A Model for AttributeBased UserRole Assignment Mohammad A
A Model for Attribute-Based User-Role Assignment Mohammad A. Al-Kahtani Ravi Sandhu George Mason University Single. Sign. On. net, Inc. & malkahta@gmu. edu George Mason University sandhu@gmu. edu ACSAC 2002 © Mohammad al-Kahtani 2002 1
Presentation Roadmap 1. 2. 3. 4. 5. Introduction Problem Description Suggested Solution Case Study Expressing MAC ACSAC 2002 © Mohammad al-Kahtani 2002 2
Introduction • Role-Based Access Control (RBAC): A proven alternative to DAC and MAC • RBAC basic components: 1. Users 2. Roles 3. Permissions ACSAC 2002 © Mohammad al-Kahtani 2002 3
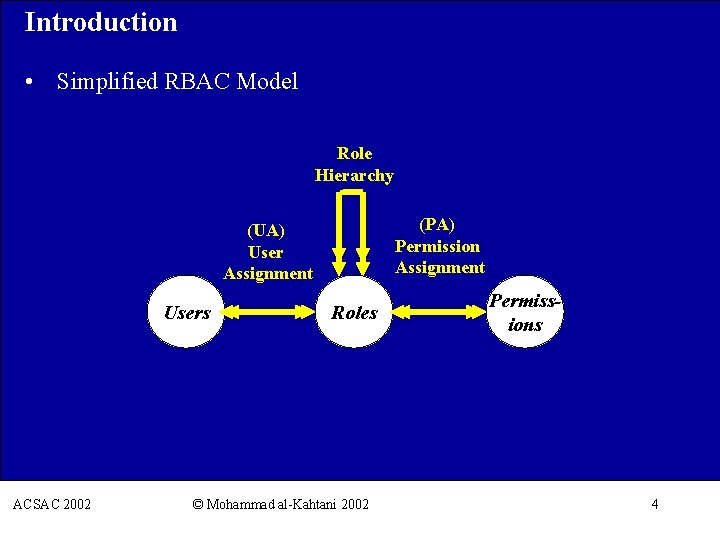
Introduction • Simplified RBAC Model Role Hierarchy (PA) Permission Assignment (UA) User Assignment Users Roles ACSAC 2002 © Mohammad al-Kahtani 2002 Permissions 4
Presentation Roadmap 1. 2. 3. 4. 5. Introduction Problem Description Suggested Solution Case Study Expressing MAC ACSAC 2002 © Mohammad al-Kahtani 2002 5
Problem Description • In RBAC, user-to-role assignment is done manually • Many enterprises have huge customer bases: § Banks § Utilities companies § Popular web sties • Manual assignment becomes a formidable task ACSAC 2002 © Mohammad al-Kahtani 2002 6
Presentation Roadmap 1. 2. 3. 4. 5. Introduction Problem Description Suggested Solution Case Study Expressing MAC ACSAC 2002 © Mohammad al-Kahtani 2002 7
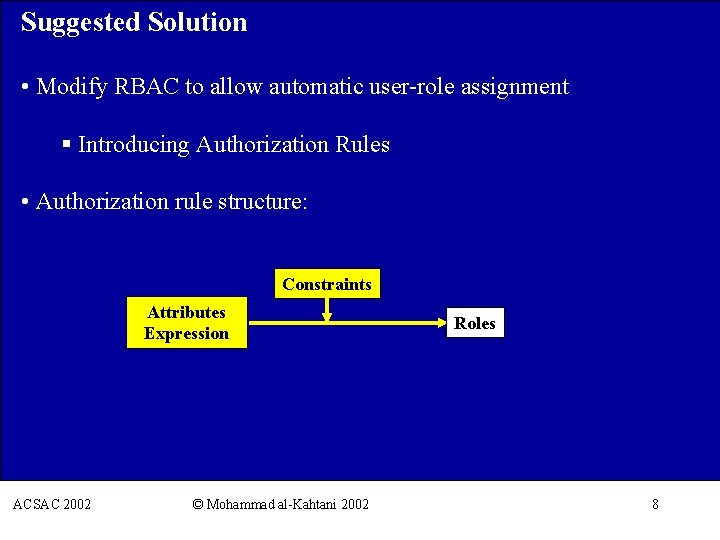
Suggested Solution • Modify RBAC to allow automatic user-role assignment § Introducing Authorization Rules • Authorization rule structure: Constraints Attributes Expression Roles ACSAC 2002 © Mohammad al-Kahtani 2002 8
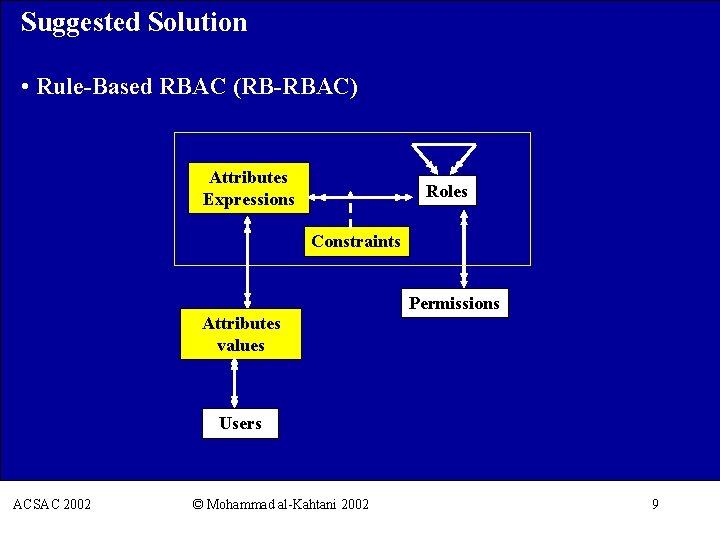
Suggested Solution • Rule-Based RBAC (RB-RBAC) Attributes Expressions Roles Constraints Permissions Attributes values Users ACSAC 2002 © Mohammad al-Kahtani 2002 9
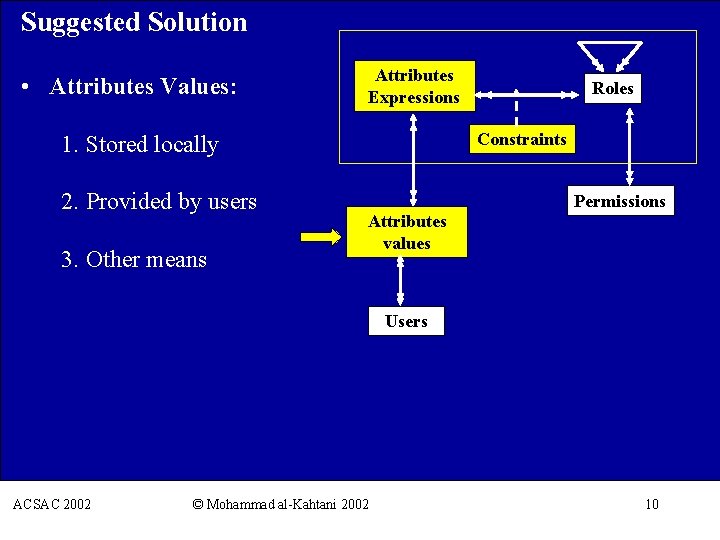
Suggested Solution • Attributes Values: Attributes Expressions Constraints 1. Stored locally 2. Provided by users 3. Other means Roles Permissions Attributes values Users ACSAC 2002 © Mohammad al-Kahtani 2002 10
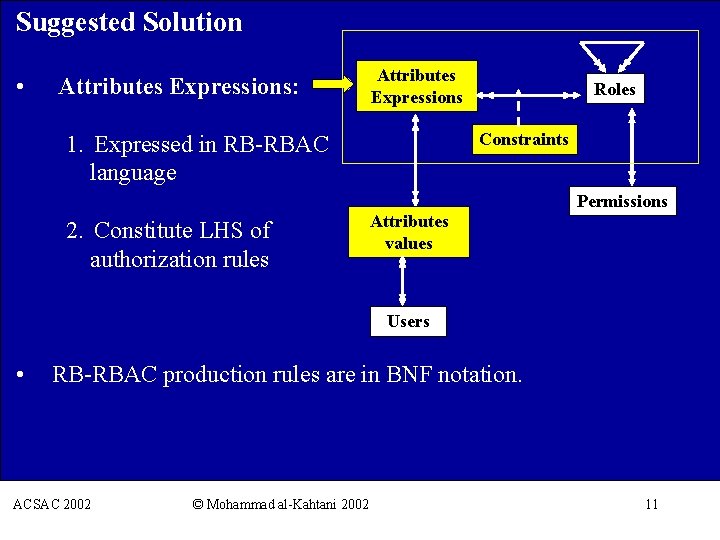
Suggested Solution • Attributes Expressions: Attributes Expressions Roles Constraints 1. Expressed in RB-RBAC language Permissions 2. Constitute LHS of authorization rules Attributes values Users • RB-RBAC production rules are in BNF notation. ACSAC 2002 © Mohammad al-Kahtani 2002 11
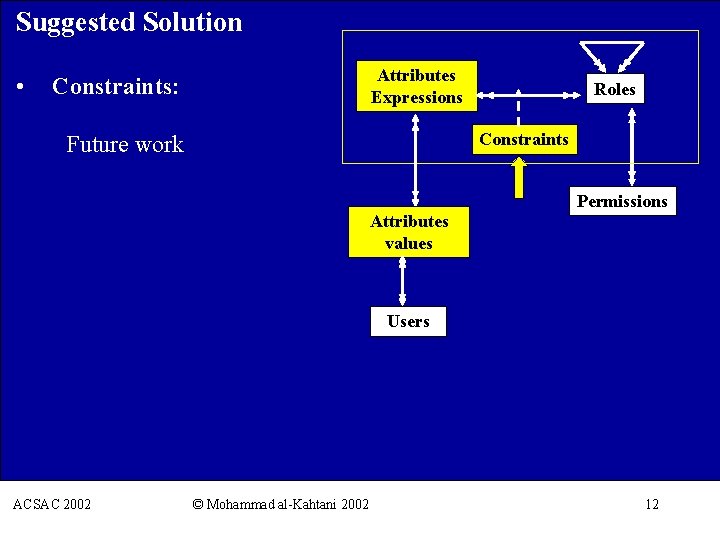
Suggested Solution • Constraints: Attributes Expressions Roles Constraints Future work Permissions Attributes values Users ACSAC 2002 © Mohammad al-Kahtani 2002 12
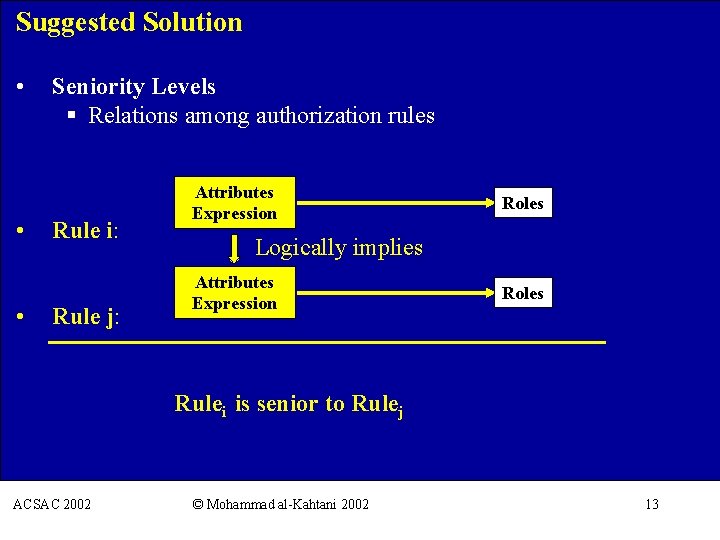
Suggested Solution • • • Seniority Levels § Relations among authorization rules Rule i: Rule j: Attributes Expression Roles Logically implies Attributes Expression Roles Rulei is senior to Rulej ACSAC 2002 © Mohammad al-Kahtani 2002 13
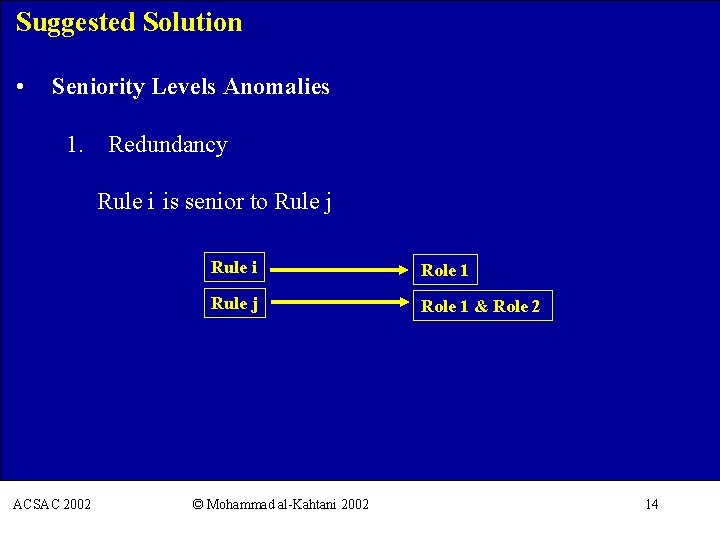
Suggested Solution • Seniority Levels Anomalies 1. Redundancy Rule i is senior to Rule j Rule i Role 1 Rule j Role 1 & Role 2 ACSAC 2002 © Mohammad al-Kahtani 2002 14
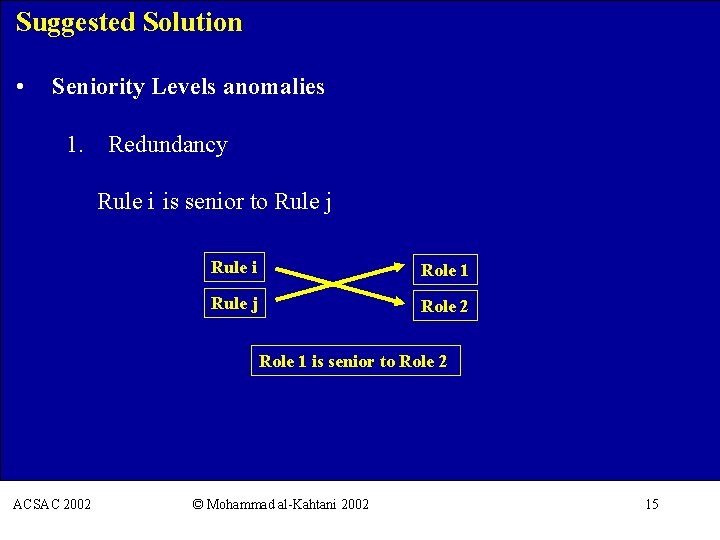
Suggested Solution • Seniority Levels anomalies 1. Redundancy Rule i is senior to Rule j Rule i Role 1 Rule j Role 2 Role 1 is senior to Role 2 ACSAC 2002 © Mohammad al-Kahtani 2002 15
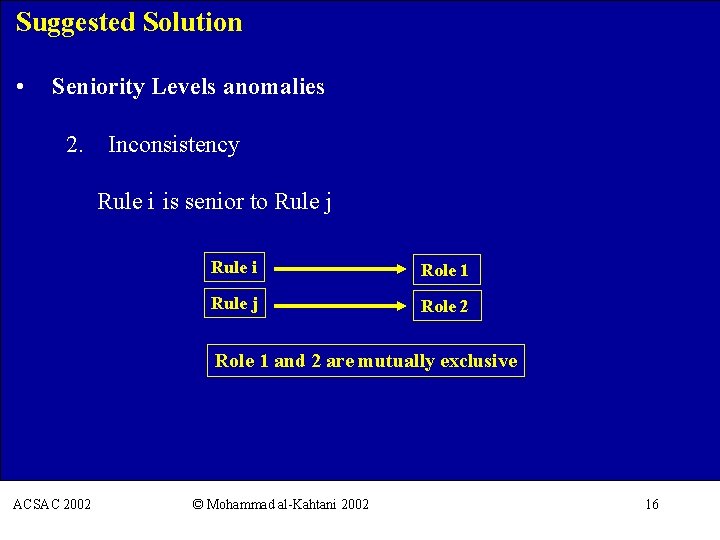
Suggested Solution • Seniority Levels anomalies 2. Inconsistency Rule i is senior to Rule j Rule i Role 1 Rule j Role 2 Role 1 and 2 are mutually exclusive ACSAC 2002 © Mohammad al-Kahtani 2002 16
Presentation Roadmap 1. 2. 3. 4. 5. Introduction Problem Description Suggested Solution Case Study Expressing MAC ACSAC 2002 © Mohammad al-Kahtani 2002 17
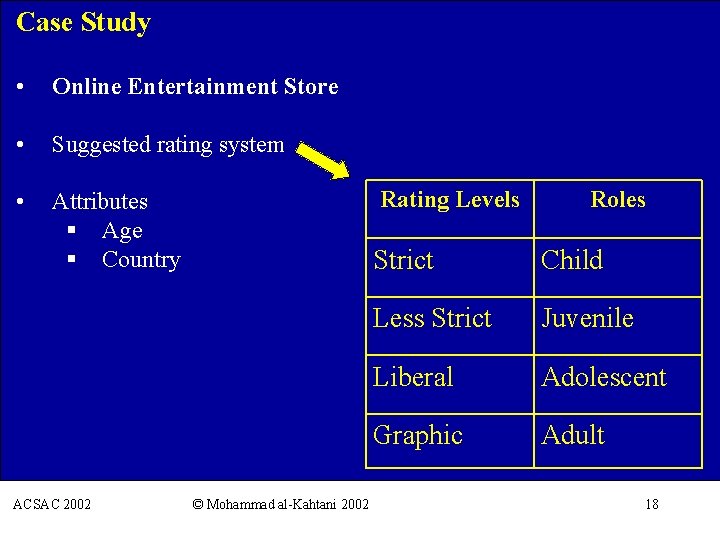
Case Study • Online Entertainment Store • Suggested rating system • Attributes § Age § Country ACSAC 2002 © Mohammad al-Kahtani 2002 Rating Levels Roles Strict Child Less Strict Juvenile Liberal Adolescent Graphic Adult 18
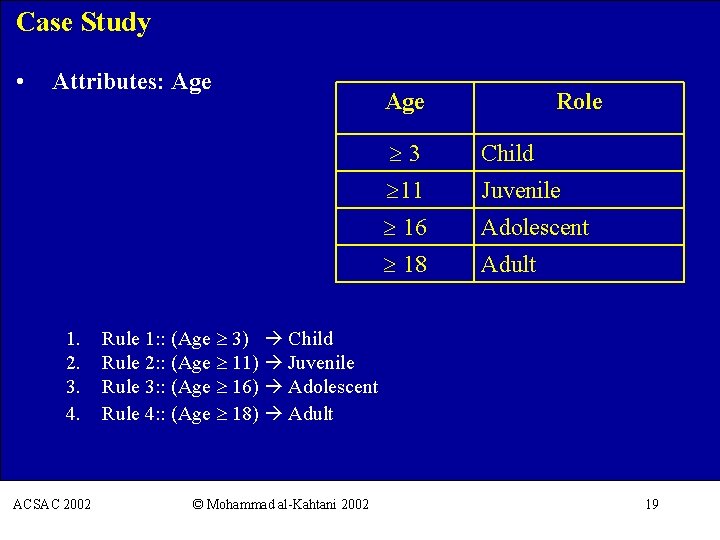
Case Study • Attributes: Age 1. 2. 3. 4. Age Role 3 Child 11 Juvenile 16 Adolescent 18 Adult Rule 1: : (Age 3) Child Rule 2: : (Age 11) Juvenile Rule 3: : (Age 16) Adolescent Rule 4: : (Age 18) Adult ACSAC 2002 © Mohammad al-Kahtani 2002 19
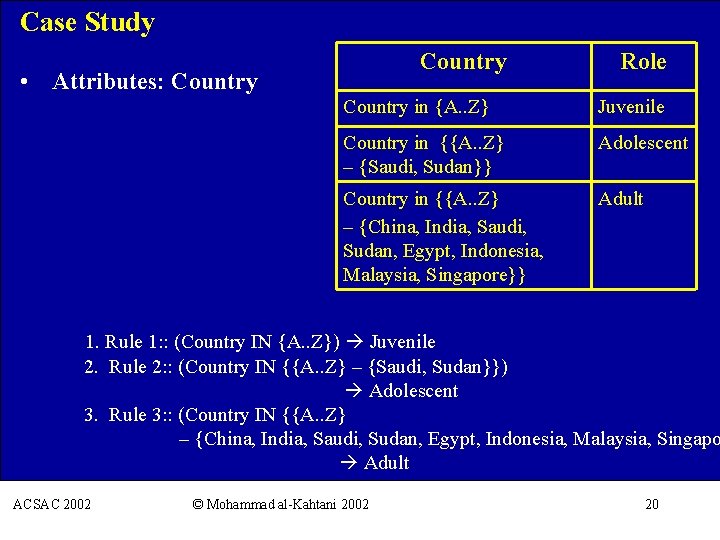
Case Study Country • Attributes: Country Role Country in {A. . Z} Juvenile Country in {{A. . Z} – {Saudi, Sudan}} Adolescent Country in {{A. . Z} – {China, India, Saudi, Sudan, Egypt, Indonesia, Malaysia, Singapore}} Adult 1. Rule 1: : (Country IN {A. . Z}) Juvenile 2. Rule 2: : (Country IN {{A. . Z} – {Saudi, Sudan}}) Adolescent 3. Rule 3: : (Country IN {{A. . Z} – {China, India, Saudi, Sudan, Egypt, Indonesia, Malaysia, Singapo Adult ACSAC 2002 © Mohammad al-Kahtani 2002 20
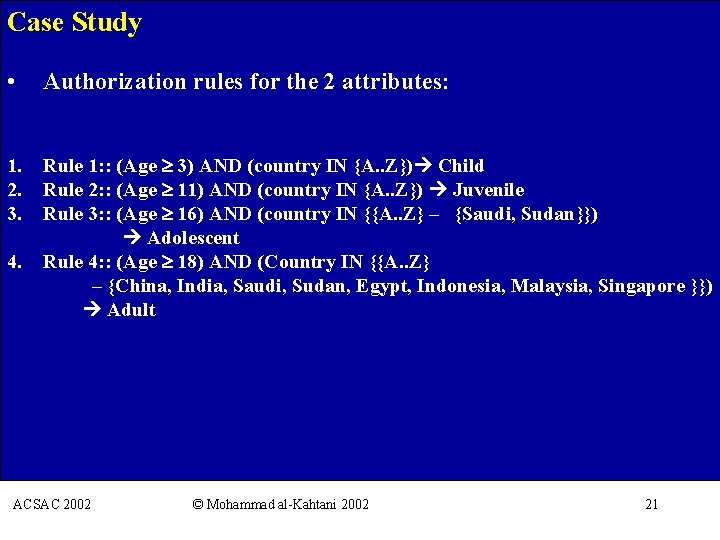
Case Study • Authorization rules for the 2 attributes: 1. Rule 1: : (Age 3) AND (country IN {A. . Z}) Child 2. Rule 2: : (Age 11) AND (country IN {A. . Z}) Juvenile 3. Rule 3: : (Age 16) AND (country IN {{A. . Z} – {Saudi, Sudan}}) Adolescent 4. Rule 4: : (Age 18) AND (Country IN {{A. . Z} – {China, India, Saudi, Sudan, Egypt, Indonesia, Malaysia, Singapore }}) Adult ACSAC 2002 © Mohammad al-Kahtani 2002 21
Presentation Roadmap 1. 2. 3. 4. 5. Introduction Problem Description Suggested Solution Case Study Expressing MAC ACSAC 2002 © Mohammad al-Kahtani 2002 22
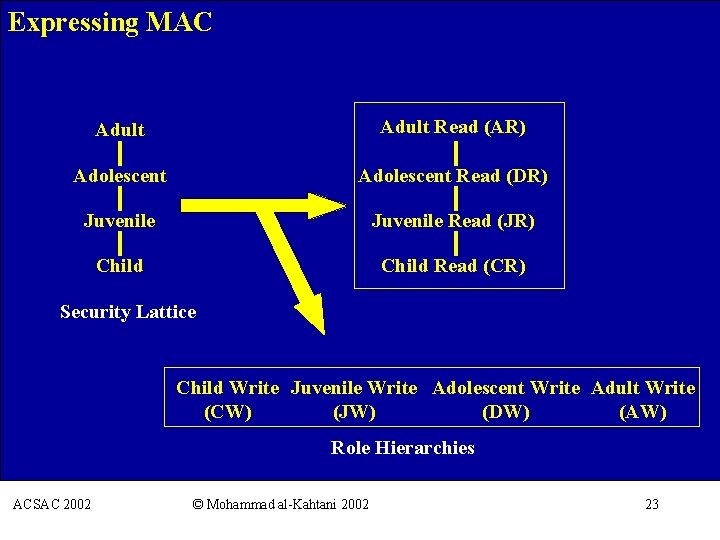
Expressing MAC Adult Read (AR) Adolescent Read (DR) Juvenile Read (JR) Child Read (CR) Security Lattice Child Write Juvenile Write Adolescent Write Adult Write (CW) (JW) (DW) (AW) Role Hierarchies ACSAC 2002 © Mohammad al-Kahtani 2002 23
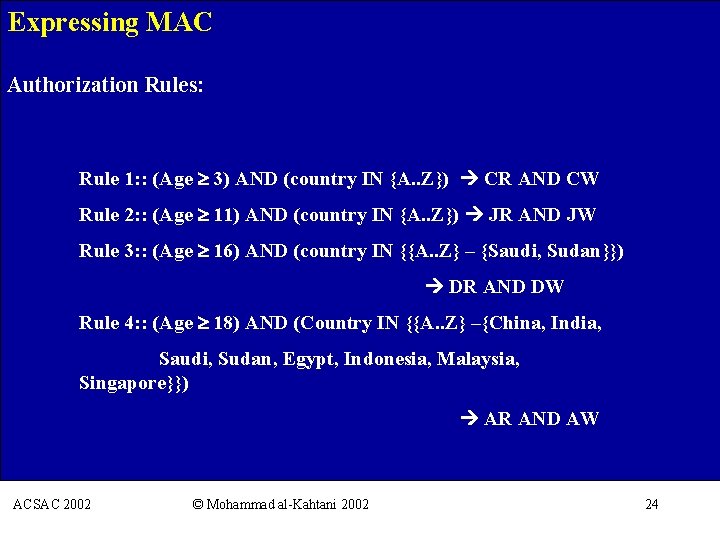
Expressing MAC Authorization Rules: Rule 1: : (Age 3) AND (country IN {A. . Z}) CR AND CW Rule 2: : (Age 11) AND (country IN {A. . Z}) JR AND JW Rule 3: : (Age 16) AND (country IN {{A. . Z} – {Saudi, Sudan}}) DR AND DW Rule 4: : (Age 18) AND (Country IN {{A. . Z} –{China, India, Saudi, Sudan, Egypt, Indonesia, Malaysia, Singapore}}) AR AND AW ACSAC 2002 © Mohammad al-Kahtani 2002 24
- Slides: 24