3 Web Proxies 1 Web Protocols and Practice
3 Web Proxies 1 Web Protocols and Practice
WEB PROXIES Topics 2 Web Proxy Definition Three of the Most Common Intermediaries Classification of Proxies Gateway to non-HTTP Systems Filtering Request and Responses Request-Response Exchange with a Proxy Handling HTTP Requests and Responses Proxy Chaining and Hierarchies Proxy Configuration Proxy Privacy Issues Other kinds of Proxies Web Protocols and Practice
WEB PROXIES Web Proxy Definition A Web proxy is an intermediary program that could be on the same machine or on a machine different form where the request originated. A Web proxy acts on behalf of a set of clients in communication with servers. A proxy acts as a server to clients and as a client to other proxies or origin servers. 3 Web Protocols and Practice
WEB PROXIES Web Proxy Definition A Web proxy is used for Ø Sharing of resource access Ø Caching of responses Ø Anonymization Ø Transformation of requests and responses Ø Filtering requests/responses 4 Web Protocols and Practice
WEB PROXIES Three of the Most Common Intermediaries Three of the most common intermediaries are Ø Proxy » An intermediary program which acts as both a server and a client for the purpose of forwarding requests. Ø Gateway » A server that typically acts as an intermediary for a non-HTTP server such as a mail or FTP server. Ø Tunnel » 5 An intermediary program that relays bits between two connections and acts at the syntactic level, unlike a proxy or gateway; it does not parse or interpret the HTTP message following through it. Web Protocols and Practice
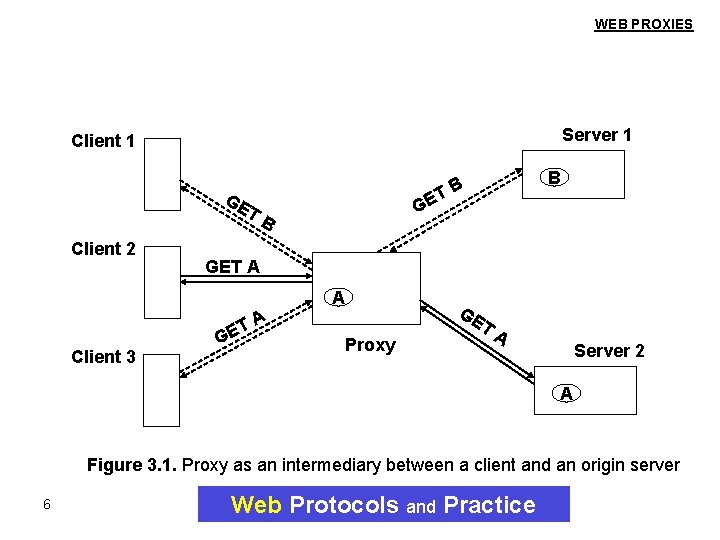
WEB PROXIES Server 1 Client 1 GE T Client 2 GE B GET A A TA Client 3 B TB GE Proxy GE TA Server 2 A Figure 3. 1. Proxy as an intermediary between a client and an origin server 6 Web Protocols and Practice
WEB PROXIES Figure 3. 1 demonstrates a proxy playing the role of client and server. Client 1’s request for resource B being forwarded by the proxy to server 1 and the response returned to the client. This response is not cached. The request from client 2 for resource A is forwarded to server 2, but the response is cached in the proxy and returned to the client. Now, when client 3 requests for resource A, the request is not forwarded by the proxy; instead a cached copy of resource A is returned to client 3. 7 Web Protocols and Practice
WEB PROXIES Classification of Proxies can be divided to: Ø Caching proxy » Proxies that have caches associated with them. Ø Transparent proxy » 8 Proxies that do not modify messages as they flow through them. Web Protocols and Practice
WEB PROXIES Gateway to non-HTTP Systems A proxy can play the role of an intermediary like gateway to other systems that communicate using non-HTTP. In communicating between a Web client and a FTP server, proxy acts as a gateway, because the client and server do not speak the same protocol (Figure 3. 2). 9 Web Protocols and Practice
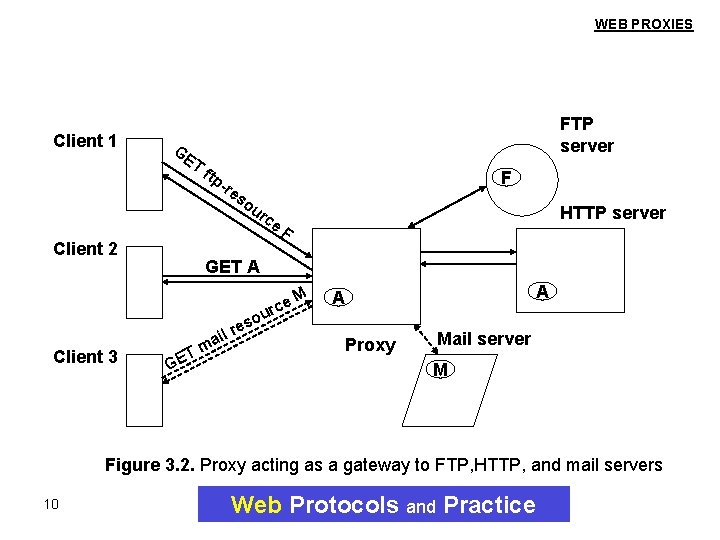
WEB PROXIES Client 1 GE T Client 2 Client 3 FTP server ftp -re so F ur ce F HTTP server F GET A G m ET res l i a ou M rce A A Proxy Mail server M Figure 3. 2. Proxy acting as a gateway to FTP, HTTP, and mail servers 10 Web Protocols and Practice
WEB PROXIES Figure 3. 2 shows how an proxy acts as a gateway to an FTP and mail server while also playing the role of an HTTP proxy. A Web client sends a request to an FTP server via a proxy. The request to the proxy is a regular HTTP request. The proxy first converts the Web client’s request into an FTP request. Similarly, the proxy can act as a gateway to a mail server and obtain a mail resource M. The proxy would return the file to the Web client in the form of an HTTP response. 11 Web Protocols and Practice
WEB PROXIES Filtering Requests and Responses A proxy filters improper requests and responses based on Ø Ø 12 Destination sites Characteristics (response size) Performance Security Web Protocols and Practice
WEB PROXIES Request-Response Exchange with a Proxy A proxy can play the role in handling HTTP requests and responses. Various steps involved when a proxy is present in the path of a request from a browser to an origin server (Figure 3. 3). 13 Web Protocols and Practice
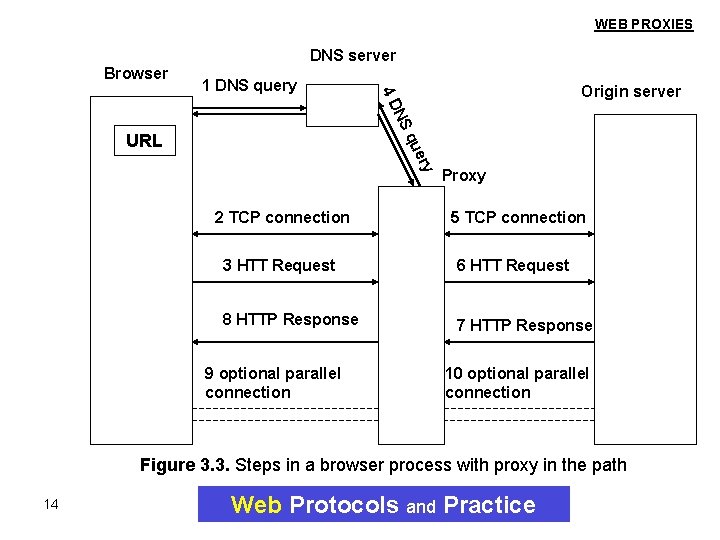
WEB PROXIES DNS server Browser Origin server NS 4 D 1 DNS query qu URL 2 TCP connection Proxy 5 TCP connection 3 HTT Request 6 HTT Request 8 HTTP Response 7 HTTP Response 9 optional parallel connection 10 optional parallel connection Figure 3. 3. Steps in a browser process with proxy in the path 14 Web Protocols and Practice
WEB PROXIES Figure 3. 3 shows that upon the user’s selection of a URL, the browser does the Domain Name System (DNS) lookup of the proxy and then sets up a TCP connection to the proxy (steps 1 and 2). The HTTP request form the browser (step 3) triggers the proxy to do the DNS lookup of the origin server (step 4). The proxy sets up a TCP connection to the origin server and then sends the HTTP request to the origin server (steps 5 and 6). The response from the origin server is sent back to the proxy, which forwards it to the browser (steps 7 and 8). The browser might set up optional parallel connections to the proxy, and the proxy may set up its own optional parallel connections to the origin server (steps 9 and 10). 15 Web Protocols and Practice
WEB PROXIES Handling HTTP Requests and Responses A proxy must be able to abide by several requirements like: Ø Syntactic requirements Ø Semantic requirements 16 Web Protocols and Practice
WEB PROXIES Syntactic Requirements Syntactic requirements typically concern headers that a proxy add to messages and modifications of existing headers. 17 Web Protocols and Practice
WEB PROXIES Semantic Requirements The semantic requirements include proper handling of requests and responses and obeying the constraints on returning cached responses. 18 Web Protocols and Practice
WEB PROXIES Handling HTTP Requests and Responses The various requirements (syntactic and semantic) fall into the following categories: Ø Identification Ø Version number change Ø Adding obligatory information about the resource Ø Semantic neutrality Ø Handling delays and buffering Ø State maintenance and policy issues Ø Practical implementation issues Ø Handling cookies 19 Web Protocols and Practice
WEB PROXIES Proxy Chaining and Hierarchies A user’s request and origin server’s response may travel through several proxies chained together. (Figure 3. 4) A set of proxies within an organization may be connected in a hierarchy. A regional proxy may be connected to other regional proxies, which in turn may be connected to a national proxy. This way is useful for reducing Ø Communication costs Ø Communication latency 20 Web Protocols and Practice
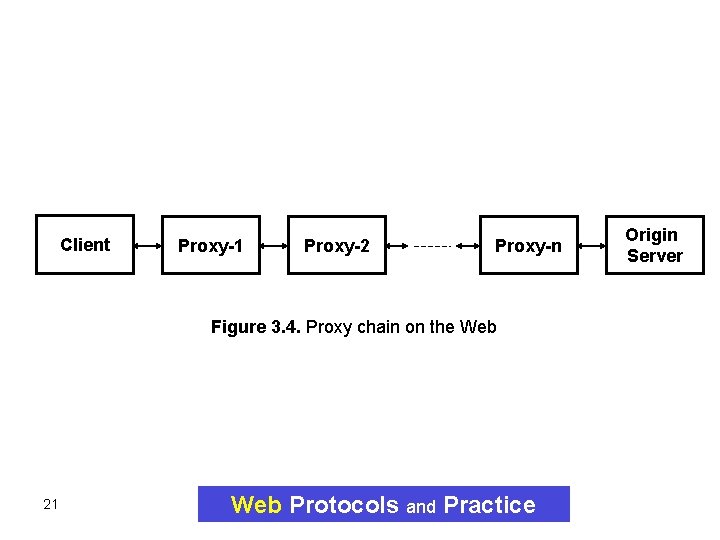
Client Proxy-1 Proxy-2 Proxy-n Figure 3. 4. Proxy chain on the Web 21 Web Protocols and Practice Origin Server
WEB PROXIES Figure 3. 4 shows that a message form a user agent may traverse through multiple servers before it reaches the origin server. Often, rather than a simple linear pipeline, the intermediate servers have other servers connected to them as well on both sides. 22 Web Protocols and Practice
WEB PROXIES Proxy Configuration A user can configure a browser to set various physical and semantic attributes. In the case of proxies, end users do not have any influence in changing configuration information associated with a proxy such as its cache size or frequency of revalidation. 23 Web Protocols and Practice
WEB PROXIES Proxy Privacy Issues A proxy is aware of many details that affects the privacy of the user. A proxy is viewed as a trusted intermediary. To keep user’s privacy, a proxy must act as a tunnel and providing end-to-end encryption. 24 Web Protocols and Practice
WEB PROXIES Other kinds of Proxies Reverse proxies Ø Proxies had to be positioned closer to the origin server to » » 25 Reduce the load on servers Prevent the origin server from being vulnerable Balance the load between the set of servers Access to origin servers behind a firewall Web Protocols and Practice
WEB PROXIES Other kinds of Proxies Interception proxies Ø A proxy that either directly examines network traffic and intercepts Web traffic or receives redirected traffic flow from network elements performing traffic interception. Interception proxies were called Transparent proxies in the industry. 26 Web Protocols and Practice
- Slides: 26