A TopDown Approach to Modeling Global Behaviors of
A Top-Down Approach to Modeling Global Behaviors of Web Services Xiang Fu, Tevfik Bultan and Jianwen Su Department of Computer Science University of California, Santa Barbara {fuxiang, bultan, su}@cs. ucsb. edu
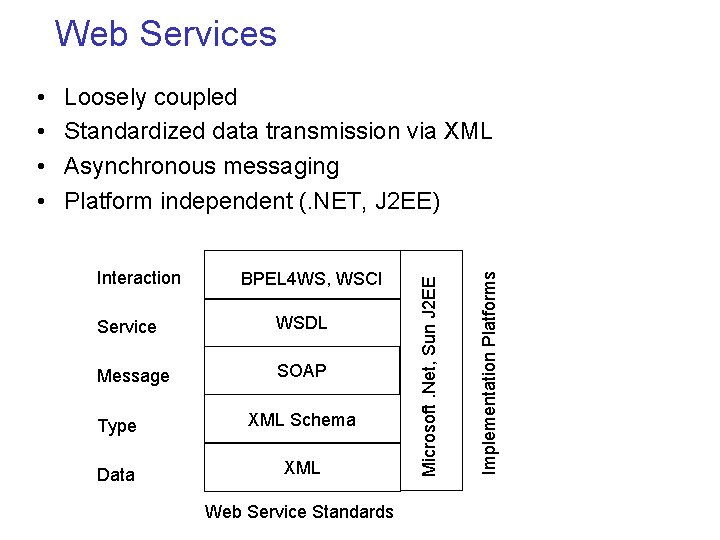
Web Services Interaction BPEL 4 WS, WSCI Service WSDL Message SOAP Type XML Schema Data XML Web Service Standards Implementation Platforms Loosely coupled Standardized data transmission via XML Asynchronous messaging Platform independent (. NET, J 2 EE) Microsoft. Net, Sun J 2 EE • •
Motivation • Challenges in both specification and verification – Distributed nature, no central control • How do we model the global behavior? • How do we specify the global properties? – Asynchronous messaging introduces undecidability in analysis • How do we check the global behavior? • How do we enforce the global behavior?
Outline • • • Web Service Composition Model Capturing Global Behavior: Conversations Bottom-Up vs. Top-Down Specification and Verification Realizability Problem Current and Future Work
Web Service Example • A user accesses to the Up. To. The. Minute. News. com (U 2 MNews) web service using a Browser • To access the U 2 MNews, user’s Browser has to traverse a web proxy on the corporate firewall • A company called Acme Web Speedup Services (AWS) provides a caching proxy web service to speedup web accesses • The corporate IT starts using AWS caching service • The user starts receiving stale pages from U 2 MNews • We want to specify/model the following global property – User’s Browser always receives the webpages (which have U 2 MNews as the source) from the U 2 MNews web service, not from the AWS
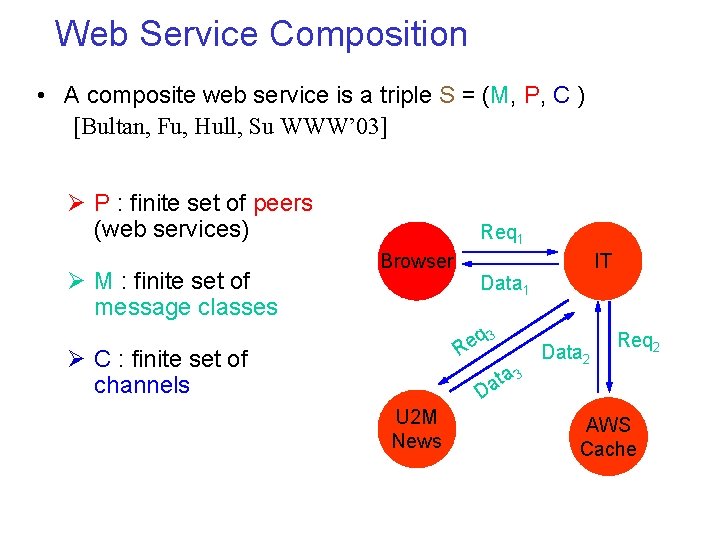
Web Service Composition • A composite web service is a triple S = (M, P, C ) [Bultan, Fu, Hull, Su WWW’ 03] Ø P : finite set of peers (web services) Ø M : finite set of message classes Req 1 Browser Data 1 q 3 e R Ø C : finite set of channels ta a D U 2 M News IT Data 2 Req 2 3 AWS Cache
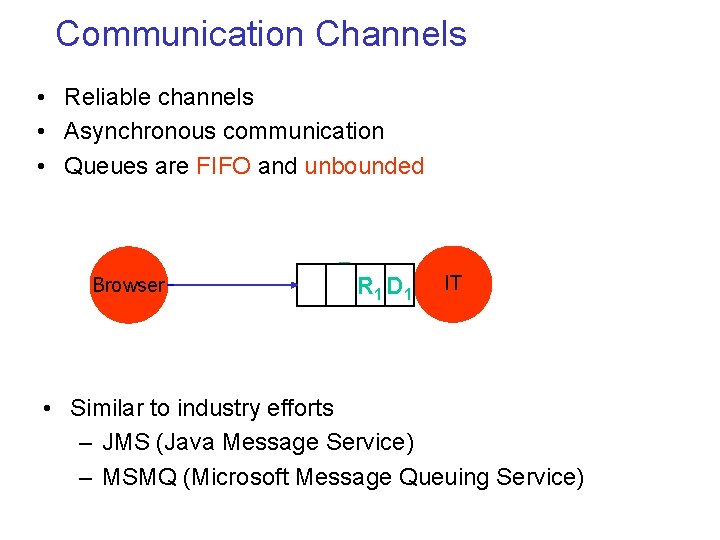
Communication Channels • Reliable channels • Asynchronous communication • Queues are FIFO and unbounded Browser Req 1 R 1 D 1 IT • Similar to industry efforts – JMS (Java Message Service) – MSMQ (Microsoft Message Queuing Service)
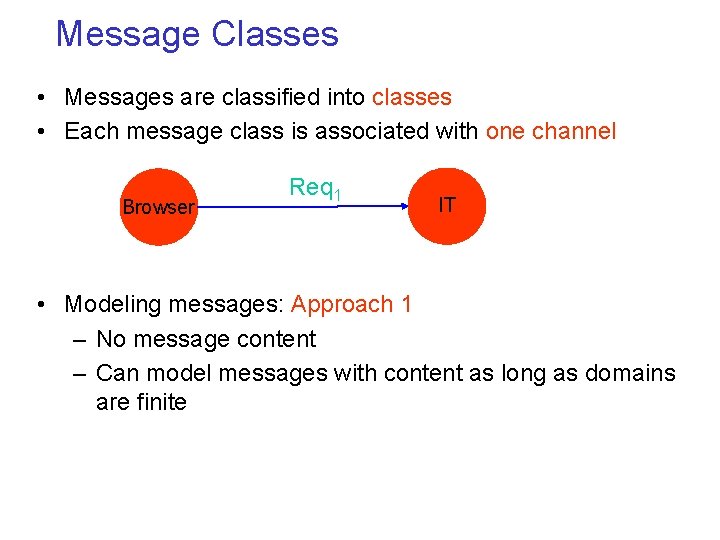
Message Classes • Messages are classified into classes • Each message class is associated with one channel Browser Req 1 IT • Modeling messages: Approach 1 – No message content – Can model messages with content as long as domains are finite
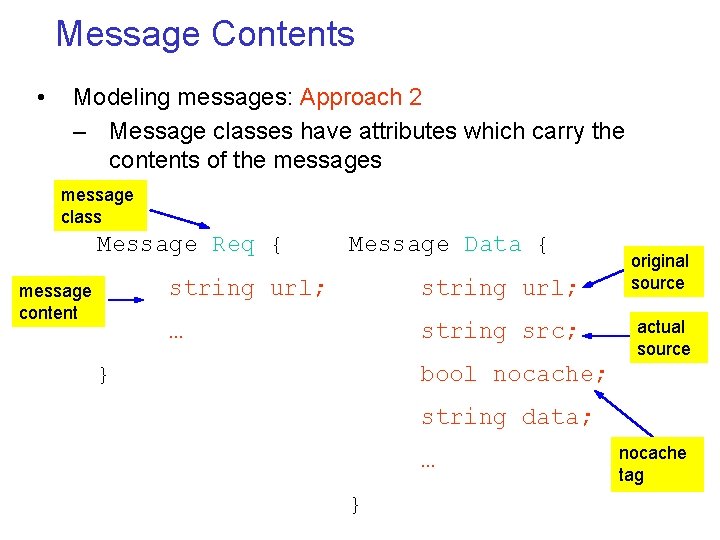
Message Contents • Modeling messages: Approach 2 – Message classes have attributes which carry the contents of the messages message class Message Req { message content Message Data { string url; … string src; } original source actual source bool nocache; string data; … } nocache tag
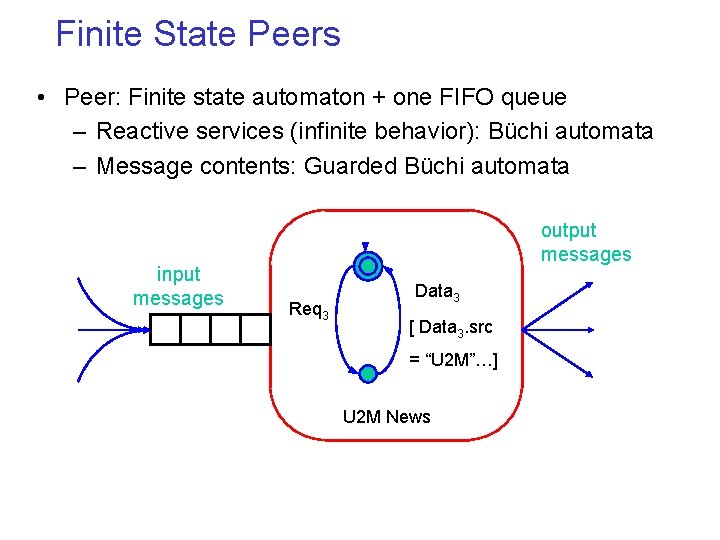
Finite State Peers • Peer: Finite state automaton + one FIFO queue – Reactive services (infinite behavior): Büchi automata – Message contents: Guarded Büchi automata input messages output messages Req 3 Data 3 [ Data 3. src = “U 2 M”…] U 2 M News
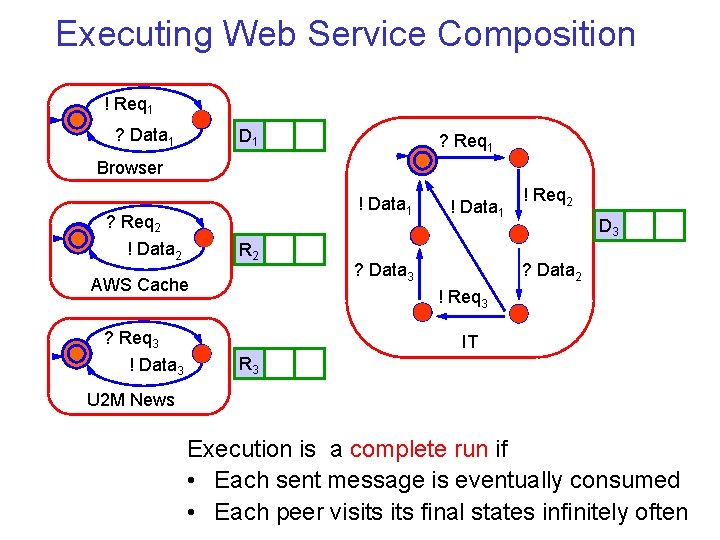
Executing Web Service Composition ! Req 1 ? Data 1 D 1 ? Req 1 Browser ! Data 1 ? Req 2 ! Data 2 R 2 AWS Cache ? Req 3 ! Data 1 ? Data 3 ! Req 2 R 321 D ? Data 2 ! Req 3 IT R 3 U 2 M News Execution is a complete run if • Each sent message is eventually consumed • Each peer visits final states infinitely often
Outline • • • Web Service Composition Model Capturing Global Behavior: Conversations Bottom-Up vs. Top-Down Specification and Verification Realizability Problem Current and Future Work
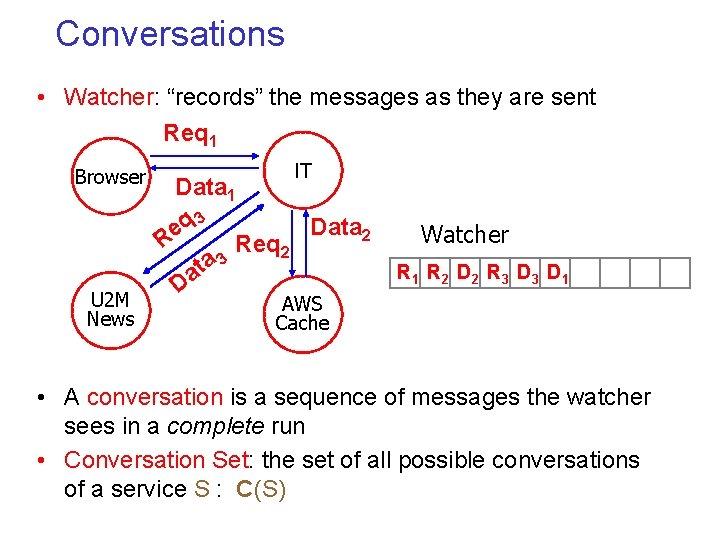
Conversations • Watcher: “records” the messages as they are sent Req 1 Browser U 2 M News IT Data 1 q 3 Data 2 e R Req 2 a 3 t Da Watcher R 1 R 2 D 2 R 3 D 1 AWS Cache • A conversation is a sequence of messages the watcher sees in a complete run • Conversation Set: the set of all possible conversations of a service S : C(S)
Specify System Goal Using LTL • The notion of conversation enables us to reason about temporal properties of the web service composition • LTL framework extends naturally to conversations – LTL temporal operators X (ne. Xt), U (Until), G (Globally), F (Future) – Atomic properties Predicates on message classes or contents Example: The news is always up to date G (Data 1 Data 1. src = Data 1. url = “U 2 M”) • Model checking problem: Given an LTL property, does the conversation set C(S) satisfy the property?
Question • Given a web service composition S, is the language C(S) always regular? If it is regular, finite state model checking techniques can be used for verification
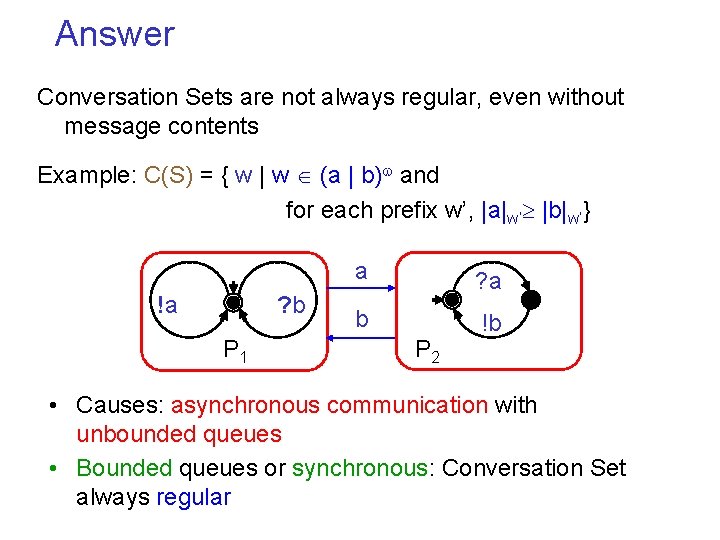
Answer Conversation Sets are not always regular, even without message contents Example: C(S) = { w | w (a | b) and for each prefix w’, |a|w’ |b|w’} !a ? b P 1 a ? a b !b P 2 • Causes: asynchronous communication with unbounded queues • Bounded queues or synchronous: Conversation Set always regular
Outline • • • Web Service Composition Model Capturing Global Behavior: Conversations Bottom-Up vs. Top-Down Specification and Verification Realizability Problem Current and Future Work
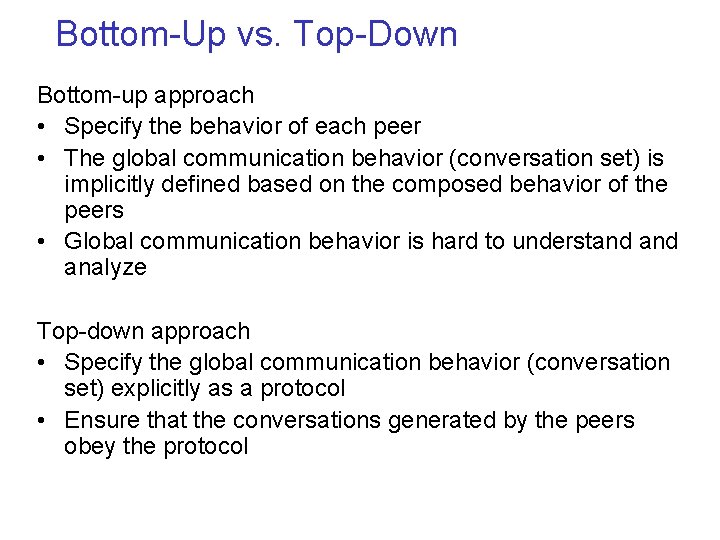
Bottom-Up vs. Top-Down Bottom-up approach • Specify the behavior of each peer • The global communication behavior (conversation set) is implicitly defined based on the composed behavior of the peers • Global communication behavior is hard to understand analyze Top-down approach • Specify the global communication behavior (conversation set) explicitly as a protocol • Ensure that the conversations generated by the peers obey the protocol
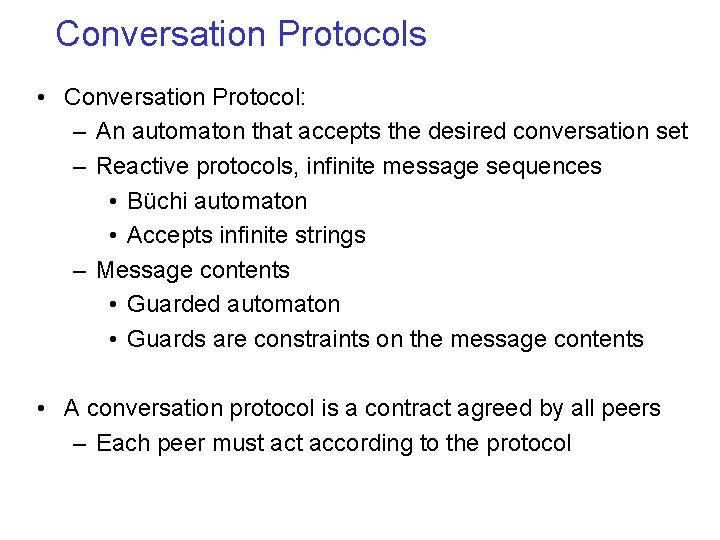
Conversation Protocols • Conversation Protocol: – An automaton that accepts the desired conversation set – Reactive protocols, infinite message sequences • Büchi automaton • Accepts infinite strings – Message contents • Guarded automaton • Guards are constraints on the message contents • A conversation protocol is a contract agreed by all peers – Each peer must according to the protocol
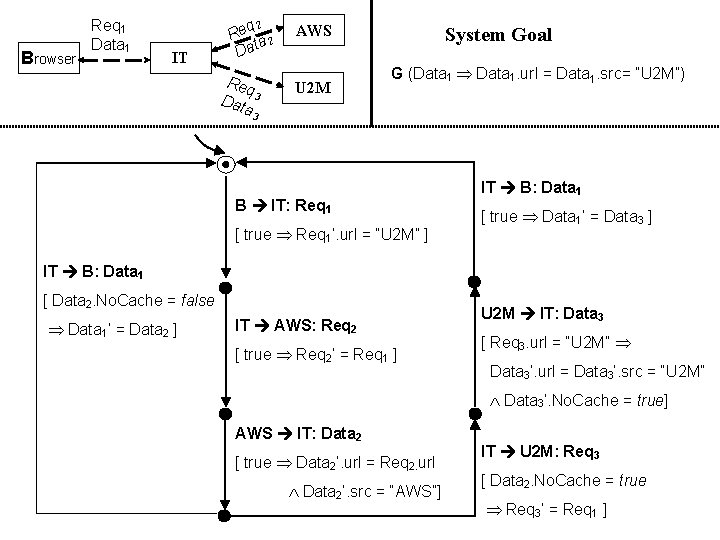
Browser Req 1 Data 1 IT q 2 Re a 2 t Da Req Dat 3 a AWS U 2 M System Goal G (Data 1 Data 1. url = Data 1. src= “U 2 M”) 3 B IT: Req 1 [ true Req 1’. url = “U 2 M” ] IT B: Data 1 [ true Data 1’ = Data 3 ] IT B: Data 1 [ Data 2. No. Cache = false Data 1’ = Data 2 ] IT AWS: Req 2 [ true Req 2’ = Req 1 ] U 2 M IT: Data 3 [ Req 3. url = “U 2 M” Data 3’. url = Data 3’. src = “U 2 M” Data 3’. No. Cache = true] AWS IT: Data 2 [ true Data 2’. url = Req 2. url Data 2’. src = “AWS”] IT U 2 M: Req 3 [ Data 2. No. Cache = true Req 3’ = Req 1 ]
Model Checking • Protocols without message contents – Finite state model checking techniques and tools • Protocols with finite domain message contents – Finite state model checking techniques and tools • Protocols with infinite domain message contents – Infinite state model checking techniques and tools
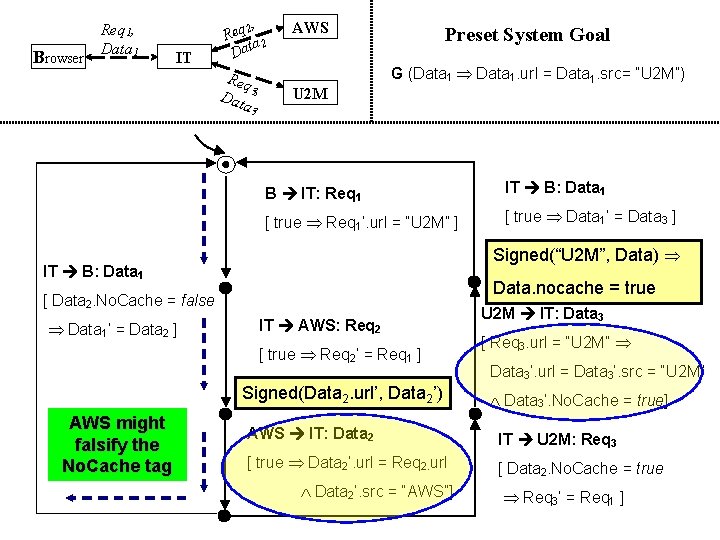
Browser Req 1, Data 1 IT 2, Req a 2 Dat Req Dat 3 , a AWS U 2 M Preset System Goal G (Data 1 Data 1. url = Data 1. src= “U 2 M”) 3 B IT: Req 1 IT B: Data 1 [ true Req 1’. url = “U 2 M” ] [ true Data 1’ = Data 3 ] Signed(“U 2 M”, Data) IT B: Data 1 Data. nocache = true [ Data 2. No. Cache = false Data 1’ = Data 2 ] IT AWS: Req 2 [ true Req 2’ = Req 1 ] Signed(Data 2. url’, Data 2’) AWS might falsify the No. Cache tag U 2 M IT: Data 3 [ Req 3. url = “U 2 M” Data 3’. url = Data 3’. src = “U 2 M” Data 3’. No. Cache = true] AWS IT: Data 2 IT U 2 M: Req 3 [ true Data 2’. url = Req 2. url [ Data 2. No. Cache = true Data 2’. src = “AWS”] Req 3’ = Req 1 ]
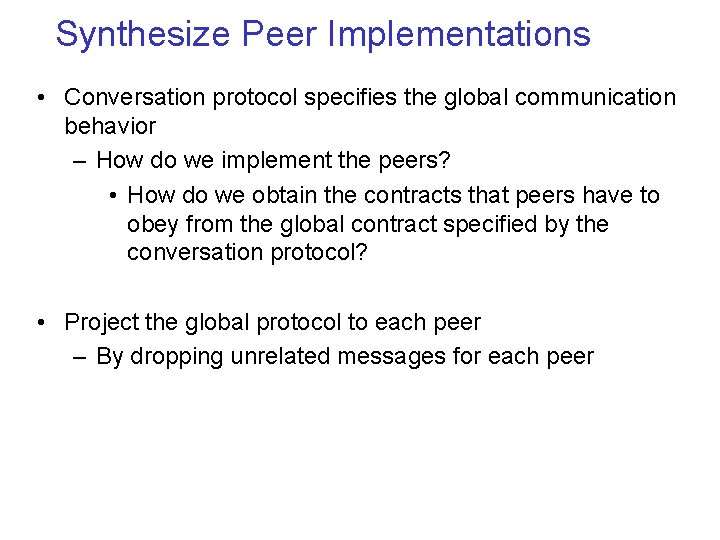
Synthesize Peer Implementations • Conversation protocol specifies the global communication behavior – How do we implement the peers? • How do we obtain the contracts that peers have to obey from the global contract specified by the conversation protocol? • Project the global protocol to each peer – By dropping unrelated messages for each peer
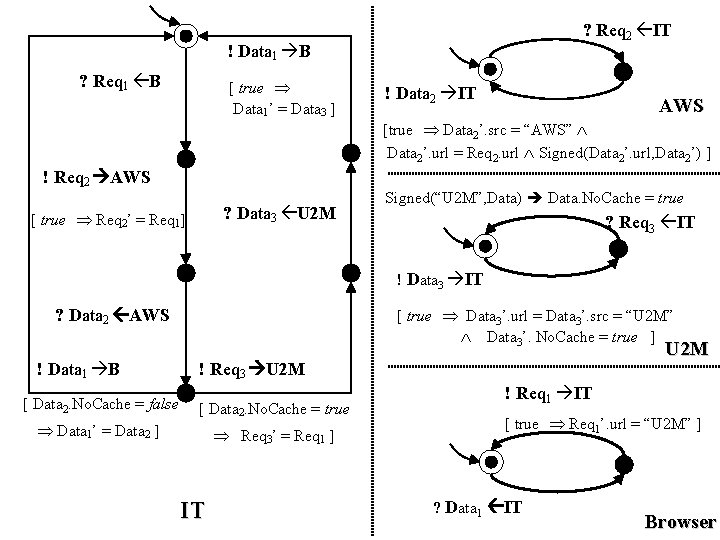
? Req 2 IT ! Data 1 B ? Req 1 B [ true Data 1’ = Data 3 ] ! Data 2 IT AWS [true Data 2’. src = “AWS” Data 2’. url = Req 2. url Signed(Data 2’. url, Data 2’) ] ! Req 2 AWS ? Data 3 U 2 M [ true Req 2’ = Req 1] Signed(“U 2 M”, Data) Data. No. Cache = true ? Req 3 IT ! Data 3 IT [ true Data 3’. url = Data 3’. src = “U 2 M” Data 3’. No. Cache = true ] ? Data 2 AWS ! Data 1 B U 2 M ! Req 3 U 2 M [ Data 2. No. Cache = false [ Data 2. No. Cache = true Data 1’ = Data 2 ] Req 3’ = Req 1 ] IT ! Req 1 IT [ true Req 1’. url = “U 2 M” ] ? Data 1 IT Browser
Interesting Question Conversations specified by the conversation protocol ? Conversations generated by the composed behavior of the projected services Are there conditions which ensure the equivalence?
Outline • • • Web Service Composition Model Capturing Global Behavior: Conversations Bottom-Up vs. Top-Down Specification and Verification Realizability Problem Current and Future Work
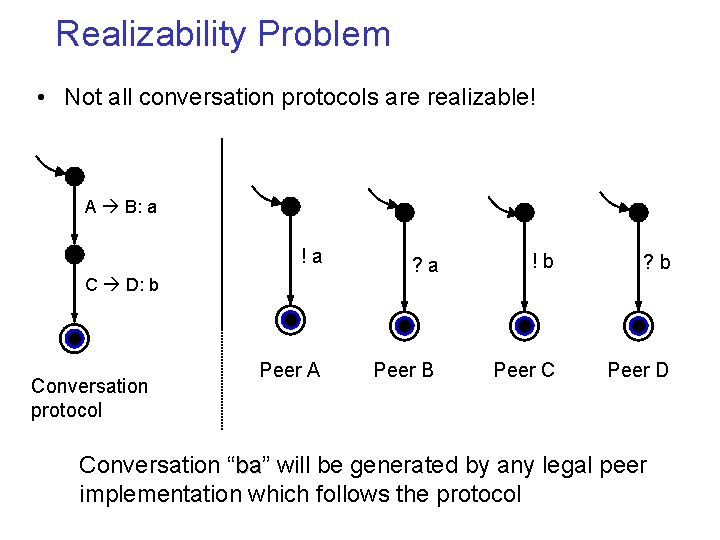
Realizability Problem • Not all conversation protocols are realizable! A B: a !a ? a !b ? b Peer A Peer B Peer C Peer D C D: b Conversation protocol Conversation “ba” ba will be generated by any legal peer implementation which follows the protocol
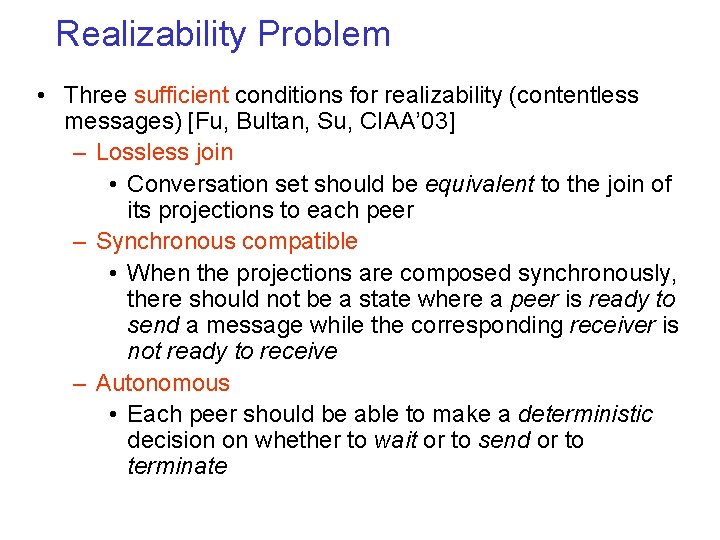
Realizability Problem • Three sufficient conditions for realizability (contentless messages) [Fu, Bultan, Su, CIAA’ 03] – Lossless join • Conversation set should be equivalent to the join of its projections to each peer – Synchronous compatible • When the projections are composed synchronously, there should not be a state where a peer is ready to send a message while the corresponding receiver is not ready to receive – Autonomous • Each peer should be able to make a deterministic decision on whether to wait or to send or to terminate
Realizability for Guarded Protocols • One natural conjecture: – Drop all guards and message contents to get the “skeleton” of the conversation protocol – Check realizability of the skeleton • Conjecture fails because there exists – Nonrealizable guarded protocols with realizable skeletons, and – Realizable guarded protocols with nonrealizable skeletons.
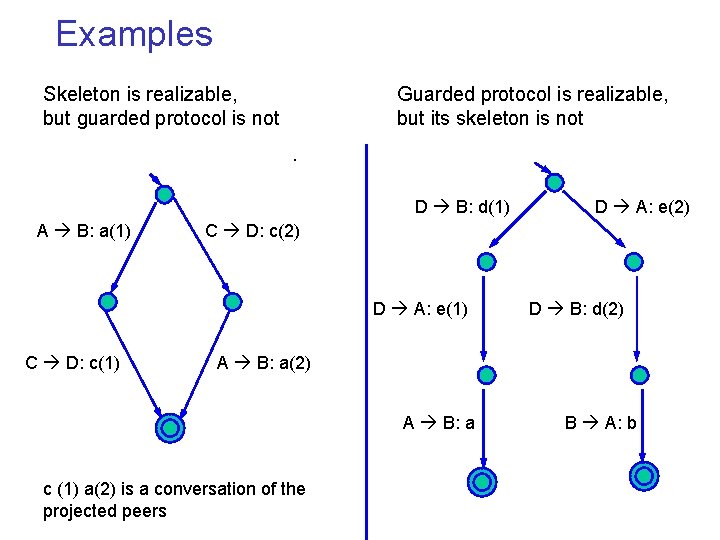
Examples Skeleton is realizable, but guarded protocol is not Guarded protocol is realizable, but its skeleton is not. D B: d(1) A B: a(1) C D: c(2) D A: e(1) C D: c(1) D A: e(2) D B: d(2) A B: a c (1) a(2) is a conversation of the projected peers B A: b
Realizability for Guarded Protocols • Skeleton Approach: The fourth condition – “unambiguous” property: for each word w accepted by a projected peer: there is one and only one w’ accepted by the conversation protocol whose projection to that peer is w • This extra condition might be too restrictive – Skeleton of U 2 M protocol does not satisfy the fourth condition • Exhaustive state space exploration – Treat each valuation of message contents as a new message class and get a standard conversation protocol without contents – Accurate, but costly
Current and Future Work • More analysis tools are necessary for guarded protocols with infinite domains – Symbolic analysis – Abstraction • Tying the formal model to the web service standards – Conversation protocols, peers: BPEL 4 WS – Message contents: XML, XML Schema – Guard conditions: XPath • Tools for model checking web services – Finite state vs. infinite-state – Message contents, local variables
Related Work • Conversation specification – IBM Conversation support project http: //www. research. ibm. com/convsupport/ – Conversation support for business process integration [Hanson, Nandi, Kumaran EDOCC’ 02] – Orchestrating computations on the world-wide web [Choi, Garg, Rai, Misram, Vin Euro. Par’ 02] • Verification of web services – Simulation, verification, composition of web services [Narayanan, Mc. Ilraith WWW’ 02] • Realizability problem – Realizability of Message Sequence Charts (MSC) [Alur, Etassami, Yannakakis ICSE’ 00, ICALP’ 01]
![Our Previous Work • Verification of Vortex workflows [Fu, Bultan, Hull, Su TACAS’ 01] Our Previous Work • Verification of Vortex workflows [Fu, Bultan, Hull, Su TACAS’ 01]](http://slidetodoc.com/presentation_image/43b3f49730b24083b94d64320923f56f/image-34.jpg)
Our Previous Work • Verification of Vortex workflows [Fu, Bultan, Hull, Su TACAS’ 01] – Restrict to finite domains, use SMV • Formal verification of e-services and workflows [Fu, Bultan, Hull, Su WES’ 01] – Infinite domains, use Action Language Verifier • Conversations specification [Bultan, Fu, Hull, Su WWW’ 01] – A formalism for specification of composite e-services • Conversation protocols [Fu, Bultan, Su CIAA’ 03] – Realizability conditions, model checking
- Slides: 34