About the Presentations The presentations cover the objectives
About the Presentations • The presentations cover the objectives found in the opening of each chapter. • All chapter objectives are listed in the beginning of each presentation. • You may customize the presentations to fit your class needs. • Some figures from the chapters are included. A complete set of images from the book can be found on the Instructor Resources disc.
Security Awareness Chapter 1 Introduction to Security
Objectives After completing this chapter, you should be able to do the following: • Describe the challenges of securing information • Define information security and explain why it is important • Identify the types of attackers that are common today • List the basic steps of an attack • Describe the steps in a defense and a comprehensive defense strategy Security Awareness, 3 rd Edition 3
Challenges of Securing Information • No single simple solution to protecting computers and securing information • Different types of attacks • Difficulties in defending against these attacks Security Awareness, 3 rd Edition 4
Today’s Security Attacks • Typical monthly security newsletter – Malicious program was introduced in the manufacturing process of a popular brand of digital photo frames – E-mail claiming to be from the United Nations (U. N. ) ‘‘Nigerian Government Reimbursement Committee’’ is sent to unsuspecting users – ‘‘Booby-trapped’’ Web pages are growing at an increasing rate – Mac computers can be the victim of attackers Security Awareness, 3 rd Edition 5
Today’s Security Attacks (cont’d. ) • Security statistics – 45 million credit and debit card numbers stolen – Number of security breaches continues to rise – Recent report revealed that of 24 federal government agencies overall grade was only ‘‘C-’’ Security Awareness, 3 rd Edition 6
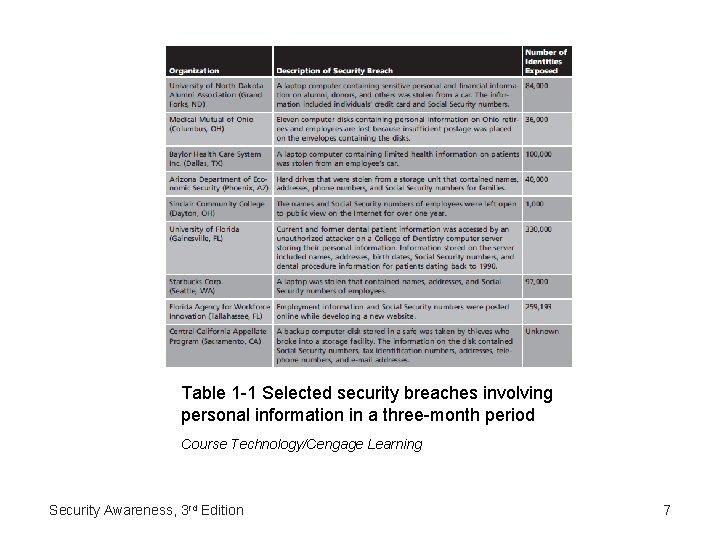
Table 1 -1 Selected security breaches involving personal information in a three-month period Course Technology/Cengage Learning Security Awareness, 3 rd Edition 7
Difficulties in Defending Against Attacks • • Speed of attacks Greater sophistication of attacks Simplicity of attack tools Quicker detection of vulnerabilities – Zero day attack • Delays in patching products • Distributed attacks • User confusion Security Awareness, 3 rd Edition 8
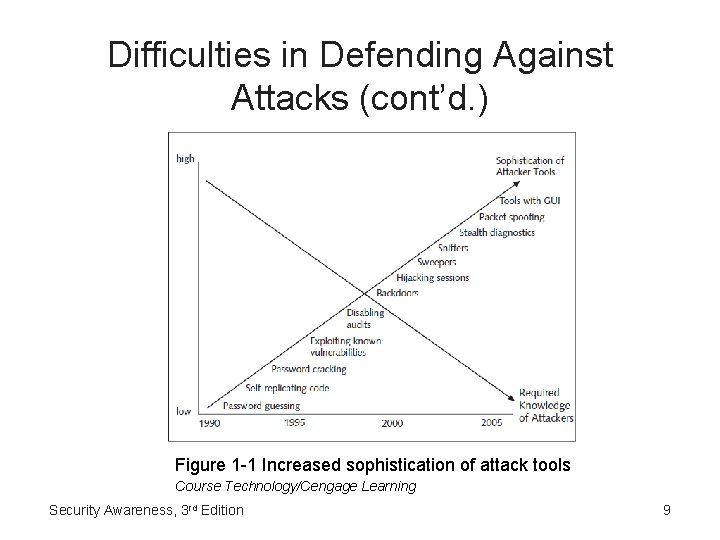
Difficulties in Defending Against Attacks (cont’d. ) Figure 1 -1 Increased sophistication of attack tools Course Technology/Cengage Learning Security Awareness, 3 rd Edition 9
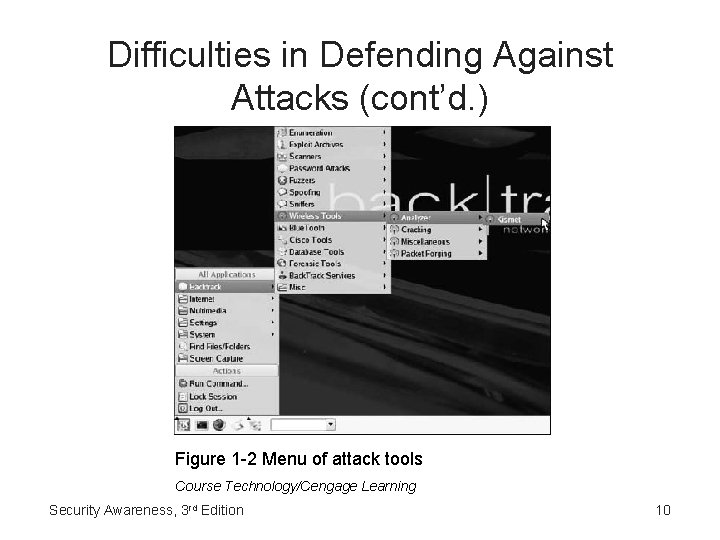
Difficulties in Defending Against Attacks (cont’d. ) Figure 1 -2 Menu of attack tools Course Technology/Cengage Learning Security Awareness, 3 rd Edition 10
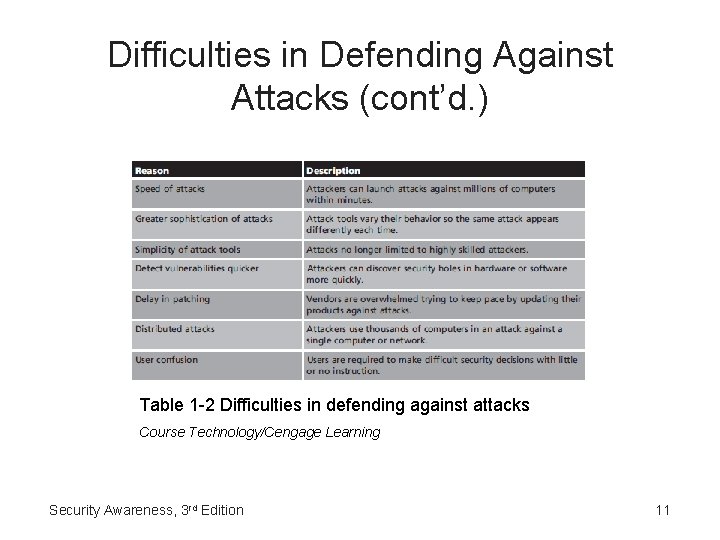
Difficulties in Defending Against Attacks (cont’d. ) Table 1 -2 Difficulties in defending against attacks Course Technology/Cengage Learning Security Awareness, 3 rd Edition 11
What Is Information Security? • Understand what information security is • Why is information security important today? • Who are the attackers? Security Awareness, 3 rd Edition 12
Defining Information Security • Security – State of freedom from a danger or risk • Information security – Tasks of guarding information that is in a digital format – Ensures that protective measures are properly implemented – Protect information that has value to people and organizations • Value comes from the characteristics of the information Security Awareness, 3 rd Edition 13
Defining Information Security (cont’d. ) • Characteristics of information that must be protected by information security – Confidentiality – Integrity – Availability • Achieved through a combination of three entities – Products – People – Procedures Security Awareness, 3 rd Edition 14
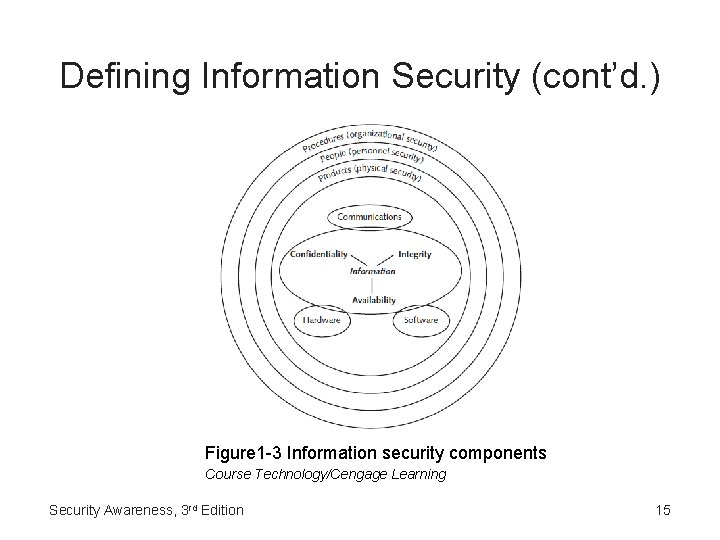
Defining Information Security (cont’d. ) Figure 1 -3 Information security components Course Technology/Cengage Learning Security Awareness, 3 rd Edition 15
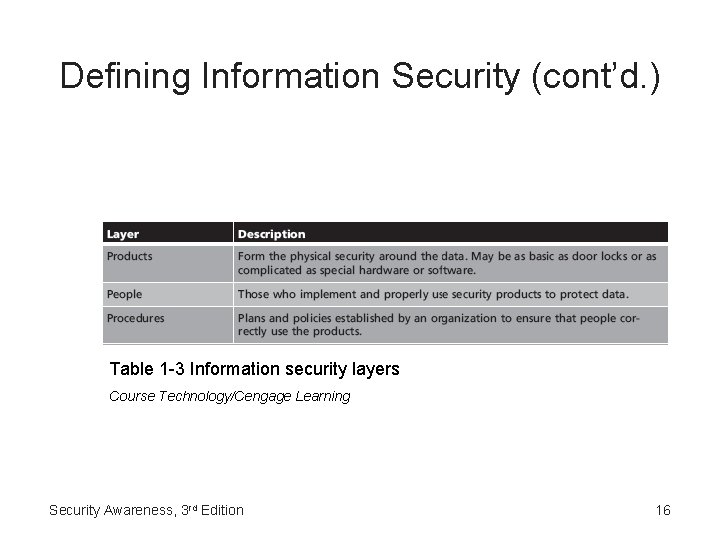
Defining Information Security (cont’d. ) Table 1 -3 Information security layers Course Technology/Cengage Learning Security Awareness, 3 rd Edition 16
Information Security Terminology • Asset – Something that has a value • Threat – Event or object that may defeat the security measures in place and result in a loss – By itself does not mean that security has been compromised • Threat agent – Person or thing that has the power to carry out a threat Security Awareness, 3 rd Edition 17
Information Security Terminology (cont’d. ) • Vulnerability – Weakness that allows a threat agent to bypass security • Exploiting the security weakness – Taking advantage of the vulnerability • Risk – Likelihood that a threat agent will exploit a vulnerability – Some degree of risk must always be assumed – Three options for dealing with risk Security Awareness, 3 rd Edition 18
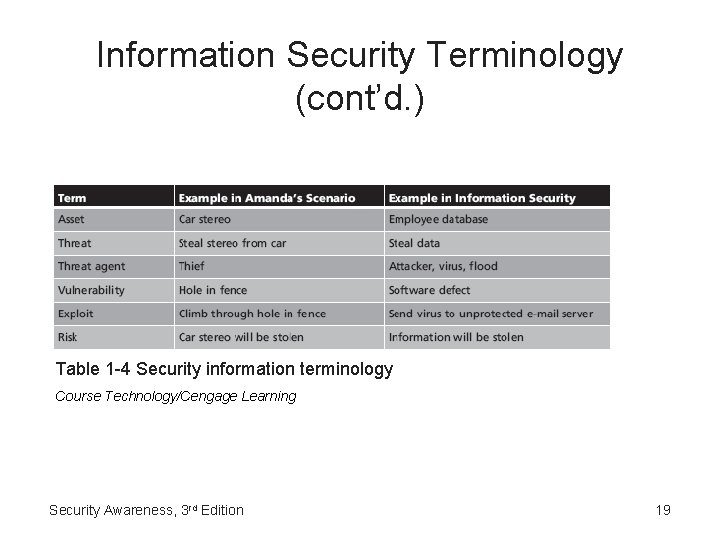
Information Security Terminology (cont’d. ) Table 1 -4 Security information terminology Course Technology/Cengage Learning Security Awareness, 3 rd Edition 19
Understanding the Importance of Information Security • Preventing data theft – Theft of data is one of the largest causes of financial loss due to an attack – Affects businesses and individuals • Thwarting identity theft – Identity theft • Using someone’s personal information to establish bank or credit card accounts that are then left unpaid • Leaves the victim with debts and ruins their credit rating – Legislation continues to be enacted Security Awareness, 3 rd Edition 20
Understanding the Importance of Information Security (cont’d. ) • Avoiding legal consequences – Federal and state laws that protect the privacy of electronic data • The Health Insurance Portability and Accountability Act of 1996 (HIPAA) • The Sarbanes-Oxley Act of 2002 (Sarbox) • The Gramm-Leach-Bliley Act (GLBA) • USA Patriot Act (2001) • The California Database Security Breach Act (2003) • Children’s Online Privacy Protection Act of 1998 (COPPA) Security Awareness, 3 rd Edition 21
Understanding the Importance of Information Security (cont’d. ) • Maintaining productivity – Lost wages and productivity during an attack and cleanup – Unsolicited e-mail message security risk • U. S. businesses forfeit $9 billion each year restricting spam • Foiling cyberterrorism – Could cripple a nation’s electronic and commercial infrastructure – ‘‘Information Security Problem’’ Security Awareness, 3 rd Edition 22
Who Are the Attackers? • Divided into several categories – – – Hackers Script kiddies Spies Employees Cybercriminals Cyberterrorists Security Awareness, 3 rd Edition 23
Hackers • Debated definition of hacker – Identify anyone who illegally breaks into or attempts to break into a computer system – Person who uses advanced computer skills to attack computers only to expose security flaws • ‘‘White Hats’ Security Awareness, 3 rd Edition 24
Script Kiddies • Unskilled users • Use automated hacking software • Do not understand the technology behind what they are doing • Often indiscriminately target a wide range of computers Security Awareness, 3 rd Edition 25
Spies • Person who has been hired to break into a computer and steal information • Do not randomly search for unsecured computers • Hired to attack a specific computer or system • Goal – Break into computer or system – Take the information without drawing any attention to their actions Security Awareness, 3 rd Edition 26
Employees • Reasons for attacks by employees – – – Show company weakness in security Retaliation Money Blackmail Carelessness Security Awareness, 3 rd Edition 27
Cybercriminals • Loose-knit network of attackers, identity thieves, and financial fraudsters • Motivated by money • Financial cybercrime categories – Stolen financial data – Spam email to sell counterfeits and pornography Security Awareness, 3 rd Edition 28
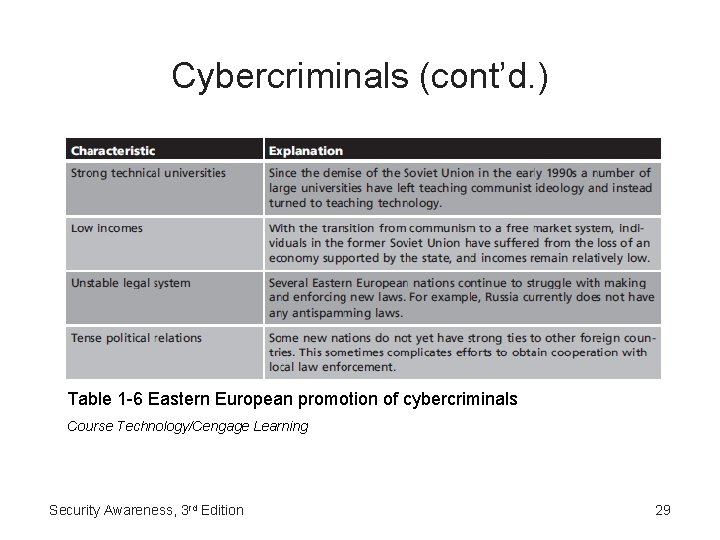
Cybercriminals (cont’d. ) Table 1 -6 Eastern European promotion of cybercriminals Course Technology/Cengage Learning Security Awareness, 3 rd Edition 29
Cyberterrorists • Motivated by ideology • Sometimes considered attackers that should be feared most Security Awareness, 3 rd Edition 30
Attacks and Defenses • Same basic steps are used in most attacks • Protecting computers against these steps – Calls for five fundamental security principles Security Awareness, 3 rd Edition 31
Steps of an Attack • • • Probe for information Penetrate any defenses Modify security settings Circulate to other systems Paralyze networks and devices Security Awareness, 3 rd Edition 32
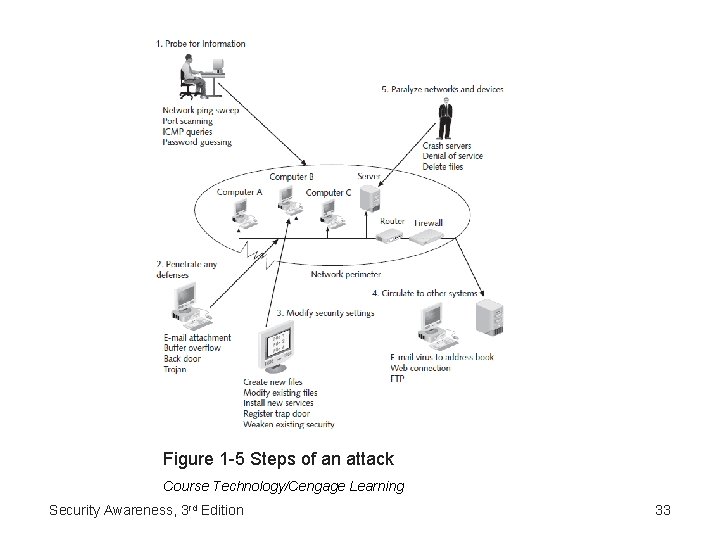
Figure 1 -5 Steps of an attack Course Technology/Cengage Learning Security Awareness, 3 rd Edition 33
Defenses Against Attacks • Layering – If one layer is penetrated, several more layers must still be breached – Each layer is often more difficult or complicated than the previous – Useful in resisting a variety of attacks • Limiting – Limiting access to information reduces the threat against it – Technology-based and procedural methods Security Awareness, 3 rd Edition 34
Defenses Against Attacks (cont’d. ) • Diversity – Important that security layers are diverse – Breaching one security layer does not compromise the whole system • Obscurity – Avoiding clear patterns of behavior make attacks from the outside much more difficult • Simplicity – Complex security systems can be hard to understand, troubleshoot, and feel secure about Security Awareness, 3 rd Edition 35
Building a Comprehensive Security Strategy • Block attacks – Strong security perimeter • Part of the computer network to which a personal computer is attached – Local security important too • Update defenses – Continually update defenses to protect information against new types of attacks Security Awareness, 3 rd Edition 36
Building a Comprehensive Security Strategy (cont’d. ) • Minimize losses – Realize that some attacks will get through security perimeters and local defenses – Make backup copies of important data – Business recovery policy • Send secure information – ‘‘Scramble’’ data so that unauthorized eyes cannot read it – Establish a secure electronic link between the sender and receiver Security Awareness, 3 rd Edition 37
Summary • Attacks against information security have grown exponentially in recent years • Difficult to defend against today’s attacks • Information security definition – That which protects the integrity, confidentiality, and availability of information • Main goals of information security – Prevent data theft, thwart identity theft, avoid the legal consequences of not securing information, maintain productivity, and foil cyberterrorism Security Awareness, 3 rd Edition 38
Summary (cont’d. ) • Several types of people are typically behind computer attacks • Five general steps that make up an attack • Practical, comprehensive security strategy involves four key elements Security Awareness, 3 rd Edition 39
- Slides: 39