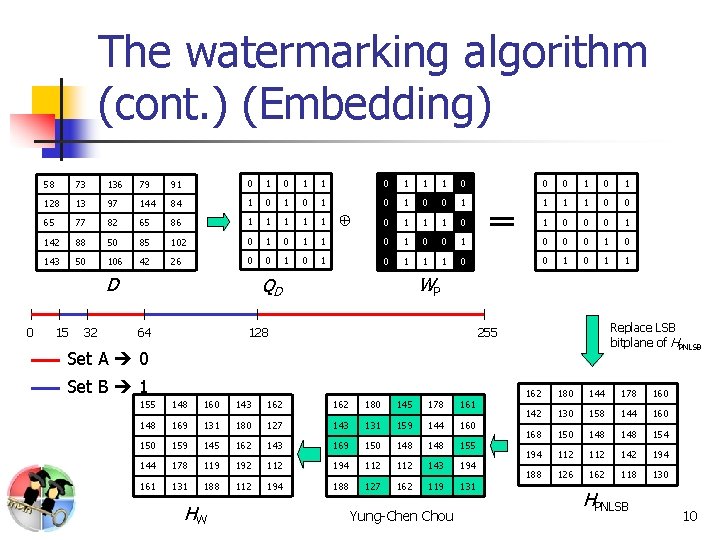
The watermarking algorithm (cont. ) (Embedding) 58 73 136 79 91 0 1 1 1 0 0 0 1 128 13 97 144 84 1 0 1 0 0 1 1 0 0 65 77 82 65 86 1 1 1 0 0 0 1 142 88 50 85 102 0 1 1 0 0 0 143 50 106 42 26 0 0 1 0 1 1 1 0 0 1 1 D 0 15 32 ⊕ WP QD 64 128 Replace LSB bitplane of HPNLSB 255 Set A 0 Set B 1 155 148 160 143 162 180 145 178 161 148 169 131 180 127 143 131 159 144 160 159 145 162 143 169 150 148 155 144 178 119 192 112 194 112 143 194 161 131 188 112 194 188 127 162 119 131 HW Yung-Chen Chou 162 180 144 178 160 142 130 158 144 160 168 150 148 154 194 112 142 194 188 126 162 118 130 HPNLSB 10
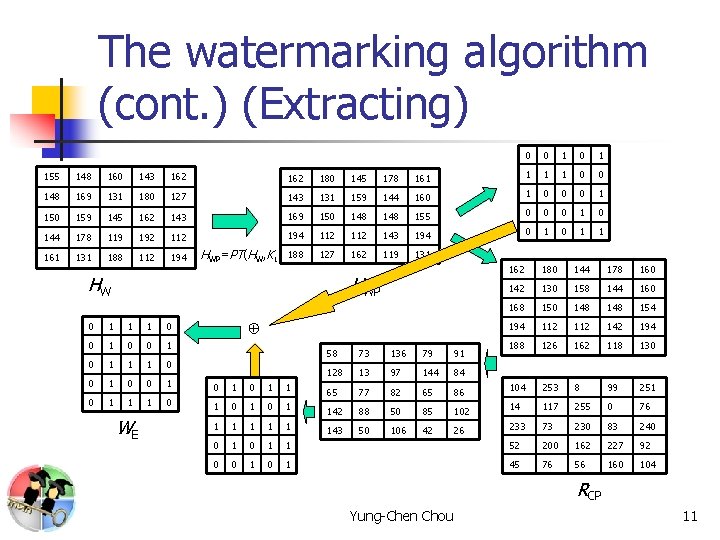
The watermarking algorithm (cont. ) (Extracting) 0 0 1 155 148 160 143 162 180 145 178 161 1 0 0 148 169 131 180 127 143 131 159 144 160 1 0 0 0 1 150 159 145 162 143 169 150 148 155 0 0 0 144 178 119 192 112 194 112 143 194 0 1 1 161 131 188 112 194 188 127 162 119 131 HWP=PT(HW, K 1) HW HWP ⊕ 0 1 1 1 0 0 1 0 1 1 1 0 1 0 0 WE 162 180 144 178 160 142 130 158 144 160 168 150 148 154 194 112 142 194 188 126 162 118 130 58 73 136 79 91 128 13 97 144 84 65 77 82 65 86 104 253 8 99 251 1 142 88 50 85 102 14 117 255 0 76 1 1 143 50 106 42 26 233 73 230 83 240 0 1 1 52 200 162 227 92 1 0 1 45 76 56 160 104 RCP Yung-Chen Chou 11
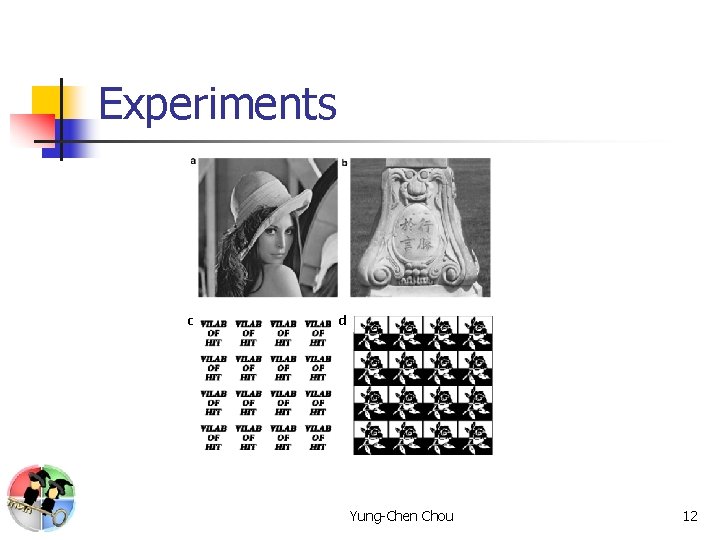
Experiments c d Yung-Chen Chou 12
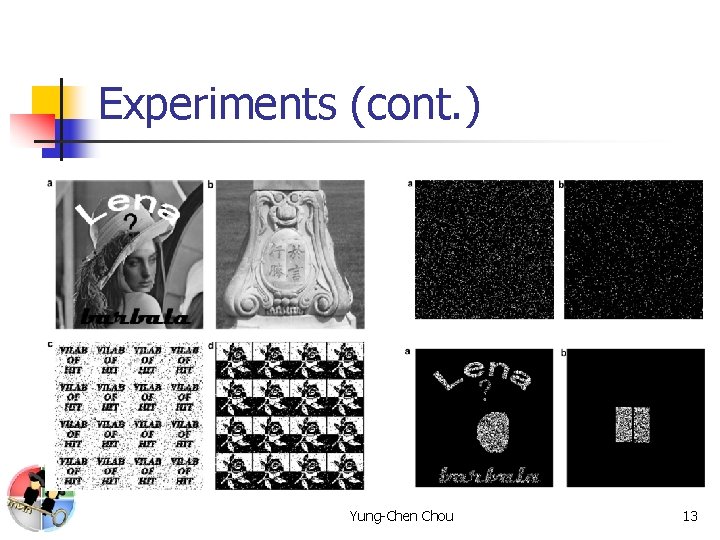
Experiments (cont. ) Yung-Chen Chou 13
Conclusions n n Chaotic map and permutation transform are used to improve the security. The method can exactly detect the tampered areas on the watermarked image. Yung-Chen Chou 14
- Slides: 14