40 System Call Ch 5 System Call 1
- Slides: 11
제 40강 : System Call Ch 5 System Call 1
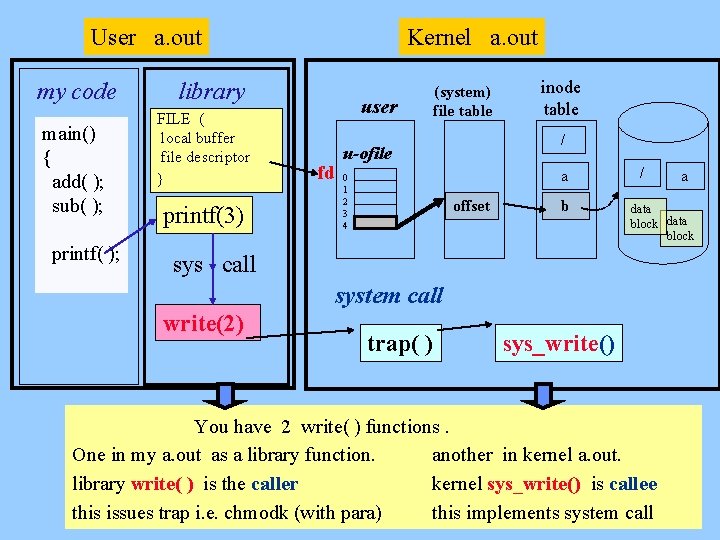
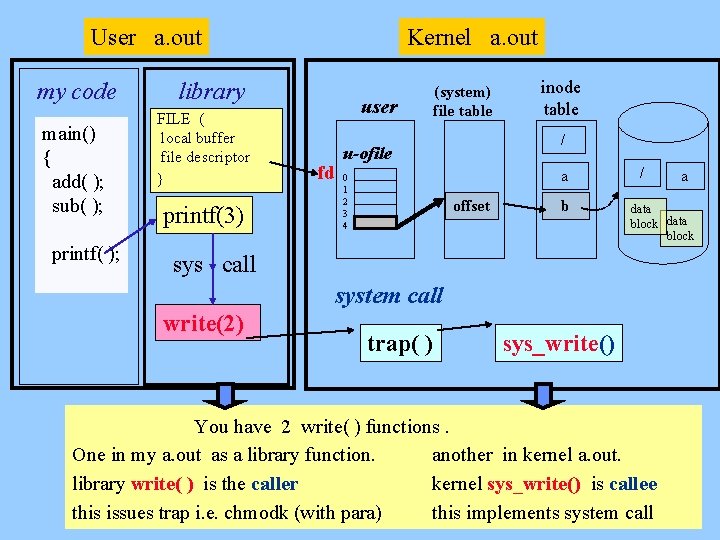
Kernel a. out User a. out my code main() { add( ); sub( ); printf( ); library FILE ( local buffer file descriptor } printf(3) user fd (system) file table / u-ofile 0 1 2 3 4 inode table offset a / b data block a sys call system call write(2) trap( ) sys_write() You have 2 write( ) functions. One in my a. out as a library function. another in kernel a. out. library write( ) is the caller kernel sys_write() is callee this issues trap i. e. chmodk (with para) this implements system call 2
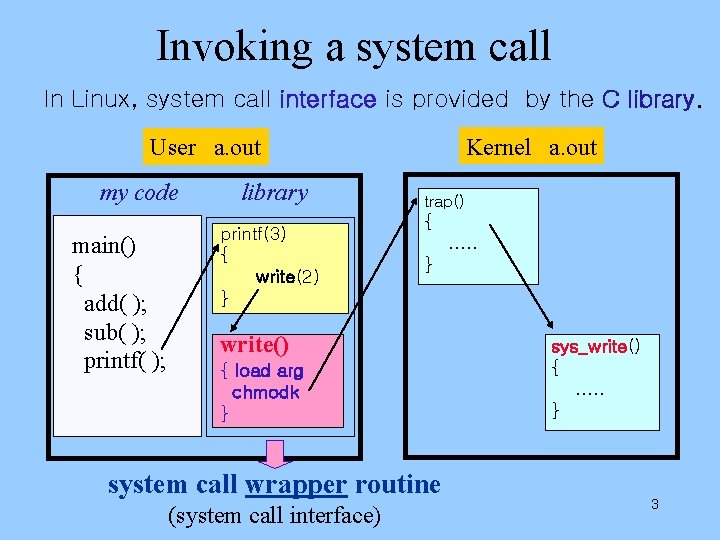
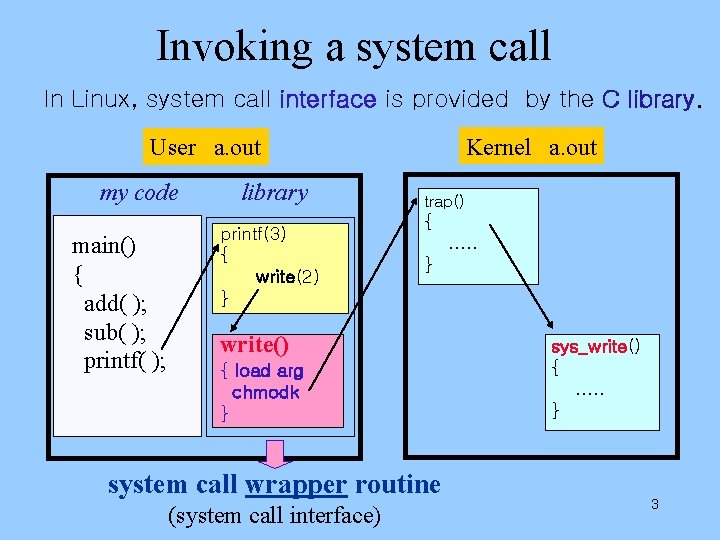
Invoking a system call In Linux, system call interface is provided by the C library. Kernel a. out User a. out my code main() { add( ); sub( ); printf( ); library printf(3) { write(2) } trap() { …. . } write() { load arg chmodk } system call wrapper routine (system call interface) sys_write() { …. . } 3
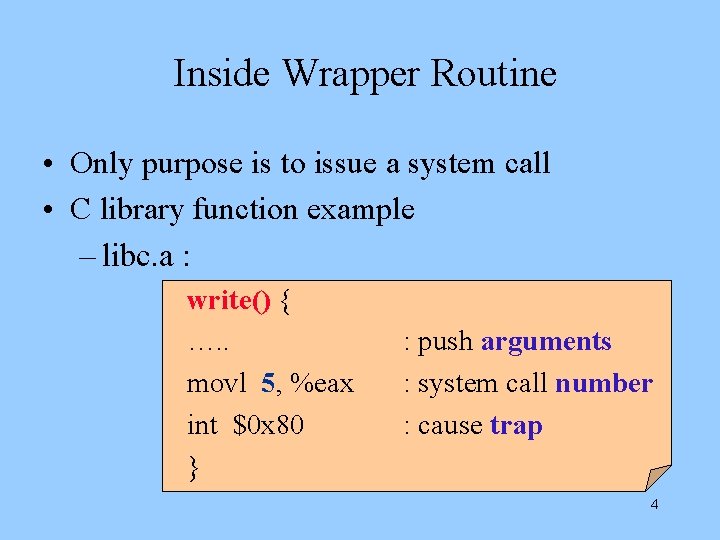
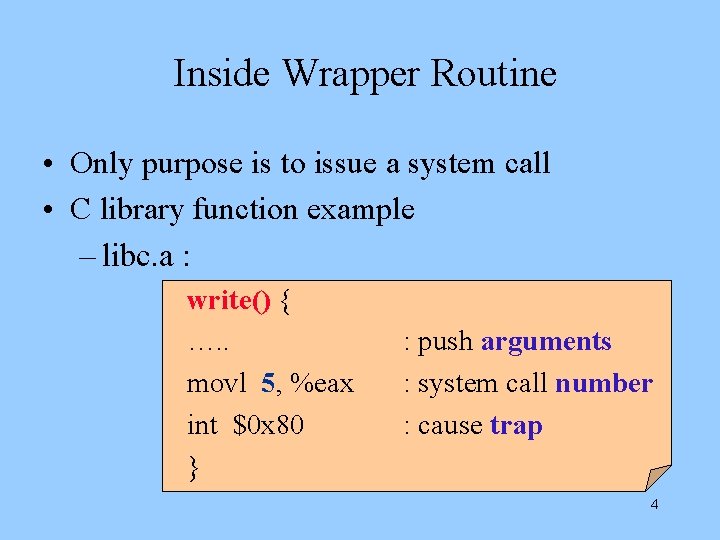
Inside Wrapper Routine • Only purpose is to issue a system call • C library function example – libc. a : write() { …. . movl 5, %eax int $0 x 80 } : push arguments : system call number : cause trap 4
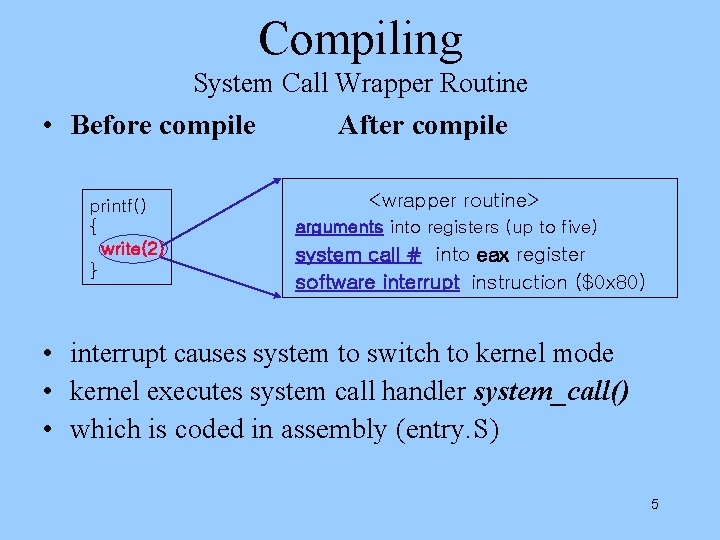
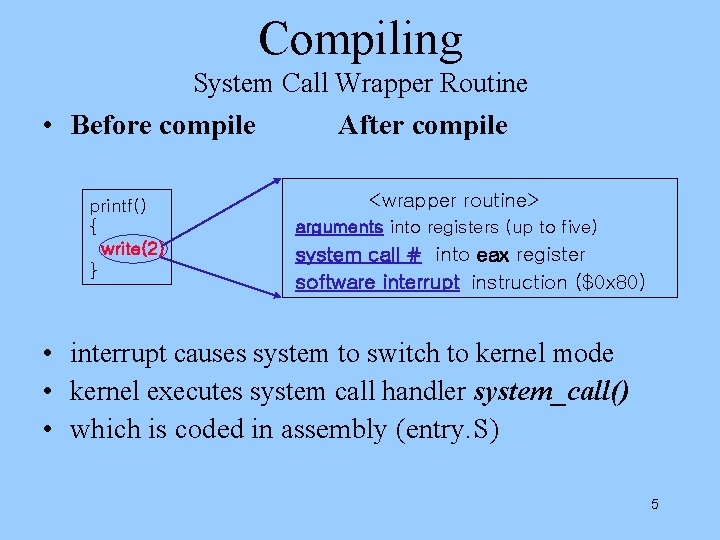
Compiling System Call Wrapper Routine • Before compile printf() { write(2) } After compile <wrapper routine> arguments into registers (up to five) system call # into eax register software interrupt instruction ($0 x 80) • interrupt causes system to switch to kernel mode • kernel executes system call handler system_call() • which is coded in assembly (entry. S) 5
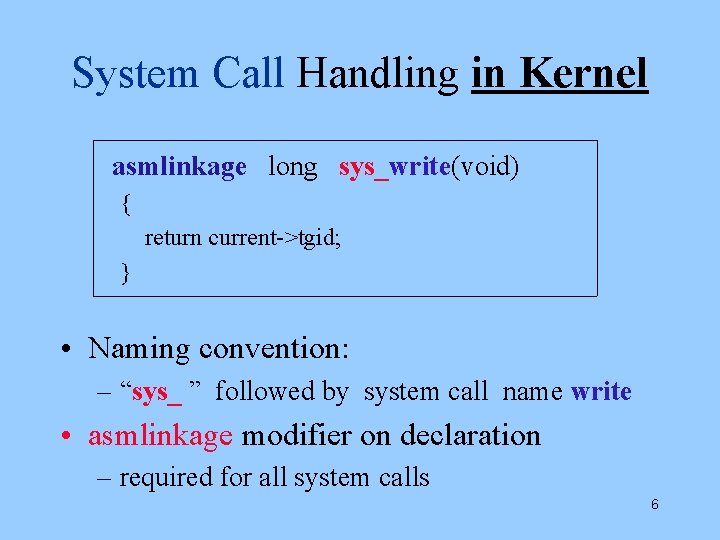
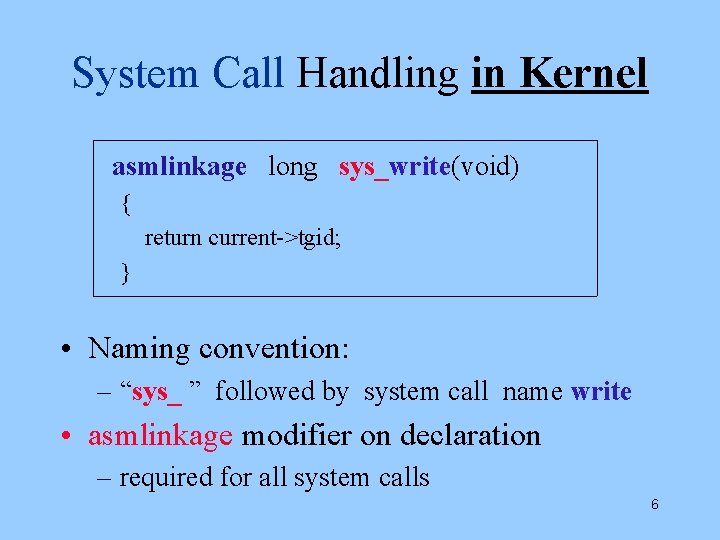
System Call Handling in Kernel asmlinkage long sys_write(void) { return current->tgid; } • Naming convention: – “sys_ ” followed by system call name write • asmlinkage modifier on declaration – required for all system calls 6
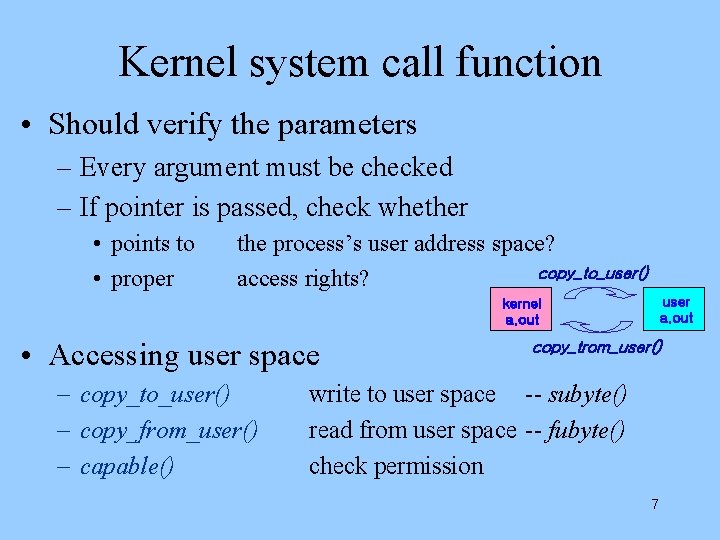
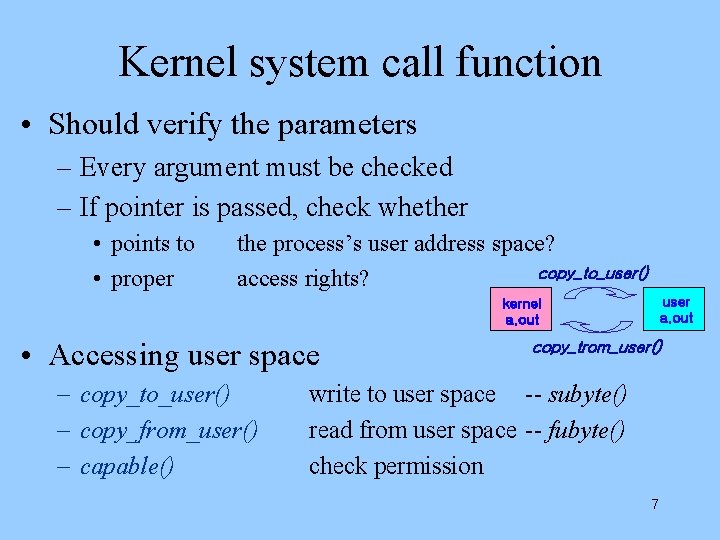
Kernel system call function • Should verify the parameters – Every argument must be checked – If pointer is passed, check whether • points to • proper the process’s user address space? copy_to_user() access rights? user a. out kernel a. out • Accessing user space – copy_to_user() – copy_from_user() – capable() copy_trom_user() write to user space -- subyte() read from user space -- fubyte() check permission 7
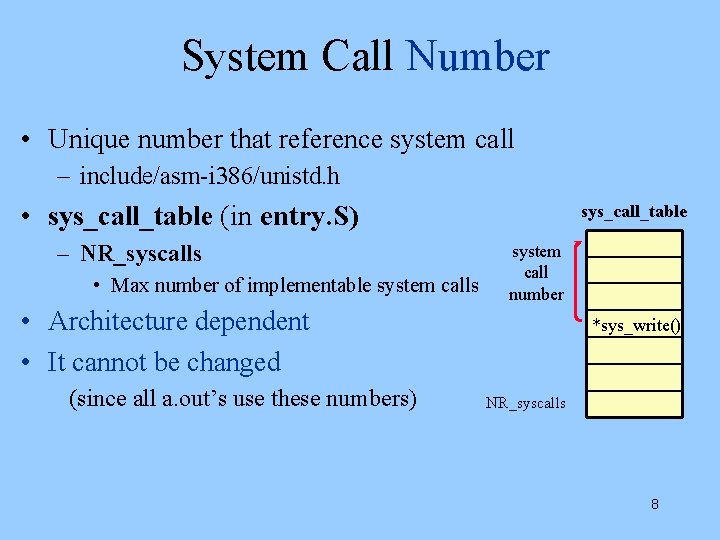
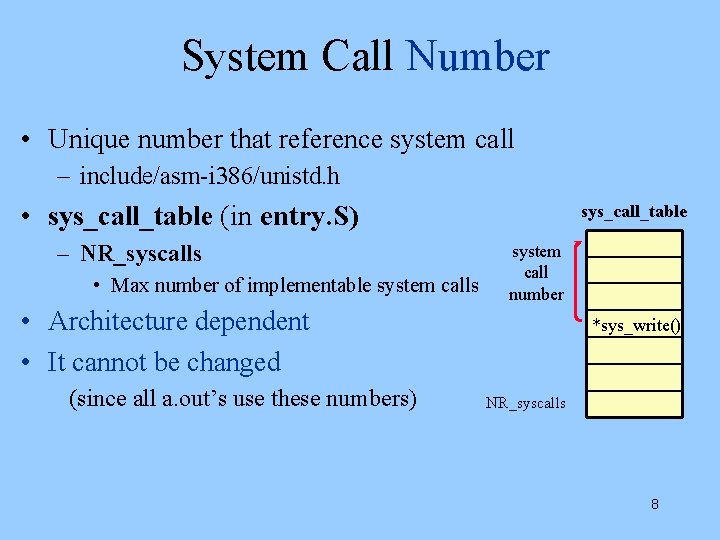
System Call Number • Unique number that reference system call – include/asm-i 386/unistd. h • sys_call_table (in entry. S) – NR_syscalls • Max number of implementable system calls sys_call_table system call number • Architecture dependent • It cannot be changed (since all a. out’s use these numbers) *sys_write() NR_syscalls 8
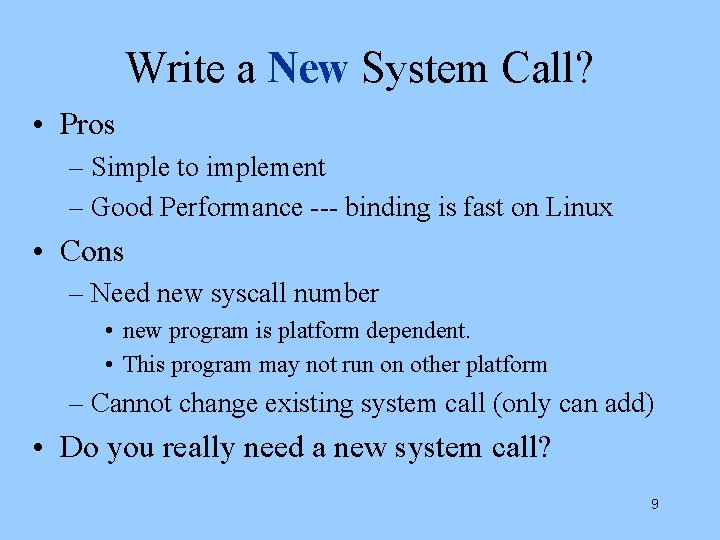
Write a New System Call? • Pros – Simple to implement – Good Performance --- binding is fast on Linux • Cons – Need new syscall number • new program is platform dependent. • This program may not run on other platform – Cannot change existing system call (only can add) • Do you really need a new system call? 9
Alternative to New System Call • Implement a new file fd. NEW • Let this file correspond to a new system call – read(fd. NEW), write(fd. NEW), ioctl(fd. NEW) to it. – which pass data & control between user & kernel • Nobody adds new system call in Linux • Linux keeps very clean system call layer 10
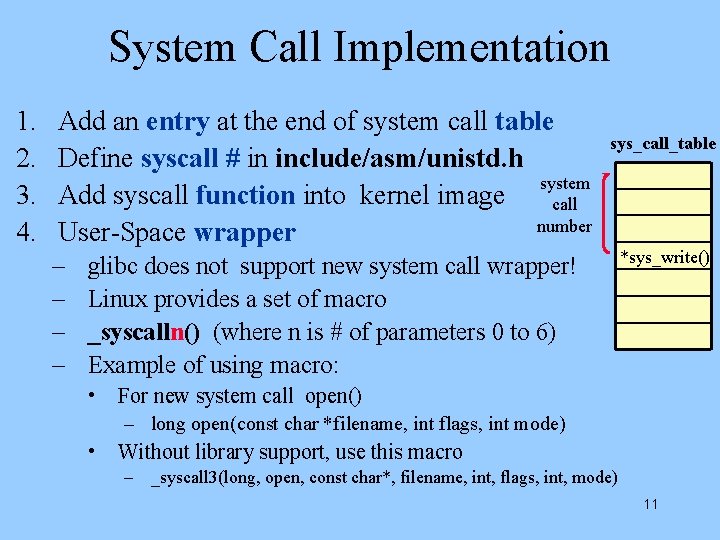
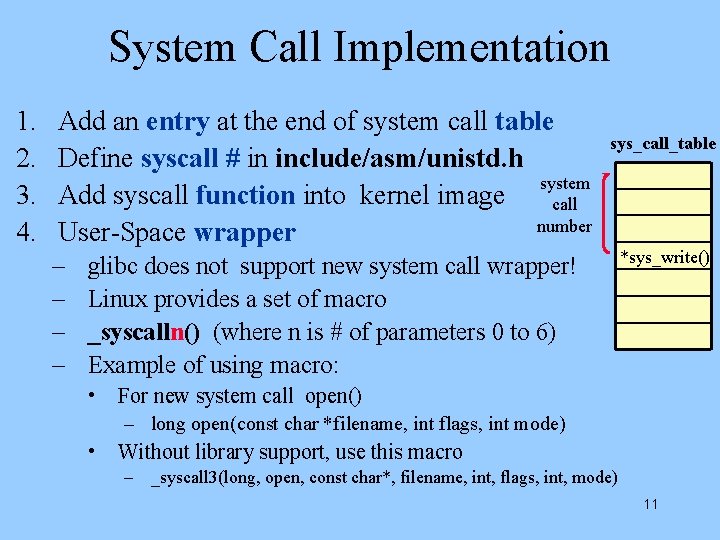
System Call Implementation 1. 2. 3. 4. Add an entry at the end of system call table Define syscall # in include/asm/unistd. h system Add syscall function into kernel image call number User-Space wrapper – – sys_call_table glibc does not support new system call wrapper! Linux provides a set of macro _syscalln() (where n is # of parameters 0 to 6) Example of using macro: *sys_write() • For new system call open() – long open(const char *filename, int flags, int mode) • Without library support, use this macro – _syscall 3(long, open, const char*, filename, int, flags, int, mode) 11