Adrian Crenshaw http Irongeek com About Adrian I
Adrian Crenshaw http: //Irongeek. com
About Adrian I run Irongeek. com I have an interest in Info. Sec education I don’t know everything - I’m just a geek with time on my hands Sr. Information Security Consultant at Trusted. Sec Co-Founder of Derbycon http: //www. derbycon. com http: //Irongeek. com Twitter: @Irongeek_ADC
What and Why of Port Scanning Since ports are fairly standard, if port 80 tcp is listening on a host, more than likely it’s running web services By sending packets to these port numbers, you can see what services are running on the host Knowing what services are running lets you know something about the potential attack surface What about finger printing? http: //Irongeek. com
Nmap One of the most popular port scanners Started by Gordon Lyon (Fyodor) back in 1997, as an article for Phrack Magazine 51 Started as a fairly simple port scanner, and has suffered some pretty serious feature creep since. Multiplatform (Linux, Windows, BSD, OS X) Open Source and available from http: //nmap. org http: //Irongeek. com
TCP/UDP/IP Basics To use an analogy, if IPs are an apartment complex’s address, ports are the apartment number Both UDP and TCP use incoming and outgoing ports Most IP based services listen on standard ports (HTTP 80/TCP, SMTP 25/TCP, SMB 139/445/TCP, DNS port 53/TCP and UDP) http: //Irongeek. com
http: //Irongeek. com
http: //Irongeek. com
MAC Addresses MAC (Media Access Control) is the address on the NIC (Network Interface Card) Term is user in Ethernet, but the same concept apply elsewhere Burned in address should be unique, and if they ask on the exam it is, but reality is sometimes different http: //Irongeek. com
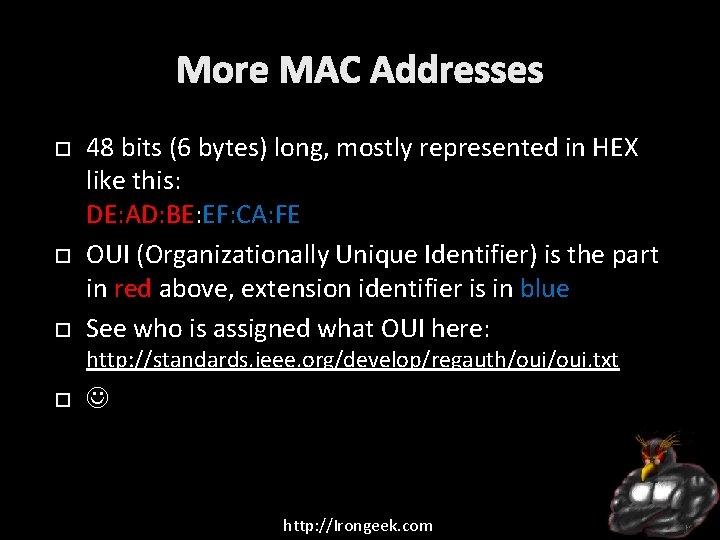
More MAC Addresses 48 bits (6 bytes) long, mostly represented in HEX like this: DE: AD: BE: EF: CA: FE OUI (Organizationally Unique Identifier) is the part in red above, extension identifier is in blue See who is assigned what OUI here: http: //standards. ieee. org/develop/regauth/oui. txt http: //Irongeek. com
EUI-64 MAC addresses 64 byte MAC addesses OUI is still 24 Not sure what uses these http: //Irongeek. com
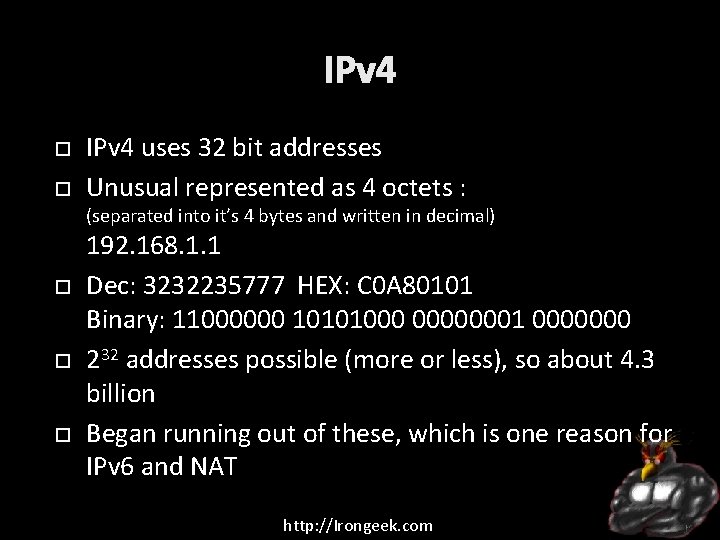
IPv 4 uses 32 bit addresses Unusual represented as 4 octets : (separated into it’s 4 bytes and written in decimal) 192. 168. 1. 1 Dec: 3232235777 HEX: C 0 A 80101 Binary: 11000000 10101000 00000001 0000000 232 addresses possible (more or less), so about 4. 3 billion Began running out of these, which is one reason for IPv 6 and NAT http: //Irongeek. com
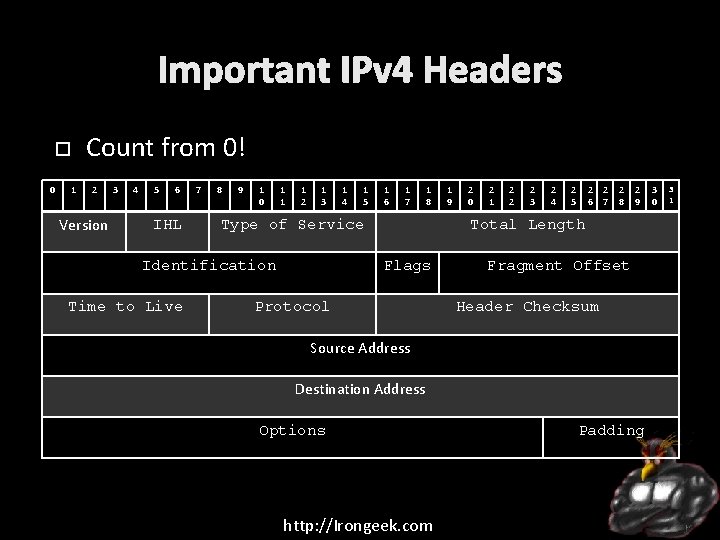
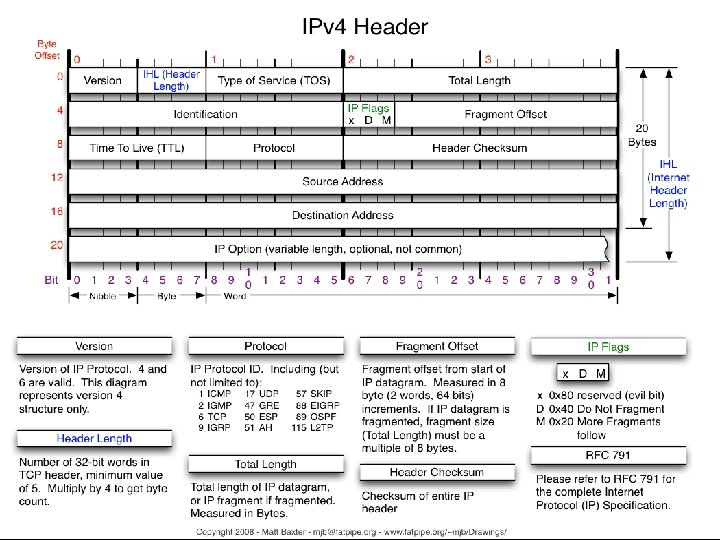
Important IPv 4 Headers Count from 0! 0 1 2 Version 3 4 5 6 IHL 7 8 9 1 0 1 1 1 2 1 3 1 5 1 6 1 7 1 8 Type of Service Identification Time to Live 1 4 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 2 6 7 2 8 2 9 Total Length Flags Protocol Fragment Offset Header Checksum Source Address Destination Address Options http: //Irongeek. com Padding 3 0 3 1
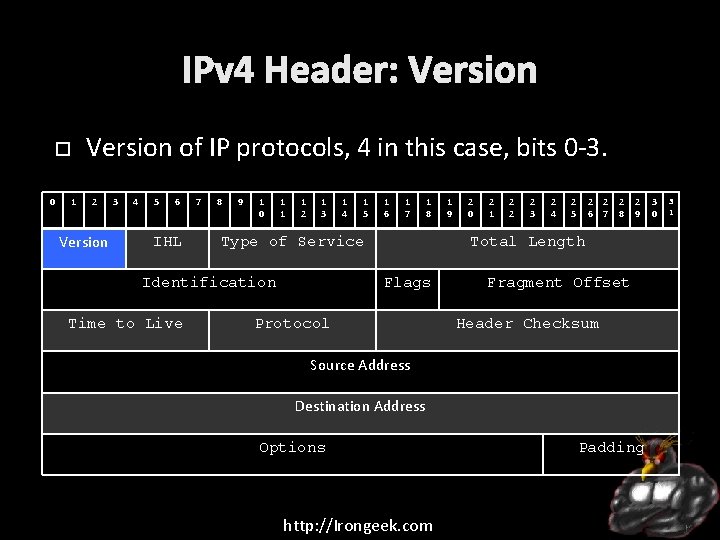
IPv 4 Header: Version of IP protocols, 4 in this case, bits 0 -3. 0 1 2 Version 3 4 5 6 IHL 7 8 9 1 0 1 1 1 2 1 3 1 5 1 6 1 7 1 8 Type of Service Identification Time to Live 1 4 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 2 6 7 2 8 2 9 Total Length Flags Protocol Fragment Offset Header Checksum Source Address Destination Address Options http: //Irongeek. com Padding 3 0 3 1
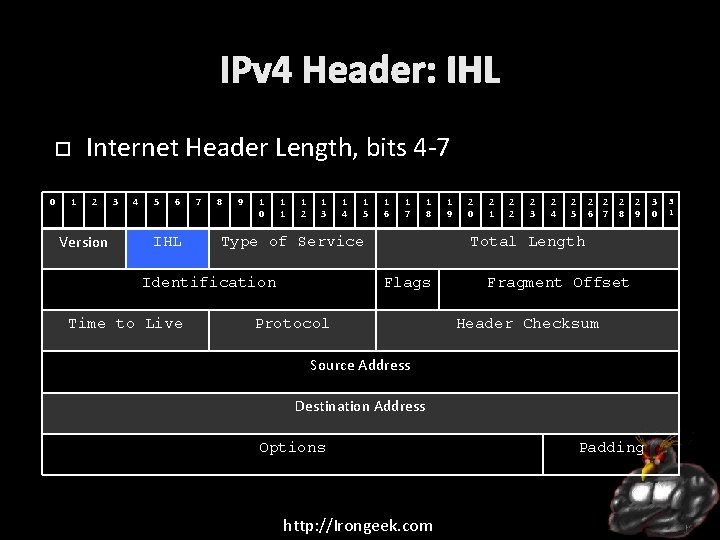
IPv 4 Header: IHL Internet Header Length, bits 4 -7 0 1 2 Version 3 4 5 6 IHL 7 8 9 1 0 1 1 1 2 1 3 1 5 1 6 1 7 1 8 Type of Service Identification Time to Live 1 4 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 2 6 7 2 8 2 9 Total Length Flags Protocol Fragment Offset Header Checksum Source Address Destination Address Options http: //Irongeek. com Padding 3 0 3 1
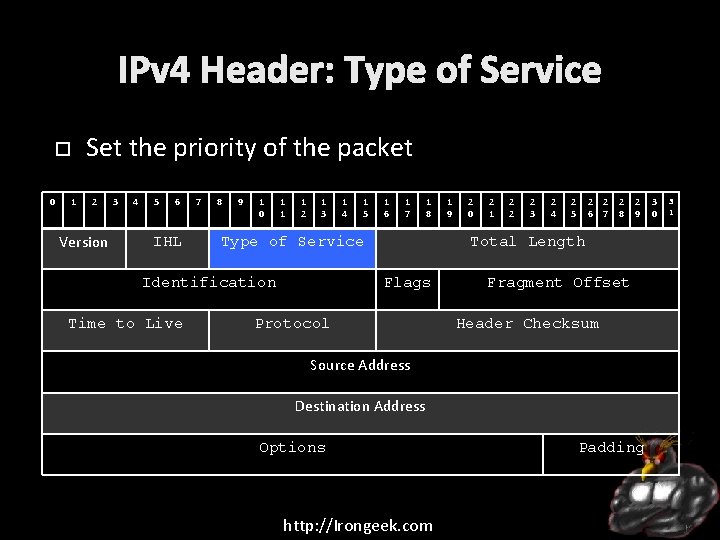
IPv 4 Header: Type of Service Set the priority of the packet 0 1 2 Version 3 4 5 6 IHL 7 8 9 1 0 1 1 1 2 1 3 1 5 1 6 1 7 1 8 Type of Service Identification Time to Live 1 4 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 2 6 7 2 8 2 9 Total Length Flags Protocol Fragment Offset Header Checksum Source Address Destination Address Options http: //Irongeek. com Padding 3 0 3 1
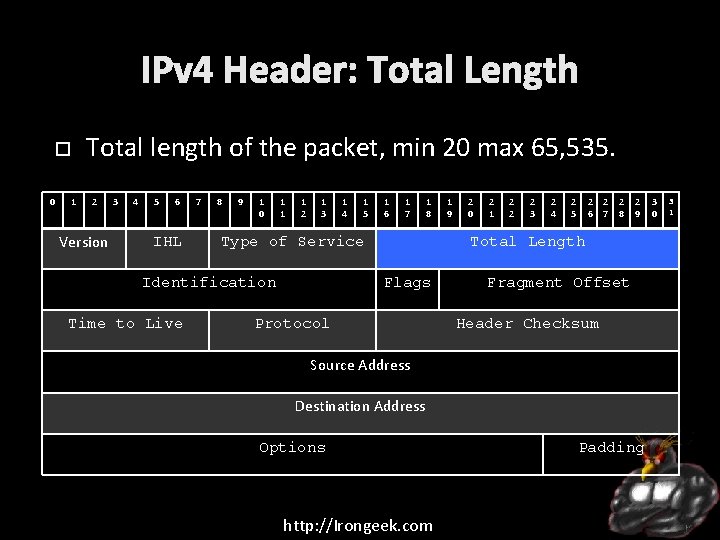
IPv 4 Header: Total Length Total length of the packet, min 20 max 65, 535. 0 1 2 Version 3 4 5 6 IHL 7 8 9 1 0 1 1 1 2 1 3 1 5 1 6 1 7 1 8 Type of Service Identification Time to Live 1 4 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 2 6 7 2 8 2 9 Total Length Flags Protocol Fragment Offset Header Checksum Source Address Destination Address Options http: //Irongeek. com Padding 3 0 3 1
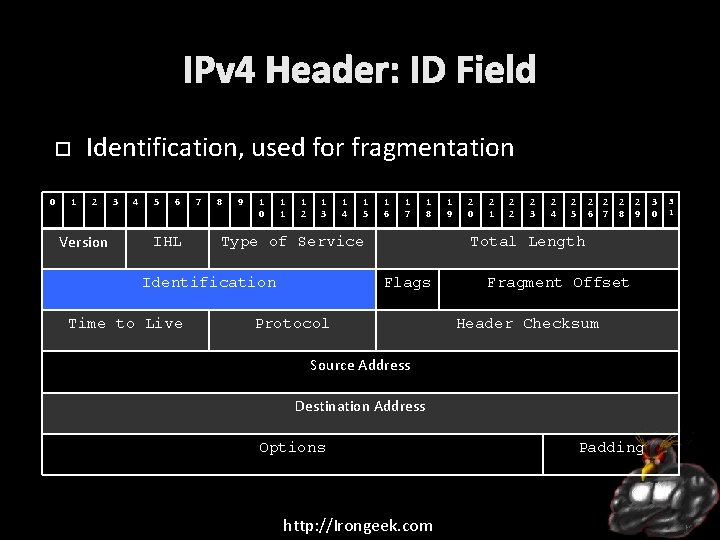
IPv 4 Header: ID Field Identification, used for fragmentation 0 1 2 Version 3 4 5 6 IHL 7 8 9 1 0 1 1 1 2 1 3 1 5 1 6 1 7 1 8 Type of Service Identification Time to Live 1 4 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 2 6 7 2 8 2 9 Total Length Flags Protocol Fragment Offset Header Checksum Source Address Destination Address Options http: //Irongeek. com Padding 3 0 3 1
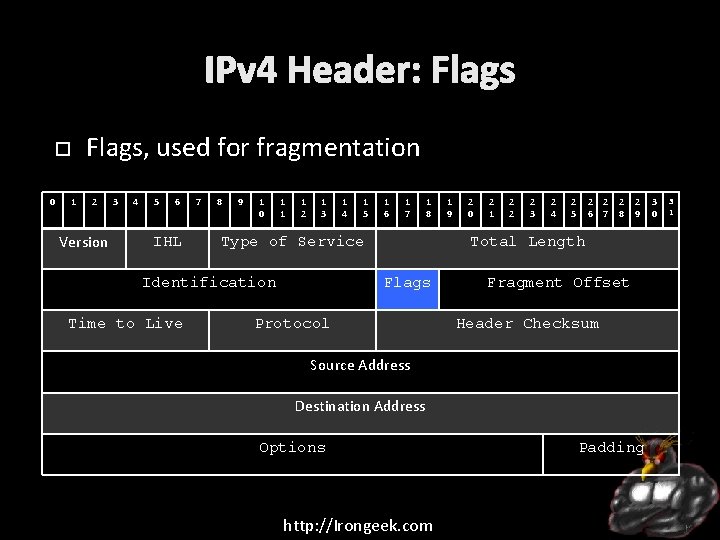
IPv 4 Header: Flags, used for fragmentation 0 1 2 Version 3 4 5 6 IHL 7 8 9 1 0 1 1 1 2 1 3 1 5 1 6 1 7 1 8 Type of Service Identification Time to Live 1 4 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 2 6 7 2 8 2 9 Total Length Flags Protocol Fragment Offset Header Checksum Source Address Destination Address Options http: //Irongeek. com Padding 3 0 3 1
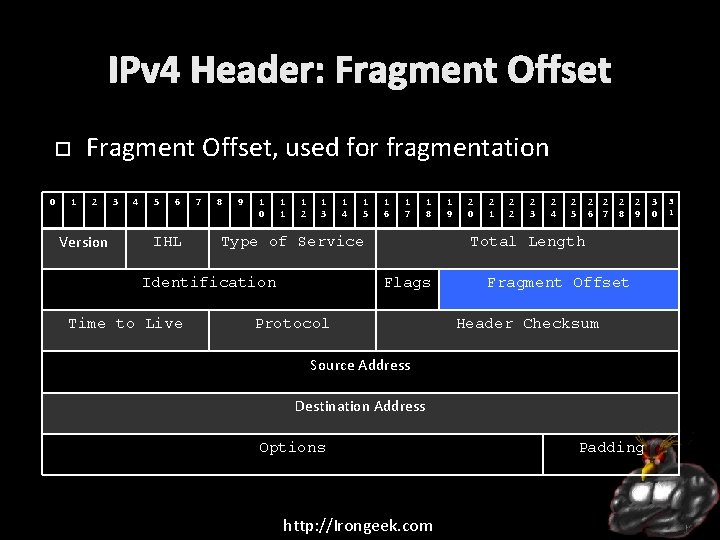
IPv 4 Header: Fragment Offset, used for fragmentation 0 1 2 Version 3 4 5 6 IHL 7 8 9 1 0 1 1 1 2 1 3 1 5 1 6 1 7 1 8 Type of Service Identification Time to Live 1 4 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 2 6 7 2 8 2 9 Total Length Flags Protocol Fragment Offset Header Checksum Source Address Destination Address Options http: //Irongeek. com Padding 3 0 3 1
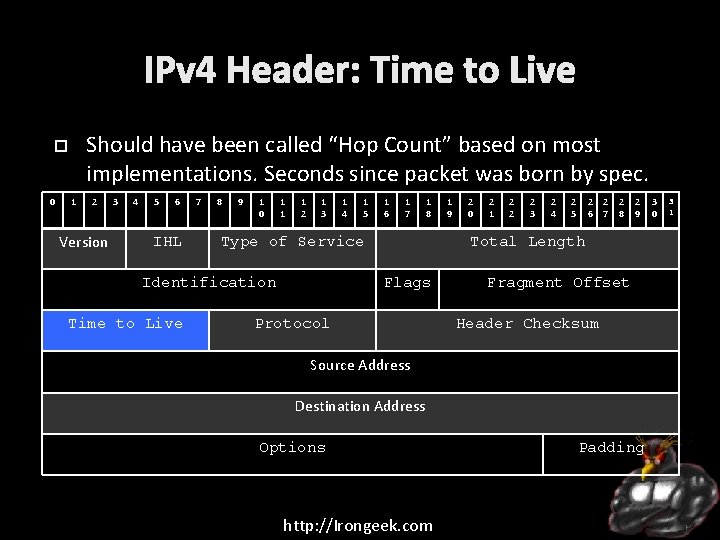
IPv 4 Header: Time to Live Should have been called “Hop Count” based on most implementations. Seconds since packet was born by spec. 0 1 2 Version 3 4 5 6 IHL 7 8 9 1 0 1 1 1 2 1 3 1 5 1 6 1 7 1 8 Type of Service Identification Time to Live 1 4 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 2 6 7 2 8 2 9 Total Length Flags Protocol Fragment Offset Header Checksum Source Address Destination Address Options http: //Irongeek. com Padding 3 0 3 1
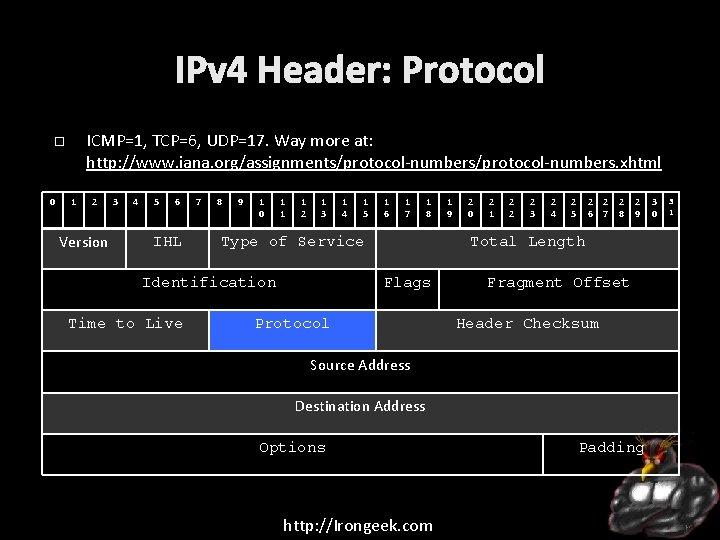
IPv 4 Header: Protocol ICMP=1, TCP=6, UDP=17. Way more at: http: //www. iana. org/assignments/protocol-numbers. xhtml 0 1 2 Version 3 4 5 6 IHL 7 8 9 1 0 1 1 1 2 1 3 1 5 1 6 1 7 1 8 Type of Service Identification Time to Live 1 4 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 2 6 7 2 8 2 9 Total Length Flags Protocol Fragment Offset Header Checksum Source Address Destination Address Options http: //Irongeek. com Padding 3 0 3 1
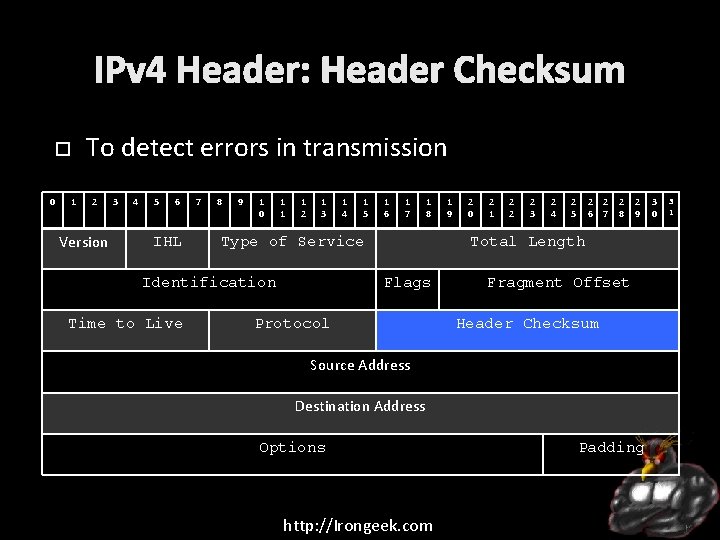
IPv 4 Header: Header Checksum To detect errors in transmission 0 1 2 Version 3 4 5 6 IHL 7 8 9 1 0 1 1 1 2 1 3 1 5 1 6 1 7 1 8 Type of Service Identification Time to Live 1 4 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 2 6 7 2 8 2 9 Total Length Flags Protocol Fragment Offset Header Checksum Source Address Destination Address Options http: //Irongeek. com Padding 3 0 3 1
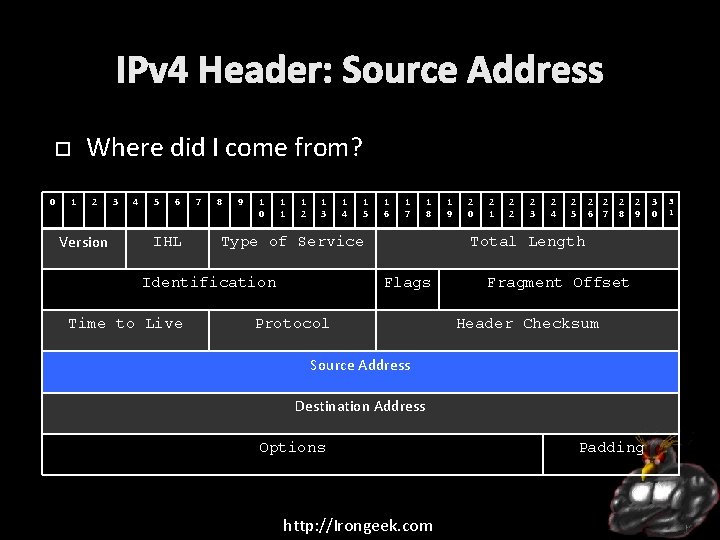
IPv 4 Header: Source Address Where did I come from? 0 1 2 Version 3 4 5 6 IHL 7 8 9 1 0 1 1 1 2 1 3 1 5 1 6 1 7 1 8 Type of Service Identification Time to Live 1 4 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 2 6 7 2 8 2 9 Total Length Flags Protocol Fragment Offset Header Checksum Source Address Destination Address Options http: //Irongeek. com Padding 3 0 3 1
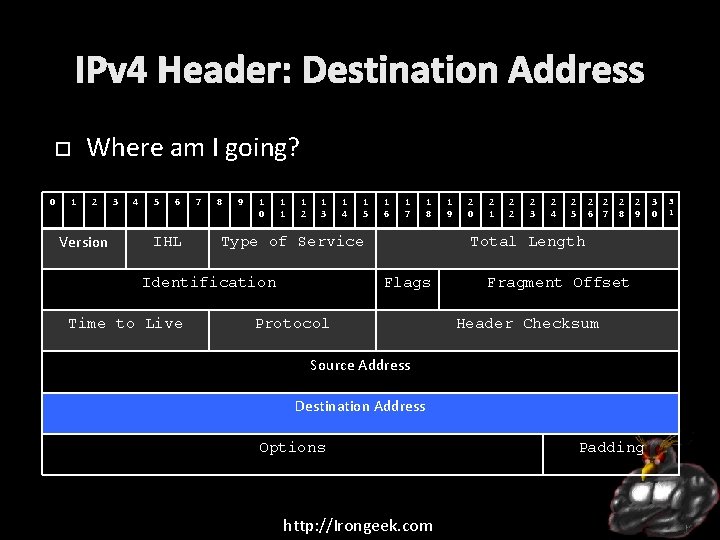
IPv 4 Header: Destination Address Where am I going? 0 1 2 Version 3 4 5 6 IHL 7 8 9 1 0 1 1 1 2 1 3 1 5 1 6 1 7 1 8 Type of Service Identification Time to Live 1 4 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 2 6 7 2 8 2 9 Total Length Flags Protocol Fragment Offset Header Checksum Source Address Destination Address Options http: //Irongeek. com Padding 3 0 3 1
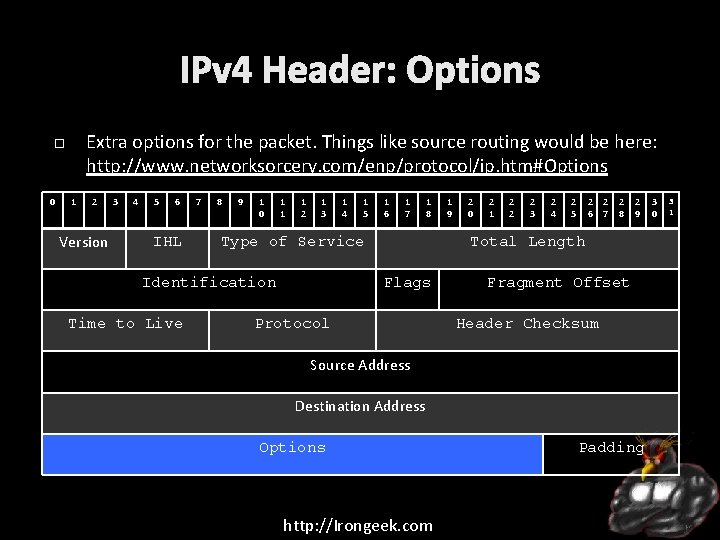
IPv 4 Header: Options Extra options for the packet. Things like source routing would be here: http: //www. networksorcery. com/enp/protocol/ip. htm#Options 0 1 2 Version 3 4 5 6 IHL 7 8 9 1 0 1 1 1 2 1 3 1 5 1 6 1 7 1 8 Type of Service Identification Time to Live 1 4 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 2 6 7 2 8 2 9 Total Length Flags Protocol Fragment Offset Header Checksum Source Address Destination Address Options http: //Irongeek. com Padding 3 0 3 1
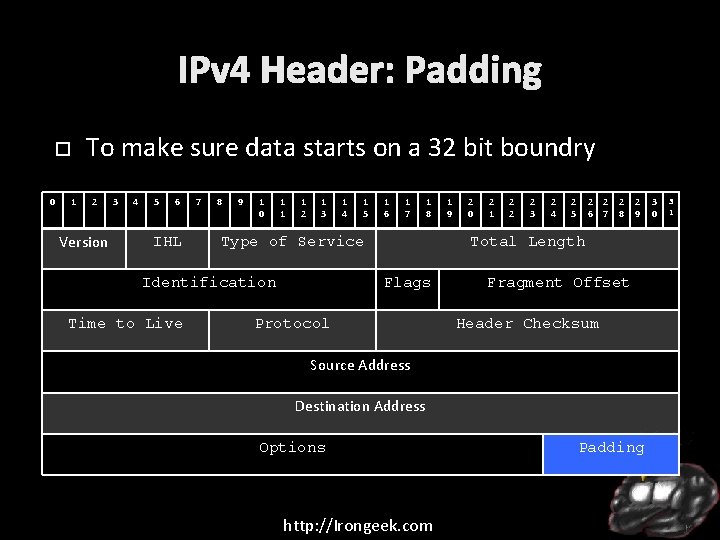
IPv 4 Header: Padding To make sure data starts on a 32 bit boundry 0 1 2 Version 3 4 5 6 IHL 7 8 9 1 0 1 1 1 2 1 3 1 5 1 6 1 7 1 8 Type of Service Identification Time to Live 1 4 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 2 6 7 2 8 2 9 Total Length Flags Protocol Fragment Offset Header Checksum Source Address Destination Address Options http: //Irongeek. com Padding 3 0 3 1
Fragmentation Networks have a Maximum Transmission Unit (MTU) size, often 1500 bytes Sometimes, packets must be broken up to fit, which can be done by a router IPID and Offset mentioned before are used to put packets back together MTU of the path can be discovered by setting the Do Not Fragment flag and keep trying smaller sizes till you do not get an ICMP “Fragmentation needed and DF set” message back http: //Irongeek. com
IPv 6 128 bit addressees, 2128 possible addresses (In technical terms: a shit load) 340 undecillion to use Yanks, 340 sextillion to Brits (which sounds like a fancy orgy) In some ways, IPv 6 has a simpler header http: //Irongeek. com
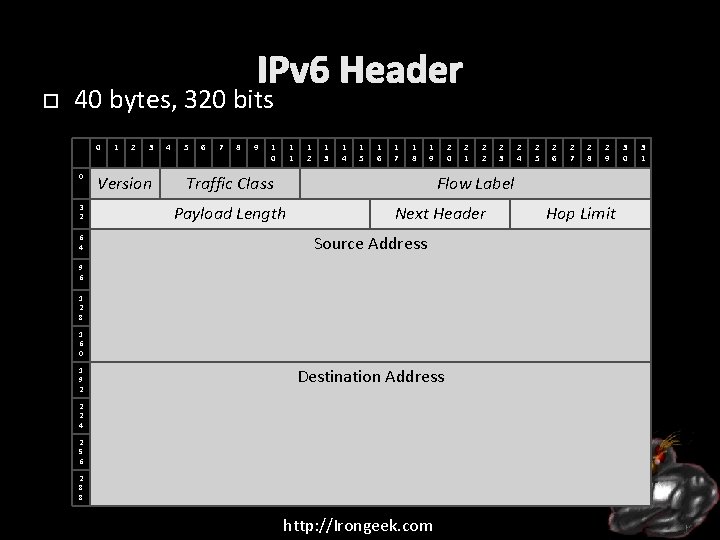
IPv 6 Header 40 bytes, 320 bits 0 0 3 2 6 4 1 2 3 Version 4 5 6 7 8 9 1 0 1 1 1 2 1 3 1 4 1 5 1 6 1 7 1 8 1 9 Traffic Class 2 0 2 2 2 3 2 4 2 5 2 6 2 7 2 8 2 9 Flow Label Payload Length Next Header Source Address 9 6 1 2 8 1 6 0 1 9 2 2 1 Destination Address 2 2 4 2 5 6 2 8 8 http: //Irongeek. com Hop Limit 3 0 3 1
IPv 6 Header Version is set to 6 Traffic Class and Flow Control are used for Qo. S Payload Length is the size of the payload, not including the IP heard itself Next Header, points to the header of the encapsulated protocol Hop Limit, was TTL in old IPv 4, this is a better name Source and Destination Addresses http: //Irongeek. com
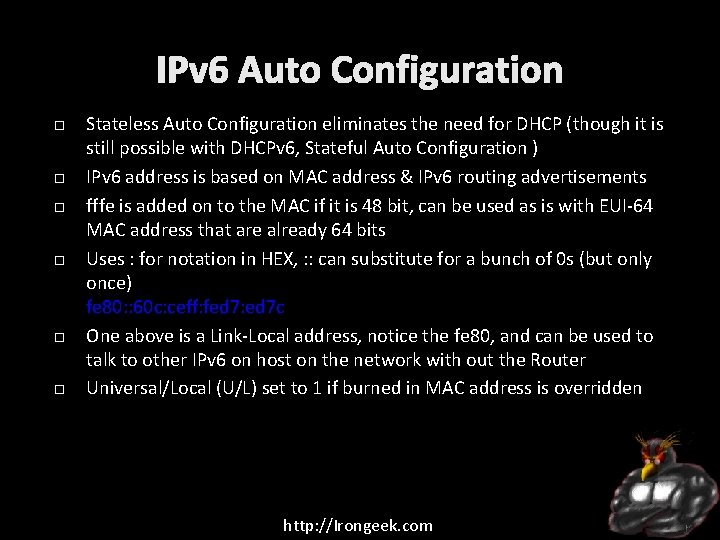
IPv 6 Auto Configuration Stateless Auto Configuration eliminates the need for DHCP (though it is still possible with DHCPv 6, Stateful Auto Configuration ) IPv 6 address is based on MAC address & IPv 6 routing advertisements fffe is added on to the MAC if it is 48 bit, can be used as is with EUI-64 MAC address that are already 64 bits Uses : for notation in HEX, : : can substitute for a bunch of 0 s (but only once) fe 80: : 60 c: ceff: fed 7: ed 7 c One above is a Link-Local address, notice the fe 80, and can be used to talk to other IPv 6 on host on the network with out the Router Universal/Local (U/L) set to 1 if burned in MAC address is overridden http: //Irongeek. com
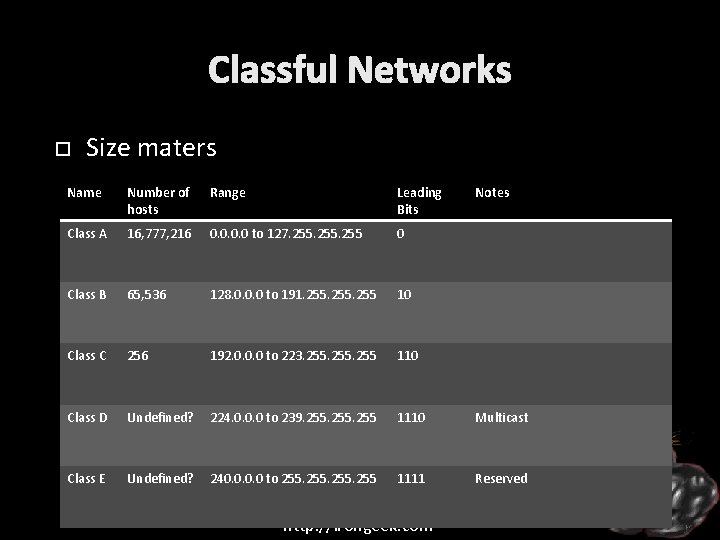
Classful Networks Size maters Name Number of hosts Range Leading Bits Class A 16, 777, 216 0. 0 to 127. 255 0 Class B 65, 536 128. 0. 0. 0 to 191. 255 10 Class C 256 192. 0. 0. 0 to 223. 255 110 Class D Undefined? 224. 0. 0. 0 to 239. 255 1110 Multicast Class E Undefined? 240. 0 to 255 1111 Reserved http: //Irongeek. com Notes
CIDR allows for less waste by splitting networks up CIDER notation: 255. 0 = /24 255. 0. 0 = /16 255. 0. 0. 0 = /8 Could also be others http: //Irongeek. com
Subnetting Dickins Corp uses IP range 10. *. *. * Assume a an example host is 10. 69. 69 Let’s say they use 255. 240 (/20) for a subnet. 111111110000 Red is network section, blue the host section AND with host IP 00001010. 01000101 111111110000 = 00001010. 01000101. 01000000 If two different IPs ANDed with the same subnet mask give the same result, they are on the same network http: //Irongeek. com
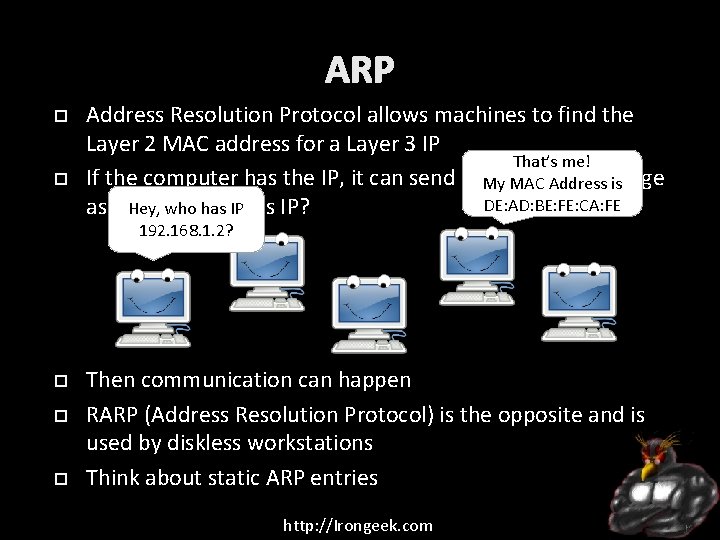
ARP Address Resolution Protocol allows machines to find the Layer 2 MAC address for a Layer 3 IP That’s me! If the computer has the IP, it can send a broadcast message My MAC Address is DE: AD: BE: FE: CA: FE asking Hey, who has IPthis IP? 192. 168. 1. 2? Then communication can happen RARP (Address Resolution Protocol) is the opposite and is used by diskless workstations Think about static ARP entries http: //Irongeek. com
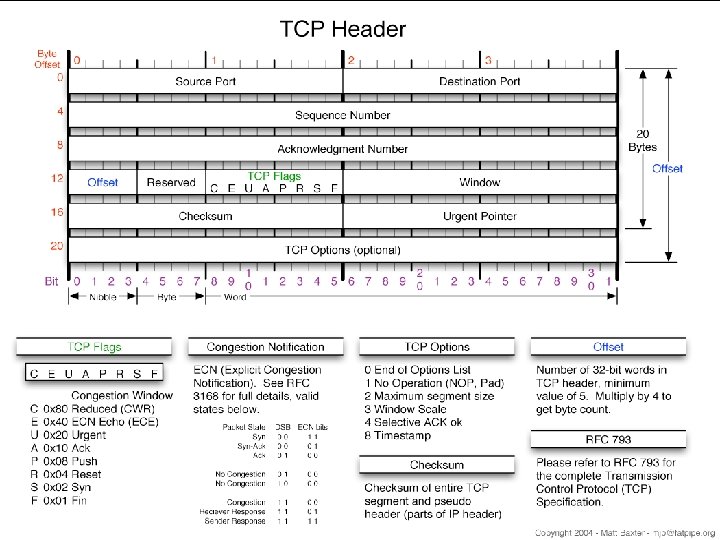
I am Adrianholio, I need TCP for my IP! TCP = Transmission Control Protocol Considered a “reliable”, session based protocol (though is is said to be on the Transport layer of OSI, AKA Layer 4) Starts with the three way handshake of: Host 1: SYN Host 2: SYN/ACK Host 3: ACK Has the concept of source and destination ports to specify what service to connect to http: //Irongeek. com
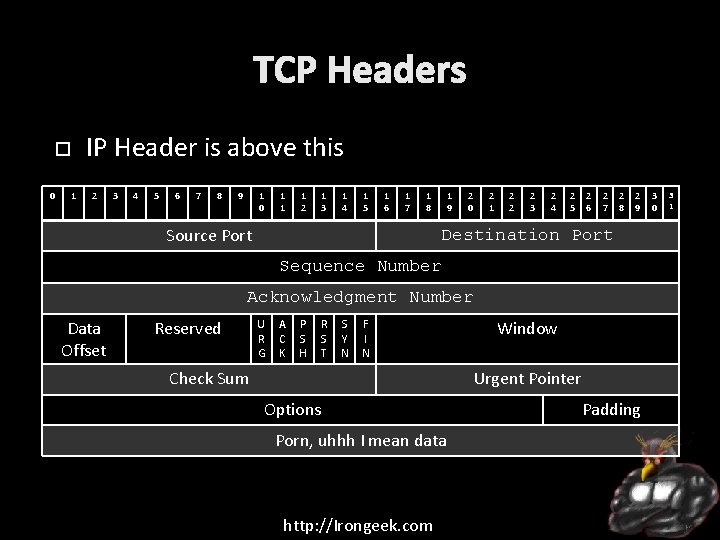
TCP Headers IP Header is above this 0 1 2 3 4 5 6 7 8 9 1 0 1 1 1 2 1 3 1 4 1 5 1 6 1 7 1 8 Source Port 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 6 2 7 2 8 2 9 Destination Port Sequence Number Acknowledgment Number Data Offset Reserved U R G A C K P S H R S T S Y N F I N Check Sum Window Urgent Pointer Options Porn, uhhh I mean data http: //Irongeek. com Padding 3 0 3 1
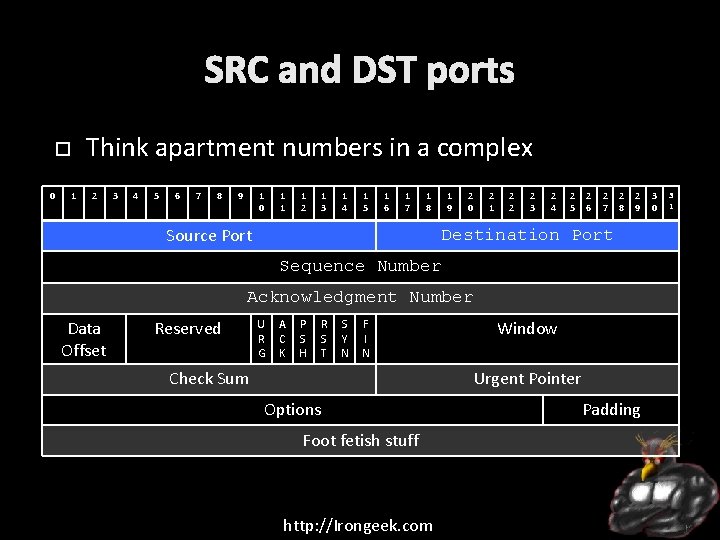
SRC and DST ports Think apartment numbers in a complex 0 1 2 3 4 5 6 7 8 9 1 0 1 1 1 2 1 3 1 4 1 5 1 6 1 7 1 8 Source Port 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 6 2 7 2 8 2 9 Destination Port Sequence Number Acknowledgment Number Data Offset Reserved U R G A C K P S H R S T S Y N F I N Check Sum Window Urgent Pointer Options Foot fetish stuff http: //Irongeek. com Padding 3 0 3 1
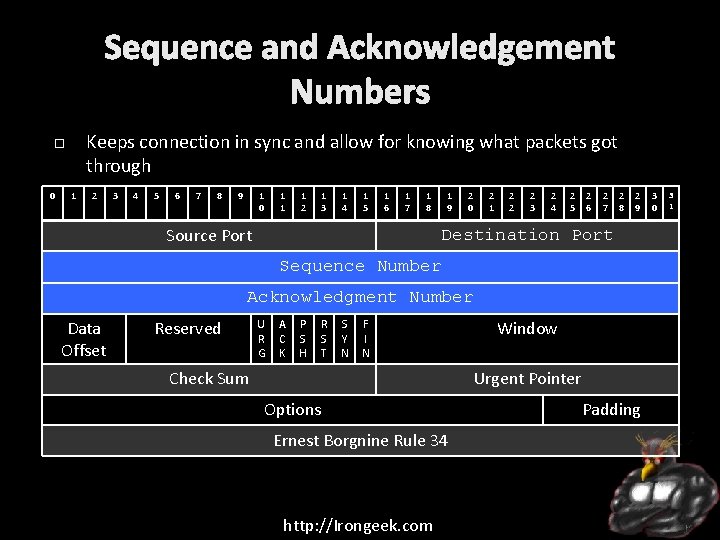
Sequence and Acknowledgement Numbers Keeps connection in sync and allow for knowing what packets got through 0 1 2 3 4 5 6 7 8 9 1 0 1 1 1 2 1 3 1 4 1 5 1 6 1 7 1 8 Source Port 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 6 2 7 2 8 2 9 Destination Port Sequence Number Acknowledgment Number Data Offset Reserved U R G A C K P S H R S T S Y N F I N Check Sum Window Urgent Pointer Options Ernest Borgnine Rule 34 http: //Irongeek. com Padding 3 0 3 1
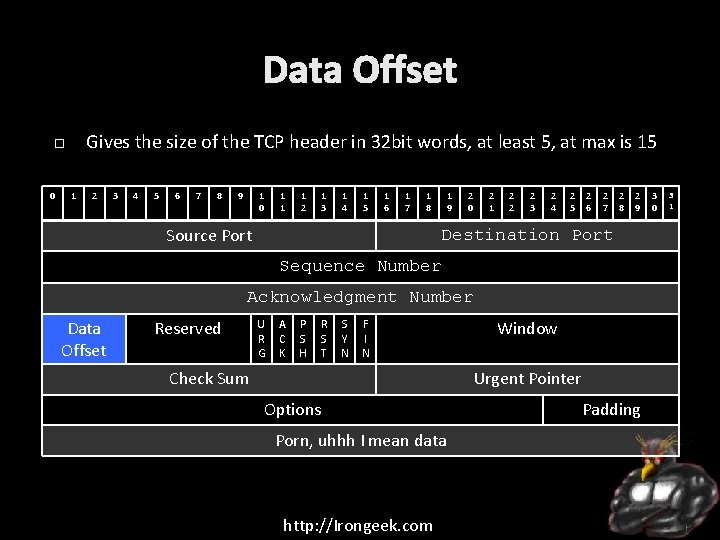
Data Offset Gives the size of the TCP header in 32 bit words, at least 5, at max is 15 0 1 2 3 4 5 6 7 8 9 1 0 1 1 1 2 1 3 1 4 1 5 1 6 1 7 1 8 Source Port 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 6 2 7 2 8 2 9 Destination Port Sequence Number Acknowledgment Number Data Offset Reserved U R G A C K P S H R S T S Y N F I N Check Sum Window Urgent Pointer Options Porn, uhhh I mean data http: //Irongeek. com Padding 3 0 3 1
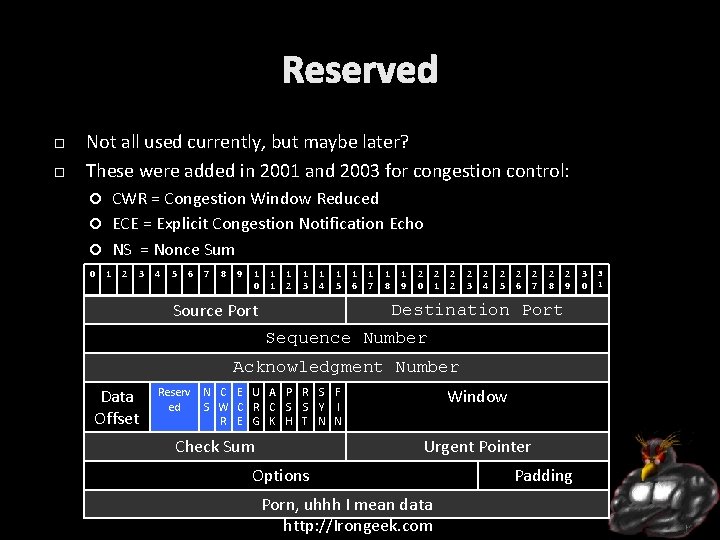
Reserved Not all used currently, but maybe later? These were added in 2001 and 2003 for congestion control: CWR = Congestion Window Reduced ECE = Explicit Congestion Notification Echo NS = Nonce Sum 0 1 2 3 4 5 6 7 8 9 1 0 1 1 1 2 1 3 1 4 1 5 Source Port 1 6 1 7 1 8 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 6 2 7 2 8 2 9 Destination Port Sequence Number Acknowledgment Number Data Offset Reserv ed Window N C E U A P R S F S W C R C S S Y I R E G K H T N N Check Sum Urgent Pointer Options Porn, uhhh I mean data http: //Irongeek. com Padding 3 0 3 1
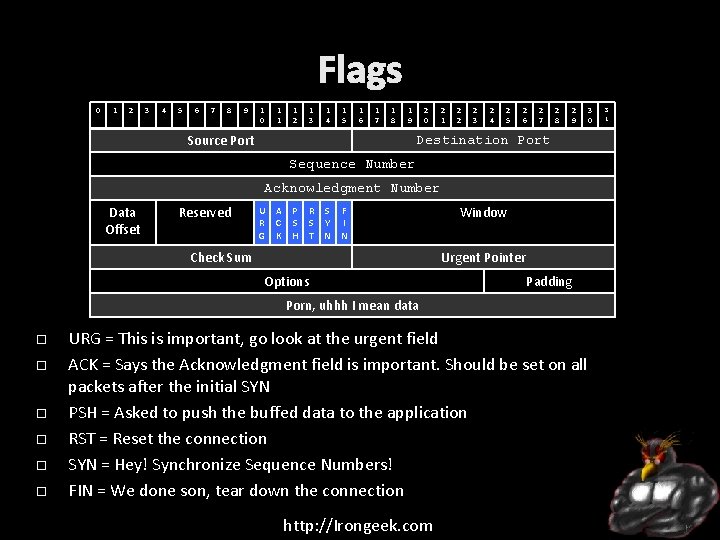
Flags 0 1 2 3 4 5 6 7 8 9 1 0 1 1 1 2 1 3 1 4 1 5 1 6 1 7 1 8 1 9 Source Port 2 0 2 1 2 2 2 3 2 4 2 5 2 6 2 7 2 8 2 9 Destination Port Sequence Number Acknowledgment Number Data Offset Reserved U A P R S F R C S S Y I G K H T N N Check Sum Window Urgent Pointer Options Padding Porn, uhhh I mean data URG = This is important, go look at the urgent field ACK = Says the Acknowledgment field is important. Should be set on all packets after the initial SYN PSH = Asked to push the buffed data to the application RST = Reset the connection SYN = Hey! Synchronize Sequence Numbers! FIN = We done son, tear down the connection http: //Irongeek. com 3 0 3 1
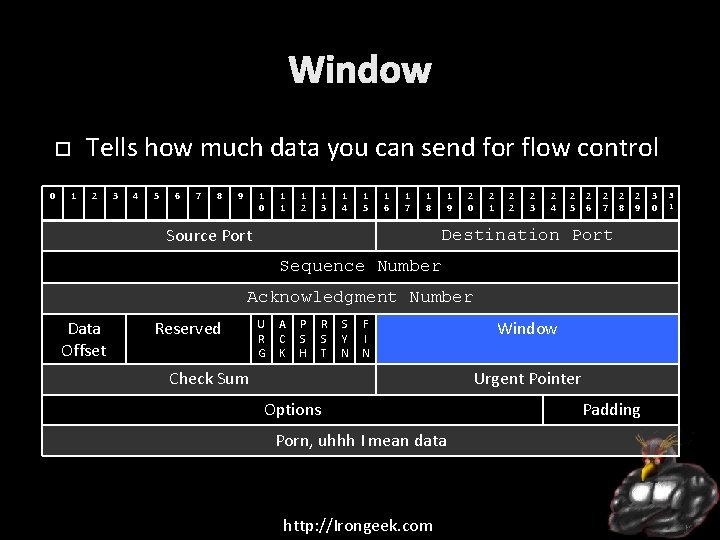
Window Tells how much data you can send for flow control 0 1 2 3 4 5 6 7 8 9 1 0 1 1 1 2 1 3 1 4 1 5 1 6 1 7 1 8 Source Port 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 6 2 7 2 8 2 9 Destination Port Sequence Number Acknowledgment Number Data Offset Reserved U R G A C K P S H R S T S Y N F I N Check Sum Window Urgent Pointer Options Porn, uhhh I mean data http: //Irongeek. com Padding 3 0 3 1
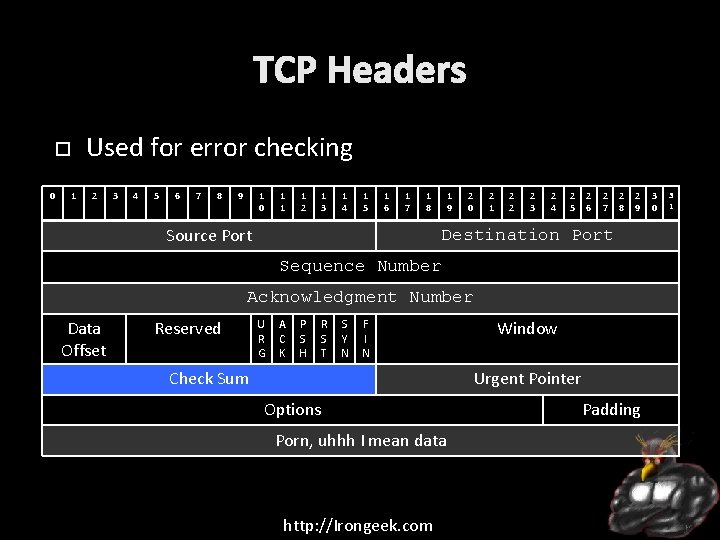
TCP Headers Used for error checking 0 1 2 3 4 5 6 7 8 9 1 0 1 1 1 2 1 3 1 4 1 5 1 6 1 7 1 8 Source Port 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 6 2 7 2 8 2 9 Destination Port Sequence Number Acknowledgment Number Data Offset Reserved U R G A C K P S H R S T S Y N F I N Check Sum Window Urgent Pointer Options Porn, uhhh I mean data http: //Irongeek. com Padding 3 0 3 1
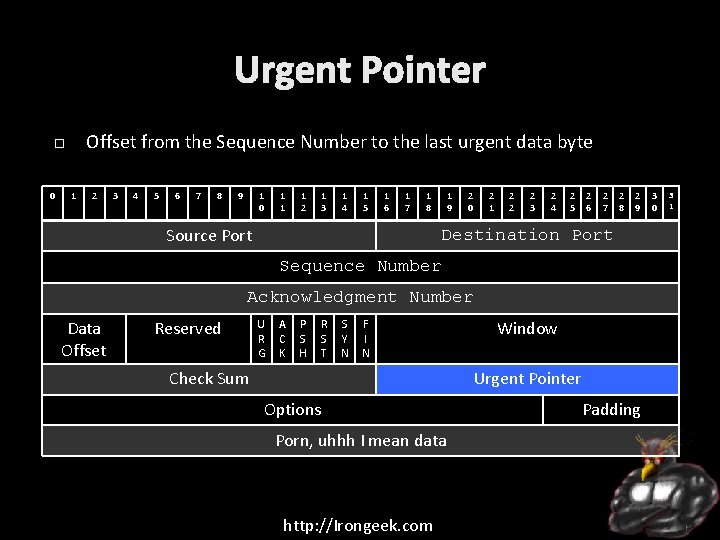
Urgent Pointer Offset from the Sequence Number to the last urgent data byte 0 1 2 3 4 5 6 7 8 9 1 0 1 1 1 2 1 3 1 4 1 5 1 6 1 7 1 8 Source Port 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 6 2 7 2 8 2 9 Destination Port Sequence Number Acknowledgment Number Data Offset Reserved U R G A C K P S H R S T S Y N F I N Check Sum Window Urgent Pointer Options Porn, uhhh I mean data http: //Irongeek. com Padding 3 0 3 1
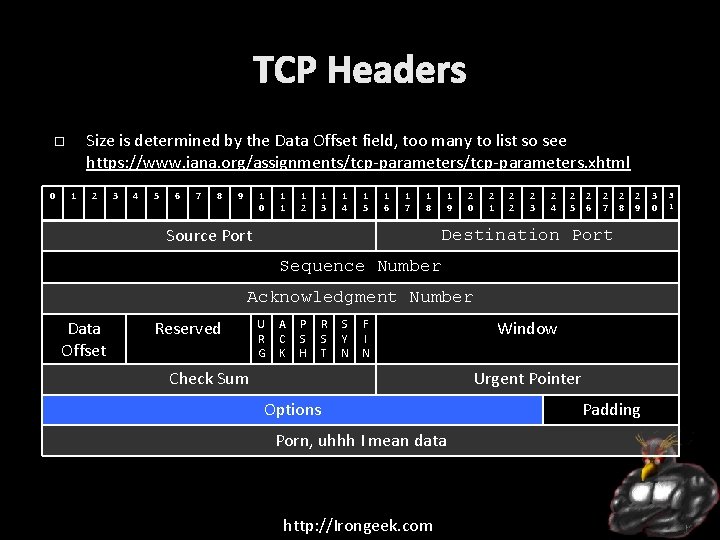
TCP Headers Size is determined by the Data Offset field, too many to list so see https: //www. iana. org/assignments/tcp-parameters. xhtml 0 1 2 3 4 5 6 7 8 9 1 0 1 1 1 2 1 3 1 4 1 5 1 6 1 7 1 8 Source Port 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 6 2 7 2 8 2 9 Destination Port Sequence Number Acknowledgment Number Data Offset Reserved U R G A C K P S H R S T S Y N F I N Check Sum Window Urgent Pointer Options Porn, uhhh I mean data http: //Irongeek. com Padding 3 0 3 1
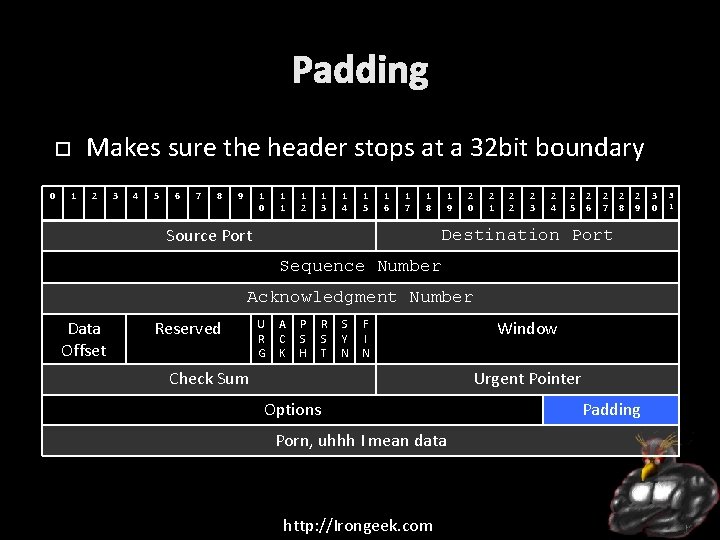
Padding Makes sure the header stops at a 32 bit boundary 0 1 2 3 4 5 6 7 8 9 1 0 1 1 1 2 1 3 1 4 1 5 1 6 1 7 1 8 Source Port 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 6 2 7 2 8 2 9 Destination Port Sequence Number Acknowledgment Number Data Offset Reserved U R G A C K P S H R S T S Y N F I N Check Sum Window Urgent Pointer Options Porn, uhhh I mean data http: //Irongeek. com Padding 3 0 3 1
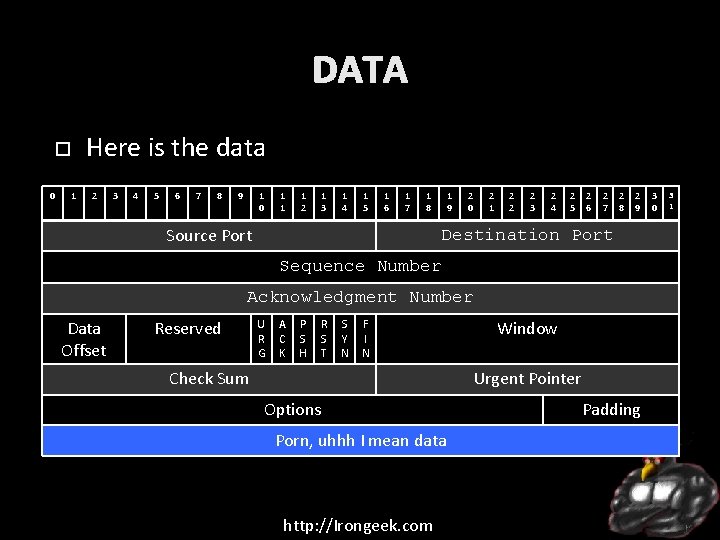
DATA Here is the data 0 1 2 3 4 5 6 7 8 9 1 0 1 1 1 2 1 3 1 4 1 5 1 6 1 7 1 8 Source Port 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 6 2 7 2 8 2 9 Destination Port Sequence Number Acknowledgment Number Data Offset Reserved U R G A C K P S H R S T S Y N F I N Check Sum Window Urgent Pointer Options Porn, uhhh I mean data http: //Irongeek. com Padding 3 0 3 1
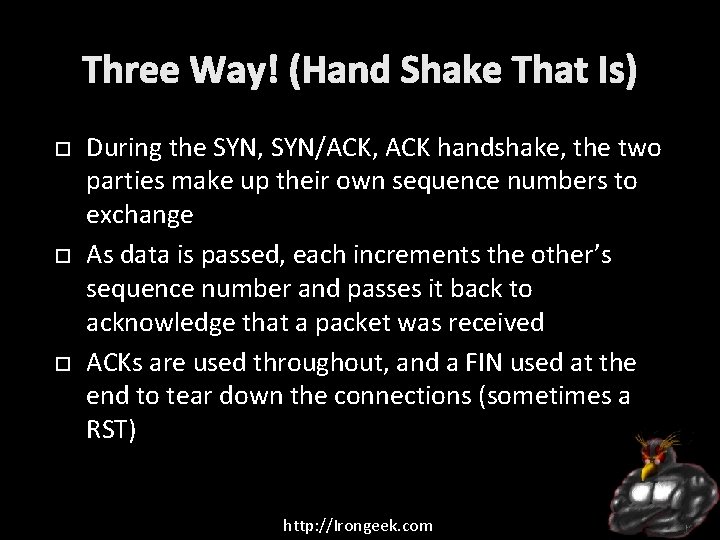
Three Way! (Hand Shake That Is) During the SYN, SYN/ACK, ACK handshake, the two parties make up their own sequence numbers to exchange As data is passed, each increments the other’s sequence number and passes it back to acknowledge that a packet was received ACKs are used throughout, and a FIN used at the end to tear down the connections (sometimes a RST) http: //Irongeek. com
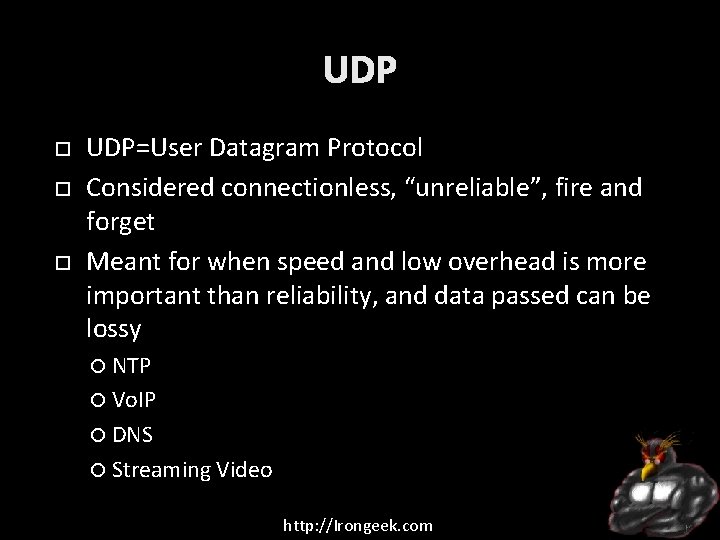
UDP UDP=User Datagram Protocol Considered connectionless, “unreliable”, fire and forget Meant for when speed and low overhead is more important than reliability, and data passed can be lossy NTP Vo. IP DNS Streaming Video http: //Irongeek. com
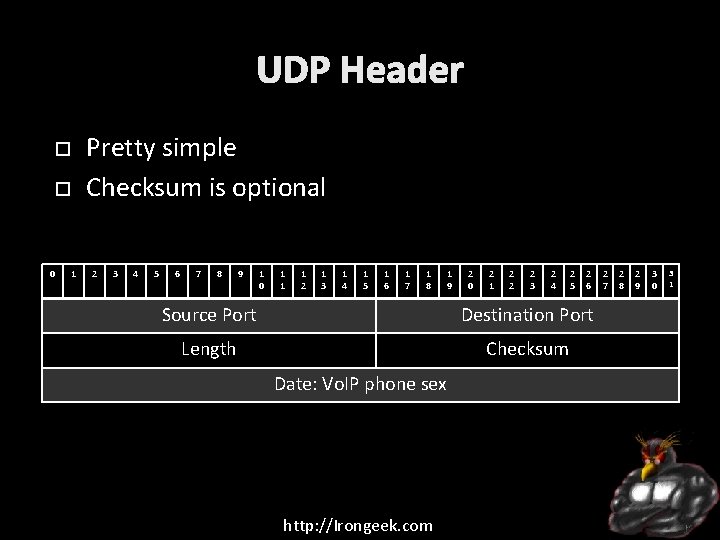
UDP Header Pretty simple Checksum is optional 0 1 2 3 4 5 6 7 8 9 1 0 1 1 1 2 1 3 1 4 1 5 1 6 1 7 1 8 1 9 2 0 2 1 2 2 2 3 2 4 2 5 2 6 Source Port Destination Port Length Checksum Date: Vo. IP phone sex http: //Irongeek. com 2 7 2 8 2 9 3 0 3 1
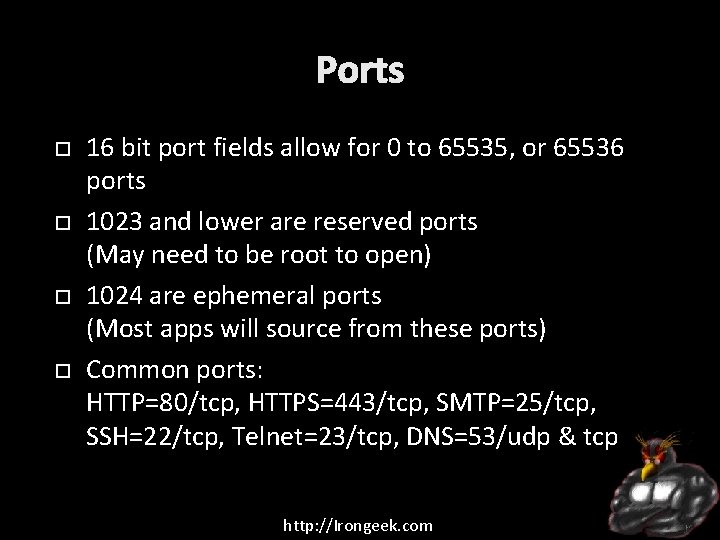
Ports 16 bit port fields allow for 0 to 65535, or 65536 ports 1023 and lower are reserved ports (May need to be root to open) 1024 are ephemeral ports (Most apps will source from these ports) Common ports: HTTP=80/tcp, HTTPS=443/tcp, SMTP=25/tcp, SSH=22/tcp, Telnet=23/tcp, DNS=53/udp & tcp http: //Irongeek. com
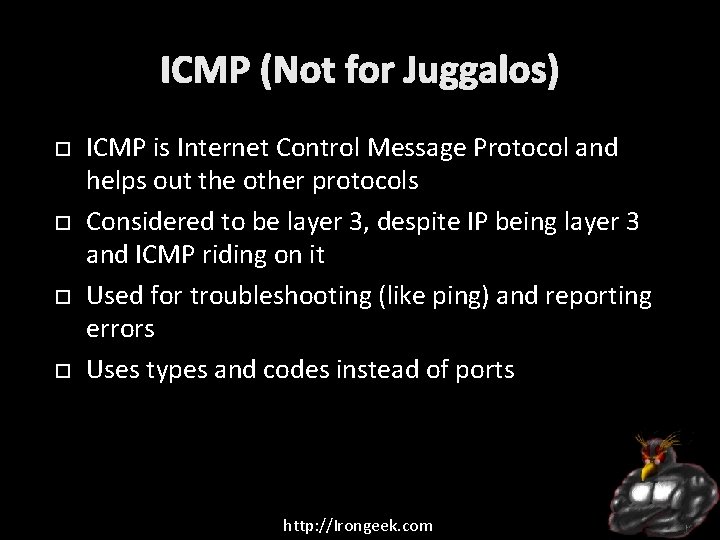
ICMP (Not for Juggalos) ICMP is Internet Control Message Protocol and helps out the other protocols Considered to be layer 3, despite IP being layer 3 and ICMP riding on it Used for troubleshooting (like ping) and reporting errors Uses types and codes instead of ports http: //Irongeek. com
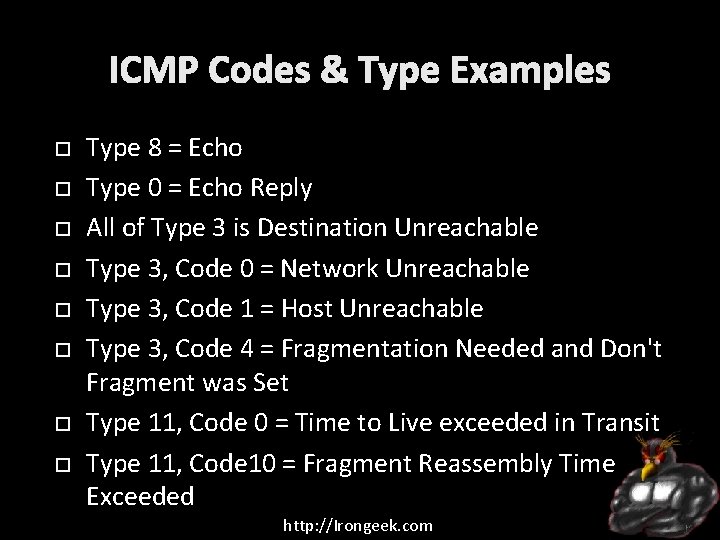
ICMP Codes & Type Examples Type 8 = Echo Type 0 = Echo Reply All of Type 3 is Destination Unreachable Type 3, Code 0 = Network Unreachable Type 3, Code 1 = Host Unreachable Type 3, Code 4 = Fragmentation Needed and Don't Fragment was Set Type 11, Code 0 = Time to Live exceeded in Transit Type 11, Code 10 = Fragment Reassembly Time Exceeded http: //Irongeek. com
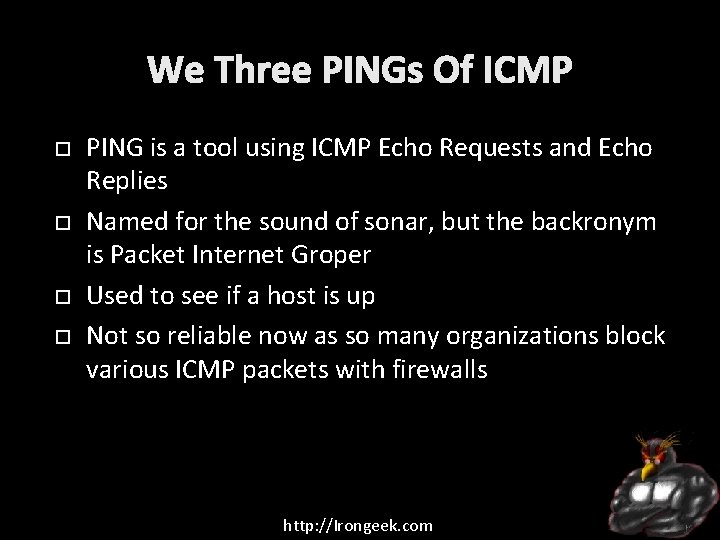
We Three PINGs Of ICMP PING is a tool using ICMP Echo Requests and Echo Replies Named for the sound of sonar, but the backronym is Packet Internet Groper Used to see if a host is up Not so reliable now as so many organizations block various ICMP packets with firewalls http: //Irongeek. com
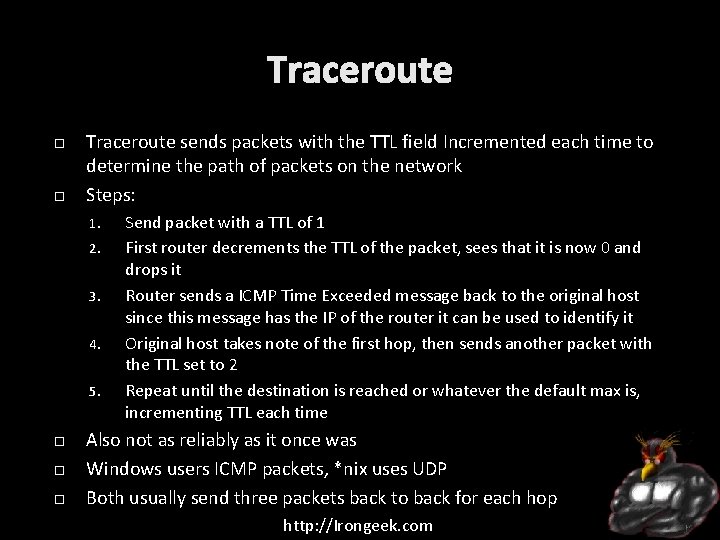
Traceroute sends packets with the TTL field Incremented each time to determine the path of packets on the network Steps: 1. 2. 3. 4. 5. Send packet with a TTL of 1 First router decrements the TTL of the packet, sees that it is now 0 and drops it Router sends a ICMP Time Exceeded message back to the original host since this message has the IP of the router it can be used to identify it Original host takes note of the first hop, then sends another packet with the TTL set to 2 Repeat until the destination is reached or whatever the default max is, incrementing TTL each time Also not as reliably as it once was Windows users ICMP packets, *nix uses UDP Both usually send three packets back to back for each hop http: //Irongeek. com
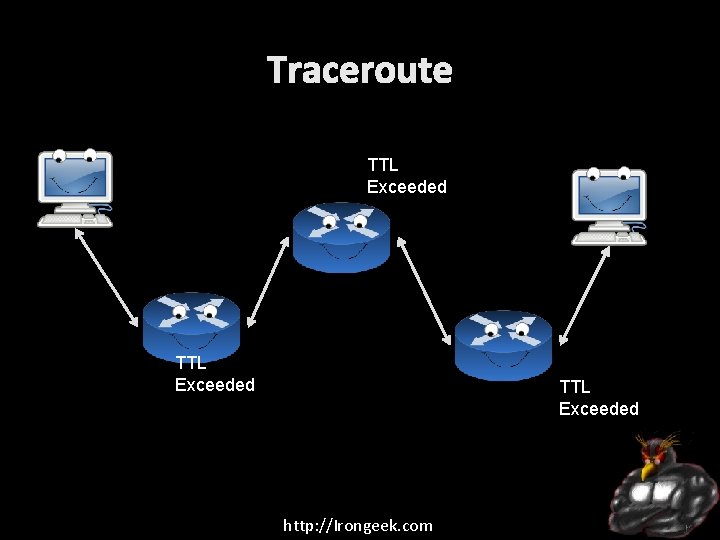
Traceroute TTL Exceeded http: //Irongeek. com
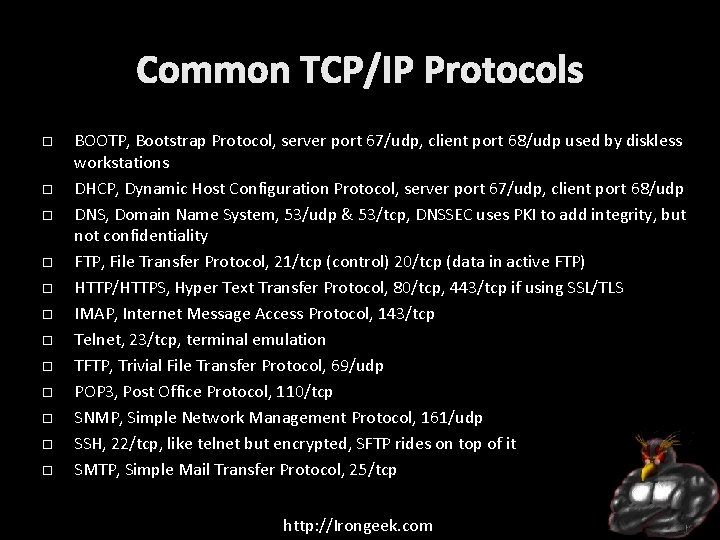
Common TCP/IP Protocols BOOTP, Bootstrap Protocol, server port 67/udp, client port 68/udp used by diskless workstations DHCP, Dynamic Host Configuration Protocol, server port 67/udp, client port 68/udp DNS, Domain Name System, 53/udp & 53/tcp, DNSSEC uses PKI to add integrity, but not confidentiality FTP, File Transfer Protocol, 21/tcp (control) 20/tcp (data in active FTP) HTTP/HTTPS, Hyper Text Transfer Protocol, 80/tcp, 443/tcp if using SSL/TLS IMAP, Internet Message Access Protocol, 143/tcp Telnet, 23/tcp, terminal emulation TFTP, Trivial File Transfer Protocol, 69/udp POP 3, Post Office Protocol, 110/tcp SNMP, Simple Network Management Protocol, 161/udp SSH, 22/tcp, like telnet but encrypted, SFTP rides on top of it SMTP, Simple Mail Transfer Protocol, 25/tcp http: //Irongeek. com
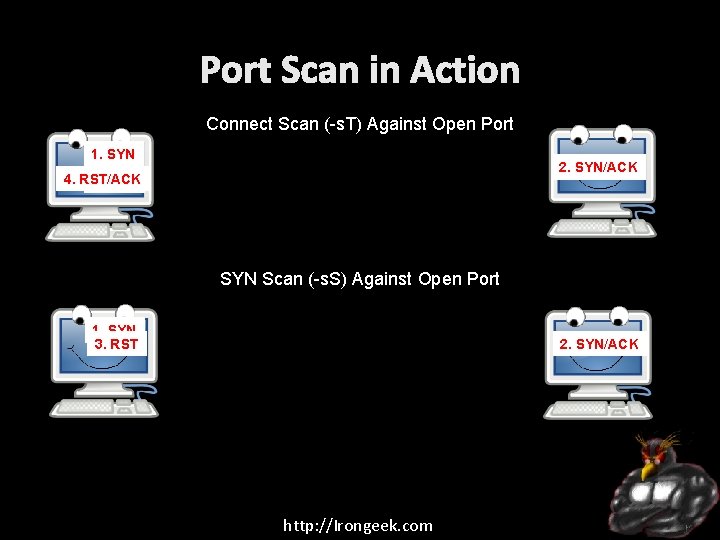
Port Scan in Action Connect Scan (-s. T) Against Open Port 1. SYN 2. SYN/ACK 4. RST/ACK 3. ACK SYN Scan (-s. S) Against Open Port 1. SYN 3. RST 2. SYN/ACK http: //Irongeek. com
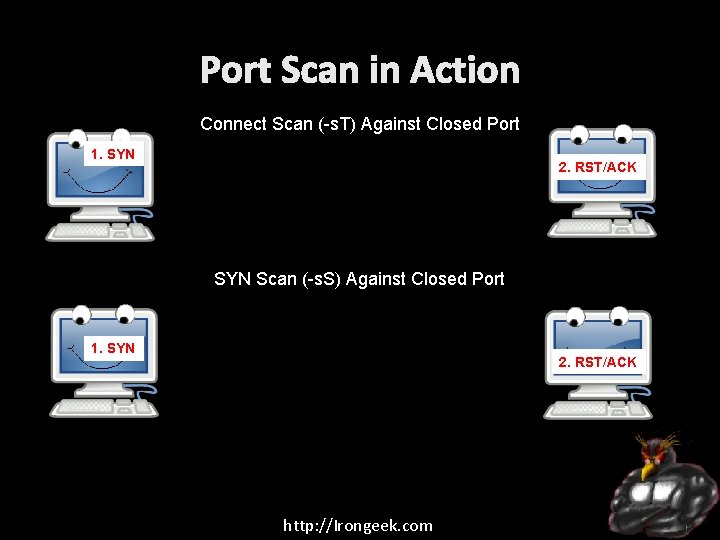
Port Scan in Action Connect Scan (-s. T) Against Closed Port 1. SYN 2. RST/ACK SYN Scan (-s. S) Against Closed Port 1. SYN 2. RST/ACK http: //Irongeek. com
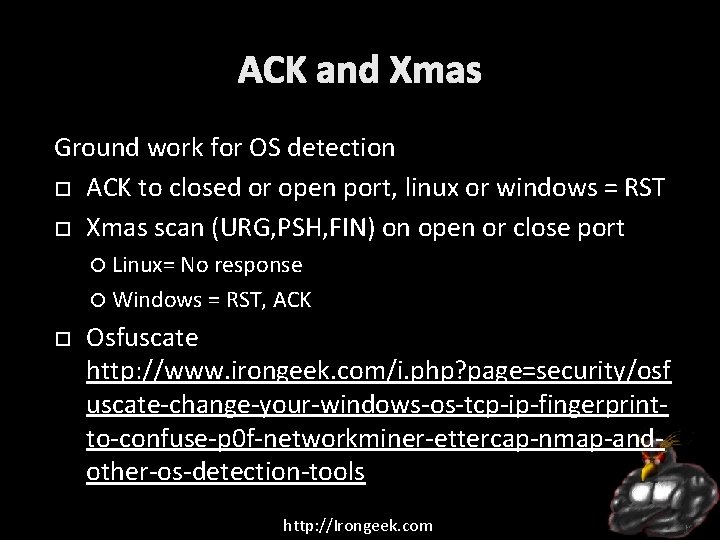
ACK and Xmas Ground work for OS detection ACK to closed or open port, linux or windows = RST Xmas scan (URG, PSH, FIN) on open or close port Linux= No response Windows = RST, ACK Osfuscate http: //www. irongeek. com/i. php? page=security/osf uscate-change-your-windows-os-tcp-ip-fingerprintto-confuse-p 0 f-networkminer-ettercap-nmap-andother-os-detection-tools http: //Irongeek. com
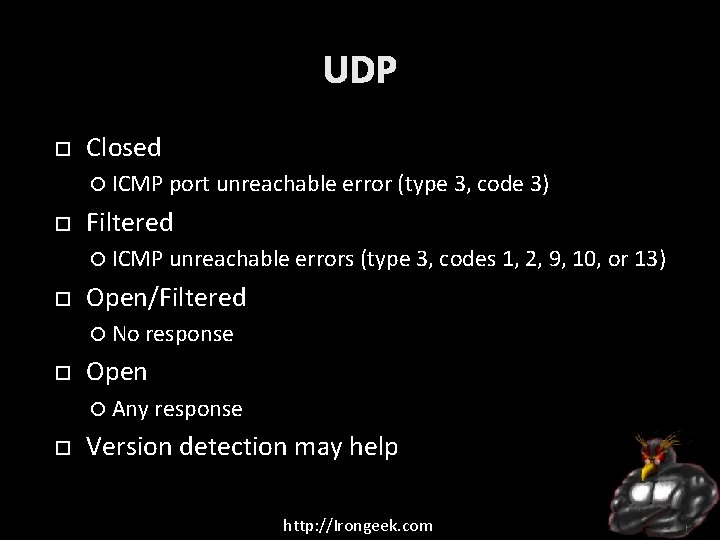
UDP Closed ICMP port unreachable error (type 3, code 3) Filtered ICMP unreachable errors (type 3, codes 1, 2, 9, 10, or 13) Open/Filtered No response Open Any response Version detection may help http: //Irongeek. com
Simple Scan Demo Examples nmap 10. 0. 0. 1 nmap –s. S 10. 0. 0. 1 http: //Irongeek. com
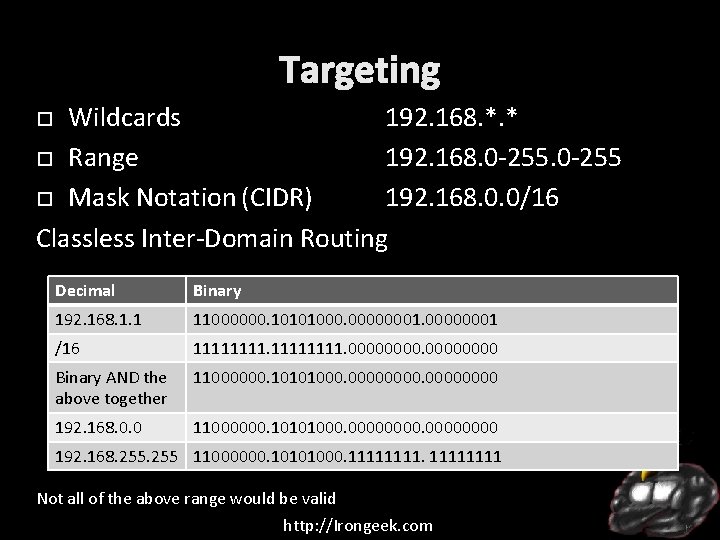
Targeting Wildcards 192. 168. *. * Range 192. 168. 0 -255 Mask Notation (CIDR) 192. 168. 0. 0/16 Classless Inter-Domain Routing Decimal Binary 192. 168. 1. 1 11000000. 10101000. 00000001 /16 11111111. 0000 Binary AND the above together 11000000. 10101000. 00000000 192. 168. 0. 0 11000000. 10101000. 00000000 192. 168. 255 11000000. 10101000. 11111111 Not all of the above range would be valid http: //Irongeek. com
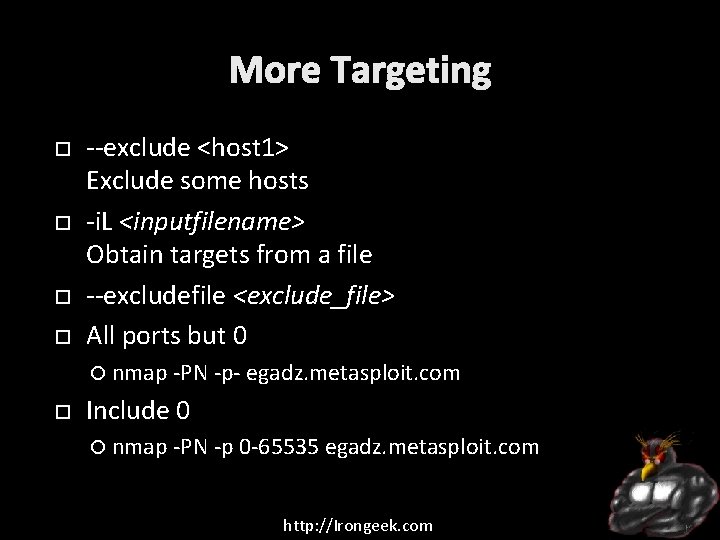
More Targeting --exclude <host 1> Exclude some hosts -i. L <inputfilename> Obtain targets from a file --excludefile <exclude_file> All ports but 0 nmap -PN -p- egadz. metasploit. com Include 0 nmap -PN -p 0 -65535 egadz. metasploit. com http: //Irongeek. com
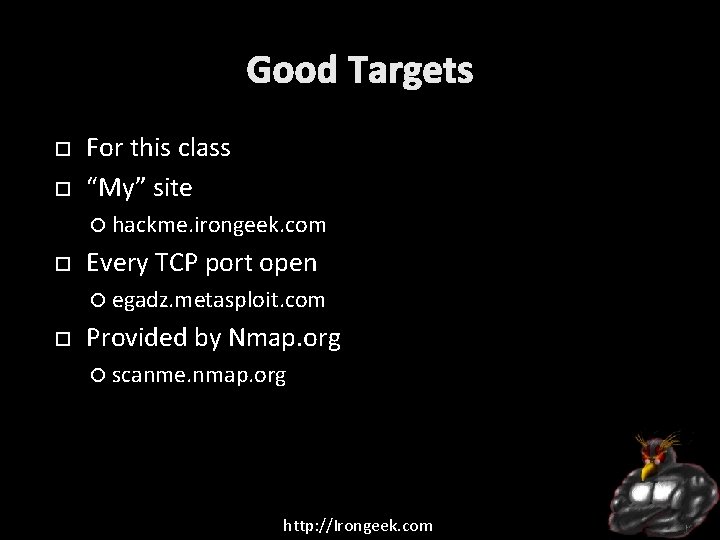
Good Targets For this class “My” site hackme. irongeek. com Every TCP port open egadz. metasploit. com Provided by Nmap. org scanme. nmap. org http: //Irongeek. com
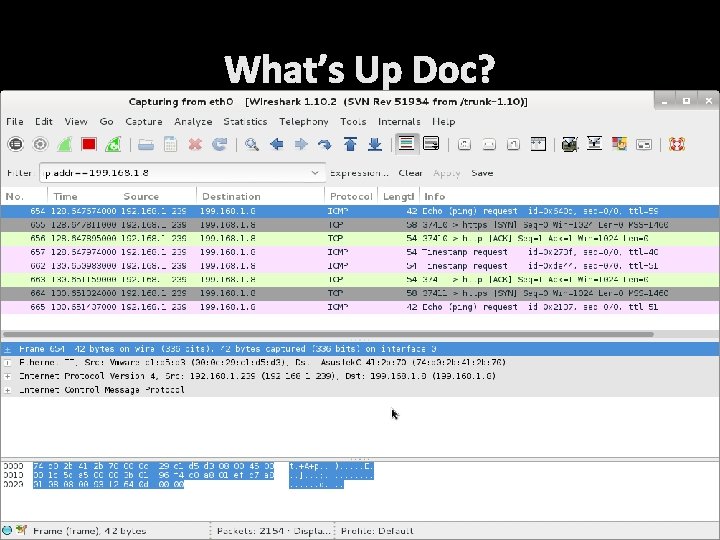
What’s Up Doc? Default “Ping” ARP if on same subnet, and that’s it, otherwise: ICMP Echo SYN to 443 (https) ACK to 80 (http) ICMP Timestamp Request And then in reverse http: //Irongeek. com
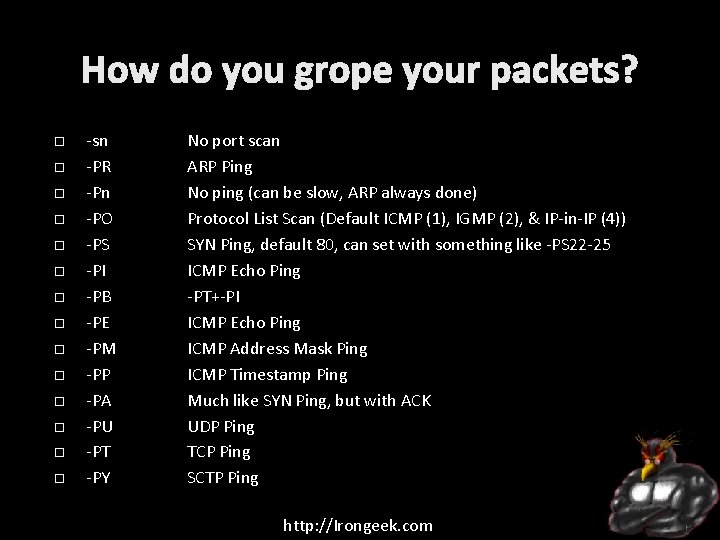
How do you grope your packets? -sn -PR -Pn -PO -PS -PI -PB -PE -PM -PP -PA -PU -PT -PY No port scan ARP Ping No ping (can be slow, ARP always done) Protocol List Scan (Default ICMP (1), IGMP (2), & IP-in-IP (4)) SYN Ping, default 80, can set with something like -PS 22 -25 ICMP Echo Ping -PT+-PI ICMP Echo Ping ICMP Address Mask Ping ICMP Timestamp Ping Much like SYN Ping, but with ACK UDP Ping TCP Ping SCTP Ping http: //Irongeek. com
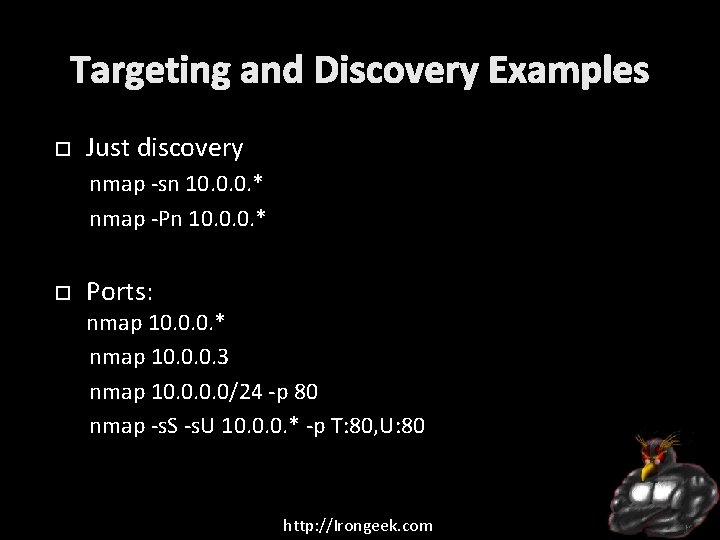
Targeting and Discovery Examples Just discovery nmap -sn 10. 0. 0. * nmap -Pn 10. 0. 0. * Ports: nmap 10. 0. 0. * nmap 10. 0. 0. 3 nmap 10. 0/24 -p 80 nmap -s. S -s. U 10. 0. 0. * -p T: 80, U: 80 http: //Irongeek. com
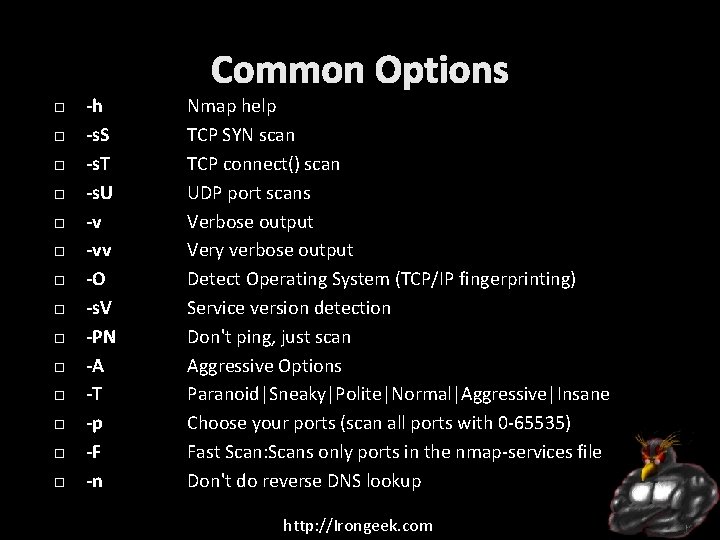
Common Options -h -s. S -s. T -s. U -v -vv -O -s. V -PN -A -T -p -F -n Nmap help TCP SYN scan TCP connect() scan UDP port scans Verbose output Very verbose output Detect Operating System (TCP/IP fingerprinting) Service version detection Don't ping, just scan Aggressive Options Paranoid|Sneaky|Polite|Normal|Aggressive|Insane Choose your ports (scan all ports with 0 -65535) Fast Scan: Scans only ports in the nmap-services file Don't do reverse DNS lookup http: //Irongeek. com
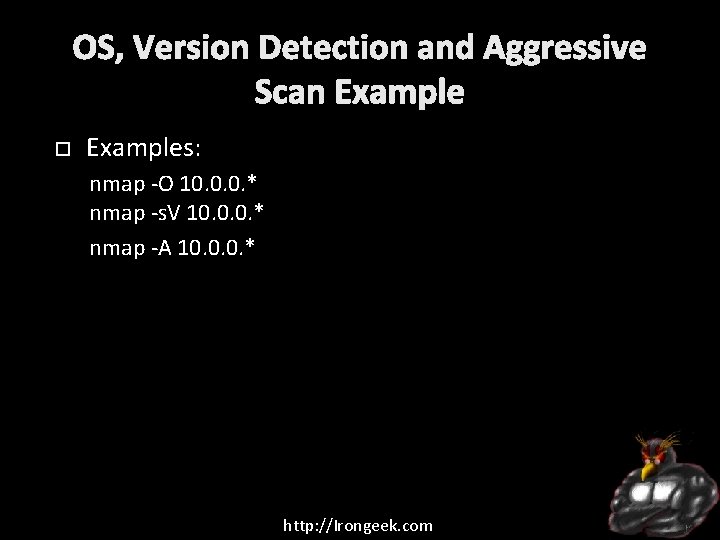
OS, Version Detection and Aggressive Scan Examples: nmap -O 10. 0. 0. * nmap -s. V 10. 0. 0. * nmap -A 10. 0. 0. * http: //Irongeek. com
GUI for you Wimps http: //Irongeek. com
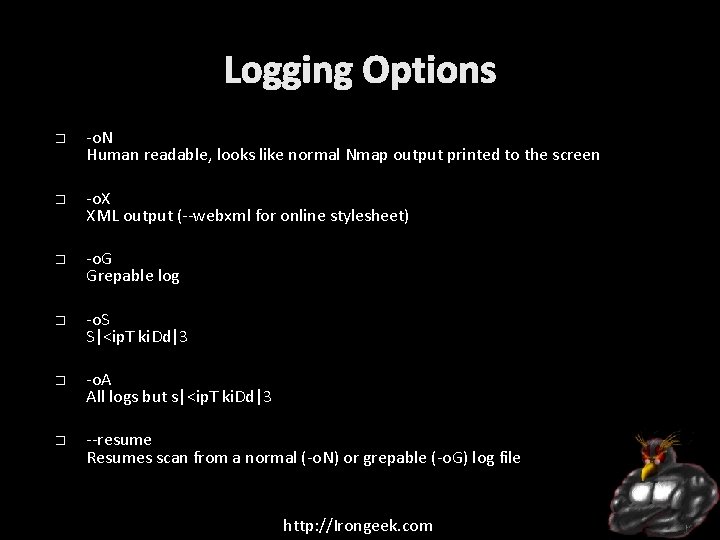
Logging Options � � � -o. N Human readable, looks like normal Nmap output printed to the screen -o. X XML output (--webxml for online stylesheet) -o. G Grepable log -o. S S|<ip. T ki. Dd|3 -o. A All logs but s|<ip. T ki. Dd|3 --resume Resumes scan from a normal (-o. N) or grepable (-o. G) log file http: //Irongeek. com
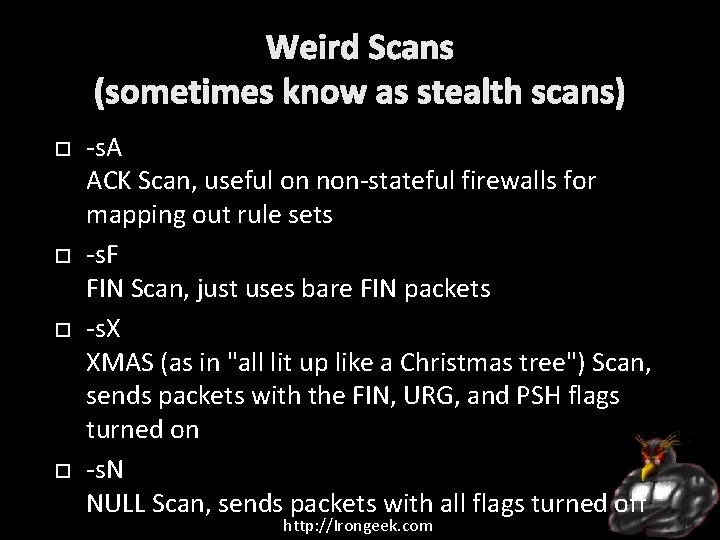
Weird Scans (sometimes know as stealth scans) -s. A ACK Scan, useful on non-stateful firewalls for mapping out rule sets -s. F FIN Scan, just uses bare FIN packets -s. X XMAS (as in "all lit up like a Christmas tree") Scan, sends packets with the FIN, URG, and PSH flags turned on -s. N NULL Scan, sends packets with all flags turned off http: //Irongeek. com
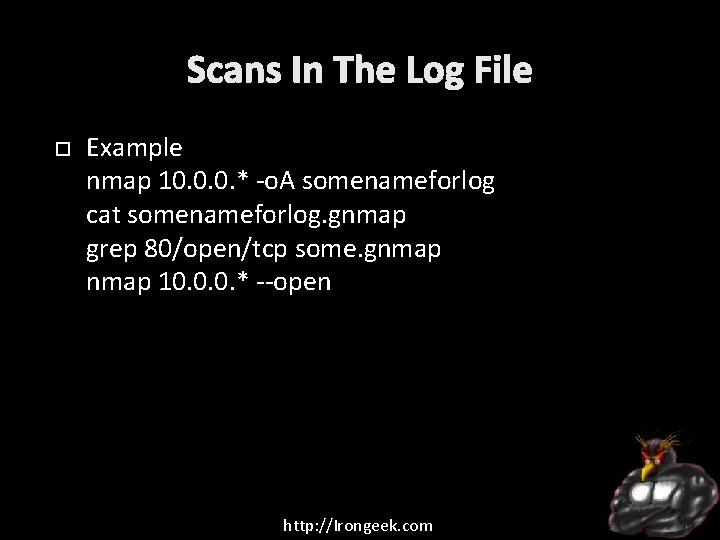
Scans In The Log File Example nmap 10. 0. 0. * -o. A somenameforlog cat somenameforlog. gnmap grep 80/open/tcp some. gnmap 10. 0. 0. * --open http: //Irongeek. com
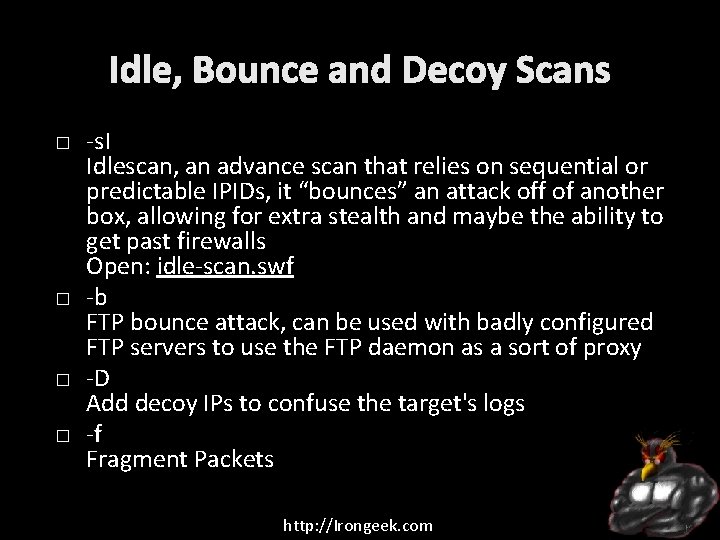
Idle, Bounce and Decoy Scans � � -s. I Idlescan, an advance scan that relies on sequential or predictable IPIDs, it “bounces” an attack off of another box, allowing for extra stealth and maybe the ability to get past firewalls Open: idle-scan. swf -b FTP bounce attack, can be used with badly configured FTP servers to use the FTP daemon as a sort of proxy -D Add decoy IPs to confuse the target's logs -f Fragment Packets http: //Irongeek. com
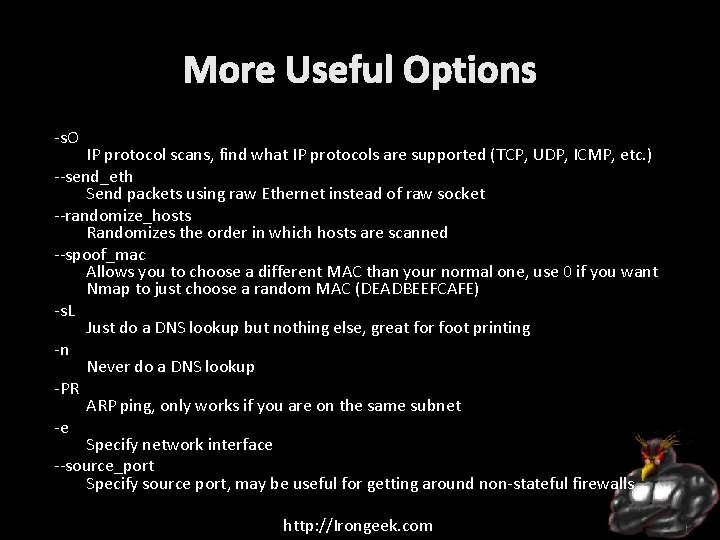
More Useful Options -s. O IP protocol scans, find what IP protocols are supported (TCP, UDP, ICMP, etc. ) --send_eth Send packets using raw Ethernet instead of raw socket --randomize_hosts Randomizes the order in which hosts are scanned --spoof_mac Allows you to choose a different MAC than your normal one, use 0 if you want Nmap to just choose a random MAC (DEADBEEFCAFE) -s. L Just do a DNS lookup but nothing else, great for foot printing -n Never do a DNS lookup -PR ARP ping, only works if you are on the same subnet -e Specify network interface --source_port Specify source port, may be useful for getting around non-stateful firewalls http: //Irongeek. com
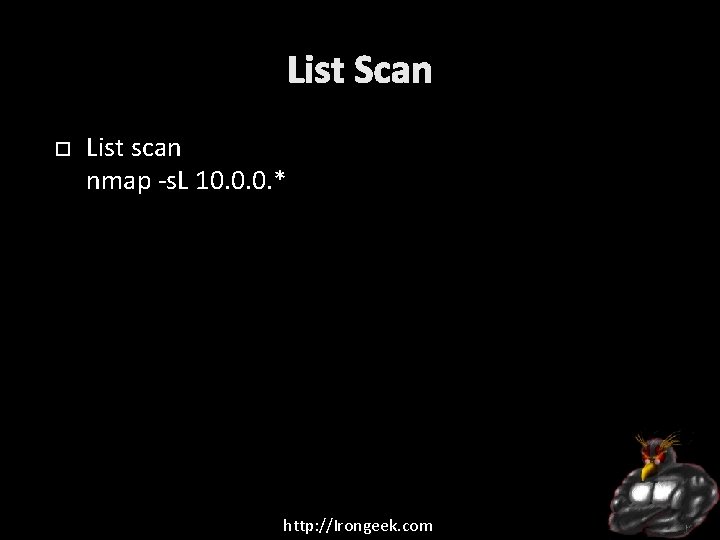
List Scan List scan nmap -s. L 10. 0. 0. * http: //Irongeek. com
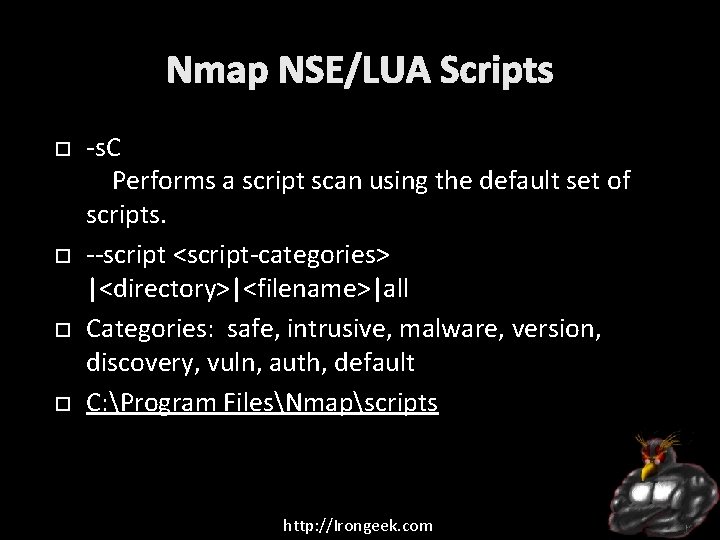
Nmap NSE/LUA Scripts -s. C Performs a script scan using the default set of scripts. --script <script-categories> |<directory>|<filename>|all Categories: safe, intrusive, malware, version, discovery, vuln, auth, default C: Program FilesNmapscripts http: //Irongeek. com
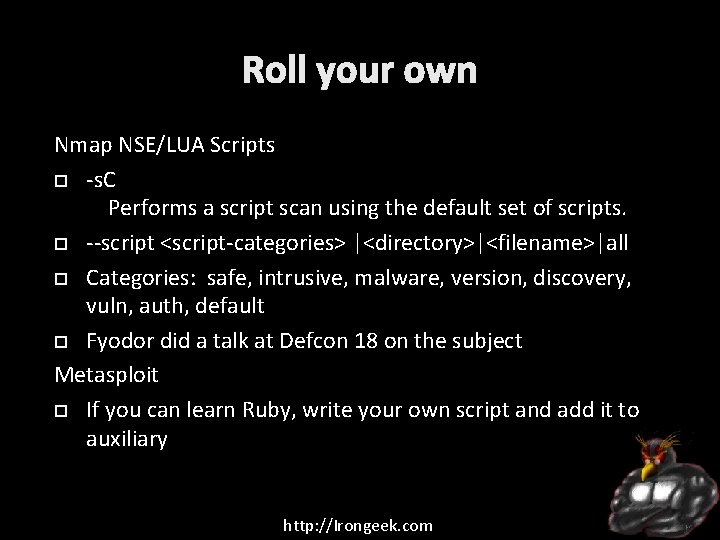
Roll your own Nmap NSE/LUA Scripts -s. C Performs a script scan using the default set of scripts. --script <script-categories> |<directory>|<filename>|all Categories: safe, intrusive, malware, version, discovery, vuln, auth, default Fyodor did a talk at Defcon 18 on the subject Metasploit If you can learn Ruby, write your own script and add it to auxiliary http: //Irongeek. com
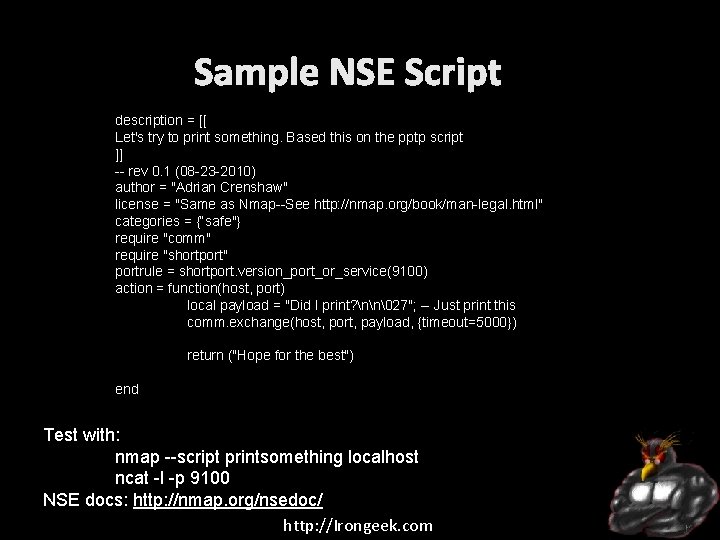
Sample NSE Script description = [[ Let's try to print something. Based this on the pptp script ]] -- rev 0. 1 (08 -23 -2010) author = "Adrian Crenshaw" license = "Same as Nmap--See http: //nmap. org/book/man-legal. html" categories = {“safe"} require "comm" require "shortport" portrule = shortport. version_port_or_service(9100) action = function(host, port) local payload = "Did I print? nn�27"; -- Just print this comm. exchange(host, port, payload, {timeout=5000}) return ("Hope for the best") end Test with: nmap --script printsomething localhost ncat -l -p 9100 NSE docs: http: //nmap. org/nsedoc/ http: //Irongeek. com

Events Derbycon Sept 24 th-28 th, 2014 Derbycon Art Credits to Digi. P Photo Credits to KC (devauto) http: //www. derbycon. com Others http: //www. louisvilleinfosec. com http: //skydogcon. com http: //hack 3 rcon. org http: //outerz 0 ne. org http: //phreaknic. info http: //notacon. org http: //Irongeek. com
QUESTIONS? 42 Twitter: @Irongeek_ADC http: //Irongeek. com
- Slides: 83