A Sanitizable Signature Scheme with Aggregation ISPEC 2007
A Sanitizable Signature Scheme with Aggregation ISPEC 2007, LNCS 4464, pp. 51 -64, 2007, Springer-Verlag Berlin Heidelberg 2007 Author: T. Izu, N. Kunihiro, K. Ohta, M. Takenaka and T. Yoshioka Adviser: 鄭錦楸 , 郭文中 教授 Reporter: 林彥宏 1
Outline Introduction Preliminaries Sanitizable Signature Scheme with Aggregation Security of the Proposed Scheme Comparison with the IKTY Scheme Efficiency Improvements Comparison Conclusions 2
Introduction sanitizable signature scheme Transparency: dishonest sanitizer: additional sanitizing attack large overhead Contribution of This Paper construct an efficient and provably secure sanitizable signature scheme with aggregation reducing the number of hash values 3
Preliminaries G 1, G 2, GT are multiplicative cyclic group with order p g 1 , g 2 are generators of G 1, G 2 e be a bilinear map from G 1 × G 2 to GT such that e(ua, vb)=e(u, v)ab for all H 1: {0, 1}* →{0, 1}l H 2: random oracle model “short signatures from the Weil pairing”, ASIACRYPT 2001, LNCS 3679, pp. 159 -177 4
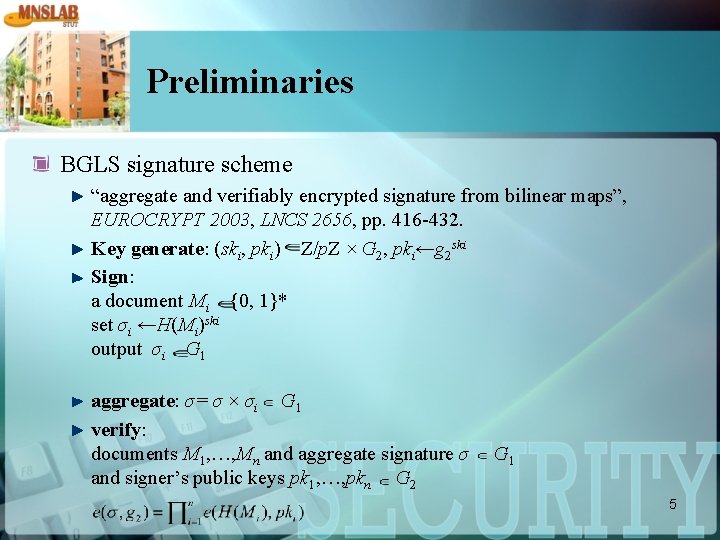
Preliminaries BGLS signature scheme “aggregate and verifiably encrypted signature from bilinear maps”, EUROCRYPT 2003, LNCS 2656, pp. 416 -432. Key generate: (ski, pki) Z/p. Z × G 2, pki←g 2 ski Sign: a document Mi {0, 1}* set σi ←H(Mi)ski output σi G 1 aggregate: σ= σ × σi G 1 verify: documents M 1, …, Mn and aggregate signature σ and signer’s public keys pk 1, …, pkn G 2 G 1 5
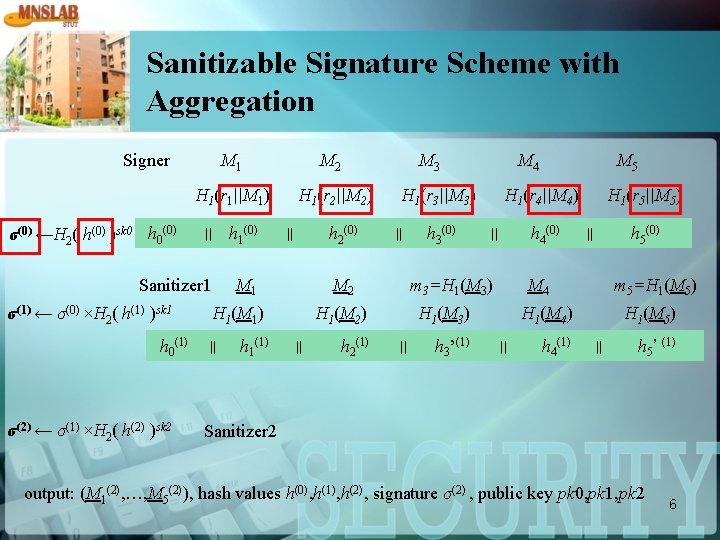
Sanitizable Signature Scheme with Aggregation Signer σ(0) ←H 2( h(0) )sk 0 h 0(0) M 1 M 2 H 1(r 1||M 1) H 1(r 2||M 2) || h 1(0) Sanitizer 1 σ(1) ← σ(0) ×H 2( h(1) )sk 1 h 0(1) σ(2) ← σ(1) ×H 2( h(2) )sk 2 h 2(0) || M 1 h 1(1) || h 2(1) h 3(0) h 4(0) || h 3’(1) H 1(r 5||M 5) h 5(0) || M 4 H 1(M 3) || M 5 H 1(r 4||M 4) m 3=H 1(M 3) H 1(M 2) || M 4 H 1(r 3||M 3) M 2 H 1(M 1) || M 3 m 5=H 1(M 5) H 1(M 4) || h 4(1) H 1(M 5) || h 5’ (1) Sanitizer 2 output: (M 1(2), …, M 5(2)), hash values h(0), h(1), h(2), signature σ(2) , public key pk 0, pk 1, pk 2 6
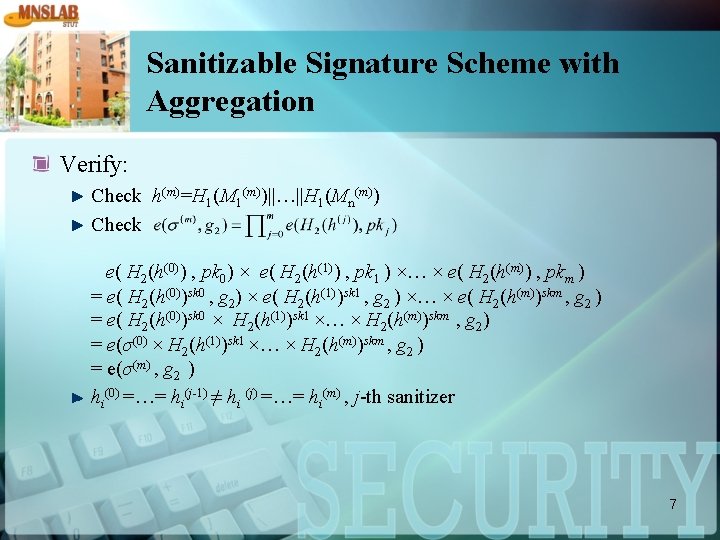
Sanitizable Signature Scheme with Aggregation Verify: Check h(m)=H 1(M 1(m))||…||H 1(Mn(m)) Check e( H 2(h(0)) , pk 0) × e( H 2(h(1)) , pk 1 ) ×… × e( H 2(h(m)) , pkm ) = e( H 2(h(0))sk 0 , g 2) × e( H 2(h(1))sk 1 , g 2 ) ×… × e( H 2(h(m))skm , g 2 ) = e( H 2(h(0))sk 0 × H 2(h(1))sk 1 ×… × H 2(h(m))skm , g 2) = e(σ(0) × H 2(h(1))sk 1 ×… × H 2(h(m))skm , g 2 ) = e(σ(m) , g 2 ) hi(0) =…= hi(j-1) ≠ hi (j) =…= hi(m) , j-th sanitizer 7
Security of the Proposed Scheme no one can forge a valid aggregate signature and corresponding messages no information of original subdocuments are leaked from sanitized subdocuments 8
Comparison with the IKTY Scheme “A Partially Sanitizable Signature Scheme ”, ICICS 2005, LNCS 3783, pp. 72 -83 Sanitized document, j+1 hash information h(0) , …, h(j) , and j+1 signature σ0, …, σj Delete-of-Intermediate-Sanitizer Attack Delete-of-Last-Sanitizer Attack 9
Efficiency Improvements sanitizers: m subdocuments: n n subdocuments: M(m)={M 1(m), …, Mn(m)} (m+1)(n+1) hash values: h 0(0), …, hn(0), h 0(1), …, hn(1), …, h 0(m), …, hn(m) (m+1) public keys: pk 0 , …, pkm an aggregate signature: σ(m) 10
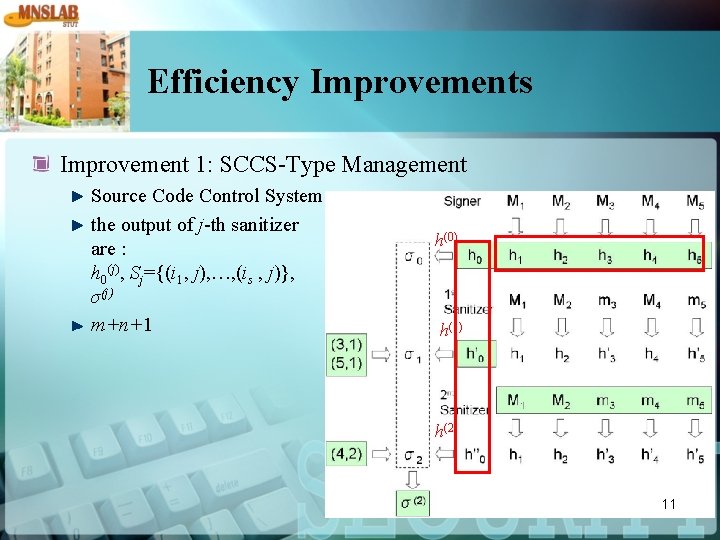
Efficiency Improvements Improvement 1: SCCS-Type Management Source Code Control System the output of j-th sanitizer are : h 0(j), Sj={(i 1, j), …, (is , j)}, σ(j) m+n+1 h(0) h(1) h(2) 11
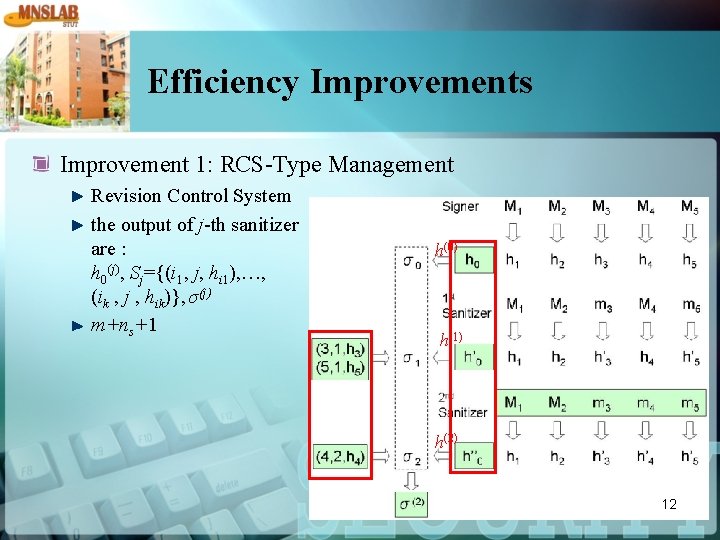
Efficiency Improvements Improvement 1: RCS-Type Management Revision Control System the output of j-th sanitizer are : h 0(j), Sj={(i 1, j, hi 1), …, (ik , j , hik)}, σ(j) m+ns+1 h(0) h(1) h(2) 12
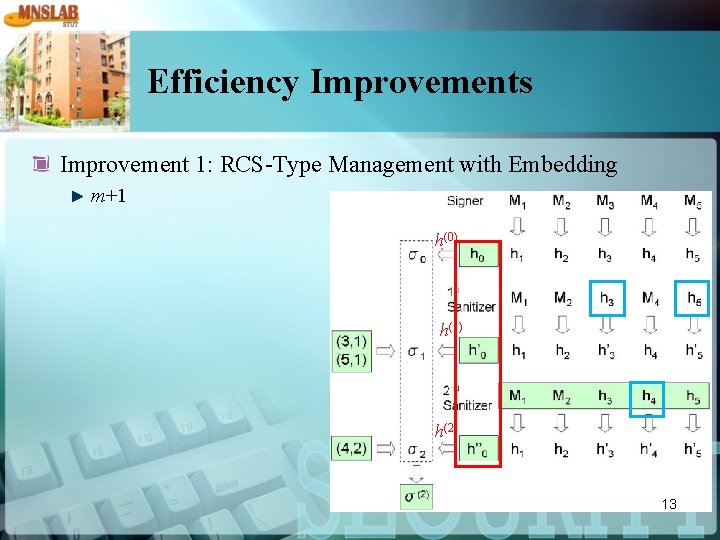
Efficiency Improvements Improvement 1: RCS-Type Management with Embedding m+1 h(0) h(1) h(2) 13
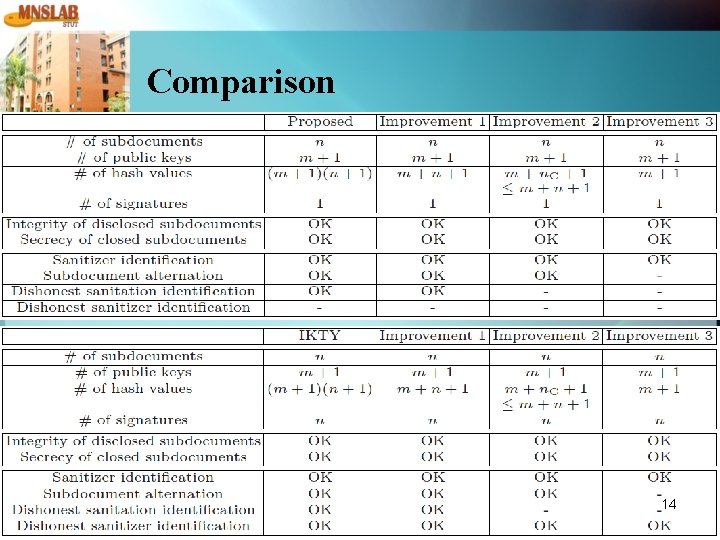
Comparison 14
Conclusions This paper constructs an efficient and provably secure sanitizable signature scheme with aggregation. We also provide security proofs of the proposed scheme. In addition, some improvements are proposed for efficiency. 15
- Slides: 15