Adaptive Data Hide in Palette Images by Color
Adaptive Data Hide in Palette Images by Color Ordering and Mapping With Security Protection Source: IEEE Transactions on communications, Vol. 52, No. 5, pp. 791 - 800, May 2004 Authors: Chih-Hsuan Tzeng, Zhi-Fang Yang, Wen- Hsiang Tsai Speaker: Yu-Cheng Wang Date: 2004/06/08 1
Outline • • Introduction Color-Ordering Relationship Color-Mapping function Embedding process and Extraction process Security Protection Experimental Results Conclusions 2
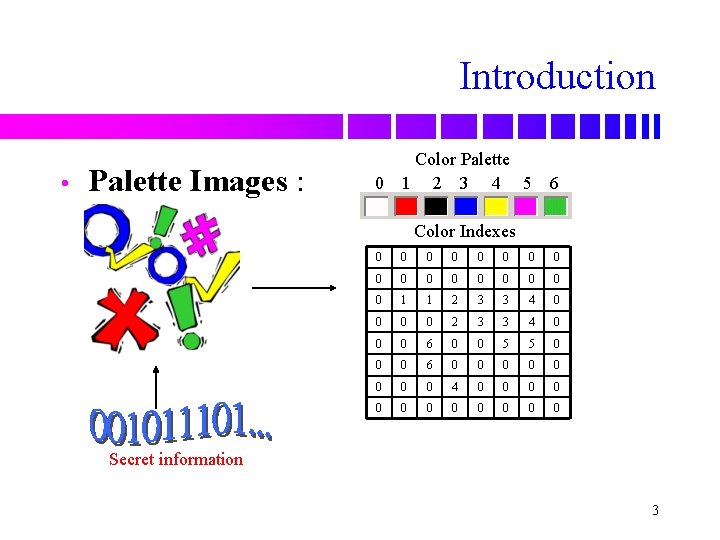
Introduction • Palette Images : 0 Color Palette 1 2 3 4 5 6 Color Indexes 0 0 0 0 0 1 1 2 3 3 4 0 0 0 6 0 0 5 5 0 0 0 6 0 0 0 0 4 0 0 0 Secret information 3
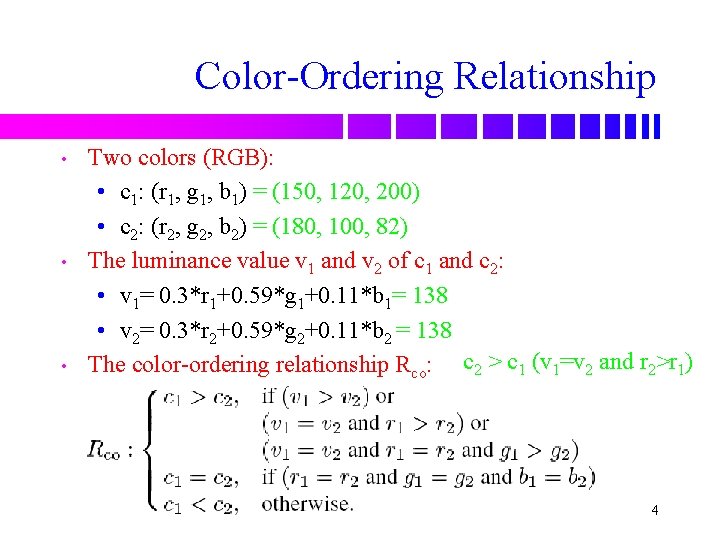
Color-Ordering Relationship • • • Two colors (RGB): • c 1: (r 1, g 1, b 1) = (150, 120, 200) • c 2: (r 2, g 2, b 2) = (180, 100, 82) The luminance value v 1 and v 2 of c 1 and c 2: • v 1= 0. 3*r 1+0. 59*g 1+0. 11*b 1= 138 • v 2= 0. 3*r 2+0. 59*g 2+0. 11*b 2 = 138 The color-ordering relationship Rco: c 2 > c 1 (v 1=v 2 and r 2>r 1) 4
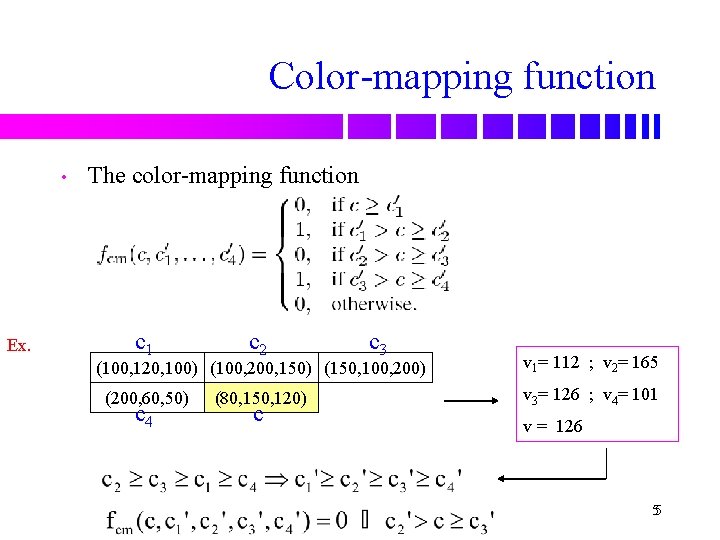
Color-mapping function • The color-mapping function c 1 Ex. c 2 c 3 (100, 120, 100) (100, 200, 150) (150, 100, 200) c 1 c 2 (200, 60, 50) c 4 c c 3 (80, 150, 120) c v 1= 112 ; v 2= 165 Color-ordering v = 126 ; v 4= 101 relationship 3 v = 126 55
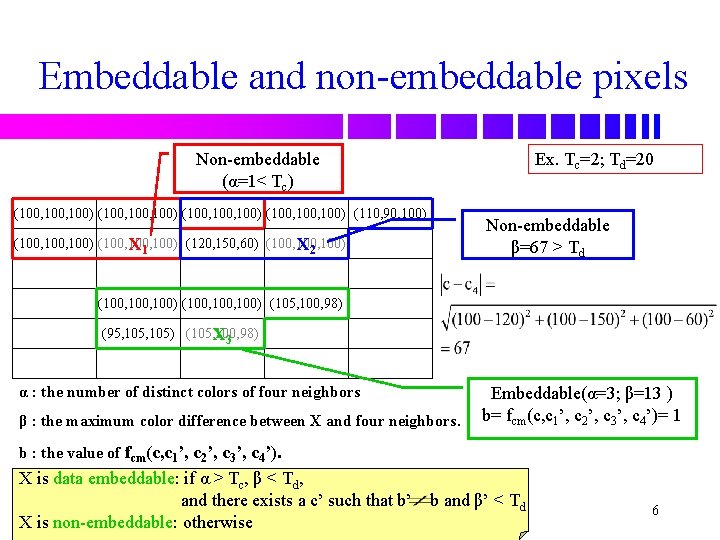
Embeddable and non-embeddable pixels Non-embeddable (α=1< Tc) Ex. Tc=2; Td=20 (100, 100, 100) (110, 90, 100) Non-embeddable β=67 > Td (100, 100) (120, 150, 60) (100, 100) X 1 X 2 (100, 100) (105, 100, 98) (95, 105) (105, 100, 98) X 3 α : the number of distinct colors of four neighbors β : the maximum color difference between X and four neighbors. Embeddable(α=3; β=13 ) b= fcm(c, c 1’, c 2’, c 3’, c 4’)= 1 b : the value of fcm(c, c 1’, c 2’, c 3’, c 4’). X is data embeddable: if α > Tc, β < Td, and there exists a c’ such that b’ X is non-embeddable: otherwise b and β’ < Td 6
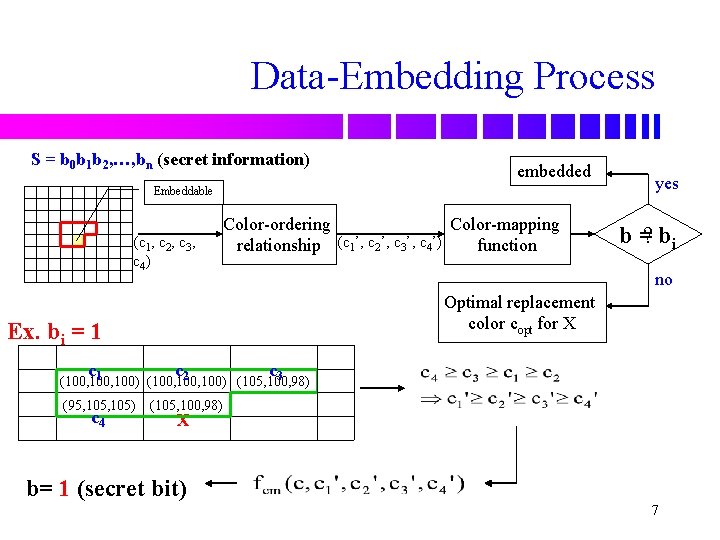
Data-Embedding Process S = b 0 b 1 b 2, …, bn (secret information) embedded Embeddable (c 1, c 2, c 3, c 4) Color-ordering Color-mapping relationship (c 1’, c 2’, c 3’, c 4’) function b =? bi no Optimal replacement color copt for X Ex. bi = 1 c yes c c 1 2 3 (100, 100) (105, 100, 98) (95, 105) c 4 (105, 100, 98) X b= 1 (secret bit) 7
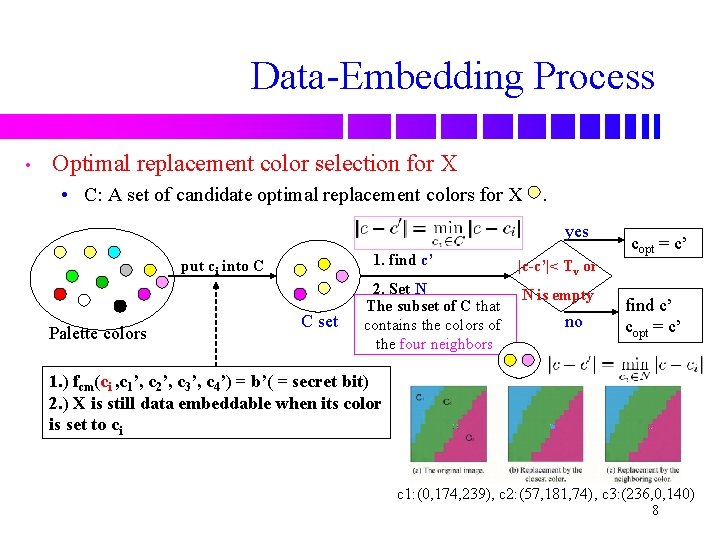
Data-Embedding Process • Optimal replacement color selection for X • C: A set of candidate optimal replacement colors for X. yes 1. find c’ put ci into C Palette colors C set 2. Set N The subset of C that contains the colors of the four neighbors copt = c’ |c-c’|< Tv or N is empty no find c’ copt = c’ 1. ) fcm(ci , c 1’, c 2’, c 3’, c 4’) = b’( = secret bit) 2. ) X is still data embeddable when its color is set to ci c 1: (0, 174, 239), c 2: (57, 181, 74), c 3: (236, 0, 140) 8
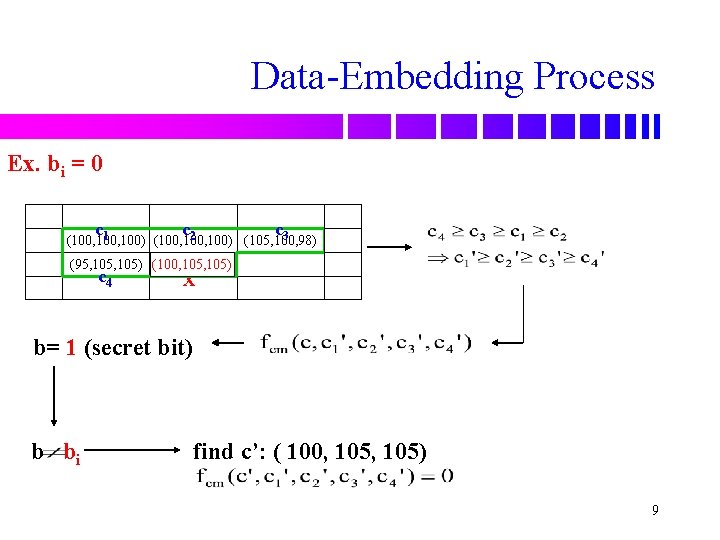
Data-Embedding Process Ex. bi = 0 c c c 1 2 3 (100, 100) (105, 100, 98) (95, 105) (100, 105) (105, 100, 98) c 4 X b= 1 (secret bit) b bi find c’: ( 100, 105) 9
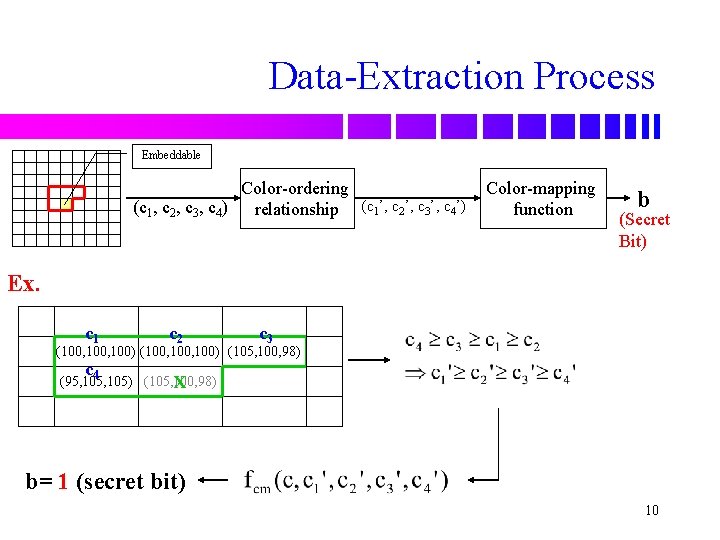
Data-Extraction Process Embeddable Color-ordering (c 1, c 2, c 3, c 4) relationship (c 1’, c 2’, c 3’, c 4’) Color-mapping function b (Secret Bit) Ex. c 1 c 2 c 3 (100, 100) (105, 100, 98) c 4 (95, 105) (105, 100, 98) X b= 1 (secret bit) 10
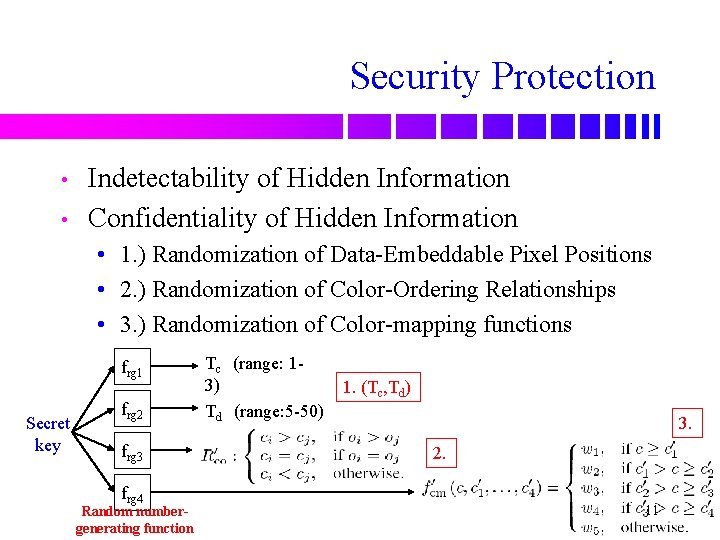
Security Protection • • Indetectability of Hidden Information Confidentiality of Hidden Information • 1. ) Randomization of Data-Embeddable Pixel Positions • 2. ) Randomization of Color-Ordering Relationships • 3. ) Randomization of Color-mapping functions frg 1 Secret key frg 2 frg 3 frg 4 Random numbergenerating function Tc (range: 13) Td (range: 5 -50) 1. (Tc, Td) 3. 2. 11
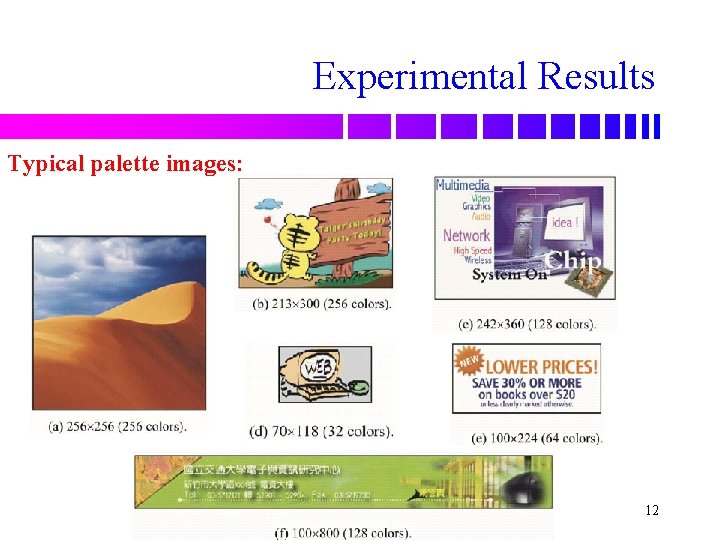
Experimental Results Typical palette images: 12
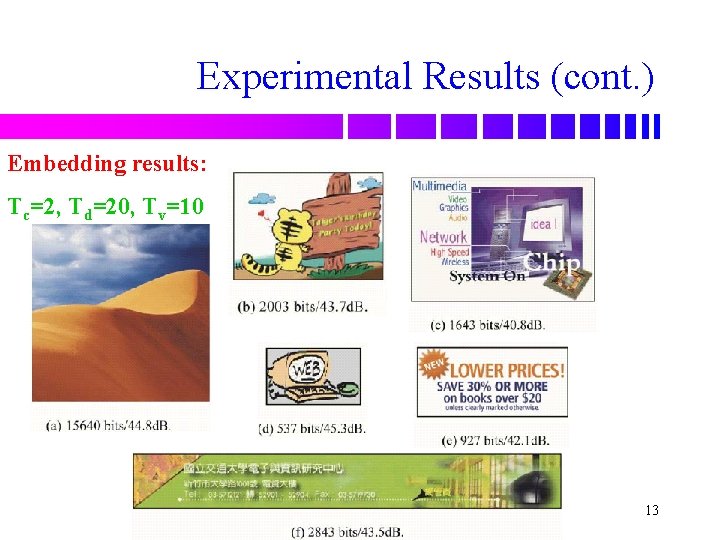
Experimental Results (cont. ) Embedding results: Tc=2, Td=20, Tv=10 13
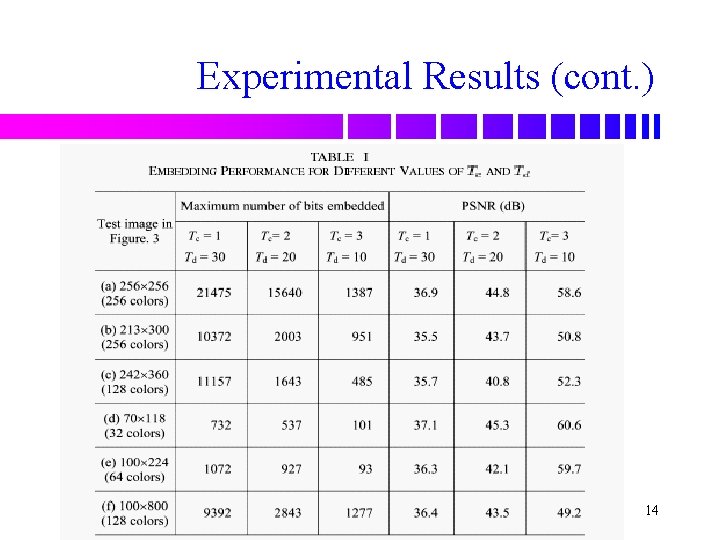
Experimental Results (cont. ) 14
Conclusions • • • Using the color-mapping function based on color-ordering relationship. To modify the color value lets the binary output of colormapping function is same as the secret bit. Using the optimal color from the color palette that has the least distortion. Spatial properties of the image content. Indetectability. Randomizing the parameters obtains good security protection. 15
- Slides: 15