An Efficient IdentityBased Conditional PrivacyPreserving Authentication Scheme for
An Efficient Identity-Based Conditional Privacy-Preserving Authentication Scheme for Vehicular Ad Hoc Networks Author: Debiao He, Sherali Zeadally, Baowen Xu, Member, IEEE, and Xinyi Huang Publisher: 2015 IEEE Transactions On Information Forensics And Security Presenter: 柯懷貿 Date: 2019/05/29 Department of Computer Science and Information Engineering National Cheng Kung University, Taiwan R. O. C.
Structure l Communications in VANETs can be divided into two types: Vehicle-to. Vehicle (V 2 V) communication and Vehicle-to Infrastructure (V 2 I) communication, which are controlled by the Dedicated Short Range Communication (DSRC) protocol. l The leakage of traveling routes violates drivers’ privacy and may result in serious consequences because those traveling routes may be used for crimes. To address this privacy issue, anonymity must be provided in VANETs but, it should still be extract the real identity from the message by a trusted authority. l Therefore, conditional privacy should be provided in VANETs. National Cheng Kung University CSIE Computer & Internet Architecture Lab 2
Conditional Privacy-Preserving Authentication l The Conditional Privacy-Preserving Authentication (CPPA) scheme, is suitable for addressing the privacy issue in VANETs because it can support message authentication and conditional privacy. l Although previously proposed ID-based CPPA schemes could solve several weaknesses that exist in some PKI-based CPPA schemes, the performance of such schemes is not satisfactory because the computation costs of the bilinear pairing operation and the scalar multiplication operation are quite complex. l Therefore, we propose an ID-based CPPA scheme for VANETs without bilinear pairing. National Cheng Kung University CSIE Computer & Internet Architecture Lab 3
Bilinear Pairing l Define , where G 1 is an additive group generated by a point P on the super singular elliptic curve. l Traditional elliptic curve math lets you check linear constraints on the numbers (eg. if P = G * p, Q = G * q and R = G * r, checking 5 * P + 7 * Q = 11 * R is really checking that 5 * p + 7 * q = 11 * r), pairings let you check quadratic constraints (eg. checking e(P, Q) * e(G, G * 5) = 1 is really checking that p * q + 5 = 0). l The word “bilinear” here basically means that it satisfies the constraints: e(P, Q + R) = e(P, Q) * e(P, R) and e(P + S, Q) = e(P, Q) * e(S, Q) National Cheng Kung University CSIE Computer & Internet Architecture Lab 4
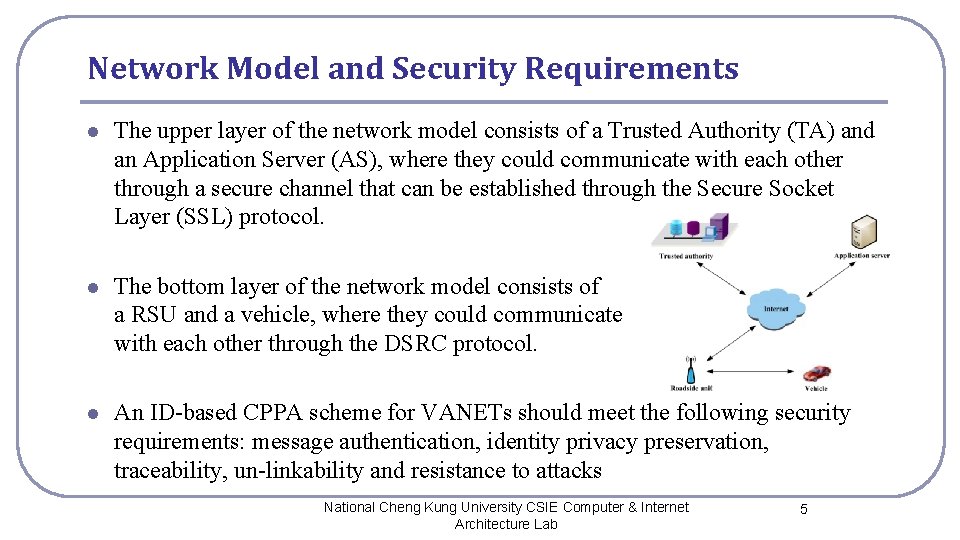
Network Model and Security Requirements l The upper layer of the network model consists of a Trusted Authority (TA) and an Application Server (AS), where they could communicate with each other through a secure channel that can be established through the Secure Socket Layer (SSL) protocol. l The bottom layer of the network model consists of a RSU and a vehicle, where they could communicate with each other through the DSRC protocol. l An ID-based CPPA scheme for VANETs should meet the following security requirements: message authentication, identity privacy preservation, traceability, un-linkability and resistance to attacks National Cheng Kung University CSIE Computer & Internet Architecture Lab 5
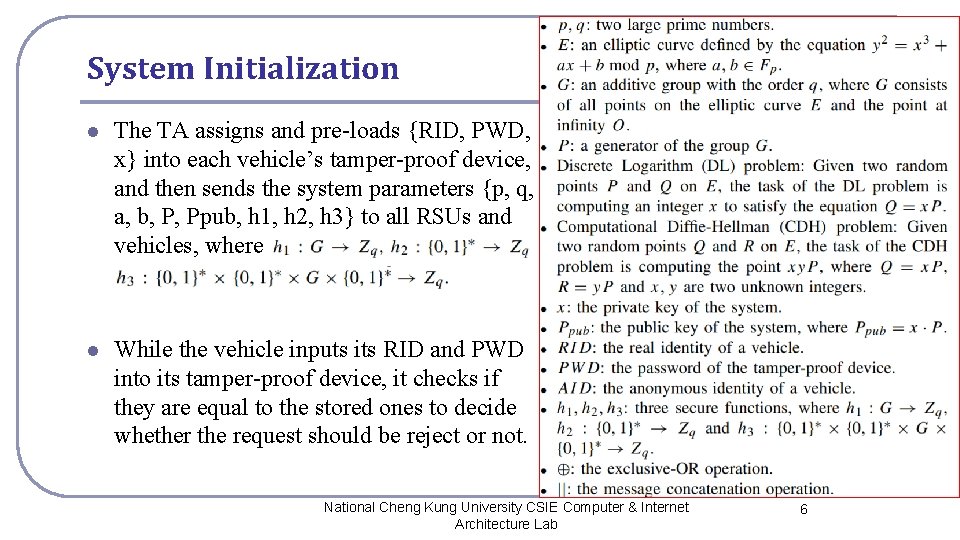
System Initialization l The TA assigns and pre-loads {RID, PWD, x} into each vehicle’s tamper-proof device, and then sends the system parameters {p, q, a, b, P, Ppub, h 1, h 2, h 3} to all RSUs and vehicles, where l While the vehicle inputs its RID and PWD into its tamper-proof device, it checks if they are equal to the stored ones to decide whether the request should be reject or not. National Cheng Kung University CSIE Computer & Internet Architecture Lab 6
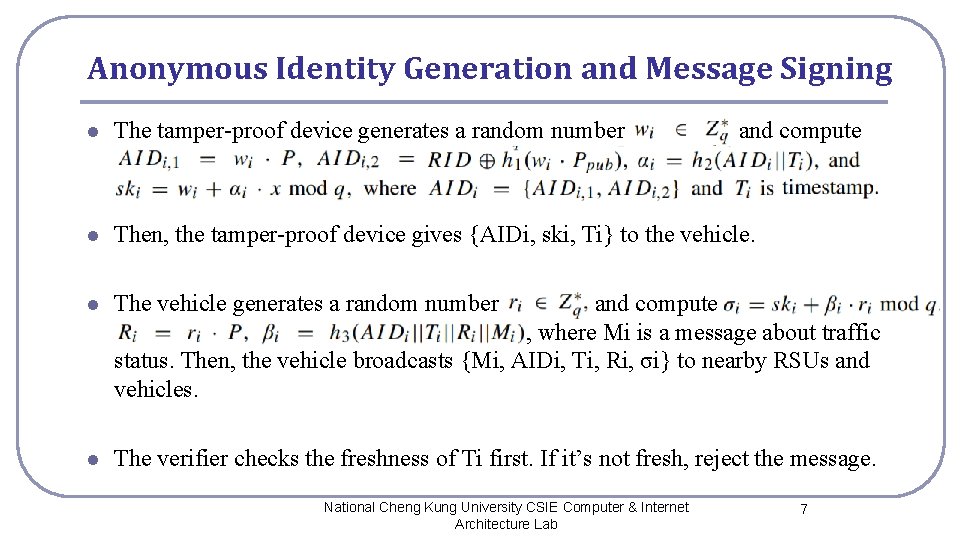
Anonymous Identity Generation and Message Signing l The tamper-proof device generates a random number l Then, the tamper-proof device gives {AIDi, ski, Ti} to the vehicle. l The vehicle generates a random number and compute 2 where Mi is a message about traffic statu, where Mi is a message about traffic status. Then, the vehicle broadcasts {Mi, AIDi, Ti, Ri, σi} to nearby RSUs and vehicles. l The verifier checks the freshness of Ti first. If it’s not fresh, reject the message. National Cheng Kung University CSIE Computer & Internet Architecture Lab and compute 7
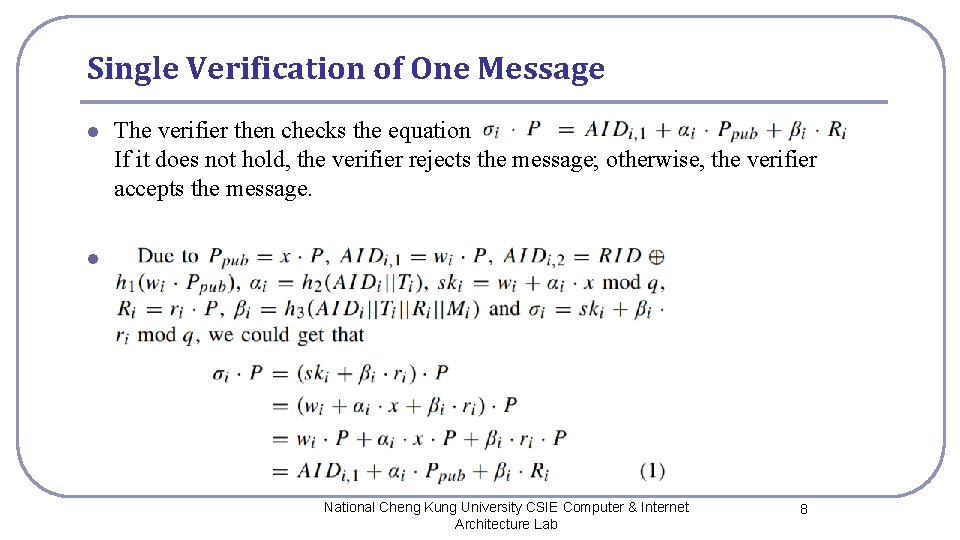
Single Verification of One Message l The verifier then checks the equation If it does not hold, the verifier rejects the message; otherwise, the verifier accepts the message. l The bottom layer of the network model consists of traceability, un-linkability and resistance to attacks National Cheng Kung University CSIE Computer & Internet Architecture Lab 8
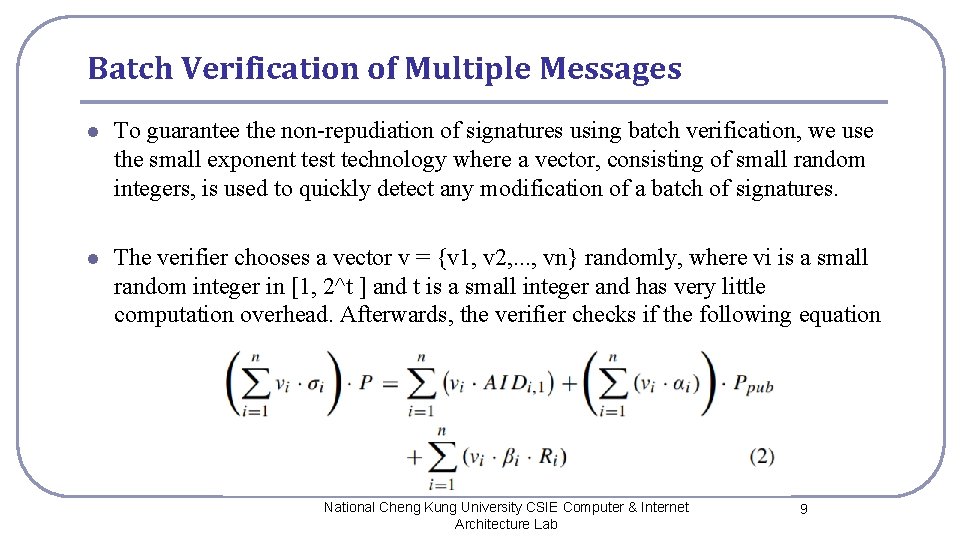
Batch Verification of Multiple Messages l To guarantee the non-repudiation of signatures using batch verification, we use the small exponent test technology where a vector, consisting of small random integers, is used to quickly detect any modification of a batch of signatures. l The verifier chooses a vector v = {v 1, v 2, . . . , vn} randomly, where vi is a small random integer in [1, 2^t ] and t is a small integer and has very little computation overhead. Afterwards, the verifier checks if the following equation National Cheng Kung University CSIE Computer & Internet Architecture Lab 9
Security Analysis l We have evaluated the security of the proposed ID-based CPPA scheme for VANETs and demonstrated that the proposed scheme is secure in the random oracle model consisting of Setup−Oracle, h 1/h 2/h 3−Oracle and Sign−Oracle. l Suppose there’s an adversary A can violate the authentication of the CPPA scheme and forge a message {Mi, AID 1, Ti, Ri, σi}. We can construct a challenger C, which could solve the DL problem with a non-negligible probability by running A as a subroutine. Given an instance (P, Q = x · P) of the DL problem, C simulates oracles queried by A as follows. l Setup−Oracle: C sets Ppub ← Q, and sends the system parameters = {p, q, a, b, P, Ppub, h 1, h 2, h 3} to A. National Cheng Kung University CSIE Computer & Internet Architecture Lab 10
Random Oracle Model l h 1/h 2/h 3−Oracle: C keeps a list L 1/L 2/L 3 with the form of / / , which is initialized to empty. Upon receiving A’s query with the message / / , C checks whether a corresponding tuple exists in L 1/L 2/L 3 first. If so, C sends τ to A; otherwise, C generates a random number τ ∈ Zq , adds tuple in L 1/L 2/L 3 and sends to A. l Sign−Oracle: Upon receiving A’s query with the message Mi , C generates three random numbers σi, αi, βi ∈ Z∗ q , chooses a random point and computes C adds into L 2 and add into L 3. Finally, C sends the message {Mi, AIDi, Ti, Ri, σi} to A. Therefore, all signatures generated by C are indistinguishable from those generated by legal vehicles. National Cheng Kung University CSIE Computer & Internet Architecture Lab 11
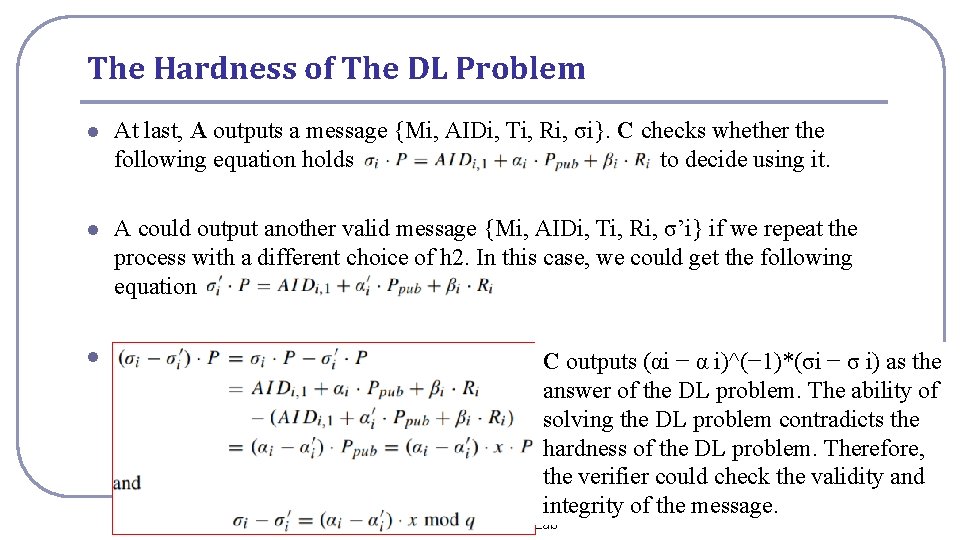
The Hardness of The DL Problem l At last, A outputs a message {Mi, AIDi, Ti, Ri, σi}. C checks whether the following equation holds to decide using it. l A could output another valid message {Mi, AIDi, Ti, Ri, σ’i} if we repeat the process with a different choice of h 2. In this case, we could get the following equation l C outputs (αi − α i)^(− 1)*(σi − σ i) as the answer of the DL problem. The ability of solving the DL problem contradicts the hardness of the DL problem. Therefore, the verifier could check the validity and National Cheng Kung University CSIE Computer & integrity of. Internet the message. 12 Architecture Lab
Privacy Analysis l Preserving identity privacy: The vehicle’s real identity RID is involved in AIDi generated by the vehicle. To extract RID from the adversary computes and needs wi or x. l Traceability: TA computes the real identity by computing RID = l Un-linkability: Due to the randomness of wi and ri , no adversary could link two anonymous identities or two signatures generated by the same vehicle. National Cheng Kung University CSIE Computer & Internet Architecture Lab and extracts 13
Resistant Against Various Types of Attacks l The adversary must generate a message {Mi, AIDi, Ti, Ri, σi} satisfying the equation , but he cannot. Therefore, we can avoid Impersonation attack, Modification attack and Man-in-the-middle attack. l RSUs and other vehicles could find the Replay attack of the message by checking the freshness of the timestamp Ti. l Neither the RSU nor the vehicle maintains a verifier table for message authentication because they just needs to store their own private key. Then, the adversary cannot steal any verifier table for Stolen verifier table attack. National Cheng Kung University CSIE Computer & Internet Architecture Lab 14
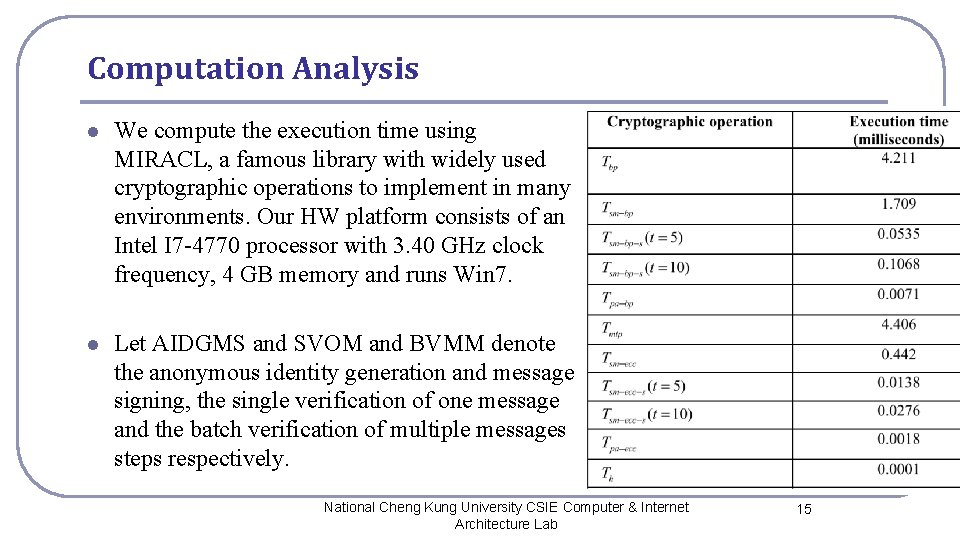
Computation Analysis l We compute the execution time using MIRACL, a famous library with widely used cryptographic operations to implement in many environments. Our HW platform consists of an Intel I 7 -4770 processor with 3. 40 GHz clock frequency, 4 GB memory and runs Win 7. l Let AIDGMS and SVOM and BVMM denote the anonymous identity generation and message signing, the single verification of one message and the batch verification of multiple messages steps respectively. National Cheng Kung University CSIE Computer & Internet Architecture Lab 15
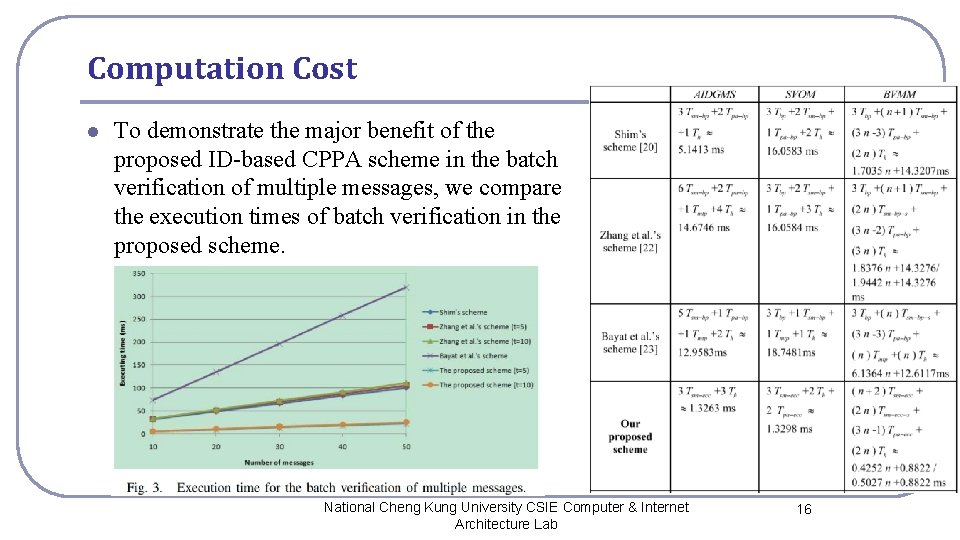
Computation Cost l To demonstrate the major benefit of the proposed ID-based CPPA scheme in the batch verification of multiple messages, we compare the execution times of batch verification in the proposed scheme. National Cheng Kung University CSIE Computer & Internet Architecture Lab 16
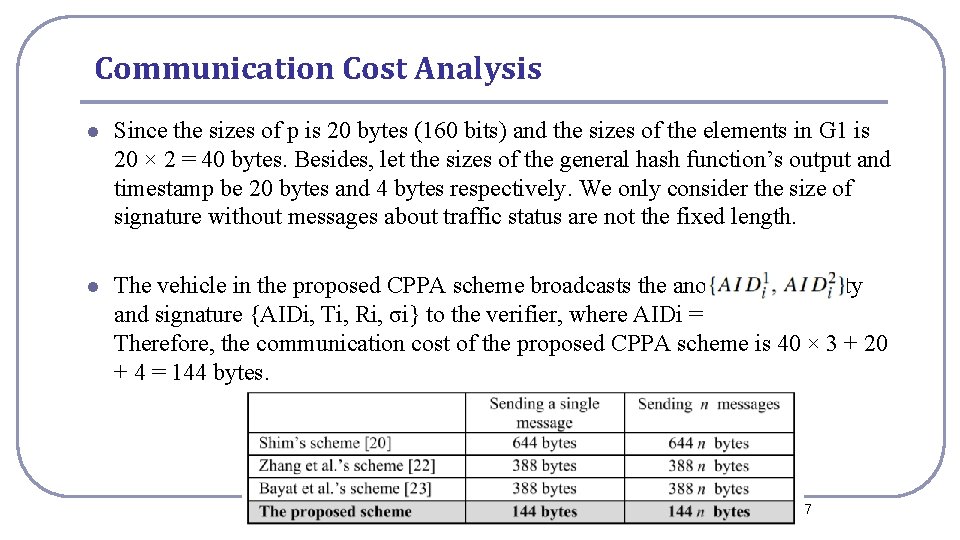
Communication Cost Analysis l Since the sizes of p is 20 bytes (160 bits) and the sizes of the elements in G 1 is 20 × 2 = 40 bytes. Besides, let the sizes of the general hash function’s output and timestamp be 20 bytes and 4 bytes respectively. We only consider the size of signature without messages about traffic status are not the fixed length. l The vehicle in the proposed CPPA scheme broadcasts the anonymous identity and signature {AIDi, Ti, Ri, σi} to the verifier, where AIDi = Therefore, the communication cost of the proposed CPPA scheme is 40 × 3 + 20 + 4 = 144 bytes. National Cheng Kung University CSIE Computer & Internet Architecture Lab 17
- Slides: 17