Advantages Disadvantages Advantages Disadvantages Scalability Easy and cheap
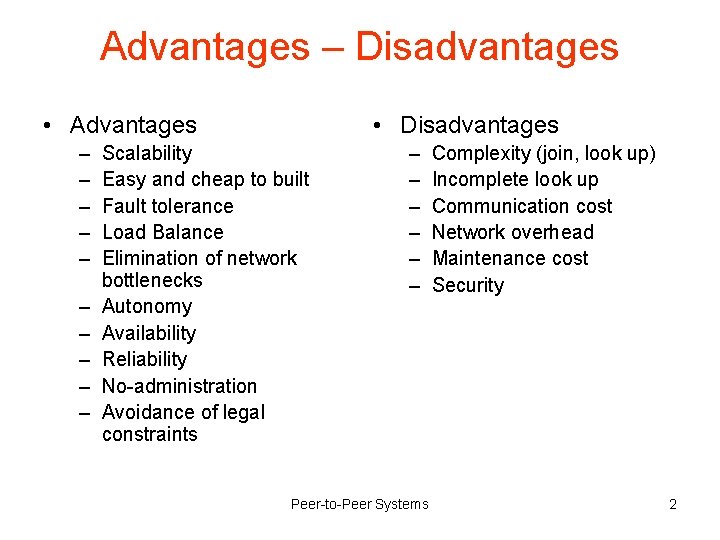
Advantages – Disadvantages • Advantages – – – – – • Disadvantages Scalability Easy and cheap to built Fault tolerance Load Balance Elimination of network bottlenecks Autonomy Availability Reliability No-administration Avoidance of legal constraints – – – Peer-to-Peer Systems Complexity (join, look up) Incomplete look up Communication cost Network overhead Maintenance cost Security 2
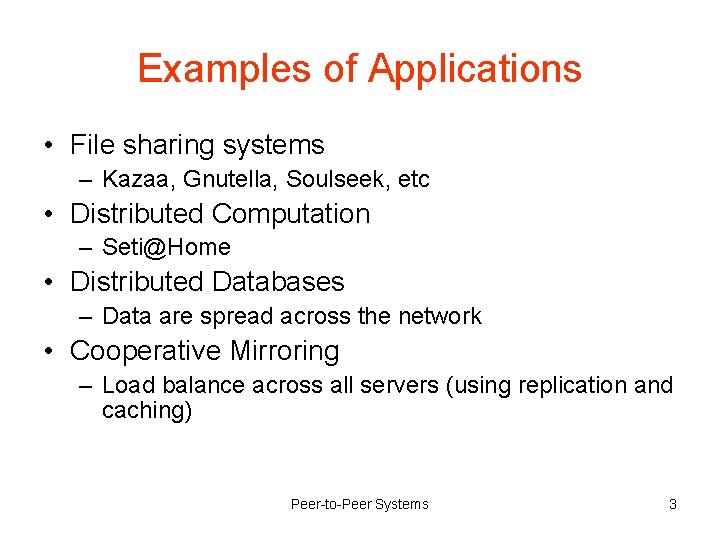
Examples of Applications • File sharing systems – Kazaa, Gnutella, Soulseek, etc • Distributed Computation – Seti@Home • Distributed Databases – Data are spread across the network • Cooperative Mirroring – Load balance across all servers (using replication and caching) Peer-to-Peer Systems 3
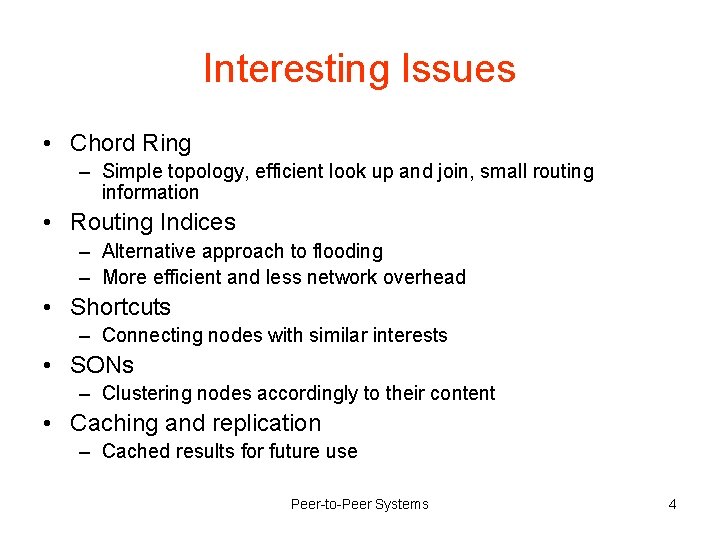
Interesting Issues • Chord Ring – Simple topology, efficient look up and join, small routing information • Routing Indices – Alternative approach to flooding – More efficient and less network overhead • Shortcuts – Connecting nodes with similar interests • SONs – Clustering nodes accordingly to their content • Caching and replication – Cached results for future use Peer-to-Peer Systems 4
Best Paper • Chord: A Scalable Peer-to-peer Lookup Service for Internet Applications – Clever concept – Simple structure (just a ring) – Complete paper Peer-to-Peer Systems 5
Main Issues for Future Work • Clustering techniques without a-priori knowledge of existing clusters • Cycle prediction and elimination – Unstructured systems (too many messages) – Routing indices (inaccurate indices) • Security – Anonymity – Authenticity Peer-to-Peer Systems 6
END Peer-to-Peer Systems 7
- Slides: 7