Algebraic Lower Bounds for Computing on Encrypted Data
Algebraic Lower Bounds for Computing on Encrypted Data Rafail Ostrovsky William E. Skeith III
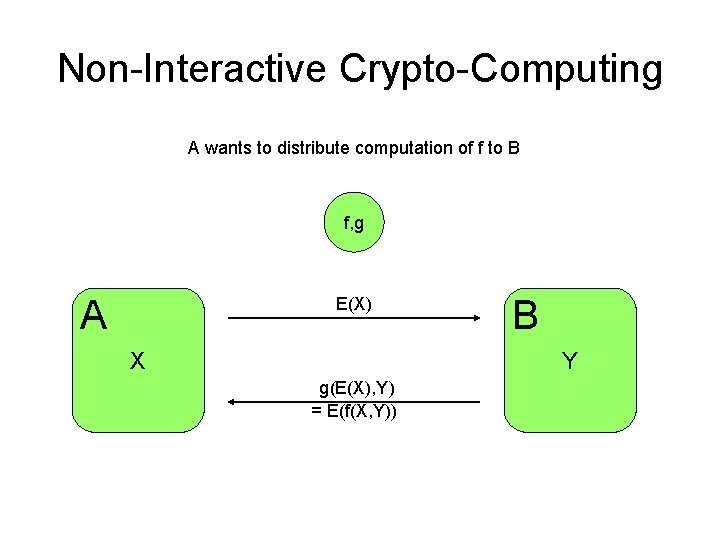
Non-Interactive Crypto-Computing A wants to distribute computation of f to B f, g A E(X) X B Y g(E(X), Y) = E(f(X, Y))
Homomorphic Encryption and CC • Homomorphic encryption is a very natural starting point, and the primary tool for many CC protocols: • Let f be a function, and A some algebraic structure. – If f can be computed by the algebra of A and A is preserved via homomorphic encryption, – Then we have non-interactive CC of f
Algebraic Non-Interactive CC • Main question: which crypto-computing functions can we implement using known homomorphic cryptosystems? • For a given algebraic structure, what can be accomplished with algebraic computation?
Examples We’ll Study • In an algebraic setting, we address the following: – Private Database Modification – Homomorphic PIR Protocols – Private Keyword Search
![Algebraic Private Database Modification [BKOS] U Mi=(g 1, …, gm) g 1, g 2, Algebraic Private Database Modification [BKOS] U Mi=(g 1, …, gm) g 1, g 2,](http://slidetodoc.com/presentation_image/45aa94e94126e3fcf18b0fa60aa75294/image-6.jpg)
Algebraic Private Database Modification [BKOS] U Mi=(g 1, …, gm) g 1, g 2, …, gm DB X= X 1 X 2 X 3 … … … . . … … … … Xn X’ = F(x 1, …, xn, g 1, …gm , h 1, …hr) All gj, xi, hk 2 A, and F is some “algebraic” function
![Homomorphic PIR Protocols [BGN, KO] U g 1, g 2, …, gm Qi=(g 1, Homomorphic PIR Protocols [BGN, KO] U g 1, g 2, …, gm Qi=(g 1,](http://slidetodoc.com/presentation_image/45aa94e94126e3fcf18b0fa60aa75294/image-7.jpg)
Homomorphic PIR Protocols [BGN, KO] U g 1, g 2, …, gm Qi=(g 1, …, gm) (xj 1, …, xil)=FX(g 1, …gm , h 1, …hr) DB X= X 1 X 2 X 3 … … … . . … … … … Xn FX(g 1, …gm , h 1, …hr) All gj, hk 2 A, and FX is some “algebraic” function determined by the database X 2 An
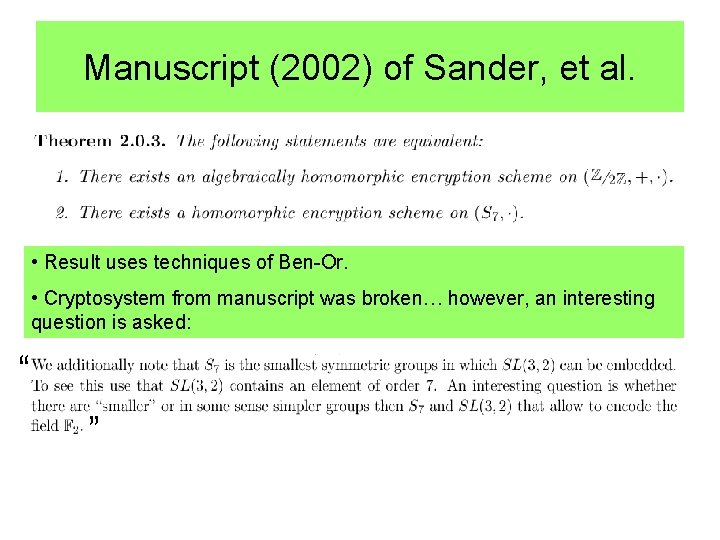
Manuscript (2002) of Sander, et al. • Result uses techniques of Ben-Or. • Cryptosystem from manuscript was broken… however, an interesting question is asked: “ “
Two Results • A positive result: – Homomorphic encryption over any simple non-abelian group is equivalent to fully homomorphic encryption (preserving a ring). – Homomorphic encryption over any simple non-abelian group is equivalent to non-interactive CC. • A family of negative results (i. e. , lower bounds): – Using the algebras preserved by existing cryptosystems, we can show lower bounds for homomorphic PIR, database modification, characteristic vectors…
Our First Result: • For any non-abelian simple group, the following holds: Any circuit with N gates can be replaced by a circuit of size O(N) that uses only the group operation to simulate gates (wires will carry group elements). • Example: for A 5, we can represent a NAND gate ¼ 50 group operations (this may not be minimal…).
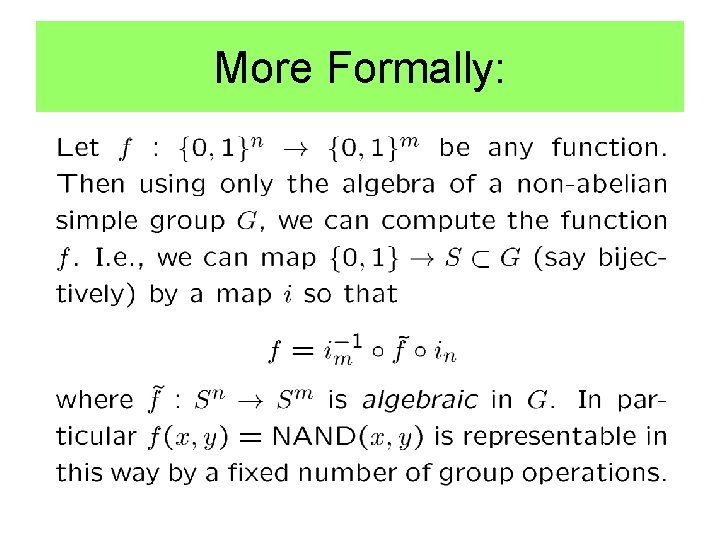
More Formally:
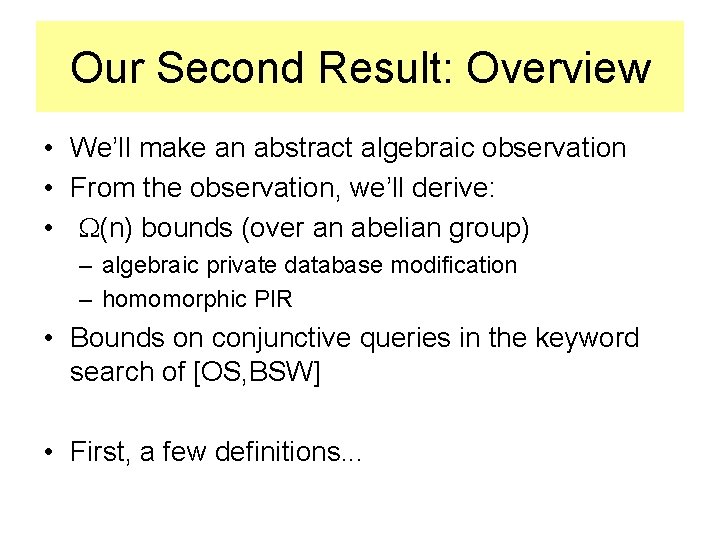
Our Second Result: Overview • We’ll make an abstract algebraic observation • From the observation, we’ll derive: • (n) bounds (over an abelian group) – algebraic private database modification – homomorphic PIR • Bounds on conjunctive queries in the keyword search of [OS, BSW] • First, a few definitions. . .
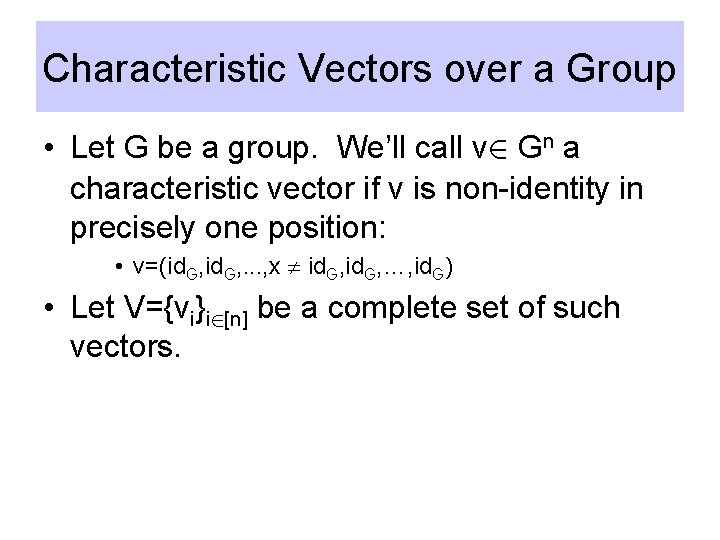
Characteristic Vectors over a Group • Let G be a group. We’ll call v 2 Gn a characteristic vector if v is non-identity in precisely one position: • v=(id. G, . . . , x id. G, …, id. G) • Let V={vi}i 2[n] be a complete set of such vectors.
Question • What is the inherent communication involved in “algebraic” functions that generate characteristic vectors? • We’ll reduce all of our algebraic cryptocomputing protocols to this basic functionality.
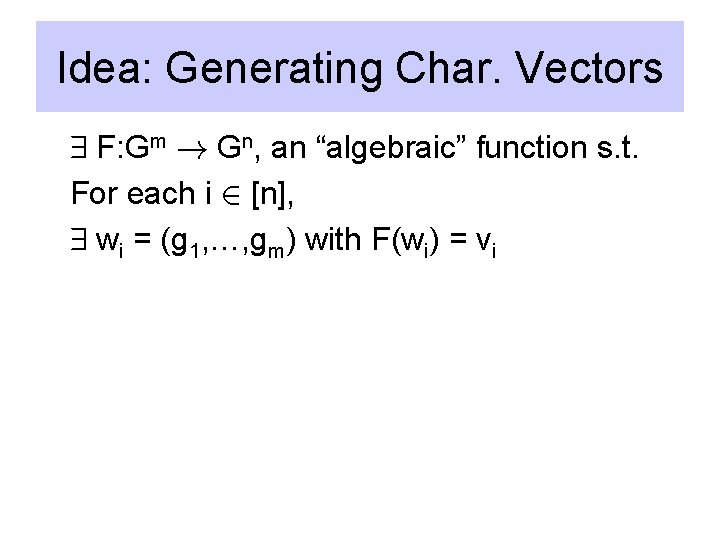
Idea: Generating Char. Vectors 9 F: Gm ! Gn, an “algebraic” function s. t. For each i 2 [n], 9 wi = (g 1, …, gm) with F(wi) = vi
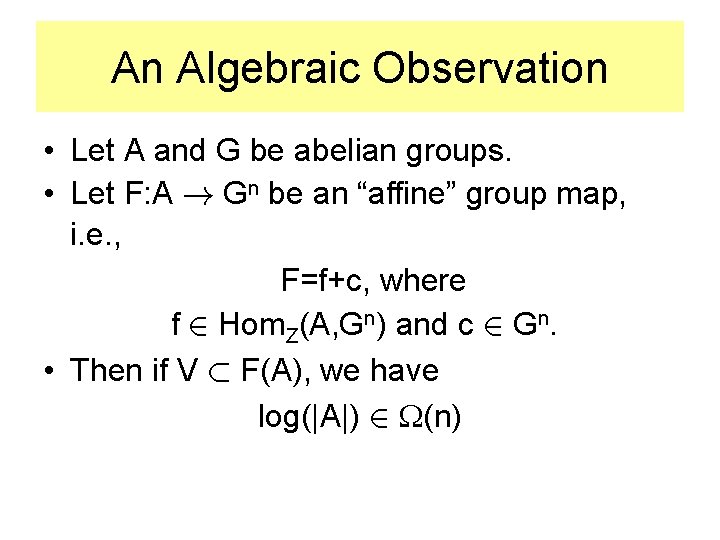
An Algebraic Observation • Let A and G be abelian groups. • Let F: A ! Gn be an “affine” group map, i. e. , F=f+c, where f 2 Hom. Z(A, Gn) and c 2 Gn. • Then if V ½ F(A), we have log(|A|) 2 (n)
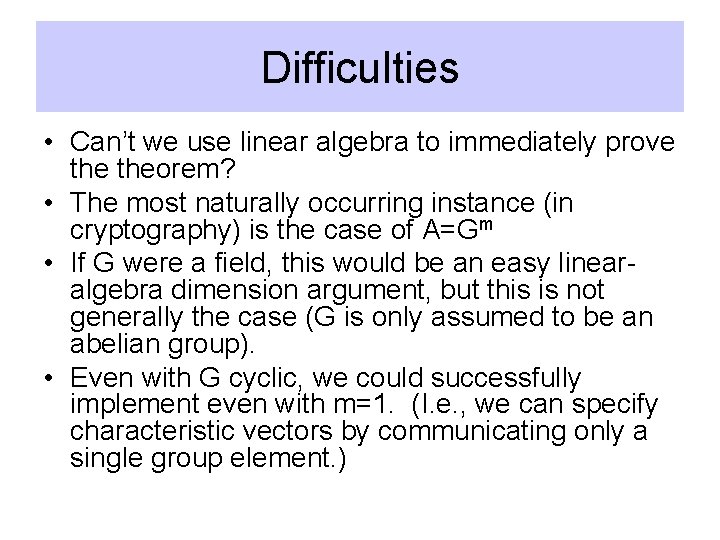
Difficulties • Can’t we use linear algebra to immediately prove theorem? • The most naturally occurring instance (in cryptography) is the case of A=Gm • If G were a field, this would be an easy linearalgebra dimension argument, but this is not generally the case (G is only assumed to be an abelian group). • Even with G cyclic, we could successfully implement even with m=1. (I. e. , we can specify characteristic vectors by communicating only a single group element. )
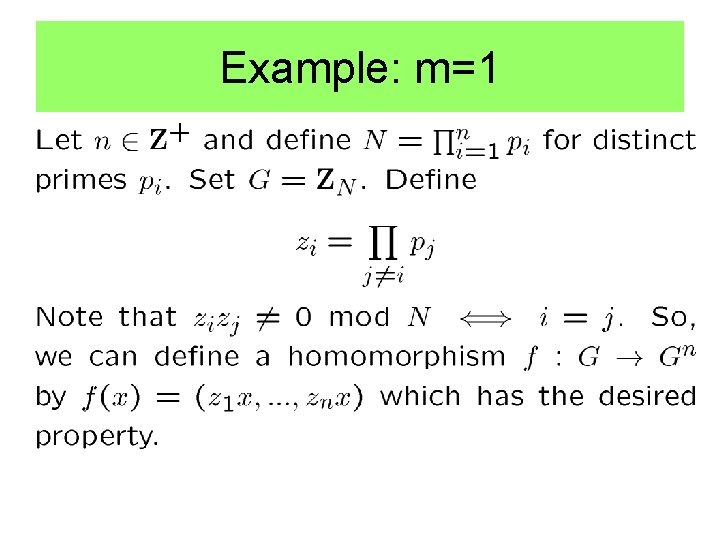
Example: m=1
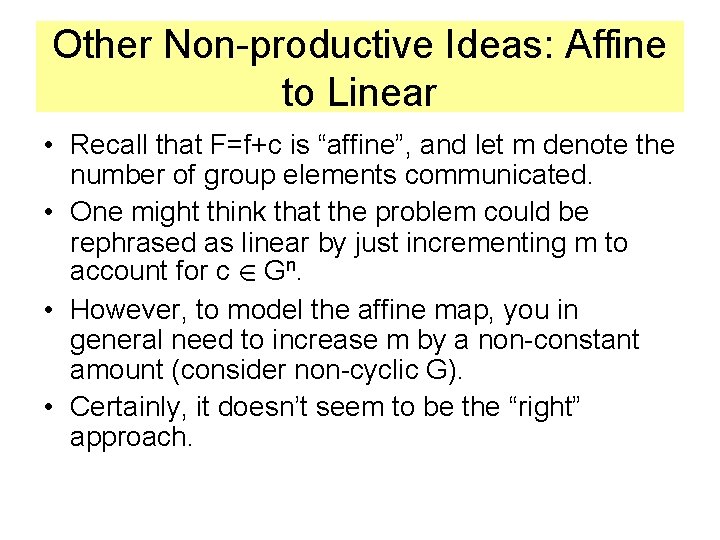
Other Non-productive Ideas: Affine to Linear • Recall that F=f+c is “affine”, and let m denote the number of group elements communicated. • One might think that the problem could be rephrased as linear by just incrementing m to account for c 2 Gn. • However, to model the affine map, you in general need to increase m by a non-constant amount (consider non-cyclic G). • Certainly, it doesn’t seem to be the “right” approach.
The “Right” Approach: • Stay abstract. – Dimension is irrelevant – Will give a stronger result. – Takes care of typical cases nicely, but will actually be quite a bit more general (rules out End(G), etc…)
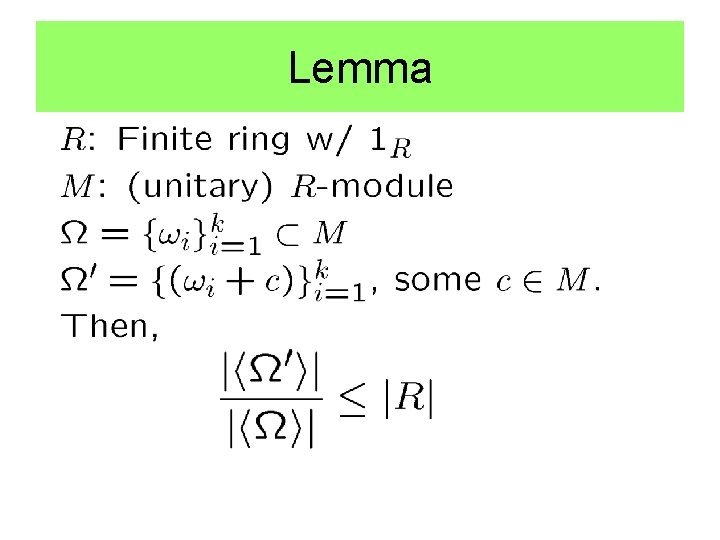
Lemma
Proof of Lemma
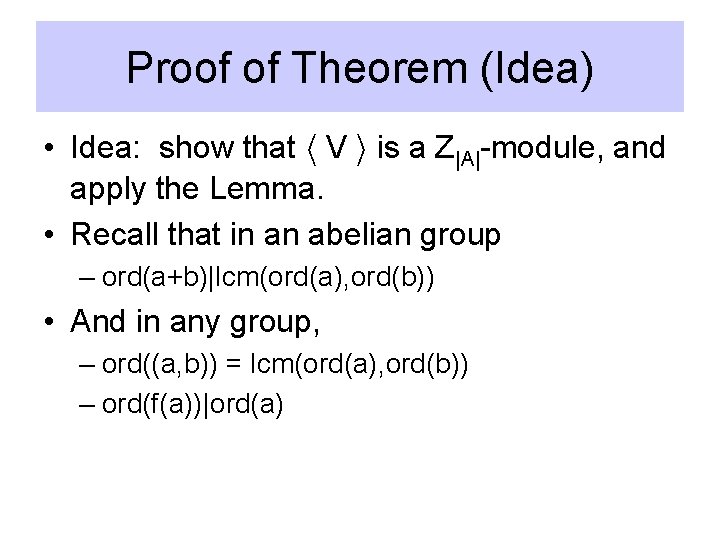
Proof of Theorem (Idea) • Idea: show that h V i is a Z|A|-module, and apply the Lemma. • Recall that in an abelian group – ord(a+b)|lcm(ord(a), ord(b)) • And in any group, – ord((a, b)) = lcm(ord(a), ord(b)) – ord(f(a))|ord(a)
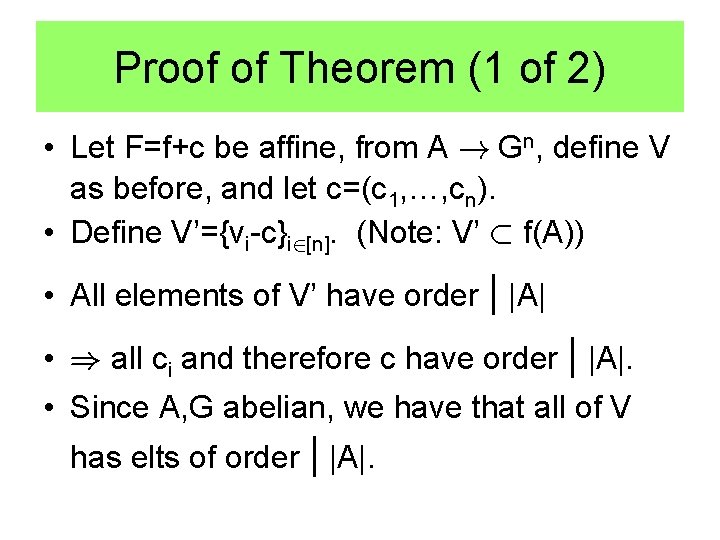
Proof of Theorem (1 of 2) • Let F=f+c be affine, from A ! Gn, define V as before, and let c=(c 1, …, cn). • Define V’={vi-c}i 2[n]. (Note: V’ ½ f(A)) • All elements of V’ have order | |A| • ) all ci and therefore c have order | |A|. • Since A, G abelian, we have that all of V has elts of order | |A|.
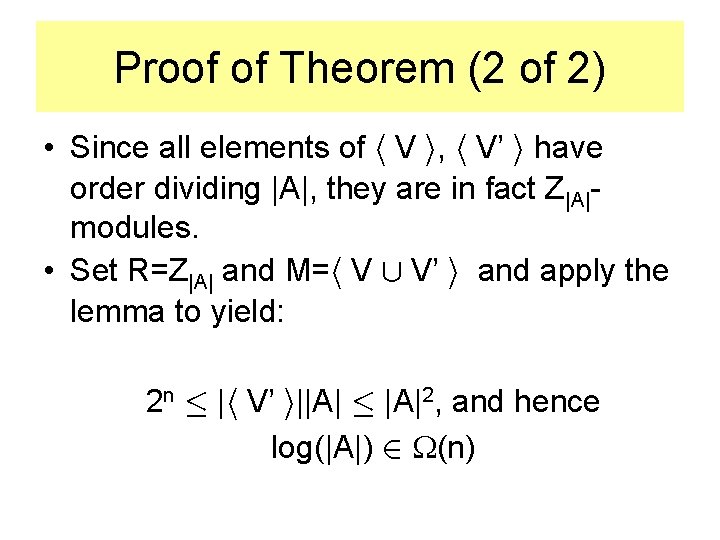
Proof of Theorem (2 of 2) • Since all elements of h V i, h V’ i have order dividing |A|, they are in fact Z|A|modules. • Set R=Z|A| and M=h V [ V’ i and apply the lemma to yield: 2 n · |h V’ i||A| · |A|2, and hence log(|A|) 2 (n)
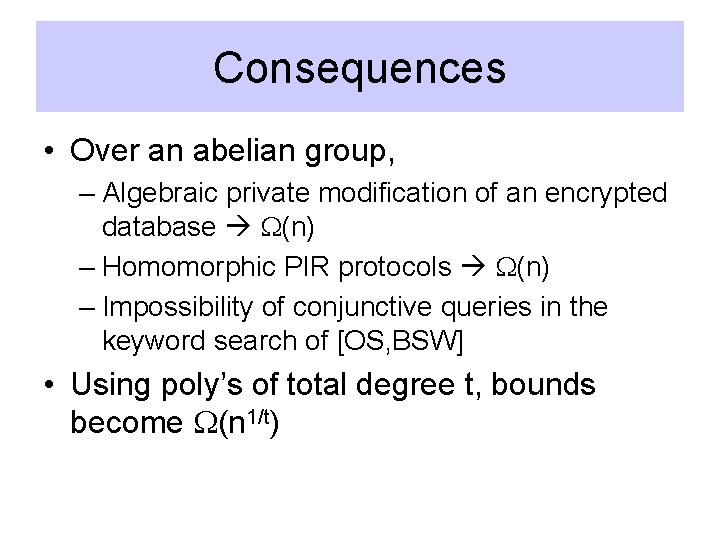
Consequences • Over an abelian group, – Algebraic private modification of an encrypted database (n) – Homomorphic PIR protocols (n) – Impossibility of conjunctive queries in the keyword search of [OS, BSW] • Using poly’s of total degree t, bounds become (n 1/t)
![Algebraic Private Database Modification [BKOS] U Mi=(g 1, …, gm) g 1, g 2, Algebraic Private Database Modification [BKOS] U Mi=(g 1, …, gm) g 1, g 2,](http://slidetodoc.com/presentation_image/45aa94e94126e3fcf18b0fa60aa75294/image-27.jpg)
Algebraic Private Database Modification [BKOS] U Mi=(g 1, …, gm) g 1, g 2, …, gm DB X= X 1 X 2 X 3 … … … . . … … … … Xn X’ = F(x 1, …, xn, g 1, …gm , h 1, …hr) All gj, xi, hk 2 A, and F is some “algebraic” function
Algebraic Database Modification Implies Characteristic Vectors • Let X be a database consisting of id. G in all locations. • Apply F(X, Mi, H) X’ • X’ = vi will be a characteristic vector.
![Homomorphic PIR Protocols [BGN, KO] U g 1, g 2, …, gm Qi=(g 1, Homomorphic PIR Protocols [BGN, KO] U g 1, g 2, …, gm Qi=(g 1,](http://slidetodoc.com/presentation_image/45aa94e94126e3fcf18b0fa60aa75294/image-29.jpg)
Homomorphic PIR Protocols [BGN, KO] U g 1, g 2, …, gm Qi=(g 1, …, gm) (xj 1, …, xil)=FX(g 1, …gm , h 1, …hr) DB X= X 1 X 2 X 3 … … … . . … … … … Xn FX(g 1, …gm , h 1, …hr) All gj, hk 2 A, and FX is some “algebraic” function determined by the database X 2 An
Homomorphic PIR Implies Characteristic Vectors • For a moment, suppose the protocol returns an encryption of a single element. • Let V={vi}i=1 n be a complete set of characteristic vectors over Gn. • Define databases Xi = vi for i 2 [n]. • If Qi queries position i, then (FX 1(Qi, H), …, FXn(Qi, H)) will be non-identity exactly in position i.
Non-singleton Query Returns • It may be the case that a PIR query returns many database values, as long as the right value is at a predictable location in the result (e. g. [KO]). • More generally, we can prove the following algebraic claim:
Claim • Let V={vi}i=1 n be a complete collection of characteristic type vectors, except… vi can be non-identity in up to w(n) locations for any positive function w. • Then if V ½ F(A), we have that: log(|A|) 2 (n/w(n))
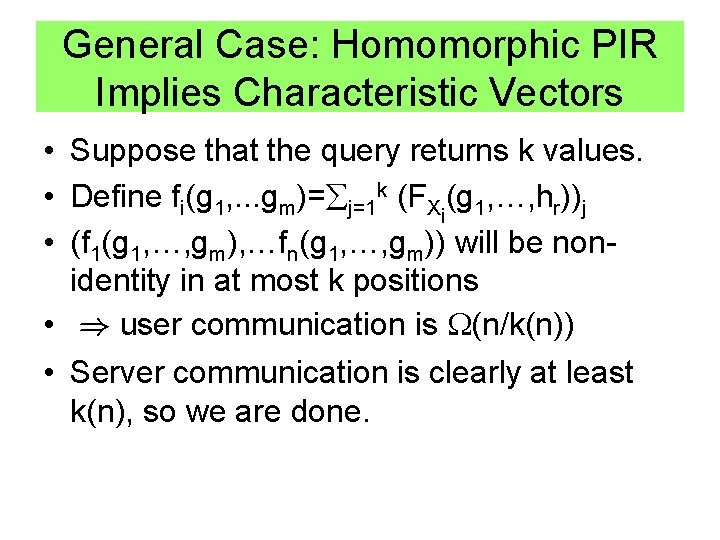
General Case: Homomorphic PIR Implies Characteristic Vectors • Suppose that the query returns k values. • Define fi(g 1, . . . gm)= j=1 k (FXi(g 1, …, hr))j • (f 1(g 1, …, gm), …fn(g 1, …, gm)) will be nonidentity in at most k positions • ) user communication is (n/k(n)) • Server communication is clearly at least k(n), so we are done.
Other Types of Cryptosystems • Recently there has been a lot of attention on bilinear maps in cryptography. • The work of [BGN] demonstrates a cryptosystem that allows polynomials of total degree 2 to be evaluated on ciphertext.
Polynomials of Bounded Total Degree • We can prove an extension of our original algebraic result, which will give similar bounds on the utility of total degree t polynomials. (even for t>2)
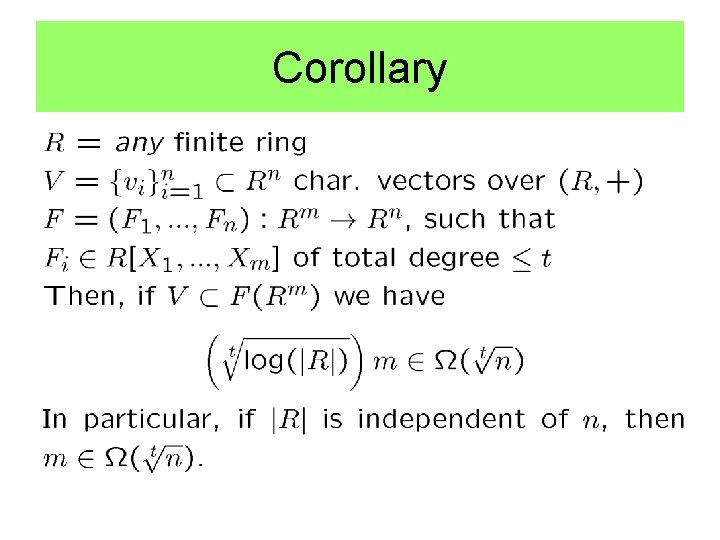
Corollary
Proof Idea • The number of monomials in an m-variable polynomial of total degree t is O(mt). • Simulate such a polynomial with a total degree 1 polynomial in O(mt) variables. • Apply initial theorem to the abelian group (R, +).
More General Results • If given the ability of computation of polynomials of total degree t, we obtain similar bounds, only n n 1/t • In particular, this corollary gives (n 1/2) bounds when applied to algebraic protocols based on the cryptosystem of [BGN] (this matches the upper bound for database modification seen in [BKOS]).
Generality of Results • The algebraic assumptions may seem quite rigid, but are often appropriate in crypto-computing settings. • From an algebraic point of view however, they are very general: – Incorporates all algebraic formulas, but also many other types of maps (formulas with End(G), changing representations, etc…). – Covers most all algebraic structures preserved by known cryptosystems
Perspective • Help researchers determine the feasibility of various new protocols. • Especially useful when such protocols are needed as a subroutine in a larger crypto-computing function. – Protocol may need output with algebraic value to continue the computation • Simple Non-abelian group-homomorphic encryption: – Seems pretty hard. – Equivalent to fully-homomorphic encryption (/ring).
Thank You
- Slides: 41