A Multifaceted Approach to Understanding the Botnet Phenomenon
A Multifaceted Approach to Understanding the Botnet Phenomenon Authors : Moheeb Abu Rajab, Jay Zarfoss, Fabian Monrose, Andreas Terzis Computer Science Department Johns Hopkins University Presented at : Internet Measurement Conference, IMC'06, Brazil, October 2006 Presented By : Ramanarayanan Ramani
Outline Working of Botnets n Measuring Botnets n Inference from Measurement n Strengths n Weaknesses n Suggestions n
Botnets n A botnet is a network of infected end-hosts (bots) under the command of a botmaster. n 3 Different Protocols Used: q q q IRC HTTP P 2 P
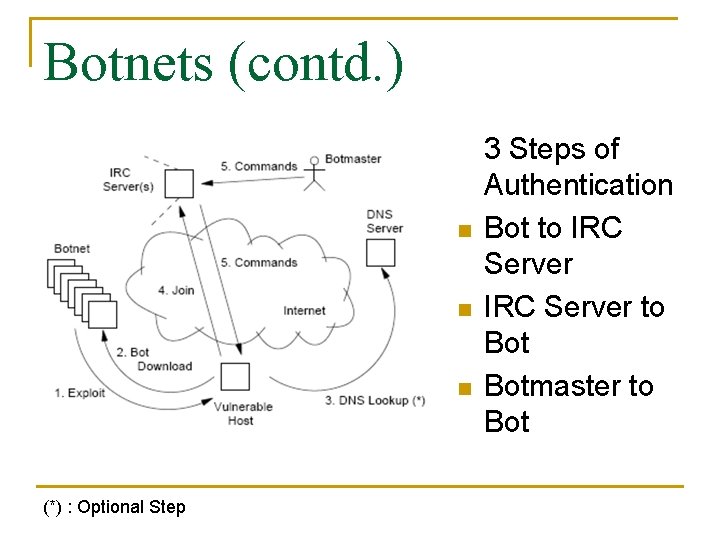
Botnets (contd. ) n n n (*) : Optional Step 3 Steps of Authentication Bot to IRC Server to Botmaster to Bot
Measuring Botnets n Three Distinct Phases q q q Malware Collection Collect as many bot binaries as possible Binary analysis via gray-box testing Extract the features of suspicious binaries Longitudinal tracking Track how bots spread and its reach
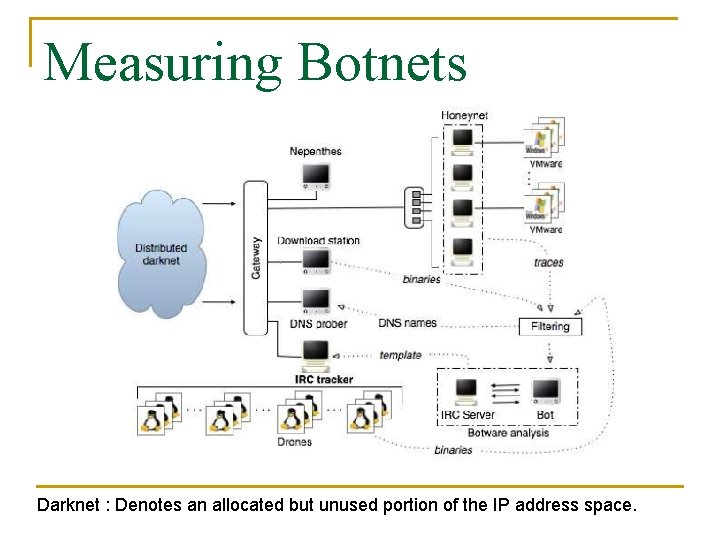
Measuring Botnets Darknet : Denotes an allocated but unused portion of the IP address space.
Malware Collection n Nepenthes is a low interaction honeypot Nepenthes mimics the replies generated by vulnerable services in order to collect the first stage exploit Modules in nepenthes q q q Resolve DNS asynchronous Emulate vulnerabilities Download files – Done here by the Download Station Submit the downloaded files Trigger events Shellcode handler
Malware Collection n n Honeynets also used along with nepenthes Catches exploits missed by nepenthes Unpatched Windows XP are run which is base copy Infected honeypot compared with base to identify Botnet binary
Gateway n n n Routing to different components Firewall : Prevent outbound attacks & self infection by honeypots Detect & Analyze outgoing traffic for infections in honeypot Only 1 infection in a honeypot Several other functions
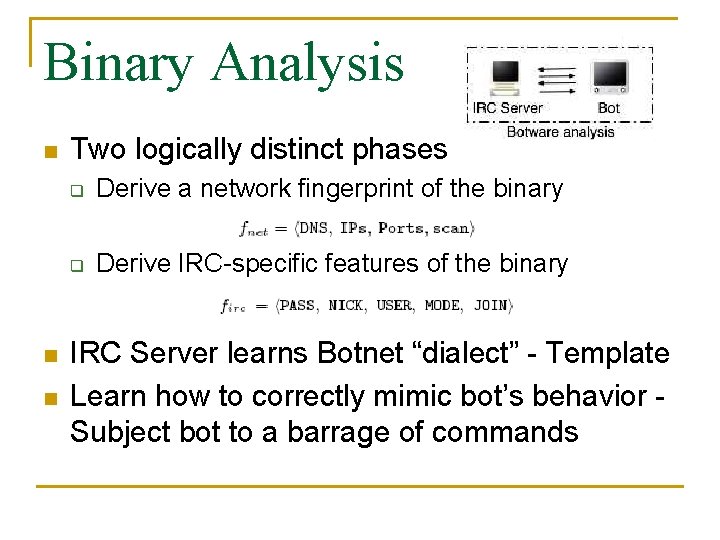
Binary Analysis n n n Two logically distinct phases q Derive a network fingerprint of the binary q Derive IRC-specific features of the binary IRC Server learns Botnet “dialect” - Template Learn how to correctly mimic bot’s behavior Subject bot to a barrage of commands
IRC Tracker n n Use template to mimic bot Connect to real IRC server Communicate with botmaster using bot “dialect” Drones modified and used to act as IRC Client by the tracker to Cover lot of IP addresss
DNS Tracker n n Bots issue DNS queries to resolve the IP addresses of their IRC servers Tracker uses DNS requests Has 800, 000 entries after reduction Maintain hits to a server
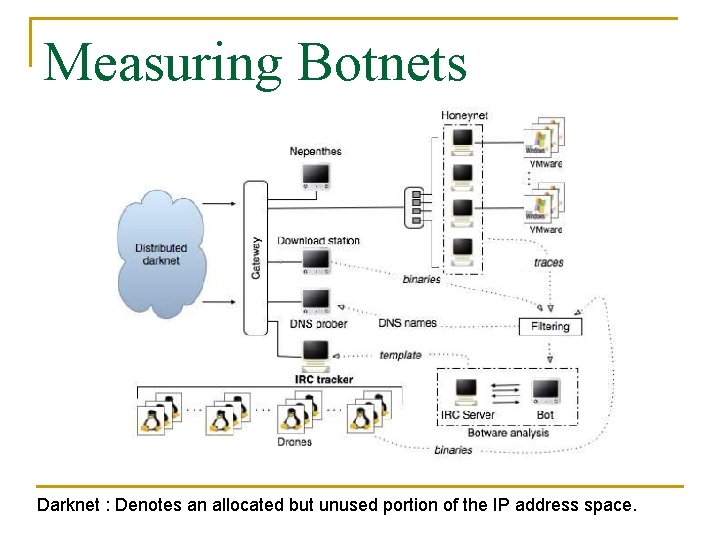
Measuring Botnets Darknet : Denotes an allocated but unused portion of the IP address space.
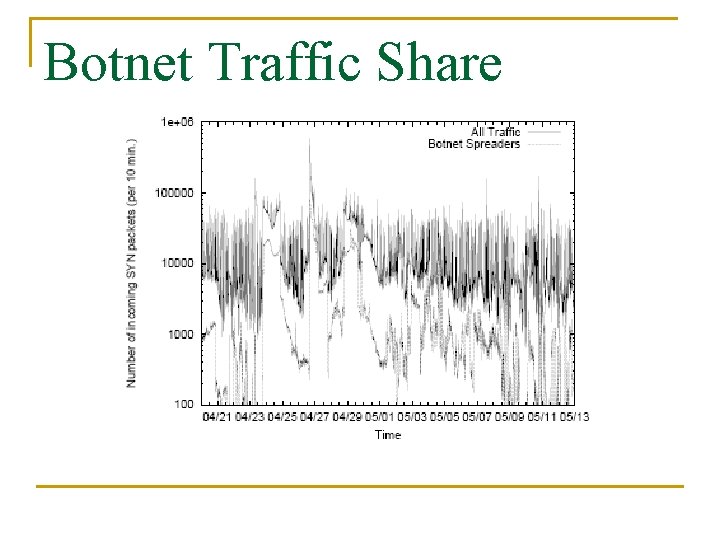
Botnet Traffic Share
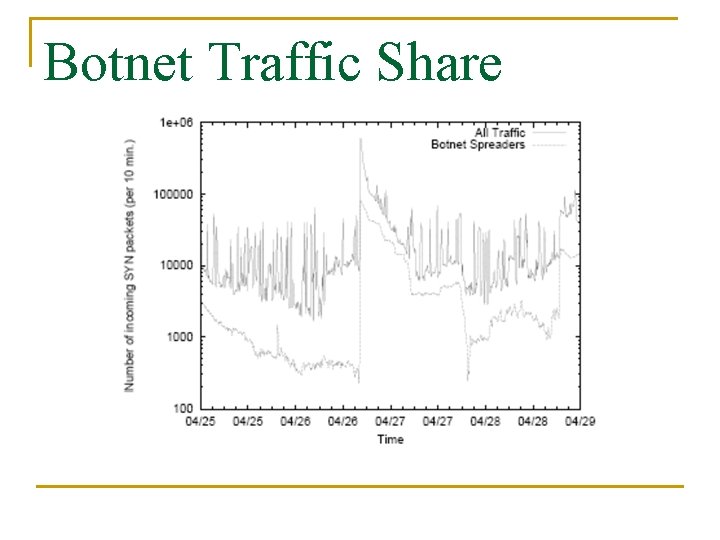
Botnet Traffic Share
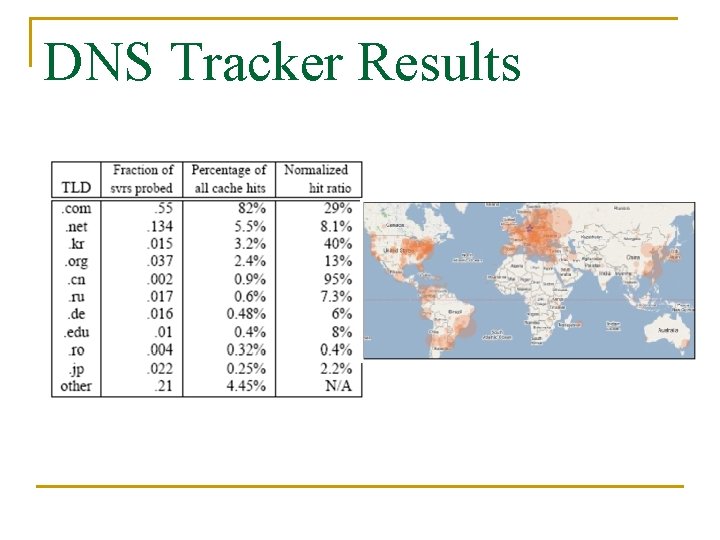
DNS Tracker Results
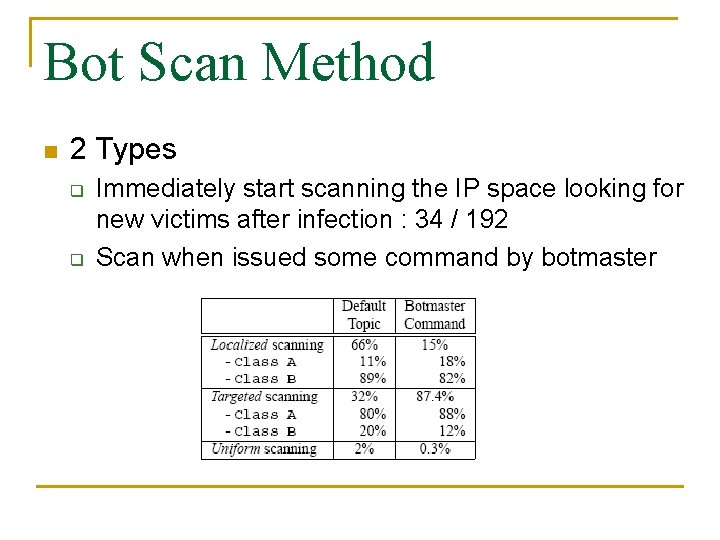
Bot Scan Method n 2 Types q q Immediately start scanning the IP space looking for new victims after infection : 34 / 192 Scan when issued some command by botmaster
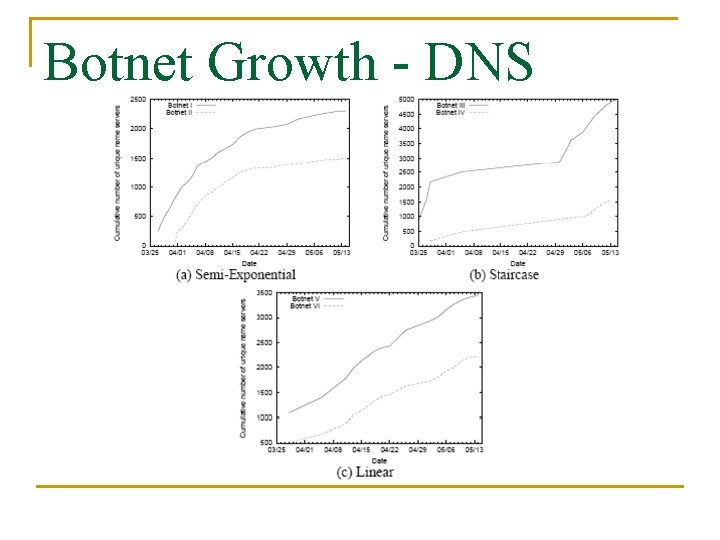
Botnet Growth - DNS
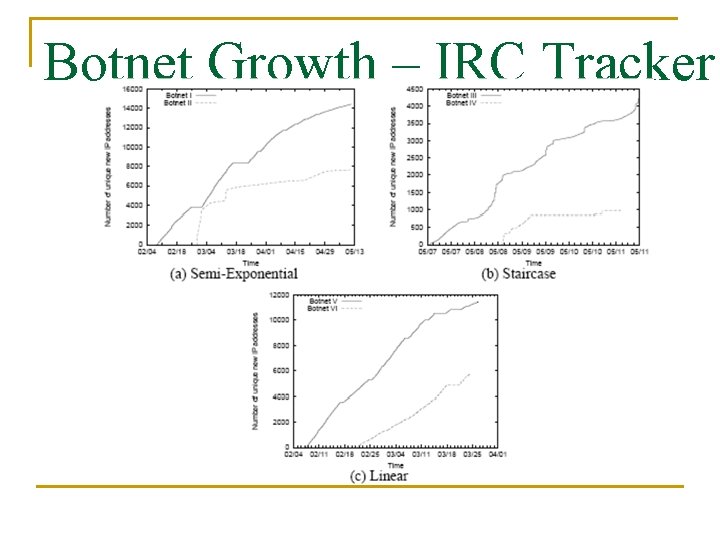
Botnet Growth – IRC Tracker
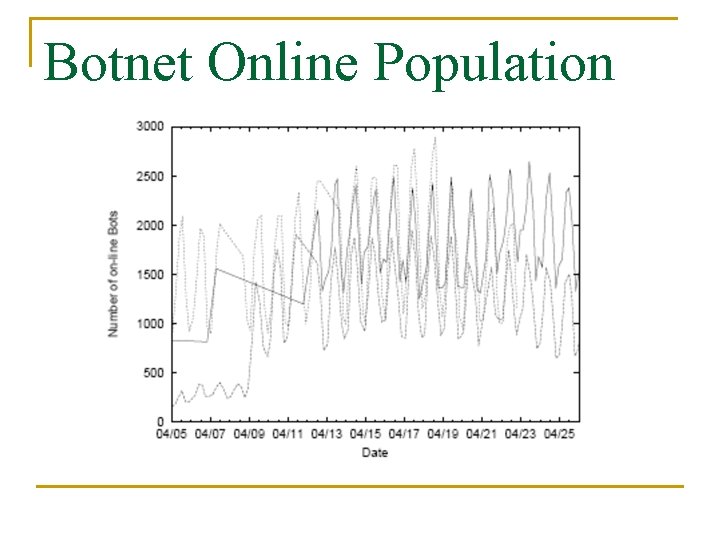
Botnet Online Population
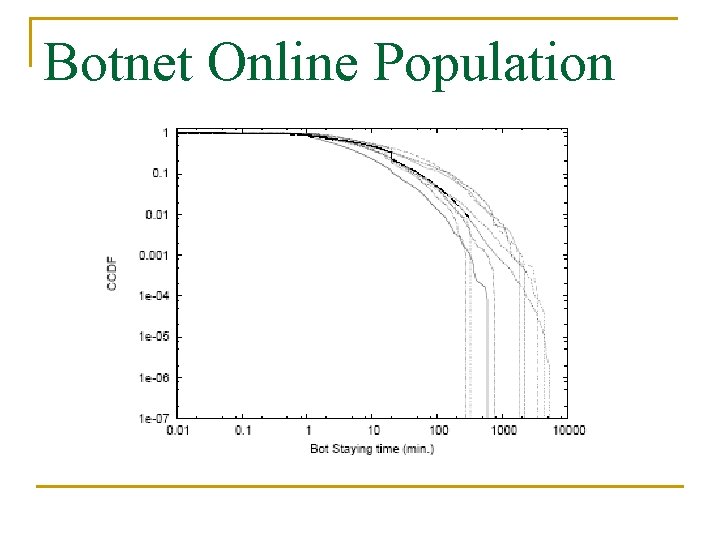
Botnet Online Population
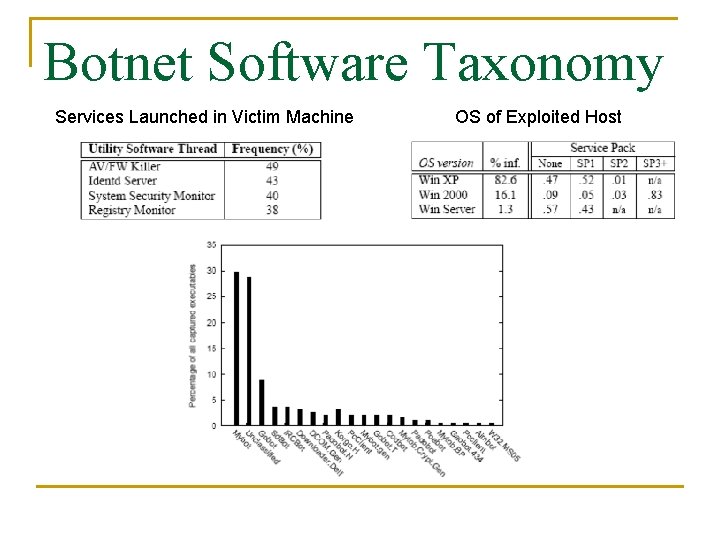
Botnet Software Taxonomy Services Launched in Victim Machine OS of Exploited Host
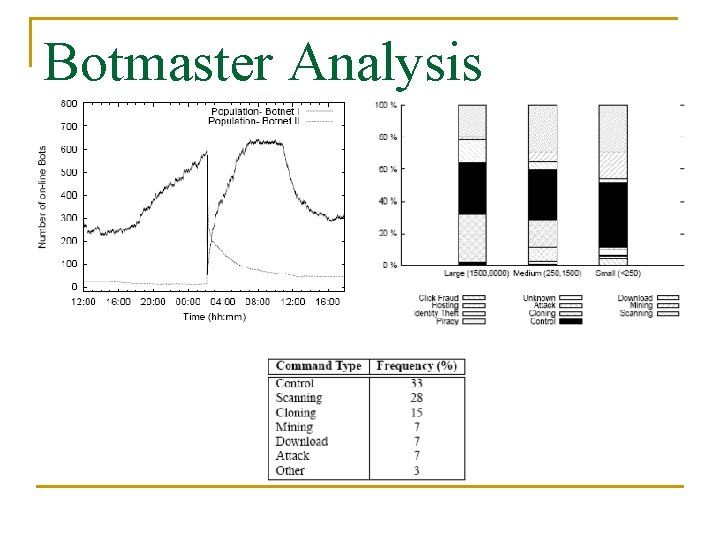
Botmaster Analysis
Strengths All aspects of a botnet analyzed n No prior analysis of bots n Ability to model various types of bots n
Weakness Only Microsoft Windows systems analyzed n Focus on IRC-based bots as they are predominant n
Suggestions Use the analysis to model new bots n Use the analysis to model protection methods n
Questions
- Slides: 27