Alibi Attested Instruction Tracing as a Secure Thin

Alibi: Attested Instruction Tracing as a Secure Thin Intermediate Layer (STIL) Primitive Amit Vasudevan, Chen, Adrian Perrig Cy. Lab, Carnegie Mellon University Vyas Sekar, Petros Maniatis ISTC for Secure Computing 1
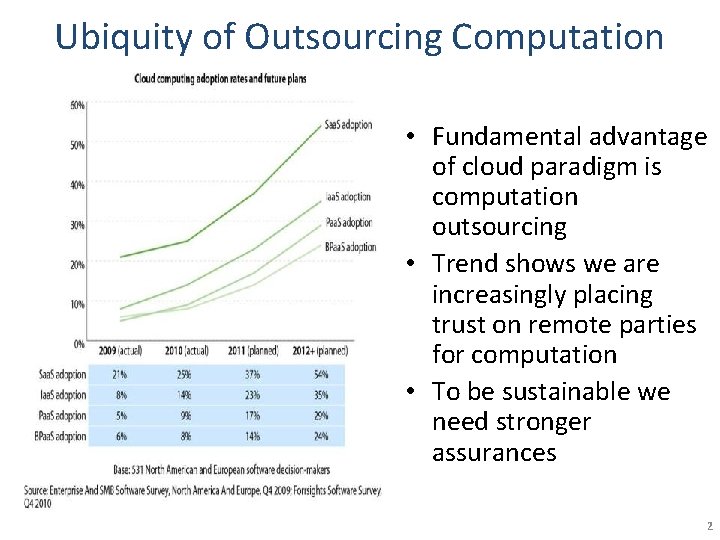
Ubiquity of Outsourcing Computation • Fundamental advantage of cloud paradigm is computation outsourcing • Trend shows we are increasingly placing trust on remote parties for computation • To be sustainable we need stronger assurances 2
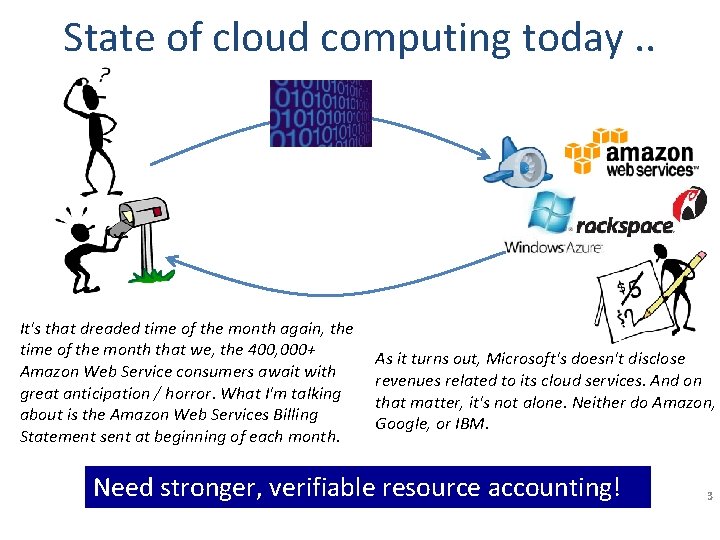
State of cloud computing today. . It's that dreaded time of the month again, the time of the month that we, the 400, 000+ Amazon Web Service consumers await with great anticipation / horror. What I'm talking about is the Amazon Web Services Billing Statement sent at beginning of each month. As it turns out, Microsoft's doesn't disclose revenues related to its cloud services. And on that matter, it's not alone. Neither do Amazon, Google, or IBM. Need stronger, verifiable resource accounting! 3
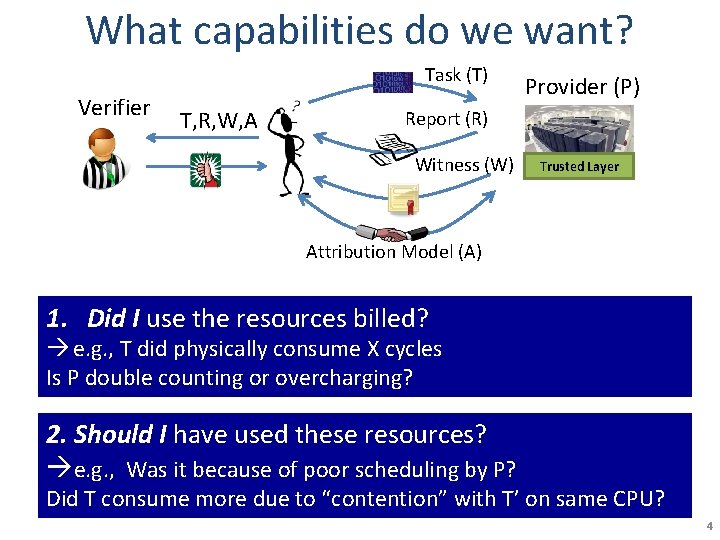
What capabilities do we want? Task (T) Verifier T, R, W, A Provider (P) Report (R) Witness (W) Trusted Layer Attribution Model (A) 1. Did I use the resources billed? e. g. , T did physically consume X cycles Is P double counting or overcharging? 2. Should I have used these resources? e. g. , Was it because of poor scheduling by P? Did T consume more due to “contention” with T’ on same CPU? 4
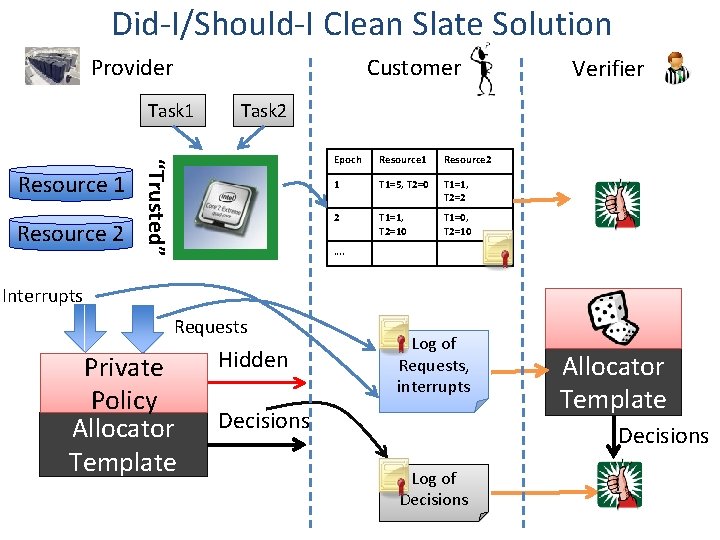
Did-I/Should-I Clean Slate Solution Provider Customer Task 1 Resource 2 Task 2 “Trusted” Resource 1 Verifier Epoch Resource 1 Resource 2 1 T 1=5, T 2=0 T 1=1, T 2=2 2 T 1=1, T 2=10 T 1=0, T 2=10 …. Interrupts Requests Private Policy Allocator Template Hidden Log of Requests, interrupts Decisions Allocator Template Decisions Log of Decisions
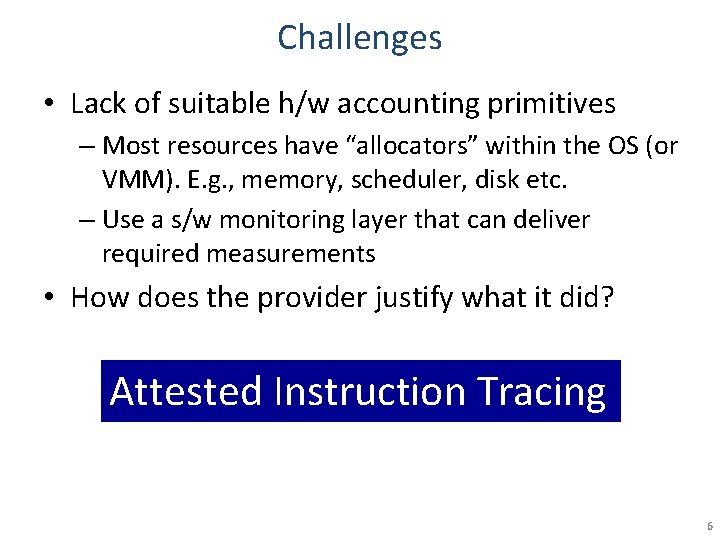
Challenges • Lack of suitable h/w accounting primitives – Most resources have “allocators” within the OS (or VMM). E. g. , memory, scheduler, disk etc. – Use a s/w monitoring layer that can deliver required measurements • How does the provider justify what it did? Attested Instruction Tracing 6
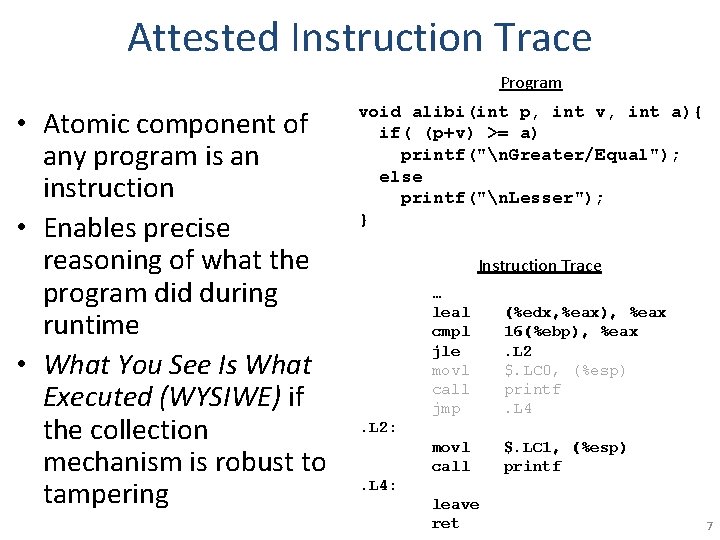
Attested Instruction Trace Program • Atomic component of any program is an instruction • Enables precise reasoning of what the program did during runtime • What You See Is What Executed (WYSIWE) if the collection mechanism is robust to tampering void alibi(int p, int v, int a){ if( (p+v) >= a) printf("n. Greater/Equal"); else printf("n. Lesser"); } Instruction Trace … leal cmpl jle movl call jmp (%edx, %eax), %eax 16(%ebp), %eax. L 2 $. LC 0, (%esp) printf. L 4 movl call $. LC 1, (%esp) printf . L 2: . L 4: leave ret 7
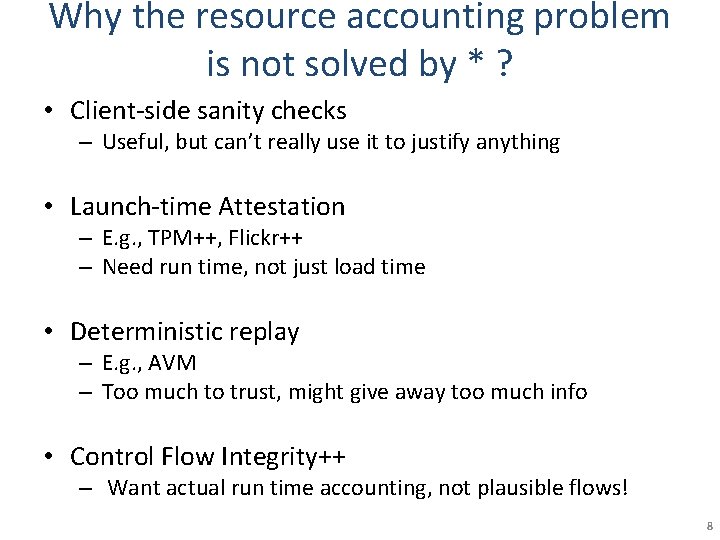
Why the resource accounting problem is not solved by * ? • Client-side sanity checks – Useful, but can’t really use it to justify anything • Launch-time Attestation – E. g. , TPM++, Flickr++ – Need run time, not just load time • Deterministic replay – E. g. , AVM – Too much to trust, might give away too much info • Control Flow Integrity++ – Want actual run time accounting, not plausible flows! 8
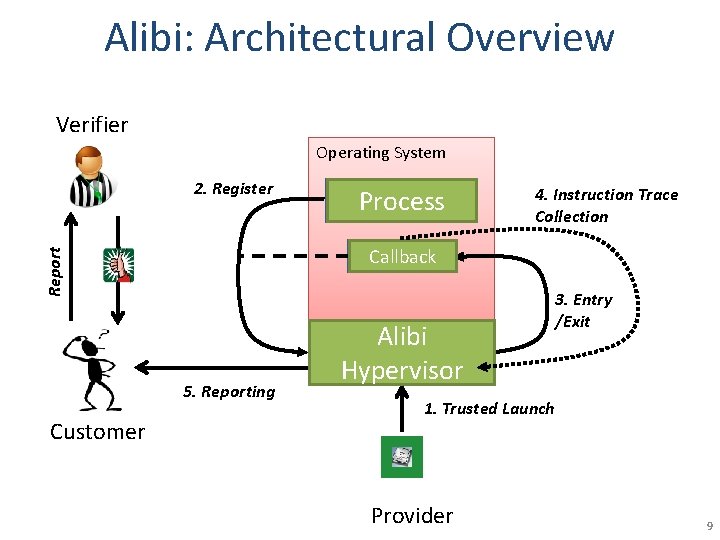
Alibi: Architectural Overview Verifier Operating System 2. Register 4. Instruction Trace Collection Report Callback 5. Reporting Customer Process Alibi Hypervisor 3. Entry /Exit 1. Trusted Launch Provider 9
Attested Instruction Tracing Benefits and Applications • A strong general primitive – Attesting actual execution vs. launch-time attestation • Benefits – fine-grained and accurate – minimal-TCB approach -> robust to tampering – can be used on commodity x 86 platforms today! • Applications – – – Attested Read from an input port Attested accesses to disk Attested CPU cycle counter read Malware detection … 10
Alibi: Attested Instruction Tracing as a Secure Thin Intermediate Layer (STIL) Primitive • Introduction and Motivation • Attested Instruction Tracing • Machinery • Summary and Discussion 11
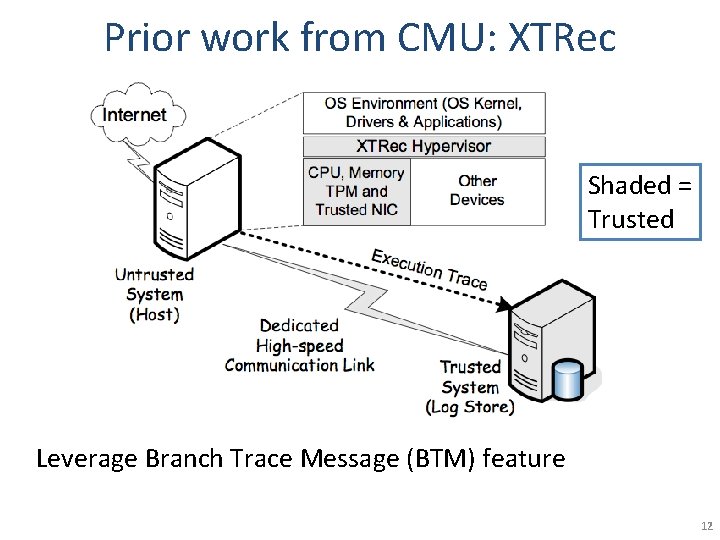
Prior work from CMU: XTRec Shaded = Trusted Leverage Branch Trace Message (BTM) feature 12
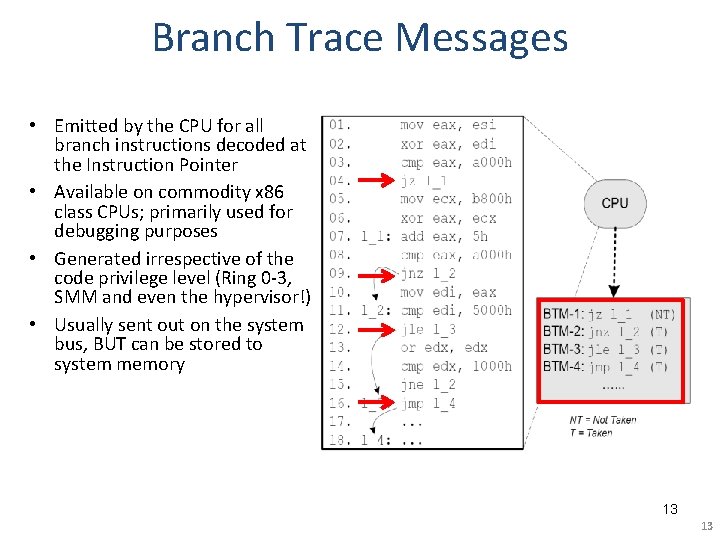
Branch Trace Messages • Emitted by the CPU for all branch instructions decoded at the Instruction Pointer • Available on commodity x 86 class CPUs; primarily used for debugging purposes • Generated irrespective of the code privilege level (Ring 0 -3, SMM and even the hypervisor!) • Usually sent out on the system bus, BUT can be stored to system memory 13 13
Dynamic Code Capture • BTMs record only control-flow instructions – What about other instructions? • Hardware managed physical memory page tables – W XOR X policy on physical memory pages – Record contents of page prior to converting it to executable status – Superimpose BTMs over corresponding code page contents 14
Alibi: Current status • Port XTRec primitives to IA-32 • Addressing performance issues – Selective logging, BTM cache, LBA-style offload • Using Alibi for Did-I verifiability – e. g. , challenges with dynamic libraries, sys-calls • Using Alibi for Should-I verifiability – Guarantee privacy (code + data) – API for selective logging 15
Alibi: Attested Instruction Tracing as a Secure Thin Intermediate Layer (STIL) Primitive • Introduction and Motivation • Attested Instruction Tracing • Machinery • Summary and Discussion 16
Summary and Discussion • Attested Instruction tracing – A strong general primitive • Attesting actual execution vs. launch-time attestation – fine-grained, accurate, minimal-TCB approach, robust to tampering and applicable to commodity x 86 platforms! • Verifiable Resource Accounting – Did-I and Should-I properties – Provider incentives • Adoption to avoid underutilization, less conservative in accounting, prevent customers from gaming the system 17
- Slides: 17