Access Controls Supervised by Dr Loai Tawalbeh Prepared
Access Controls Supervised by: Dr. Lo’ai Tawalbeh Prepared by: Abeer Saif
Introduction: Access Controls: The security features that control how users and systems communicate and interact with one another. Ø Access: The flow of information between subject and object. Ø Subject: An active entity that requests access to an object or the data in an object. Such as a user, program, or process that accesses an object to accomplish a task. Ø
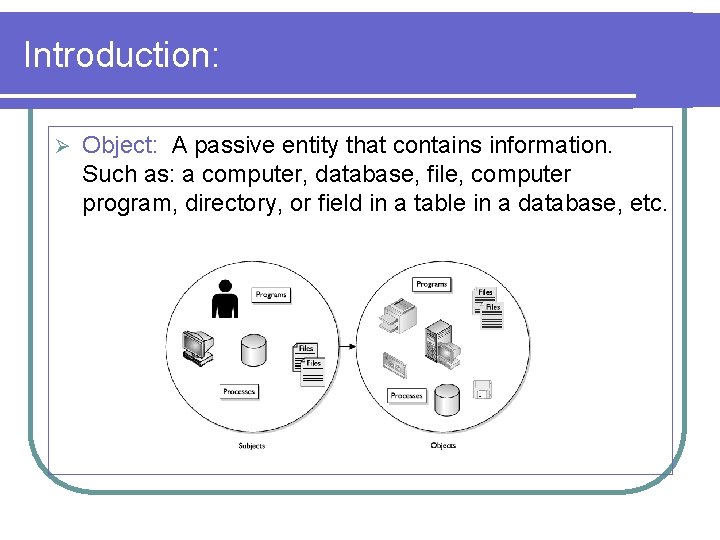
Introduction: Ø Object: A passive entity that contains information. Such as: a computer, database, file, computer program, directory, or field in a table in a database, etc.
Introduction: Access controls are extremely important because they are one of the first lines of defense used to fight against unauthorized access to systems and network resources. Ø Access controls give organizations the ability to control, restrict, monitor, and protect resource availability, integrity, and confidentiality. Ø
Access Control Administration: Two Basic forms: Ø Centralized: One entity is responsible for overseeing access to all corporate resources. Provides a consistent and uniform method of controlling access rights. Ø Decentralized: Gives control of access to the people who are closer to the resources. Has no methods for consistent control, lacks proper consistency.
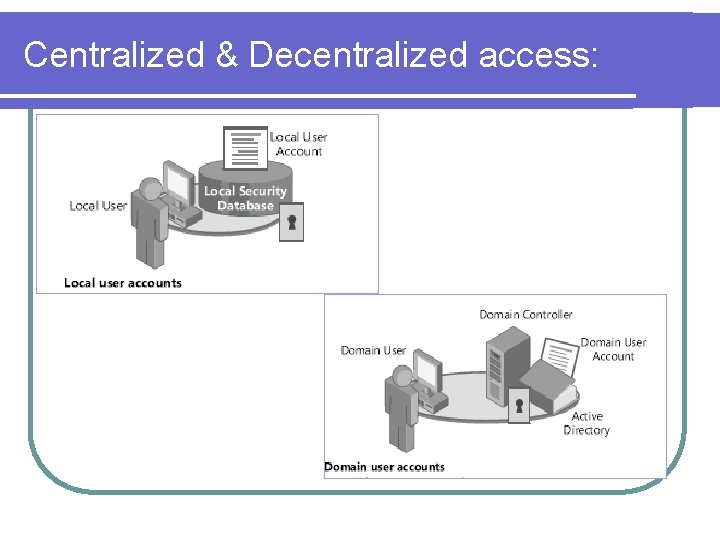
Centralized & Decentralized access:
Access Control methods: Access controls can be implemented at various layers of an organization, network, and individual systems. Ø Three broad categories: Ø Administrative Ø Physical Ø Technical (aka Logical) Ø
Access Controls ISA 2004 Internet Security & Acceleration Server 2004
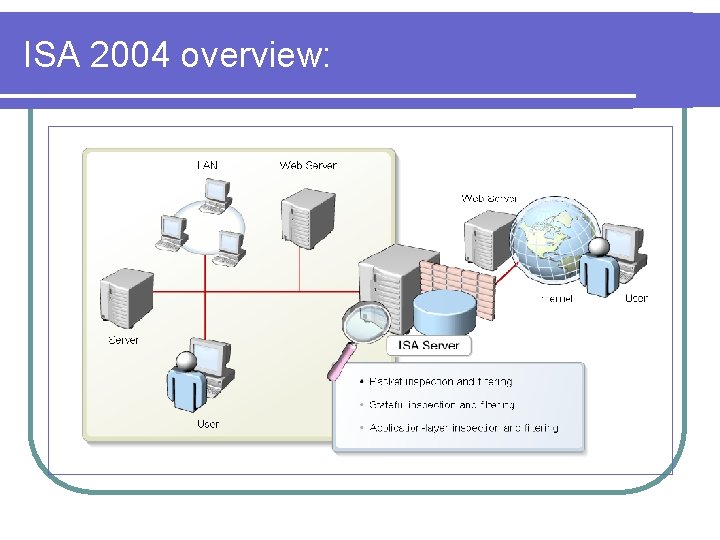
ISA 2004 overview:
ISA 2004 overview: Ø ISA Server 2004 main roles: Ø Ø Ø Firewall. Ø Packet inspection & filtering. Ø Stateful inspection & filtering. Ø Application layer inspection & filtering. VPN server. Ø Unified firewall & VPN Server. Proxy and Caching server. Ø Forward cache. Ø Backward cache.
ISA 2004 overview: Ø ISA Server 2004 as a VPN server: Ø VPN (Virtual Private Network): is a secure network connection created through a public network such as the Internet. Ø Types of VPN connections: VPN clients. Ø Site-Site VPN. Ø Quarantine Control. Ø
ISA 2004 overview: Ø Why use VPN connections: Ø Ø Ø Availability. Cost. Internet Protocol security (IPSec): A set of industrystandard, cryptography based protection services and protocols. IPSec protects all protocols in the Transmission Control Protocol/Internet Protocol (TCP/IP) protocol suite and Internet communications.
ISA 2004 overview: Ø Protocols supported by ISA Server 2004: Ø Point-Point tunneling protocol (PPTP): Uses Microsoft’s encryption (MPPE). Ø Less Complex to set than IPsec. Ø Ø Layer two tunneling protocol (L 2 TP): More secure than PPTP. Ø IPsec concepts more complex. Ø
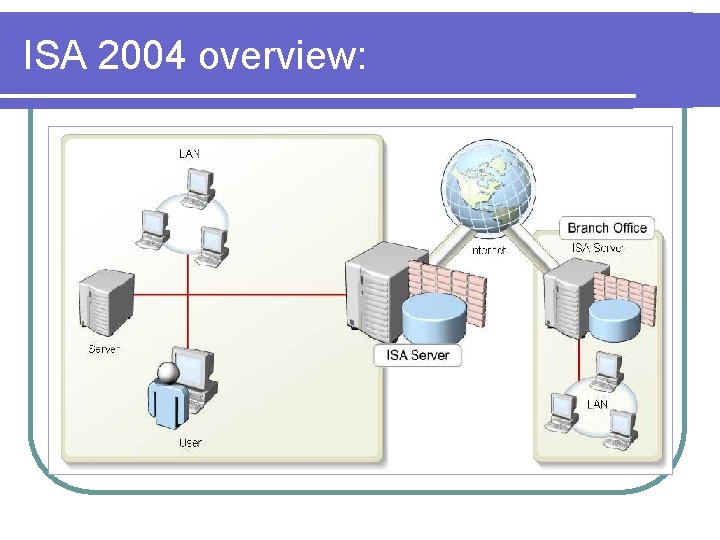
ISA 2004 overview:
References: CISSP All-in-One Exam Guide. Ø Installing, Configuring, and Administering Microsoft Windows XP Professional. Ø MCSA/MCSE Self-Paced Training Kit (Exam 70 -270). Ø Implementing Microsoft Internet Security and Acceleration Server 2004. MCSA/MCSE Self-Paced Training Kit (Exam 70 -350).
- Slides: 15