Accessing Public WiFi Security Issues Sankar Roy Department
Accessing Public Wi-Fi: Security Issues Sankar Roy Department of Computing and Information Sciences Kansas State University
Acknowledgement In preparing the presentation slides and the demo, I received help from • Professor Simon Ou • Professor Gurdip Singh • Professor Eugene Vasserman • Alex Bardas and Fengguo Wei 2
What is a public Wi-Fi? • Provides a wireless access point (AP) via which your laptop or smart phone can connect to the Internet • Wi-Fi hot spots are available in coffee shops, at airports, on KSU campus, in public libraries, etc.
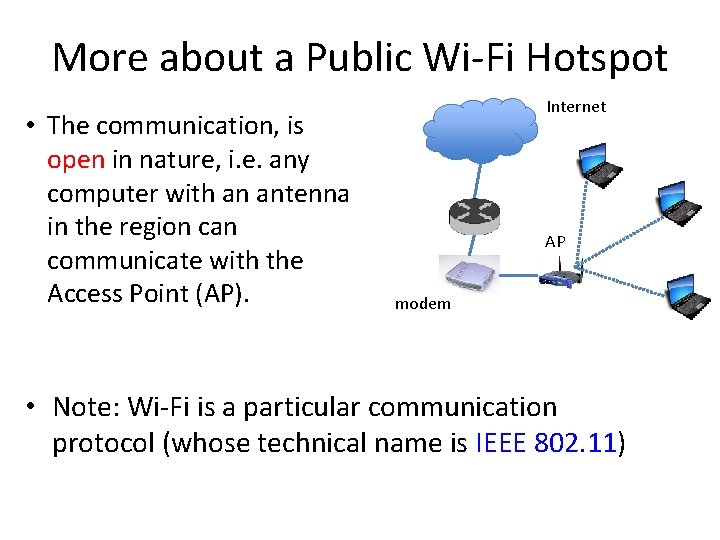
More about a Public Wi-Fi Hotspot • The communication, is open in nature, i. e. any computer with an antenna in the region can communicate with the Access Point (AP). Internet AP modem • Note: Wi-Fi is a particular communication protocol (whose technical name is IEEE 802. 11)
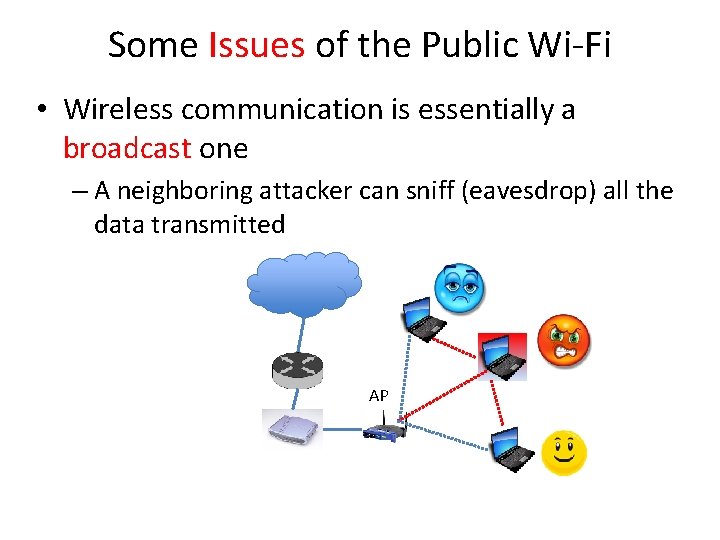
Some Issues of the Public Wi-Fi • Wireless communication is essentially a broadcast one – A neighboring attacker can sniff (eavesdrop) all the data transmitted AP
More Issues of the Public Wi-Fi • Why no encryption is employed in a public Wi-Fi? – It will become complex from the admin perspective – It will hurt the current “plug and play” feature. – Encryption does not help if everybody shares the password • Why can’t you use a secure Wi-Fi protocol yourself? – The network admin has to make the protocol available – You (the user) do not have the admin access of the AP.
Attack 1: Eavesdrop Communication • The attacker might be able to mine out secret information (e. g. a user’s emails, password, banking details, etc. ) from the sniffed communication. • Available attack-tools: air. Pcap, wireshark, driftnet, urlsnarf, etc.
Background Knowledge for Attack 2 • In some portals (e. g. Yahoo mail) the web session after successful login switches back to HTTP. The HTTP session is then authenticated only by a cookie. • What is a cookie? – a login receipt containing the web session ID – The server can identify/authenticate the client’s session by the cookie ID • Problem: client’s cookie can be stolen – (example) when the adversary does packet sniffing on the Wi-Fi network where the client’s machine is • Outcome: the HTTP session can be hijacked (also called sidejacked). 8
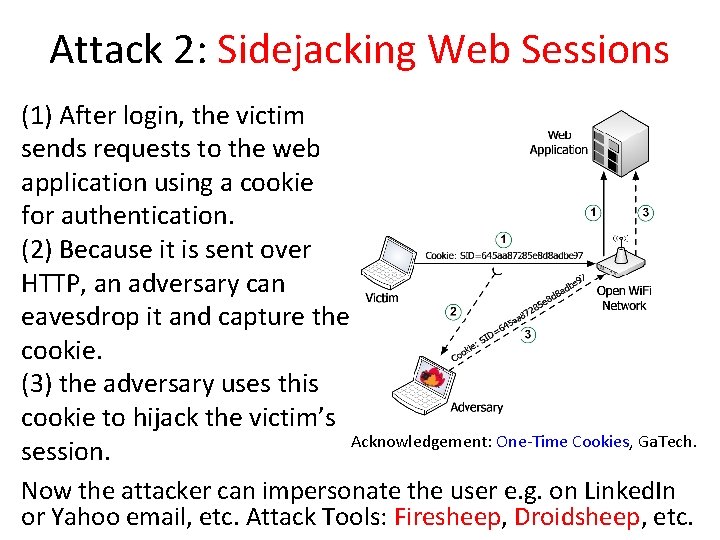
Attack 2: Sidejacking Web Sessions (1) After login, the victim sends requests to the web application using a cookie for authentication. (2) Because it is sent over HTTP, an adversary can eavesdrop it and capture the cookie. (3) the adversary uses this cookie to hijack the victim’s Acknowledgement: One-Time Cookies, Ga. Tech. session. Now the attacker can impersonate the user e. g. on Linked. In or Yahoo email, etc. Attack Tools: Firesheep, Droidsheep, etc.
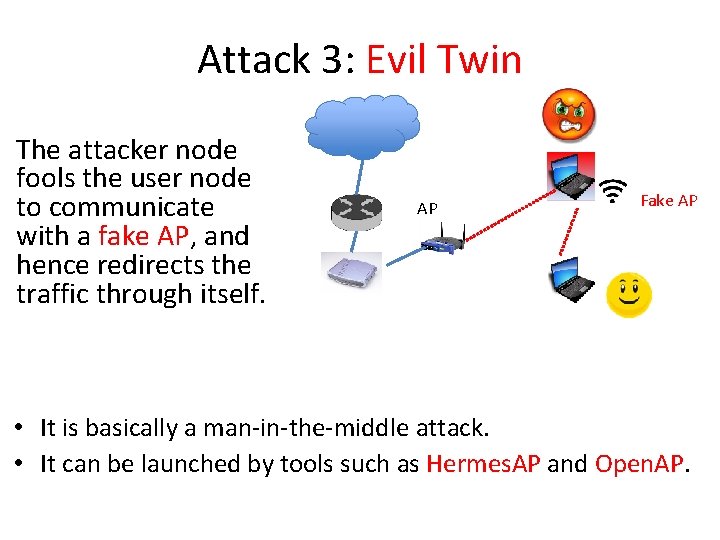
Attack 3: Evil Twin The attacker node fools the user node to communicate with a fake AP, and hence redirects the traffic through itself. AP Fake AP • It is basically a man-in-the-middle attack. • It can be launched by tools such as Hermes. AP and Open. AP.
Firesheep: One Web Session Hijacking Tool • The attack scenario: – an innocent user Alice accesses her Yahoo email or Linked. In account using a public Wi-Fi at a hotspot (e. g. an airport) – a neighboring attacker Mallory (M) uses a Firefox add-on (Firesheep) on a laptop and sniffs the user Alice’s communication • Firesheep automatically grabs the cookie of each of Alice’s insecure web sessions (i. e. HTTP sessions) • With the above cookies, Firesheep automatically hijacks Alice’s web sessions
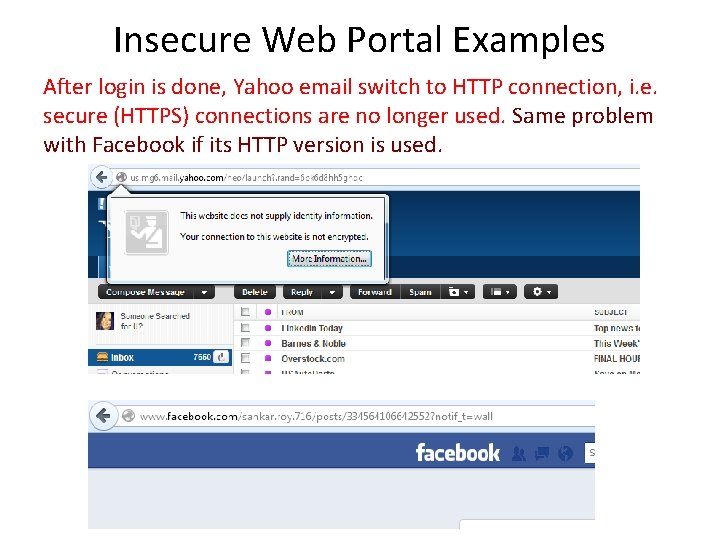
Insecure Web Portal Examples After login is done, Yahoo email switch to HTTP connection, i. e. secure (HTTPS) connections are no longer used. Same problem with Facebook if its HTTP version is used.
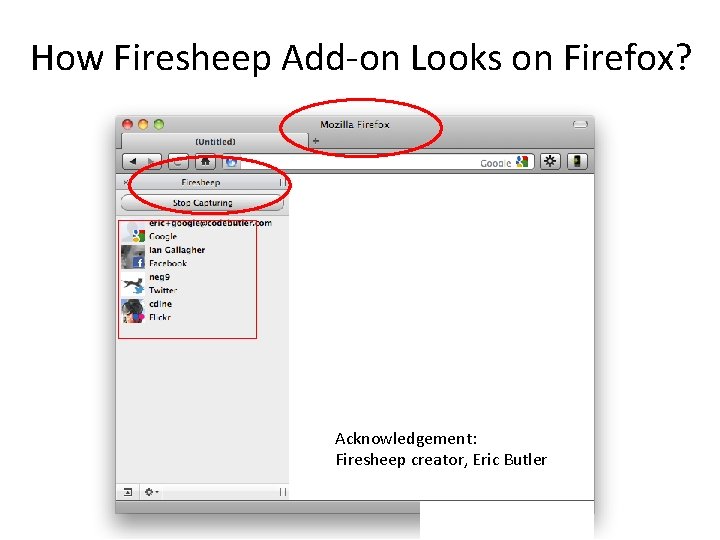
How Firesheep Add-on Looks on Firefox? Acknowledgement: Firesheep creator, Eric Butler

Attacker is Browsing Hijacked Sessions Acknowledgement: Firesheep creater, Mr. Butler
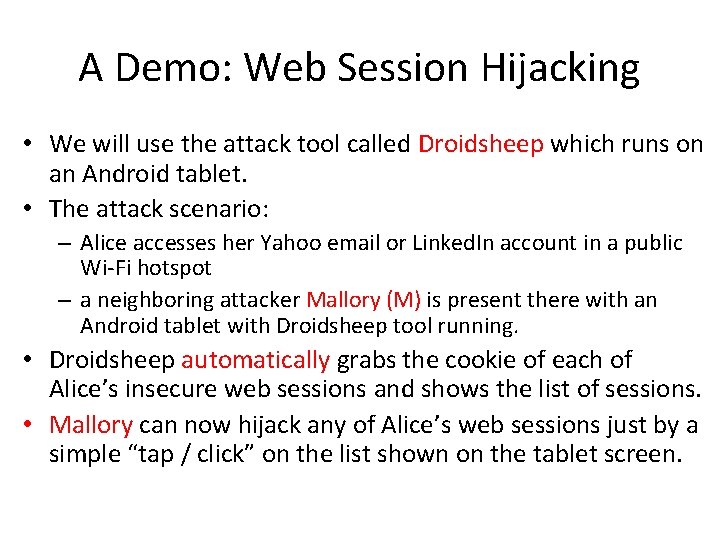
A Demo: Web Session Hijacking • We will use the attack tool called Droidsheep which runs on an Android tablet. • The attack scenario: – Alice accesses her Yahoo email or Linked. In account in a public Wi-Fi hotspot – a neighboring attacker Mallory (M) is present there with an Android tablet with Droidsheep tool running. • Droidsheep automatically grabs the cookie of each of Alice’s insecure web sessions and shows the list of sessions. • Mallory can now hijack any of Alice’s web sessions just by a simple “tap / click” on the list shown on the tablet screen.
Demonstration
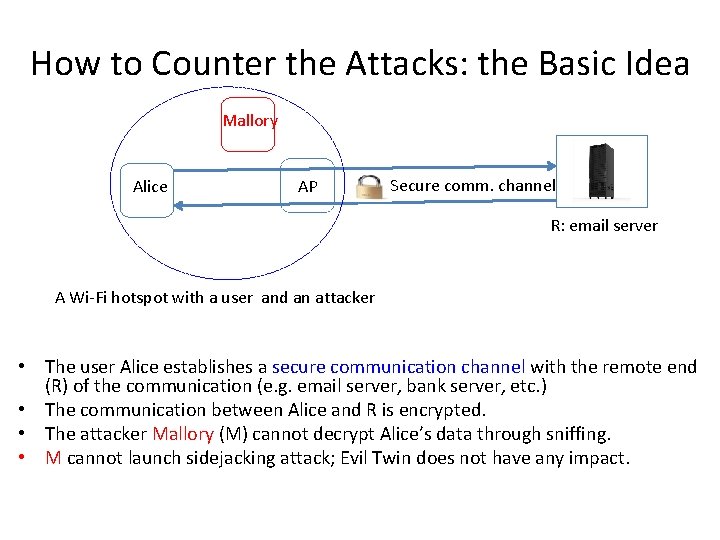
How to Counter the Attacks: the Basic Idea Mallory Alice AP Secure comm. channel R: email server A Wi-Fi hotspot with a user and an attacker • The user Alice establishes a secure communication channel with the remote end (R) of the communication (e. g. email server, bank server, etc. ) • The communication between Alice and R is encrypted. • The attacker Mallory (M) cannot decrypt Alice’s data through sniffing. • M cannot launch sidejacking attack; Evil Twin does not have any impact.
Solution 1: Browse Secure Web Only • We can avoid the above attacks if we access only the HTTPS-enabled web sites (e. g. Gmail but not the Yahoo email) • Many web portals (e. g. Facebook, Tweeter) provide both HTTPS and HTTP options; you have to choose the HTTPS option. • We discussed how to use HTTPS web browsing in the previous class.
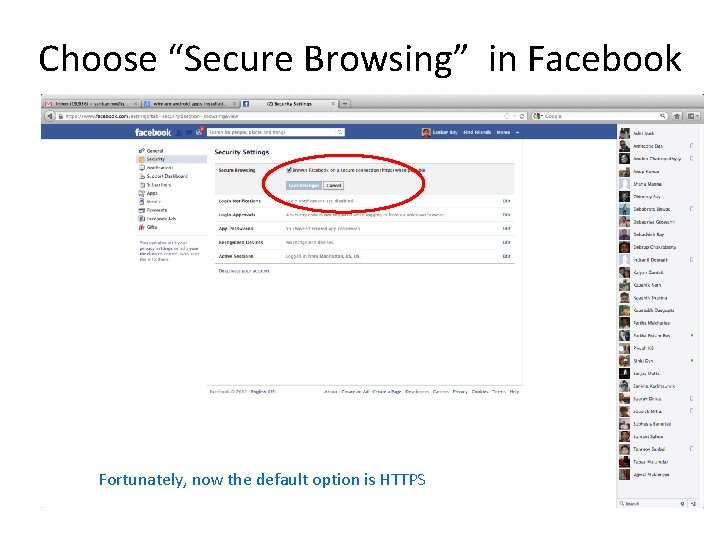
Choose “Secure Browsing” in Facebook Fortunately, now the default option is HTTPS
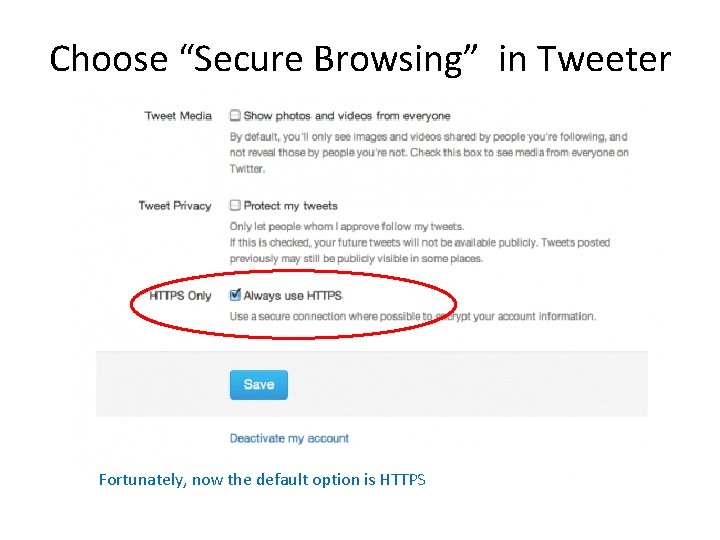
Choose “Secure Browsing” in Tweeter Fortunately, now the default option is HTTPS
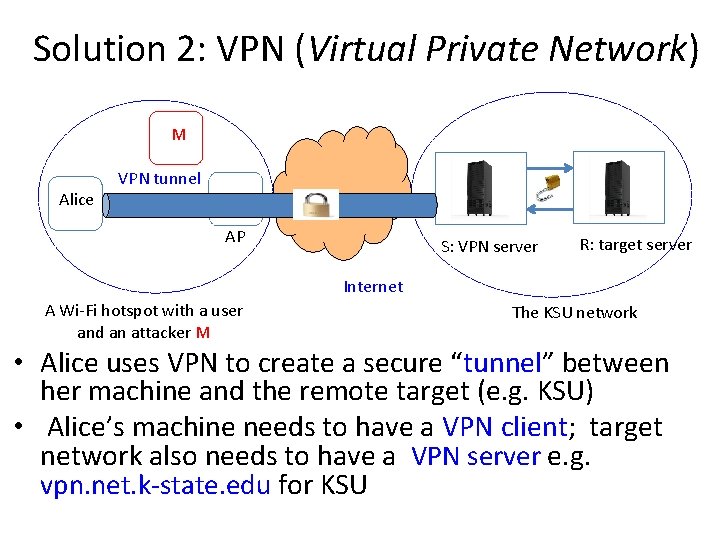
Solution 2: VPN (Virtual Private Network) M Alice VPN tunnel AP S: VPN server R: target server Internet A Wi-Fi hotspot with a user and an attacker M The KSU network • Alice uses VPN to create a secure “tunnel” between her machine and the remote target (e. g. KSU) • Alice’s machine needs to have a VPN client; target network also needs to have a VPN server e. g. vpn. net. k-state. edu for KSU
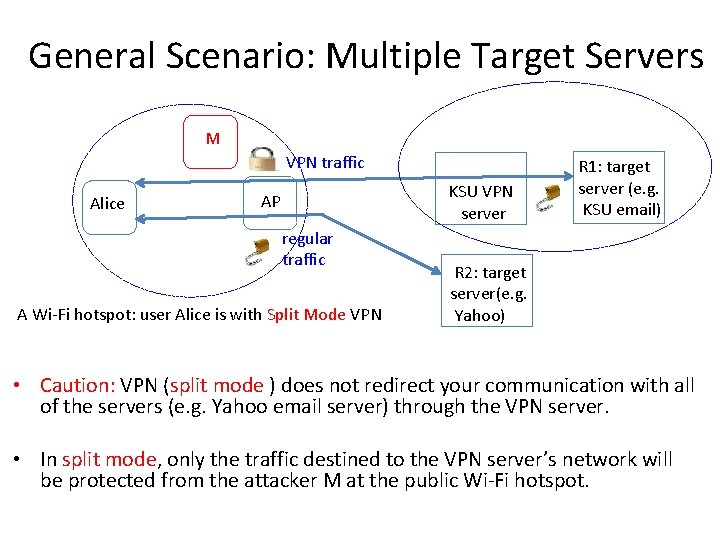
General Scenario: Multiple Target Servers M VPN traffic Alice KSU VPN server AP regular traffic A Wi-Fi hotspot: user Alice is with Split Mode VPN R 1: target server (e. g. KSU email) R 2: target server(e. g. Yahoo) • Caution: VPN (split mode ) does not redirect your communication with all of the servers (e. g. Yahoo email server) through the VPN server. • In split mode, only the traffic destined to the VPN server’s network will be protected from the attacker M at the public Wi-Fi hotspot.
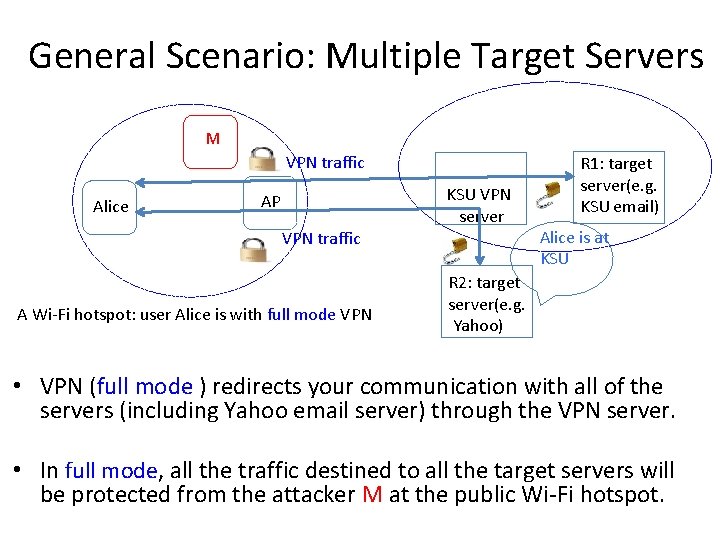
General Scenario: Multiple Target Servers M VPN traffic Alice AP VPN traffic A Wi-Fi hotspot: user Alice is with full mode VPN KSU VPN server R 1: target server(e. g. KSU email) Alice is at KSU R 2: target server(e. g. Yahoo) • VPN (full mode ) redirects your communication with all of the servers (including Yahoo email server) through the VPN server. • In full mode, all the traffic destined to all the target servers will be protected from the attacker M at the public Wi-Fi hotspot.
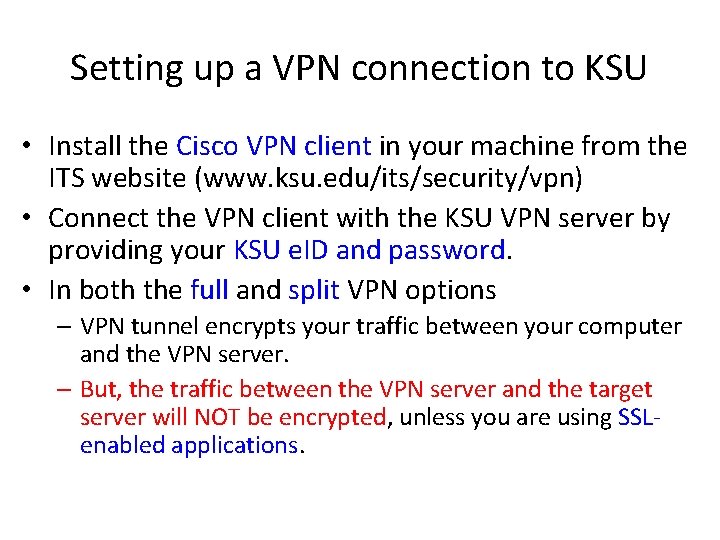
Setting up a VPN connection to KSU • Install the Cisco VPN client in your machine from the ITS website (www. ksu. edu/its/security/vpn) • Connect the VPN client with the KSU VPN server by providing your KSU e. ID and password. • In both the full and split VPN options – VPN tunnel encrypts your traffic between your computer and the VPN server. – But, the traffic between the VPN server and the target server will NOT be encrypted, unless you are using SSLenabled applications.
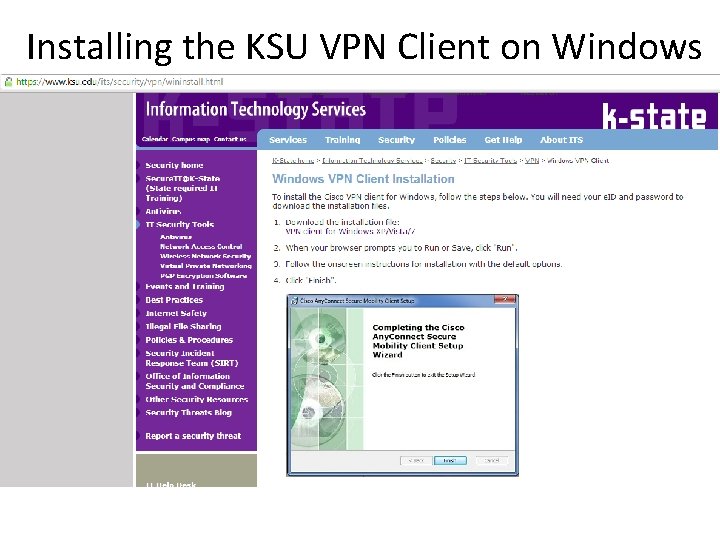
Installing the KSU VPN Client on Windows
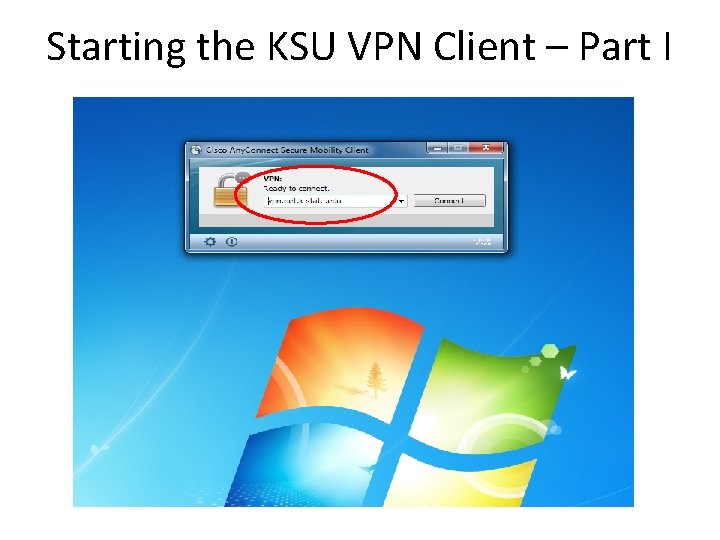
Starting the KSU VPN Client – Part I
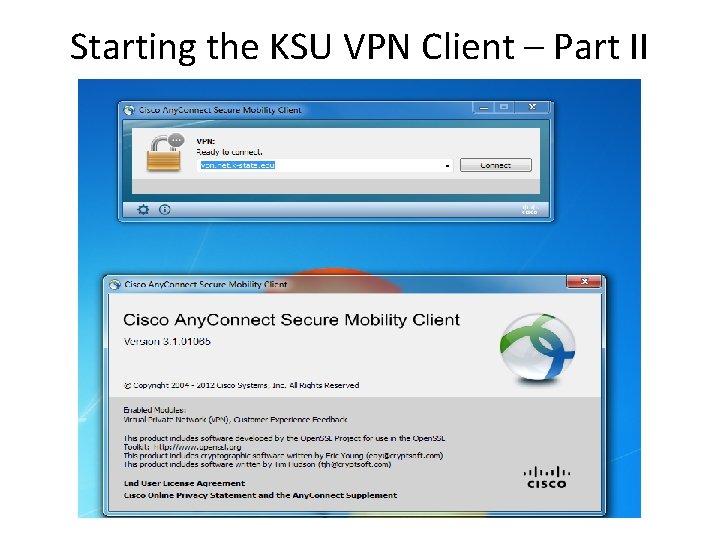
Starting the KSU VPN Client – Part II
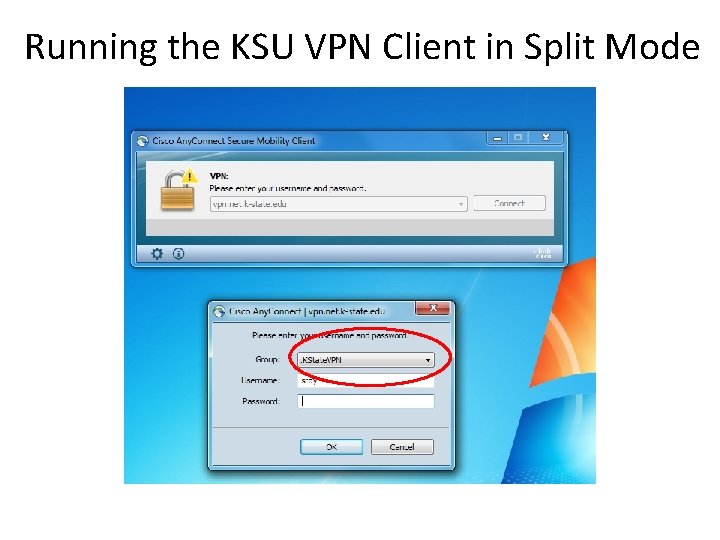
Running the KSU VPN Client in Split Mode
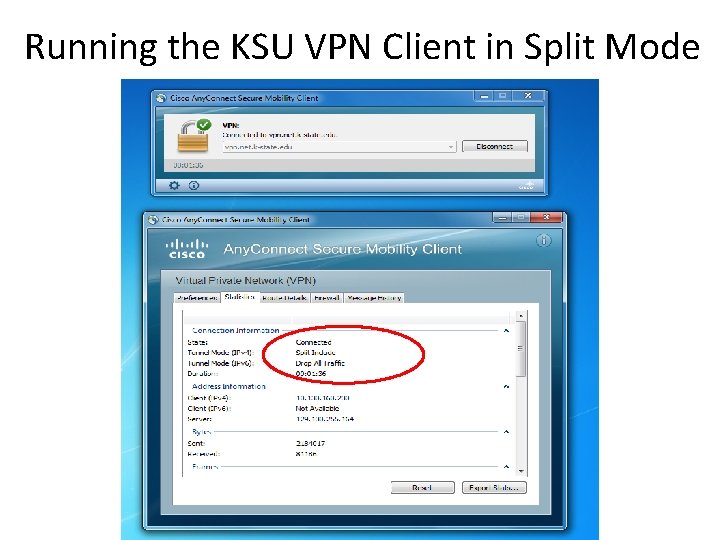
Running the KSU VPN Client in Split Mode
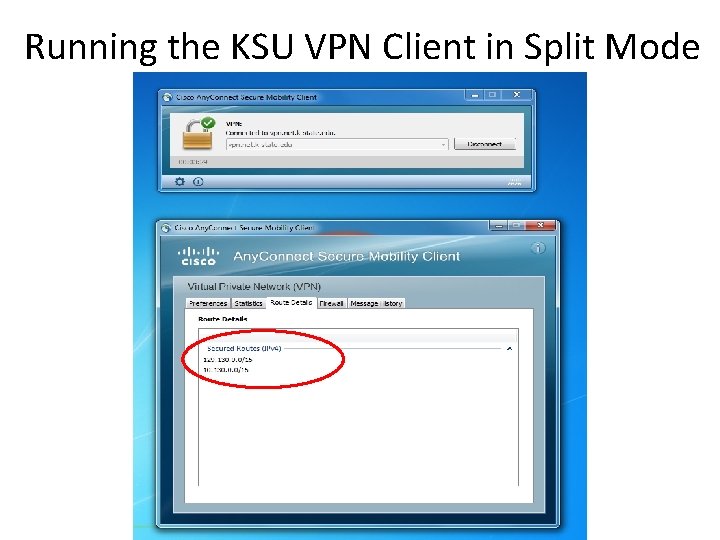
Running the KSU VPN Client in Split Mode
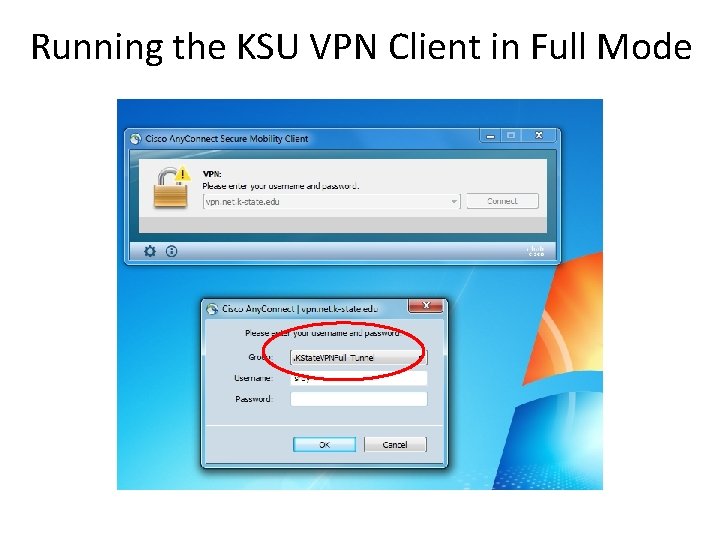
Running the KSU VPN Client in Full Mode
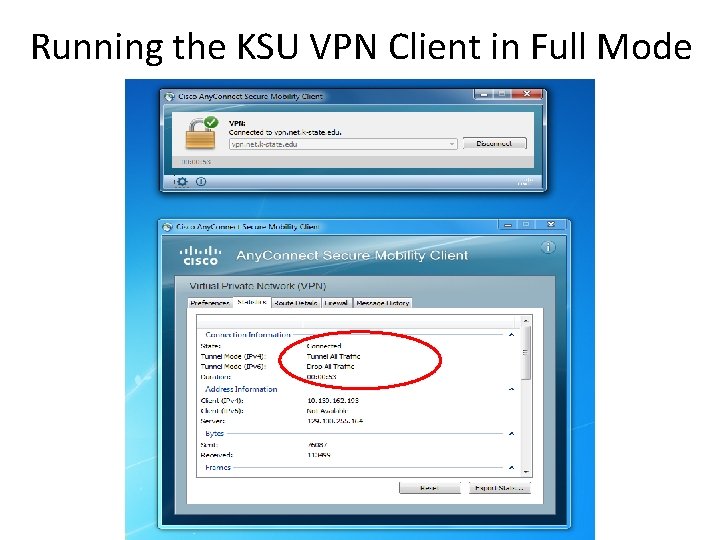
Running the KSU VPN Client in Full Mode
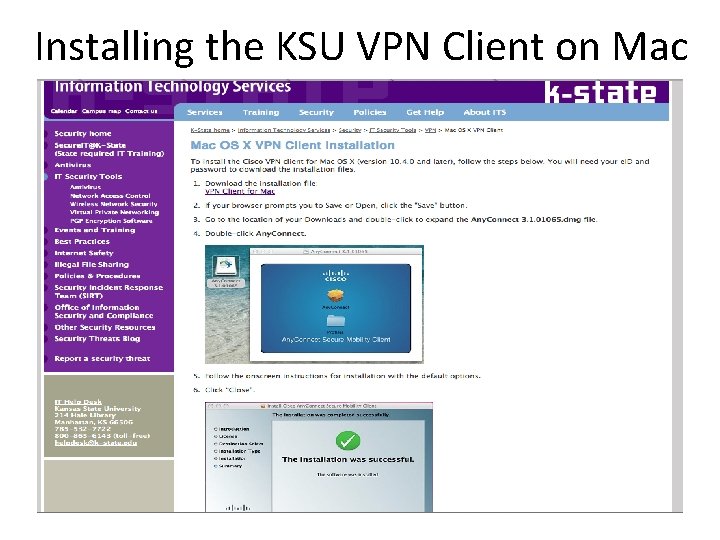
Installing the KSU VPN Client on Mac
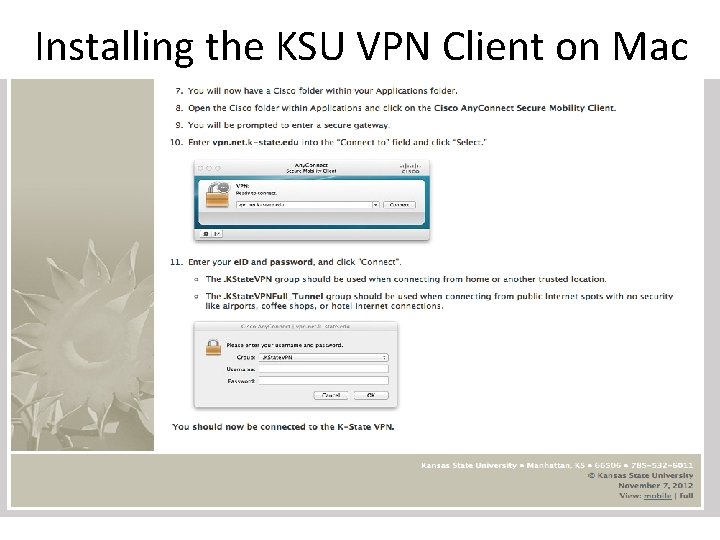
Installing the KSU VPN Client on Mac
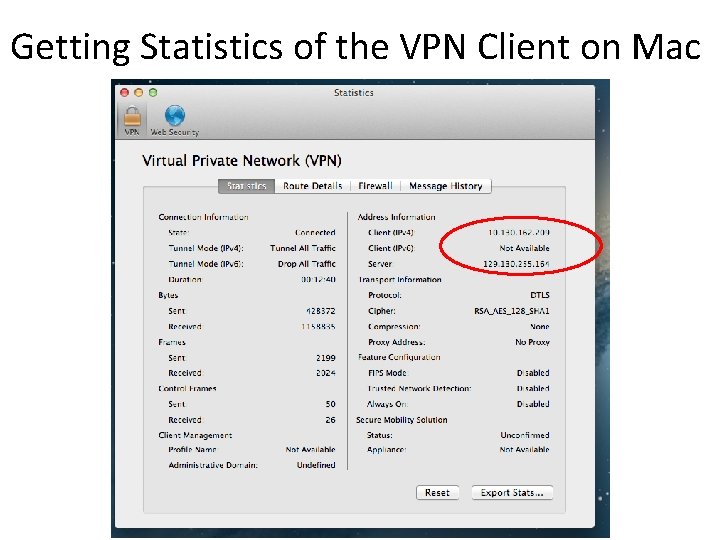
Getting Statistics of the VPN Client on Mac
Managing Common Wi-Fi Settings • Your laptop (or smartphone) may get connected automatically to a public Wi-Fi network if you have used the same network before • The above can also happen if you have used a different network with the same name (SSID) before. • How to avoid: change the default wireless network access policy of your laptop or smartphone
Similar Attacks to a Wired Network? • Wired Ethernet network can be eavesdropped – If it is a network with a “hub”, then it builds a broadcast channel like a Wi-Fi network. So, sniffing is easy – If it is a network with a “switch”, then the attacker needs some additional step before being able to sniff • So, similar attacks can be launched in a wired network where users access Internet via Ethernet cables in a public place. • Note: this even applies to cable Internet connections at home.
Summary • We discussed common security threats of using a public Wi-Fi hotspot • We presented a few standard countermeasures to mitigate the risks • Remainder: – the next homework is due before the next class (1 pm on February 14) – the next class will be held in Room 127 38
- Slides: 38