ACES VALUE ADDED Technology Bridge Vendor Agnostic Understanding
ACES VALUE ADDED • Technology Bridge • Vendor Agnostic • Understanding of multiple tools • Architecture & Design – ACES built and deployed the first C 2 C • Resource Allocation • Minimum engineering resources understood for maximum output • Forescout Subject Matter Experts (SME) • FSCEs with hundreds of diverse successful deployments across ALL industry types • Policy “Kung-Fu” Gurus – developers of Forescout policy templates • Risk-averse standard operating procedures • Broad Cybersecurity Experience • Wide range of industry experience from private and public sector • Familiarity with Do. D • OSD CIO (C 2 C Rapid Innovation Fund Design Effort) *EXCEPTIONAL CPARS* • NACCR • MCRC • ENAC / ENGEN
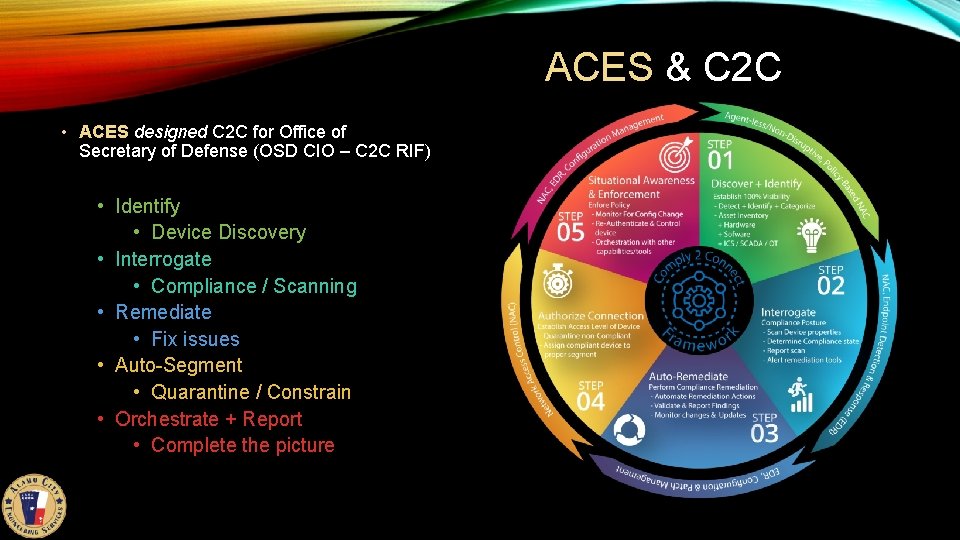
ACES & C 2 C • ACES designed C 2 C for Office of Secretary of Defense (OSD CIO – C 2 C RIF) • Identify • Device Discovery • Interrogate • Compliance / Scanning • Remediate • Fix issues • Auto-Segment • Quarantine / Constrain • Orchestrate + Report • Complete the picture
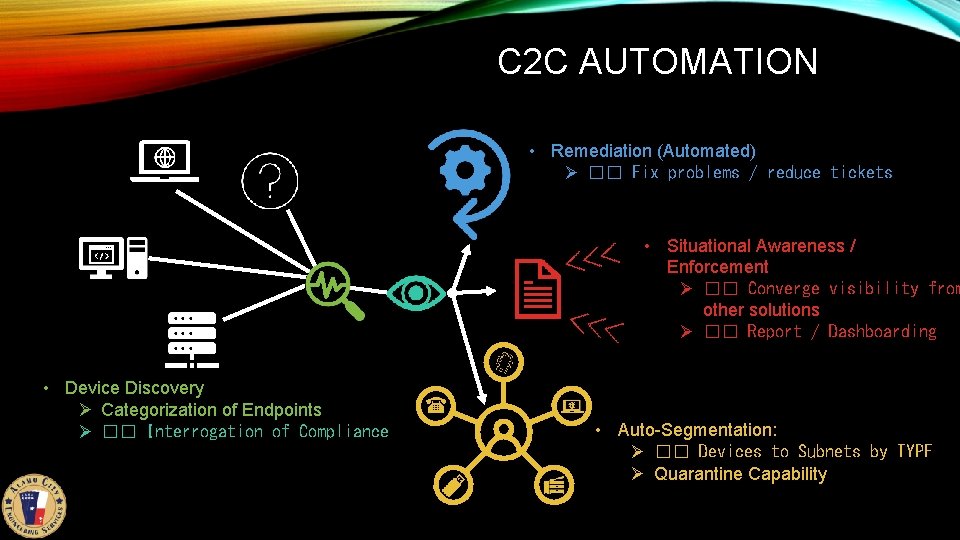
C 2 C AUTOMATION • Remediation (Automated) Ø �� Fix problems / reduce tickets • Situational Awareness / Enforcement Ø �� Converge visibility from other solutions Ø �� Report / Dashboarding • Device Discovery Ø Categorization of Endpoints Ø �� Interrogation of Compliance • Auto-Segmentation: Ø �� Devices to Subnets by TYPE Ø Quarantine Capability
POLICY-BASED PLATFORM • Designed Policy Structure • Our engineers masterminded the earliest templates used at Forescout • Full understanding of workflow automation • Cross Functional Team collaboration • Additional input on policy based on enterprise and industry knowledge • Compressed integration efforts to produce a replicate-able format • “Tuning” – ongoing sustainment and training • Organic policy tuning and environment adaptation – networks change! • Outcome: standard and tailored workflow to achieve C 2 C and beyond
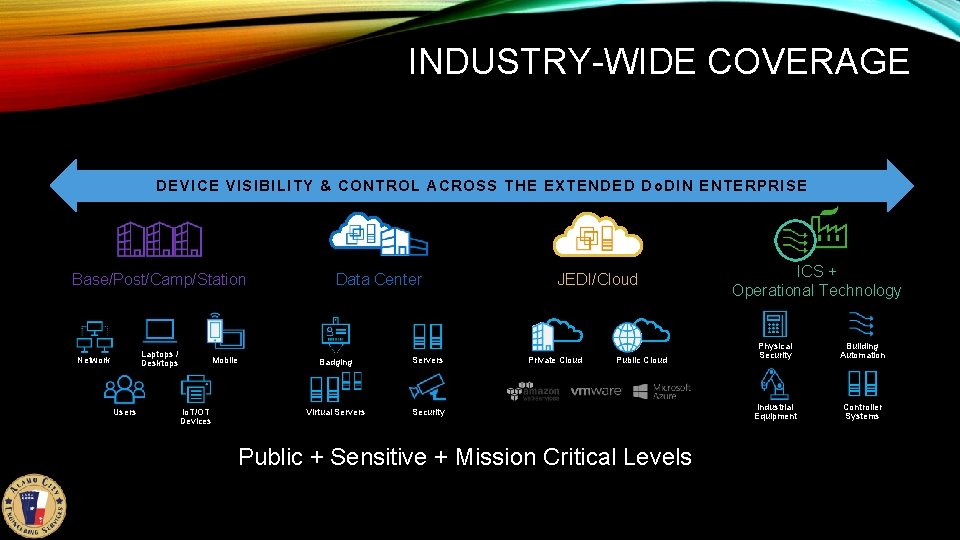
INDUSTRY-WIDE COVERAGE DEVICE VISIBILITY & CONTROL ACROSS THE EXTENDED Do. DIN ENTERPRISE Base/Post/Camp/Station Laptops / Desktops Network Users Mobile Io. T/OT Devices Data Center Badging Servers Virtual Servers Security JEDI/Cloud Private Cloud Public + Sensitive + Mission Critical Levels ICS + Operational Technology Physical Security Building Automation Industrial Equipment Controller Systems
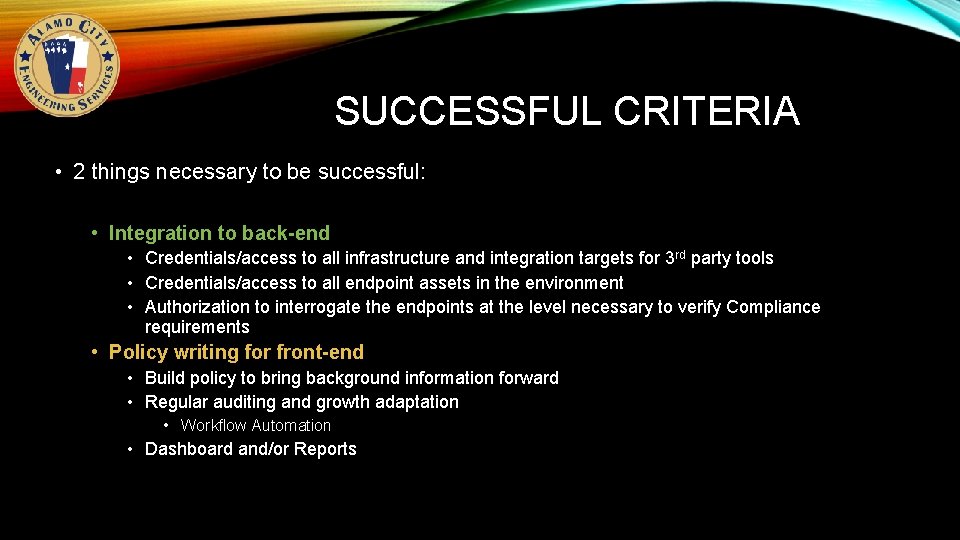
SUCCESSFUL CRITERIA • 2 things necessary to be successful: • Integration to back-end • Credentials/access to all infrastructure and integration targets for 3 rd party tools • Credentials/access to all endpoint assets in the environment • Authorization to interrogate the endpoints at the level necessary to verify Compliance requirements • Policy writing for front-end • Build policy to bring background information forward • Regular auditing and growth adaptation • Workflow Automation • Dashboard and/or Reports
QUESTIONS ?
- Slides: 7