A holistic view on information security training and

- Slides: 8
A holistic view on information security training and education Margaretha Eriksson Ph. D. Student DSV / SU margaretha. eriksson@ieee. org Ce. TUSS Dec 2005 Margaretha Eriksson
DSV / SU and Sec. Laboratory for research and education in Computer Security and Security Informatics. Professor Louise Yngström Mission • to advance theory and practice in computer and information security, for the benefit of society. Holistic approach • To investigate problems of security from technical, social, managerial, economic, and legal perspectives • In computer and systems sciences context, utilizing disciplines, such as sociology, pedagogy, jurisprudence, economics, etc. Some Research Areas: • Education and Awareness in Security (alternative methods for teching and learning security, . . . • Management of Information Security (to understand, explain, control, predict. . . ) Ce. TUSS Dec 2005 Margaretha Eriksson
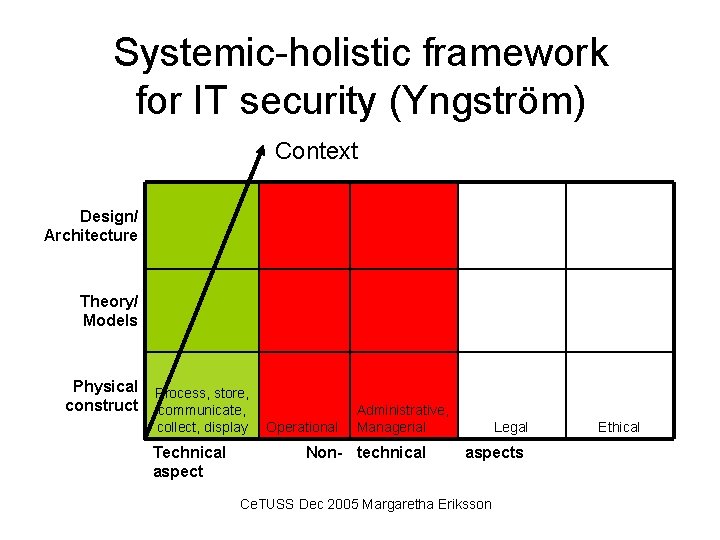
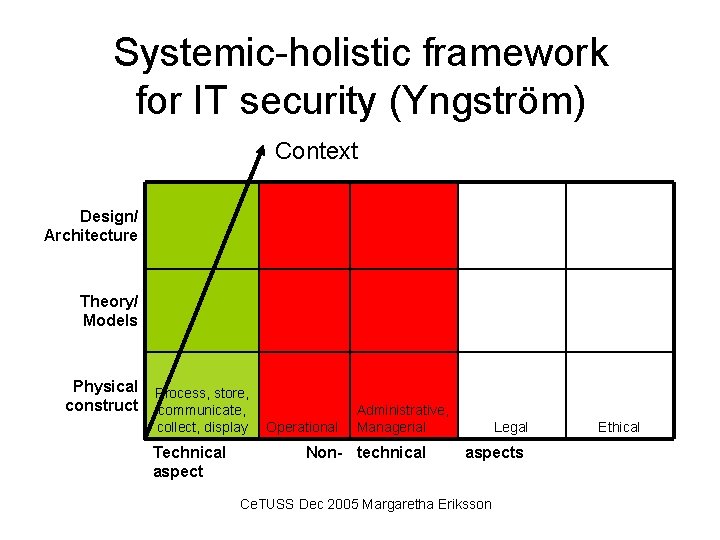
Systemic-holistic framework for IT security (Yngström) Context Design/ Architecture Theory/ Models Physical construct Process, store, communicate, collect, display Technical aspect Operational Administrative, Managerial Non- technical Legal aspects Ce. TUSS Dec 2005 Margaretha Eriksson Ethical
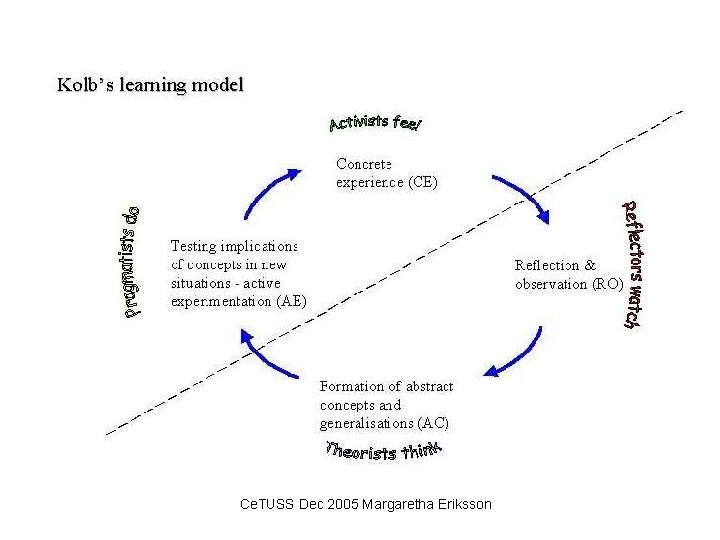
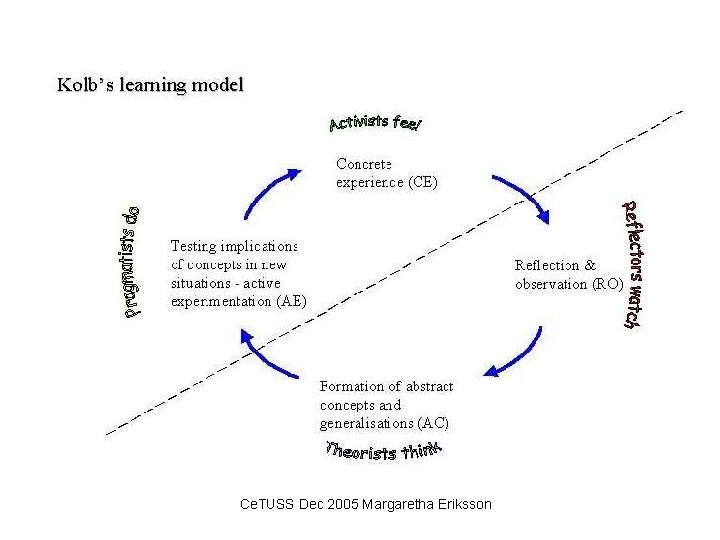
Ce. TUSS Dec 2005 Margaretha Eriksson
The Missing Human IT security in a holistic manner - in real life. . . • Attend lectures, read the literature and scan Internet • Play with IT security in a safe sandbox • Write reports on findings on technical issues • But. . . • Where are the users of the system? • The system limits is excluding the human users! Ce. TUSS Dec 2005 Margaretha Eriksson

More than technology. . . Ce. TUSS Dec 2005 Margaretha Eriksson
Cross-over areas • Steel milling vs Pulp and Paper industry - similar format, different density of material • Content Management vs Configuration Management - similar structuring, html document vs products • SW Object Orientation vs Structured writing (IMAP® method) - similar structuring method, source code vs text chunks Ce. TUSS Dec 2005 Margaretha Eriksson
A working method. . . • TÖI/SU • IT for translators course – designing and teaching • Computer based Translation tools to non-engineers • Process and work-flow related • Life-cycle approach of the translation Ce. TUSS Dec 2005 Margaretha Eriksson