Agenda Examining Use Behaviors Phishing Quiz Threats to
Agenda • • • Examining Use Behaviors Phishing Quiz Threats to Information Security Practicing Avoidance Behavior Resources
Examining Use Behaviors
Scenario 1 • Spends an hour instant messaging every night • Clicks “remind me again later” when anti-virus update alerts appear on the screen • Often downloads games that are available as freeware
Scenario 2 • Leaves browser open to monitor sales on Ebay • Downloads *. pdf files while conducting research online • Has latest versions of security software installed
Scenario 3 • Uses a neighbor’s wireless network for Internet access at home • Always deletes old e-mail messages to maintain privacy • Sometimes provides sensitive information to register with sites
What’s New Out There?
Worms and Instant Messaging A worm is a self-replicating program that takes advantage of e-mail or IM contact lists to spread from computer to computer. Intended Effects: • Clog network traffic • May damage files on your computer • May cause e-mail servers to crash
What is a Bot? A ‘bot’ is a compromised computer that is controlled remotely and is used to attack other sites or to conduct other malicious/illegal activities. How it works: • Computer is usually compromised by a ‘Trojan’ first • Hacker sends commands to your computer through an open port, turning it into a ‘bot’ • Uses the ‘bot’ to send large amounts of useless information to target and crash another site
What’s on Your Computer • • Weather bug Stock updates Free instant messaging (“IM”) software Downloaded files from untrusted sources Music Games News ticker
Good Habits • Leave fields blank when possible • Give fake information • Don’t give sensitive information or information you want to keep private – date of birth – cell phone number • Open a free e-mail account • Use a guest log-in if available • Avoid freeware from untrustworthy sources
What are they after? Any information they can get!
What is Freeware? Software that is ‘free’ to download and install. • • • Ring tones Screensavers Imoticons Wallpapers Games Informational programs: weather bug, stock ticker
Freeware Reality • Not really free • May contain adware resulting in annoying and potentially dangerous pop-ups • Often contains spyware, trojans, cookies, or other malicious software • May not work if spyware or trojans are removed • Vendor may sell your product registration information
Good Habits • • Say ‘no’ to attractive packaging Say ‘no, thanks’ to freeware from friends or family Start reading ‘Terms and Conditions’ before agreeing Stop downloading freeware from unknown or untrustworthy sites • Stop giving sensitive information in product registrations
What is Malware? Malicious, self-replicating programs • Trojans – Gather information or perform commands • Worms – Spread through e-mail and IM links or attachments • Viruses – Infect executable files (*. exe) and have the ability to modify other programs • Sniffers – Intercepts routed data, searching for information (passwords, bank account numbers) transmitted in clear text
Good Habits • • Avoiding unsecure wireless networks Avoiding links sent via e-mail or IM Avoiding ads in the margin of legitimate sites Avoiding sharing your computer with unsupervised children/teens • Keeping anti-virus software up-to-date and running • Always scanning attachments before opening
Who’s Reading Your E-mail?
Who’s Reading Your E-mail? • E-mail and IM transmissions are not secure • Key-logging software may record what you type • Your address is available for spamming, phishing, spoofing, and other scams
Good Habits • Keep in mind that it could be read • Break-up sensitive communications • Delete old e-mails and scrub your computer if you’re discarding it • ‘Log-out’ when using a shared computer to check mail • Lock your computer when you’re away • Share your computer wisely
Phishing Quiz
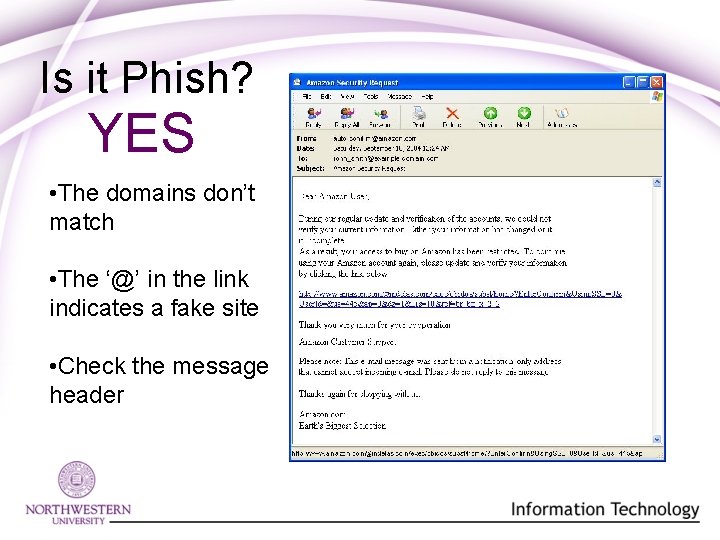
Is it Phish? YES • The domains don’t match • The ‘@’ in the link indicates a fake site • Check the message header
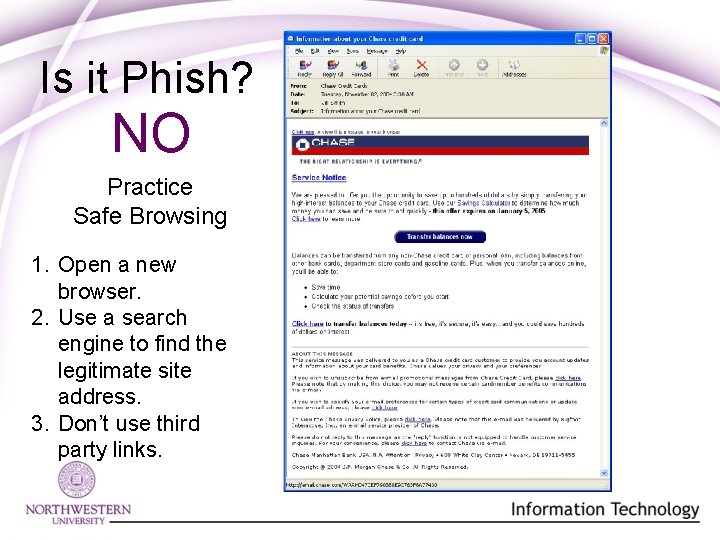
Is it Phish? NO Practice Safe Browsing 1. Open a new browser. 2. Use a search engine to find the legitimate site address. 3. Don’t use third party links.
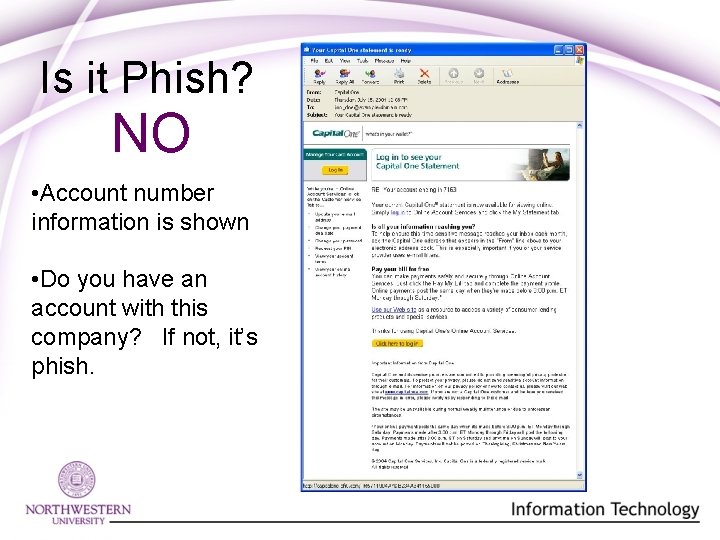
Is it Phish? NO • Account number information is shown • Do you have an account with this company? If not, it’s phish.
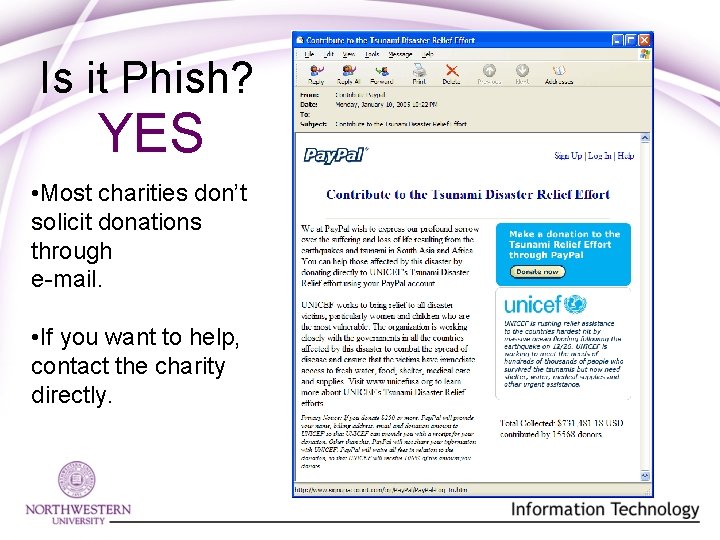
Is it Phish? YES • Most charities don’t solicit donations through e-mail. • If you want to help, contact the charity directly.
Phishing Gets Smart • Less bad grammar or misspellings • Include legitimate logos • Include authentic looking privacy or copyright information • Mirror the appearance of legitimate sites to gain your confidence To report phishing or other fraud: http: //www. ag. state. il. us/consumers/
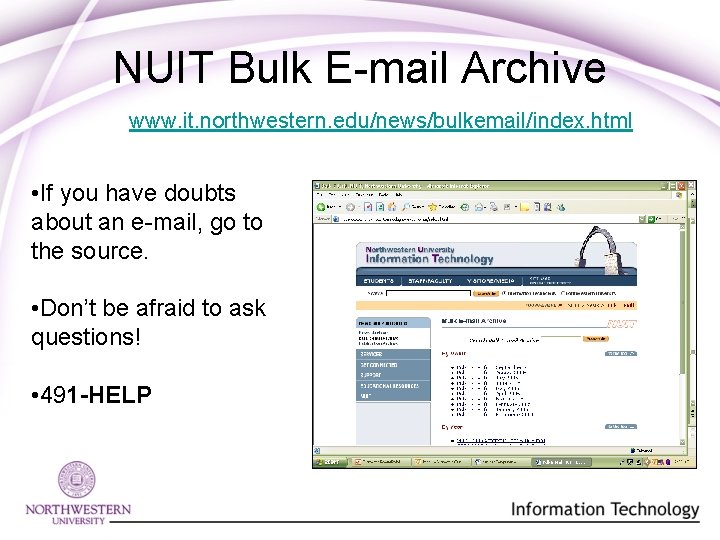
NUIT Bulk E-mail Archive www. it. northwestern. edu/news/bulkemail/index. html • If you have doubts about an e-mail, go to the source. • Don’t be afraid to ask questions! • 491 -HELP
Threats to Information Security
Threats to Information Security • According to Microsoft, an unprotected Windows PC will attract an unwelcome advance by a security threat within 23 minutes of connecting to the Internet. • A 2000% increase in the number of threats detected for IM and peer-to-peer networks was reported between 2004 and 2005. • Threats increasingly target mobile devices and are increasingly sophisticated.
Practicing Avoidance Behavior
Keep Your Guard Up • • Scan incoming attachments no matter who sends them Visit web sites directly—don’t use third party links Look for “https” in web addresses to know a page is secure Surf trusted sites Use different passwords for different classes of information Don’t log on to unsecure wireless networks Don’t disable your firewall for convenience Close your browser
Take charge of your computer and your security! • Keep anti-virus software current and install definitions as they become available. • Scan your computer frequently. • Automate it and forget it!
Be a Skeptic Question: • New sites • New services • Unusual ads and pop-ups • Things that seem to good to be true • E-mail with unusual or foreign characters in the heading • Unexpected e-mail or IM Call 1 -HELP if you have a question!
Warning Signs • Unusual requests to transfer information through firewall • Computer slowness • Changes to your browser homepage • Changes to your computer desktop • Excessive pop-up ads • Any behavior that makes you suspicious or uncomfortable
Fix It! Symantec/Norton Anti-Virus www. it. northwestern. edu/software/staff/free/antivirus/i ndex. html Spybot www. it. northwestern. edu/security/spyware/winspybot-install. html
NUIT Resources Security Awareness Tip of the Month www. it. northwestern. edu/security/tip-of-themonth/index. html “Get Control” web site www. it. northwestern. edu/5 steps E-mail Defense System www. it. northwestern. edu/security/eds/index. html Computer and Network Security www. it. northwestern. edu/security/
Next Tech Talk Laying Down the Law Illegal file sharing, copyright laws, and the Internet Understanding copyrights, software licenses, and more! Friday, November 11, 2005 Same locations, Noon – 1 p. m. Please register online: www. it. northwestern. edu
- Slides: 37