Access Control Lists and Wildcard Masks Cisco Semester
- Slides: 36
Access Control Lists and Wildcard Masks Cisco Semester 2 © 2001 by The Mc. Graw-Hill Companies, Inc. All rights reserved.
Access Lists • Lists of conditions that control access both to and from network segments • Can cause the router to analyze every packet crossing an interface in the specified direction and take action accordingly 2
Rules a packet follows when it’s being compared with an ACL • Always compared with each line of the ACL in sequential order (line 1, 2, 3…) • Compared only till a match is made • There is an implicit “deny” at the end of each ACL – If a packet does not match up to any lines in the ACL, it’ll be discarded 3
Standard ACLs • Use only the source IP address in an IP packet • Permits or denies an entire suit of protocols • You create a standard IP ACL by using the access list numbers 1 -99 • Example: • Router. A(config)# access-list 10 deny host 172. 16. 30. 2 Or • Router. A(config)# access-list 10 deny 172. 16. 30. 2 4
ACL guidelines • You can only assign one ACL per interface, per protocol, or per direction – (only one inbound ACL and one outbound ACL per interface) • Organize your access lists so that the more specific tests are at the top of the access list • Anytime a new list is added to the ACL, it will be placed at the bottom of the list • You cannot remove one line from an ACL. – If you try it, it will remove the entire list. The only exception is when using named ACLs 5
ACL guidelines (cont. ) • Unless your ACL ends with a permit any command, all packets will be discarded if they do not meet any of the lists’ tests – Every list should have at least one permit statement, or you might as well shut the interface down. • Create access lists and then apply them to an interface. 6
ACL guidelines (cont. ) • Access lists are designed to filter traffic going through the router. – They will not filter traffic originated from the router • Place IP standard access lists as close to the destination as possible • Place IP extended access lists as close to the source as possible 7
Wildcards Masks • Wildcards are used with the host or network address to tell the router a range of available address to filter – To specify a host – 172. 16. 30. 5 0. 0 (the four zeros represent each octet of the address). Whenever a zero is present, it means that octet in the address must match exactly. 8
Wildcards Masks • To specify that an octet can be any value, the value of 255 is used – 172. 16. 30. 0. 0. 255 • This tells the router to match up the first 3 octets exactly, but the 4 th octet can be any value 9
The “Wildcard Mask” Explained –The “wildcard mask” has no functional relationship with the subnet mask. –However, in many cases the subnet mask can be used to derive the wildcard mask. • For example, you want to filter traffic from all hosts on the 192. 168. 1. 0/24 subnet. –The subnet mask is 255. 0 –To find the wildcard mask, take the inverse of the subnet mask. –The wildcard mask is 0. 0. 0. 255. 10
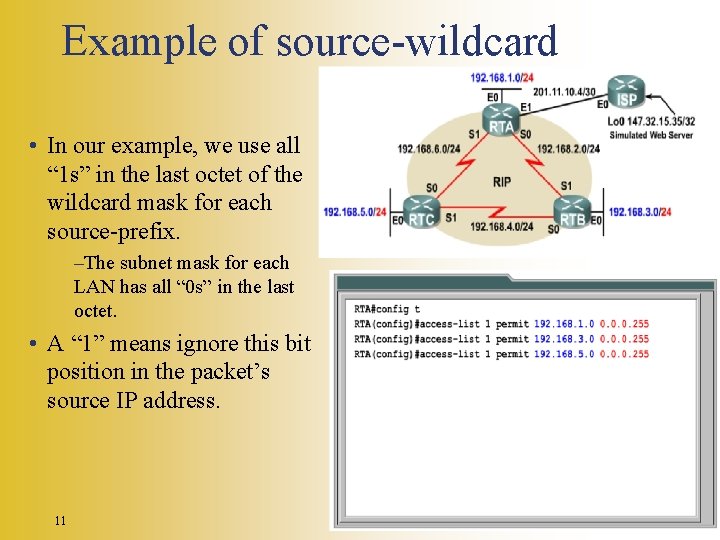
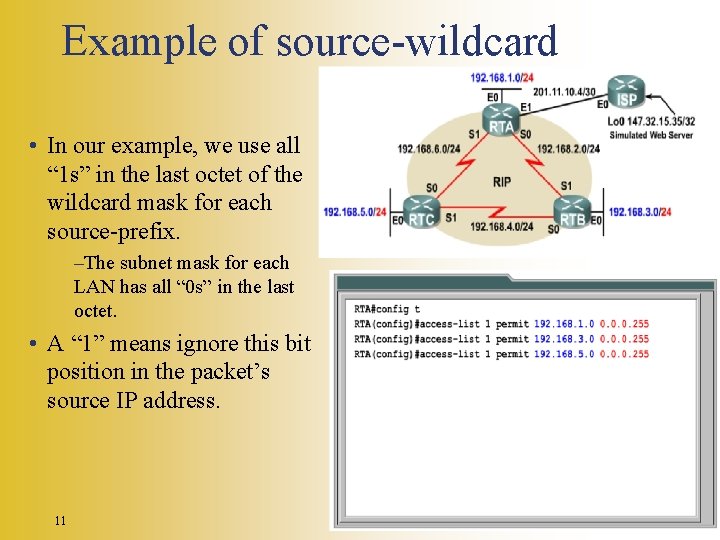
Example of source-wildcard • In our example, we use all “ 1 s” in the last octet of the wildcard mask for each source-prefix. –The subnet mask for each LAN has all “ 0 s” in the last octet. • A “ 1” means ignore this bit position in the packet’s source IP address. 11
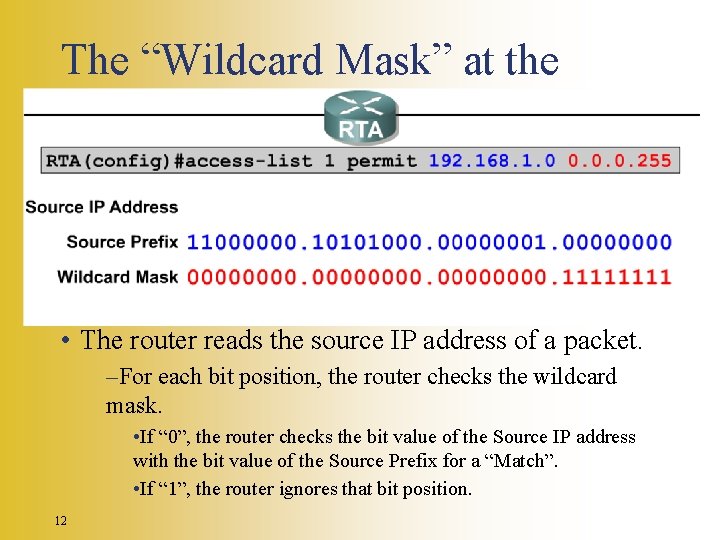
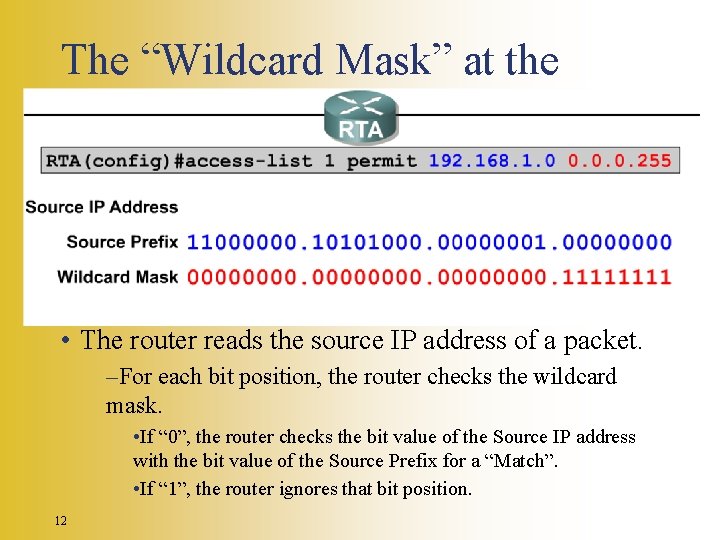
The “Wildcard Mask” at the Bit Level • The router reads the source IP address of a packet. –For each bit position, the router checks the wildcard mask. • If “ 0”, the router checks the bit value of the Source IP address with the bit value of the Source Prefix for a “Match”. • If “ 1”, the router ignores that bit position. 12
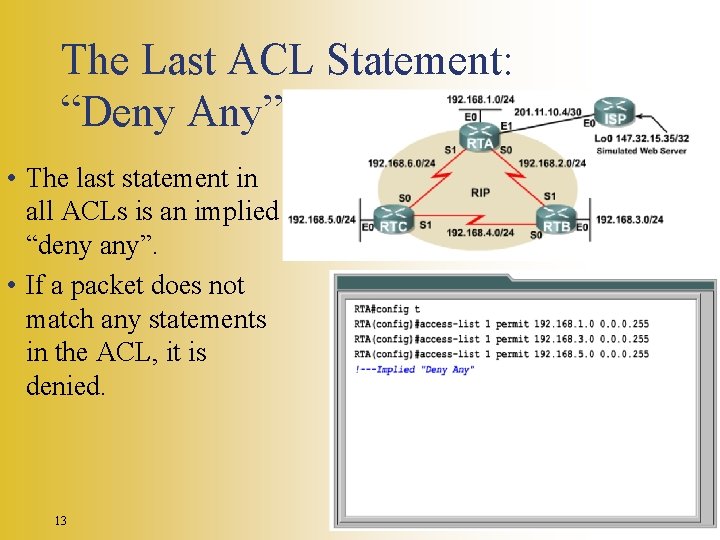
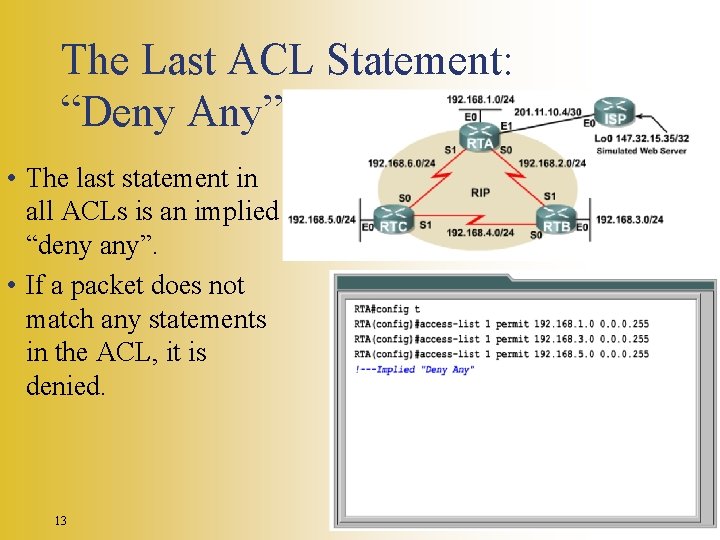
The Last ACL Statement: “Deny Any” • The last statement in all ACLs is an implied “deny any”. • If a packet does not match any statements in the ACL, it is denied. 13
Apply the ACL • An ACL cannot filter traffic until it has been applied to an interface. –This is a security feature of the IOS. • You can safely write ACL statements without having the statements take an immediate affect on traffic. • The command syntax is the same for both Standard and Extended IP ACLs. 14
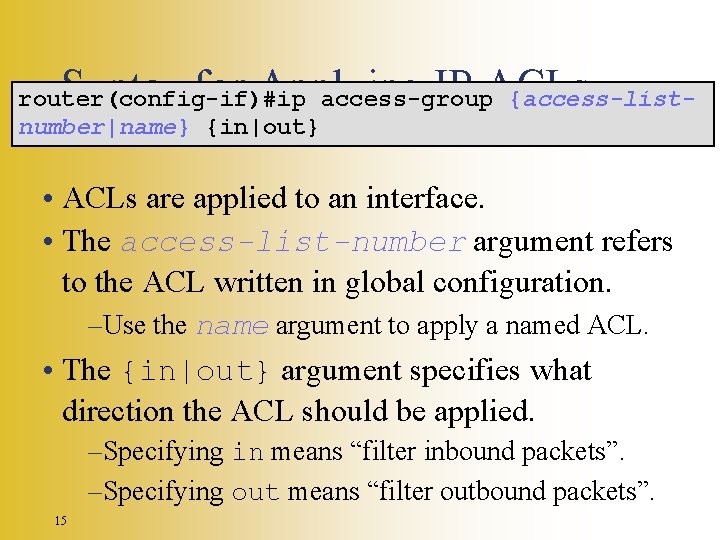
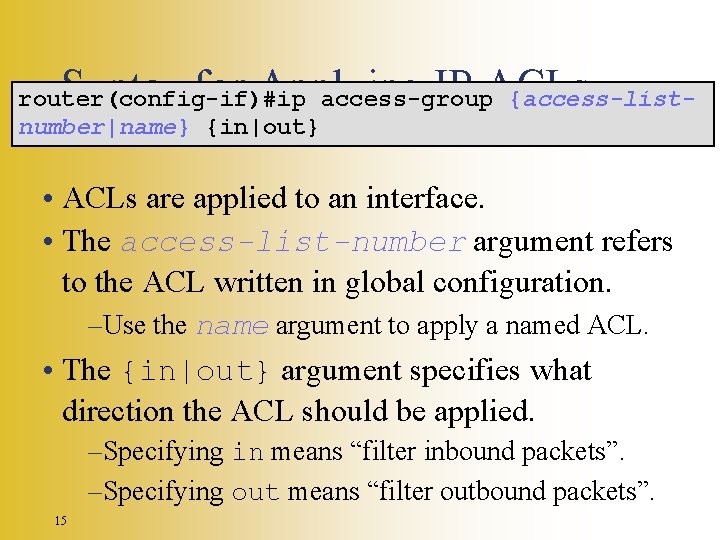
Syntax for Applying IP ACLs router(config-if)#ip access-group {access-listnumber|name} {in|out} • ACLs are applied to an interface. • The access-list-number argument refers to the ACL written in global configuration. –Use the name argument to apply a named ACL. • The {in|out} argument specifies what direction the ACL should be applied. –Specifying in means “filter inbound packets”. –Specifying out means “filter outbound packets”. 15
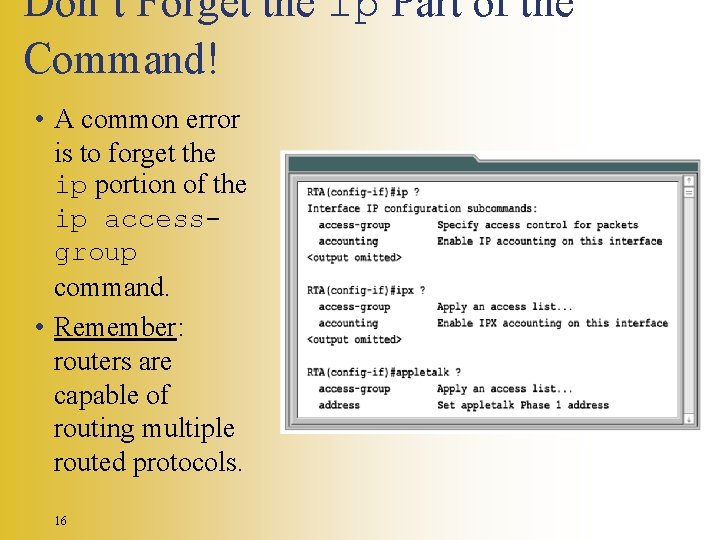
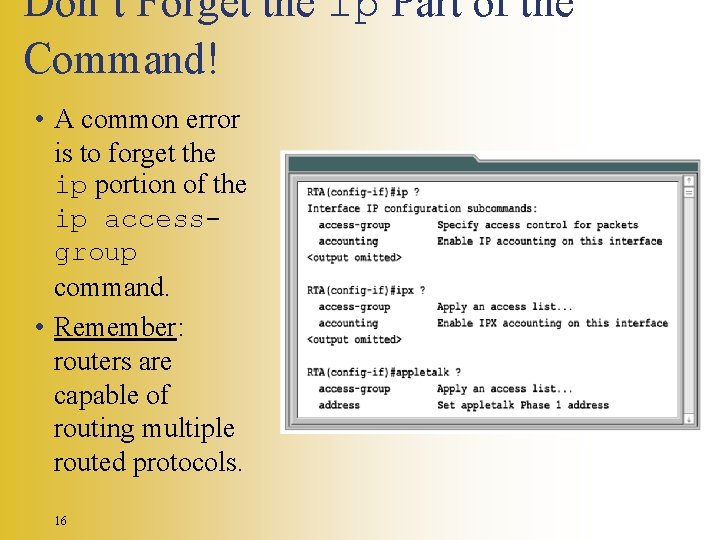
Don’t Forget the ip Part of the Command! • A common error is to forget the ip portion of the ip accessgroup command. • Remember: routers are capable of routing multiple routed protocols. 16
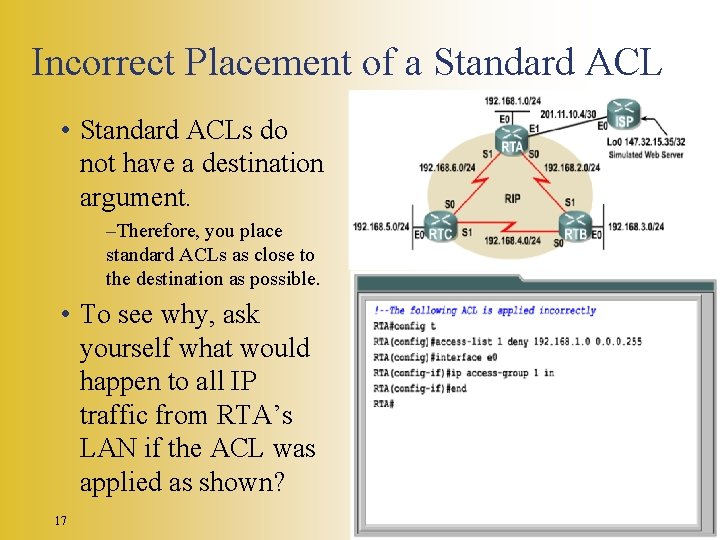
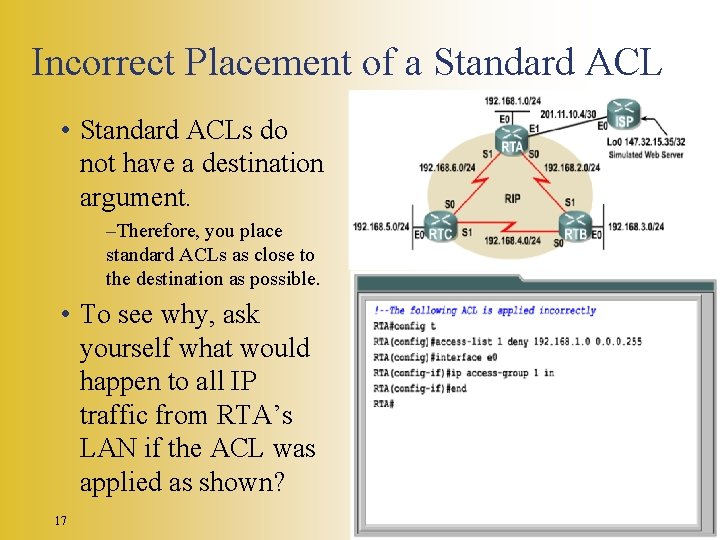
Incorrect Placement of a Standard ACL • Standard ACLs do not have a destination argument. –Therefore, you place standard ACLs as close to the destination as possible. • To see why, ask yourself what would happen to all IP traffic from RTA’s LAN if the ACL was applied as shown? 17
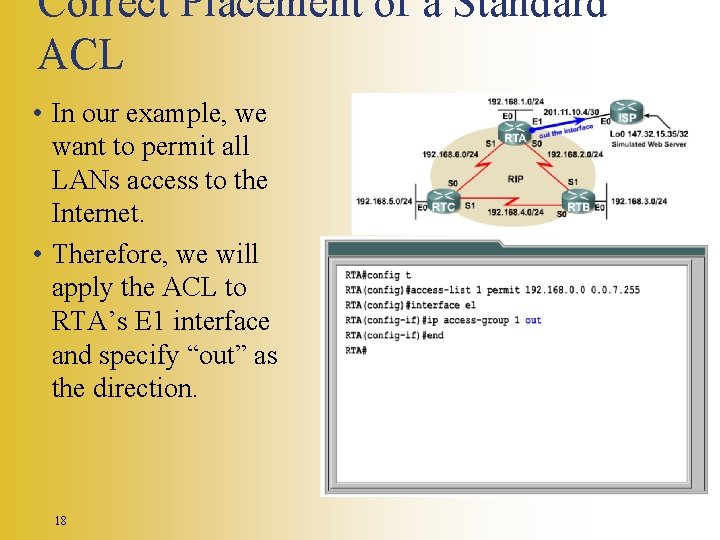
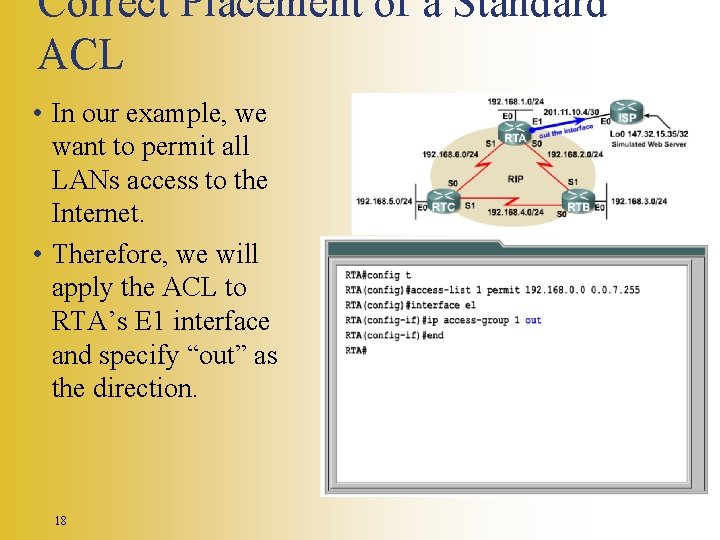
Correct Placement of a Standard ACL • In our example, we want to permit all LANs access to the Internet. • Therefore, we will apply the ACL to RTA’s E 1 interface and specify “out” as the direction. 18
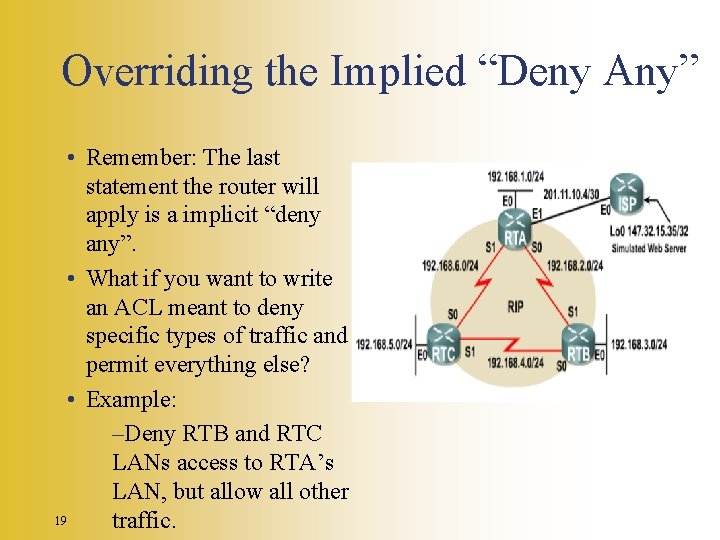
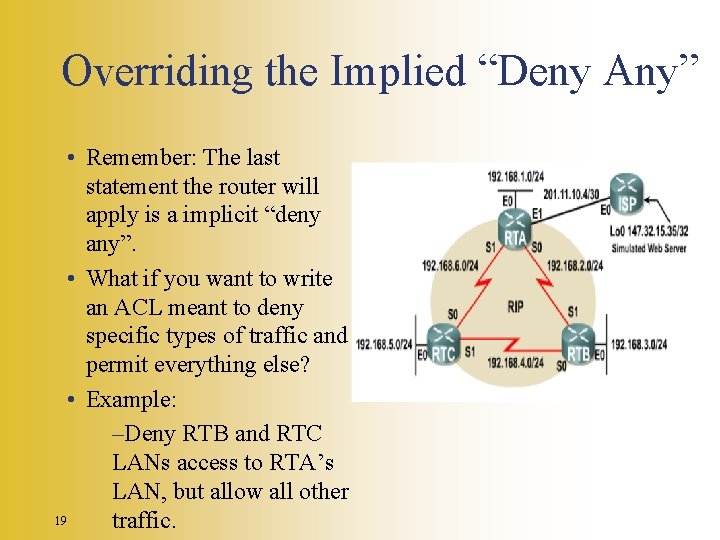
Overriding the Implied “Deny Any” • Remember: The last statement the router will apply is a implicit “deny any”. • What if you want to write an ACL meant to deny specific types of traffic and permit everything else? • Example: –Deny RTB and RTC LANs access to RTA’s LAN, but allow all other 19 traffic.
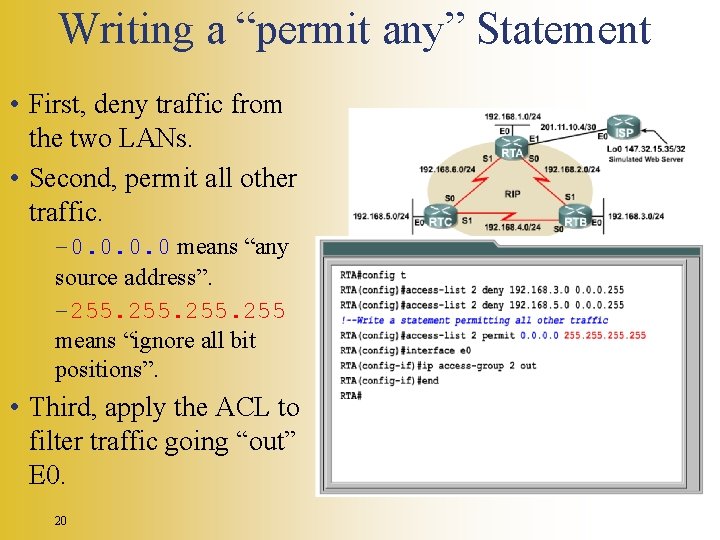
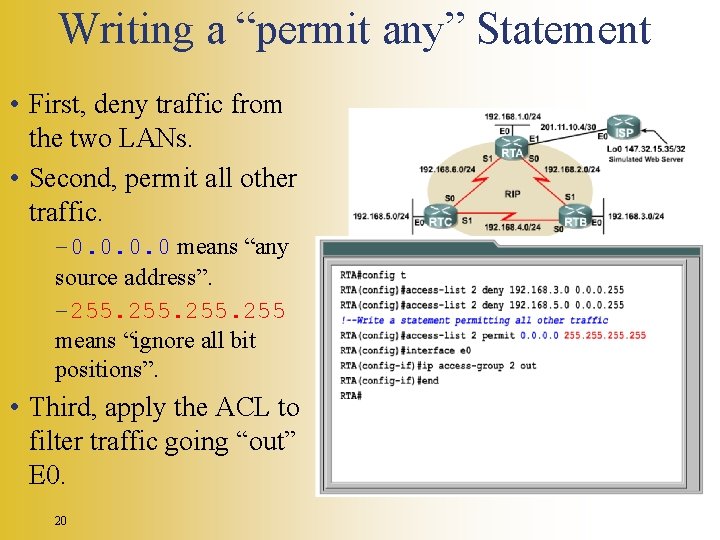
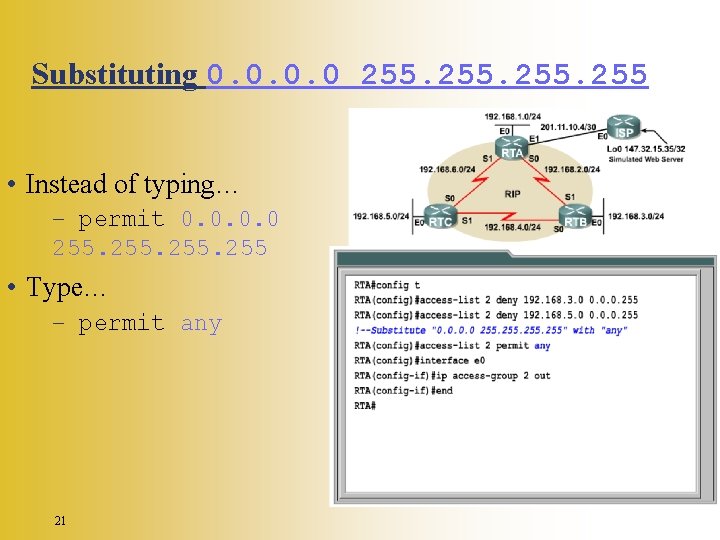
Writing a “permit any” Statement • First, deny traffic from the two LANs. • Second, permit all other traffic. – 0. 0 means “any source address”. – 255 means “ignore all bit positions”. • Third, apply the ACL to filter traffic going “out” E 0. 20
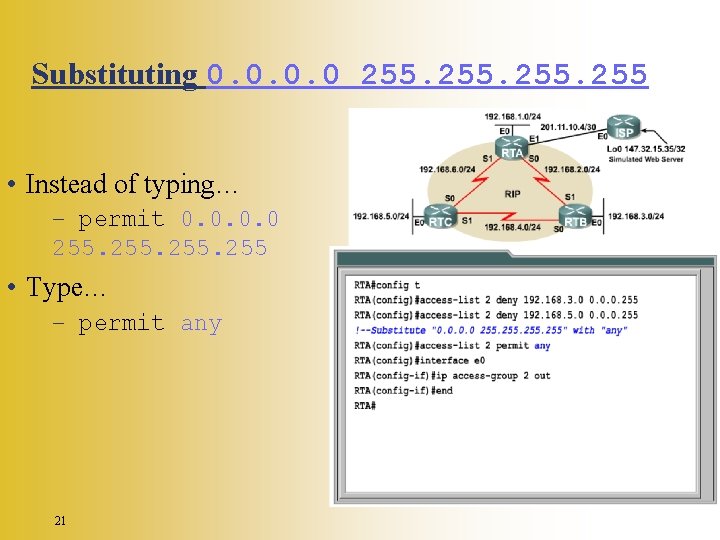
Substituting 0. 0 255 • Instead of typing… – permit 0. 0 255 • Type… – permit any 21
Filtering Traffic From a Single Host • What if a particular user is abusing Internet privileges? –How would you deny that host’s IP address, yet still permit everyone else? –Remember: A wildcard mask tells the router what bits to check. 22
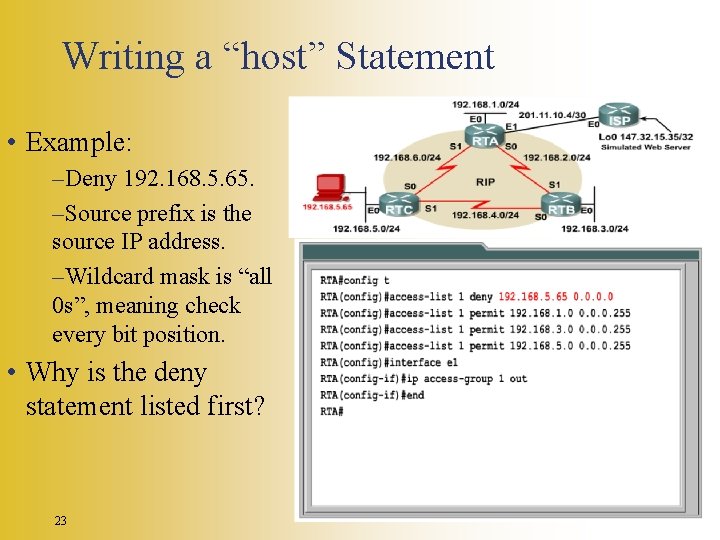
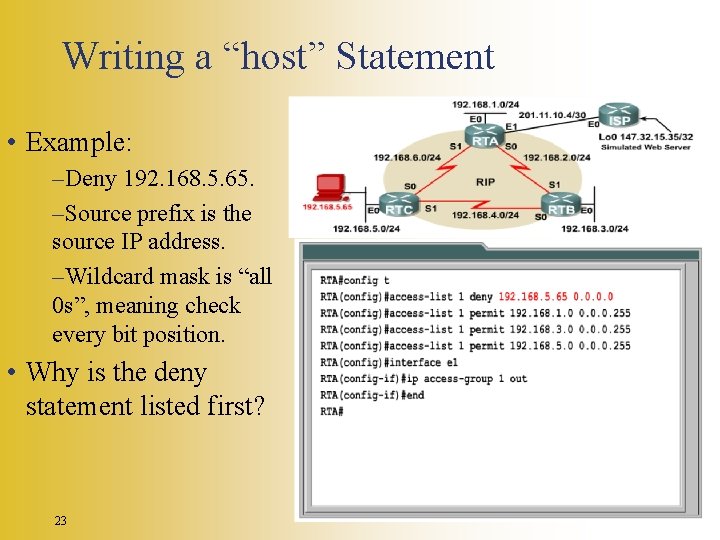
Writing a “host” Statement • Example: –Deny 192. 168. 5. 65. –Source prefix is the source IP address. –Wildcard mask is “all 0 s”, meaning check every bit position. • Why is the deny statement listed first? 23
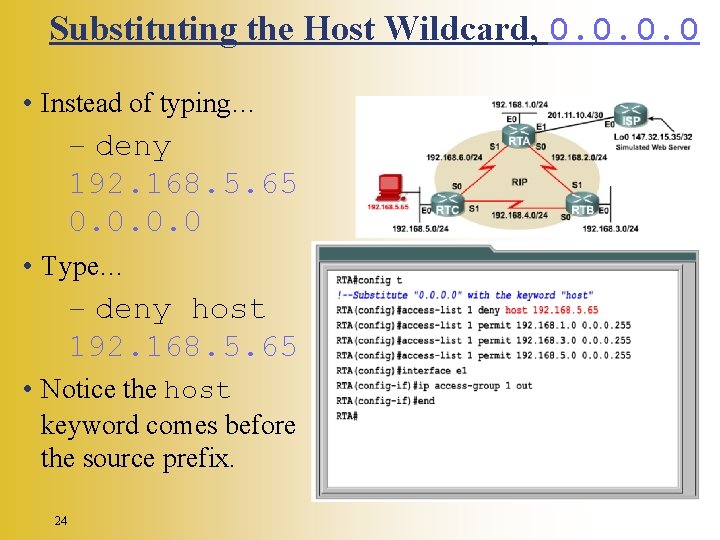
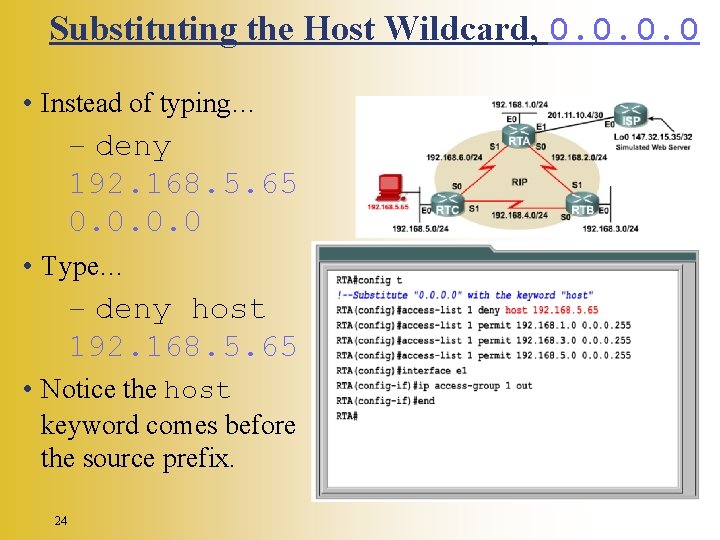
Substituting the Host Wildcard, 0. 0 • Instead of typing… – deny 192. 168. 5. 65 0. 0 • Type… – deny host 192. 168. 5. 65 • Notice the host keyword comes before the source prefix. 24
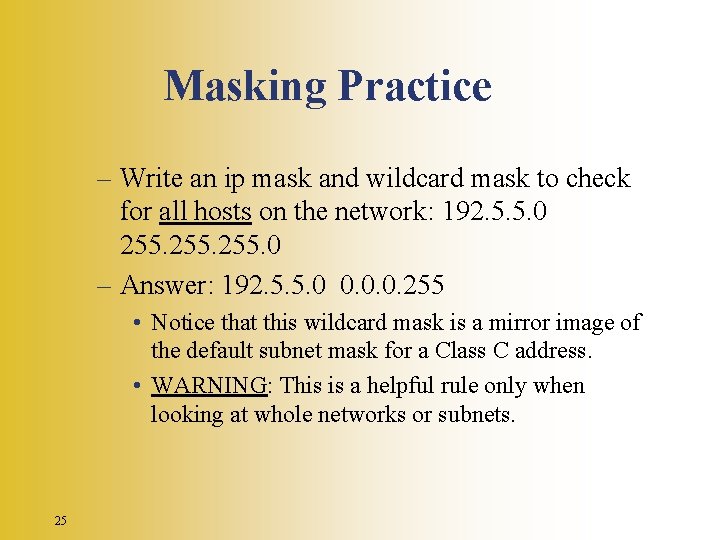
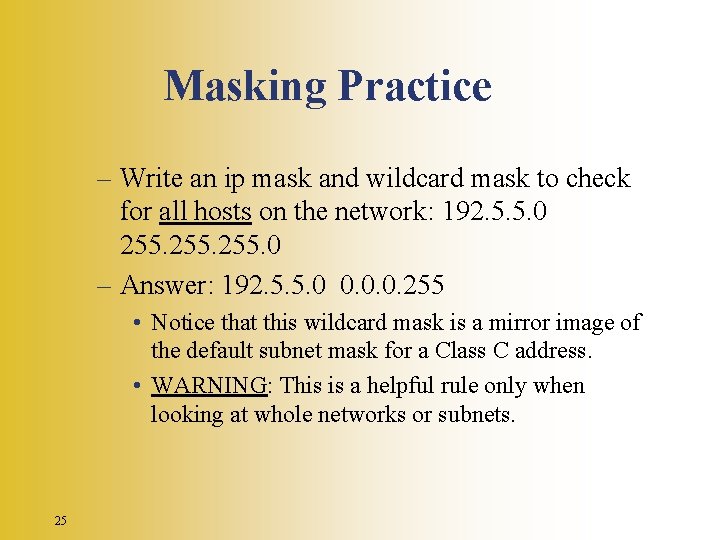
Masking Practice – Write an ip mask and wildcard mask to check for all hosts on the network: 192. 5. 5. 0 255. 0 – Answer: 192. 5. 5. 0 0. 0. 0. 255 • Notice that this wildcard mask is a mirror image of the default subnet mask for a Class C address. • WARNING: This is a helpful rule only when looking at whole networks or subnets. 25
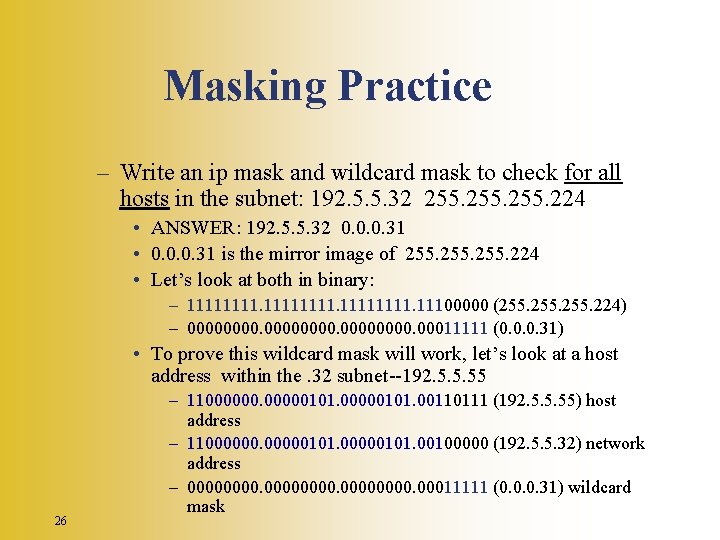
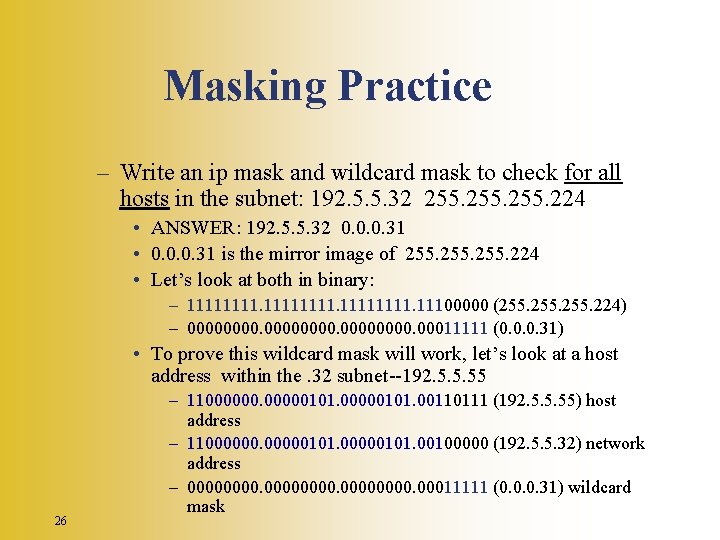
Masking Practice – Write an ip mask and wildcard mask to check for all hosts in the subnet: 192. 5. 5. 32 255. 224 • ANSWER: 192. 5. 5. 32 0. 0. 0. 31 • 0. 0. 0. 31 is the mirror image of 255. 224 • Let’s look at both in binary: – 11111111. 11100000 (255. 224) – 00000000. 00011111 (0. 0. 0. 31) • To prove this wildcard mask will work, let’s look at a host address within the. 32 subnet--192. 5. 5. 55 26 – 11000000101. 00110111 (192. 5. 5. 55) host address – 11000000101. 00100000 (192. 5. 5. 32) network address – 00000000. 00011111 (0. 0. 0. 31) wildcard mask
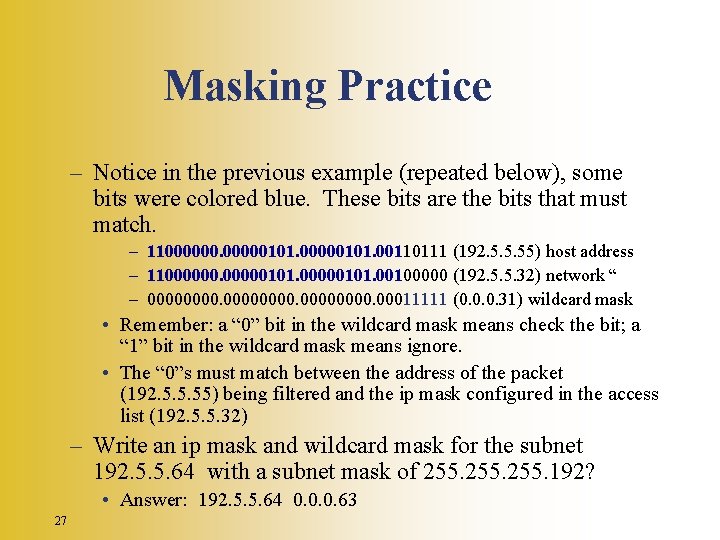
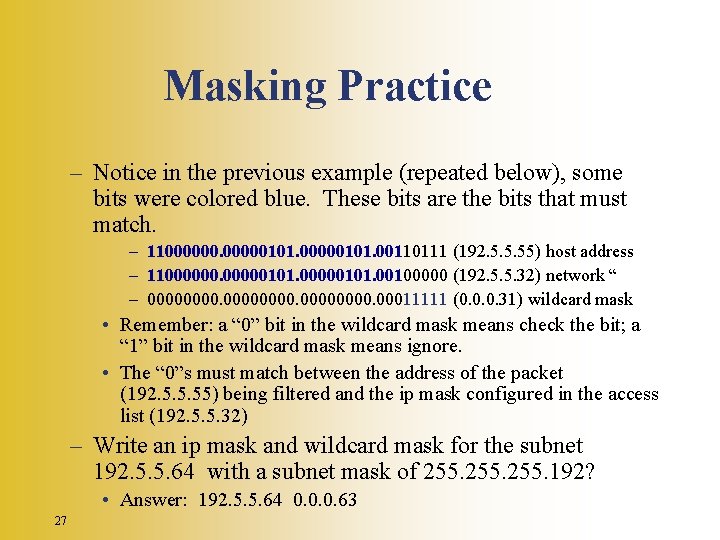
Masking Practice – Notice in the previous example (repeated below), some bits were colored blue. These bits are the bits that must match. – 11000000101. 00110111 (192. 5. 5. 55) host address – 11000000101. 00100000 (192. 5. 5. 32) network “ – 00000000. 00011111 (0. 0. 0. 31) wildcard mask • Remember: a “ 0” bit in the wildcard mask means check the bit; a “ 1” bit in the wildcard mask means ignore. • The “ 0”s must match between the address of the packet (192. 5. 5. 55) being filtered and the ip mask configured in the access list (192. 5. 5. 32) – Write an ip mask and wildcard mask for the subnet 192. 5. 5. 64 with a subnet mask of 255. 192? • Answer: 192. 5. 5. 64 0. 0. 0. 63 27
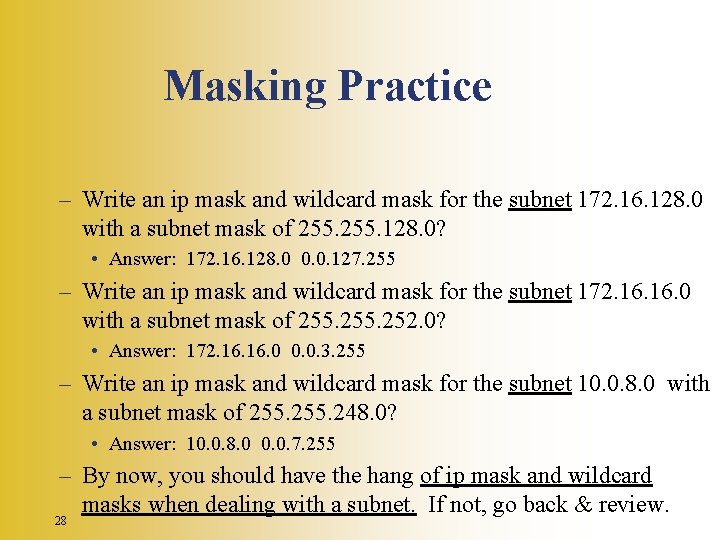
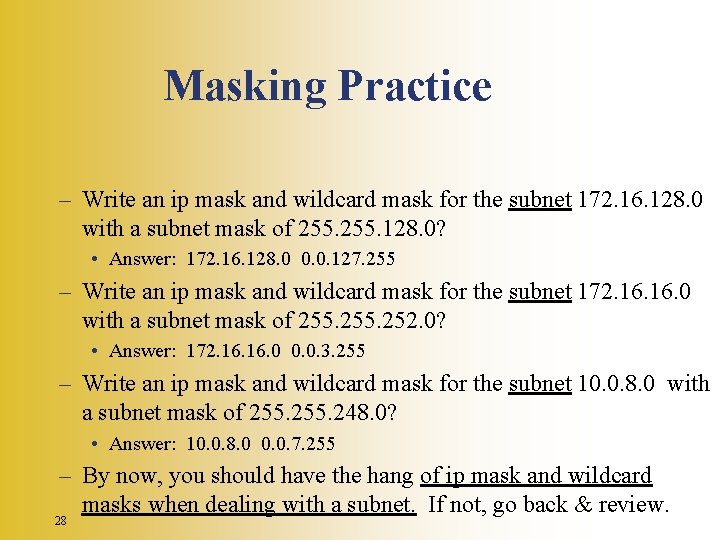
Masking Practice – Write an ip mask and wildcard mask for the subnet 172. 16. 128. 0 with a subnet mask of 255. 128. 0? • Answer: 172. 16. 128. 0 0. 0. 127. 255 – Write an ip mask and wildcard mask for the subnet 172. 16. 0 with a subnet mask of 255. 252. 0? • Answer: 172. 16. 0 0. 0. 3. 255 – Write an ip mask and wildcard mask for the subnet 10. 0. 8. 0 with a subnet mask of 255. 248. 0? • Answer: 10. 0. 8. 0 0. 0. 7. 255 – By now, you should have the hang of ip mask and wildcard masks when dealing with a subnet. If not, go back & review. 28
Wildcards Masks and Ranges • Used with ACLS to specify a host, network, or part of a network. • It’s helpful to understand block sizes – Used to specify a range of addresses. • Some block sizes available – – – 29 4 8 16 32 64
Wildcards Masks and Ranges • When you need to specify a range of addresses, you choose the closest block size for your needs. – if you need to specify 34 networks, you need a black size of 64 – If you need to specify 18 hosts, you need a block size of 32 – If you only specify two networks, then you can use a block size of 5 30
Wildcards Masks and Ranges • What if you want to specify only a small range of subnets? - use a block size • Example: block access to part of a network from 172. 16. 8. 0 thru. 172. 16. 15. 0 – Use block size of 8 (0. 0. 7. 255) – Notice that the wildcard is one number less than the block size. 31
Masking a Host Range – You’ll need to be able to deny a portion of a subnet while permitting another. – To mask a range of host within a subnet, it is often necessary to work on the binary level. – For example, students use the range 192. 5. 5. 0 to 192. 5. 5. 127 and teachers use the range 192. 5. 5. 128 to 192. 5. 5. 255. Both groups are on network 192. 5. 5. 0 255. 0 – How do you write an ip mask and wildcard mask to deny one group, yet permit another? 32
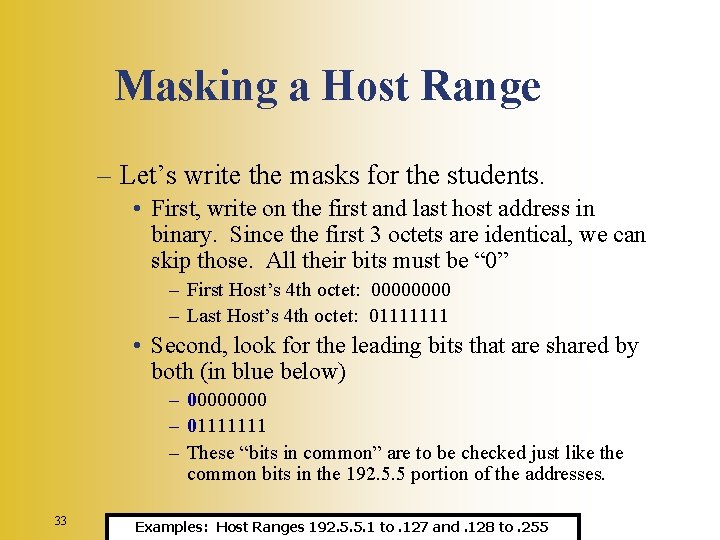
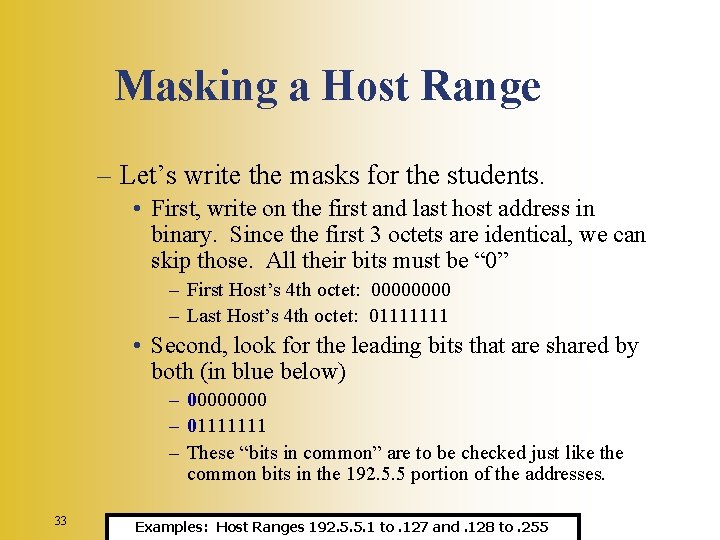
Masking a Host Range – Let’s write the masks for the students. • First, write on the first and last host address in binary. Since the first 3 octets are identical, we can skip those. All their bits must be “ 0” – First Host’s 4 th octet: 0000 – Last Host’s 4 th octet: 01111111 • Second, look for the leading bits that are shared by both (in blue below) – 0000 – 01111111 – These “bits in common” are to be checked just like the common bits in the 192. 5. 5 portion of the addresses. 33 Examples: Host Ranges 192. 5. 5. 1 to. 127 and. 128 to. 255
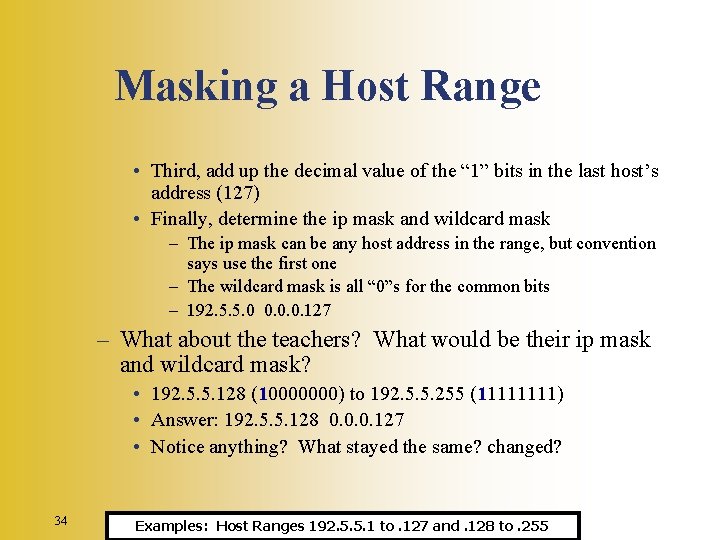
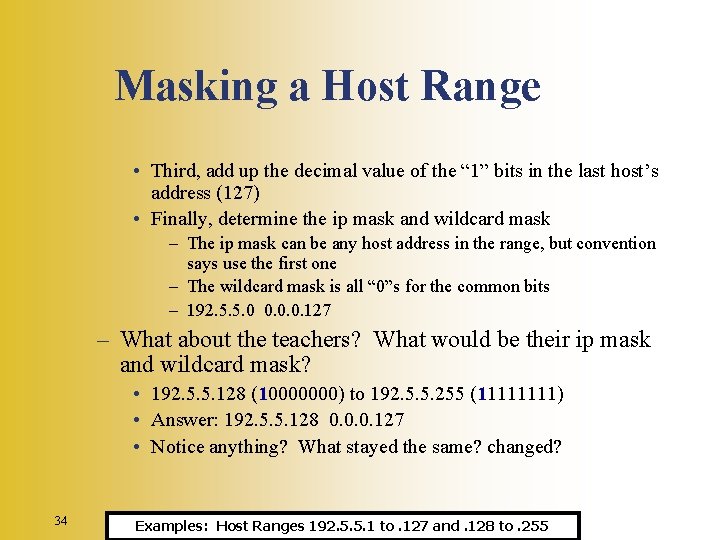
Masking a Host Range • Third, add up the decimal value of the “ 1” bits in the last host’s address (127) • Finally, determine the ip mask and wildcard mask – The ip mask can be any host address in the range, but convention says use the first one – The wildcard mask is all “ 0”s for the common bits – 192. 5. 5. 0 0. 0. 0. 127 – What about the teachers? What would be their ip mask and wildcard mask? • 192. 5. 5. 128 (10000000) to 192. 5. 5. 255 (1111) • Answer: 192. 5. 5. 128 0. 0. 0. 127 • Notice anything? What stayed the same? changed? 34 Examples: Host Ranges 192. 5. 5. 1 to. 127 and. 128 to. 255
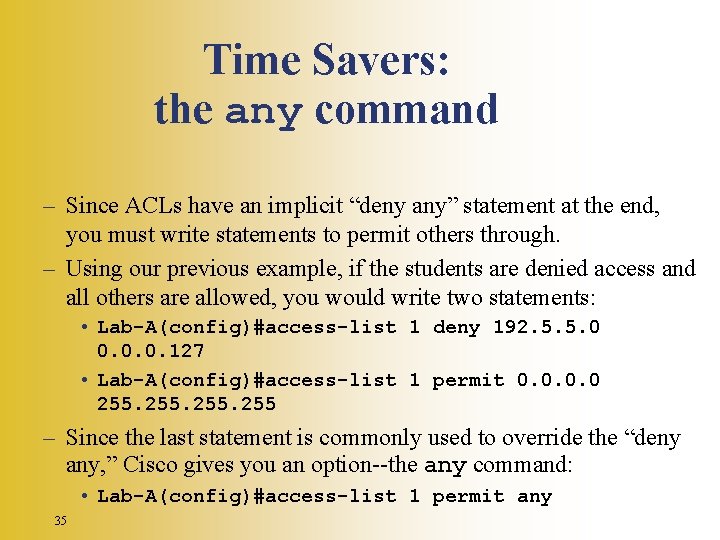
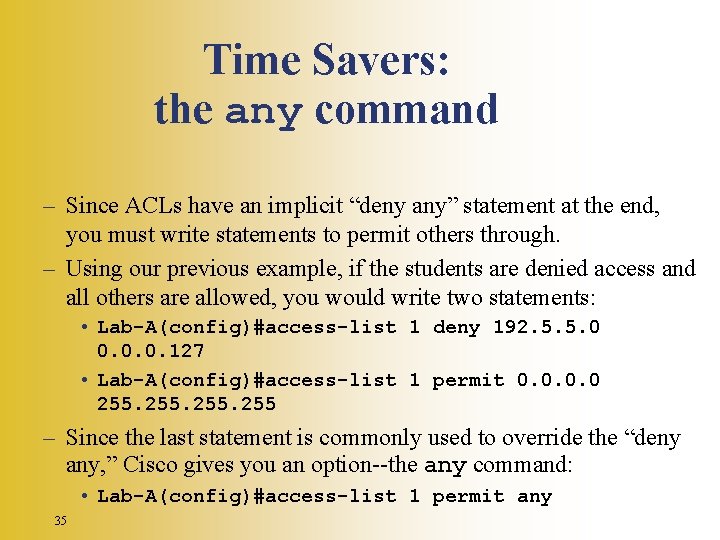
Time Savers: the any command – Since ACLs have an implicit “deny any” statement at the end, you must write statements to permit others through. – Using our previous example, if the students are denied access and all others are allowed, you would write two statements: • Lab-A(config)#access-list 1 deny 192. 5. 5. 0 0. 0. 0. 127 • Lab-A(config)#access-list 1 permit 0. 0 255 – Since the last statement is commonly used to override the “deny any, ” Cisco gives you an option--the any command: • Lab-A(config)#access-list 1 permit any 35
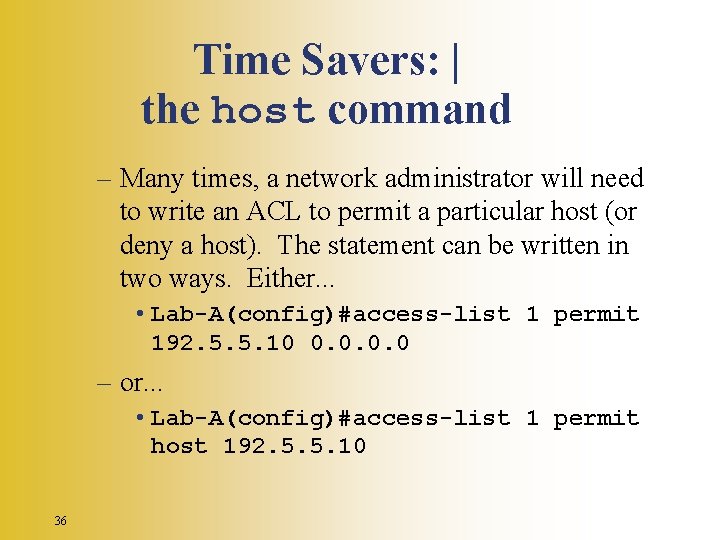
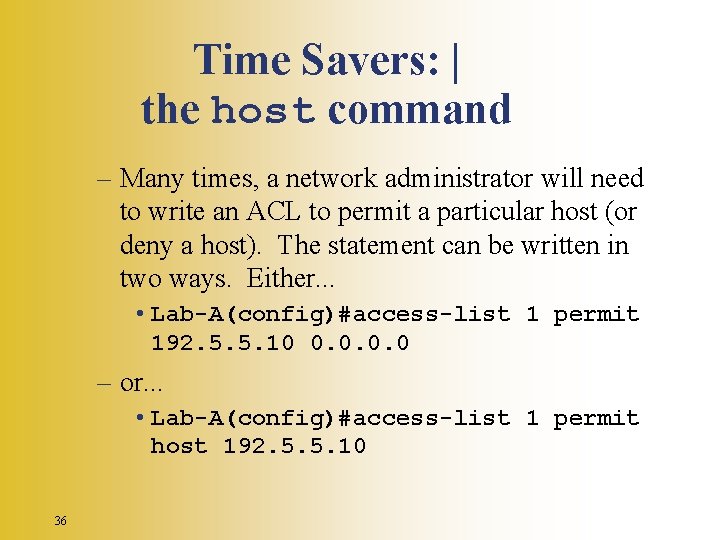
Time Savers: | the host command – Many times, a network administrator will need to write an ACL to permit a particular host (or deny a host). The statement can be written in two ways. Either. . . • Lab-A(config)#access-list 1 permit 192. 5. 5. 10 0. 0 – or. . . • Lab-A(config)#access-list 1 permit host 192. 5. 5. 10 36