ACOE 343 RealTime Embedded Processor Systems Dr Konstantinos
ACOE 343 - Real-Time Embedded Processor Systems Dr. Konstantinos Tatas Assistant Professor Office 116, Library building http: //staff. fit. ac. cy/com. tk
Course outline (1/5) • Programme of Studies: BSc in Computer Engineering, BSc in Computer Science • Name of the module: ACOE 343 - Real. Time Embedded Processor Systems • Target group: Computer Engineering – Computer Science students • Level of the unit: BSc – 6 th Semester • Entrance requirements: ACOE 201 • Number of ECTS credits: 6 2
Course outline (1/5) • Competences to be developed: – Produce efficient real-time designs using the latest technology of PIC 32 and 8051 -based microcontrollers and the state-of-art Texas Instruments TMS 320 C 64 x DSP processors. – Demonstrate real-time algorithmic design techniques for embedded applications using assembly and C/C++ programming, implementation, hardware debugging and measurement techniques using the available u. P and DSP boards. – Write realistic embedded system requirements 3 and specifications
Course outline (1/5) Course Description: • Embedded C/C++ and Assembly Languages: Embedded C and assembly for programming the 8051 -based microcontrollers. Coverage of C/C++ for programming DSPs. Real-Time Design Techniques. • 8051 -Based Microcontrollers: The MSC 121 x Development System, Real-Time Input and Output Applications, Architecture and ISA of the MSC 121 x microcontroller, Real-Time Embedded Ethernet Applications and Real-Time Data Acquisition Applications. • DSPs: The DSP Development System, Real-Time Input and Output Applications with the DSK, Architecture and ISA of the C 64 x Processor, Fixed-Point Considerations. • DSP Techniques: FIR and IIR filter Applications. FFT, digital modulation techniques and Applications. • Laboratory Work: Individual or small group experiments based on using a variety of EDA tools for programming, debugging and testing the microcontroller and DSP boards. 4
Course outline (1/5) • Textbooks: – Hermann Kopetz, "Real-Time Systems: Design Principles for Distributed Embedded Applications", Springer, 2011. – Peter Hintenaus, "Engineering Embedded Systems: Physics, Programs, Circuits", Springer, 2015 – http: //link. springer. com/book/10. 1007%2 F 978 -3 -319 -10680 -9 – Marilyn Wolf, “Computers as components: Principles of embedded computing design”, 3 rd edition, Morgan Kaufmann Publishers, 2012 • References: – M. Margolis, Arduino Cookbook, O’Reilly – T. Noergaard, Embedded Systems Architecture: A Comprehensive Guide for Engineers and Programmers, Newnes, 2005. – B. De. Muth, Designing Embedded Internet Devices, Newnes, 2002. – L. Edwards, Embedded System Design on a Shoestring, Newnes, 2003. • Course webpage: – http: //staff. fit. ac. cy/com. tk/ACOE 343. html 5
Course outline (1/5) • Assessment: – Final: 40% – Mid-term Exams: 10% – Laboratory Work: 30% – Assignment/Group project: 15% – Quizzes: 5% 6
Mid-term exams (40%) • Microcontrollers: – Multiple choice questions – Small programs • Assembly/C/either • DSPs: – Multiple choice questions – Small programs • Mostly C 7
Laboratory work (20%) • Small group experiments with the Chip. Kit MAX 32 and u. C 32 PIC-based Arduino • Deliverables: – Lab report (with source code)!!! • Assessment: – Active participation: 40% – Methodology/Source code: 30% – Board Testing: 20% – Presentation: 10% 8
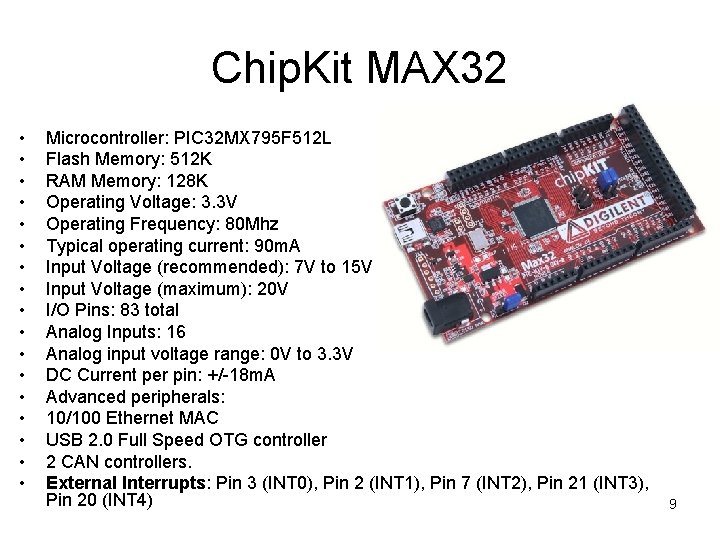
Chip. Kit MAX 32 • • • • • Microcontroller: PIC 32 MX 795 F 512 L Flash Memory: 512 K RAM Memory: 128 K Operating Voltage: 3. 3 V Operating Frequency: 80 Mhz Typical operating current: 90 m. A Input Voltage (recommended): 7 V to 15 V Input Voltage (maximum): 20 V I/O Pins: 83 total Analog Inputs: 16 Analog input voltage range: 0 V to 3. 3 V DC Current per pin: +/-18 m. A Advanced peripherals: 10/100 Ethernet MAC USB 2. 0 Full Speed OTG controller 2 CAN controllers. External Interrupts: Pin 3 (INT 0), Pin 2 (INT 1), Pin 7 (INT 2), Pin 21 (INT 3), Pin 20 (INT 4) 9
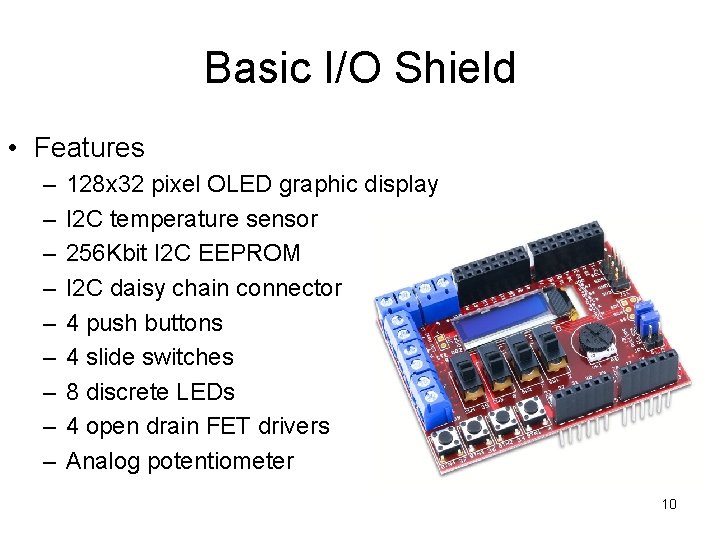
Basic I/O Shield • Features – – – – – 128 x 32 pixel OLED graphic display I 2 C temperature sensor 256 Kbit I 2 C EEPROM I 2 C daisy chain connector 4 push buttons 4 slide switches 8 discrete LEDs 4 open drain FET drivers Analog potentiometer 10
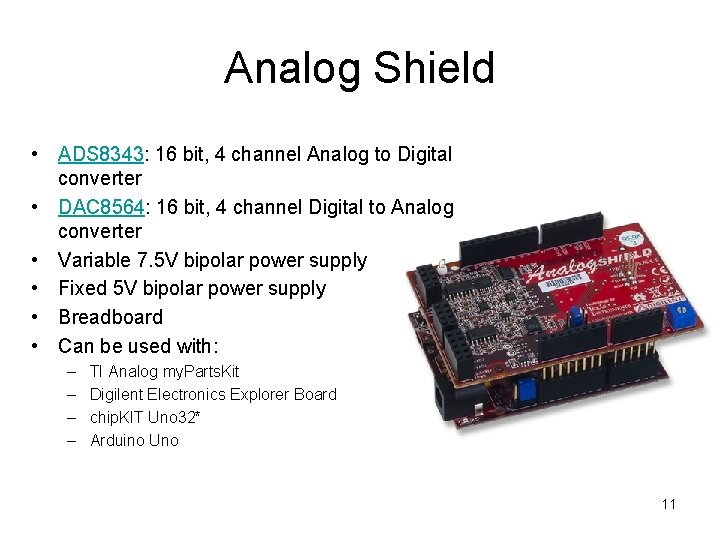
Analog Shield • ADS 8343: 16 bit, 4 channel Analog to Digital converter • DAC 8564: 16 bit, 4 channel Digital to Analog converter • Variable 7. 5 V bipolar power supply • Fixed 5 V bipolar power supply • Breadboard • Can be used with: – – TI Analog my. Parts. Kit Digilent Electronics Explorer Board chip. KIT Uno 32* Arduino Uno 11
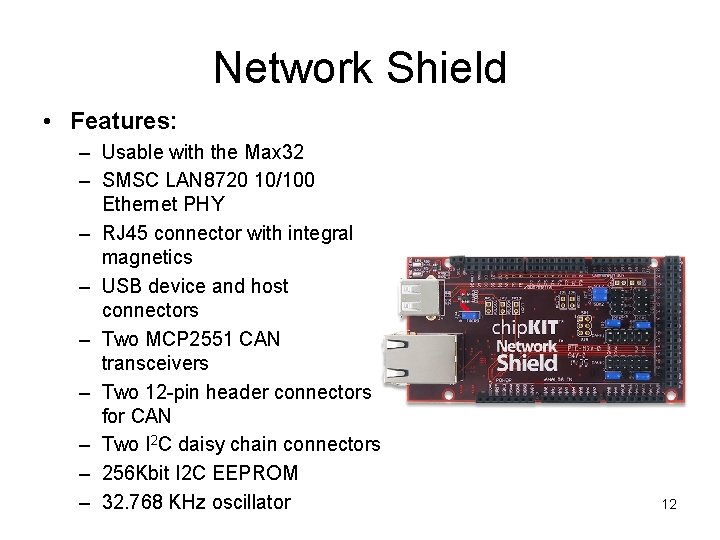
Network Shield • Features: – Usable with the Max 32 – SMSC LAN 8720 10/100 Ethernet PHY – RJ 45 connector with integral magnetics – USB device and host connectors – Two MCP 2551 CAN transceivers – Two 12 -pin header connectors for CAN – Two I 2 C daisy chain connectors – 256 Kbit I 2 C EEPROM – 32. 768 KHz oscillator 12
Assignment/Group Project (15%) • 8051 emulator or Chipkit MAX 32 application implementation • Done in small groups • Different application for each group 13
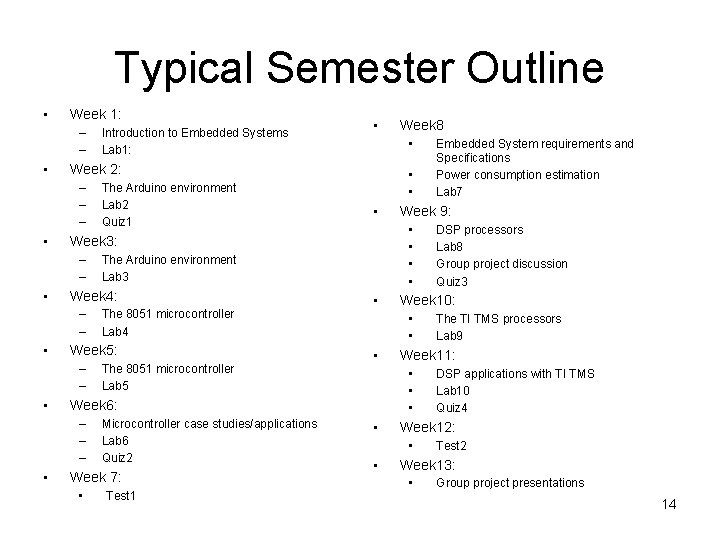
Typical Semester Outline • Week 1: – – • • The 8051 microcontroller Lab 5 • Microcontroller case studies/applications Lab 6 Quiz 2 Week 7: • Test 1 DSP applications with TI TMS Lab 10 Quiz 4 Week 12: • • The TI TMS processors Lab 9 Week 11: • • DSP processors Lab 8 Group project discussion Quiz 3 Week 10: • • • Embedded System requirements and Specifications Power consumption estimation Lab 7 Week 9: • • Week 6: – – – • The 8051 microcontroller Lab 4 Week 5: – – • • • The Arduino environment Lab 3 Week 4: – – • The Arduino environment Lab 2 Quiz 1 Week 8 • Week 3: – – • • Week 2: – – – • Introduction to Embedded Systems Lab 1: Test 2 Week 13: • Group project presentations 14
Introduction to Embedded Systems
Outline • What is an embedded system • Characteristics and Classification of Embedded Systems • Systems-on-a-Chip • Distributed Systems • Internet-of-Things • Embedded Systems Design Challenges • Real-Time Embedded Systems 16
Microprocessors for Embedded systems • Computing systems are everywhere • Most of us think of “desktop” computers – – PC’s Laptops Mainframes Servers • But there’s another type of computing system – Far more common. . . 17
Embedded systems overview • Embedded computing systems – Computing systems embedded Computers are in here. . . within electronic devices and here. . . – Hard to define. Nearly and even here. . . computing system other than a desktop computer – Billions of units produced yearly, versus millions of desktop units – Perhaps 50 per household and per Lots more of these, automobile though they cost a lot less each. – A lot more programming is done for embedded systems than 18 desktop computers or servers
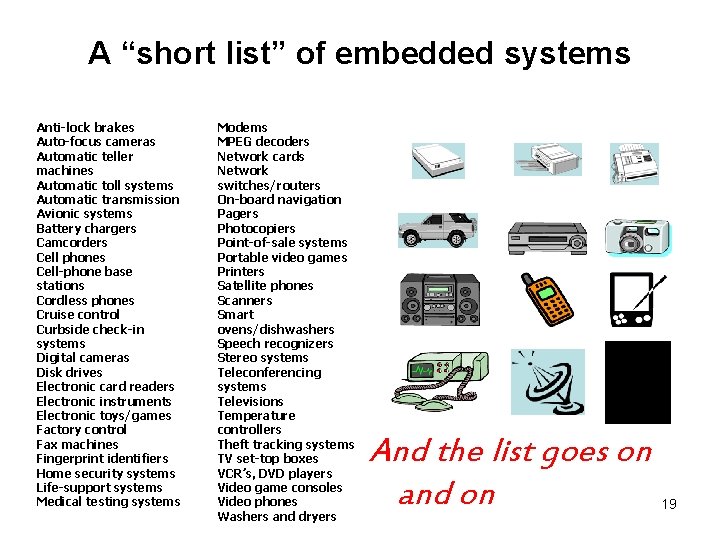
A “short list” of embedded systems Anti-lock brakes Auto-focus cameras Automatic teller machines Automatic toll systems Automatic transmission Avionic systems Battery chargers Camcorders Cell phones Cell-phone base stations Cordless phones Cruise control Curbside check-in systems Digital cameras Disk drives Electronic card readers Electronic instruments Electronic toys/games Factory control Fax machines Fingerprint identifiers Home security systems Life-support systems Medical testing systems Modems MPEG decoders Network cards Network switches/routers On-board navigation Pagers Photocopiers Point-of-sale systems Portable video games Printers Satellite phones Scanners Smart ovens/dishwashers Speech recognizers Stereo systems Teleconferencing systems Televisions Temperature controllers Theft tracking systems TV set-top boxes VCR’s, DVD players Video game consoles Video phones Washers and dryers And the list goes on and on 19
Definitions • Broad definition: – Any computer system that is not a generalpurpose computer • That would include robots, and all portable devices • Narrow definition: – A computer system (software and hardware) that interacts with its physical environment, mainly without human intervention • That would exclude printers, modems, portable devices such as dvd and mp 3 players, etc. 20
Some common characteristics of embedded systems • Single-functioned – Executes a single program, repeatedly • Tightly-constrained – Low cost, low power, small, fast, etc. • Reactive and real-time – Continually reacts to changes in the system’s environment – Must compute certain results in real-time without delay 21
Considerations in embedded system design • An embedded system receives input from its environment through sensors, processes this input and acts upon its environment through actuators • Besides the usual software and hardware design issues the embedded system designer must consider the properties of the sensors and actuators and the environment itself • The ultimate test of an embedded systems are the laws of physics 22
Classification of Embedded Systems • Centralized vs distributed • Real-time vs non real-time – Hard deadline • Failsafe • Fail-operational – Soft deadline – Firm deadline • Battery powered vs mains powered • System-on-Chip vs discrete element 23
What is real-time? Is there any other kind? • A real-time computer system is a computer system where the correctness of the system behavior depends not only on the logical results of the computations, but also on the physical time when these results are produced. • By system behavior we mean the sequence of outputs in time of a system. 24
Real-time means reactive A real-time computer system must react to stimuli from its environment The instant when a result must be produced is called a deadline. If a result has utility even after the deadline has passed, the deadline is classified as soft, otherwise it is firm. If severe consequences could result if a firm deadline is missed, the deadline is called hard. Example: Consider a traffic signal at a road before a railway crossing. If the traffic signal does not change to red before the train arrives, an accident could result. 25
Fail-Safe hard-deadline RT systems • If a safe state can be identified and quickly reached upon the occurrence of a failure, then we call the system fail-safe. • Failsafeness is a characteristic of the controlled object, not the computer system. – In case a failure is detected in a railway signaling system, it is possible to set all signals to red and thus stop all the trains in order to bring the system to a safe state. • In failsafe applications the computer system must have a high error-detection coverage. • Often a watchdog, is required to monitor the operation of the computer system and put it in safe state. 26
Fail-Operational hard-deadline RT systems • In fail-operational applications, threre is no safe state – a flight control system aboard an airplane. • The computer system must remain operational and provide a minimal level of service even in the case of a failure to avoid a catastrophe 27
• Are the following embedded systems? If yes, classify them. Which characteristics of an embedded system do they have or do not have? – Printer – DVD player – Mobile phone – Tablet – Netbook/laptop 28
Typical Embedded System Components • Sensors: Allow the system to “read” the environment • Processing Elements: Control of the embedded system • Actuators: Allow the system to act on its environment • Network Connection: Local or internet, allowing exchange of information 29
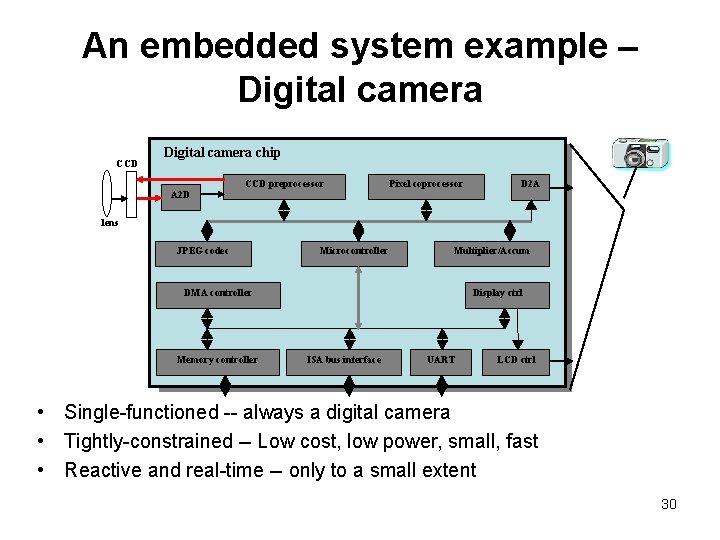
An embedded system example – Digital camera CCD Digital camera chip A 2 D CCD preprocessor Pixel coprocessor D 2 A lens JPEG codec Microcontroller Multiplier/Accum DMA controller Memory controller Display ctrl ISA bus interface UART LCD ctrl • Single-functioned -- always a digital camera • Tightly-constrained -- Low cost, low power, small, fast • Reactive and real-time -- only to a small extent 30
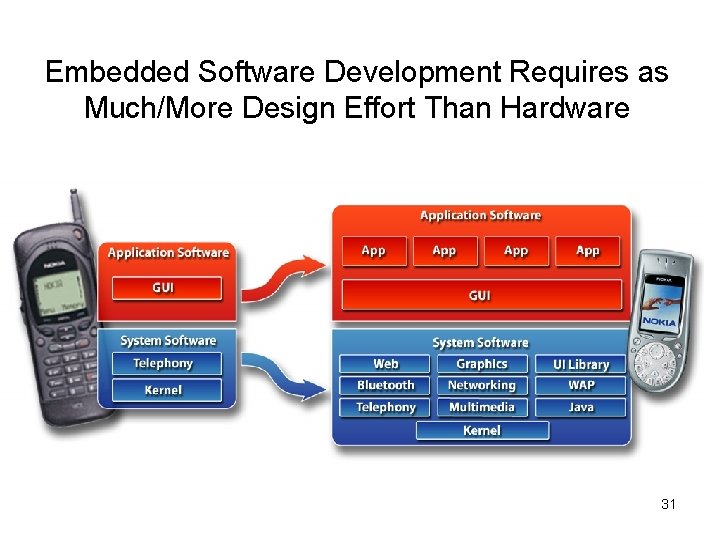
Embedded Software Development Requires as Much/More Design Effort Than Hardware 31
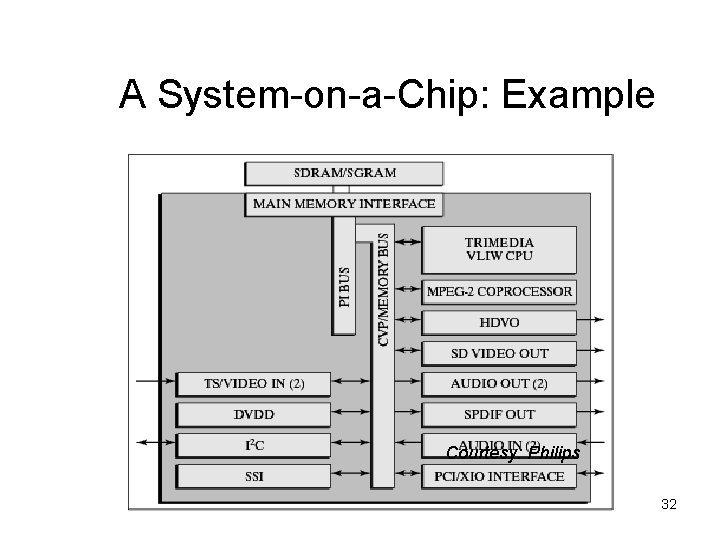
A System-on-a-Chip: Example Courtesy: Philips 32
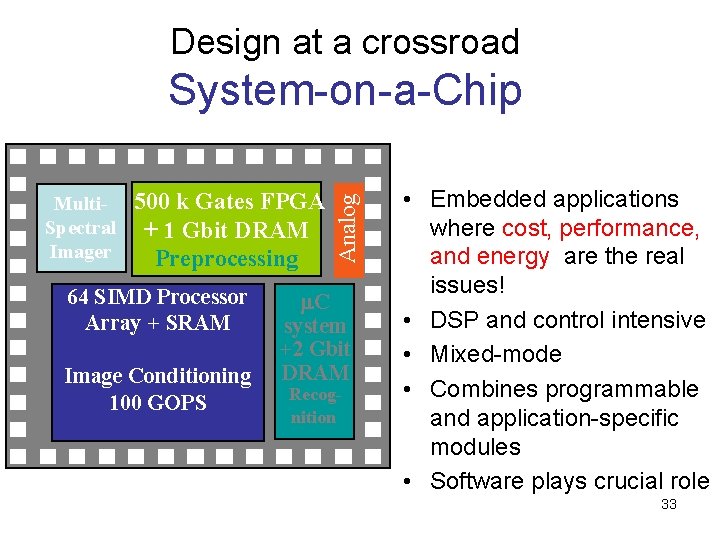
Design at a crossroad Multi- 500 k Gates FPGA Spectral + 1 Gbit DRAM Imager Preprocessing 64 SIMD Processor Array + SRAM Image Conditioning 100 GOPS Analog System-on-a-Chip m. C system +2 Gbit DRAM Recognition • Embedded applications where cost, performance, and energy are the real issues! • DSP and control intensive • Mixed-mode • Combines programmable and application-specific modules • Software plays crucial role 33
The Future of Embedded Systems • In the past an embedded system was more or less isolated • In the past decade Wireless Sensor Networks have changed that • Today embedded systems + internet connection = Internet of Things ! • Near future: Embedded systems + internet + mobile devices + cloud computing + artificial intelligence + ? = smart 34 environment
Io. T forecasts • Global Internet of Things (Io. T) market reached USD 598. 2 Billion in 2015 • is expected to reach USD 724. 2 Billion by 2023 • the market is projected to register a CAGR of 13. 2% • The number of connected Io. T (Internet of Things) devices, sensors and actuators will reach over 46 billion in 2021 35
Io. T • Embedded system with internet connection • Not quite as simple as it sounds • Increased need for security • Safety issues • Direct machine to machine (M 2 M) communication 36
Case studies of distributed embedded systems Dr. Konstantinos Tatas
Outline • Case study 1: RFID • Case study 2: Wireless sensor networks • Case study 3: Internet of things 38
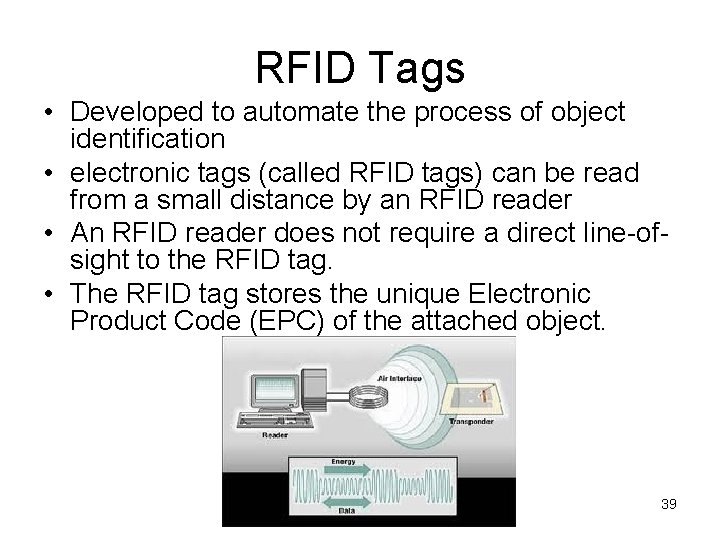
RFID Tags • Developed to automate the process of object identification • electronic tags (called RFID tags) can be read from a small distance by an RFID reader • An RFID reader does not require a direct line-ofsight to the RFID tag. • The RFID tag stores the unique Electronic Product Code (EPC) of the attached object. 39
RFID Tag dimensions • Since an RFID tag has to be attached to every object, the cost of an RFID tag is a major issue. • RFID tags come in various shapes and sizes and continue to decrease in size • RFID tags are implantable and implants have been approved in humans as well as animals. 40
RFID Reader • The RFID reader can act as a gateway to the Internet and transmit the object identity, together with the read-time and the object location (i. e. , the location of the reader) to a remote computer system that manages a large database. • It is thus possible to track objects in real-time • Applications: toll gates, hospitals and large organizations, public transportation systems, tracking of animals, libraries 41
Electronic product code • A typical EPC has a length of 96 bits and contains the following fields: – Header (8 bits): defines the type and the length of all subsequent fields. – EPC Manager (28 bits): specifies the entity (most often the manufacturer) that assigns the object class and serial number in the remaining two fields. – Object Class (24 bits): specifies a class of objects (similar to the optical bar code). – Object Identification Number (36 bits): contains the serial number within theobject class. • The EPC is unique product identification, but does not reveal anything about the properties of the product. • Two things that have the same properties, but are designed by two different manufacturers, will have completely different EPCs. 42
Passive RFID tags • Passive RFID Tags. No power supply. They get the power needed for their operation from energy harvested out of the electric field that is beamed on them by the RFID reader. The energy required to operate a passive tag of the latest generation is below 30 m. W and the cost of such a tag is below 5 ¢. • Due to the low level of the available power and the cost pressure on the production of RFID tags, the communication protocols of passive RFID tags do not conform to the standard Internet protocols. Specially designed communication protocols between the RFID tag and the RFID reader that consider the constraints of passive RFID tags have been standardized by the ISO (e. g. , ISO 18000 -6 C also known as the EPC global Gen 2) and are supported by a number of manufacturers. 43
Active RFID tags • Active RFID Tags – have their own on-board power supply – The lifetime of an active tag is limited by the lifetime of the battery – typically in the order of a year. • Active tags can transmit and receive over a longer distance – typically in the order of hundreds of meters, – can have sensors to monitor their environment – sometimes support standard Internet communication protocols. • An active RFID tag resembles a small embedded system – More expensive 44
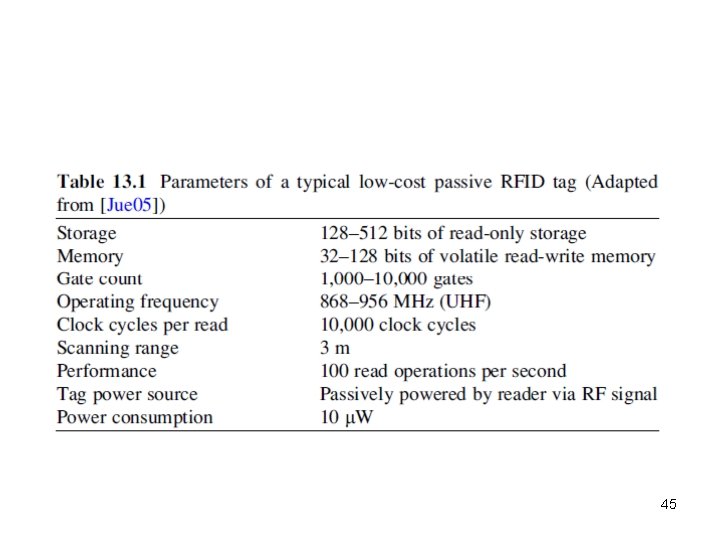
45
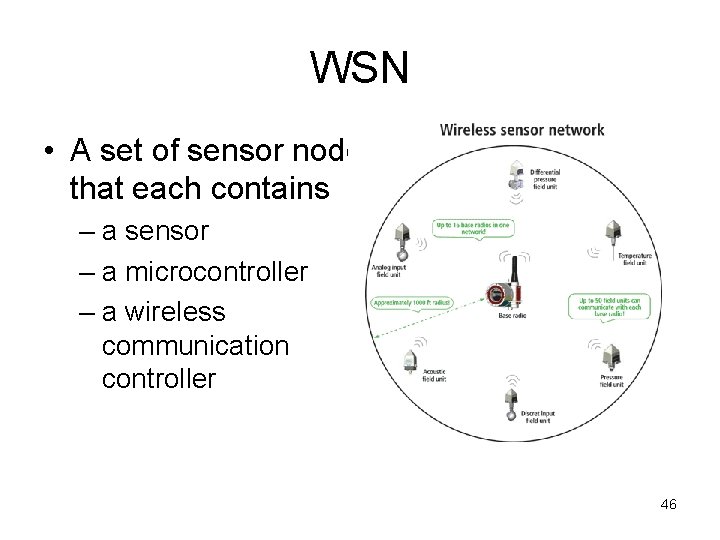
WSN • A set of sensor nodes that each contains – a sensor – a microcontroller – a wireless communication controller 46
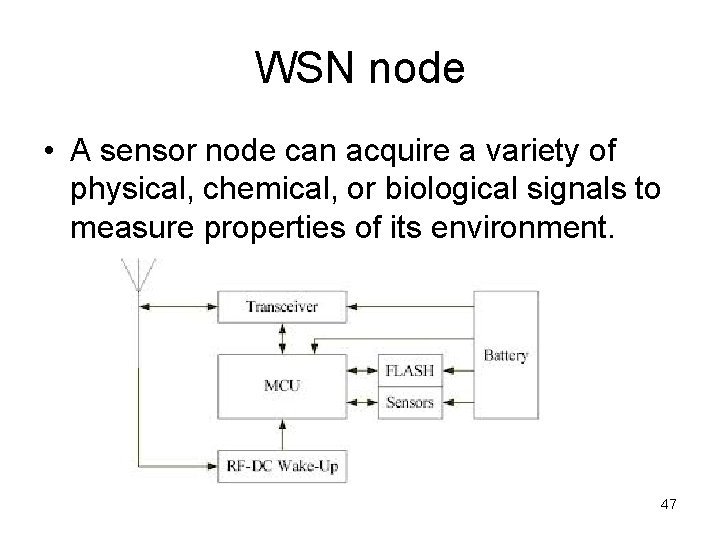
WSN node • A sensor node can acquire a variety of physical, chemical, or biological signals to measure properties of its environment. 47
WSN node constraints • Sensor nodes are resource constrained. – They are powered either by a small battery or by energy harvested from its environment, – have limited computational power, a small memory, and constrained communication capabilities. 48
WSN deployment and operation • a number (from few tens to millions) of sensor nodes are deployed, either systematically or randomly, in a sensor field to form an ad hoc self -organizing network • The WSN collects data about the targeted phenomenon and transmits the data via an adhoc multi-hop communication channel to one or more base stations that can be connected to the Internet. 49
WSN function • Phase 1: detect neighbors and establish communication • Phase 2: learn about – the arrangement in which the nodes are connected to each other, – the topology of nodes – build up ad-hoc multi-hop communication channels to a base station • In case of the failure of an active node, it must reconfigure the network • Applications: – – – remote environment monitoring, surveillance, medical applications, ambient intelligence, military • The utility of a wireless sensor network is in the collective emergent intelligence of all active sensor nodes, not the contribution of any particular node. 50
Primary concern for WSN: energy • A WSN is operational as long as a minimum number of nodes is active and the connectivity of the active nodes to one of the base stations is maintained. • In battery-powered sensor networks, the lifetime of the network depends on the energy capacity of the batteries and the power-consumption of a node. • When a sensor node has depleted its energy supply, it will cease to function and cannot forward messages to its neighbors any more. • The design of the nodes, the communication protocols, and the design of the system and application software for sensor networks are primarily determined by this quest for energy efficiency and low cost. 51
WSN + RFID = the future? • RFID infrastructure for the interconnection of autonomous low-cost RFID-based sensor nodes has been proposed • nodes operate without a battery and harvest the energy either from the environment or the electromagnetic radiation emitted by the RFID reader. • Potential for long-lasting, low-cost ubiquitous sensor nodes that may revolutionize many embedded applications. 52
Io. T component: Smart object • A smart object is a cyber-physical system or an embedded system, consisting of a thing (the physical entity) and a component (the computer) that processes the sensor data and supports a wireless communication link to the Internet. – Example: smart refrigerator keeps track of the availability and expiry date of food items and places orders 53
Io. T issues • The novelty of the Io. T is not in the functional capability of a smart object • Novelty exists in the expected size of billions or even trillions of smart objects that bring about novel technical and societal issues that are related to size. • issues are: – authentic identification of a smart object, – autonomic management and self-organization of networks of smart objects, – diagnostics and maintenance, – intrusion of privacy • Safety issues – Autonomous mobile robots and self-driving cars 54
Key technologies for Io. T • low-power wireless communication: no need of a physical connection. • GPS: makes a smart object location- and time-aware 55
Smart object categories • Goal: an autonomic smart object that – has access to a domain specific knowledge base – is empowered with reasoning capabilities to orient itself in the selected application domain. • Based on the capability level of a smart object it can be – activity aware – policy aware – process aware 56
Ultimate vision: smart planet • everyday things around us with an identity in cyberspace capable of acquiring information and intelligence • the world economy and support systems will operate more smoothly and efficiently 57
Social and legal issues in Io. T • But the life of the average citizen will also be affected by changing the relation of power between those that have access to the acquired information and can control the information and those that do not. • Io. T devices can be hacked with significant dangers to safety and property 58
Io. T drivers • The Io. T should extend the interoperability of the internet to the universe of heterogeneous smart objects. • Iot must establish a uniform access pattern to things in the physical world. 59
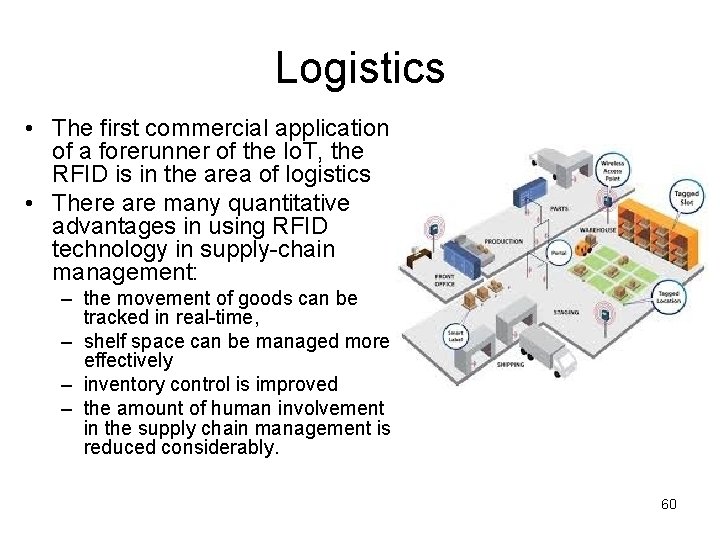
Logistics • The first commercial application of a forerunner of the Io. T, the RFID is in the area of logistics • There are many quantitative advantages in using RFID technology in supply-chain management: – the movement of goods can be tracked in real-time, – shelf space can be managed more effectively – inventory control is improved – the amount of human involvement in the supply chain management is reduced considerably. 60
Energy savings • Already today, embedded systems contribute to energy savings in many different sectors of our economy and our life. – increased fuel efficiency of automotive engines, – improved energy-efficiency of household appliances, – reduced loss in energy conversion • The future: of Io. T devices opens many new opportunities for energy savings: – Smart buildings: individual climate and lighting control in residential buildings – Smart grids: reduced energy loss in transmission by the installation of smart grids, – Smart meters: better coordination of energy supply and energy demand • Other energy savings: – Physical meetings replaced by virtual meetings – delivery of information goods such as the daily paper, music, and videos by the Internet 61
Security and safety • Automated Io. T based access control systems to buildings and homes • Io. T-based surveillance of public places • Smart passports and Io. T based identifications (e. g. , a smart key to access a hotel room or a smart ski lift ticket) • Car-to-car and car-to-infrastructure communication will alert the driver of dangerous traffic scenarios 62
Industrial • computerized observation and monitoring of industrial equipment – reduces maintenance cost – improves the safety in the plant • A smart object can monitor its own operation and call for preventive or spontaneous maintenance in case a part wears out or a physical fault is diagnosed • Automated fault-diagnosis and simple maintenance are absolutely essential prerequisites for the wide deployment of the Io. T technology in the domain of ambient intelligence. 63
Medical • The wide deployment of Io. T technology in the medical domain is anticipated. – Health monitoring (heart rate, blood pressure, etc. ) – precise control of drug delivery by a smart implant • Body area networks that are part of the clothing can monitor the behavior of impaired persons and send out alarm messages if an emergency is developing. • Smart labels on drugs can help a patient to take the right medication at the right time and enforce drug compliance. • Example: A heart pacemaker can transmit important data via a Bluetooth link to a mobile phone that is carried in the shirt pocket. The mobile phone can analyze the data and call a doctor in case an emergency develops. 64
Technical issues: internet integration • Guaranteeing the safety and information security of Io. T-based systems is considered to be a difficult task. • Many smart objects will be protected from general Internet access by a tight firewall to avoid that an adversary can acquire control of a smart object. 65
Naming and identification • A well-thought-out naming architecture in order to be able to identify a smart object and to establish an access path to the object is essential. • Isolated Objects. The following three different object names have to be distinguished when we refer to the simple case of an isolated object: – Unique object identifier (UID) refers to the physical identity of a specific object. – The Electronic Product Code (EPC) of the RFID community is such a UID. – Object type name refers to a class of objects that ideally have the same properties. – Object role name. In a given use context, an object plays a specific role that is denoted by the object role name. 66
Composite object naming • Composite Objects. Whenever a number of objects are integrated to form a composite object, a new whole, i. e. , new object is created that has an emerging identity that goes beyond the identities of the constituent objects. • The composite object resembles a new concept (see Sect. 2. 2. 1) that requires a new name. 67
Io. T vs cloud computing • Smart objects that have access to the Internet can take advantage of services that are offered by the cloud • The division of work between a smart object and the cloud will be determined, to a considerable degree, by privacy and energy considerations • If the energy required to execute a task locally is larger than the energy required to send the task parameters to a server in the cloud, then the task is a candidate for remote processing. • However, there are other aspects that influence the decision about work distribution: autonomy of the smart object, response time, reliability, and security. 68
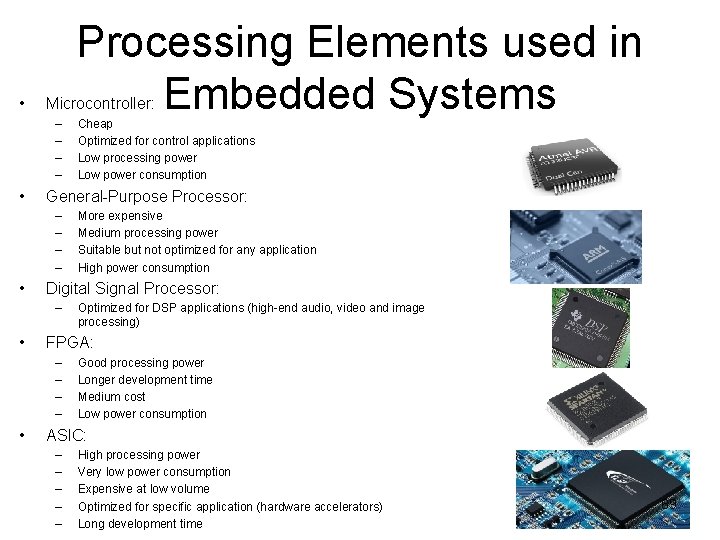
• Microcontroller: – – • Optimized for DSP applications (high-end audio, video and image processing) FPGA: – – • More expensive Medium processing power Suitable but not optimized for any application High power consumption Digital Signal Processor: – • Cheap Optimized for control applications Low processing power Low power consumption General-Purpose Processor: – – • Processing Elements used in Embedded Systems Good processing power Longer development time Medium cost Low power consumption ASIC: – – – High processing power Very low power consumption Expensive at low volume Optimized for specific application (hardware accelerators) Long development time 69
Design challenge – optimizing design metrics • Obvious design goal: – Construct an implementation with desired functionality • Key design challenge: – Simultaneously optimize numerous design metrics • Design metric – A measurable feature of a system’s implementation – Optimizing design metrics is a key challenge 70
Design challenge – optimizing design metrics • Common metrics – Unit cost: the monetary cost of manufacturing each copy of the system, excluding NRE cost – NRE cost (Non-Recurring Engineering cost): The one-time monetary cost of designing the system – – Size: the physical space required by the system Performance: the execution time or throughput of the system Power: the amount of power consumed by the system Flexibility: the ability to change the functionality of the system without incurring heavy NRE cost 71
Design challenge – optimizing design metrics • Common metrics (continued) – Time-to-prototype: the time needed to build a working version of the system – Time-to-market: the time required to develop a system to the point that it can be released and sold to customers – Maintainability: the ability to modify the system after its initial release – Correctness, safety, many more 72
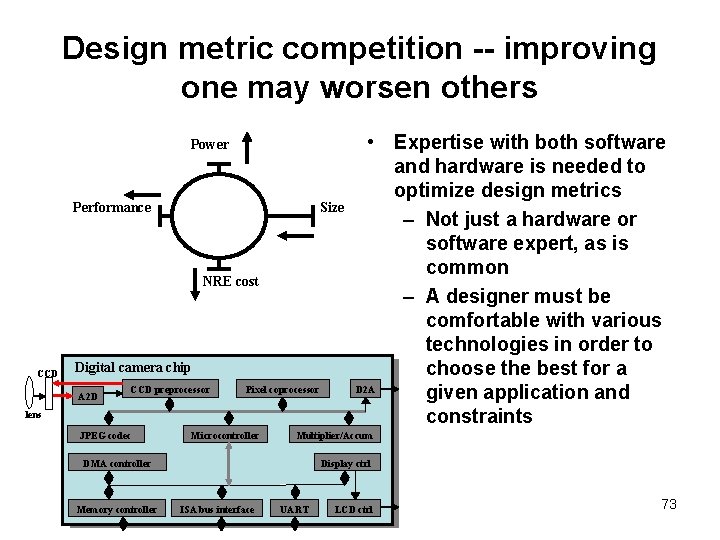
Design metric competition -- improving one may worsen others Power Performance Size NRE cost CCD Digital camera chip A 2 D CCD preprocessor Pixel coprocessor lens JPEG codec Microcontroller Multiplier/Accum DMA controller Memory controller • Expertise with both software and hardware is needed to optimize design metrics – Not just a hardware or software expert, as is common – A designer must be comfortable with various technologies in order to choose the best for a D 2 A given application and constraints Display ctrl ISA bus interface UART LCD ctrl 73
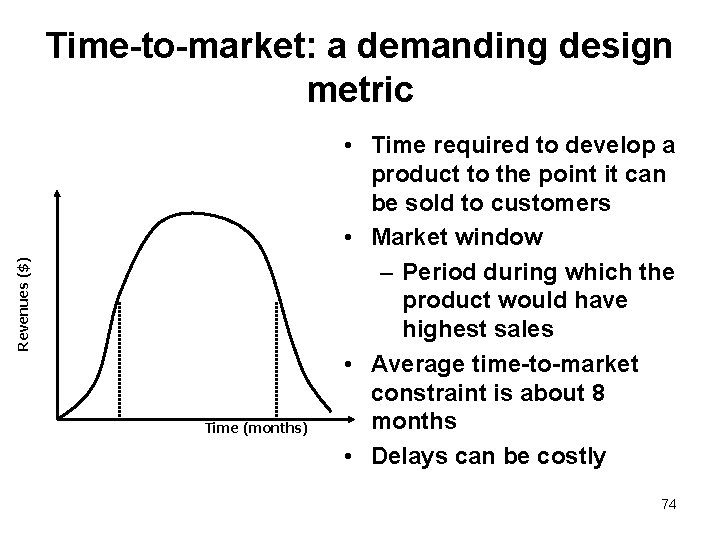
Revenues ($) Time-to-market: a demanding design metric Time (months) • Time required to develop a product to the point it can be sold to customers • Market window – Period during which the product would have highest sales • Average time-to-market constraint is about 8 months • Delays can be costly 74
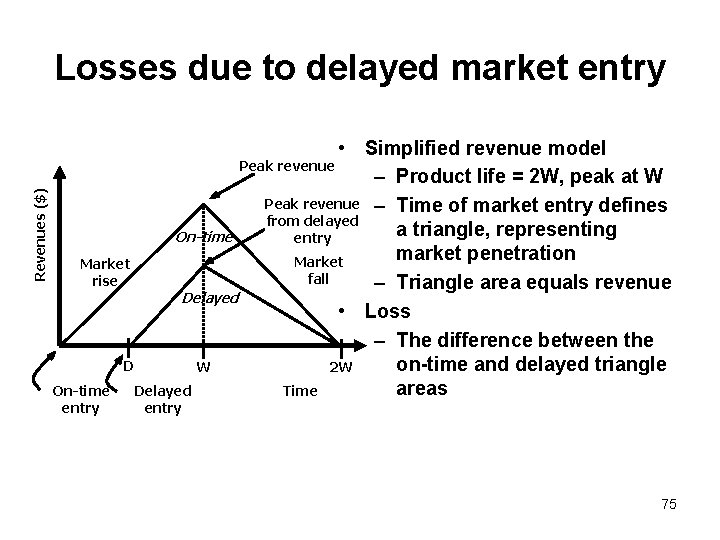
Revenues ($) Losses due to delayed market entry • Simplified revenue model Peak revenue – Product life = 2 W, peak at W Peak revenue – Time of market entry defines from delayed a triangle, representing On-time entry market penetration Market fall rise – Triangle area equals revenue Delayed • Loss – The difference between the on-time and delayed triangle D W 2 W areas On-time Delayed Time entry 75
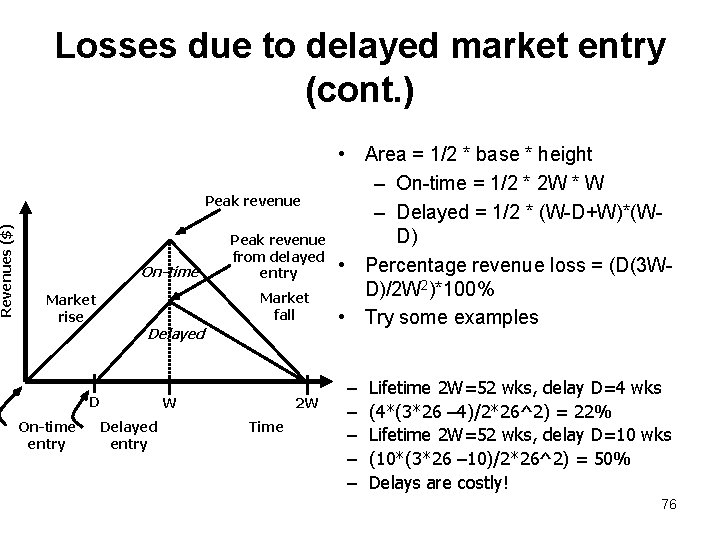
Revenues ($) Losses due to delayed market entry (cont. ) Peak revenue On-time Market fall Market rise Delayed D On-time entry Peak revenue from delayed entry Delayed entry W 2 W Time • Area = 1/2 * base * height – On-time = 1/2 * 2 W * W – Delayed = 1/2 * (W-D+W)*(WD) • Percentage revenue loss = (D(3 WD)/2 W 2)*100% • Try some examples – – – Lifetime 2 W=52 wks, delay D=4 wks (4*(3*26 – 4)/2*26^2) = 22% Lifetime 2 W=52 wks, delay D=10 wks (10*(3*26 – 10)/2*26^2) = 50% Delays are costly! 76
Real-time (reactive) systems • Systems that are bound by a real-time constraint (“deadline”) in their operation • If the deadline is not met it is usually considered a system failure, even if the output is eventually correct • Deadlines are usually relative to an event • Hard deadlines: Anti-lock brakes, • Soft deadlines: Digital video • Not the same as high-performance systems, because often running faster than real-time requirement is not necessary or desired 77
Real-time constraints • • te + to < tc te: execution time to: overhead time tc: constraint time 78
Example • Assuming a real-time system that processes samples at a f= 10 MHz sampling rate, and a to= 20 ns, select the most appropriate implementation among the following: – A processor running at 500 MHz, requiring 100 cycles at a cost of 50$ – An FPGA running at 200 MHz, requiring 10 cycles at a cost of 60$ – A DSP running at 500 MHz, requiring 20 cycles at a cost of 100$ – An ASIC running at 2 GHz, requiring 20 cycles at a cost of 500$ 79
- Slides: 79