9 Security Issues in EC mailto ckfarnmgt ncu

- Slides: 53
9 Security Issues in EC 中央大學. 資訊管理系 范錚強 mailto: ckfarn@mgt. ncu. edu. tw http: //www. mgt. ncu. edu. tw/~ckfarn 2011. 05 中央大學。范錚強 1
What Is EC Security? Computer security refers to the protection of data, networks, computer programs, computer power and other elements of computerized information systems 中央大學。范錚強 2
What kinds of security questions arise? From the user’s perspective: How can the user be sure that the Web server is owned and operated by a legitimate company? How does the user know that the Web page and form do not contain some malicious or dangerous code or content? How does the user know that the owner of the Web site will not distribute the information the user provides to some other party? 中央大學。范錚強 6
What kinds of security questions arise? From the company’s perspective: How does the company know the user will not attempt to break into the Web server or alter the pages and content at the site? How does the company know that the user will not try to disrupt the server so that it is not available to others? 中央大學。范錚強 7
What kinds of security questions arise? From both parties’ perspectives: How do both parties know that the network connection is free from eavesdropping by a third party “listening” on the line? How do they know that the information sent back-and-forth between the server and the user’s browser has not been altered? 中央大學。范錚強 8
Basic Security Terminology business continuity plan A plan that keeps the business running after a disaster occurs. Each function in the business should have a valid recovery capability plan cybercrime Intentional crimes carried out on the Internet exposure The estimated cost, loss, or damage that can result if a threat exploits a vulnerability fraud Any business activity that uses deceitful practices or devices to deprive another of property or other rights 中央大學。范錚強 9
Basic Security Terminology 2 malware (malicious software) A generic term for malicious software Phishing A crimeware technique to steal the identity of a target company to get the identities of its customers Risk The probability that a vulnerability will be known and used social engineering A type of nontechnical attack that uses some ruse to trick users into revealing information or performing an action that compromises a computer or network 中央大學。范錚強 10
Basic Security Terminology 3 Spam The electronic equivalent of junk mail Vulnerability Weakness in software or other mechanism that threatens the confidentiality, integrity, or availability of an asset (recall the CIA model). It can be directly used by a hacker to gain access to a system or network Zombies Computers infected with malware that are under the control of a spammer, hacker, or other criminal 中央大學。范錚強 11
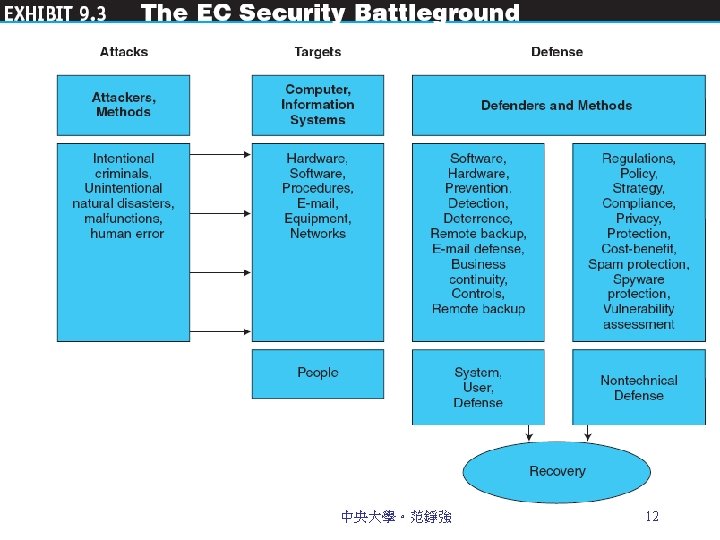
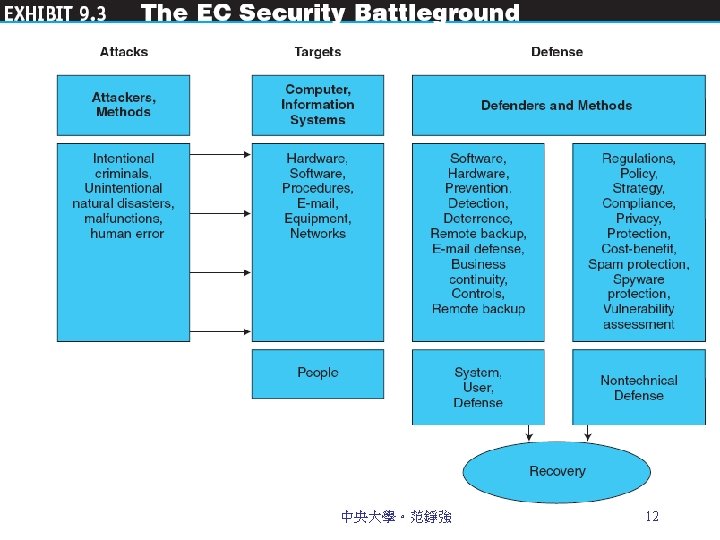
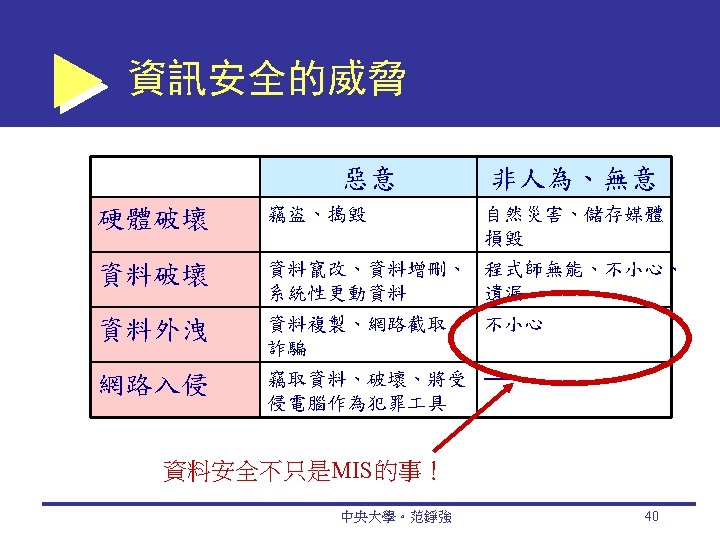
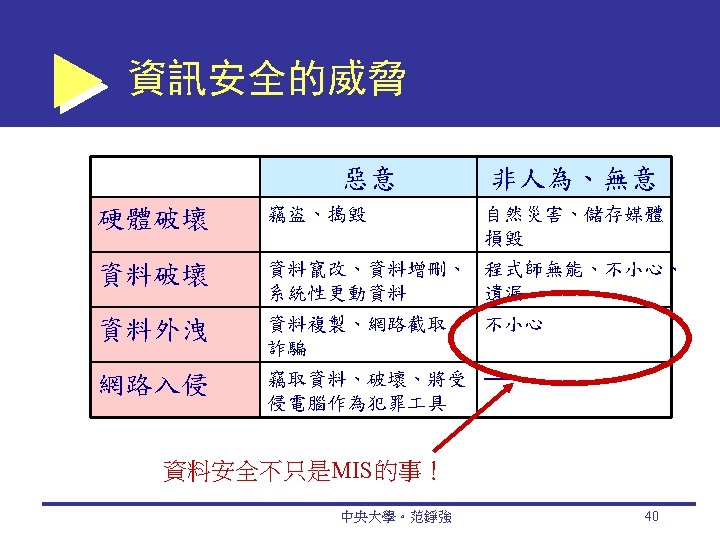
Threats and Attacks: Unintentional and Intentional Unintentional Threats Human error (標錯價) Environmental hazards (天然災害) Malfunctions in the computer system Intentional Attacks and Crimes 中央大學。范錚強 13
Criminals and Social Engineering cybercriminal A person who intentionally carries out crimes over the Internet. hacker Someone who gains unauthorized access to a computer system. cracker A malicious hacker, such as Maxwell in the opening case, who may represent a serious problem for a corporation. Vulnerable Areas Are Being Attacked 中央大學。范錚強 14
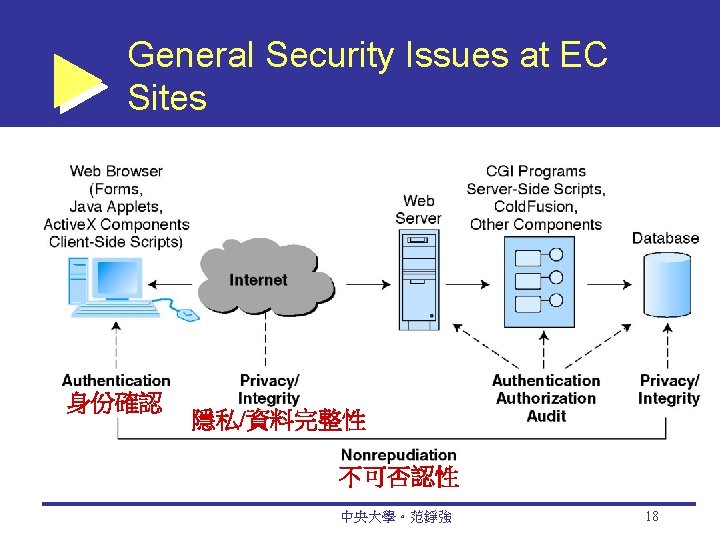
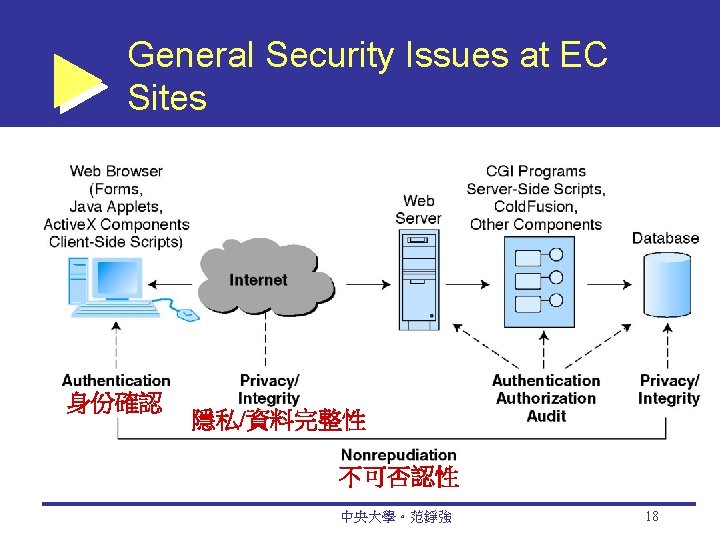
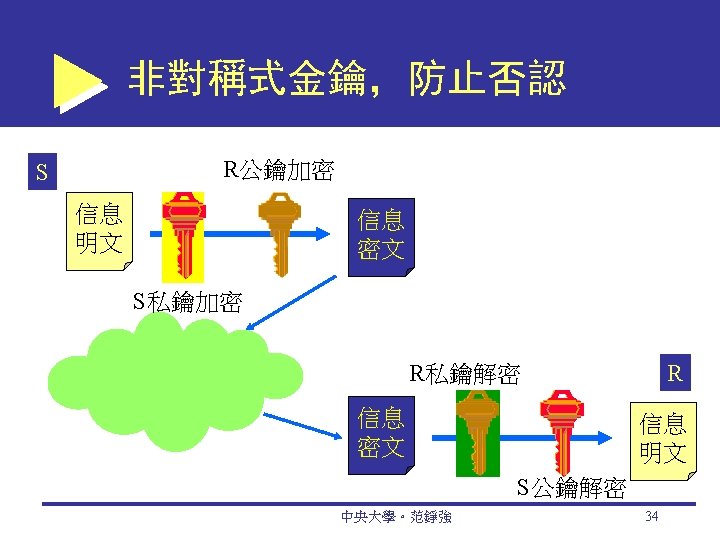
Security Requirements in EC Authentication 身份確認 Process to verify (assure) the real identity of an individual, computer program, or EC Web site Authorization 授權 Process of determining what the authenticated entity is allowed to access and what operations it is allowed to perform Nonrepudiation 不可否認 Assurance that online customers or trading partners cannot falsely deny (repudiate) their purchase or transaction Auditing 稽核軌跡 The process of collecting information about attempts to access particular resources, use particular privileges, or perform other security actions 中央大學。范錚強 15
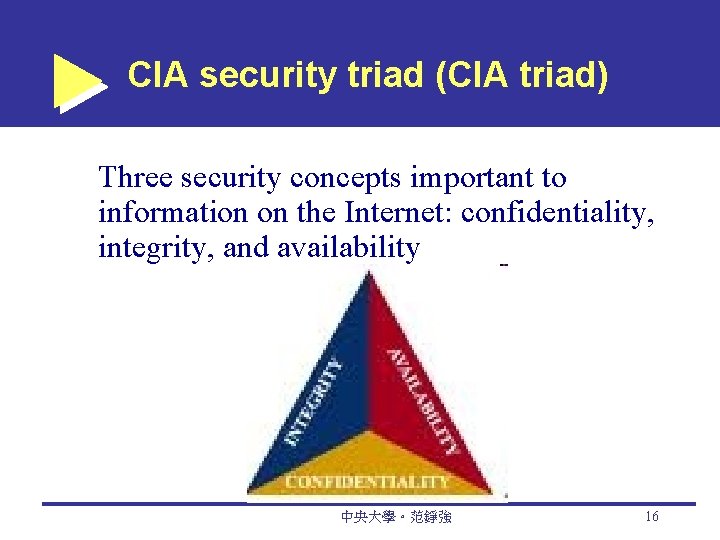
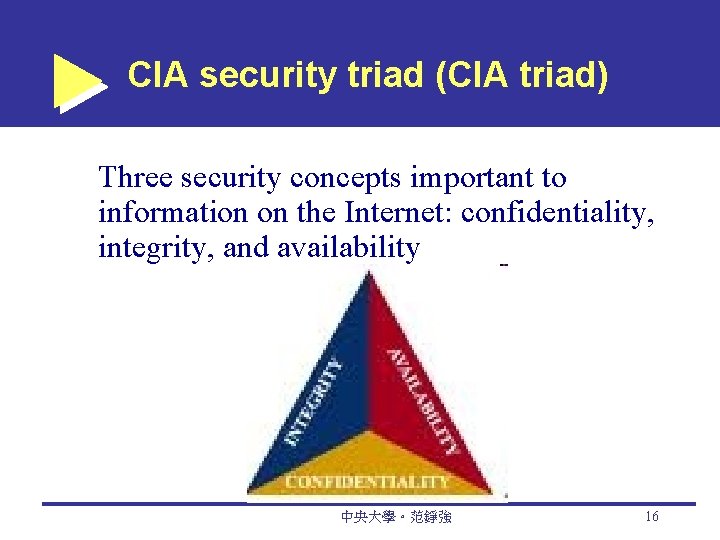
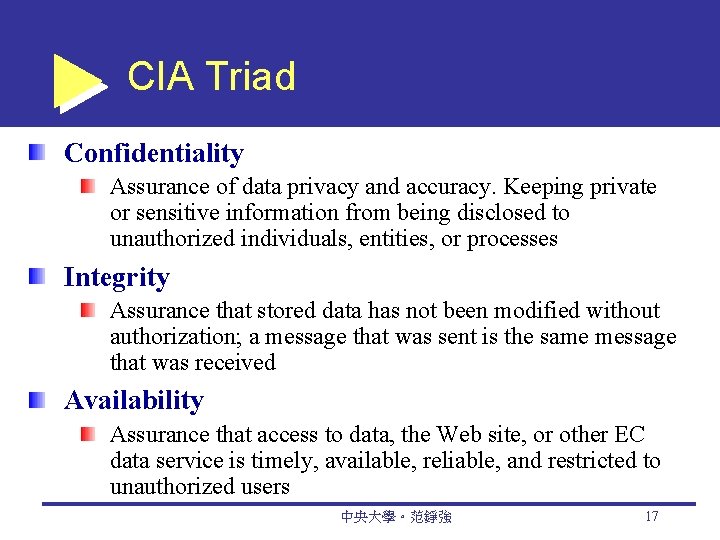
CIA security triad (CIA triad) Three security concepts important to information on the Internet: confidentiality, integrity, and availability 中央大學。范錚強 16
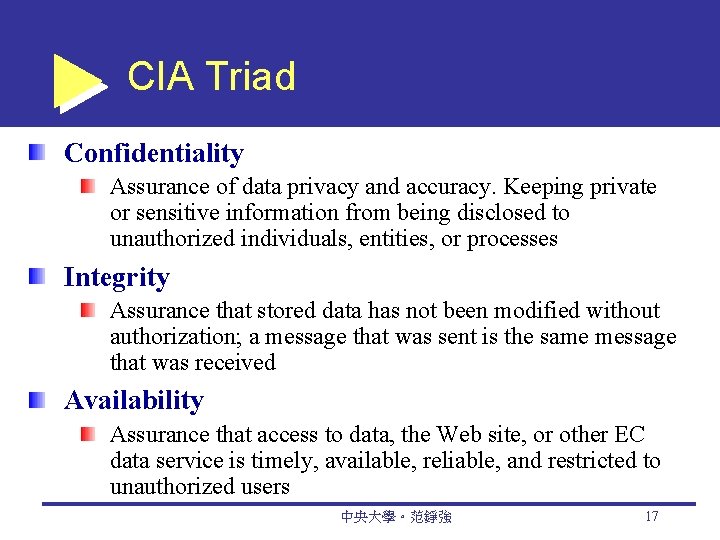
CIA Triad Confidentiality Assurance of data privacy and accuracy. Keeping private or sensitive information from being disclosed to unauthorized individuals, entities, or processes Integrity Assurance that stored data has not been modified without authorization; a message that was sent is the same message that was received Availability Assurance that access to data, the Web site, or other EC data service is timely, available, reliable, and restricted to unauthorized users 中央大學。范錚強 17
Types of Threats and Attacks nontechnical attack An attack that uses chicanery to trick people into revealing sensitive information or performing actions that compromise the security of a network 中央大學。范錚強 20
Nontechnical Attacks: Social Engineering A type of nontechnical attack that uses social pressures to trick computer users into compromising computer networks to which those individuals have access 向屬下要帳號密碼 A multiprong approach should be used to combat social engineering Education and training Policies and procedures Penetration testing 中央大學。范錚強 21
technical attack An attack perpetrated using software and systems knowledge or expertise common (security) vulnerabilities and exposures (CVEs) Publicly known computer security risks, which are collected, listed, and shared by a board of securityrelated organizations (cve. mitre. org) National Infrastructure Protection Center (NIPC) A joint partnership under the auspices of the FBI between governmental and private industry; designed to prevent and protect the nation’s infrastructure 中央大學。范錚強 22
Types of Threats and Attacks denial-of-service (Do. S) attack An attack on a Web site in which an attacker uses specialized software to send a flood of data packets to the target computer with the aim of overloading its resources distributed denial-ofservice (DDo. S) attack A denial-of-service attack in which the attacker gains illegal administrative access to as many computers on the Internet as possible and uses the multiple computers to send a flood of data packets to the target computer 中央大學。范錚強 23
Types of Threats and Attacks Malware A generic term for malicious software Virus A piece of software code that inserts itself into a host, including the operating systems, in order to propagate; it requires that its host program be run to activate it worm A software program that runs independently, consuming the resources of its host in order to maintain itself, that is capable of propagating a complete working version of itself onto another machine 中央大學。范錚強 24
Security Risk Management A systematic process for determining the likelihood of various security attacks and for identifying the actions needed to prevent or mitigate those attacks Security risk management consists of three phases: Asset identification Risk assessment Implementation 中央大學。范錚強 25
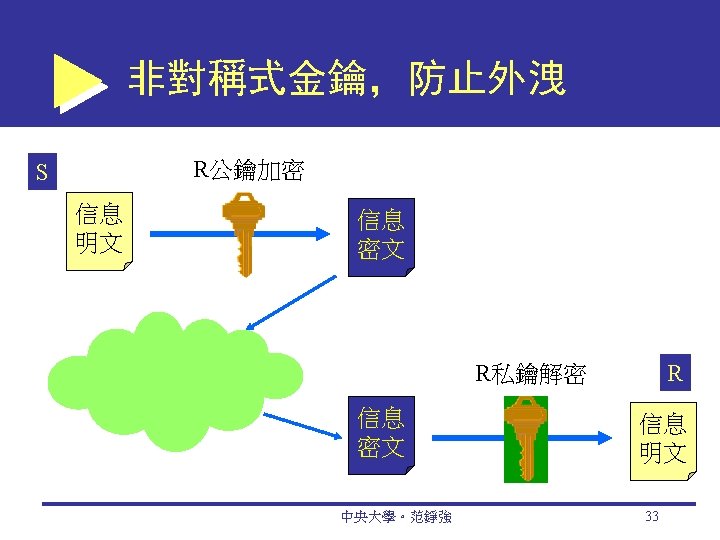
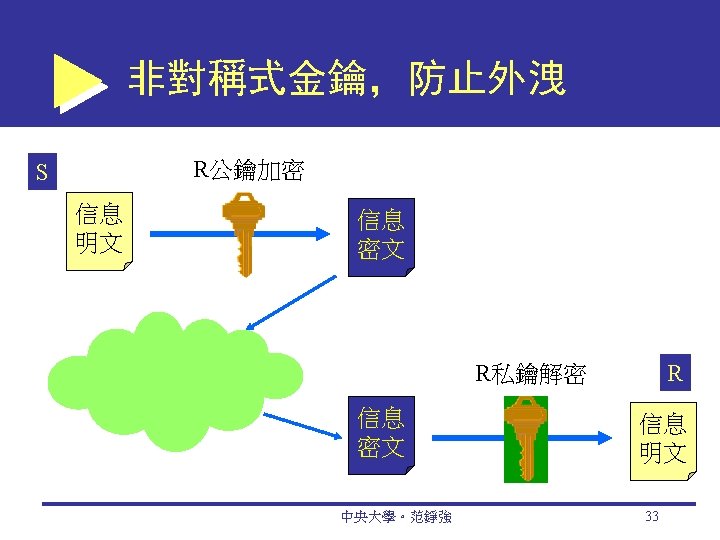
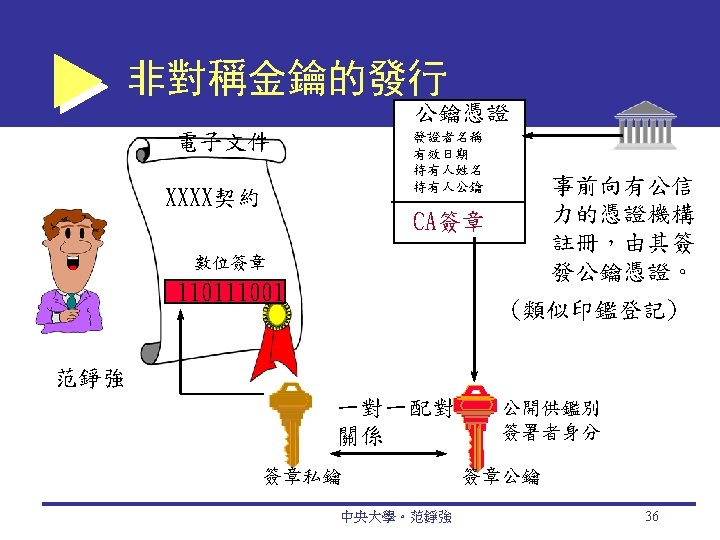
Securing EC Communications public key infrastructure (PKI) A scheme for securing e-payments using public key encryption and various technical components encryption The process of scrambling (encrypting) a message in such a way that it is difficult, expensive, or timeconsuming for an unauthorized person to unscramble (decrypt) it plaintext An unencrypted message in human-readable form 中央大學。范錚強 26
Securing EC Communications ciphertext A plaintext message after it has been encrypted into a machine-readable form encryption algorithm The mathematical formula used to encrypt the plaintext into the ciphertext, and vice versa key The secret code used to encrypt and decrypt a message 中央大學。范錚強 27
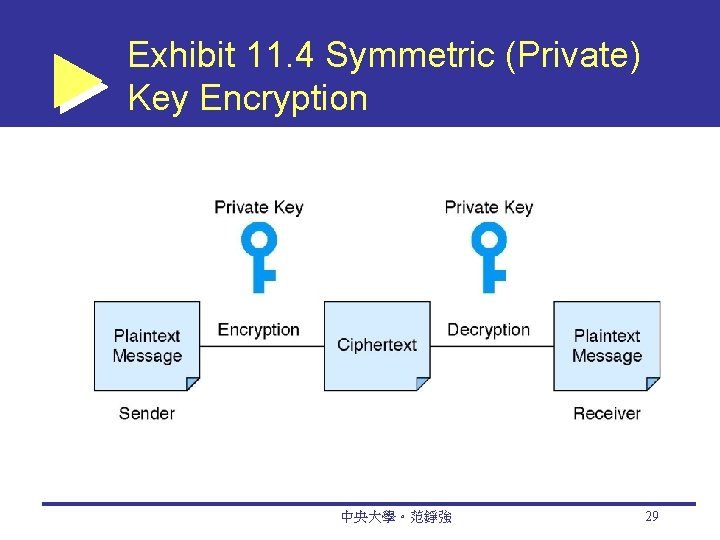
Securing EC Communications symmetric (private) key system An encryption system that uses the same key to encrypt and decrypt the message Data Encryption Standard (DES) The standard symmetric encryption algorithm supported the NIST and used by U. S. government agencies until October 2, 2000 中央大學。范錚強 28
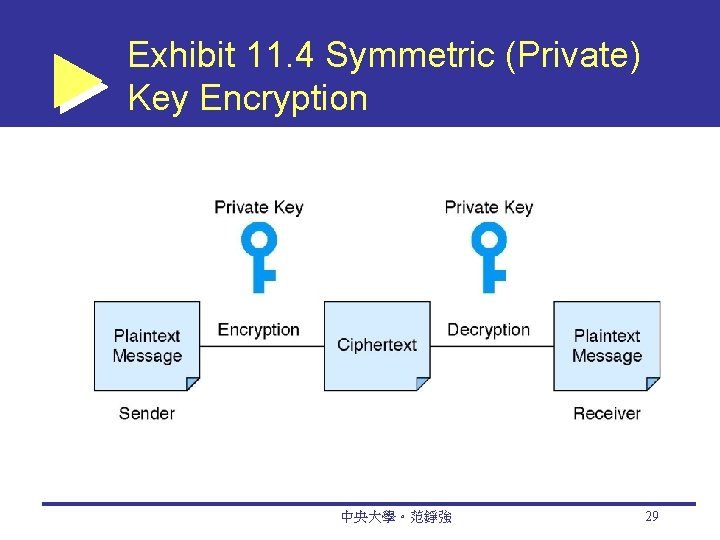
Exhibit 11. 4 Symmetric (Private) Key Encryption 中央大學。范錚強 29
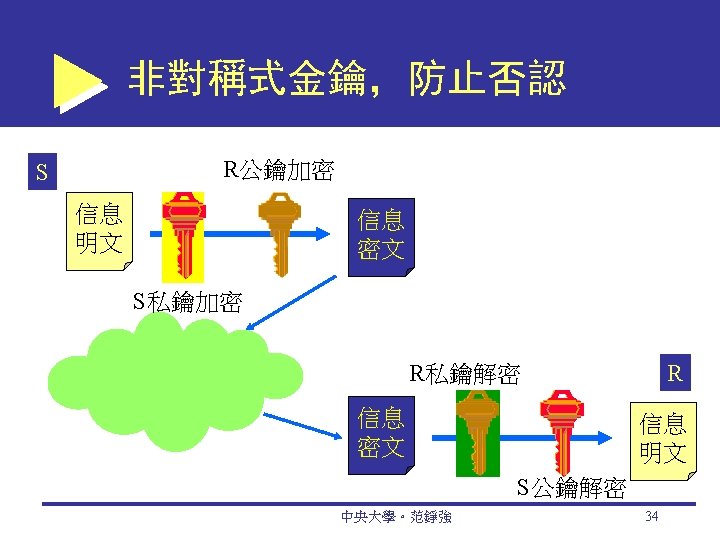
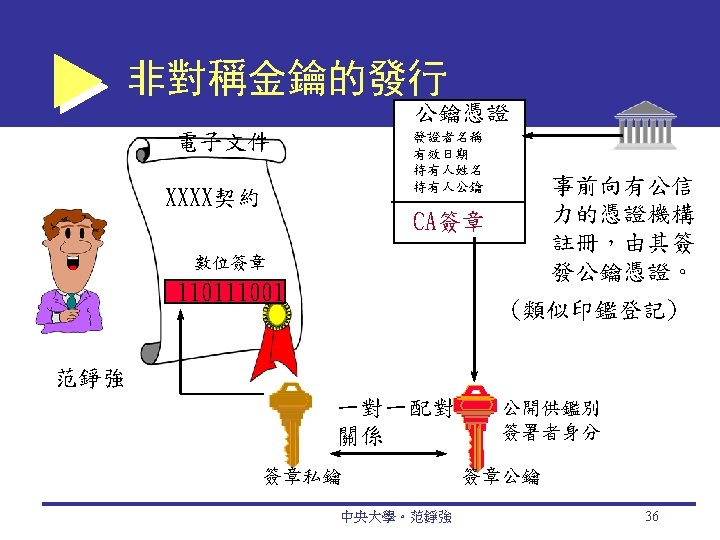
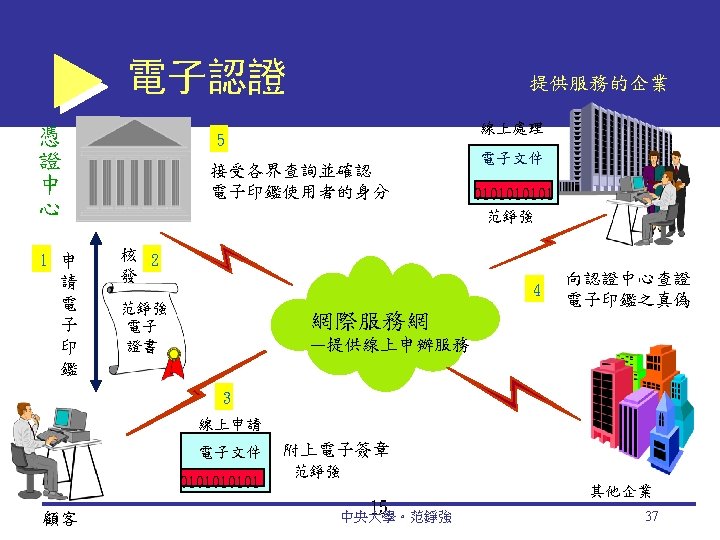
Public (Asymmetric) Key Encryption public key encryption Method of encryption that uses a pair of matched keys—a public key to encrypt a message and a private key to decrypt it, or vice versa public key Encryption code that is publicly available to anyone 中央大學。范錚強 30
Digital Signatures digital signature An identifying code that can be used to authenticate the identity of the sender of a document hash A mathematical computation that is applied to a message, using a private key, to encrypt the message digest A summary of a message, converted into a string of digits, after the hash has been applied digital envelope The combination of the encrypted original message and the digital signature, using the recipient’s public key 中央大學。范錚強 31

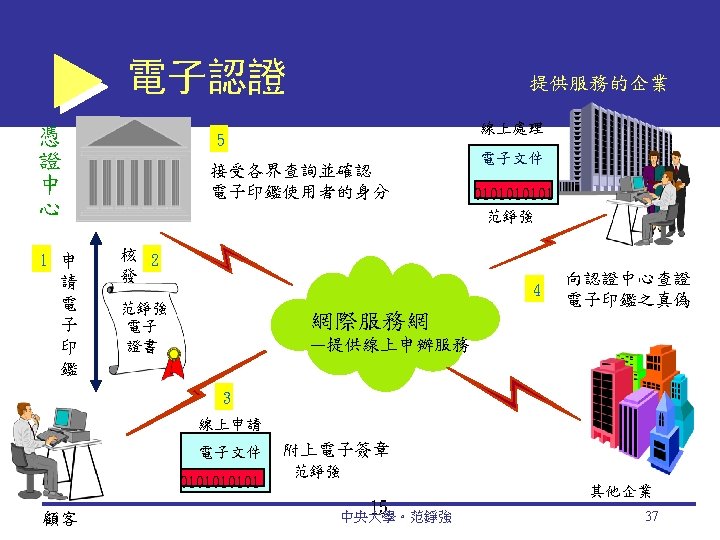
Secure Socket Layer (SSL) Protocol that utilizes standard certificates for authentication and data encryption to ensure privacy or confidentiality 在用戶不知覺的情況之下,交換資料的電 腦間交換非對稱金鑰 Transport Layer Security (TLS) As of 1996, another name for the SSL protocol 中央大學。范錚強 38
Securing EC Networks demilitarized zone (DMZ) Network area that sits between an organization’s internal network and an external network (Internet), providing physical isolation between the two networks that is controlled by rules enforced by a firewall. personal firewall A network node designed to protect an individual user’s desktop system from the public network by monitoring all the traffic that passes through the computer’s network interface card. 中央大學。范錚強 39
Business Continuity and Disaster Recovery Planning Disaster avoidance An approach oriented toward prevention. The idea is to minimize the chance of avoidable disasters (such as fire or other human-caused threats). Risk-management and cost-benefit analysis Risk-Management Analysis Ethical Issues 中央大學。范錚強 52
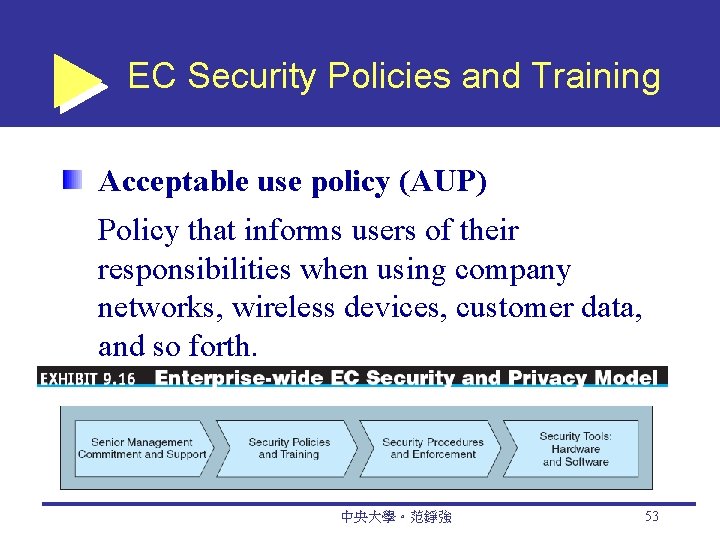
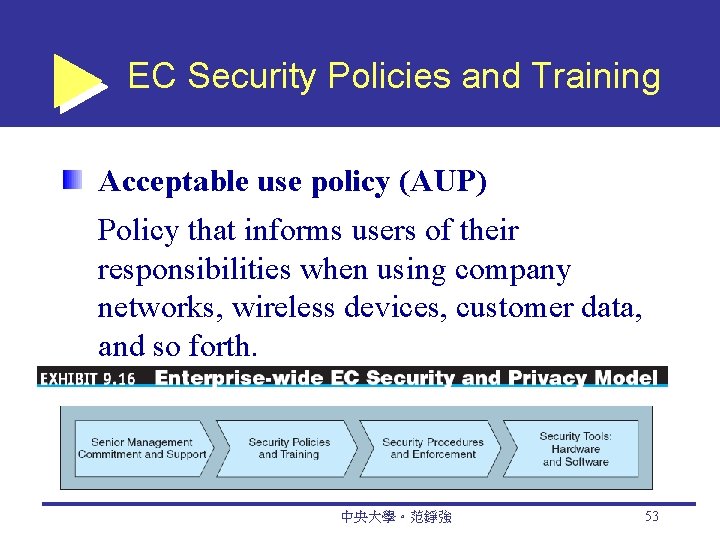
EC Security Policies and Training Acceptable use policy (AUP) Policy that informs users of their responsibilities when using company networks, wireless devices, customer data, and so forth. 中央大學。范錚強 53