about us Ive been involved in IT for
about us § I’ve been involved in IT for 19 yrs § GSEC, GMON and Security+ § Contact info: § Email: nate 648@gmail. com § Linked. In: https: //www. linkedin. com/in/natesykes § Twitter - @n 8 sec § Grant has been involved in IT for 9 yrs § CCNA-Voice, CCDP, CCNP, Security+, GPEN § Contact info: § Email: sims. grant@gmail. com § Twitter: @Chiefriver. Sims § Youtube Channel, Chief. River: https: //www. youtube. com/channel/UCl. BQQRz. LNKt 9 XSMe_Gr. VMEQ § Work at a R&K < 100 employees § § Work with Do. D, Healthcare and Higher-Ed clients Host our Saa. S Application Manage ~50 servers and ~100 VMs Network includes remote offices as well as remote users
topics § How we used network architecture and open source sensors to successfully transform our security posture from static defense to prevent/detect/respond § Why we chose to go the open source route § The capabilities of Security Onion (https: //security-onionsolutions. github. io/security-onion/ ) § The pros v. cons of open source and what to watch out for § Using Security Onion to handle an incident
Along time ago in a galaxy far, far away…

Strictly a Prevent Defense

Will inevitably FAIL
2. 5 years ago we… • Relied mainly on Antivirus for detection • Had a SIEM but didn’t get much use out of it • Incident response consisted of wipe/reimage, no real way to determine how something got in, what it did, or how to prevent it from reoccurring

No real visibility into the network
Some of you might be in the same boat…
Whose Incident Response process consists of “Wipe the machine”?
Defeat is a state of mind; no one is ever defeated until defeat has been accepted as a reality. - Bruce Lee
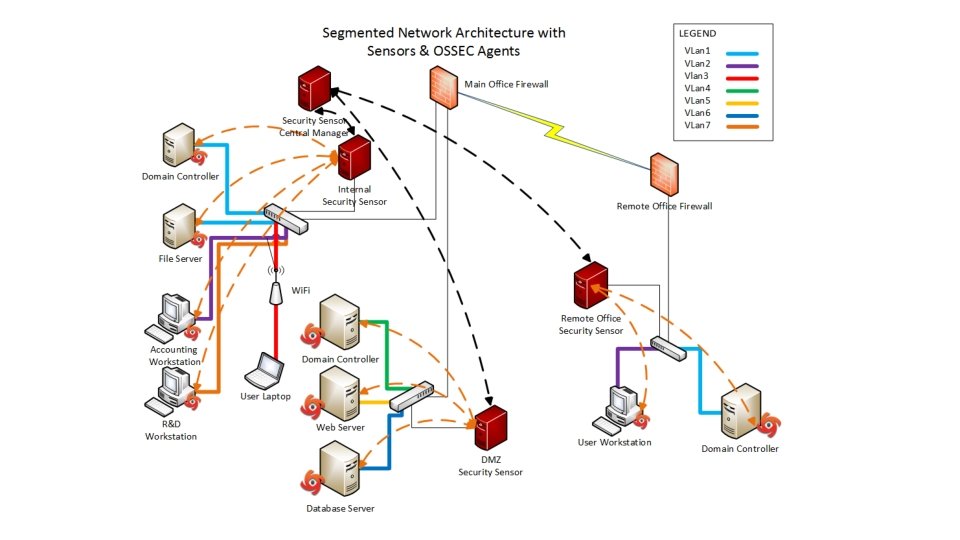
How do we defend our Network? § Network Architecture § Distributed Army of Security Onion Sensors
Network Architecture Battle Prep: Read This! • The Practice of Network Security Monitoring, Richard Bejtlich
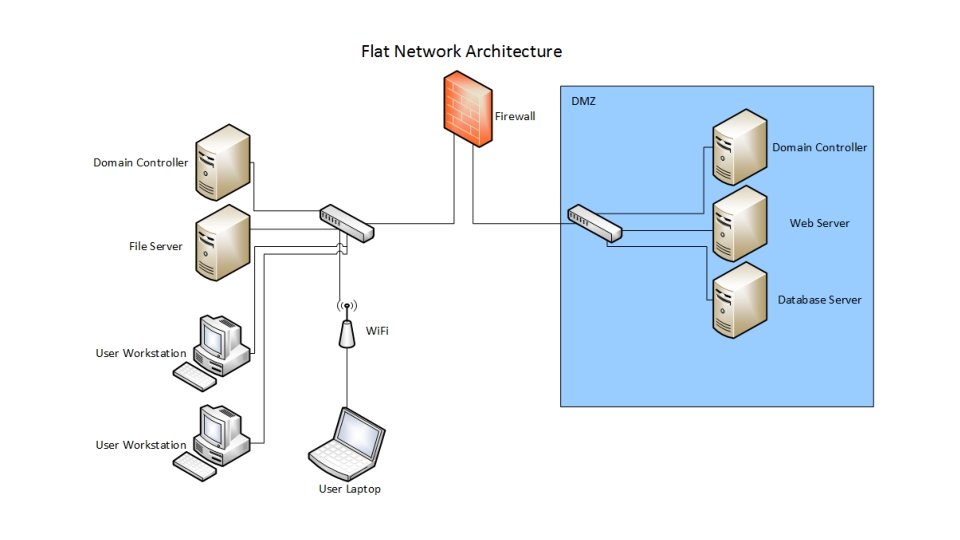
!["Verizon consultants were able to … communicate directly with cash registers in [Target] checkout "Verizon consultants were able to … communicate directly with cash registers in [Target] checkout](http://slidetodoc.com/presentation_image/55be5bb4ab4caf8a4413f3a53768a811/image-15.jpg)
"Verizon consultants were able to … communicate directly with cash registers in [Target] checkout lanes after compromising a deli meat scale located in a different store. " http: //krebsonsecurity. com/2015/09/inside-target-corpdays-after-2013 -breach/
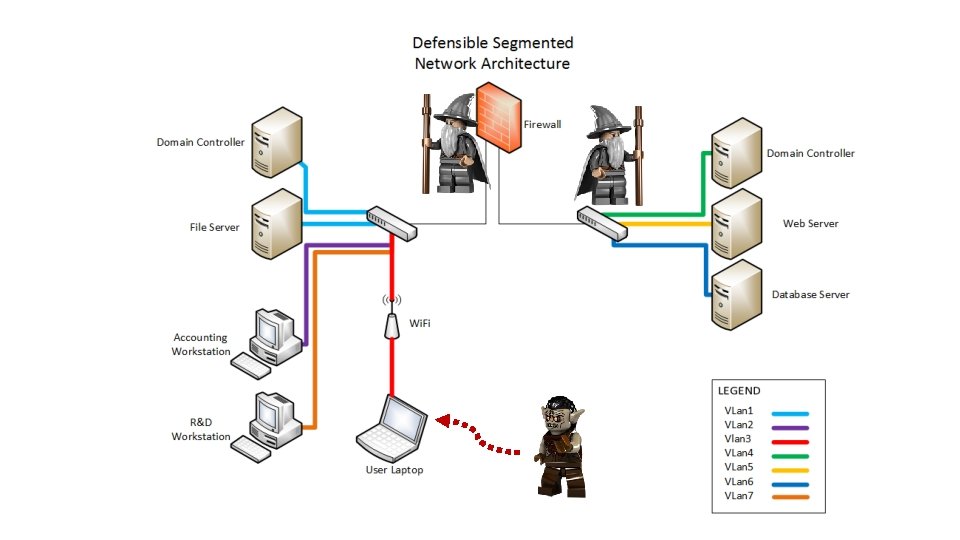
Why Segment? Attackers get a foothold and then PIVOT MERCILESSLY
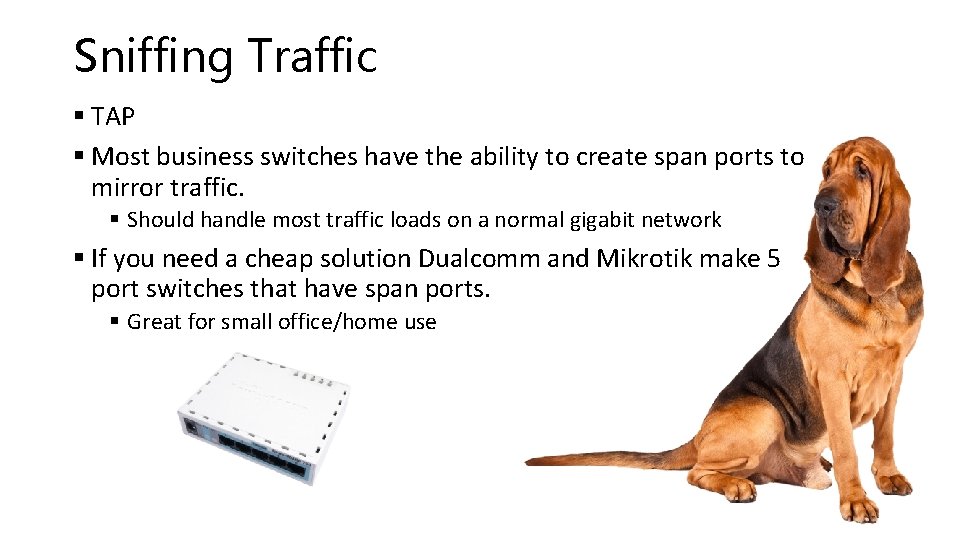
Sniffing Traffic § TAP § Most business switches have the ability to create span ports to mirror traffic. § Should handle most traffic loads on a normal gigabit network § If you need a cheap solution Dualcomm and Mikrotik make 5 port switches that have span ports. § Great for small office/home use
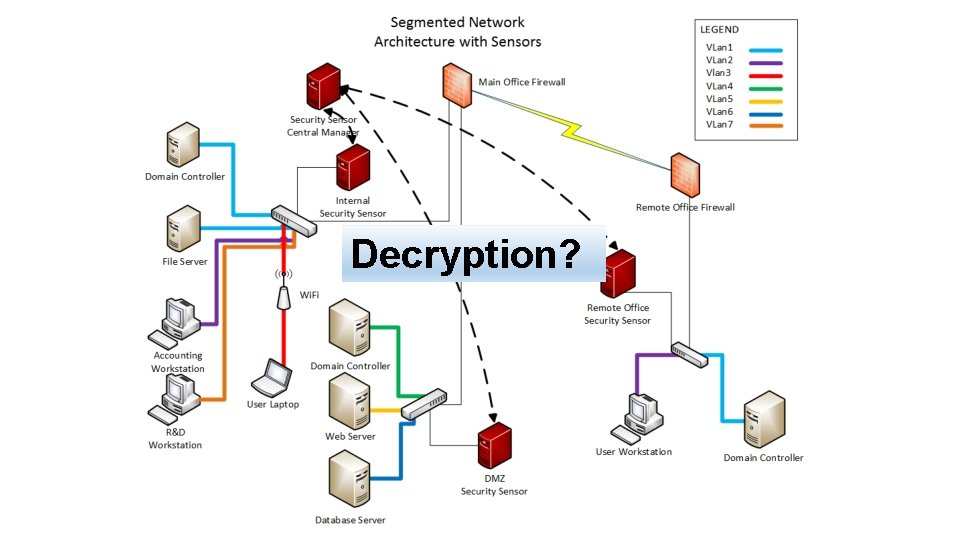
Decryption?
Restrict Movement & Increase Visibility You Shall Not Pass!
Distributed Army of Sensors
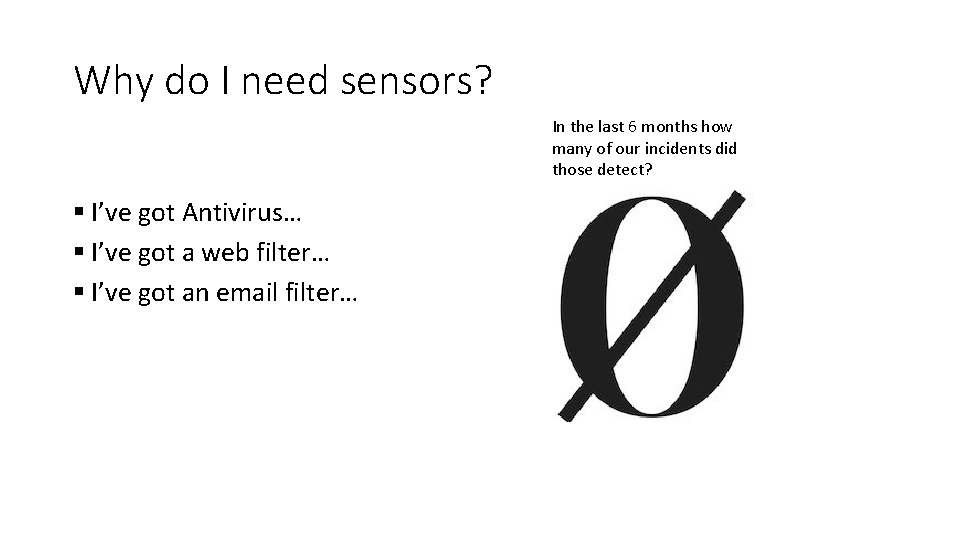
Why do I need sensors? In the last 6 months how many of our incidents did those detect? § I’ve got Antivirus… § I’ve got a web filter… § I’ve got an email filter…
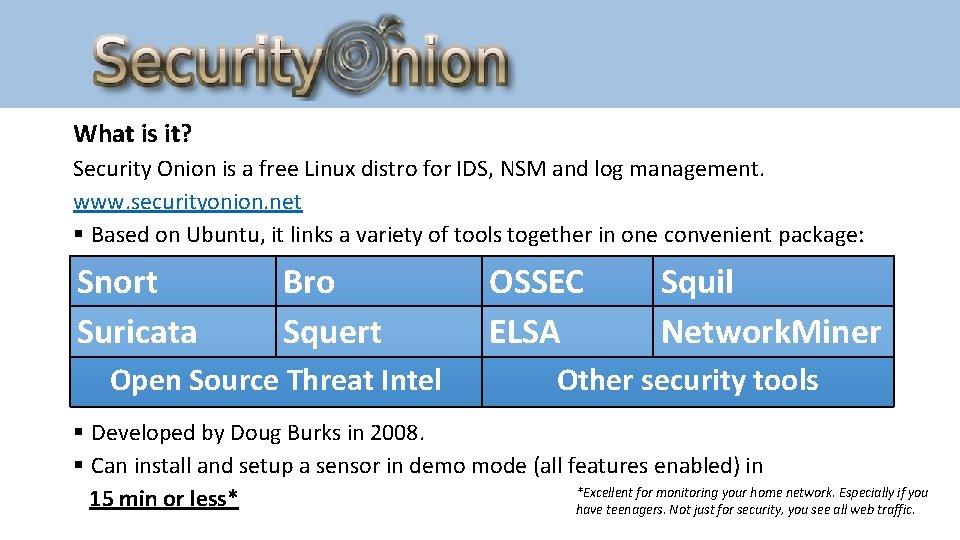
What is it? Security Onion is a free Linux distro for IDS, NSM and log management. www. securityonion. net § Based on Ubuntu, it links a variety of tools together in one convenient package: Snort Suricata Bro Squert Open Source Threat Intel OSSEC ELSA Squil Network. Miner Other security tools § Developed by Doug Burks in 2008. § Can install and setup a sensor in demo mode (all features enabled) in *Excellent for monitoring your home network. Especially if you 15 min or less* have teenagers. Not just for security, you see all web traffic.

Why did we choose Security Onion? § Needed to implement NSM on a budget § Minimal hardware/software investment § Able to start small to prove the concept, then scale § Needed to be able to operate with minimal staff § After deployment, 1 Security Analyst 20 -50% of their time on a given day § Good community support
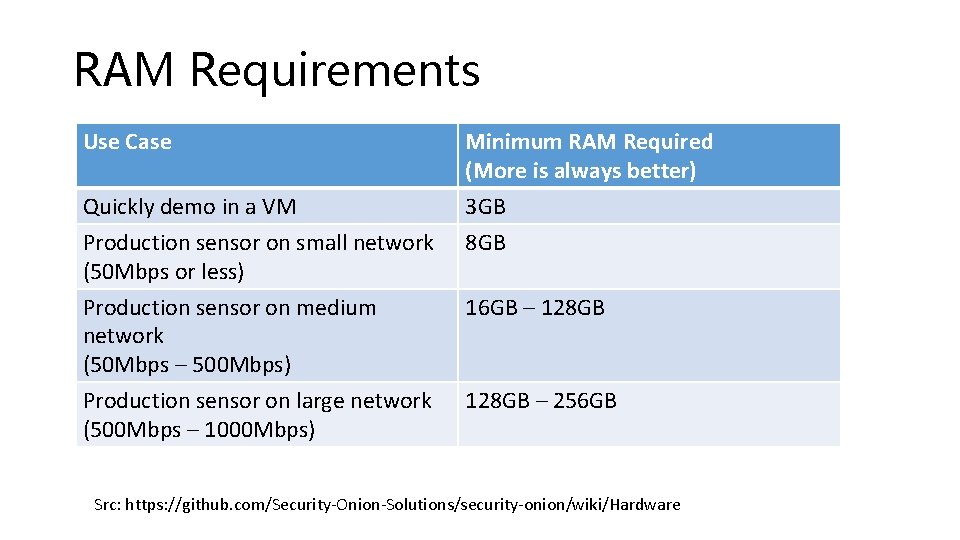
RAM Requirements Use Case Quickly demo in a VM Production sensor on small network (50 Mbps or less) Production sensor on medium network (50 Mbps – 500 Mbps) Production sensor on large network (500 Mbps – 1000 Mbps) Minimum RAM Required (More is always better) 3 GB 8 GB 16 GB – 128 GB – 256 GB Src: https: //github. com/Security-Onion-Solutions/security-onion/wiki/Hardware
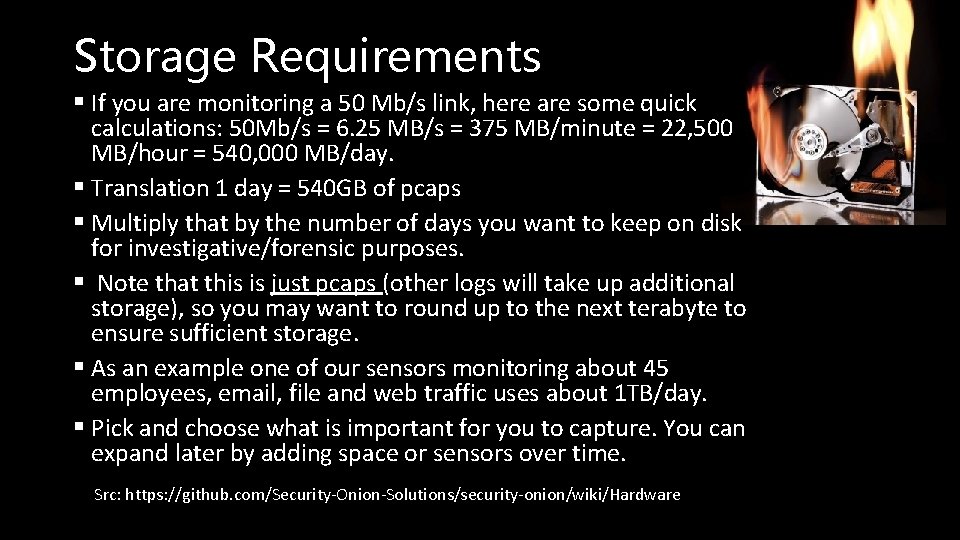
Storage Requirements § If you are monitoring a 50 Mb/s link, here are some quick calculations: 50 Mb/s = 6. 25 MB/s = 375 MB/minute = 22, 500 MB/hour = 540, 000 MB/day. § Translation 1 day = 540 GB of pcaps § Multiply that by the number of days you want to keep on disk for investigative/forensic purposes. § Note that this is just pcaps (other logs will take up additional storage), so you may want to round up to the next terabyte to ensure sufficient storage. § As an example one of our sensors monitoring about 45 employees, email, file and web traffic uses about 1 TB/day. § Pick and choose what is important for you to capture. You can expand later by adding space or sensors over time. Src: https: //github. com/Security-Onion-Solutions/security-onion/wiki/Hardware
Centralized Management You can use SALT to manage all of your sensors. Then they become SALT minions.
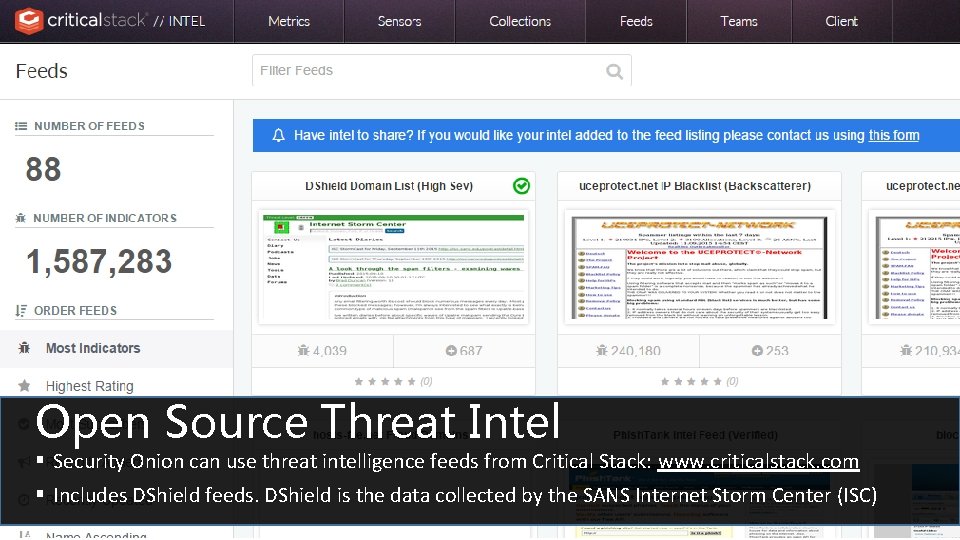
Open Source Threat Intel § Security Onion can use threat intelligence feeds from Critical Stack: www. criticalstack. com § Includes DShield feeds. DShield is the data collected by the SANS Internet Storm Center (ISC)
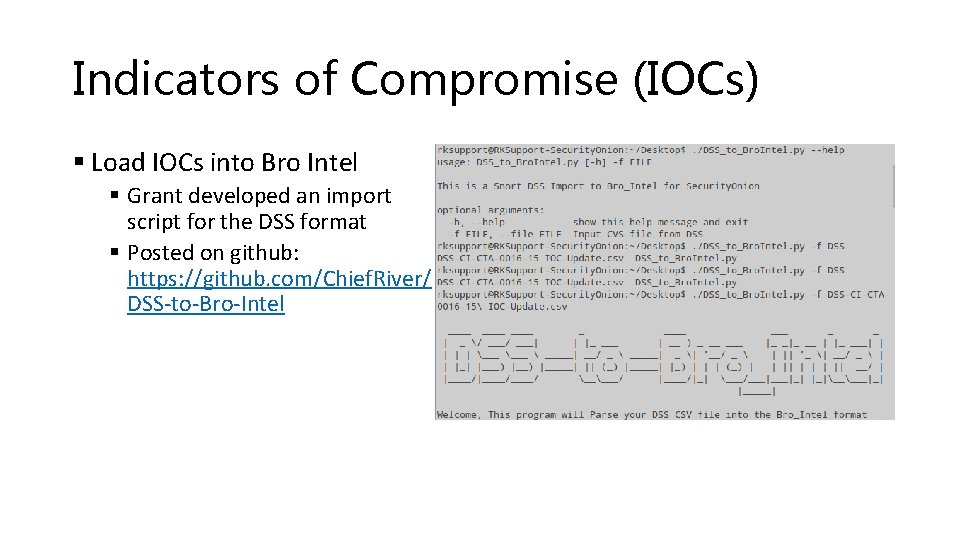
Indicators of Compromise (IOCs) § Load IOCs into Bro Intel § Grant developed an import script for the DSS format § Posted on github: https: //github. com/Chief. River/ DSS-to-Bro-Intel
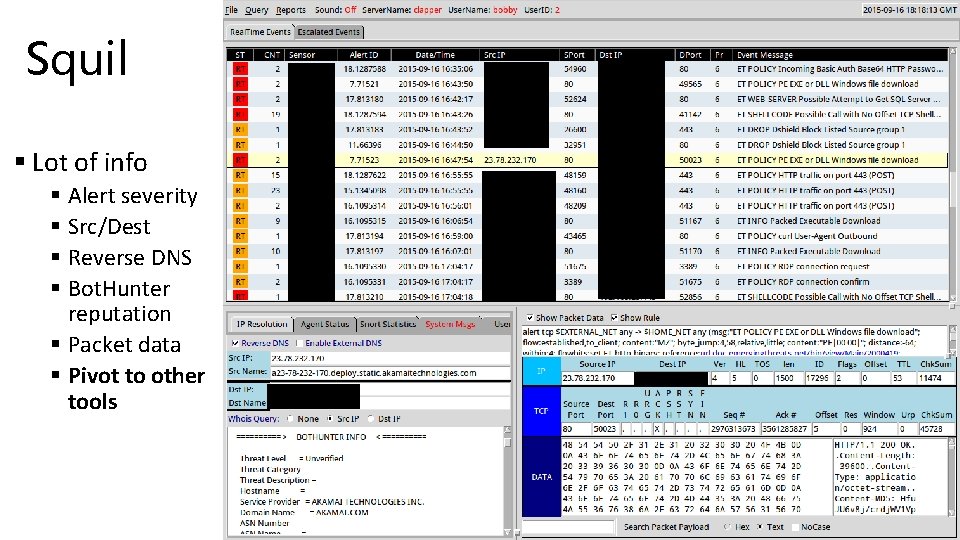
Squil § Lot of info § Alert severity § Src/Dest § Reverse DNS § Bot. Hunter reputation § Packet data § Pivot to other tools
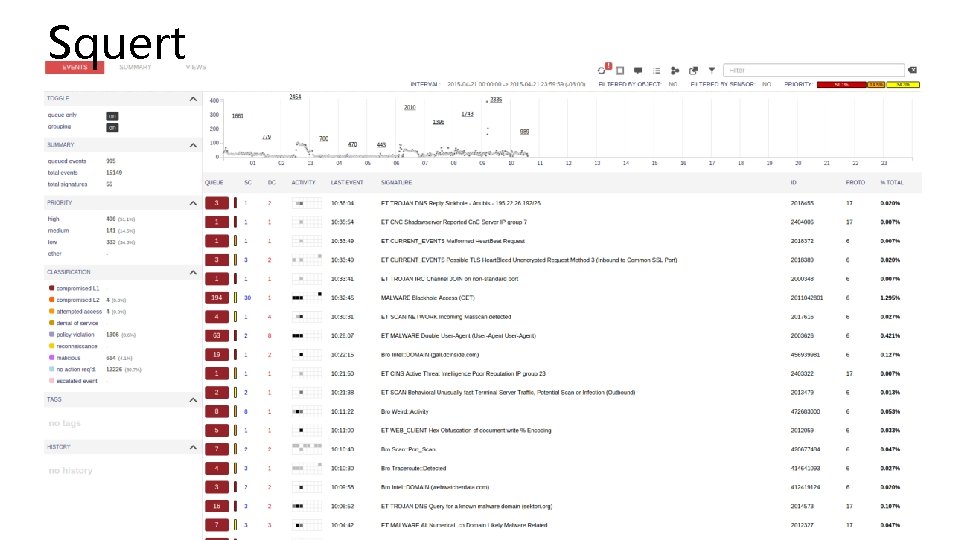
Squert
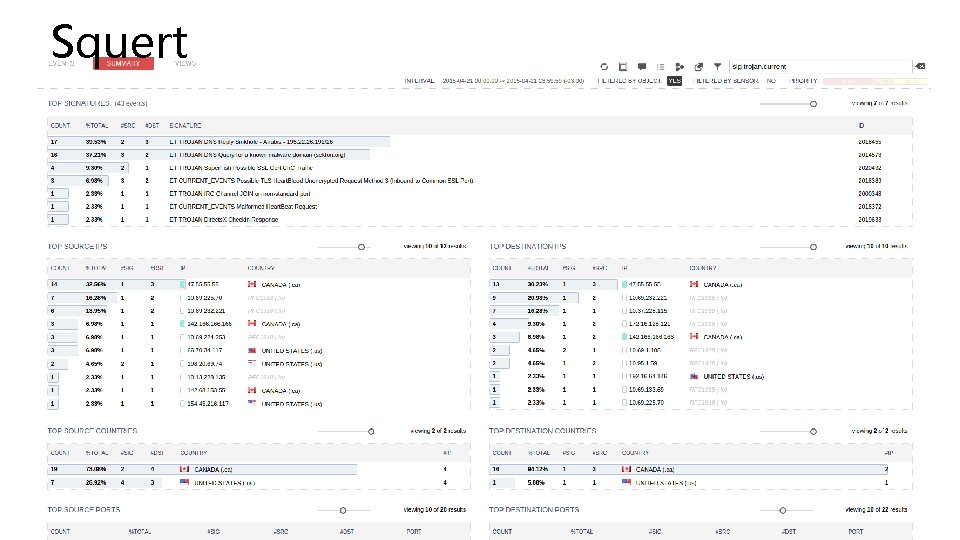
Squert
Bro – Powerful Network Analysis Framework Bro ELSA
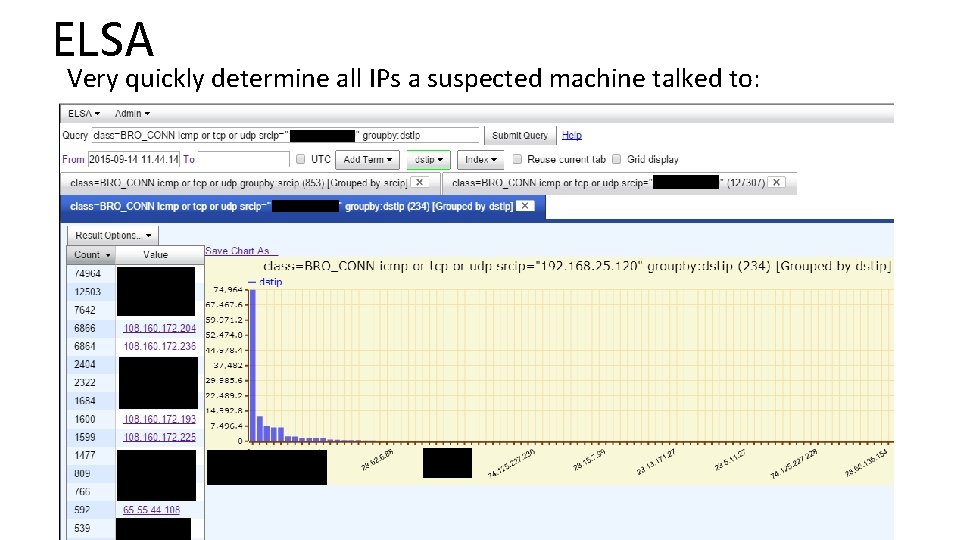
ELSA Very quickly determine all IPs a suspected machine talked to:
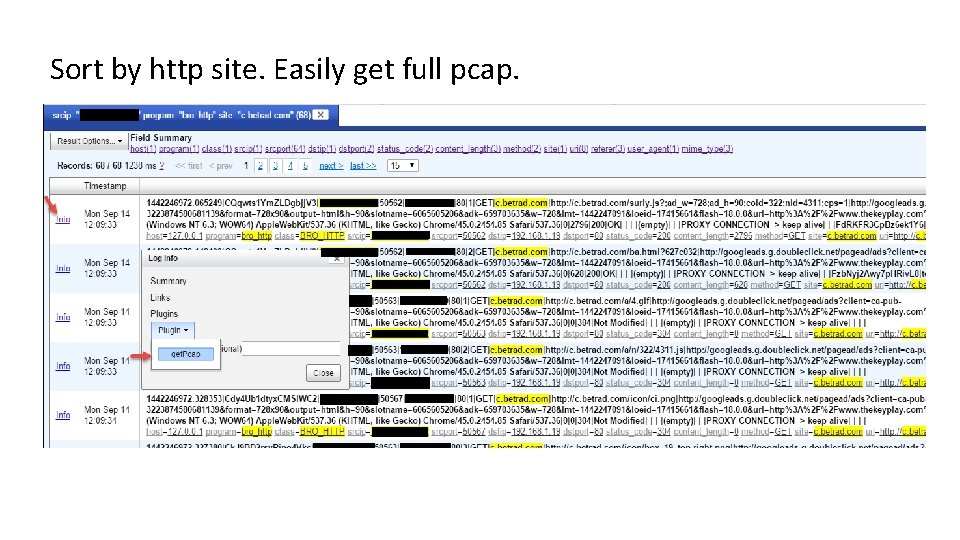
Sort by http site. Easily get full pcap.
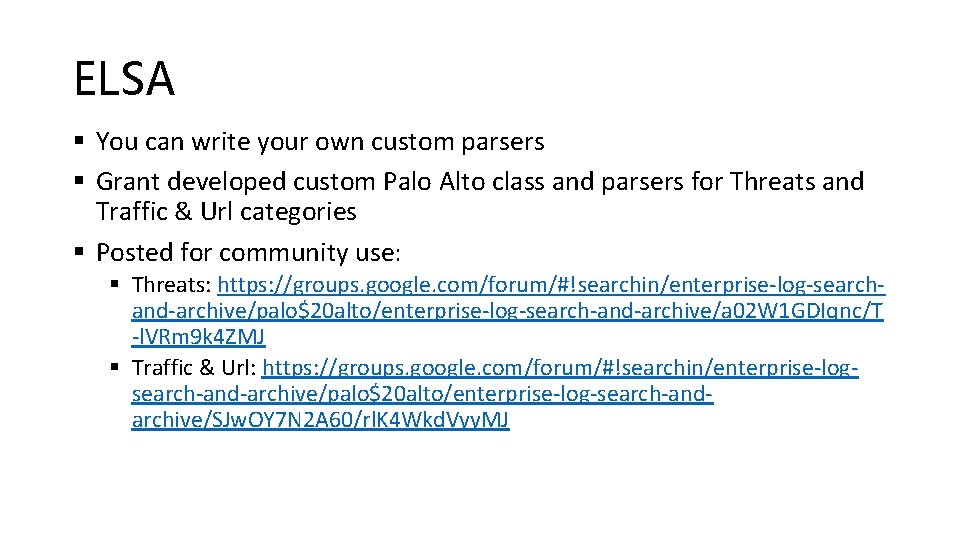
ELSA § You can write your own custom parsers § Grant developed custom Palo Alto class and parsers for Threats and Traffic & Url categories § Posted for community use: § Threats: https: //groups. google. com/forum/#!searchin/enterprise-log-searchand-archive/palo$20 alto/enterprise-log-search-and-archive/a 02 W 1 GDIqnc/T -l. VRm 9 k 4 ZMJ § Traffic & Url: https: //groups. google. com/forum/#!searchin/enterprise-logsearch-and-archive/palo$20 alto/enterprise-log-search-andarchive/SJw. OY 7 N 2 A 60/rl. K 4 Wkd. Vyy. MJ

Go Hunting!
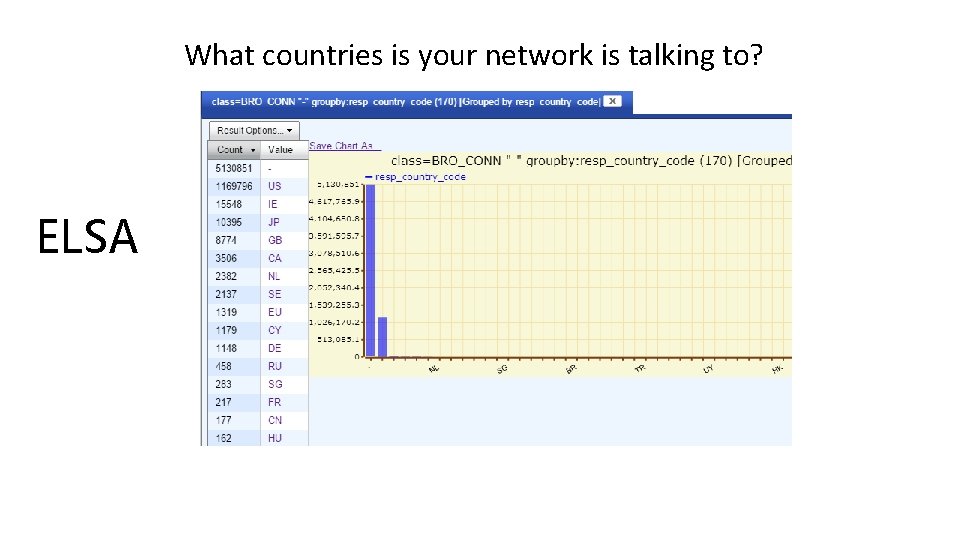
What countries is your network is talking to? ELSA
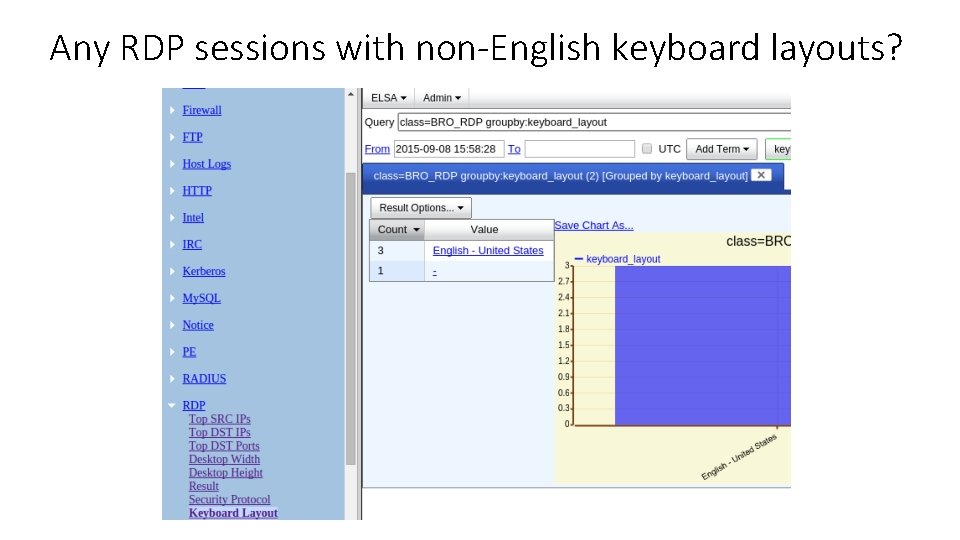
Any RDP sessions with non-English keyboard layouts?
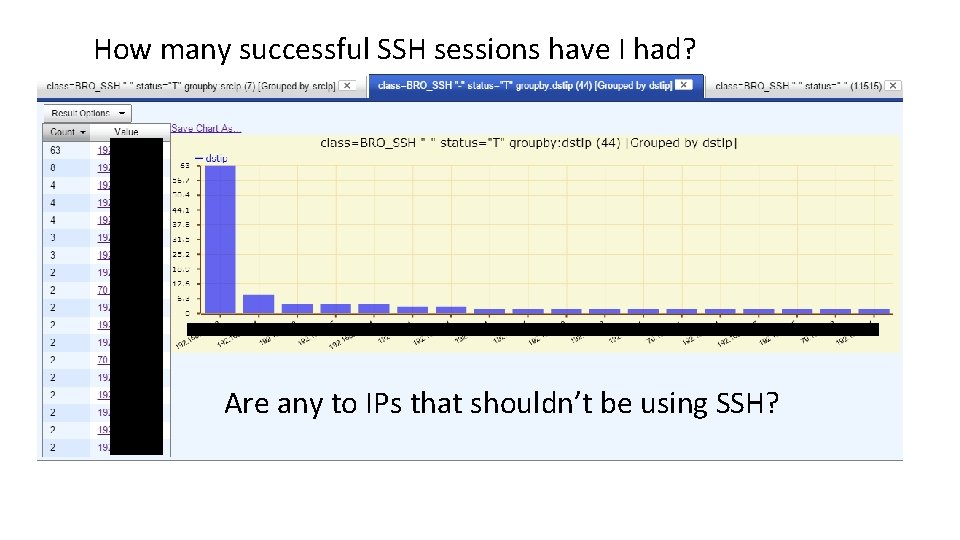
How many successful SSH sessions have I had? Are any to IPs that shouldn’t be using SSH?
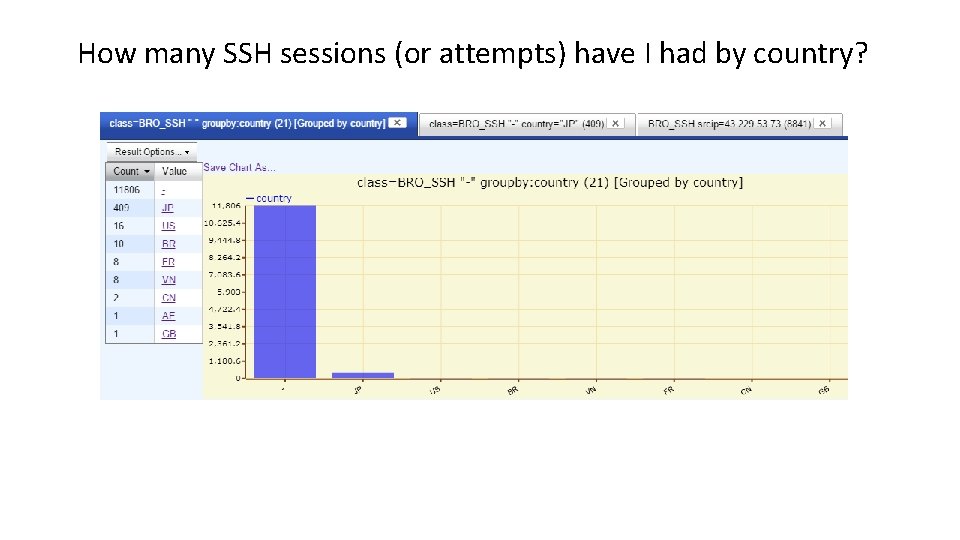
How many SSH sessions (or attempts) have I had by country?
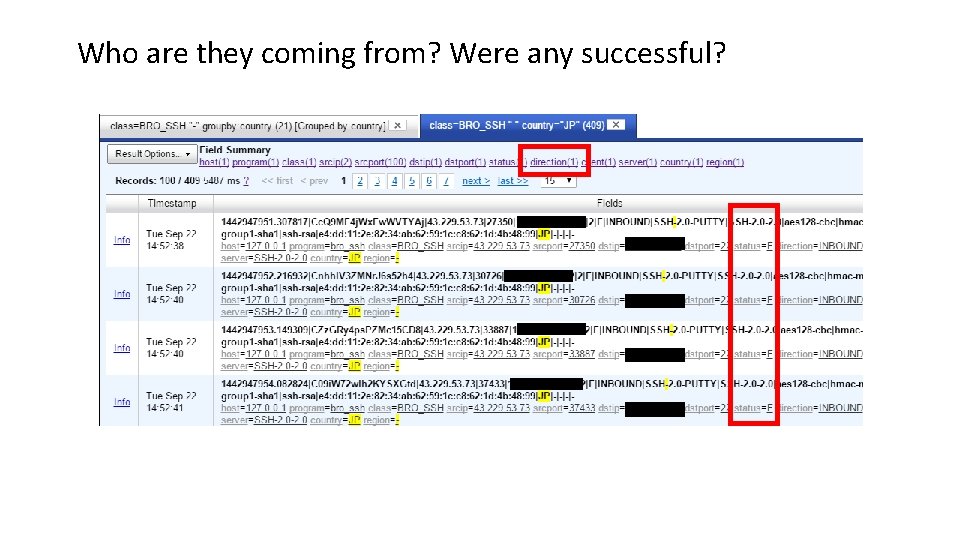
Who are they coming from? Were any successful?
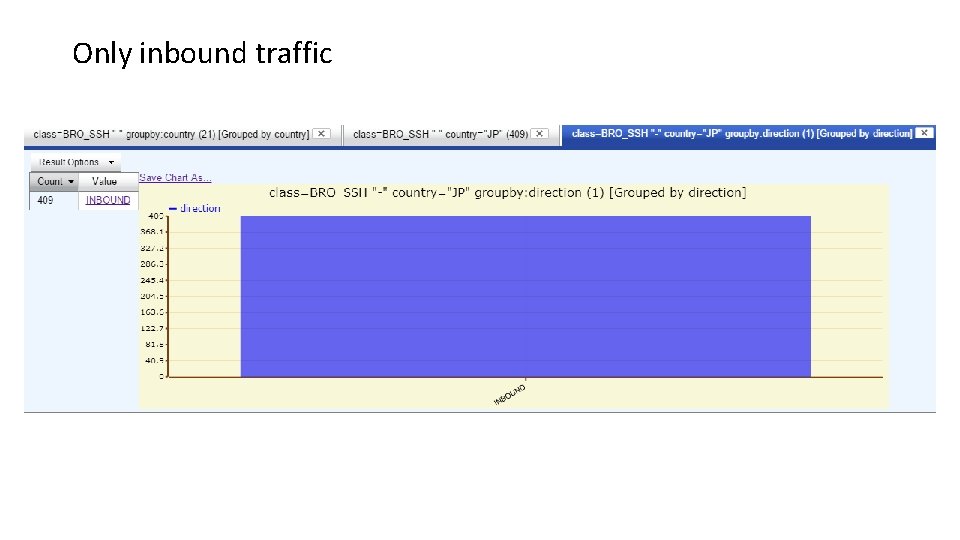
Only inbound traffic
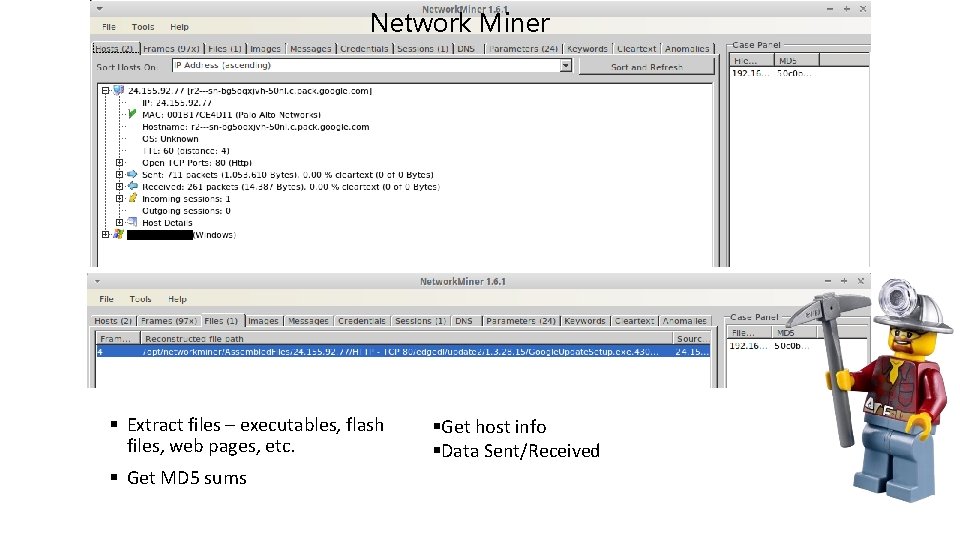
Network Miner § Extract files – executables, flash files, web pages, etc. § Get MD 5 sums §Get host info §Data Sent/Received
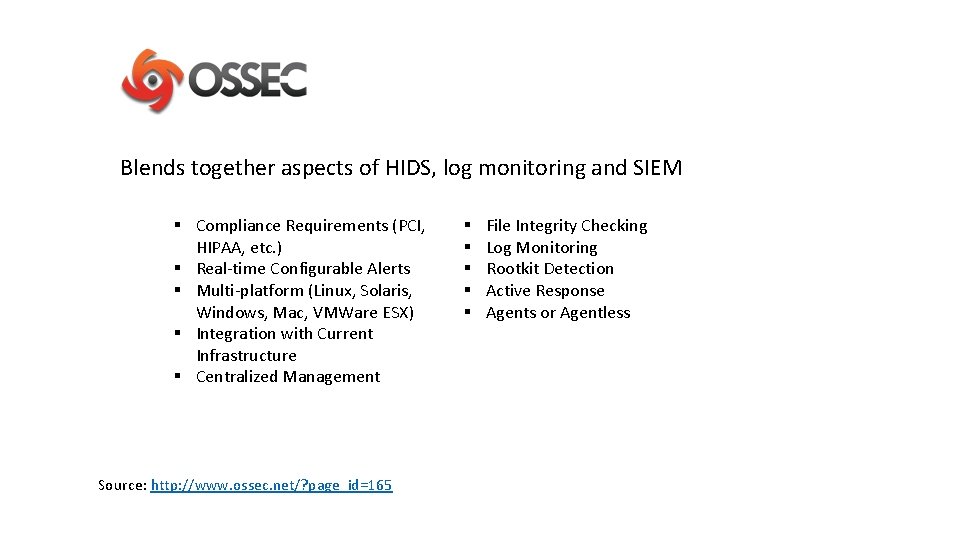
Blends together aspects of HIDS, log monitoring and SIEM § Compliance Requirements (PCI, HIPAA, etc. ) § Real-time Configurable Alerts § Multi-platform (Linux, Solaris, Windows, Mac, VMWare ESX) § Integration with Current Infrastructure § Centralized Management Source: http: //www. ossec. net/? page_id=165 § § § File Integrity Checking Log Monitoring Rootkit Detection Active Response Agents or Agentless
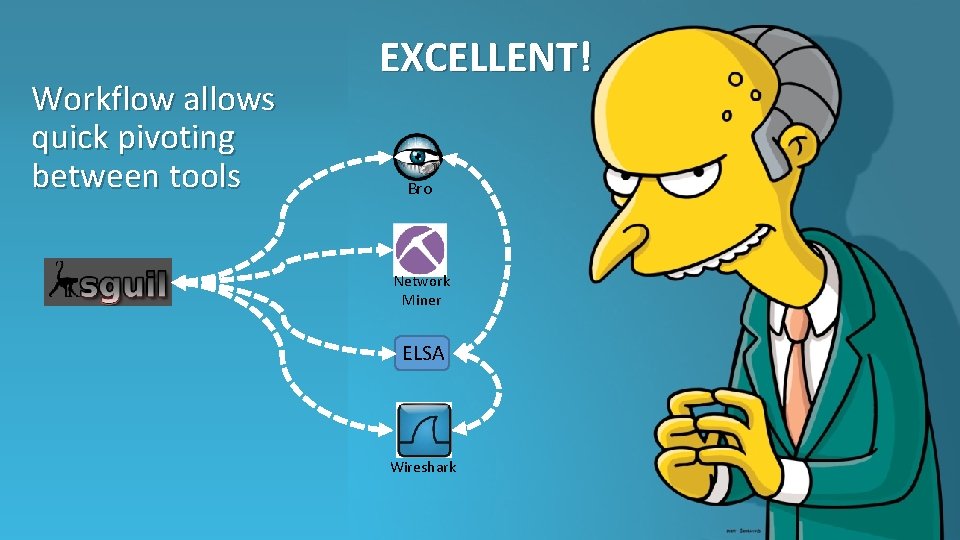
Workflow allows quick pivoting between tools EXCELLENT! Bro Network Miner ELSA Wireshark
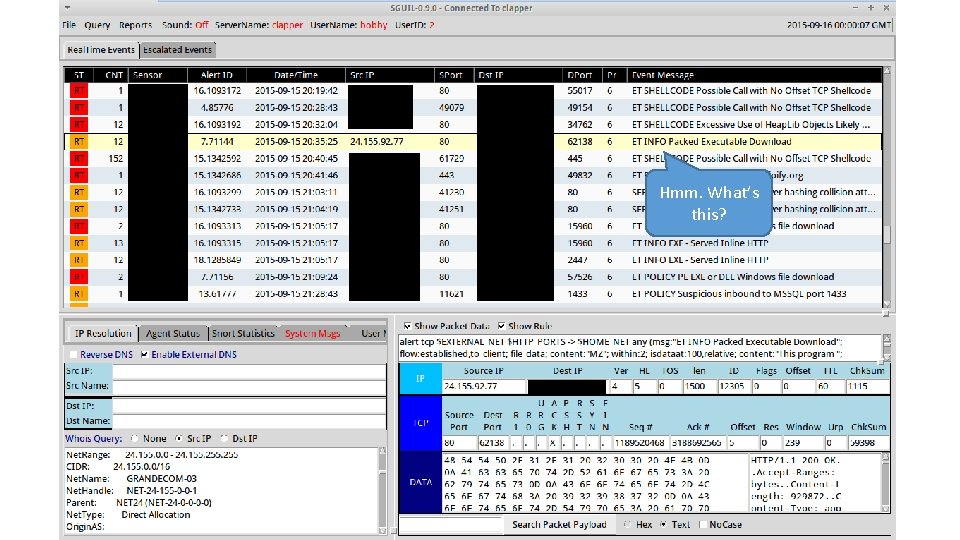
Hmm. What’s this?

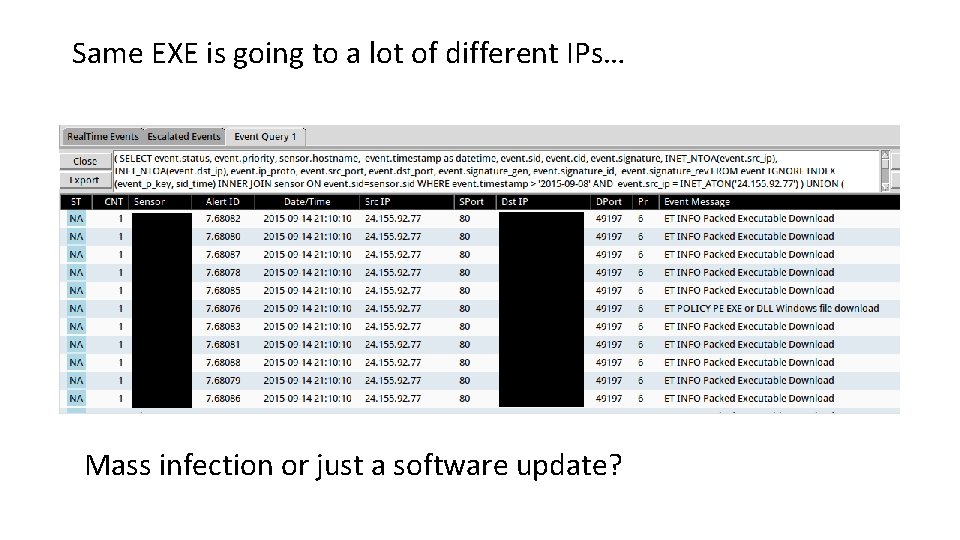
Same EXE is going to a lot of different IPs… Mass infection or just a software update?
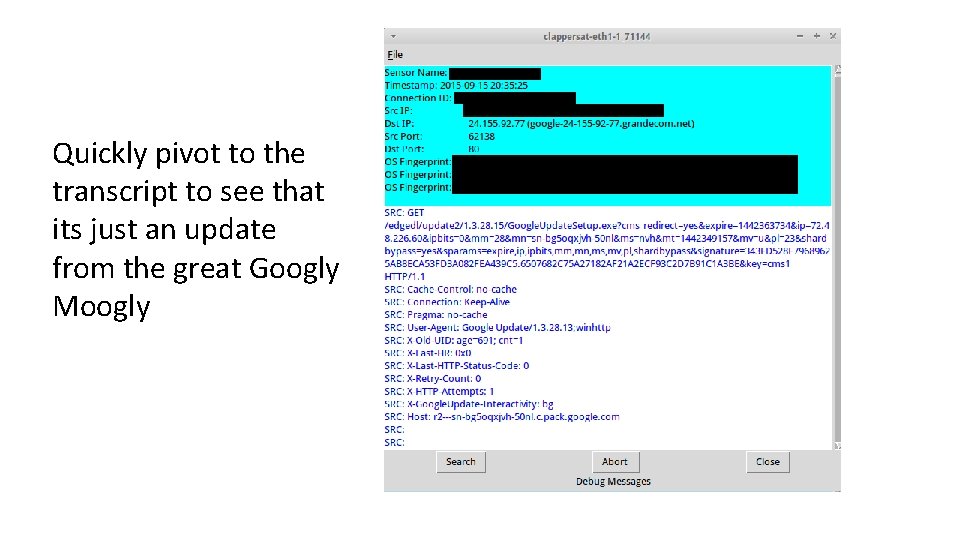
Quickly pivot to the transcript to see that its just an update from the great Googly Moogly
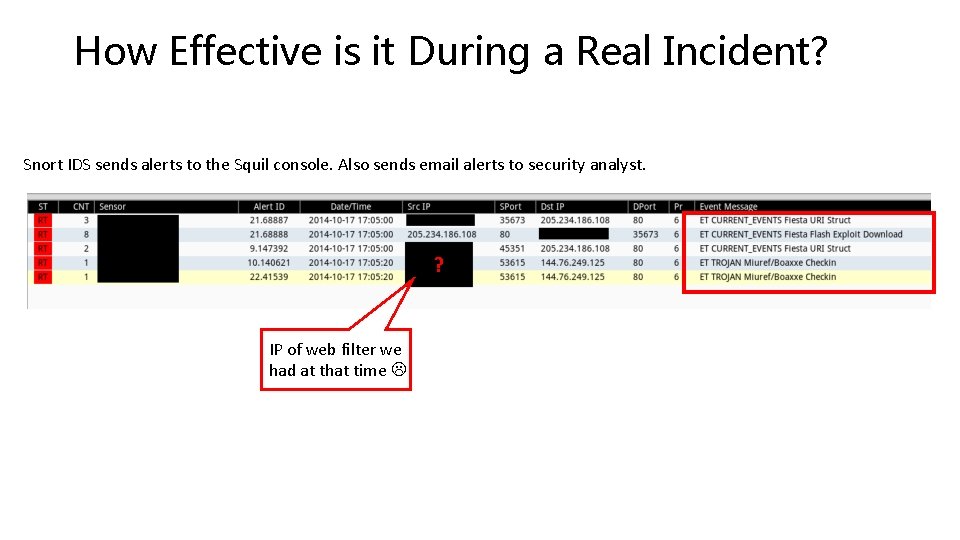
How Effective is it During a Real Incident? Snort IDS sends alerts to the Squil console. Also sends email alerts to security analyst. ? IP of web filter we had at that time
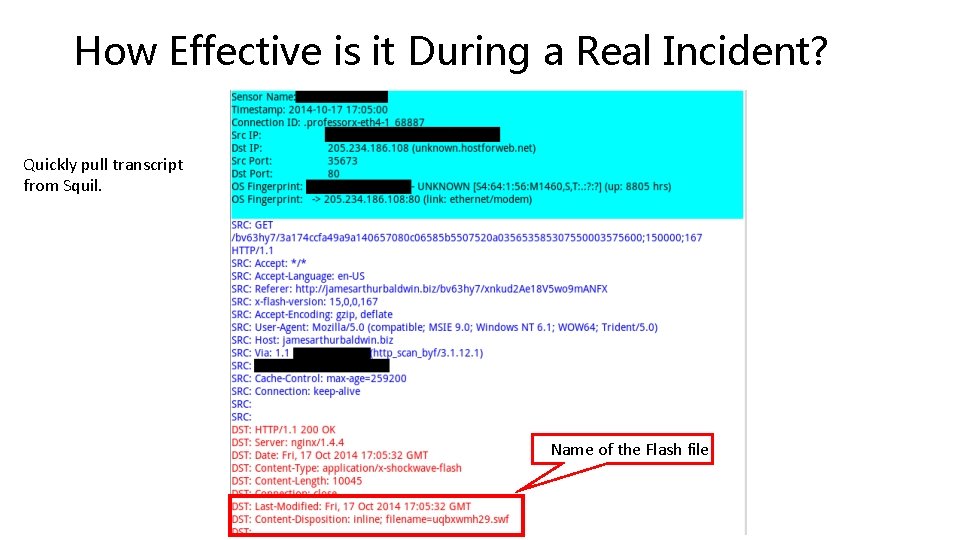
How Effective is it During a Real Incident? Quickly pull transcript from Squil. Name of the Flash file
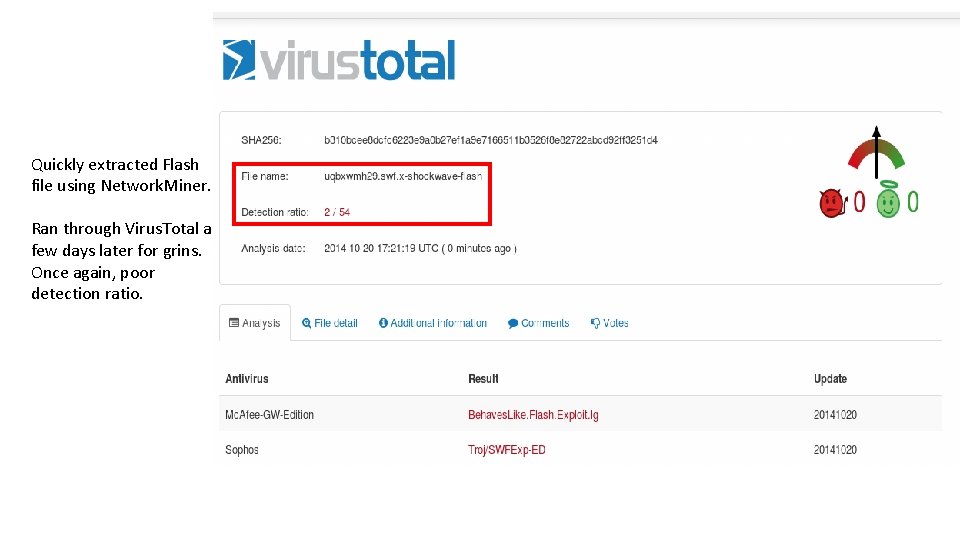
Quickly extracted Flash file using Network. Miner. Ran through Virus. Total a few days later for grins. Once again, poor detection ratio.
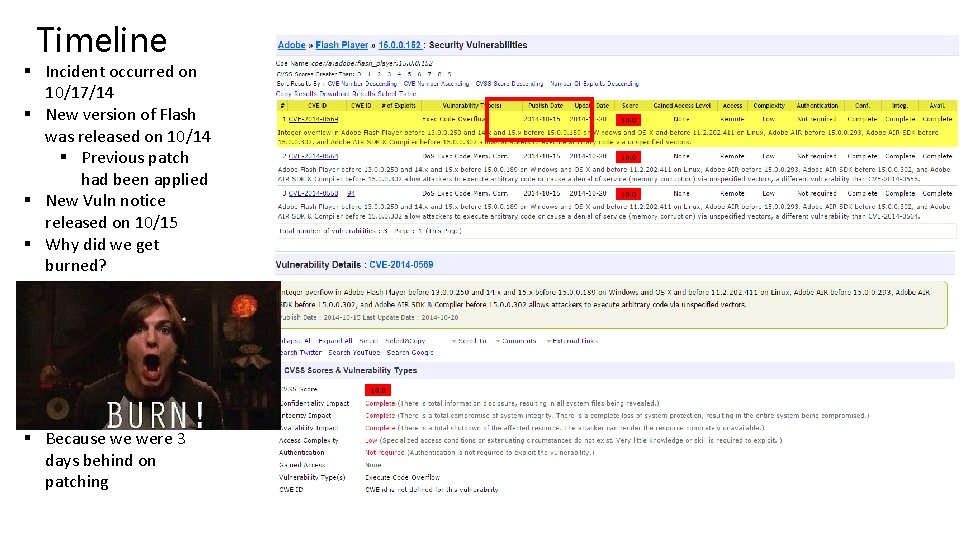
Timeline § Incident occurred on 10/17/14 § New version of Flash was released on 10/14 § Previous patch had been applied § New Vuln notice released on 10/15 § Why did we get burned? § Because we were 3 days behind on patching
No need to cry. Why? Time from notification until machine was isolated was 9 min.
Is life always that good? No. § This was a best case scenario. § Extremely happy with any detection/response within an hour. Goal is less than 24 hrs. § Sometimes things will sit and wait. § Often don’t make enough noise to detect until they phone home. Or try to cross a network segment. § Will it always find everything? Nope. § Will you have full pcaps and logs so you (or an outside expert) can determine what really happened?
Thanks to Security Onion, what bugs have we successfully exterminated over the past year? § Fiesta EK § Install. Rex § Angler EK § Cool EK § Styx EK

Baby steps
Lessons Learned Network Architecture § Use small test cases when implementing network segmentation § Put ACLs in Audit mode if possible § There will be required business traffic that you did not anticipate a need for § Be responsive to users during implementation § Communicate about the changes you are making and why
Lessons Learned § Take Doug Burk’s Security Onion 101, 201 and/or SO 301 – Best Practices for Distributed Deployments § Will save you a ton of time § Tune, Tune § Review Snort rule sets, over 15 K by default § 15 K will bog yo shiznit down § Disable/Threshold (Suppress)/Autocat § Monitor Squil alerts EVERYDAY § Otherwise you might find it gets a bit disoriented § Always run updates using soup § DO NOT update Security Onion using normal Ubuntu update procedures or it will make you cry § If you’re in a Windows Env. use a SO VM to manage your deployment.
Keep an Eye on the Health of Your Sensors • Sostat – security onion status of each sensor • Keep an eye on Squil uncategorized events • ELSA log node ssh tunnels: which sensors have made a successful connection back to the master server • Log archive: how many days of pcaps do you have stored • Bro netstats: Health of Bro and if it is missing or overlooking any data • IDS Engine packet drops: are you dropping packets/alerts – can the sensor keep up with the traffic? • SALT • Always update the master first. • Always run a SALT ping to test connectivity of all sensors before issuing commands
Pros • Easy to try before you buy • Minimal initial investment • Easy to roll out in a staged approach • Reasonable hardware costs • No software costs • Good community support • Centralized Management • Threat intelligence • Excellent workflow
Cons • Learning curve • Especially if you’re a Windows shop • No major company behind it • When we first started there was no commercial support available • There are now options: http: //www. securityonionsolutions. com/p/welc ome-to-security-onion-solutions. html • It needs daily love and care • Shouldn’t you be looking at your detection system daily anyway?
PEOPLE & PROCESS are the keys to long term success. NOT the latest gadget.
Questions?

Incident Response Using Security Onion Grant’s Presentation: https: //youtu. be/1 q. UF 3 Bv 7 d. IQ Grant’s Presentation:
Where to start? Just download Security Onion and tinker with it. Takes minutes to install in a VM or an old workstation: https: //security-onion-solutions. github. io/security-onion/ Use pcaps from http: //www. malware-traffic-analysis. net/trainingexercises. html to learn how an incident looks and how to go about investigating it. If you’re thinking about deploying it at work, this will be the best $99 you ever spent: https: //attendee. gototraining. com/9 z 73 w/catalog/81190625041584 70144? tz=America/New_York It will save you time (therefore money) and some headaches
- Slides: 69