An Architecture for Privacy Sensitive Ubiquitous Computing Jason
An Architecture for Privacy -Sensitive Ubiquitous Computing Jason I. Hong HCI Institute Carnegie Mellon University James A. Landay Computer Science and Eng. University of Washington
Ubicomp Privacy is a Serious Concern From a nurse required to wear active badge “[It] could tell when you were in the bathroom, when you left the unit, and how long and where you ate your lunch. EXACTLY what you are afraid of. ” - allnurses. com
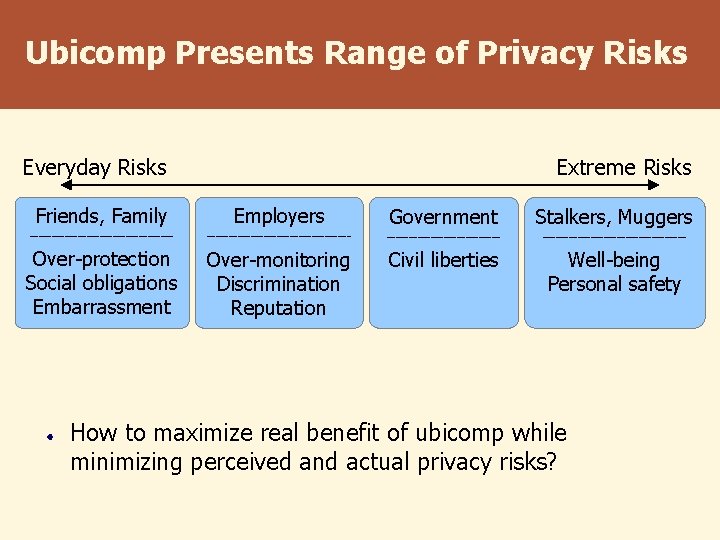
Ubicomp Presents Range of Privacy Risks Everyday Risks Friends, Family Extreme Risks Employers Government _________________________________ Over-protection Social obligations Embarrassment Over-monitoring Discrimination Reputation Civil liberties Stalkers, Muggers _________________ Well-being Personal safety How to maximize real benefit of ubicomp while minimizing perceived and actual privacy risks?
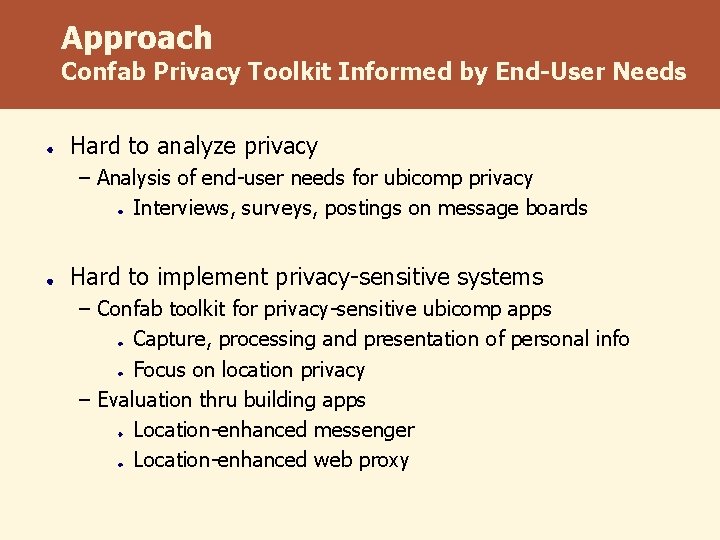
Approach Confab Privacy Toolkit Informed by End-User Needs Hard to analyze privacy – Analysis of end-user needs for ubicomp privacy Interviews, surveys, postings on message boards Hard to implement privacy-sensitive systems – Confab toolkit for privacy-sensitive ubicomp apps Capture, processing and presentation of personal info Focus on location privacy – Evaluation thru building apps Location-enhanced messenger Location-enhanced web proxy
Outline þ Motivation ¨ End-user Privacy Needs ¨ Confab Toolkit for Privacy-Sensitive Ubicomp ¨ Applications Built
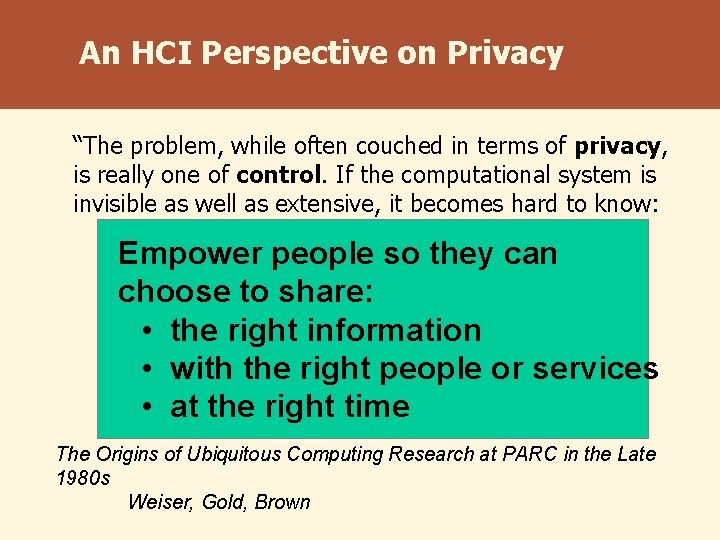
An HCI Perspective on Privacy “The problem, while often couched in terms of privacy, is really one of control. If the computational system is invisible as well as extensive, it becomes hard to know: – what is controlling what people –Empower what is connected to what so they to share: –choose where information is flowing – how it is being used • the right information can • with the right people or services • at the right time The Origins of Ubiquitous Computing Research at PARC in the Late 1980 s Weiser, Gold, Brown
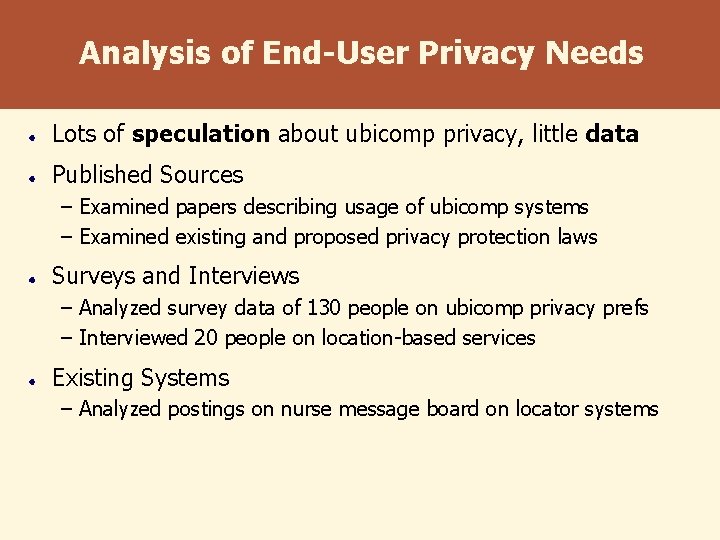
Analysis of End-User Privacy Needs Lots of speculation about ubicomp privacy, little data Published Sources – Examined papers describing usage of ubicomp systems – Examined existing and proposed privacy protection laws Surveys and Interviews – Analyzed survey data of 130 people on ubicomp privacy prefs – Interviewed 20 people on location-based services Existing Systems – Analyzed postings on nurse message board on locator systems
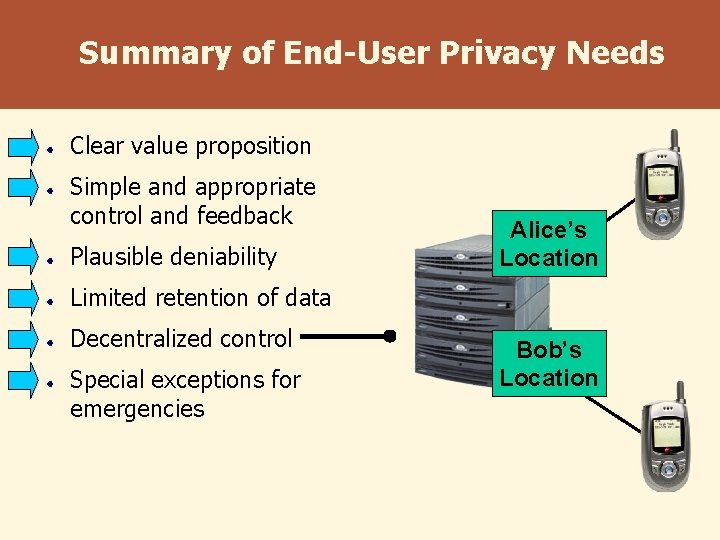
Summary of End-User Privacy Needs Clear value proposition Simple and appropriate control and feedback Plausible deniability Alice’s Location Limited retention of data Decentralized control Special exceptions for emergencies Bob’s Location
Outline þ Motivation þ End-user Privacy Needs ¨ Confab Toolkit for Privacy-Sensitive Ubicomp ¨ Applications Built
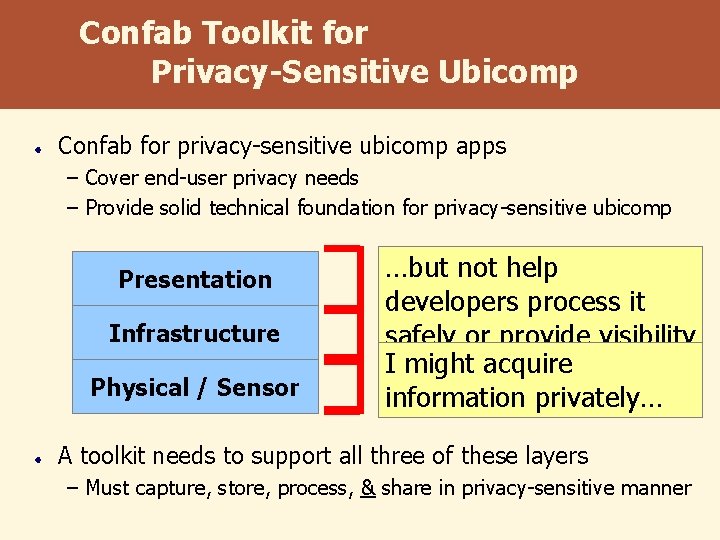
Confab Toolkit for Privacy-Sensitive Ubicomp Confab for privacy-sensitive ubicomp apps – Cover end-user privacy needs – Provide solid technical foundation for privacy-sensitive ubicomp Presentation Infrastructure Physical / Sensor …but notpresent help choices I might developers process it well to users… …but have control safely not or provide visibility Iover acquire how the info was tomight end-users information privately… acquired or processed A toolkit needs to support all three of these layers – Must capture, store, process, & share in privacy-sensitive manner
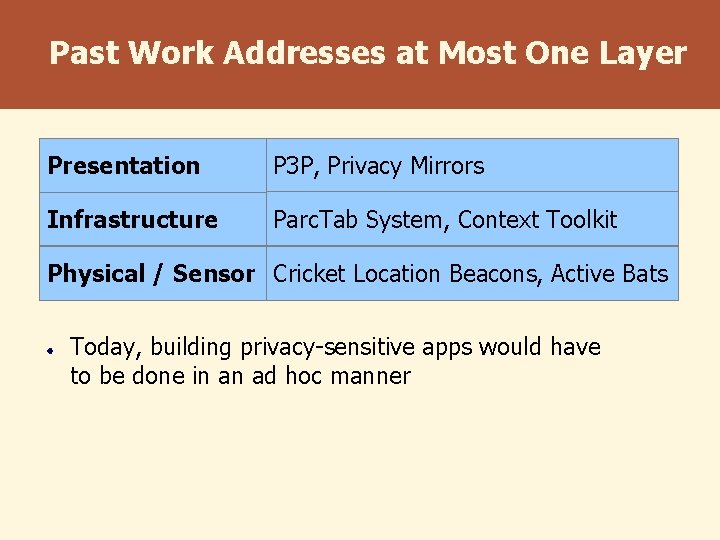
Past Work Addresses at Most One Layer Presentation P 3 P, Privacy Mirrors Infrastructure Parc. Tab System, Context Toolkit Physical / Sensor Cricket Location Beacons, Active Bats Today, building privacy-sensitive apps would have to be done in an ad hoc manner
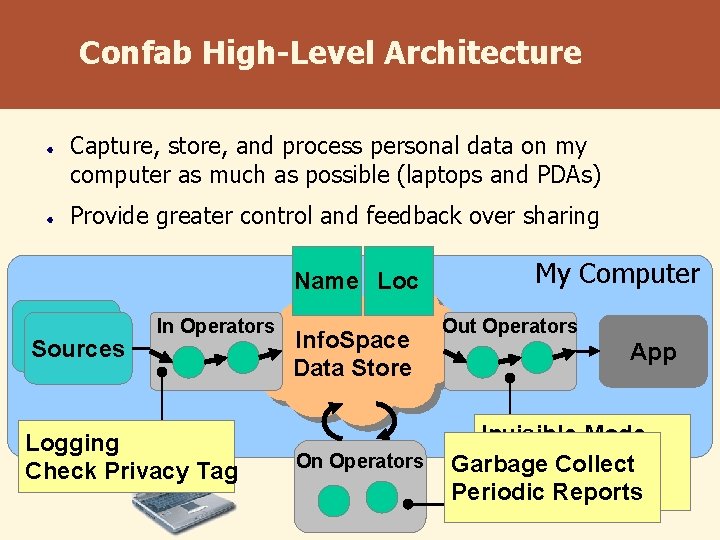
Confab High-Level Architecture Capture, store, and process personal data on my computer as much as possible (laptops and PDAs) Provide greater control and feedback over sharing Name Loc Sources In Operators Logging Check Privacy Tag Info. Space Data Store On Operators My Computer Out Operators App Invisible Mode Enforce Access Garbage Collect User Interfaces Periodic Reports
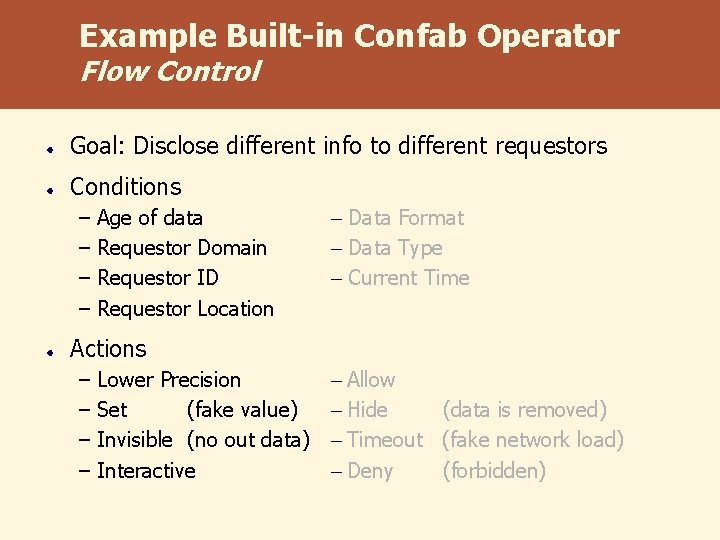
Example Built-in Confab Operator Flow Control Goal: Disclose different info to different requestors Conditions – Age of data – Requestor Domain – Requestor ID – Requestor Location – Data Format – Data Type – Current Time Actions – Lower Precision – Set (fake value) – Invisible (no out data) – Interactive – Allow – Hide (data is removed) – Timeout (fake network load) – Deny (forbidden)
Outline þ Motivation þ End-user Privacy Needs þ Confab Toolkit for Privacy-Sensitive Ubicomp ¨ Physical layer for acquiring location ¨ Infrastructure layer ¨ Presentation layer ¨ Applications Built
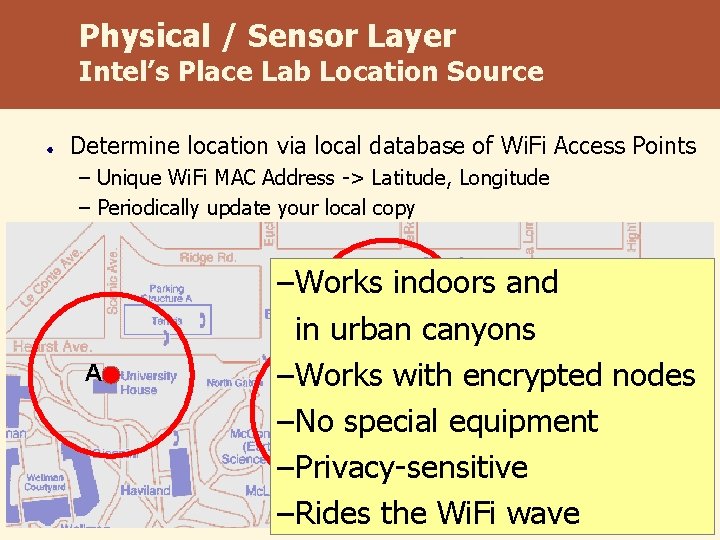
Physical / Sensor Layer Intel’s Place Lab Location Source Determine location via local database of Wi. Fi Access Points – Unique Wi. Fi MAC Address -> Latitude, Longitude – Periodically update your local copy A –Works indoors and C in urban canyons –Works with encrypted nodes B –No special equipment –Privacy-sensitive –Rides the Wi. Fi wave
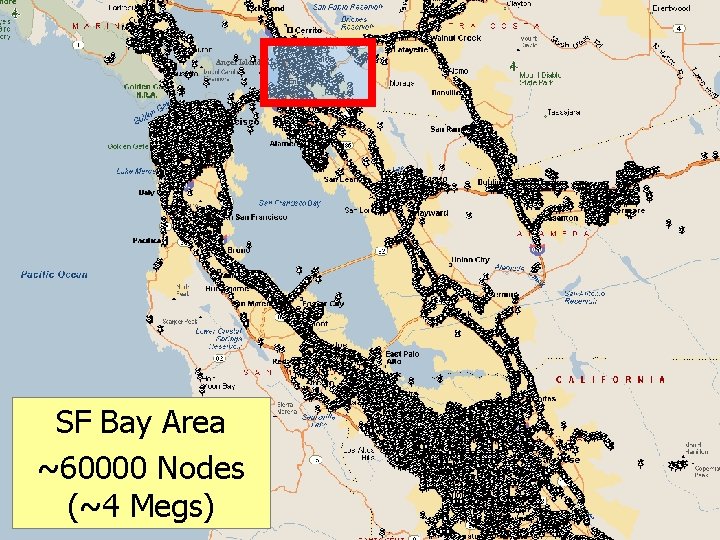
Place. Lab Data at SF Bay Area ~60000 Nodes (~4 Megs)
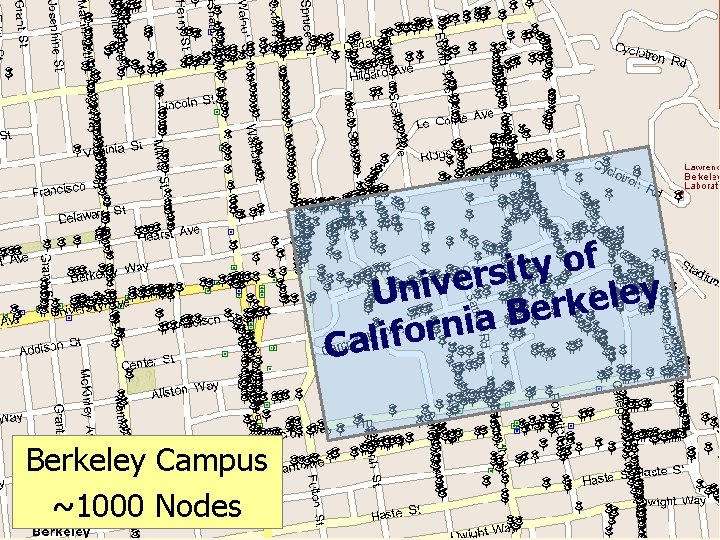
Place. Lab Data at UC Berkeley f o y t i s r e v i y Un e l e k r e B a i n r o f Cali Berkeley Campus ~1000 Nodes
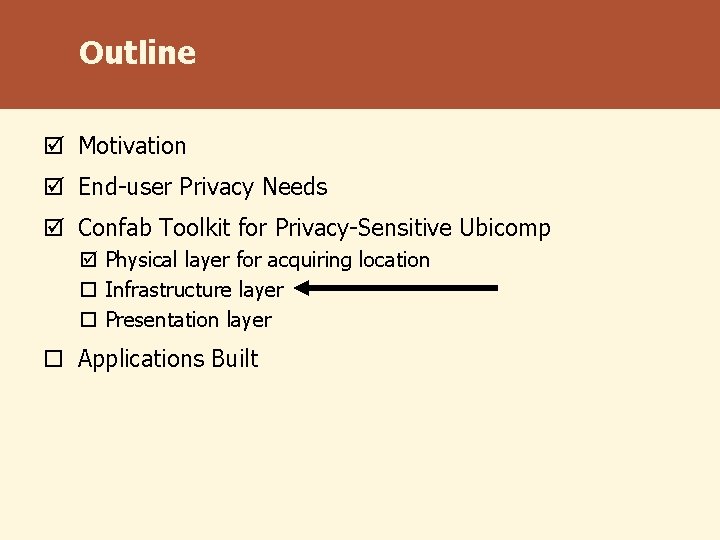
Outline þ Motivation þ End-user Privacy Needs þ Confab Toolkit for Privacy-Sensitive Ubicomp þ Physical layer for acquiring location ¨ Infrastructure layer ¨ Presentation layer ¨ Applications Built
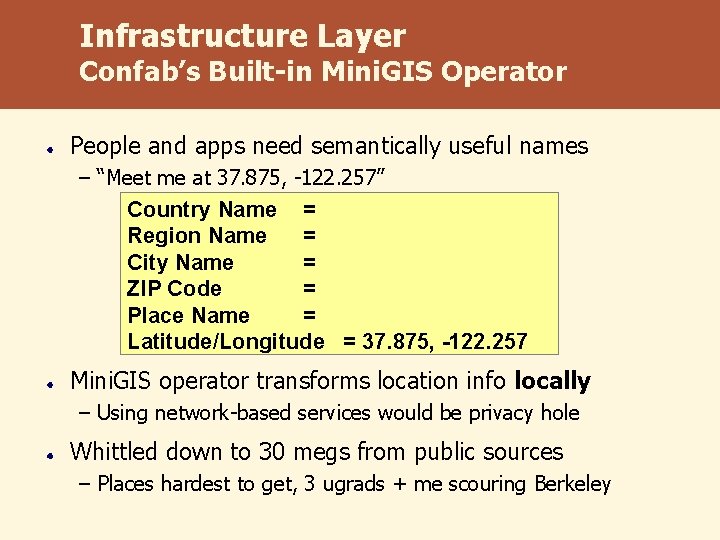
Infrastructure Layer Confab’s Built-in Mini. GIS Operator People and apps need semantically useful names – “Meet me at 37. 875, -122. 257” Country Name = United States Region Name = California City Name = Berkeley ZIP Code = 94709 Place Name = Soda Hall Latitude/Longitude = 37. 875, -122. 257 Mini. GIS operator transforms location info locally – Using network-based services would be privacy hole Whittled down to 30 megs from public sources – Places hardest to get, 3 ugrads + me scouring Berkeley
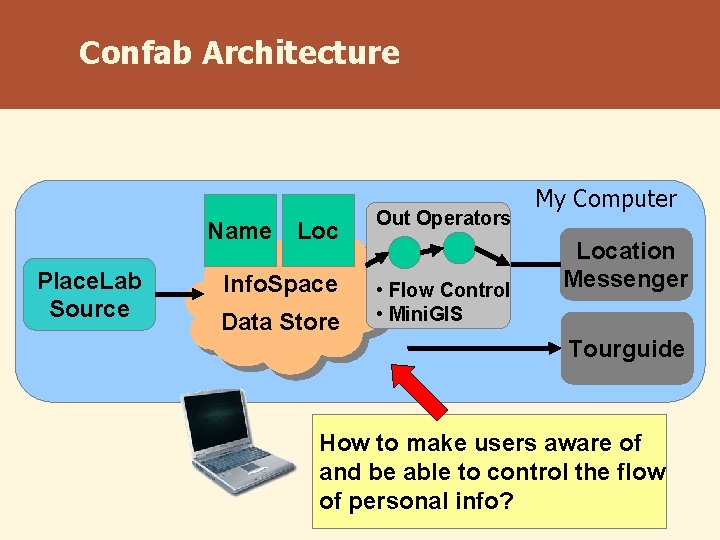
Confab Architecture Name Loc Place. Lab Source Info. Space Data Store Out Operators • Flow Control • Mini. GIS My Computer Location Messenger Tourguide How to make users aware of and be able to control the flow of personal info?
Outline þ Motivation þ End-user Privacy Needs þ Pitfalls in User Interfaces for Privacy þ Confab Toolkit for Privacy-Sensitive Ubicomp þ Physical layer for acquiring location þ Infrastructure layer ¨ Presentation layer ¨ Applications Built
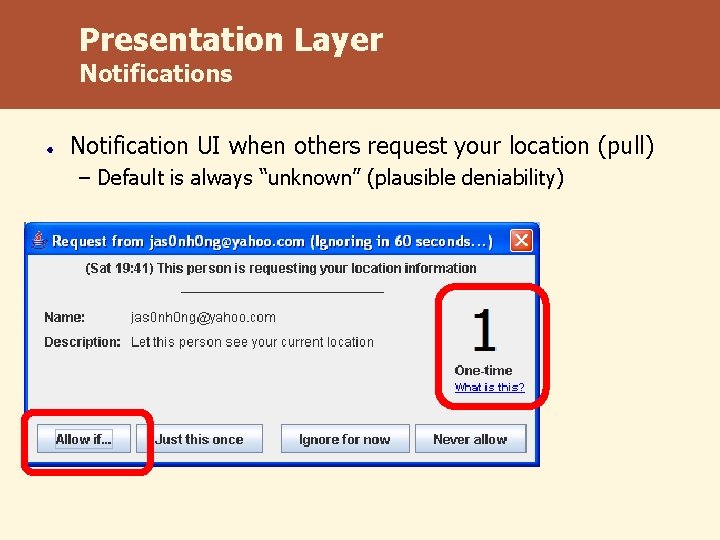
Presentation Layer Notifications Notification UI when others request your location (pull) – Default is always “unknown” (plausible deniability)
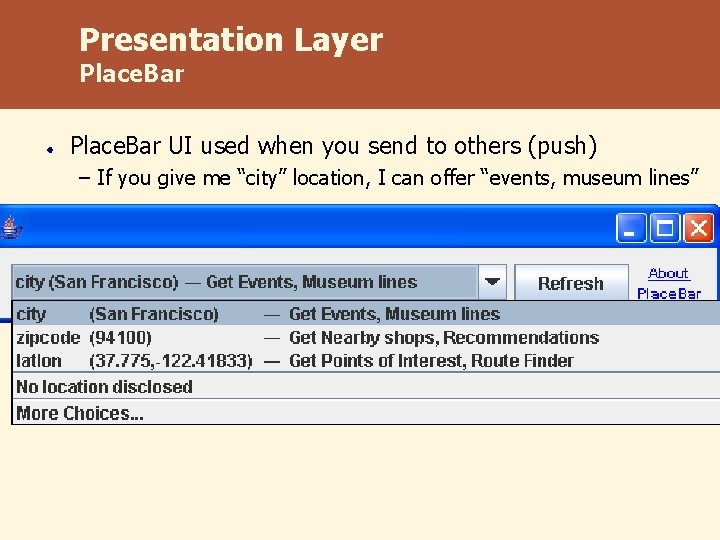
Presentation Layer Place. Bar UI used when you send to others (push) – If you give me “city” location, I can offer “events, museum lines”
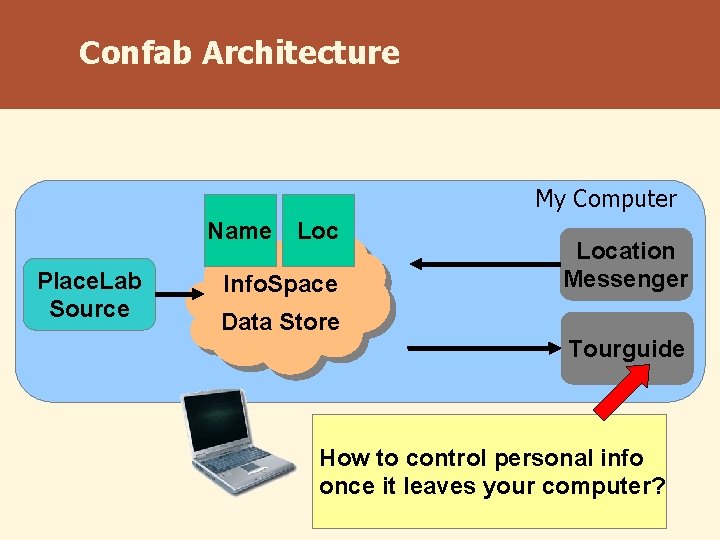
Confab Architecture My Computer Name Loc Place. Lab Source Info. Space Location Messenger Data Store Tourguide How to control personal info once it leaves your computer?

Privacy Tags Digital Rights Management for Privacy – Like adding note to email, “Please don’t forward” – Notify address - notify-abc@cs. berkeley. edu – Time to live - 5 days – Max number of sightings - last 5 sightings of my location Provide libraries for making it easy for app developers Requires non-technical solutions for deployment – Market support thru Trust. E, Consumer Reports – Legal support thru data retention laws
Outline þ Motivation þ Analysis of End-user Privacy Needs þ Confab Toolkit for Privacy-Sensitive Ubicomp ¨ Applications Built
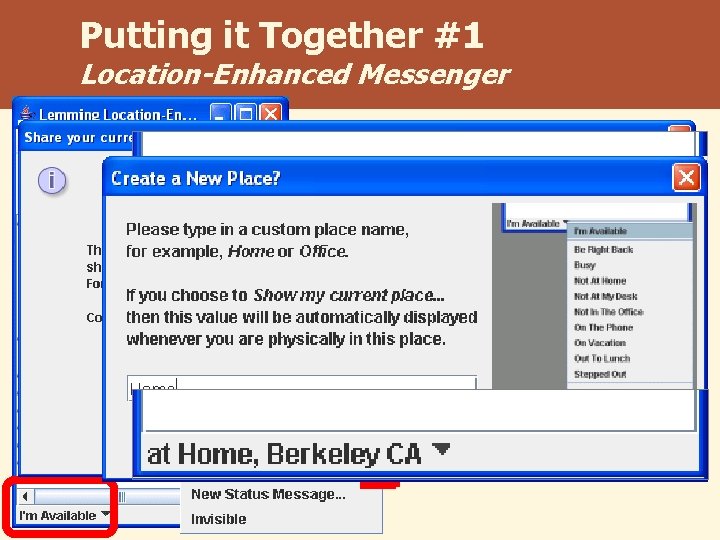
Putting it Together #1 Location-Enhanced Messenger
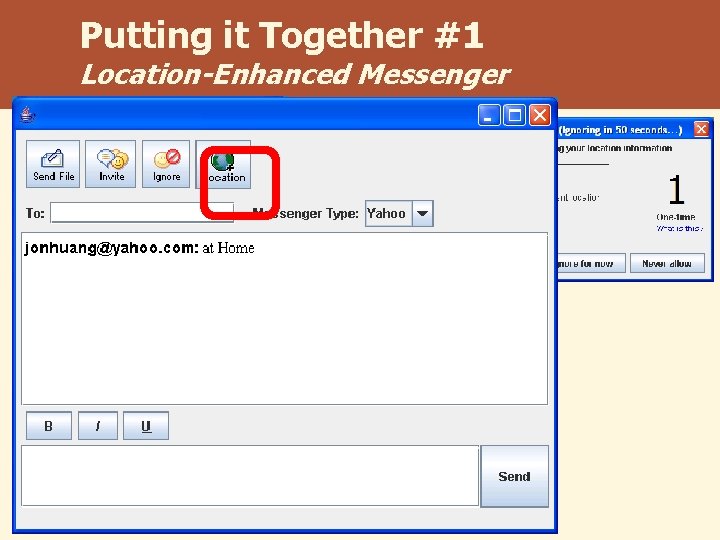
Putting it Together #1 Location-Enhanced Messenger
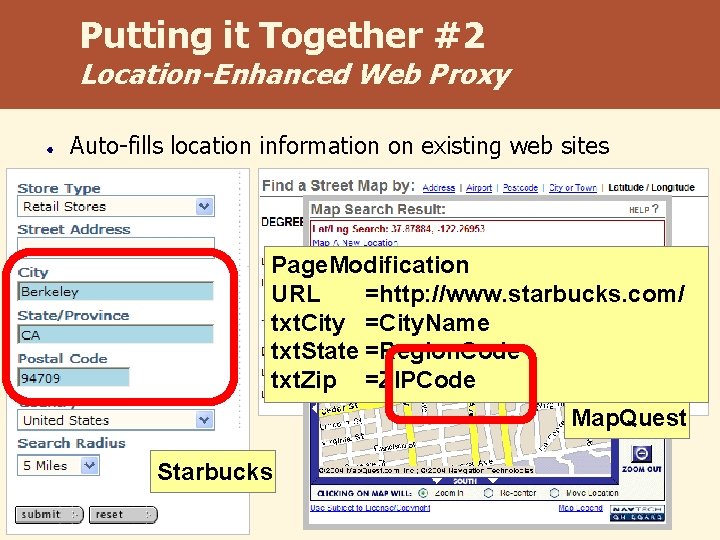
Putting it Together #2 Location-Enhanced Web Proxy Auto-fills location information on existing web sites Page. Modification URL =http: //www. starbucks. com/ txt. City =City. Name txt. State =Region. Code txt. Zip =ZIPCode Map. Quest Starbucks
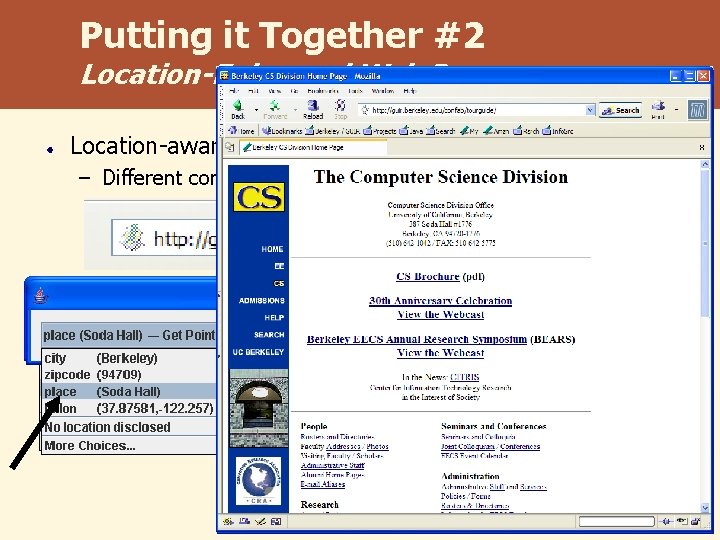
Putting it Together #2 Location-Enhanced Web Proxy Location-aware web sites – Different content based on your current location
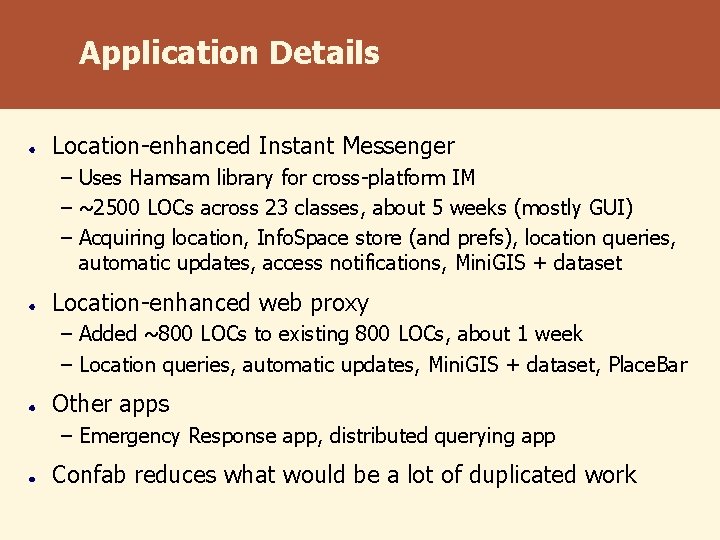
Application Details Location-enhanced Instant Messenger – Uses Hamsam library for cross-platform IM – ~2500 LOCs across 23 classes, about 5 weeks (mostly GUI) – Acquiring location, Info. Space store (and prefs), location queries, automatic updates, access notifications, Mini. GIS + dataset Location-enhanced web proxy – Added ~800 LOCs to existing 800 LOCs, about 1 week – Location queries, automatic updates, Mini. GIS + dataset, Place. Bar Other apps – Emergency Response app, distributed querying app Confab reduces what would be a lot of duplicated work
Other Parts of this Work Common risks to design for in privacy-sensitive systems? Hong, Ng, Lederer, Landay [DIS 2004] Privacy Risk Models for Designing Privacy-Sensitive Ubiquitous Computing Systems Common mistakes to avoid in the user interface? Lederer, Hong, Dey, Landay [PUC 2004] Personal Privacy through Understanding and Action: Pitfalls for Designers Design rationale at presentation layer User evaluations of the apps Five
Conclusions Confab toolkit for facilitating construction of privacysensitive ubicomp applications – Privacy at physical, infrastructure, and presentation layers – Push architecture towards local capture, processing, storage – Couple w/ better UIs for greater choice, control, and feedback “Use technology correctly to enhance life. It is important that people have a choice in how much information can be disclosed. Then the technology is useful. ”
Acknowledgements Thanks to: DARPA Expeditions NSF ITR Intel Fellowship Siebel Systems Fellowship PARC Intel Research http: //placelab. org John Canny Anind Dey Scott Lederer Jennifer Ng Bill Schilit Doug Tygar Many, many others… Jason I. Hong jasonh@cs. berkeley. edu http: //guir. berkeley. edu/confab
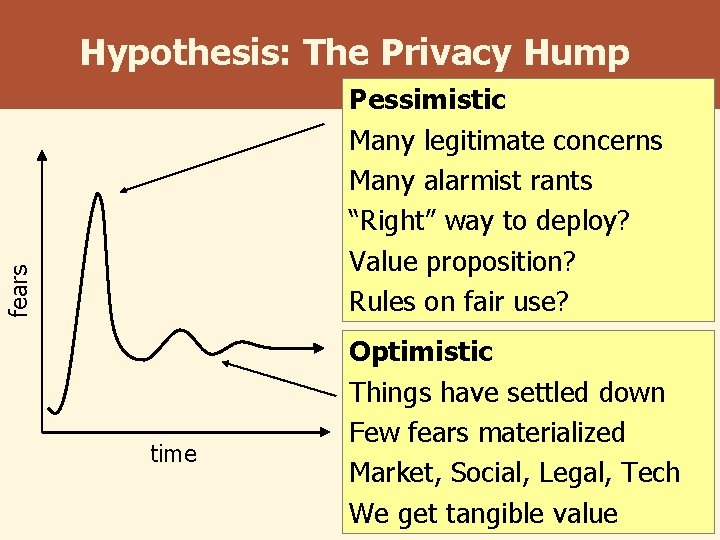
Hypothesis: The Privacy Hump fears Pessimistic Many legitimate concerns Many alarmist rants “Right” way to deploy? Value proposition? Rules on fair use? time Optimistic Things have settled down Few fears materialized Market, Social, Legal, Tech We get tangible value
Missing Pieces of the Privacy Puzzle How do privacy perceptions change over time? – Ecommerce studies suggest experience important, privacy hump How do privacy perceptions vary across cultures? – Western cultures tend to be more individualistic Metrics for privacy? – Specific data types (location) or problems (price discrimination) Economic incentives for companies to do “the right thing”? Other kinds of protection at the physical layer? How perfect do we want our ubicomp systems to be? – Accurate and reliable -> harder to lie
- Slides: 36