A Case for Collaborative Identity Management in a
A Case for Collaborative Identity Management in a Complex Decentralized Environment Andrea Beesing Assistant Director, IT Security and David Yeh Assistant Vice President and University Registrar 1
Shared Secrets, Shared Vision, Shared Governance, Shared Technologies • Life-cycle: A Shared Vision • Policies and practices • Reusable and scalable infrastructure and tools • Governance Needs Everyone – not just an IT concern 2
A Life Cycle Point of View • High school to Undergraduate to Alumni to Graduate to Employee and Friends • > 100, 000 applicants • > 350, 000 alumni, friends, guests! • Around-the-world sites – Ithaca, NY; New York City, and Washington, D. C. Doha, Qatar, Singapore, Beijing; Paris, France; Rome, Italy; Seville, Spain; London, England; Dublin, Ireland; and Geneva, Switzerland Geneva, NY, and others. • Around-the-world connecting points – faculty collaborators; students, employees, alumni, parents 3

Simplify connecting people in our community • Provide access for the right people to the right information, anytime, any place • Process entry and access to information services, securely and efficiently • Connecting from the very beginning 4
Link people and services – Anytime, Anywhere, Securely • Adopting commonly developed technology tools – Shibboleth, In. Common – Grouper, Signet, Federated Id. M • Inter-institution collaboration – faculty research, document transmission, international exchange and study abroad • Business partners – Inter-Library Services (ILIAD), National Student Clearinghouse, Law School Admissions Council (LSAC), Veterinary Medical College Application Service (VMCAS), American Medical School Application Service (AMCAS), College. Board, Educational Testing Service, and others 5
Improve management of risk • Provide appropriate level of access into transactional systems • Facilities and other resource access • Protect university and college reputation 6
Reusable and Extendable Tools • Provision identity from the beginning • Common policies and procedures • Reusing best practices and technologies 7
Use Case: Student Identity Life Cycle 8
Identity Management goals for student services • “Instant” onboarding – Establish applicant/student relationship with Cornell as early as possible – No lines on day 1 for students • Replace paper-based, manual processes with online self-service options • Improve user experience when accessing services – Across Cornell administrative units and colleges – Across institutional boundaries • Protect security and privacy 9
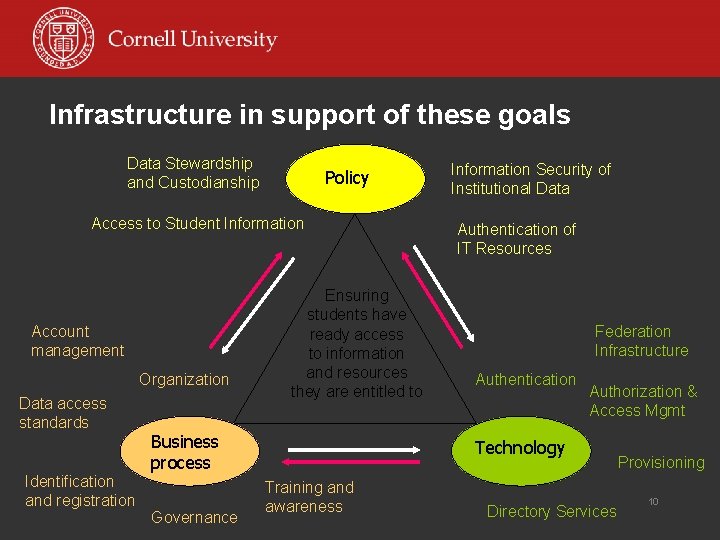
Infrastructure in support of these goals Data Stewardship and Custodianship Policy Access to Student Information Account management Organization Data access standards Identification and registration Ensuring students have ready access to information and resources they are entitled to Business process Governance Information Security of Institutional Data Authentication of IT Resources Federation Infrastructure Authentication Authorization & Access Mgmt Technology Training and awareness Directory Services Provisioning 10
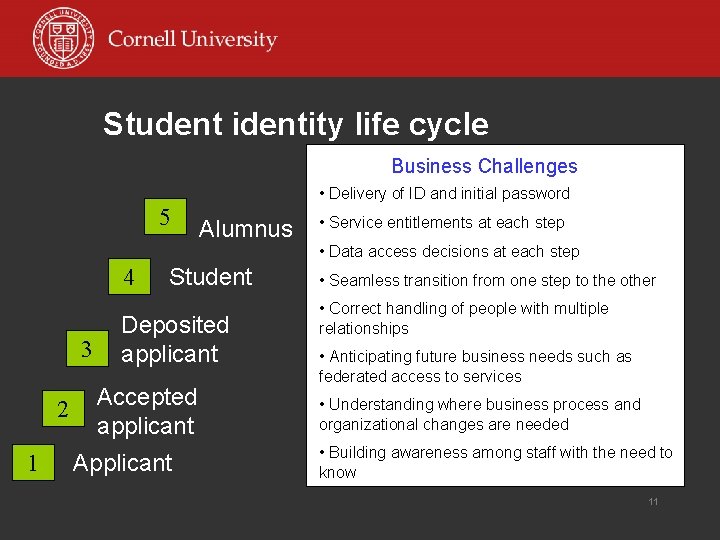
Student identity life cycle Business Challenges • Delivery of ID and initial password 5 4 3 2 1 Alumnus Student Deposited applicant Accepted applicant Applicant • Service entitlements at each step • Data access decisions at each step • Seamless transition from one step to the other • Correct handling of people with multiple relationships • Anticipating future business needs such as federated access to services • Understanding where business process and organizational changes are needed • Building awareness among staff with the need to know 11
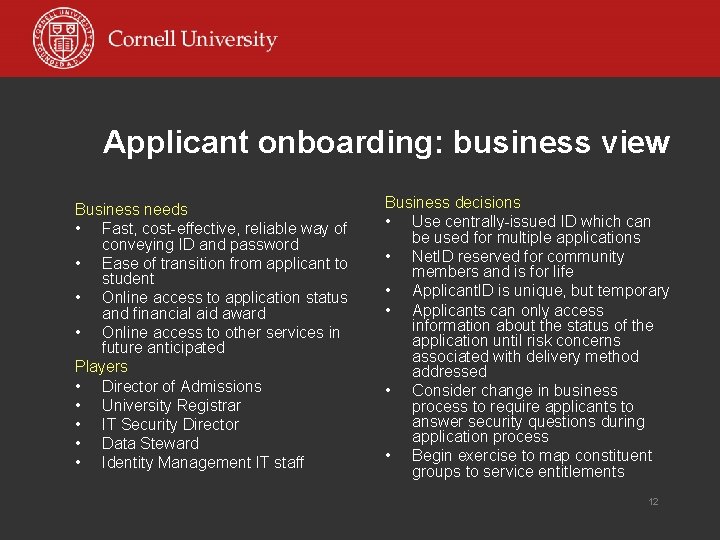
Applicant onboarding: business view Business needs • Fast, cost-effective, reliable way of conveying ID and password • Ease of transition from applicant to student • Online access to application status and financial aid award • Online access to other services in future anticipated Players • Director of Admissions • University Registrar • IT Security Director • Data Steward • Identity Management IT staff Business decisions • Use centrally-issued ID which can be used for multiple applications • Net. ID reserved for community members and is for life • Applicant. ID is unique, but temporary • Applicants can only access information about the status of the application until risk concerns associated with delivery method addressed • Consider change in business process to require applicants to answer security questions during application process • Begin exercise to map constituent groups to service entitlements 12
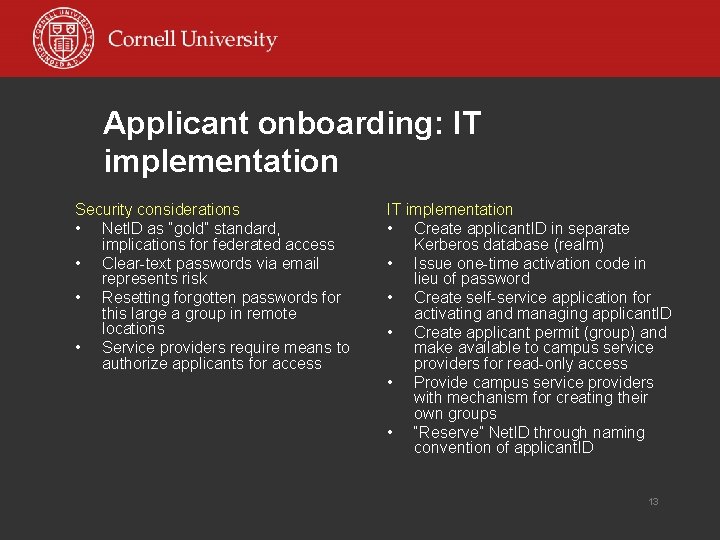
Applicant onboarding: IT implementation Security considerations • Net. ID as “gold” standard, implications for federated access • Clear-text passwords via email represents risk • Resetting forgotten passwords for this large a group in remote locations • Service providers require means to authorize applicants for access IT implementation • Create applicant. ID in separate Kerberos database (realm) • Issue one-time activation code in lieu of password • Create self-service application for activating and managing applicant. ID • Create applicant permit (group) and make available to campus service providers for read-only access • Provide campus service providers with mechanism for creating their own groups • “Reserve” Net. ID through naming convention of applicant. ID 13
Student onboarding: business view Business needs • Student gets Net. ID as soon as deposit paid and has access to student services • Student must be aware of IT policies and their responsibilities before accessing services Players • College student services staff • University Registrar’s staff • IT Security Director • IT Policy Director • Faculty Advisory Group • Identity Management IT staff Business decisions • Require each student to take an online tutorial and quiz to introduce policies and network citizenship • Deliver Net. ID in US mail until risk concerns adequately addressed 14
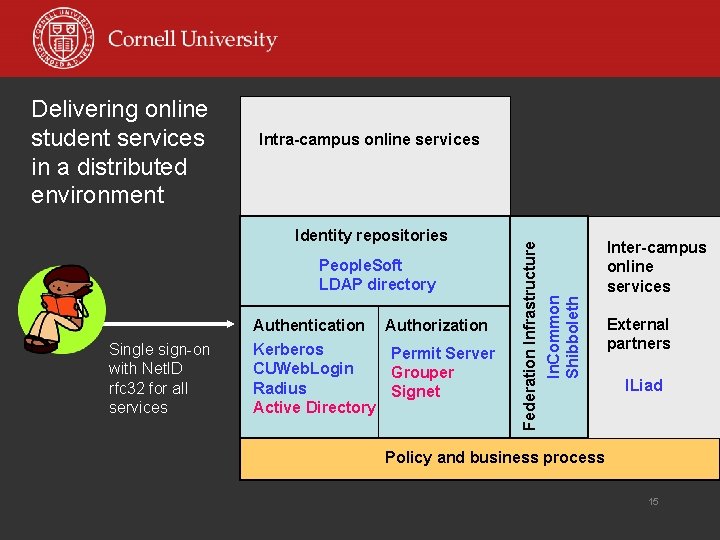
Intra-campus online services Identity repositories People. Soft LDAP directory Single sign-on with Net. ID rfc 32 for all services Authentication Kerberos CUWeb. Login Radius Active Directory Authorization Permit Server Grouper Signet Federation Infrastructure In. Common Shibboleth Delivering online student services in a distributed environment Inter-campus online services External partners ILiad Policy and business process 15
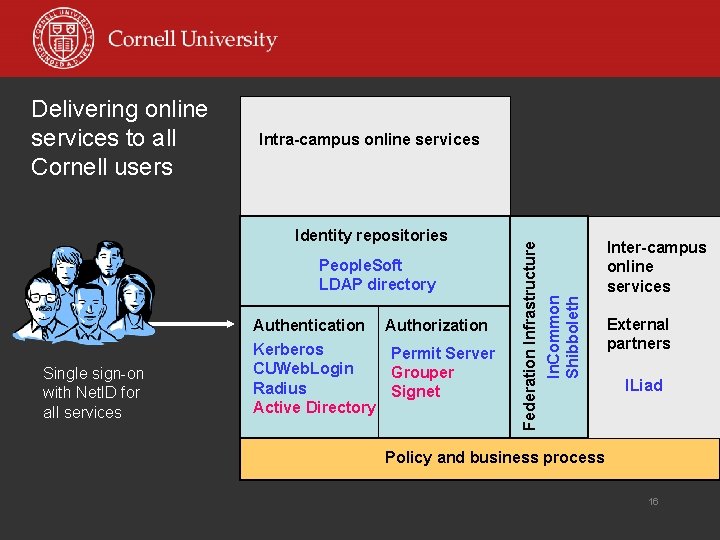
Intra-campus online services Identity repositories People. Soft LDAP directory Single sign-on with Net. ID for all services Authentication Kerberos CUWeb. Login Radius Active Directory Authorization Permit Server Grouper Signet Federation Infrastructure In. Common Shibboleth Delivering online services to all Cornell users Inter-campus online services External partners ILiad Policy and business process 16
- Slides: 16