An Efficient and Anonymous Buyer Seller Watermarking Protocol
An Efficient and Anonymous Buyer. Seller Watermarking Protocol C. L. Lei, P. L. Yu, P. L. Tsai and M. H. Chan IEEE TRANSACTIONS ON IMAGE PROCESSING, Vol. 13, No. 12, pp. 1618 -1626, December 2004. Speaker: Cheng-Hsiung Li Date: 2005 -05 -05 1
Outline o o Introduction Related work n n o o o The customer ‘s right problem The unblinding problem Proposed scheme Discussions Conclusion 2
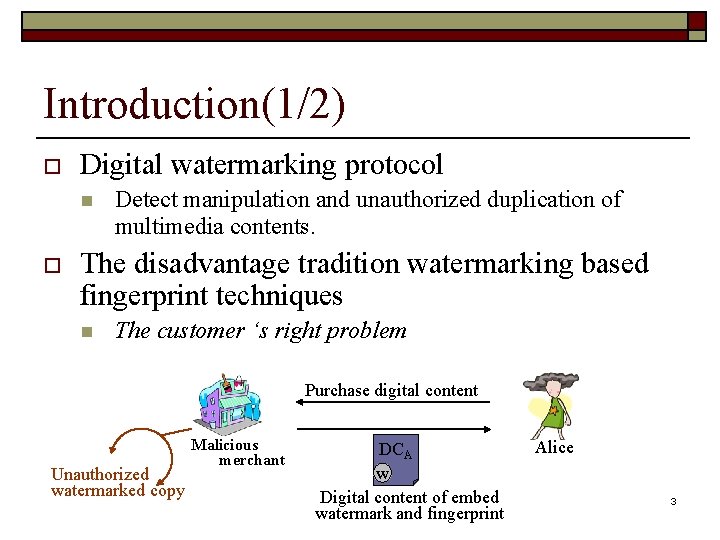
Introduction(1/2) o Digital watermarking protocol n o Detect manipulation and unauthorized duplication of multimedia contents. The disadvantage tradition watermarking based fingerprint techniques n The customer ‘s right problem Purchase digital content Unauthorized watermarked copy Malicious merchant DCA w Digital content of embed watermark and fingerprint Alice 3
Introduction(2/2) o A buyer-seller watermarking protocol (Memon Wong, 2001) n n Solve the customer’s right problem Existence unblinding problem 4
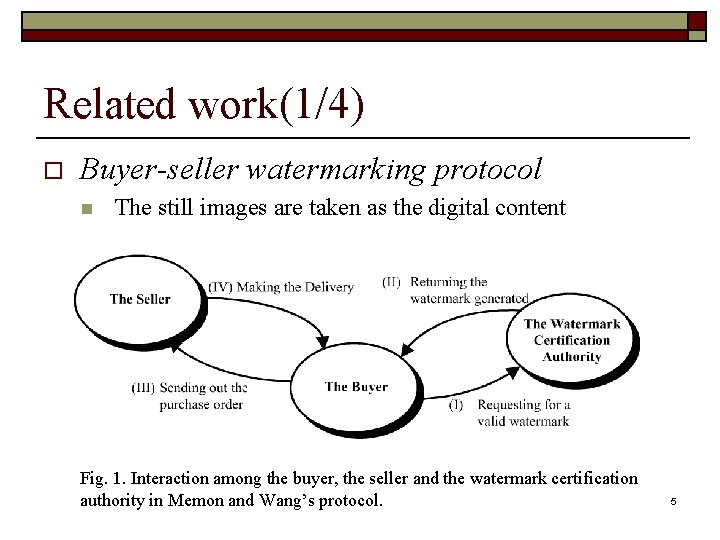
Related work(1/4) o Buyer-seller watermarking protocol n The still images are taken as the digital content Fig. 1. Interaction among the buyer, the seller and the watermark certification authority in Memon and Wang’s protocol. 5
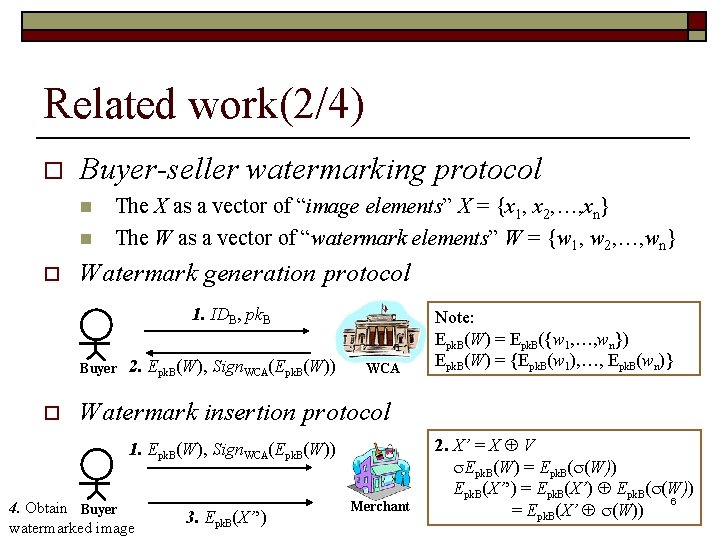
Related work(2/4) o Buyer-seller watermarking protocol n n o The X as a vector of “image elements” X = {x 1, x 2, …, xn} The W as a vector of “watermark elements” W = {w 1, w 2, …, wn} Watermark generation protocol 1. IDB, pk. B Buyer o 2. Epk. B(W), Sign. WCA(Epk. B(W)) WCA Note: Epk. B(W) = Epk. B({w 1, …, wn}) Epk. B(W) = {Epk. B(w 1), …, Epk. B(wn)} Watermark insertion protocol 1. Epk. B(W), Sign. WCA(Epk. B(W)) 4. Obtain Buyer watermarked image 3. Epk. B(X’’) Merchant 2. X’ = X V Epk. B(W) = Epk. B( (W)) Epk. B(X’’) = Epk. B(X’) Epk. B( (W)) 6 = Epk. B(X’ (W))
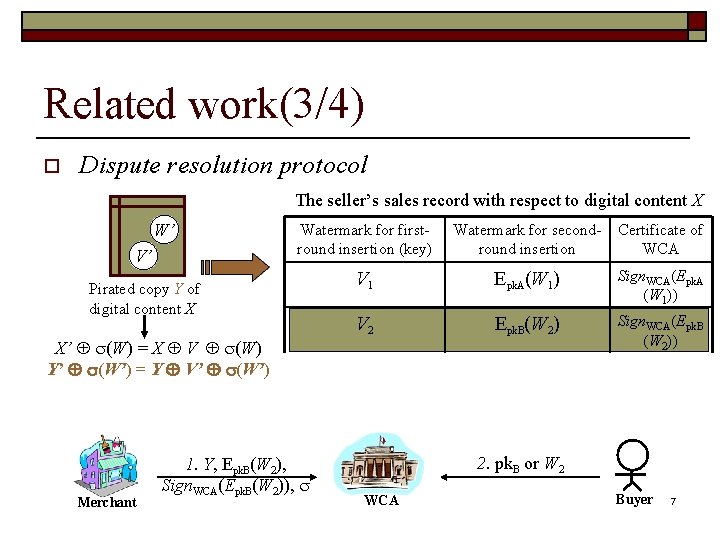
Related work(3/4) o Dispute resolution protocol The seller’s sales record with respect to digital content X W’ V’ Watermark for firstround insertion (key) Watermark for secondround insertion Certificate of WCA V 1 Epk. A(W 1) Sign. WCA(Epk. A (W 1)) V 2 Epk. B(W 2) Sign. WCA(Epk. B (W 2)) Pirated copy Y of digital content X X’ (W) = X V (W) Y’ (W’) = Y V’ (W’) Merchant 1. Y, Epk. B(W 2), Sign. WCA(Epk. B(W 2)), 2. pk. B or W 2 WCA Buyer 7
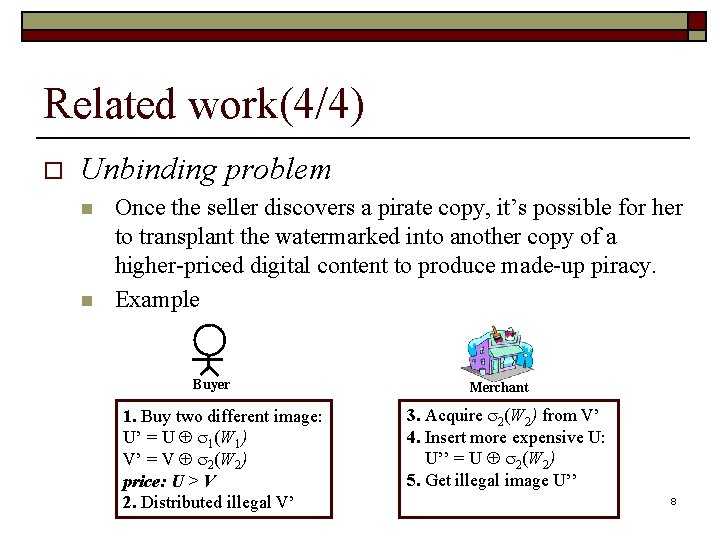
Related work(4/4) o Unbinding problem n n Once the seller discovers a pirate copy, it’s possible for her to transplant the watermarked into another copy of a higher-priced digital content to produce made-up piracy. Example Buyer 1. Buy two different image: U’ = U 1(W 1) V’ = V 2(W 2) price: U > V 2. Distributed illegal V’ Merchant 3. Acquire 2(W 2) from V’ 4. Insert more expensive U: U’’ = U 2(W 2) 5. Get illegal image U’’ 8
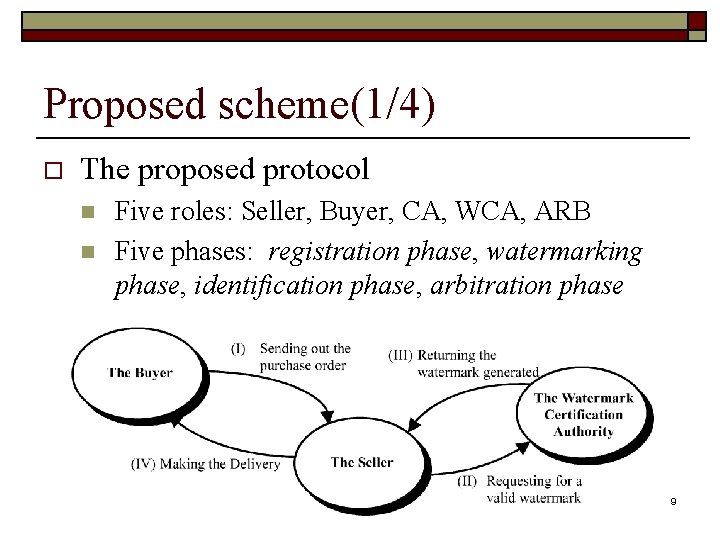
Proposed scheme(1/4) o The proposed protocol n n Five roles: Seller, Buyer, CA, WCA, ARB Five phases: registration phase, watermarking phase, identification phase, arbitration phase 9
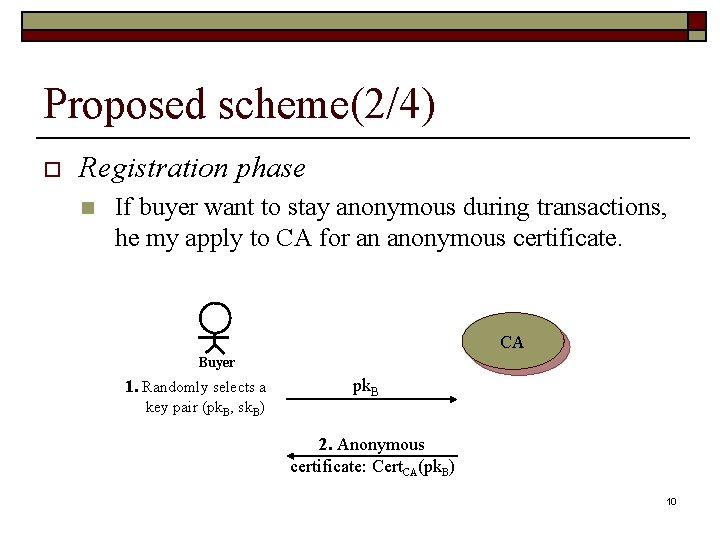
Proposed scheme(2/4) o Registration phase n If buyer want to stay anonymous during transactions, he my apply to CA for an anonymous certificate. CA Buyer 1. Randomly selects a key pair (pk. B, sk. B) pk. B 2. Anonymous certificate: Cert. CA(pk. B) 10
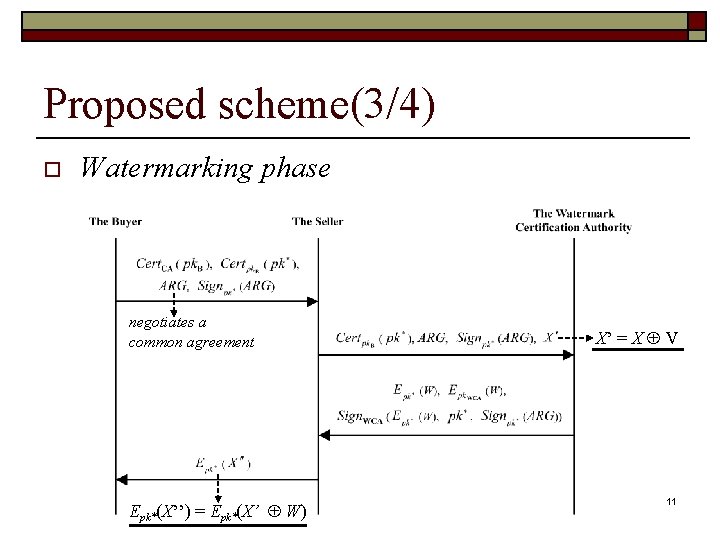
Proposed scheme(3/4) o Watermarking phase negotiates a common agreement Epk*(X’’) = Epk*(X’ W) X’ = X V 11
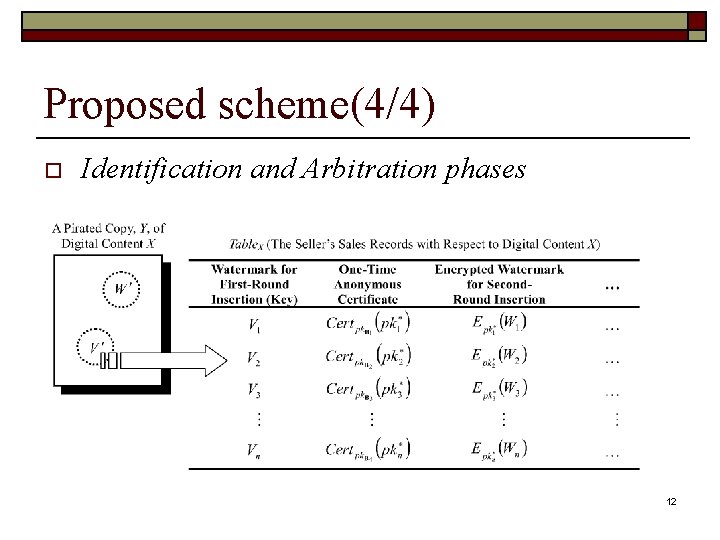
Proposed scheme(4/4) o Identification and Arbitration phases 12
Discussions o o Accomplishment of design goals Deployment of trusted third parties Storage requirements of the seller System availability 13
Conclusion o The authors propose a buyer-seller watermarking protocol derived from Memon and Wong’s protocol and solve both the proposed customer’s right problem and the unblinding problem. 14
- Slides: 14