An IDBased Broadcast Encryption Scheme for Key Distribution
An ID-Based Broadcast Encryption Scheme for Key Distribution Author: Xinjun Du, Ying Wang, Jianhua Ge, and Yumin Wang Source: IEEE TRANSACTIONS ON BROADCASTING, Volume 51, Issue 2, June 2005 Reporter: Peng-Yuan Chen Date: 2006. 12. 27 1
Outline n n Introduction Preliminaries - Bilinear Pairings - ID-Based Public Key Infrastructure - Boneh-Franklin Encryption Scheme n n n Proposed Scheme - ID-BASED BROADCAST ENCRYPTION SCHEME Analysis Conclusion 2
Introduction n ID-based Cryptography q q n n the public key can be an arbitrary string. simplify the management of public certificates, using the identity of receiver as the public key. Many ID-based cryptographic schemes have been proposed using the bilinear pairings. This scheme is a variation of the Boneh. Franklin identity based encryption scheme. 3
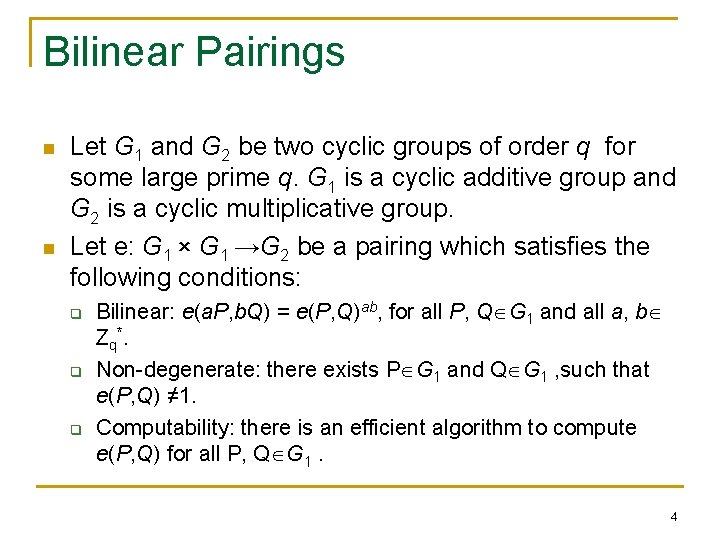
Bilinear Pairings n n Let G 1 and G 2 be two cyclic groups of order q for some large prime q. G 1 is a cyclic additive group and G 2 is a cyclic multiplicative group. Let e: G 1 × G 1 →G 2 be a pairing which satisfies the following conditions: q q q Bilinear: e(a. P, b. Q) = e(P, Q)ab, for all P, Q G 1 and all a, b Z q*. Non-degenerate: there exists P G 1 and Q G 1 , such that e(P, Q) ≠ 1. Computability: there is an efficient algorithm to compute e(P, Q) for all P, Q G 1. 4
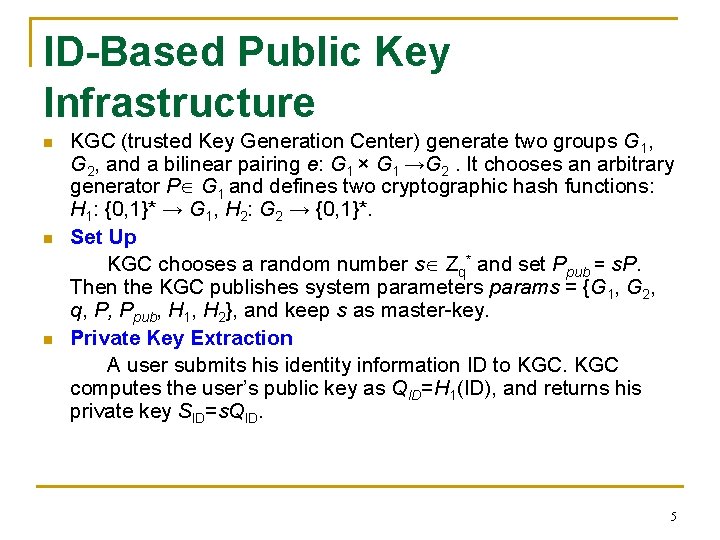
ID-Based Public Key Infrastructure n n n KGC (trusted Key Generation Center) generate two groups G 1, G 2, and a bilinear pairing e: G 1 × G 1 →G 2. It chooses an arbitrary generator P G 1 and defines two cryptographic hash functions: H 1: {0, 1}* → G 1, H 2: G 2 → {0, 1}*. Set Up KGC chooses a random number s Zq* and set Ppub = s. P. Then the KGC publishes system parameters params = {G 1, G 2, q, P, Ppub, H 1, H 2}, and keep s as master-key. Private Key Extraction A user submits his identity information ID to KGC computes the user’s public key as QID=H 1(ID), and returns his private key SID=s. QID. 5
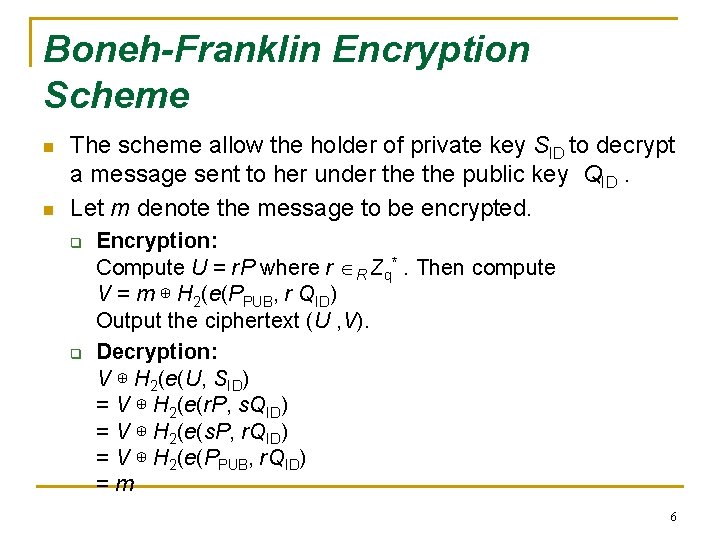
Boneh-Franklin Encryption Scheme n n The scheme allow the holder of private key SID to decrypt a message sent to her under the public key QID. Let m denote the message to be encrypted. q q Encryption: Compute U = r. P where r R Zq*. Then compute V = m ⊕ H 2(e(PPUB, r QID) Output the ciphertext (U , V). Decryption: V ⊕ H 2(e(U, SID) = V ⊕ H 2(e(r. P, s. QID) = V ⊕ H 2(e(s. P, r. QID) = V ⊕ H 2(e(PPUB, r. QID) =m 6
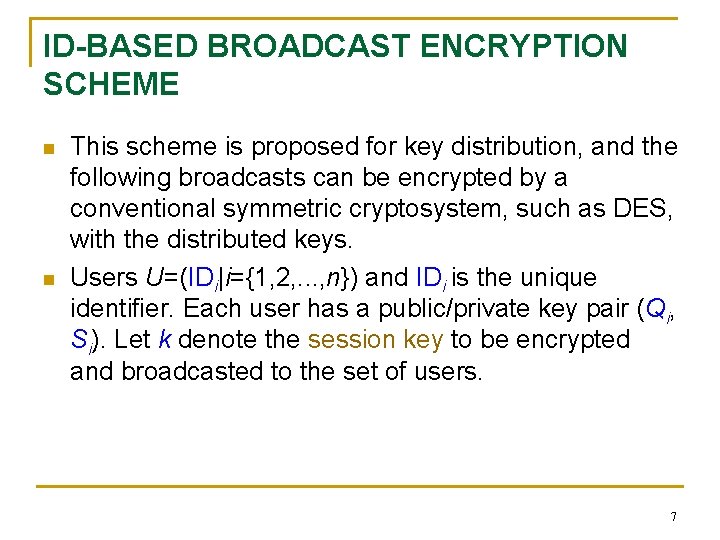
ID-BASED BROADCAST ENCRYPTION SCHEME n n This scheme is proposed for key distribution, and the following broadcasts can be encrypted by a conventional symmetric cryptosystem, such as DES, with the distributed keys. Users U=(IDi|i={1, 2, . . . , n}) and IDi is the unique identifier. Each user has a public/private key pair (Qi, Si). Let k denote the session key to be encrypted and broadcasted to the set of users. 7
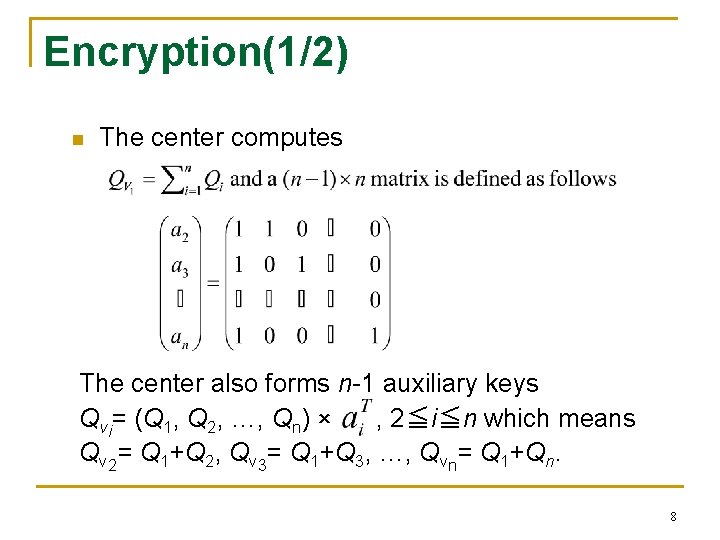
Encryption(1/2) n The center computes The center also forms n-1 auxiliary keys Qvi= (Q 1, Q 2, …, Qn) × , 2≦i≦n which means Qv 2= Q 1+Q 2, Qv 3= Q 1+Q 3, …, Qvn= Q 1+Qn. 8
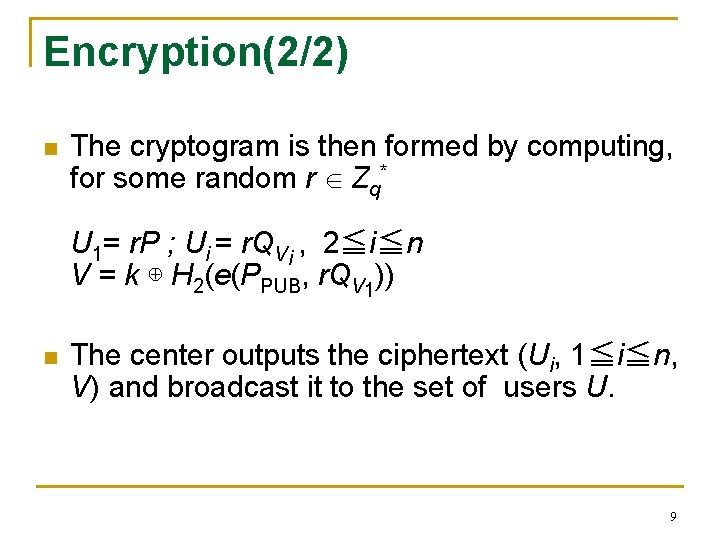
Encryption(2/2) n The cryptogram is then formed by computing, for some random r Zq* U 1= r. P ; Ui = r. QVi , 2≦i≦n V = k ⊕ H 2(e(PPUB, r. QV 1)) n The center outputs the ciphertext (Ui, 1≦i≦n, V) and broadcast it to the set of users U. 9
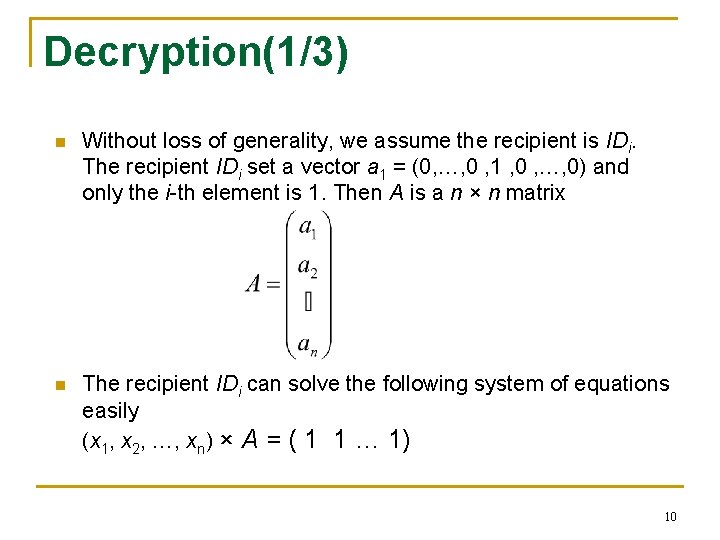
Decryption(1/3) n Without loss of generality, we assume the recipient is IDi. The recipient IDi set a vector a 1 = (0, …, 0 , 1 , 0 , …, 0) and only the i-th element is 1. Then A is a n × n matrix n The recipient IDi can solve the following system of equations easily (x 1, x 2, …, xn) × A = ( 1 1 … 1) 10
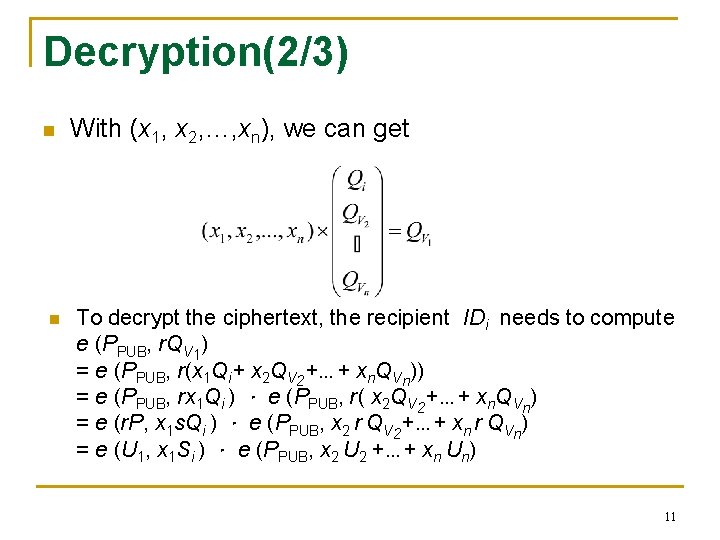
Decryption(2/3) n n With (x 1, x 2, …, xn), we can get To decrypt the ciphertext, the recipient IDi needs to compute e (PPUB, r. QV 1) = e (PPUB, r(x 1 Qi+ x 2 QV 2+…+ xn. QVn)) = e (PPUB, rx 1 Qi ) . e (PPUB, r( x 2 QV 2+…+ xn. QVn) = e (r. P, x 1 s. Qi ) . e (PPUB, x 2 r QV 2+…+ xn r QVn) = e (U 1, x 1 Si ) . e (PPUB, x 2 U 2 +…+ xn Un) 11
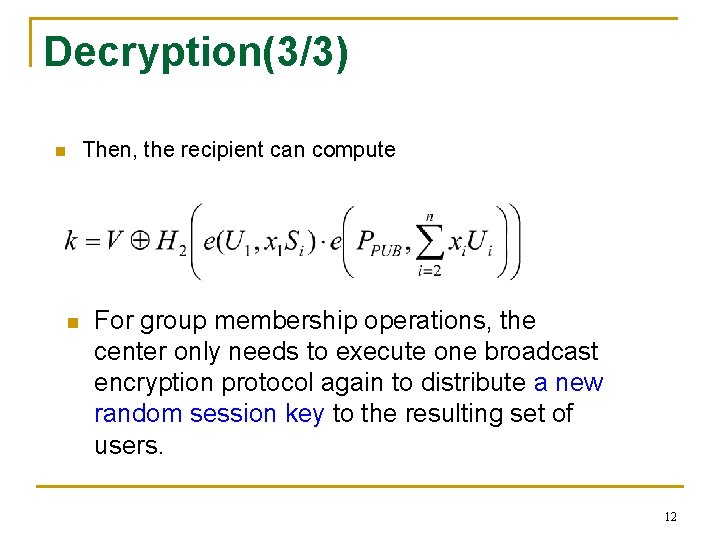
Decryption(3/3) Then, the recipient can compute n n For group membership operations, the center only needs to execute one broadcast encryption protocol again to distribute a new random session key to the resulting set of users. 12
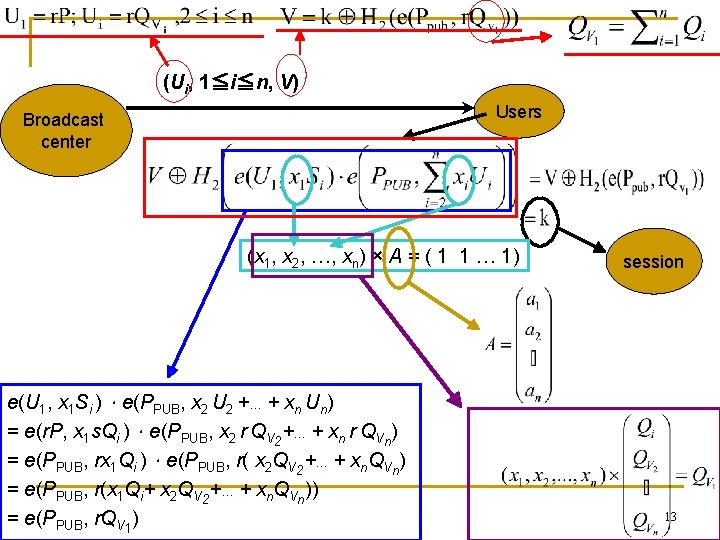
(Ui, 1≦i≦n, V) Users Broadcast center (x 1, x 2, …, xn) × A = ( 1 1 … 1) e(U 1, x 1 Si ).e(PPUB, x 2 U 2 +…+ xn Un) = e(r. P, x 1 s. Qi ).e(PPUB, x 2 r QV 2+…+ xn r QVn) = e(PPUB, rx 1 Qi ).e(PPUB, r( x 2 QV 2+…+ xn. QVn) = e(PPUB, r(x 1 Qi+ x 2 QV 2+…+ xn. QVn)) = e(PPUB, r. QV 1) session 13
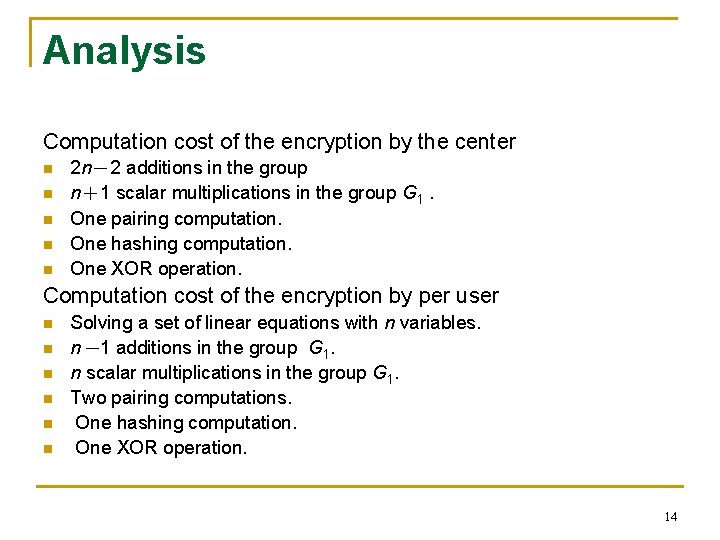
Analysis Computation cost of the encryption by the center n n n 2 n-2 additions in the group n+1 scalar multiplications in the group G 1. One pairing computation. One hashing computation. One XOR operation. Computation cost of the encryption by per user n n n Solving a set of linear equations with n variables. n-1 additions in the group G 1. n scalar multiplications in the group G 1. Two pairing computations. One hashing computation. One XOR operation. 14
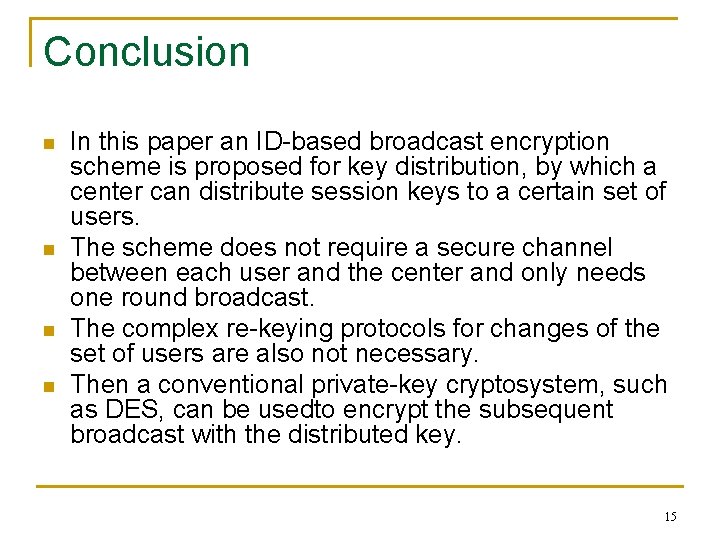
Conclusion n n In this paper an ID-based broadcast encryption scheme is proposed for key distribution, by which a center can distribute session keys to a certain set of users. The scheme does not require a secure channel between each user and the center and only needs one round broadcast. The complex re-keying protocols for changes of the set of users are also not necessary. Then a conventional private-key cryptosystem, such as DES, can be usedto encrypt the subsequent broadcast with the distributed key. 15
- Slides: 15