Access Xpert Solution Overview Simple Smart Flexible Presented

Access. Xpert™ Solution Overview Simple Smart Flexible Presented By: XXX Confidential Property of Schneider Electric

Faced with growing challenges and greater bottom line responsibilities, those who manage large, enterprise buildings need a comprehensive Security Solution that break through traditional boundaries to: > leverage industry Open Standards > re-use existing infrastructures > leverage the latest in Web and Cloud technologies > provide anytime, anywhere access to building information Confidential Property of Schneider Electric | Page 2
Schneider Electric’s Access. Xpert™ solution has been created with customers’ needs foremost in mind. By leveraging the latest in Open Standards with the flexibility of the Web, Schneider Electric delivers a robust Security Solution today that is ready for the next industry evolution. Confidential Property of Schneider Electric | Page 3
Why Access. Xpert Experience beyond open systems One of the industry’s most innovative and open solutions, Access. Xpert incorporates the flexibility of Mercury Hardware, the standard communications of BACnet. TM and the global history of Schneider Electric open solutions. Utilizing a full RESTFUL API and Web. Services, Access. Xpert simplifies integrations and reduces development cost. Increase flexibility and mobility Mobile applications get your security operations team out of the command center and allow them to be visible and present throughout your business. From a smart device or laptop, your team can make clear, informed decisions to more effectively secure your enterprise. Choose cloud-based or local The hosted application and database reside in a secured cloud environment with replication across multiple servers for redundancy, or a nonhosted server and database option resides on your premise. The choice is yours. Confidential Property of Schneider Electric | Page 4
Why Access. Xpert Merge physical and cyber security The secure structure in Access. Xpert meets stringent security requirements and government regulations, so only authorized personnel access your security system. Encryption and authentication protect communications between controllers, workstations, and mobile devices. Simplify integration Access. Xpert brings together disparate security systems such as access control, intrusion detection, mass messaging, and video surveillance into an easy-to-use interface. Furthermore, Access. Xpert enables simplified integration with building management systems fostering new possibilities for enhanced security and efficiency. Reduce operating costs The integration, wireless, and cloud capabilities of Access. Xpert combine for a highly efficient cost footprint, upfront and ongoing. The familiar, intuitive user interface reduces personnel training costs while off-the-shelf devices and universal protocols simplify support and maintenance. Integration to your BMS enables greater energy savings. Confidential Property of Schneider Electric | Page 5
What makes Access. Xpert a smart choice? #1 Freedom to Choose Access. Xpert allows Freedom of Choice by providing seamless operation either in the Cloud or on a Server at your facility • A choice today can easily be changed tomorrow Access. Xpert allows Freedom of Hardware Choice • Customers can enjoy today's leading hardware options including Mercury, HID and legacy Continuum Access. Xpert allows Freedom of Integration Choice • Support for many leading Video Platforms allows customers additional opportunities to choose the video system that is right for them • Support for Open BACnet means customers can enhance their security environment with beneficial integrations with many other Building Technologies such as temperature, lighting and energy Confidential Property of Schneider Electric | Page 8
What makes Access. Xpert a smart choice? #2 – Holistic approach to Security Management Monitor and manage multiple sites through a single Web environment including: • Credential Management including arm/disarm codes • Alarm Management • One click lockdown across the enterprise • Broadcast emergencies from one location Confidential Property of Schneider Electric | Page 9
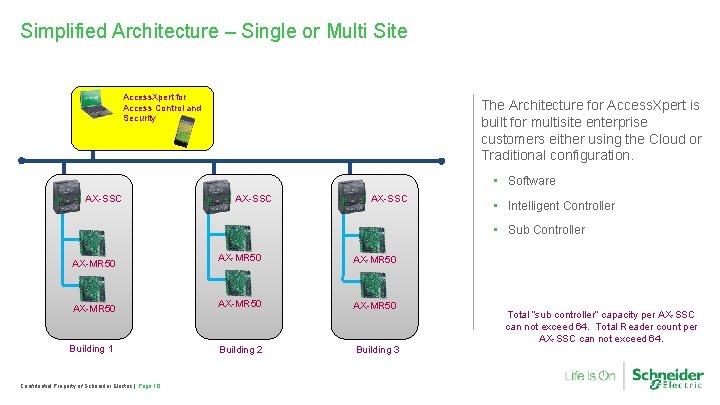
Simplified Architecture – Single or Multi Site Access. Xpert for Access Control and Security The Architecture for Access. Xpert is built for multisite enterprise customers either using the Cloud or Traditional configuration. • Software AX-SSC • Intelligent Controller • Sub Controller AX-MR 50 Building 1 Confidential Property of Schneider Electric | Page 10 AX-MR 50 Building 2 Building 3 Total “sub controller” capacity per AX-SSC can not exceed 64. Total Reader count per AX-SSC can not exceed 64.
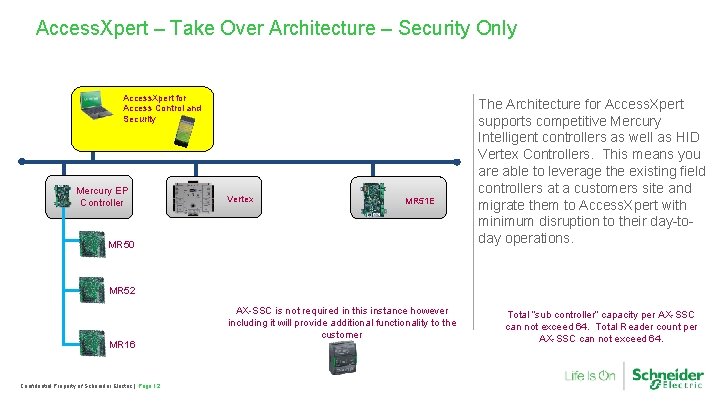
Access. Xpert – Take Over Architecture – Security Only Access. Xpert for Access Control and Security Mercury EP Controller Vertex MR 51 E MR 50 The Architecture for Access. Xpert supports competitive Mercury Intelligent controllers as well as HID Vertex Controllers. This means you are able to leverage the existing field controllers at a customers site and migrate them to Access. Xpert with minimum disruption to their day-today operations. MR 52 MR 16 Confidential Property of Schneider Electric | Page 12 AX-SSC is not required in this instance however including it will provide additional functionality to the customer Total “sub controller” capacity per AX-SSC can not exceed 64. Total Reader count per AX-SSC can not exceed 64.
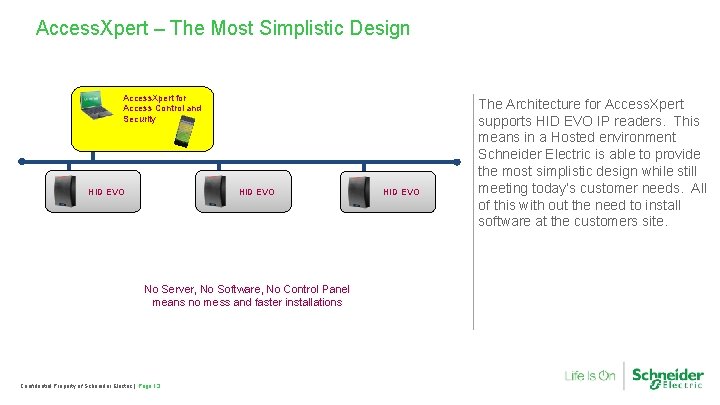
Access. Xpert – The Most Simplistic Design Access. Xpert for Access Control and Security HID EVO No Server, No Software, No Control Panel means no mess and faster installations Confidential Property of Schneider Electric | Page 13 HID EVO The Architecture for Access. Xpert supports HID EVO IP readers. This means in a Hosted environment Schneider Electric is able to provide the most simplistic design while still meeting today’s customer needs. All of this with out the need to install software at the customers site.
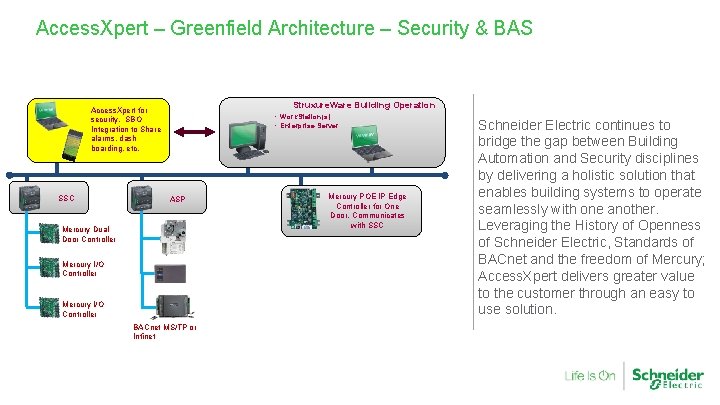
Access. Xpert – Greenfield Architecture – Security & BAS Struxure. Ware Building Operation Access. Xpert for security. SBO Integration to Share alarms, dash boarding, etc. SSC • Work. Station(s) • Enterprise Server ASP Mercury Dual Door Controller Mercury I/O Controller BACnet MS/TP or Infinet Mercury POE IP Edge Controller for One Door. Communicates with SSC Schneider Electric continues to bridge the gap between Building Automation and Security disciplines by delivering a holistic solution that enables building systems to operate seamlessly with one another. Leveraging the History of Openness of Schneider Electric, Standards of BACnet and the freedom of Mercury; Access. Xpert delivers greater value to the customer through an easy to use solution.
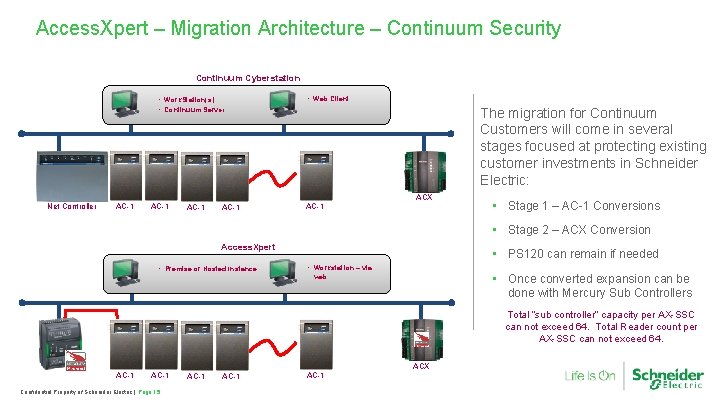
Access. Xpert – Migration Architecture – Continuum Security Continuum Cyberstation • Work. Station(s) • Continuum Server • Web Client The migration for Continuum Customers will come in several stages focused at protecting existing customer investments in Schneider Electric: ACX Net Controller AC-1 AC-1 • Stage 1 – AC-1 Conversions • Stage 2 – ACX Conversion Access. Xpert • Premise or Hosted Instance • PS 120 can remain if needed • Workstation – via • Once converted expansion can be done with Mercury Sub Controllers web Total “sub controller” capacity per AX-SSC can not exceed 64. Total Reader count per AX-SSC can not exceed 64. ACX AC-1 Confidential Property of Schneider Electric | Page 15 AC-1

Access. Xpert™ Security Solution Harmonized Software and Hardware for an integrated security environment that transcends Security Confidential Property of Schneider Electric | Page 16
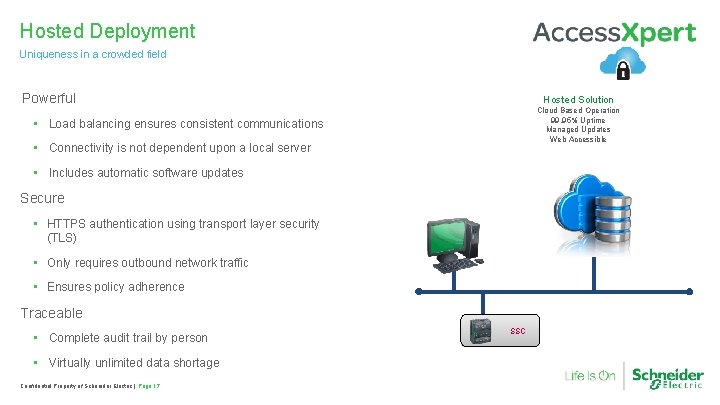
Hosted Deployment Uniqueness in a crowded field Powerful Hosted Solution Cloud Based Operation 99. 95% Uptime Managed Updates Web Accessible • Load balancing ensures consistent communications • Connectivity is not dependent upon a local server • Includes automatic software updates Secure • HTTPS authentication using transport layer security (TLS) • Only requires outbound network traffic • Ensures policy adherence Traceable • Complete audit trail by person • Virtually unlimited data shortage Confidential Property of Schneider Electric | Page 17 SSC
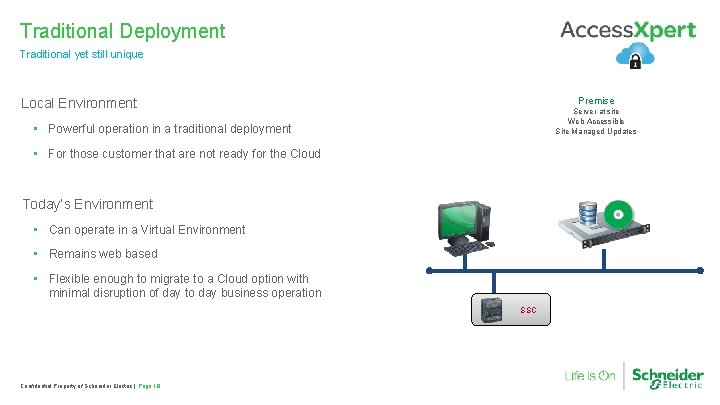
Traditional Deployment Traditional yet still unique Premise Local Environment Server at site Web Accessible Site Managed Updates • Powerful operation in a traditional deployment • For those customer that are not ready for the Cloud Today’s Environment • Can operate in a Virtual Environment • Remains web based • Flexible enough to migrate to a Cloud option with minimal disruption of day to day business operation SSC Confidential Property of Schneider Electric | Page 18
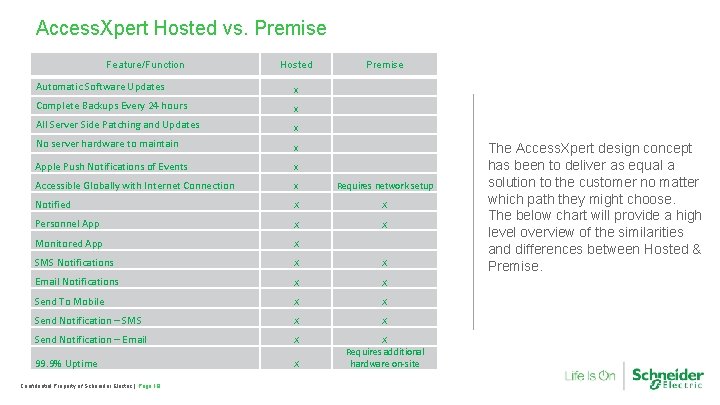
Access. Xpert Hosted vs. Premise Feature/Function Hosted Premise Automatic Software Updates x Complete Backups Every 24 hours x All Server Side Patching and Updates x No server hardware to maintain x Apple Push Notifications of Events x Accessible Globally with Internet Connection x Requires network setup Notified X X Personnel App X X Monitored App X SMS Notifications X X Email Notifications X X Send To Mobile X X Send Notification – SMS X X Send Notification – Email X 99. 9% Uptime X X Requires additional hardware on-site Confidential Property of Schneider Electric | Page 19 The Access. Xpert design concept has been to deliver as equal a solution to the customer no matter which path they might choose. The below chart will provide a high level overview of the similarities and differences between Hosted & Premise.
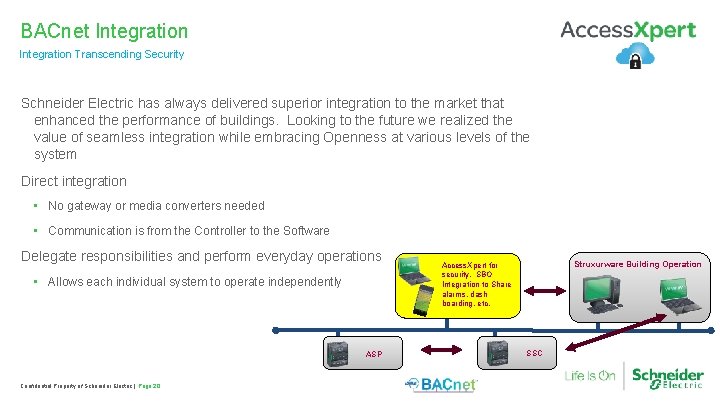
BACnet Integration Transcending Security Schneider Electric has always delivered superior integration to the market that enhanced the performance of buildings. Looking to the future we realized the value of seamless integration while embracing Openness at various levels of the system Direct integration • No gateway or media converters needed • Communication is from the Controller to the Software Delegate responsibilities and perform everyday operations • Allows each individual system to operate independently ASP Confidential Property of Schneider Electric | Page 20 Struxurware Building Operation Access. Xpert for security. SBO Integration to Share alarms, dash boarding, etc. SSC
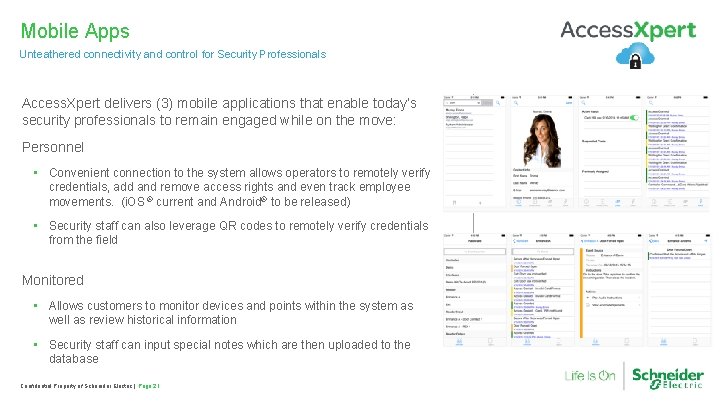
Mobile Apps Unteathered connectivity and control for Security Professionals Access. Xpert delivers (3) mobile applications that enable today’s security professionals to remain engaged while on the move: Personnel • Convenient connection to the system allows operators to remotely verify credentials, add and remove access rights and even track employee movements. (i. OS ® current and Android® to be released) • Security staff can also leverage QR codes to remotely verify credentials from the field Monitored • Allows customers to monitor devices and points within the system as well as review historical information • Security staff can input special notes which are then uploaded to the database Confidential Property of Schneider Electric | Page 21
Software modules Minimalist approach with embedded software modules Access. Xpert is built to deliver maximum features without the need to worry about an expansive list of optional modules. From day one; customers can benefit from: – TLS encryption – Unlimited Pelco VMS integration licenses – Unlimited cardholder fields – Built-in reporting package – Built-in map creation & editors – Built-in Mass Notification Confidential Property of Schneider Electric | Page 22
Smart. Struxure™ solution user experience features Monitor, manage and control your facilities, and simplify day-to-day operation, with the most user-friendly BMS on the market Confidential Property of Schneider Electric | Page 23
Personalized user interface Organize workspace views to meet individual needs Create a unique view based upon your individual log in Ability to see what is important to the: • HR Director • Security Manager • Security Operator • Facility Manager • And even unique tenant views Preferences follow the user so they see their layout wherever they log in Confidential Property of Schneider Electric | Page 24
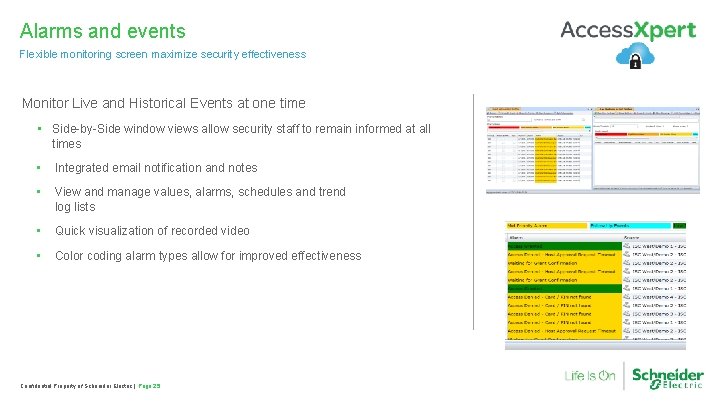
Alarms and events Flexible monitoring screen maximize security effectiveness Monitor Live and Historical Events at one time • Side-by-Side window views allow security staff to remain informed at all times • Integrated email notification and notes • View and manage values, alarms, schedules and trend log lists • Quick visualization of recorded video • Color coding alarm types allow for improved effectiveness Confidential Property of Schneider Electric | Page 25
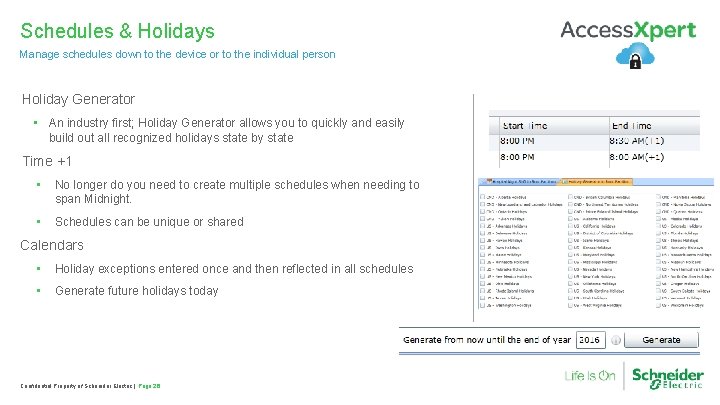
Schedules & Holidays Manage schedules down to the device or to the individual person Holiday Generator • An industry first; Holiday Generator allows you to quickly and easily build out all recognized holidays state by state Time +1 • No longer do you need to create multiple schedules when needing to span Midnight. • Schedules can be unique or shared Calendars • Holiday exceptions entered once and then reflected in all schedules • Generate future holidays today Confidential Property of Schneider Electric | Page 26
Reports Understand share reports easily and automatically Powerful reporting tool • Includes over a dozen canned reports • Reports can be scheduled, emailed and modified • Available in PDF and Excel • Can be saved for future use • Can be modified and saved for future use Confidential Property of Schneider Electric | Page 27
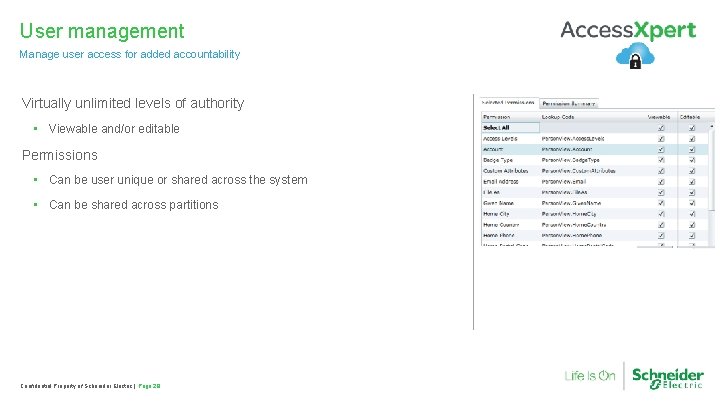
User management Manage user access for added accountability Virtually unlimited levels of authority • Viewable and/or editable Permissions • Can be user unique or shared across the system • Can be shared across partitions Confidential Property of Schneider Electric | Page 28
Robust Video Integration Multiple Options To Support Customer Needs Access. Xpert Supports multiple industry leading video platforms at the same time on the same system. This reinforces our commitment to leading the industry in Open Solutions. Out of the box; Access. Xpert supports: • Pelco Digital Sentry • Pelco Video Expert • Salient • Exacq • Cognimatics Confidential Property of Schneider Electric | Page 29
Hardware components Native hardware for Smart. Struxure solution Confidential Property of Schneider Electric | Page 30
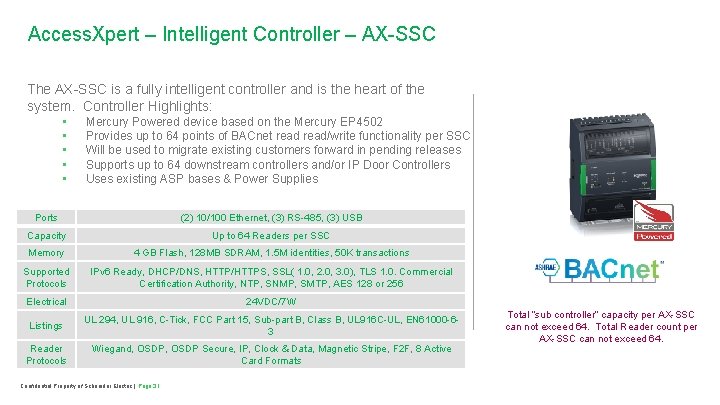
Access. Xpert – Intelligent Controller – AX-SSC The AX-SSC is a fully intelligent controller and is the heart of the system. Controller Highlights: • • • Mercury Powered device based on the Mercury EP 4502 Provides up to 64 points of BACnet read/write functionality per SSC Will be used to migrate existing customers forward in pending releases Supports up to 64 downstream controllers and/or IP Door Controllers Uses existing ASP bases & Power Supplies Ports (2) 10/100 Ethernet, (3) RS-485, (3) USB Capacity Up to 64 Readers per SSC Memory 4 GB Flash, 128 MB SDRAM, 1. 5 M identities, 50 K transactions Supported Protocols IPv 6 Ready, DHCP/DNS, HTTP/HTTPS, SSL( 1. 0, 2. 0, 3. 0), TLS 1. 0. Commercial Certification Authority, NTP, SNMP, SMTP, AES 128 or 256 Electrical 24 VDC/7 W Listings UL 294, UL 916, C-Tick, FCC Part 15, Sub-part B, Class B, UL 916 C-UL, EN 61000 -63 Reader Protocols Wiegand, OSDP Secure, IP, Clock & Data, Magnetic Stripe, F 2 F, 8 Active Card Formats Confidential Property of Schneider Electric | Page 31 Total “sub controller” capacity per AX-SSC can not exceed 64. Total Reader count per AX-SSC can not exceed 64.
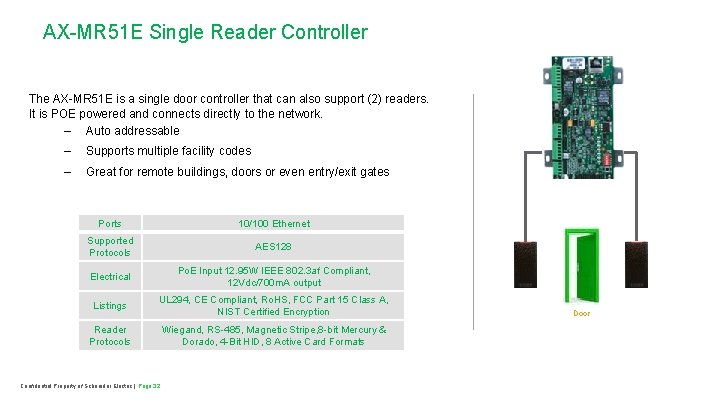
AX-MR 51 E Single Reader Controller The AX-MR 51 E is a single door controller that can also support (2) readers. It is POE powered and connects directly to the network. – Auto addressable – Supports multiple facility codes – Great for remote buildings, doors or even entry/exit gates Ports 10/100 Ethernet Supported Protocols AES 128 Electrical Po. E Input 12. 95 W IEEE 802. 3 af Compliant, 12 Vdc/700 m. A output Listings UL 294, CE Compliant, Ro. HS, FCC Part 15 Class A, NIST Certified Encryption Reader Protocols Wiegand, RS-485, Magnetic Stripe, 8 -bit Mercury & Dorado, 4 -Bit HID, 8 Active Card Formats Confidential Property of Schneider Electric | Page 32 Door
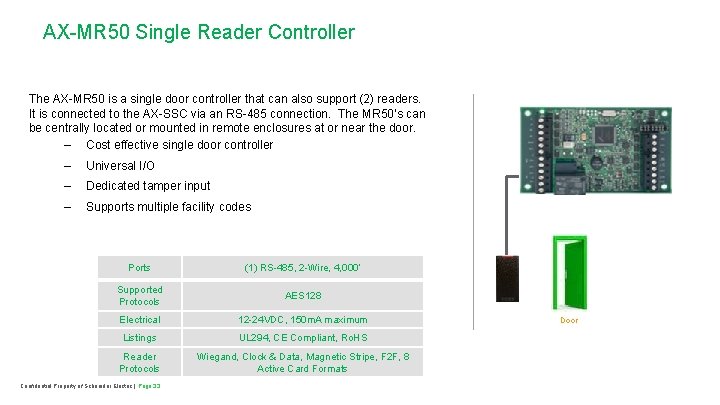
AX-MR 50 Single Reader Controller The AX-MR 50 is a single door controller that can also support (2) readers. It is connected to the AX-SSC via an RS-485 connection. The MR 50’s can be centrally located or mounted in remote enclosures at or near the door. – Cost effective single door controller – Universal I/O – Dedicated tamper input – Supports multiple facility codes Ports (1) RS-485, 2 -Wire, 4, 000’ Supported Protocols AES 128 Electrical 12 -24 VDC, 150 m. A maximum Listings UL 294, CE Compliant, Ro. HS Reader Protocols Wiegand, Clock & Data, Magnetic Stripe, F 2 F, 8 Active Card Formats Confidential Property of Schneider Electric | Page 33 Door
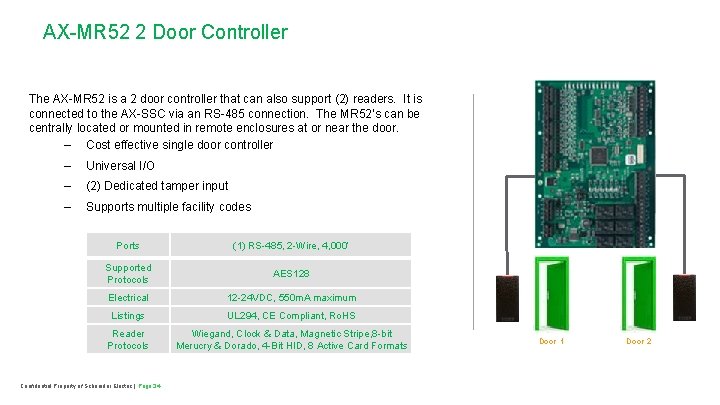
AX-MR 52 2 Door Controller The AX-MR 52 is a 2 door controller that can also support (2) readers. It is connected to the AX-SSC via an RS-485 connection. The MR 52’s can be centrally located or mounted in remote enclosures at or near the door. – Cost effective single door controller – Universal I/O – (2) Dedicated tamper input – Supports multiple facility codes Ports (1) RS-485, 2 -Wire, 4, 000’ Supported Protocols AES 128 Electrical 12 -24 VDC, 550 m. A maximum Listings UL 294, CE Compliant, Ro. HS Reader Protocols Wiegand, Clock & Data, Magnetic Stripe, 8 -bit Merucry & Dorado, 4 -Bit HID, 8 Active Card Formats Confidential Property of Schneider Electric | Page 34 Door 1 Door 2
AX-MR 16 IN – 16 Point Input Controller The AX-MR 16 IN is a 16 point input controller that is connected to the AXSSC via an RS-485 connection. The MR 16 IN can be centrally located or mounted in remote enclosures. – 16 General Purpose Inputs – Localized Processing – Dedicated Tamper Monitoring – Dedicated Power Monitoring – Fail Safe/Secure Operation – On/Off/Pulse/Repeat Commands Ports (1) RS-485 2 -Wire, 4, 000’ Supported Protocols AES 128 Electrical 12 -24 VDC, 350 m. A Maximum Listings UL 294, CE Compliant, Ro. HS Confidential Property of Schneider Electric | Page 35
AX-MR 16 OUT – 16 Point Output Controller The AX-MR 16 OUT is a 16 point output controller that is connected to the AX-SSC via an RS-485 connection. The MR 16 OUT can be centrally located or mounted in remote enclosures. – 16 General Purpose Outputs – Localized Processing – Dedicated Tamper Monitoring – Dedicated Power Monitoring – Fail Safe/Secure Operation – On/Off/Pulse/Repeat Commands – Event or Time Based Operation Ports (1) RS-485 2 -Wire, 4, 000’ Supported Protocols AES 128 Electrical 12 -24 VDC, 1100 m. A Maximum Listings UL 294, CE Compliant, Ro. HS Confidential Property of Schneider Electric | Page 36
Questions? Confidential Property of Schneider Electric | Page 38
- Slides: 34