A Brief History of Distributed Denial of Service
A Brief History of Distributed Denial of Service Attacks Uniforum Chicago August 22, 2000 Viki Navratilova Security Architect, Blue. Meteor, Inc.
Tonight’s Talk • • What is DDo. S? Famous DDo. S incidents Brief History of DDo. S tools What’s new in DDo. S tools Where to get more info on DDo. S tools <break> How to keep DDo. S from getting you down
Denial of Service (DOS) • An attack to suspend • Network DOS – the availability of a modern times service • Prevent a Network • Early DOS – smashing based service from computer with sledge doing its job hammer • Can be as easy as pulling the network plug
What is DDo. S? • Distributed Denial of Service • Many “zombie” computers ganging up on one computer, directed by one “master”, which is controlled by the attacker
The Week of Famous DDo. S Attacks • February 7 -11 2000 • CNN, Yahoo, E-Bay, Datek taken down for several hours at a time due to traffic flooding • Underadministrated computers at California college used as the slave attack computers • Trinoo, Tribal Flood Network, TFN 2 K, and Stacheldraht suspected tools used in attacks
Early DDo. S Tools (c. 1990? – 1997) • Simple 1 -tier attacks – computer with bigger bandwidth wins, kicks loser off modem/irc channel • Ping flood • SYN flood • UDP flood • Smurf Attack – early 2 -tier attack • Attacker machine imitates victim, gets everyone to flood real victim • Ping flood
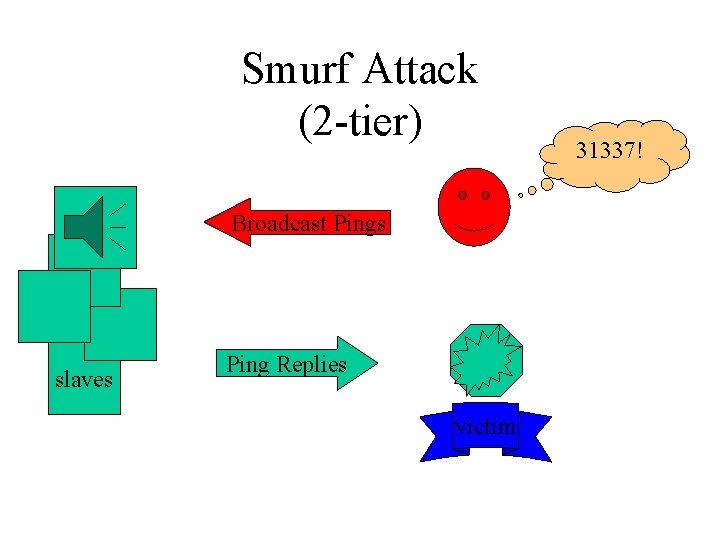
Smurf Attack (2 -tier) Broadcast Pings slaves Ping Replies victim 31337!
Modern DDo. S Tools • Once sites blocked broadcast pings, attackers found new ways to accomplish same things • DDo. S tools gave new way to communicate across networks to slave attack computers • Attacker has to infiltrate several slave computers with DDo. S slave client • Master client sometimes found on ISP’s name server – unlikely to be taken off network
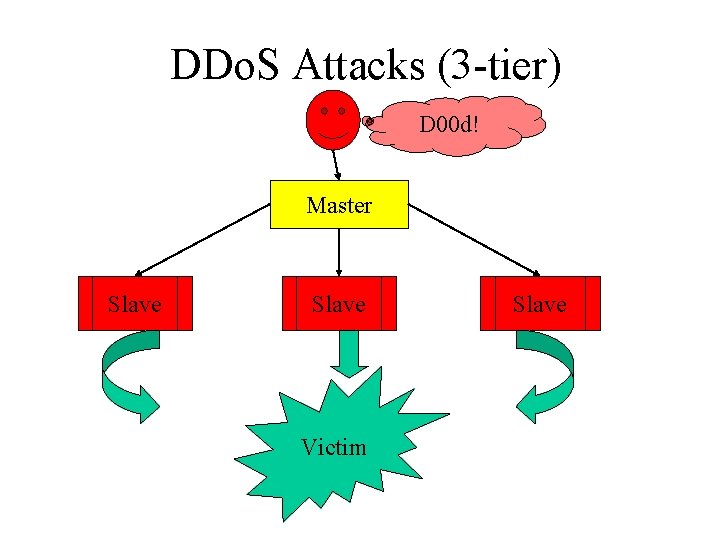
DDo. S Attacks (3 -tier) D 00 d! Master Slave Victim Slave
Why DDo. S Tools Suck for Your Network • Hard to Trace to original culprit • Difficult to cut off flow of traffic attacking you because it’s coming from everywhere • Difficult to catch pre-attack communications between master and slave machines
Trinoo – First Publicly Available DDo. S Tool (c. 1997) • Attacker, Master, Slave Communications via unencrypted UDP • Easy to detect communications and passwords • Attack Method : UDP Flood • Solaris & Linux machines
Tribe Flood Network (TFN) (c. 1998) • Attacker & Master communicate via unencrypted TCP, UDP, SSH, ICMP, telnet • No password required to run commands • Commands are sent as pre-determined 16 -bit binary numbers • Master & Slaves talk ICMP • DOS Attacks available : ICMP, SYN, UDP, &Smurf-style Floods • Linux & Solaris
TFN 2 K (1999) • Builds on TFN • Decoy packets & other measures make traffic difficult to identify & filter • Fakes source address of communications • New attacks include malformed packet floods – greater devastation in fewer packets • Available for Unix & NT Systems
Stacheldraht “Barbed Wire” Fine German Engineering (late 1999) • Master – Slave communications require passwords • telnet-like encrypted connections over TCP and ICMP • Only way to prevent communications is to block all ICMP traffic (undesirable) • Ability to upgrade master & slave software via rcp – increases client functionality • Several DOS attacks like TFN • Solaris & Linux
What’s New in DDo. S Tools (since February 2000) • Shaft (Nov 1999) – modeled after Trinoo – – Attacker-master : password : tcp / master-zombie : udp Can switch master servers and ports on the fly Uses ticket system to match zombies with their masters Keeps zombie packet statistics • Mstream (April 2000) – Still in development – Attacker to master commands sent in one packet over unencrypted TCP – password protected – Master and zombies talk over udp – All logged in users (attackers) are notified of access attempts
Where to Find More Info on DDo. S Tools • Dave Dittrich’s White Papers http: //staff. washington. edu/dittrich/misc/ddos • Packetstorm’s Distributed Attack Tools http: //packetstorm. security. com/distributed • CERT Coordination Center http: //www. cert. org
Break
How to Keep DDo. S Tools from Getting You Down • Pay attention to your machines! • Egress filter your network, i. e. make sure whatever comes out of your network only has source addresses that belong to you • Ingress filter – confirm that packets coming to you have source addresses that aren’t on your inside network • Use tcpdump on Solaris or Linux to capture logs, and report incident to law enforcement (NIPC) tcpdump –i interface –s 1500 –w capture_file snoop –d interface –o capture_file –s 1500
Cisco Router Configuration Options • Ip verify unicast reverse-path : confirms packets that arrive should be going back on same interface, otherwise drops • Rate limit ICMP and SYN packets • Filter non-routable address space: Interface xy ip access-group 101 in access-list 101 deny ip 10. 0 0. 255 any access-list 101 deny ip 192. 168. 0. 0. 255 any access-list 101 deny ip 172. 16. 0. 0 0. 15. 255 any access-list 101 permit ip any
Tools to Help Detect DDo. S Tools • NIPC Tools – locates installations on hard drive by scanning file contents http: //www. nipc. gov • Zombie Zapper – puts Trinoo, TFN, Stacheldraht, and Shaft zombies “to sleep” when flooding http: //razor. bindview. com • Remote Intrusion Detector (RID) : Locates Trinoo, Stacheldraht, TFN on network http: //www. theorygroup. com/Software/RID/
Q&A
Thank you
- Slides: 22