Accounting Information Systems Essential Concepts and Applications Fourth
- Slides: 35
Accounting Information Systems: Essential Concepts and Applications Fourth Edition by Wilkinson, Cerullo, Raval, and Wong-On-Wing Chapter 7: Risk Exposures and the Internal Control Structure Slides Authored by Somnath Florida Atlantic University Bhattacharya, Ph. D.
Internal Control z Internal Control is a state that management strives to achieve to provide reasonable assurance that the firm’s objectives will be achieved z These controls encompass all the measures and practices that are used to counteract exposures to risks z The control framework is called the Internal Control Structure
Objectives of the Internal Control Structure z Promoting Effectiveness and Efficiency of Operations z Reliability of Financial Reporting z Safeguarding assets z Checking the accuracy and reliability of accounting data z Compliance with applicable laws and regulations z Encouraging adherence to prescribed managerial policies
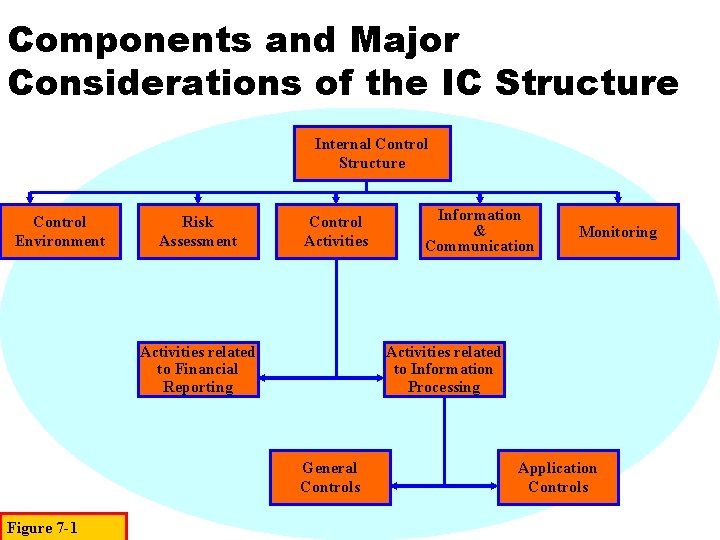
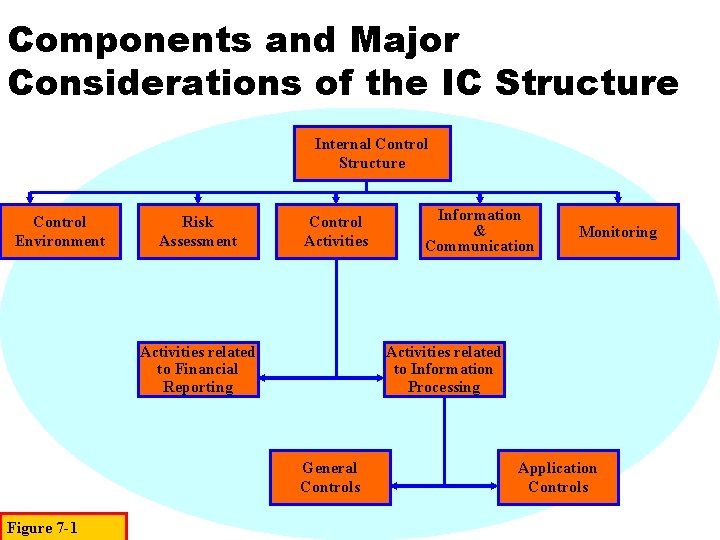
Components and Major Considerations of the IC Structure Internal Control Structure Control Environment Risk Assessment Control Activities related to Financial Reporting Monitoring Activities related to Information Processing General Controls Figure 7 -1 Information & Communication Application Controls
Control Environment z The Control Environment establishes the tone of a company, influencing the control consciousness of its employees z It is comprised of seven components: • • Management philosophy and operating style Integrity and ethical values Commitment to competence The Board of Directors and the Audit Committee Organizational Structure Assignment of authority and responsibility Human resources policies and practices External Influences
Highlights of CE Components - I z. Management Philosophy and Operating Style Figure 7 -2 y. Does management emphasize short-term profits and operating goals over long-term goals? y. Is management dominated by one or a few individuals? y. What type of business risks does management take and how are these risks managed? y. Is management conservative or aggressive toward selecting from available alternative accounting principles?
Highlights of CE Components - II z. Organization Structure y. Is an up-to-date organization chart prepared, showing the names of key personnel? y. Is the information systems function separated from incompatible functions? y. How is the accounting department organized? y. Is the internal audit function separate and distinct from accounting? y. Do subordinate managers report to more than one supervisor? Figure 7 -2 Continued
Highlights of CE Components - III z. Assignment of Authority and Responsibility y. Does the company prepare written employee job descriptions defining specific duties and reporting relationships? y. Is written approval required for changes made to information systems? y. Does the company clearly delineate employees and managers the boundaries of authority-responsibility relationships? y. Does the company properly delegate authority to employees and departments? Figure 7 -2 Continued
Highlights of CE Components - IV z. Human Resource Policies and Practices y. Are new personnel indoctrinated with respect to Internal Controls, Ethics Policies, and Corporate Code of Conduct? y. Is the company in compliance with the ADA? The EEOA? y. Are Grievance Procedures to manage conflict in force? y. Does the company maintain a sound Employee Relations program? y. Do employees work in a safe, healthy environment? y. Are Counseling Programs available to employees? y. Are proper Separation Programs in force for employees who leave the firm? y. Are critical employees Bonded? Figure 7 -2 Continued
Key Functions Performed by Audit Committees z. Establish an Internal Audit Department z. Review the Scope and Status of Audits z. Review Audit Findings with the Board and ensure that Management has taken proper action recommended in the Audit Report and Letter of Reportable Conditions z. Maintain a direct Line of Communication among the Board, Management, External and Internal Auditors, and periodically arrange Meetings among the parties Figure 7 -3
Key Functions Performed by Audit Committees z. Review the Audited Financial Statements with the Internal Auditors and the Board of Directors z. Require periodic Quality Reviews of the operations of the Internal Audit Departments to identify areas needing improvement z. Supervise special investigations, such as Fraud Investigations z. Assess the performance of Financial Management z. Require the Review of Compliance with Laws and Regulations and with Corporate Figure 7 -3 Codes of Conduct
Risk Assessment z. Top management must be directly involved in Business Risk Assessment. z. This involves the Identification and Analysis of Relevant Risks that may prevent the attainment of Company-wide Objectives and Objectives of Organizational Units and the formation of a plan to determine how to manage the risks.
Control Activities - I z Control Activities as related to Financial Reporting may be classified according to their intended uses in a system: • Preventive Controls block adverse events, such as errors or losses, from occurring • Detective Controls discover the occurrence of adverse events such as operational inefficiency • Corrective controls are designed to remedy problems discovered through detective controls • Security Measures are intended to provide adequate safeguards over access to and use of assets and data records
Control Activities - II z Control Activities relating to Information Processing may also be classified according to where they will be applied within the system • General controls are those controls that pertain to all activities involving a firm’s AIS and assets • Application controls relate to specific accounting tasks or transactions z The overall trend seems to be going from specific application controls to more global general controls
Control Activities - III z. Performance Reviews y. Comparing Budgets to Actual Values y. Relating Different Sets of Data-Operating or Financial-to one another, together with Analyses of the relationships and Investigative and Corrective Actions y. Reviewing Functional Performance such as a bank’s consumer loan manager’s review of reports by branch, region, and loan type for loan approvals and collections
Information & Communication z All Transactions entered for processing are Valid and Authorized z All valid transactions are captured and entered for processing on a Timely Basis and in Sufficient Detail to permit the proper Classification of Transactions z The input data of all entered transactions are Accurate and Complete, with the transactions being expressed in proper Monetary terms z All entered transactions are processed properly to update all affected records of Master Files and/or Other Types of Data sets z All required Outputs are prepared according to Appropriate Rules to provide Accurate and Reliable Information z All transactions are recorded in the proper Accounting Period
Risk z Business firms face risks that reduce the chances of achieving their control objectives. z Risk exposures arise from internal sources, such as employees, as well as external sources, such as computer hackers. z Risk assessment consists of identifying relevant risks, analyzing the extent of exposure to those risks, and managing risks by proposing effective control procedures.
Some Typical Sources of Risk - I z. Clerical and Operational Employees, who process transactional data and have access to Assets z. Computer Programmers, who have knowledge relating to the Instructions by which transactions are processed z. Managers and Accountants, who have access to Records and Financial Reports and often have Authority to Approve Transactions Figure 7 -4
Some Typical Sources of Risk - II z Former Employees, who may still understand the Control Structure and may harbor grudges against the firm z Customers and Suppliers, who generate many of the transactions processed by the firm z Competitors, who may desire to acquire confidential information of the firm z Outside Persons, such as Computer Hackers and Criminals, who have various reasons to access the firm’s data or its assets or to commit destructive acts z Acts of Nature or Accidents, such as floods, fires, and equipment breakdowns Figure 7 -4 Continued
Types of Risks z. Unintentional errors z. Deliberate Errors (Fraud) z. Unintentional Losses of Assets z. Thefts of assets z. Breaches of Security z. Acts of Violence and Natural Disasters
Factors that Increase Risk Exposure z. Frequency - the more frequent an occurrence of a transaction the greater the exposure to risk z. Vulnerability - liquid and/or portable assets contribute to risk exposure z. Size of the potential loss - the higher the monetary value of a loss, the greater the risk exposure
Problem Conditions Affecting Risk Exposures z Collusion (both internal and external), which is the cooperation of two or more people for a fraudulent purpose, is difficult to counteract even with sound control procedures z Lack of Enforcement Management may not prosecute wrongdoers because of the potential embarrassment z Computer crime poses very high degrees of risk, and fraudulent activities are difficult to detect
Computer Crime z. Computer crime (computer abuse) is the use of a computer to deceive for personal gain. z. Due to the proliferation of networks and personal computers, computer crime is expected to significantly increase both in frequency and amount of loss. z. It is speculated that a relatively small proportion of computer crime gets detected an even smaller proportion gets reported.
Examples of Computer Crime z. Theft of Computer Hardware & Software z. Unauthorized Use of Computer Facilities for Personal Use z. Fraudulent Modification or Use of Data or Programs
Reasons Why Computers Cause Control Problems z Processing is Concentrated z Audit Trails may be Undermined z Human Judgment is bypassed z Data are stored in Device-Oriented rather than Human-Oriented forms y. Invisible Data y. Stored data are Erasable y. Data are stored in a Compressed form y. Stored data are relatively accessible z Computer Equipment is Powerful but Complex and Vulnerable
Feasibility of Controls z Audit Considerations z Cost-Benefit Considerations y Determine Specific Computer Resources Subject to Control y Determine all Potential Threats to the company’s Computer System y Assess the Relevant Risks to which the firm is exposed y Measure the Extent of each Relevant Risk exposure in dollar terms y Multiply the Estimated Effect of each Relevant Risk Exposure by the Estimated Frequency of Occurrence over a Reasonable Period, such as a year y Compute the Cost of Installing and Maintaining a Control that is to Counter each Relevant Risk Exposure y Compare the Benefits against the Costs of Each Control
Legislation z The Foreign Corrupt Practices Act of 1977 z Of the Federal Legislation governing the use of computers, The Computer Fraud and Abuse Act of 1984 (amended in 1986) is perhaps the most important y. This act makes it a federal crime to intentionally access a computer for such purposes as: (1) obtaining top-secret military information, personal, financial or credit information y(2) committing a fraud y(3) altering or destroying federal information
Methods for Thwarting Computer Abuse z Enlist top-management support so that awareness of computer abuse will filter down through management ranks. z Implement and enforce control procedures. z Increase employee awareness in the seriousness of computer abuse, the amount of costs, and the disruption it creates. z Establish a code of conduct. z Be aware of the common characteristics of most computer abusers.
Methods for Thwarting Computer Abuse z Recognize the symptoms of computer abuse such as: ybehavioral or lifestyle changes in an employee yaccounting irregularities such as forged, altered or destroyed input documents or suspicious accounting adjustments yabsent or ignored control procedures ythe presence of many odd or unusual anomalies that go unchallenged z Encourage ethical behavior
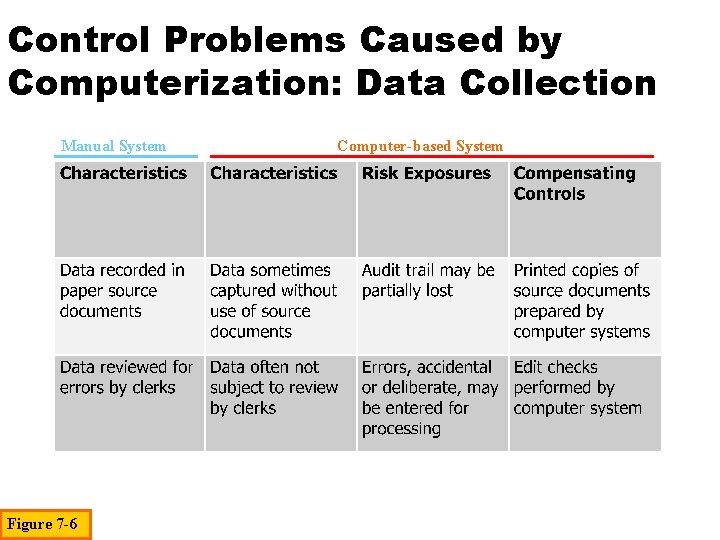
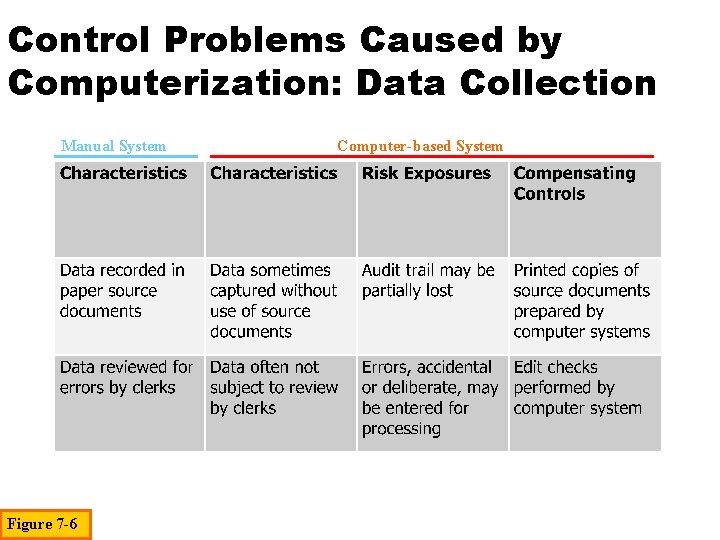
Control Problems Caused by Computerization: Data Collection Manual System Figure 7 -6 Computer-based System
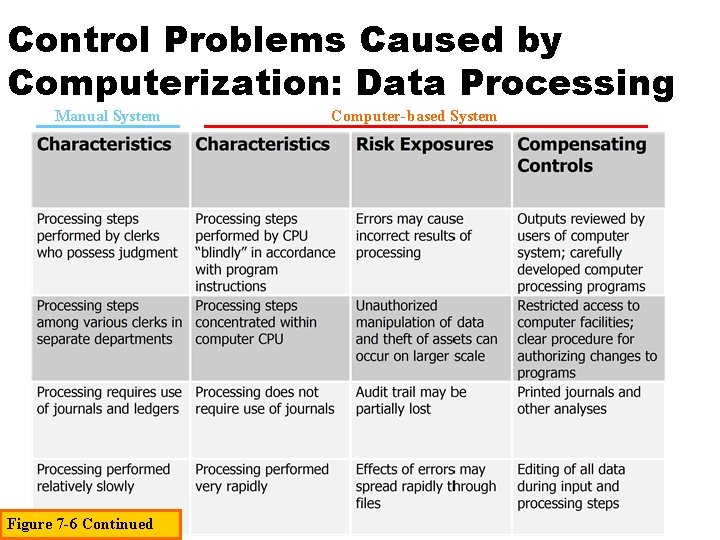
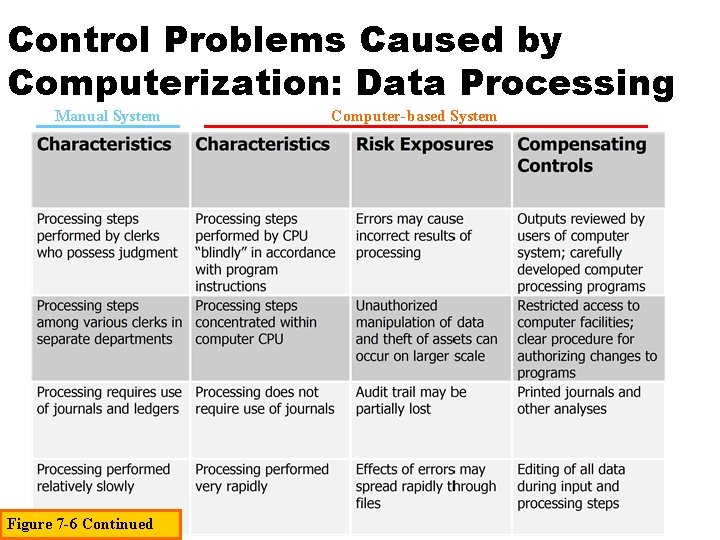
Control Problems Caused by Computerization: Data Processing Manual System Figure 7 -6 Continued Computer-based System
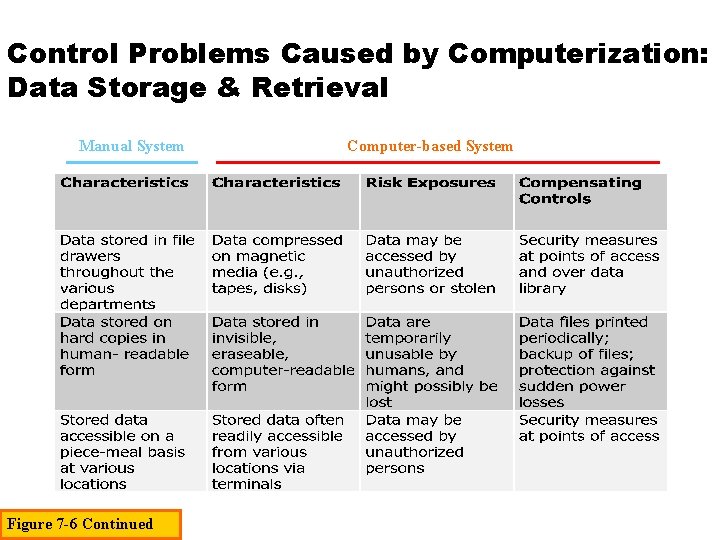
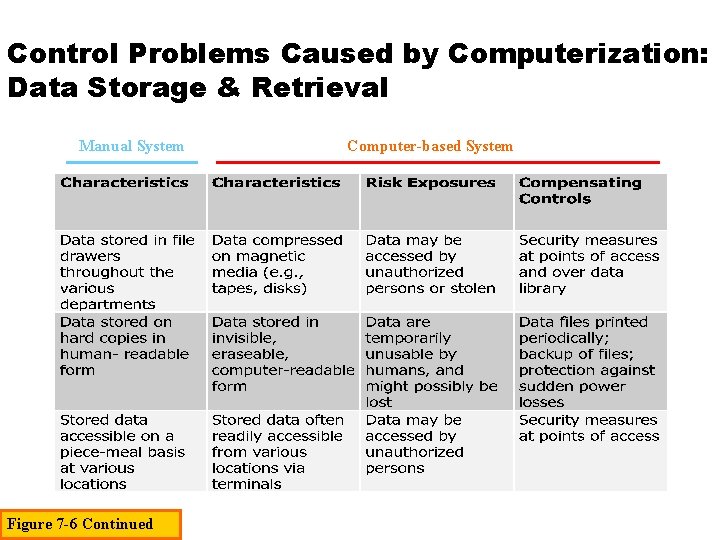
Control Problems Caused by Computerization: Data Storage & Retrieval Manual System Figure 7 -6 Continued Computer-based System
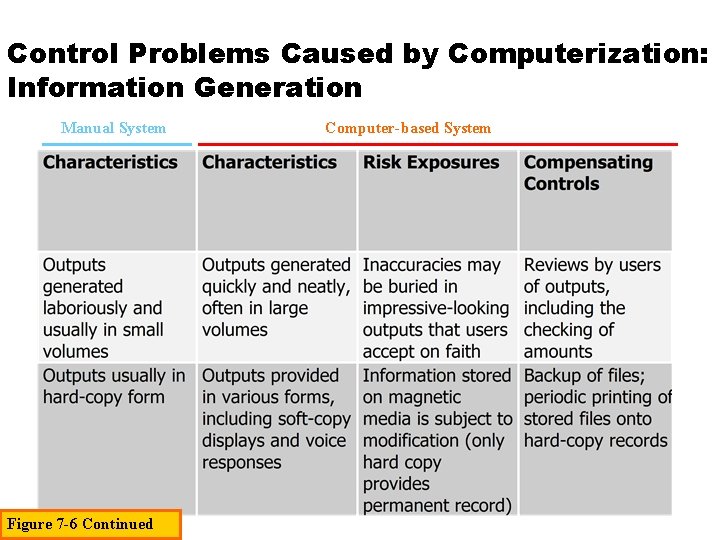
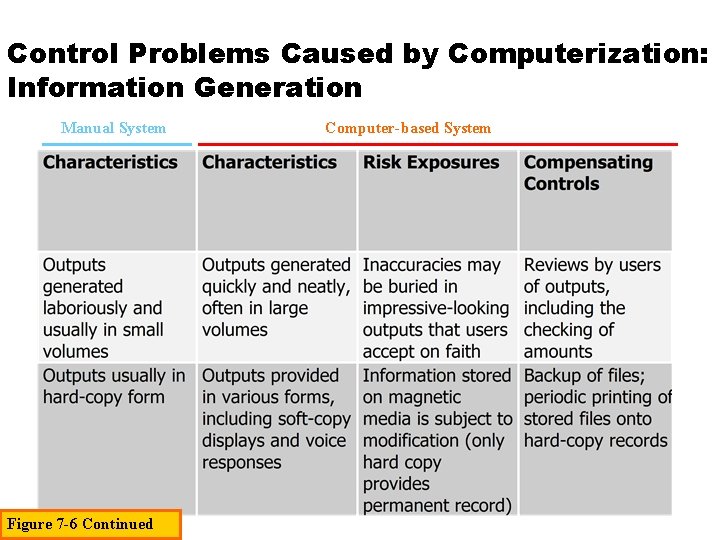
Control Problems Caused by Computerization: Information Generation Manual System Figure 7 -6 Continued Computer-based System
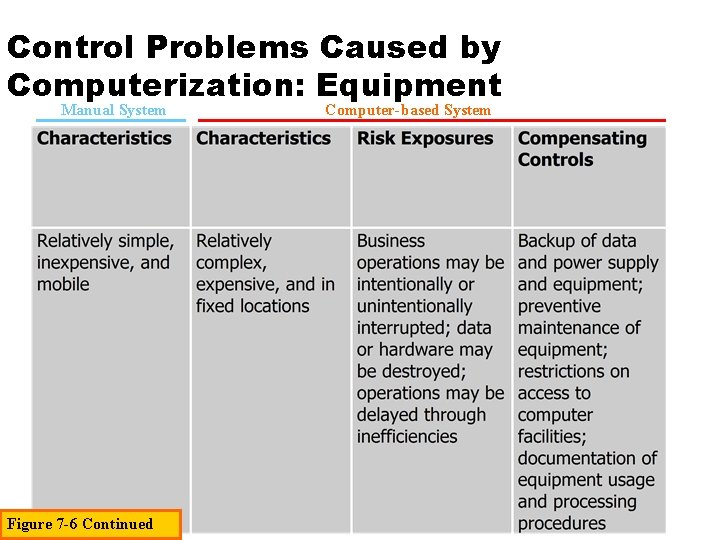
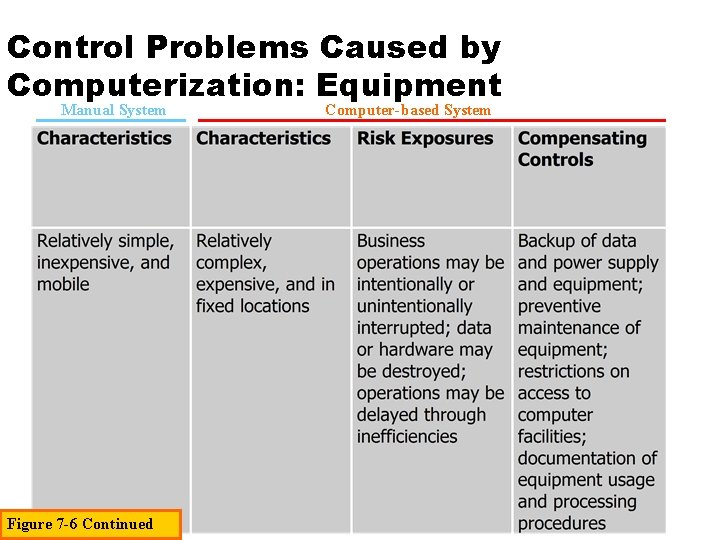
Control Problems Caused by Computerization: Equipment Manual System Figure 7 -6 Continued Computer-based System
Accounting Information Systems: Essential Concepts and Applications Fourth Edition by Wilkinson, Cerullo, Raval, and Wong-On-Wing Copyright © 2000 John Wiley & Sons, Inc. All rights reserved. Reproduction or translation of this work beyond that permitted in Section 117 of the 1976 United States Copyright Act without the express written permission of the copyright owner is unlawful. Request for further information should be addressed to the Permissions Department, John Wiley & Sons, Inc. The purchaser may make back-up copies for his/her own use only and not for distribution or resale. The publisher assumes no responsibility for errors, omissions, or damages, caused by the use of these programs or from the use of the information contained herein.