A LowCost Flooding Algorithm for Wireless Sensor Networks

- Slides: 25
A Low-Cost Flooding Algorithm for Wireless Sensor Networks WCNC 2007, Hong Kong Ou Liang, Ahmet Sekercioglu and Nallasamy Mani Department of Electrical and Computer Systems Engineering Monash University, Australia www. eng. monash. edu
Sections 1. Flooding in WSNs. 2. Our Low-Cost Flooding algorithm. 3. Simulation study. 4. Conclusion and future work. www. eng. monash. edu 2
Section 1 Section 2 Section 3 Section 4 Flooding in WSNs • Flooding is the simplest way of routing. It requires each node in the network to broadcast a packet upon receiving it for the first time. • Flooding is widely used in WSNs by many applications. Problems: • Redundant packets — nodes receive multiple copies of a packet. • Contention and collision — happen when using a contention MAC layer like IEEE 802. 11. • Energy wastage — redundant retransmissions consume energy. www. eng. monash. edu 3
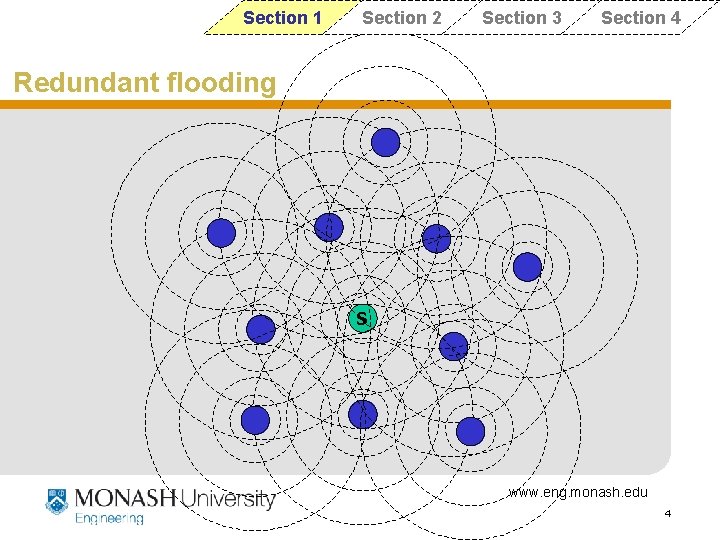
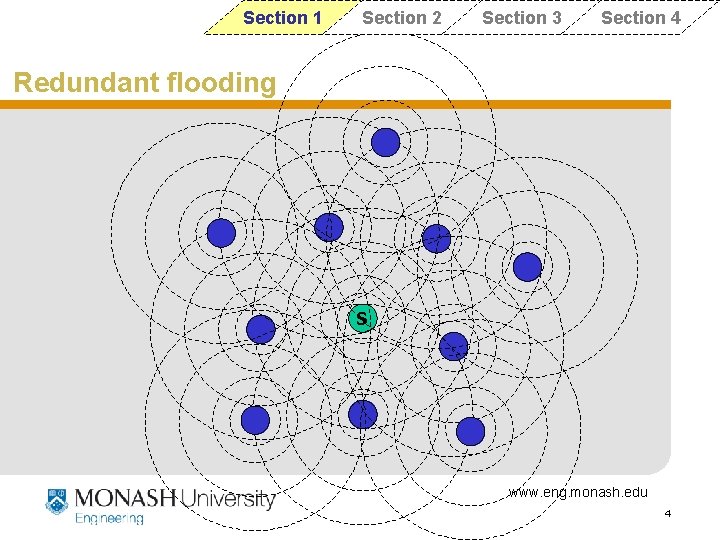
Section 1 Section 2 Section 3 Section 4 Redundant flooding S www. eng. monash. edu 4
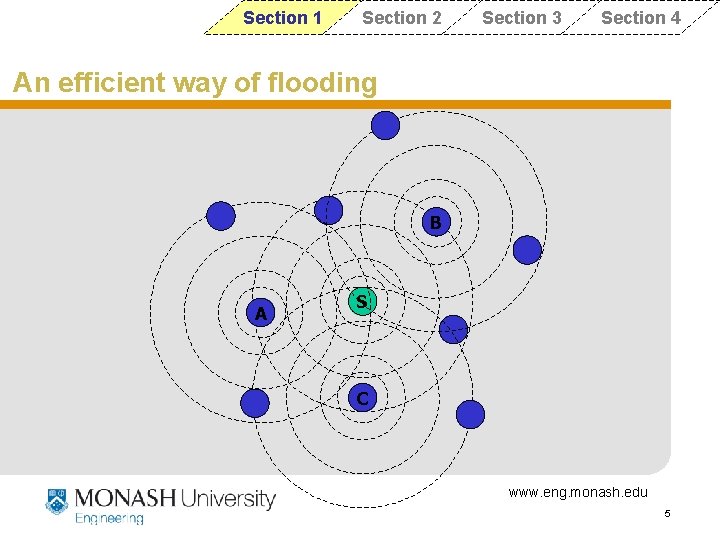
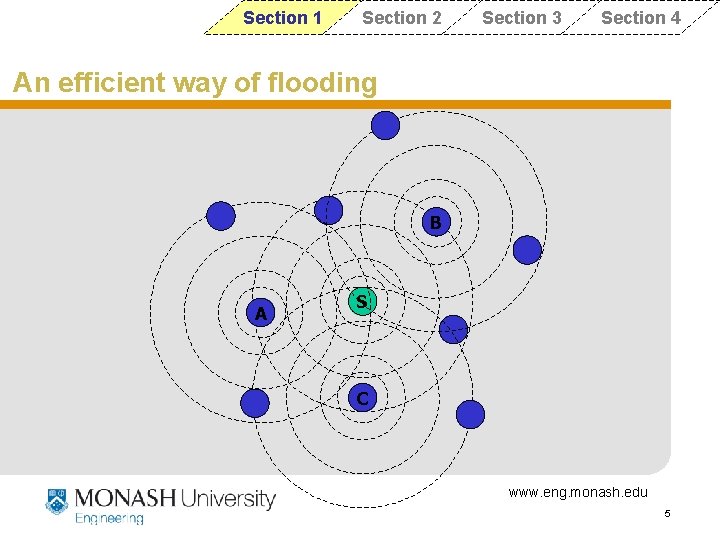
Section 1 Section 2 Section 3 Section 4 An efficient way of flooding B A S C www. eng. monash. edu 5
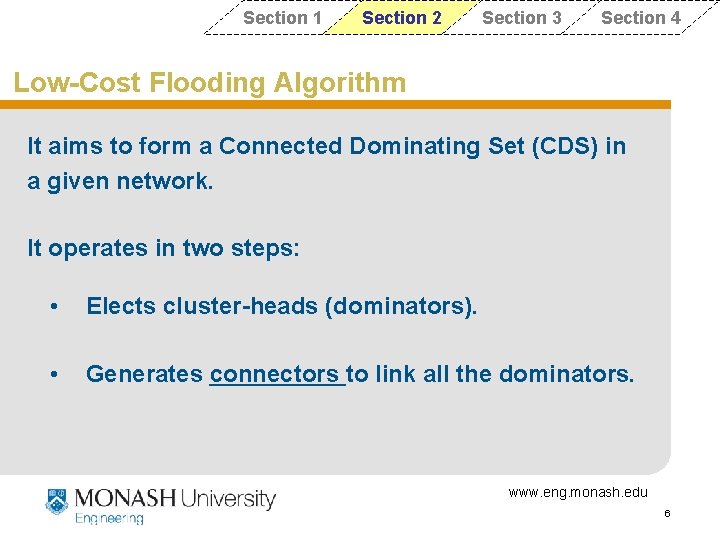
Section 1 Section 2 Section 3 Section 4 Low-Cost Flooding Algorithm It aims to form a Connected Dominating Set (CDS) in a given network. It operates in two steps: • Elects cluster-heads (dominators). • Generates connectors to link all the dominators. www. eng. monash. edu 6
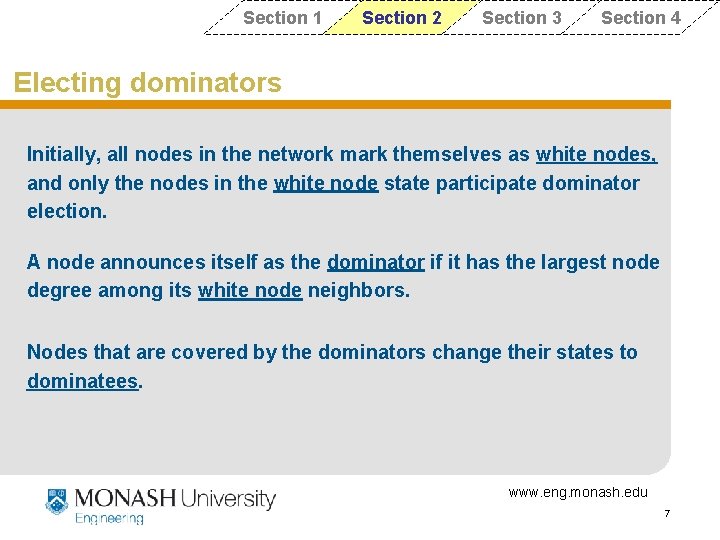
Section 1 Section 2 Section 3 Section 4 Electing dominators Initially, all nodes in the network mark themselves as white nodes, and only the nodes in the white node state participate dominator election. A node announces itself as the dominator if it has the largest node degree among its white node neighbors. Nodes that are covered by the dominators change their states to dominatees. www. eng. monash. edu 7
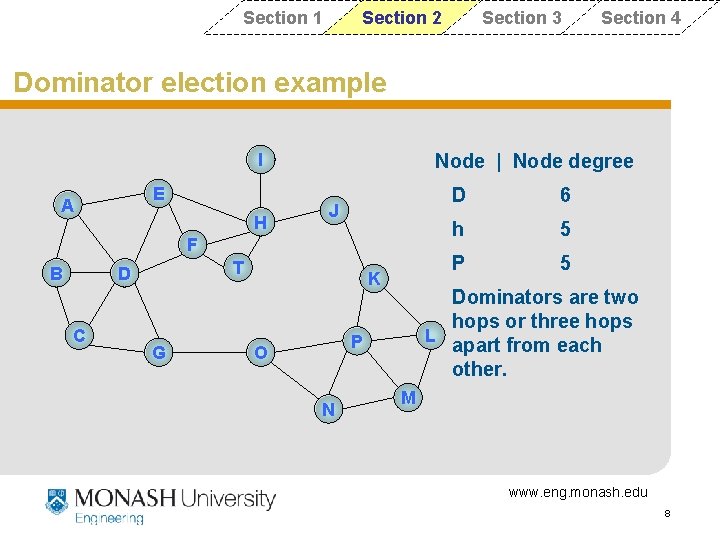
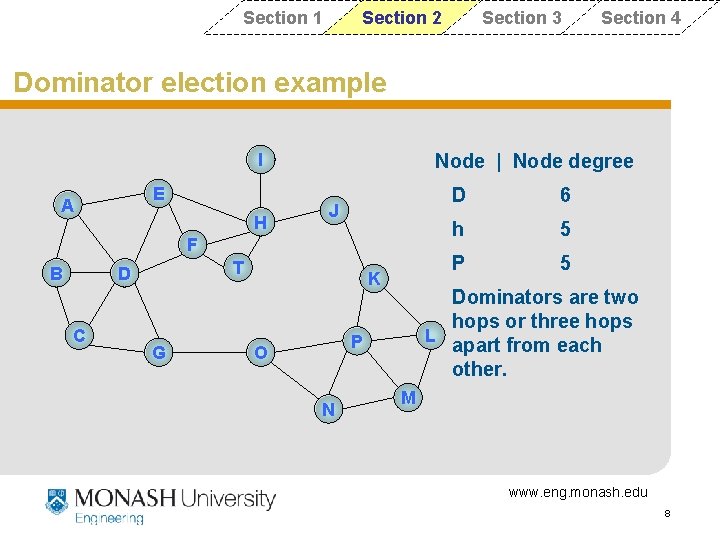
Section 1 Section 2 Section 3 Section 4 Dominator election example I E A H Node | Node degree J F B T D C G K N 6 h 5 P 5 Dominators are two hops or three hops L apart from each other. P O D M www. eng. monash. edu 8
Section 1 Section 2 Section 3 Section 4 Generating connectors Two types of connectors: • Active-Connector – selected by dominators • Passive-Connector – selected by dominators and active connectors. Passive-Connectors connect two-hop away dominators. Active-Connectors + Passive-connectors connect three-hop away dominators. www. eng. monash. edu 9
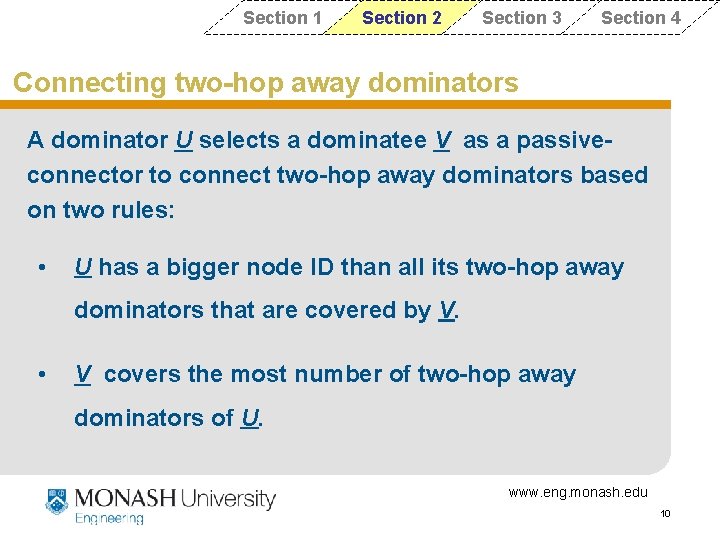
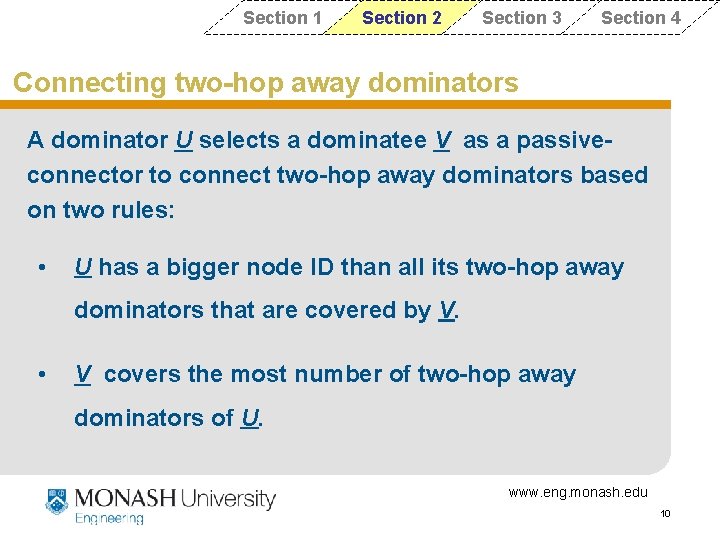
Section 1 Section 2 Section 3 Section 4 Connecting two-hop away dominators A dominator U selects a dominatee V as a passiveconnector to connect two-hop away dominators based on two rules: • U has a bigger node ID than all its two-hop away dominators that are covered by V. • V covers the most number of two-hop away dominators of U. www. eng. monash. edu 10
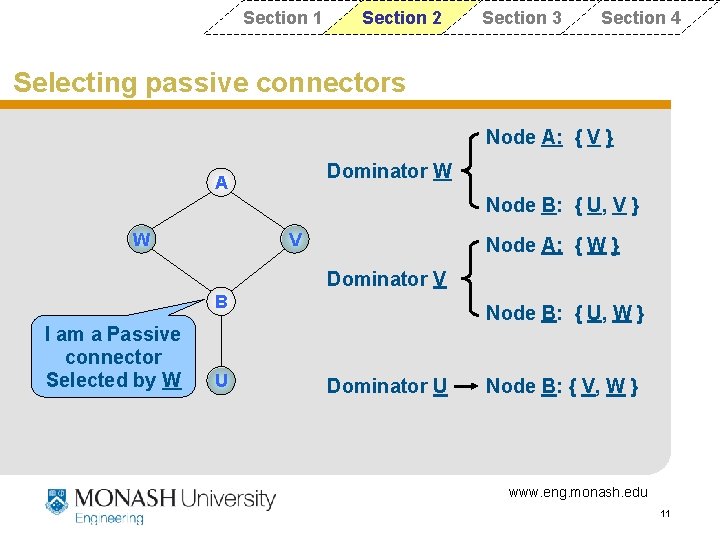
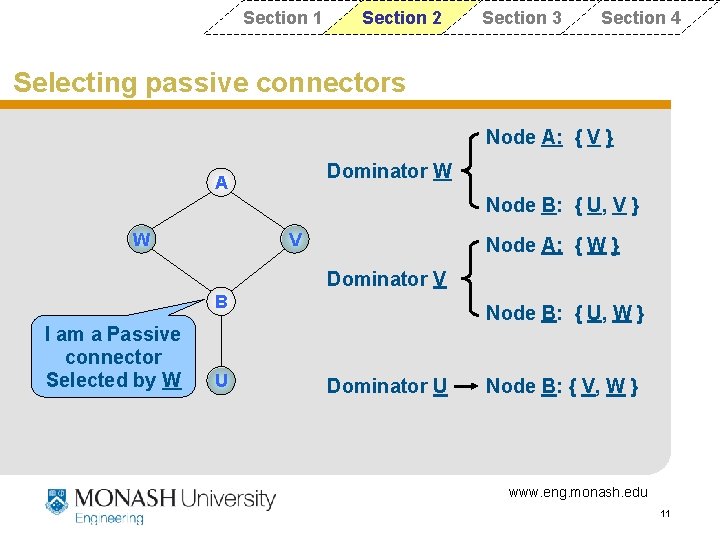
Section 1 Section 2 Section 3 Section 4 Selecting passive connectors Node A: { V } Dominator W A Node B: { U, V } W V Node A: { W } Dominator V B I am a Passive connector Selected by W U Node B: { U, W } Dominator U Node B: { V, W } www. eng. monash. edu 11
Section 1 Section 2 Section 3 Section 4 Connecting three-hop away dominators Two steps to connect three-hop away dominators: • A dominator U selects an active-connector V. • Active-connector V selects other passive connectors to connect three-hop away dominators. www. eng. monash. edu 12
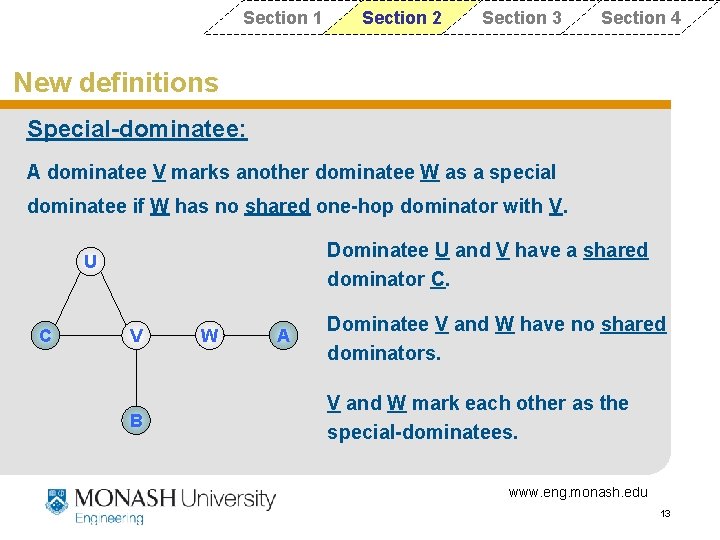
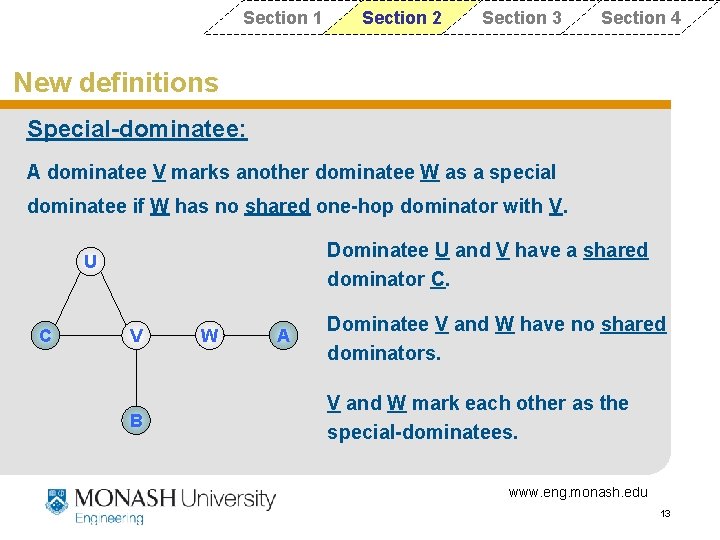
Section 1 Section 2 Section 3 Section 4 New definitions Special-dominatee: A dominatee V marks another dominatee W as a special dominatee if W has no shared one-hop dominator with V. Dominatee U and V have a shared dominator C. U C V B W A Dominatee V and W have no shared dominators. V and W mark each other as the special-dominatees. www. eng. monash. edu 13
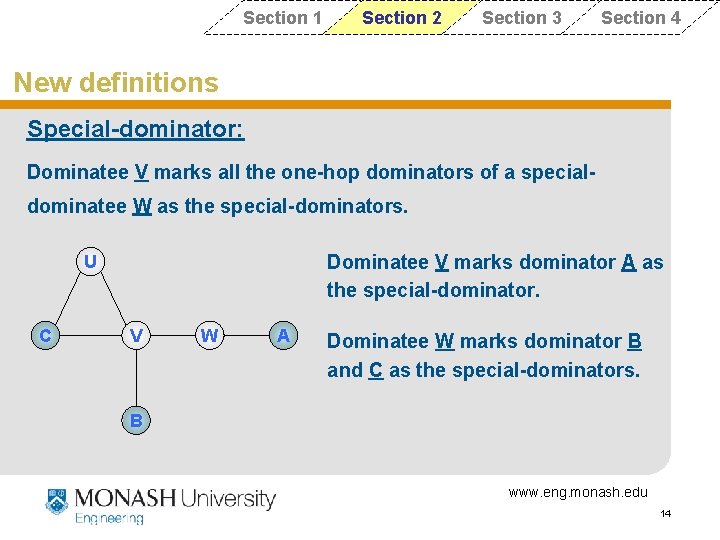
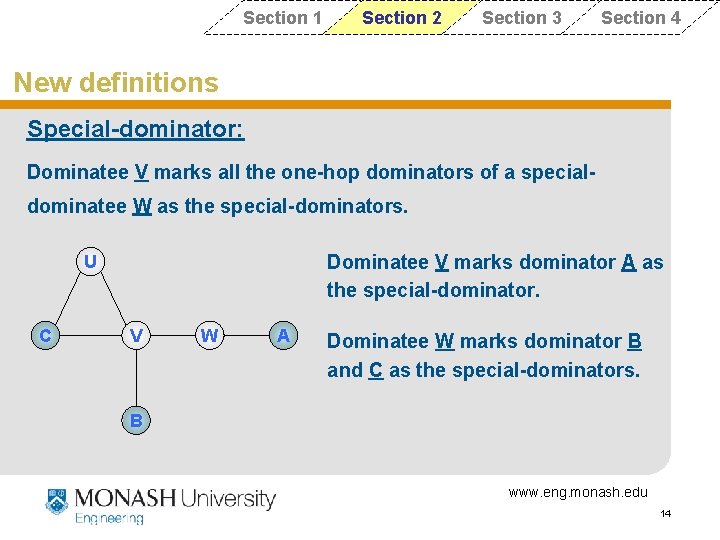
Section 1 Section 2 Section 3 Section 4 New definitions Special-dominator: Dominatee V marks all the one-hop dominators of a specialdominatee W as the special-dominators. Dominatee V marks dominator A as the special-dominator. U C V W A Dominatee W marks dominator B and C as the special-dominators. B www. eng. monash. edu 14
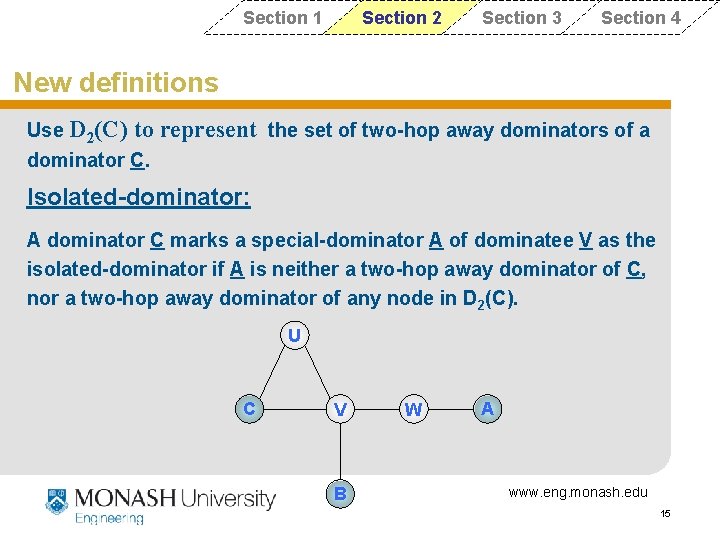
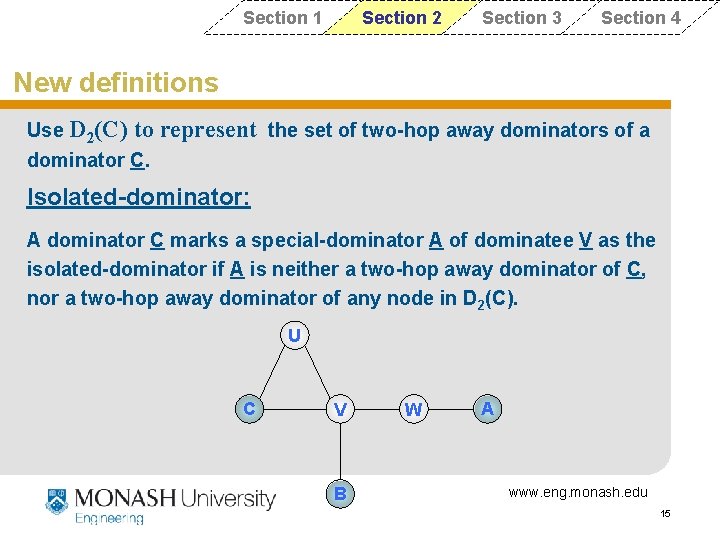
Section 1 Section 2 Section 3 Section 4 New definitions Use D 2(C) to represent the set of two-hop away dominators of a dominator C. Isolated-dominator: A dominator C marks a special-dominator A of dominatee V as the isolated-dominator if A is neither a two-hop away dominator of C, nor a two-hop away dominator of any node in D 2(C). U C V B W A www. eng. monash. edu 15
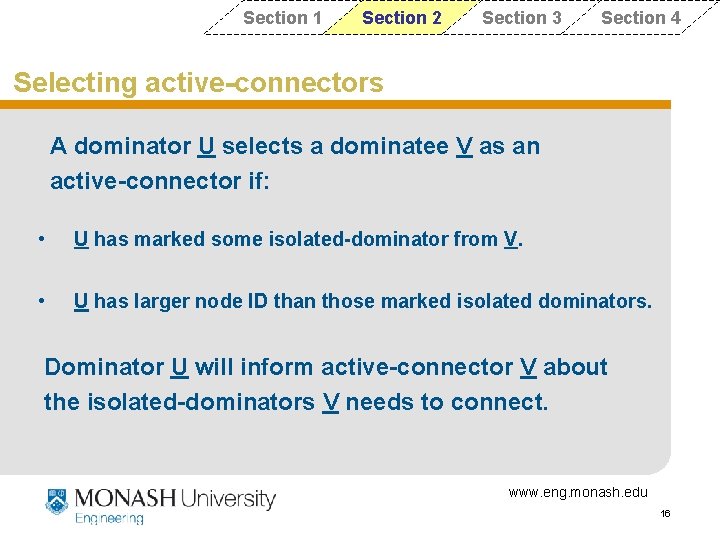
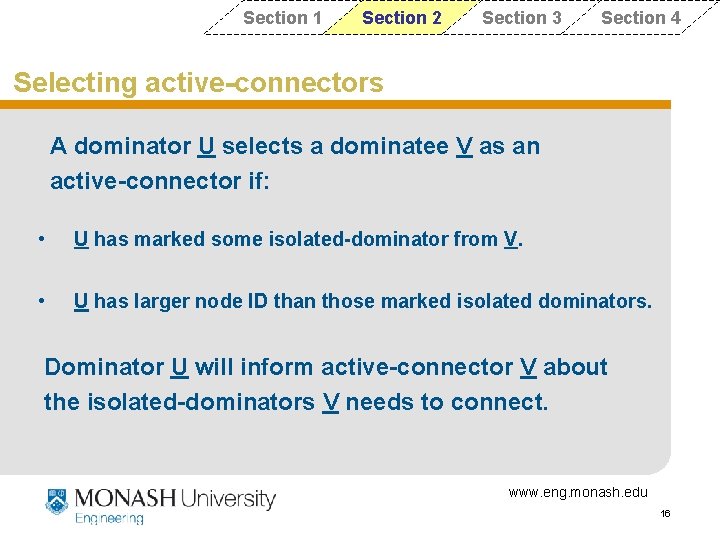
Section 1 Section 2 Section 3 Section 4 Selecting active-connectors A dominator U selects a dominatee V as an active-connector if: • U has marked some isolated-dominator from V. • U has larger node ID than those marked isolated dominators. Dominator U will inform active-connector V about the isolated-dominators V needs to connect. www. eng. monash. edu 16
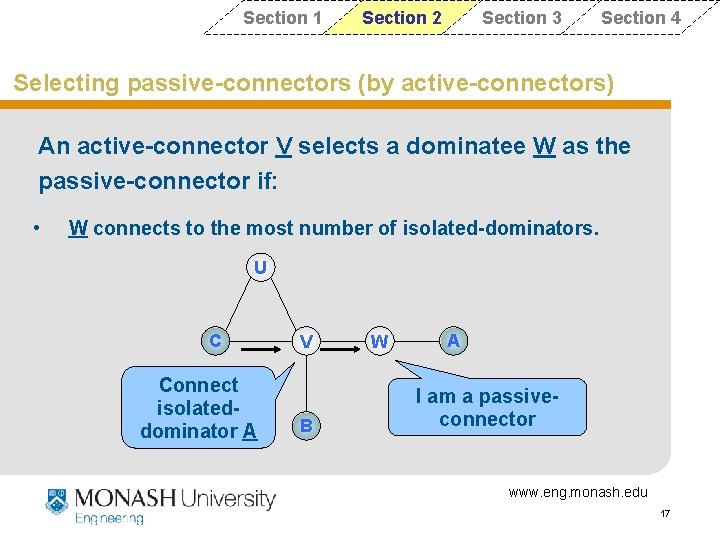
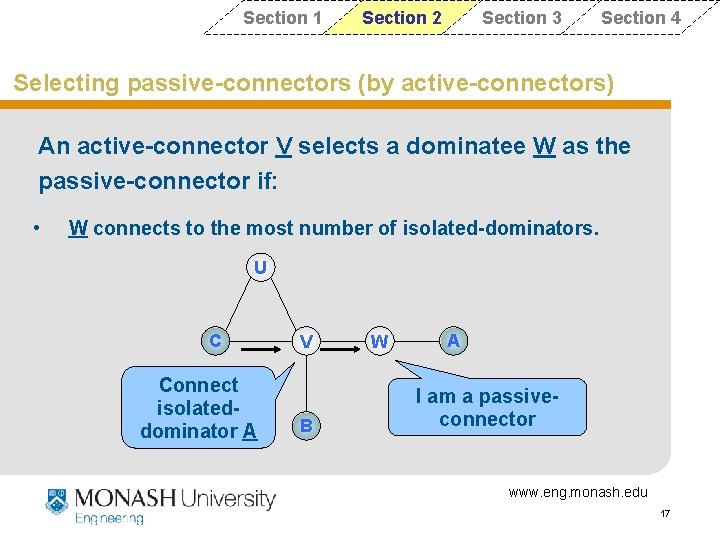
Section 1 Section 2 Section 3 Section 4 Selecting passive-connectors (by active-connectors) An active-connector V selects a dominatee W as the passive-connector if: • W connects to the most number of isolated-dominators. U C Connect isolateddominator A V B W A I am a passiveconnector www. eng. monash. edu 17
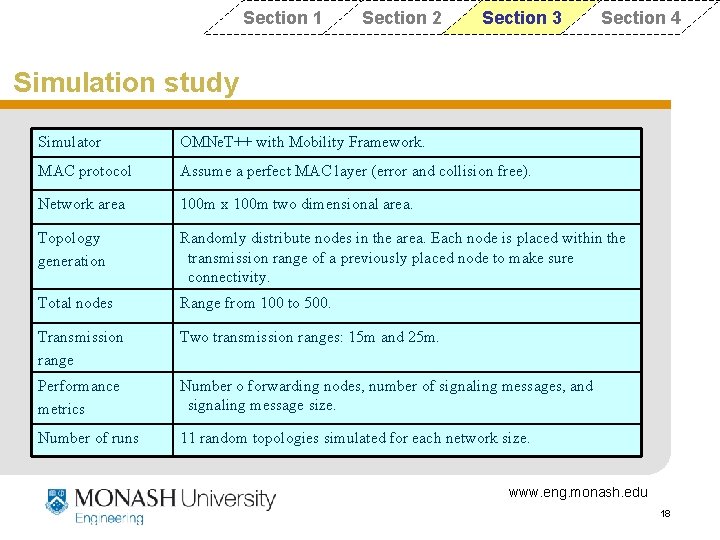
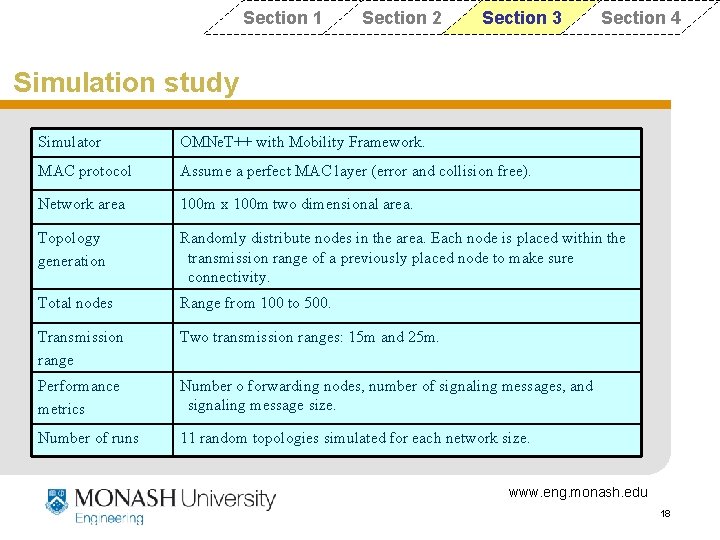
Section 1 Section 2 Section 3 Section 4 Simulation study Simulator OMNe. T++ with Mobility Framework. MAC protocol Assume a perfect MAC layer (error and collision free). Network area 100 m x 100 m two dimensional area. Topology generation Randomly distribute nodes in the area. Each node is placed within the transmission range of a previously placed node to make sure connectivity. Total nodes Range from 100 to 500. Transmission range Two transmission ranges: 15 m and 25 m. Performance metrics Number o forwarding nodes, number of signaling messages, and signaling message size. Number of runs 11 random topologies simulated for each network size. www. eng. monash. edu 18
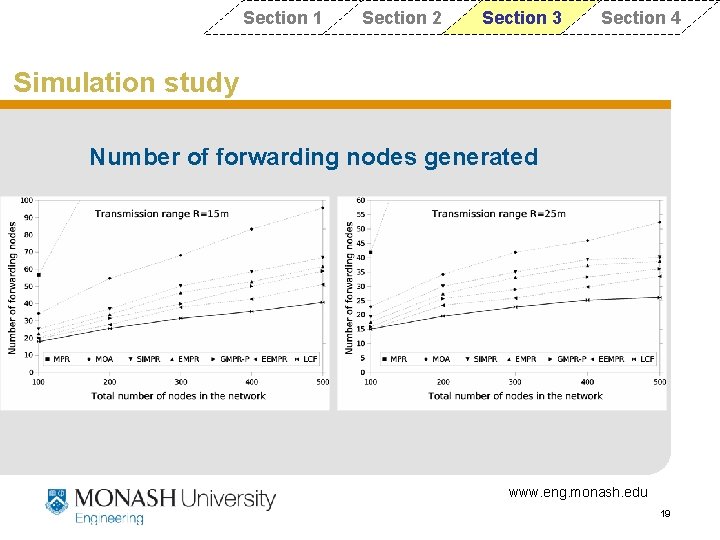
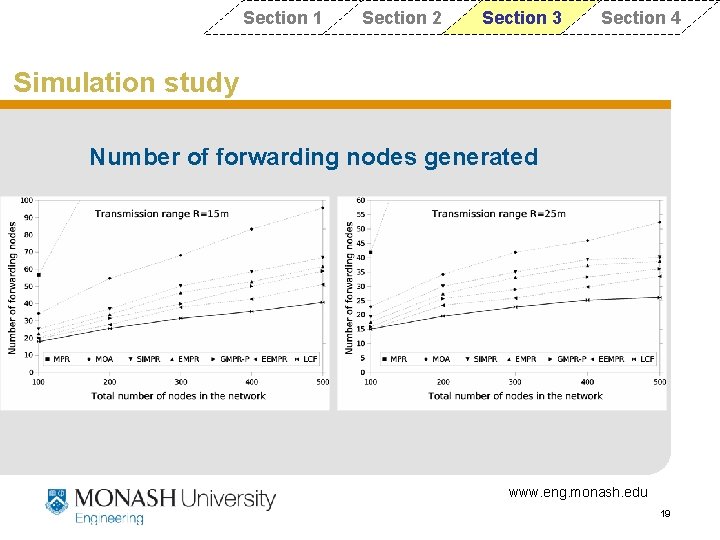
Section 1 Section 2 Section 3 Section 4 Simulation study Number of forwarding nodes generated www. eng. monash. edu 19
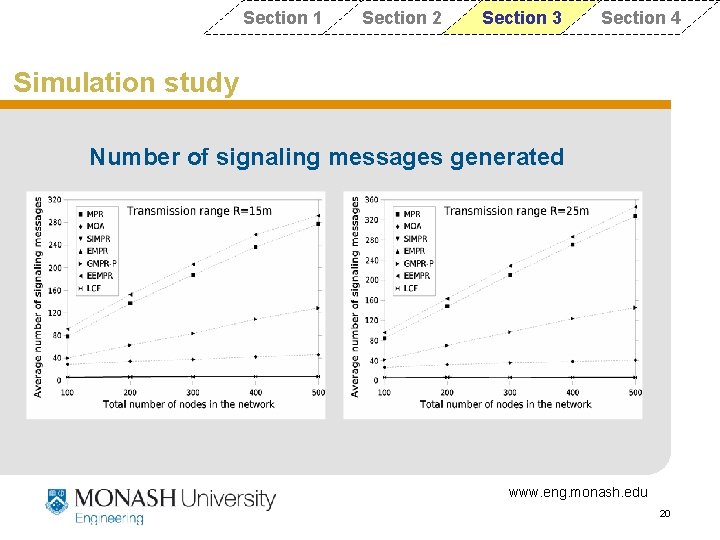
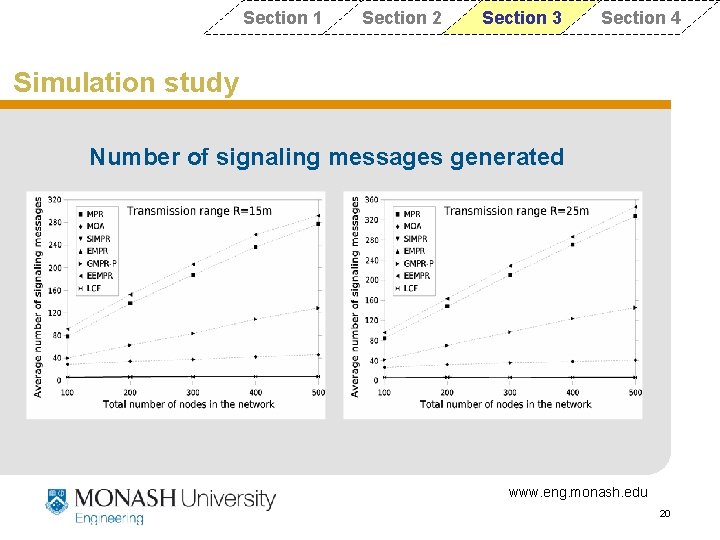
Section 1 Section 2 Section 3 Section 4 Simulation study Number of signaling messages generated www. eng. monash. edu 20
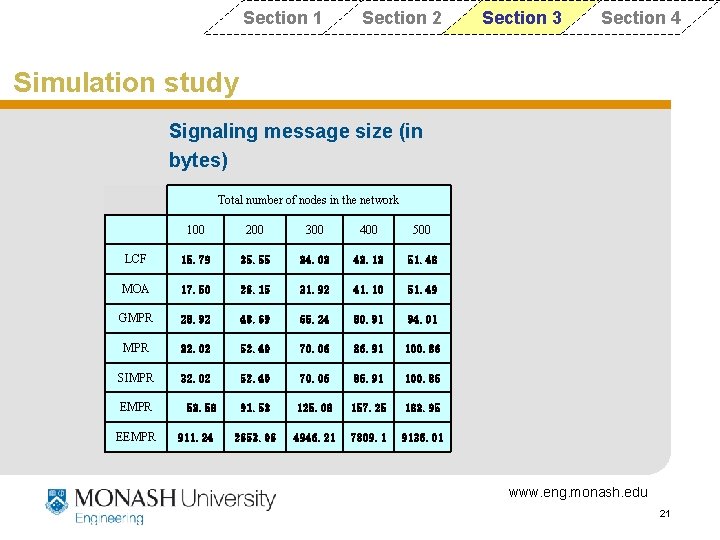
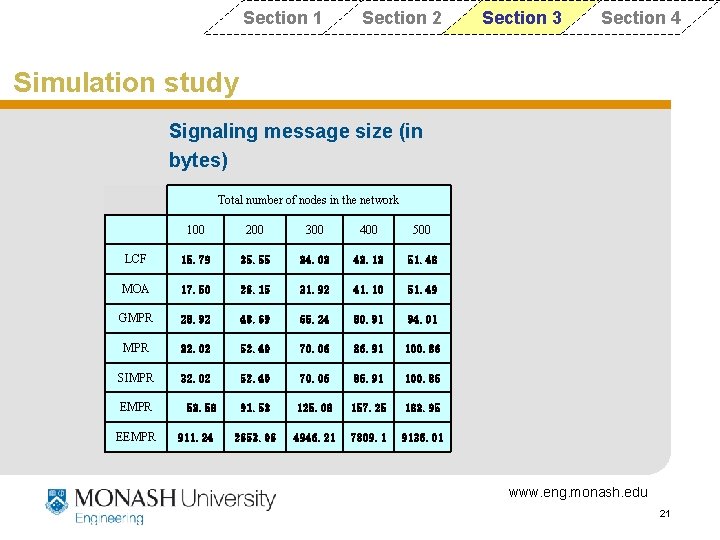
Section 1 Section 2 Section 3 Section 4 Simulation study Signaling message size (in bytes) R=15 m Total number of nodes in the network 100 200 300 400 500 LCF 15. 79 25. 55 34. 03 43. 13 51. 48 MOA 17. 50 26. 15 31. 92 41. 10 51. 49 GMPR 28. 92 48. 69 65. 24 80. 91 94. 01 MPR 32. 02 52. 40 70. 06 86. 91 100. 86 SIMPR 32. 02 52. 40 70. 06 86. 91 100. 86 91. 53 125. 08 157. 25 183. 95 2653. 06 4946. 21 7809. 1 9136. 01 EMPR EEMPR 53. 58 911. 24 www. eng. monash. edu 21
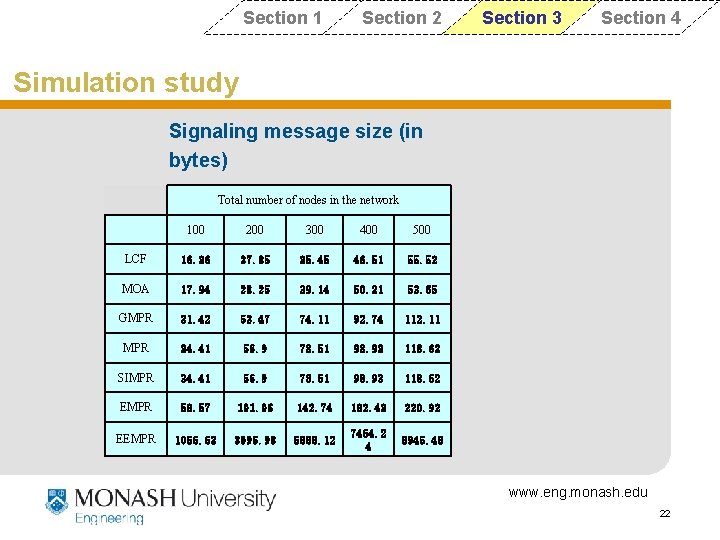
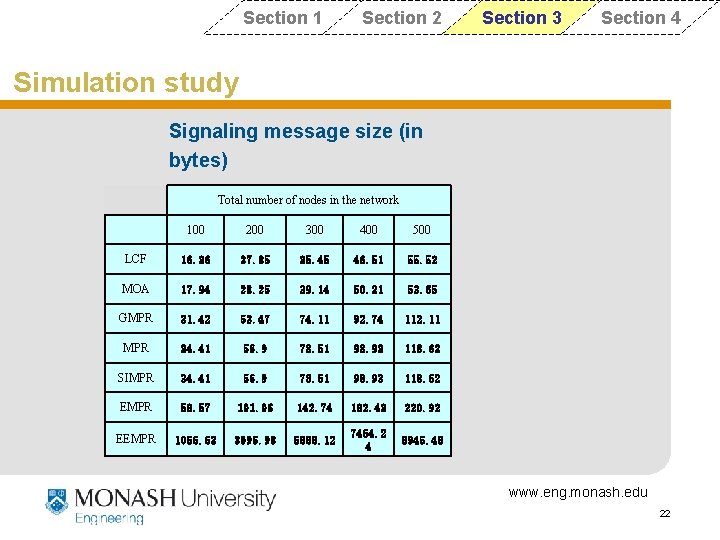
Section 1 Section 2 Section 3 Section 4 Simulation study Signaling message size (in bytes) R=25 m Total number of nodes in the network 100 200 300 400 500 LCF 16. 36 27. 85 35. 45 46. 51 55. 52 MOA 17. 94 28. 25 39. 14 50. 21 53. 65 GMPR 31. 42 52. 47 74. 11 92. 74 112. 11 MPR 34. 41 56. 9 78. 51 98. 93 118. 62 SIMPR 34. 41 56. 9 78. 51 98. 93 118. 62 EMPR 58. 57 101. 06 142. 74 182. 43 220. 92 EEMPR 1056. 63 3096. 98 5888. 12 7464. 2 4 8945. 48 www. eng. monash. edu 22
Section 1 Section 2 Section 3 Section 4 Conclusion and future work We have proposed a Low-Cost Flooding (LCF) algorithm for wireless senor networks. The algorithm aims to minimize the redundant retransmissions in the network by generating a Connected Dominating Set (CDS). Future work: • Design efficient routing protocols for sensor networks. • Implement a real world sensor network test bed. www. eng. monash. edu 23

Thank you for your attention! www. eng. monash. edu 24
Section 1 Section 2 Section 3 Section 4 Flooding protocol designing considerations • Scalability — flooding algorithms for WSNs need to be distributed and depends on localized information. • Simplicity — flooding algorithms need to be simple in both computation and communication. • Efficiency — flooding algorithms can dramatically reduce unnecessary redundant transmissions and save energy. www. eng. monash. edu 25