An Authenticated Payword Scheme without Public Key Cryptosystems
An Authenticated Payword Scheme without Public Key Cryptosystems Author: Chia-Chi Wu, Chin-Chen Chang, and Iuon-Chang Lin. Source: International Journal of Innovative Computing, Information and Control, 2009, Vol. 5, No. 9, pp. 2881– 2891. Presenter: Tsuei-Hung Sun (孫翠鴻) Date: 2011/3/11
Outline • • Introduction Motivation Scheme Security Analysis Performance Evaluation Advantage vs. Drawback Comment
Introduction(1/6) • Micro Payment Transfer Protocol (MPTP) stipulate some related security risks that need to be consider as follow: – Credit liability – Abused credit – Counterfeiting – Unauthorized withdrawal – Double spending
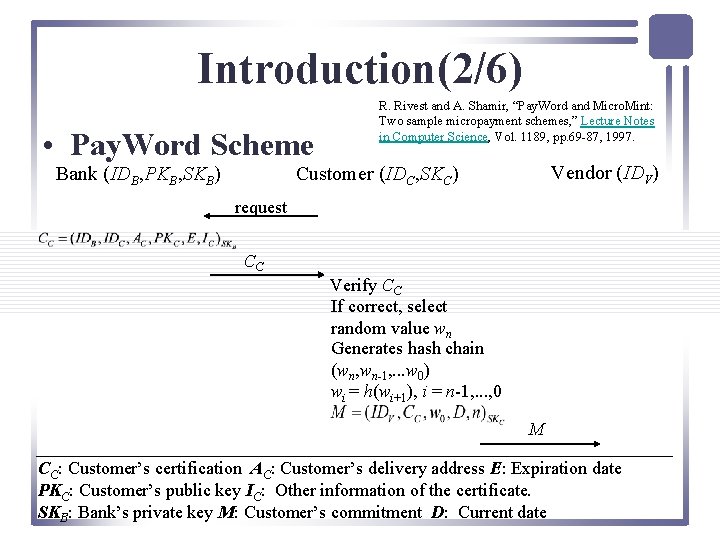
Introduction(2/6) • Pay. Word Scheme Bank (IDB, PKB, SKB) R. Rivest and A. Shamir, “Pay. Word and Micro. Mint: Two sample micropayment schemes, ” Lecture Notes in Computer Science, Vol. 1189, pp. 69 -87, 1997. Vendor (IDV) Customer (IDC, SKC) request CC Verify CC If correct, select random value wn Generates hash chain (wn, wn-1, . . . w 0) wi = h(wi+1), i = n-1, . . . , 0 M CC: Customer’s certification AC: Customer’s delivery address E: Expiration date PKC: Customer’s public key IC: Other information of the certificate. SKB: Bank’s private key M: Customer’s commitment D: Current date
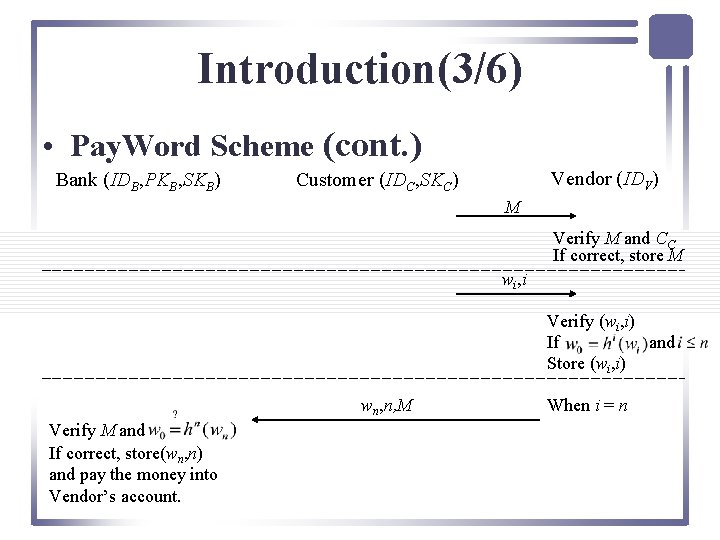
Introduction(3/6) • Pay. Word Scheme (cont. ) Bank (IDB, PKB, SKB) Vendor (IDV) Customer (IDC, SKC) M Verify M and CC If correct, store M wi, i Verify (wi, i) If and Store (wi, i) wn, n, M Verify M and If correct, store(wn, n) and pay the money into Vendor’s account. When i = n
Introduction(4/6) • The Advantage of Pay. Word – Using hash chain to lower computational cost – No need to settle with the bank for each transaction. • The Drawback of Pay. Word – Customer’s consumption is no limited. – No trusted Certificate Authority (CA) – Bank falsification attack – Certificate abuse attack
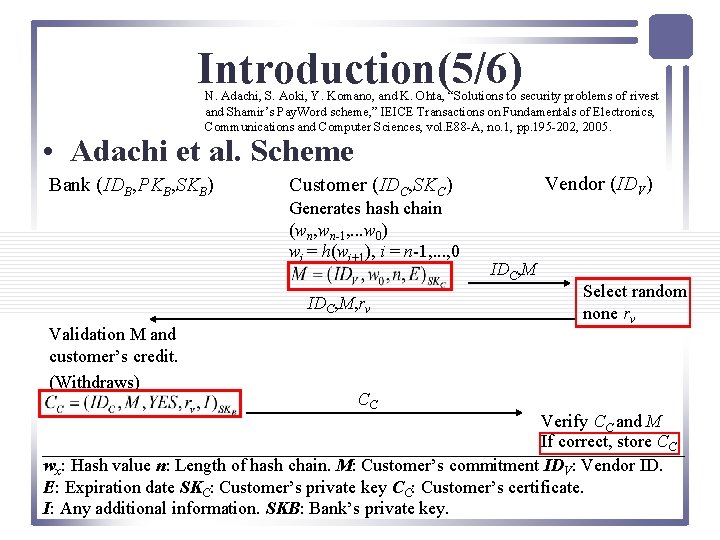
Introduction(5/6) N. Adachi, S. Aoki, Y. Komano, and K. Ohta, “Solutions to security problems of rivest and Shamir’s Pay. Word scheme, ” IEICE Transactions on Fundamentals of Electronics, Communications and Computer Sciences, vol. E 88 -A, no. 1, pp. 195 -202, 2005. • Adachi et al. Scheme Bank (IDB, PKB, SKB) Generates hash chain (wn, wn-1, . . . w 0) wi = h(wi+1), i = n-1, . . . , 0 IDC, M, rv Validation M and customer’s credit. (Withdraws) Vendor (IDV) Customer (IDC, SKC) CC IDC, M Select random none rv Verify CC and M If correct, store CC wx: Hash value n: Length of hash chain. M: Customer’s commitment IDV: Vendor ID. E: Expiration date SKC: Customer’s private key CC: Customer’s certificate. I: Any additional information. SKB: Bank’s private key.
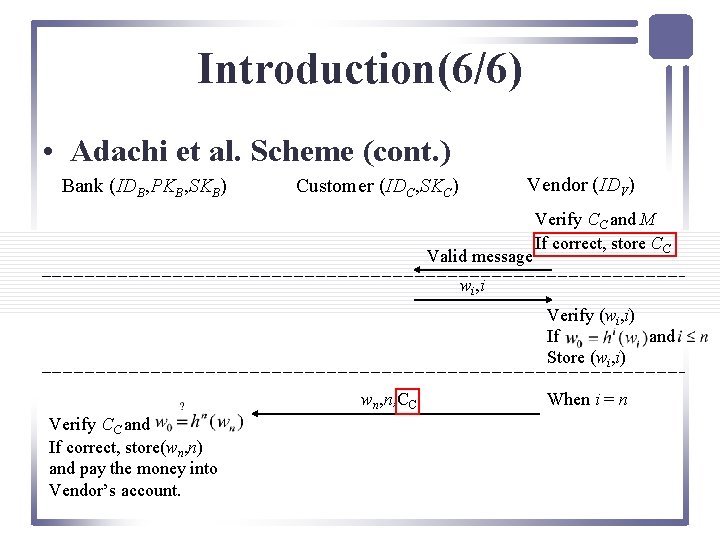
Introduction(6/6) • Adachi et al. Scheme (cont. ) Bank (IDB, PKB, SKB) Vendor (IDV) Customer (IDC, SKC) Valid message Verify CC and M If correct, store CC wi, i Verify (wi, i) If and Store (wi, i) wn, n, CC Verify CC and If correct, store(wn, n) and pay the money into Vendor’s account. When i = n
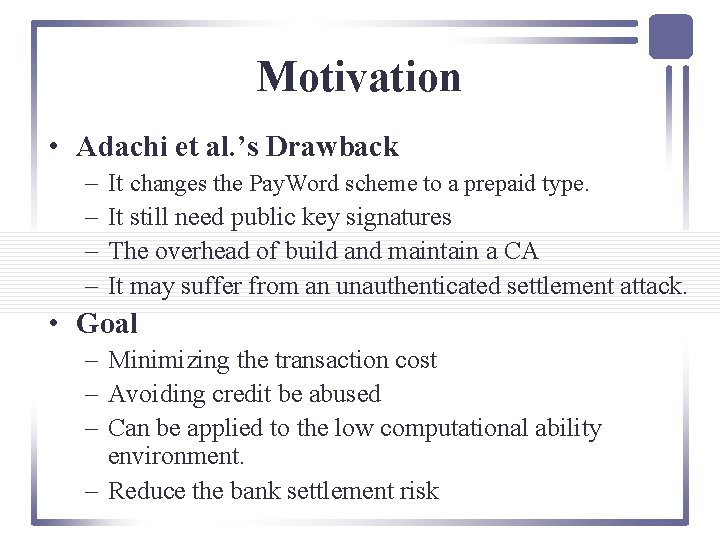
Motivation • Adachi et al. ’s Drawback – – It changes the Pay. Word scheme to a prepaid type. It still need public key signatures The overhead of build and maintain a CA It may suffer from an unauthenticated settlement attack. • Goal – Minimizing the transaction cost – Avoiding credit be abused – Can be applied to the low computational ability environment. – Reduce the bank settlement risk
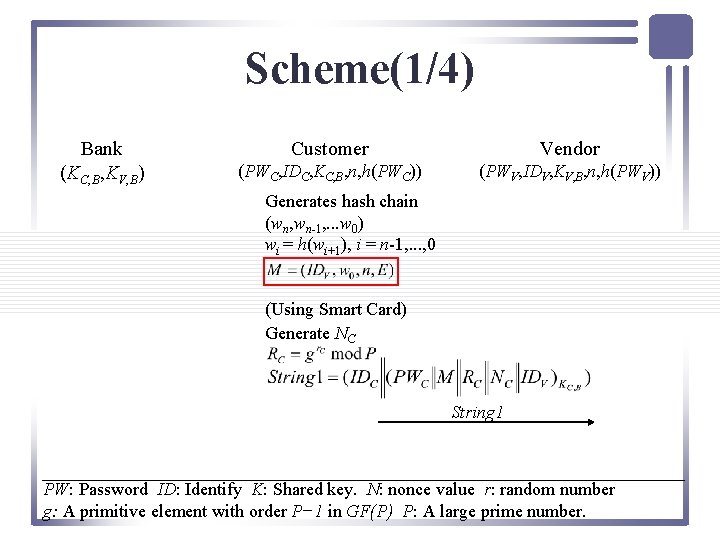
Scheme(1/4) Bank (KC, B, KV, B) Customer Vendor (PWC, IDC, KC, B, n, h(PWC)) (PWV, IDV, KV, B, n, h(PWV)) Generates hash chain (wn, wn-1, . . . w 0) wi = h(wi+1), i = n-1, . . . , 0 (Using Smart Card) Generate NC String 1 PW: Password ID: Identify K: Shared key. N: nonce value r: random number g: A primitive element with order P− 1 in GF(P) P: A large prime number.
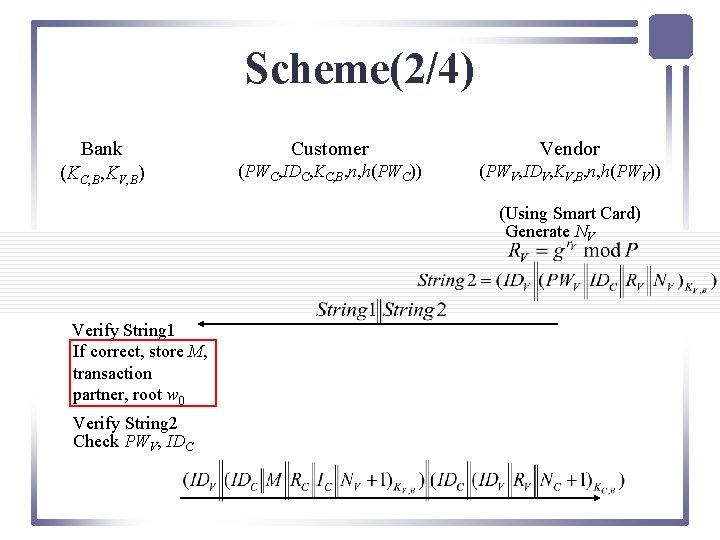
Scheme(2/4) Bank (KC, B, KV, B) Customer Vendor (PWC, IDC, KC, B, n, h(PWC)) (PWV, IDV, KV, B, n, h(PWV)) (Using Smart Card) Generate NV Verify String 1 If correct, store M, transaction partner, root w 0 Verify String 2 Check PWV, IDC
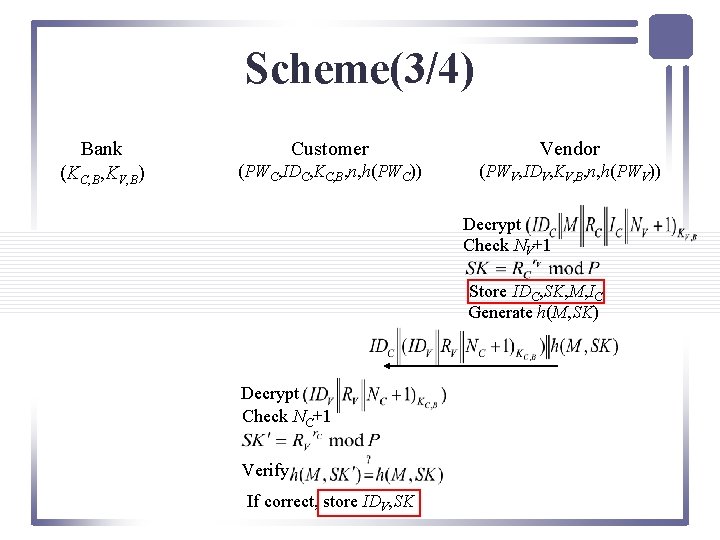
Scheme(3/4) Bank (KC, B, KV, B) Customer Vendor (PWC, IDC, KC, B, n, h(PWC)) (PWV, IDV, KV, B, n, h(PWV)) Decrypt Check NV+1 Store IDC, SK, M, IC Generate h(M, SK) Decrypt Check NC+1 Verify If correct, store IDV, SK
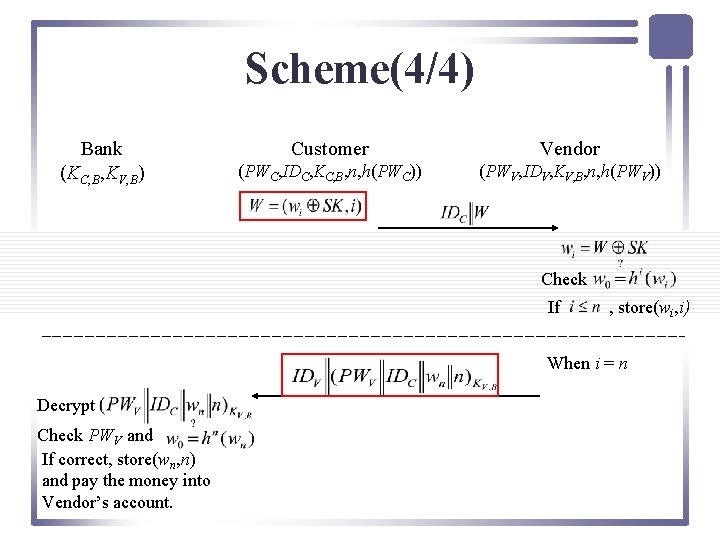
Scheme(4/4) Bank (KC, B, KV, B) Customer Vendor (PWC, IDC, KC, B, n, h(PWC)) (PWV, IDV, KV, B, n, h(PWV)) Check If , store(wi, i) When i = n Decrypt Check PWV and If correct, store(wn, n) and pay the money into Vendor’s account.
Security Analysis • • • Credit Abuse Attack Counterfeiting Pay. Word Bank Falsification Attack Unauthorized Withdrawal Double Spending Replay Attack
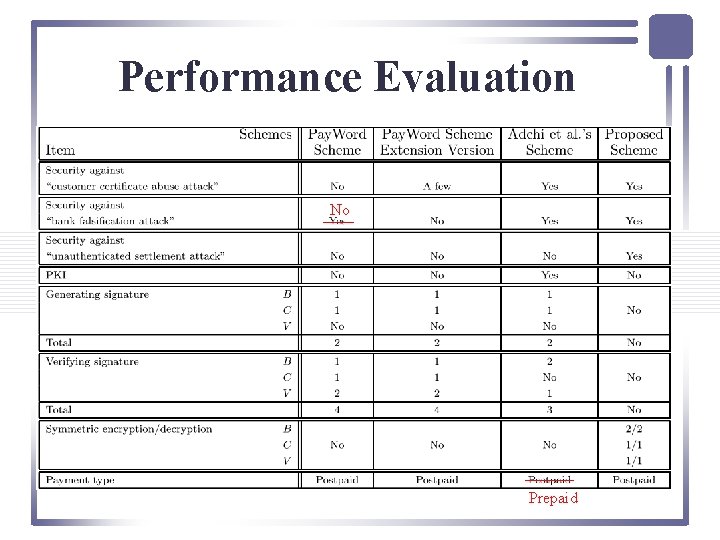
Performance Evaluation No Prepaid
Advantage vs. Drawback • Advantage – Low power consumption – It can resist several attack. – All wi are secret over the Internet, and each transmission message has to be authenticated. • Drawback – Bank has to pre-share the secret keys to customer and the vender.
Comment • It didn’t consider about the exponentiation cost of session key. • It may not need the smart card to do this protocol. • It didn’t have comparison of storage. • It is not convenient to used on mobile phone or PDA. • This scheme need additional hardware (ex. smart card, reader) and middleware to handle the transactions.
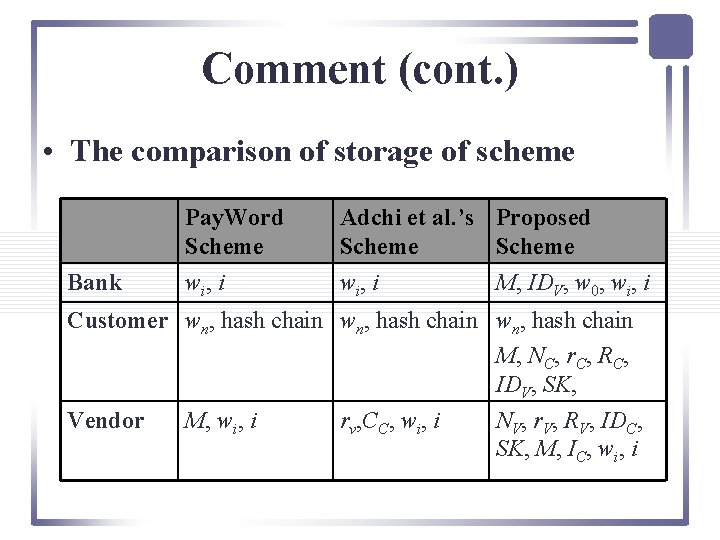
Comment (cont. ) • The comparison of storage of scheme Bank Pay. Word Scheme w i, i Adchi et al. ’s Proposed Scheme w i, i M, IDV, w 0, wi, i Customer wn, hash chain M, NC, r. C, RC, IDV, SK, Vendor M, wi, i rv, CC, wi, i NV, r. V, RV, IDC, SK, M, IC, wi, i
- Slides: 18