3 Valued Logic Analyzer TVP Part II Tal
![Dereference of NULL pointers ]elem : = c; ]1 ]found : = false; ]2 Dereference of NULL pointers ]elem : = c; ]1 ]found : = false; ]2](https://slidetodoc.com/presentation_image_h2/0e03ca33185dfafc6cc51f600f4f4e1d/image-7.jpg)
![Structural Semantics for SWhile axioms ]assvsos] <x : = a, s=(O, e, car, cdr)> Structural Semantics for SWhile axioms ]assvsos] <x : = a, s=(O, e, car, cdr)>](https://slidetodoc.com/presentation_image_h2/0e03ca33185dfafc6cc51f600f4f4e1d/image-10.jpg)
![Structural Semantics for SWhile rules ]comp 1 sos] <S 1 , s> <S’ 1, Structural Semantics for SWhile rules ]comp 1 sos] <S 1 , s> <S’ 1,](https://slidetodoc.com/presentation_image_h2/0e03ca33185dfafc6cc51f600f4f4e1d/image-11.jpg)
![Running Example ]elem : = c; ]1 ]found : = false; ]2 while ([c Running Example ]elem : = c; ]1 ]found : = false; ]2 while ([c](https://slidetodoc.com/presentation_image_h2/0e03ca33185dfafc6cc51f600f4f4e1d/image-15.jpg)
![prgm. tvs %n = {u, u 0{ %p} = sm = {u: 1/2{ s[cdr] prgm. tvs %n = {u, u 0{ %p} = sm = {u: 1/2{ s[cdr]](https://slidetodoc.com/presentation_image_h2/0e03ca33185dfafc6cc51f600f4f4e1d/image-34.jpg)
 = v 1, v 2: cdr(v 1, v) cdr(v 2, Example: Heap Sharing is[cdr](v) = v 1, v 2: cdr(v 1, v) cdr(v 2,](https://slidetodoc.com/presentation_image_h2/0e03ca33185dfafc6cc51f600f4f4e1d/image-37.jpg)
 = v 1, v 2: cdr(v 1, v) cdr(v 2, Example: Heap Sharing is[cdr](v) = v 1, v 2: cdr(v 1, v) cdr(v 2,](https://slidetodoc.com/presentation_image_h2/0e03ca33185dfafc6cc51f600f4f4e1d/image-38.jpg)
- Slides: 49
3 -Valued Logic Analyzer (TVP) Part II Tal Lev-Ami and Mooly Sagiv
Outline u The Shape Analysis Problem u Solving Shape Analysis with TVLA – Structural Operational Semantics – Predicate logic – Embedding – )Imprecise) Abstract Interpretation – Instrumentation Predicates – Focus – Coerce u Bibliography
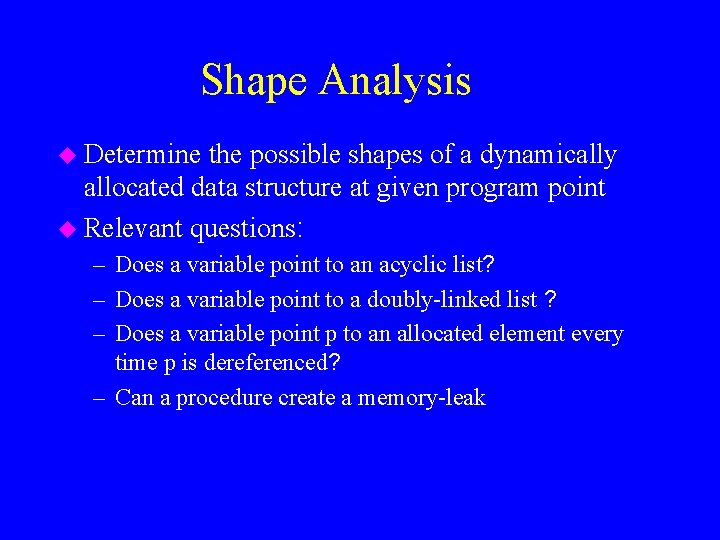
Shape Analysis u Determine the possible shapes of a dynamically allocated data structure at given program point u Relevant questions: – Does a variable point to an acyclic list? – Does a variable point to a doubly-linked list ? – Does a variable point p to an allocated element every time p is dereferenced? – Can a procedure create a memory-leak
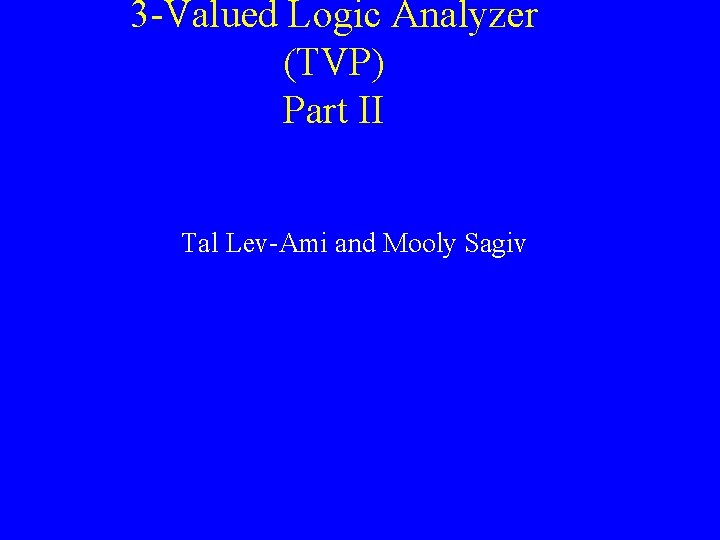
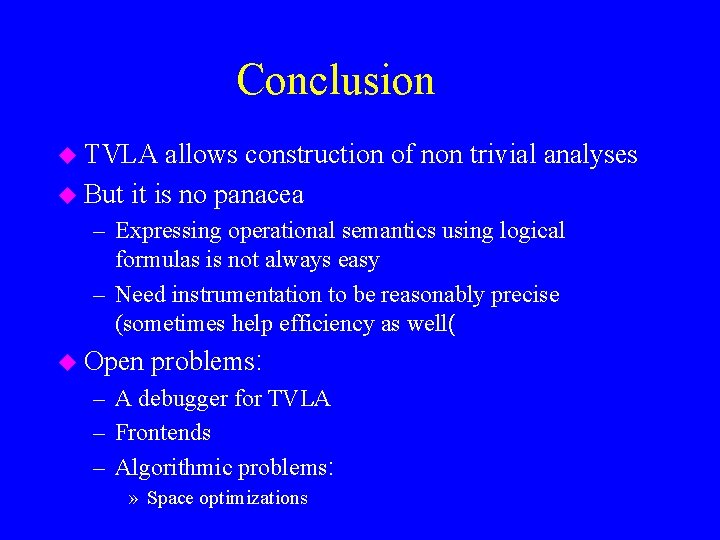
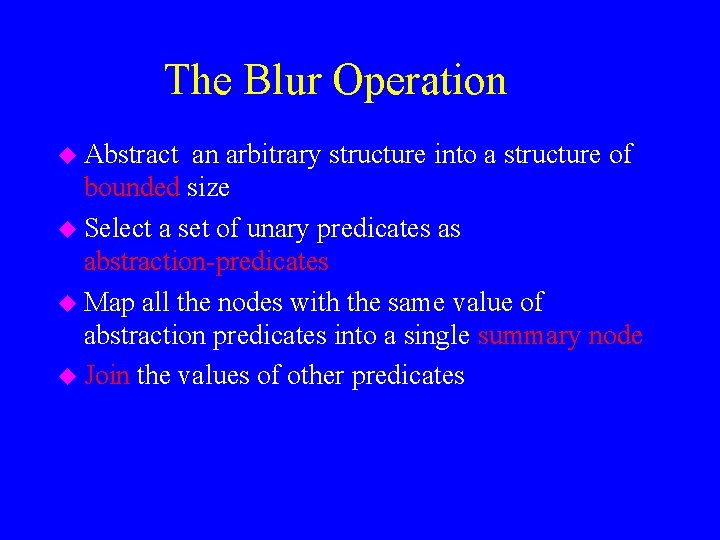
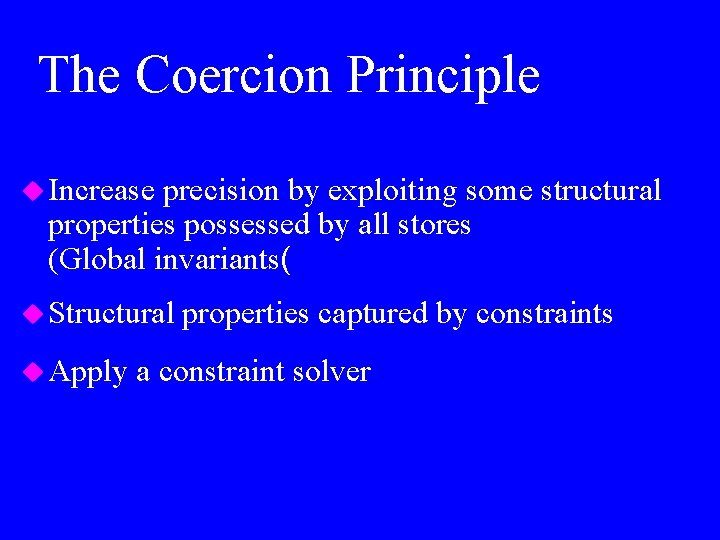
Dereference of NULL pointers typedef struct element} int value; struct element *next ; {Elements bool search(int value, Elements *c) { Elements *elem; for ( elem = c; c != NULL; elem = elem->next; ) if (elem->val == value( NULL dereference return TRUE; return FALSE
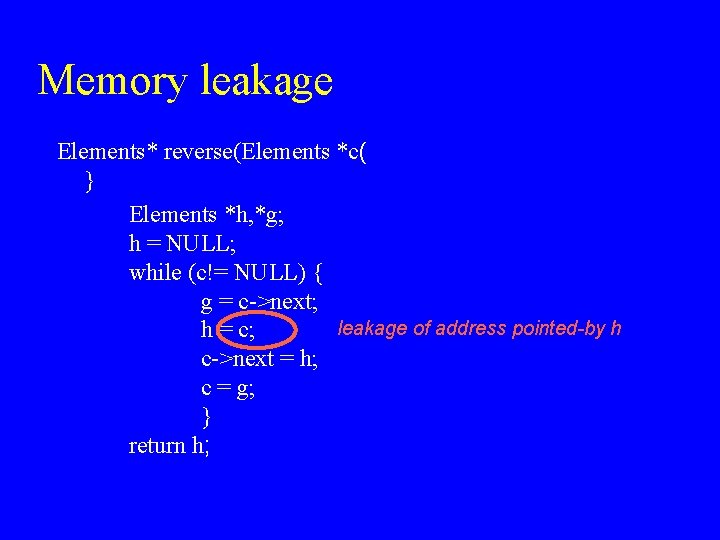
Memory leakage Elements* reverse(Elements *c( } Elements *h, *g; h = NULL; while (c!= NULL) { g = c->next; leakage of address pointed-by h h = c; c->next = h; c = g; } return h;
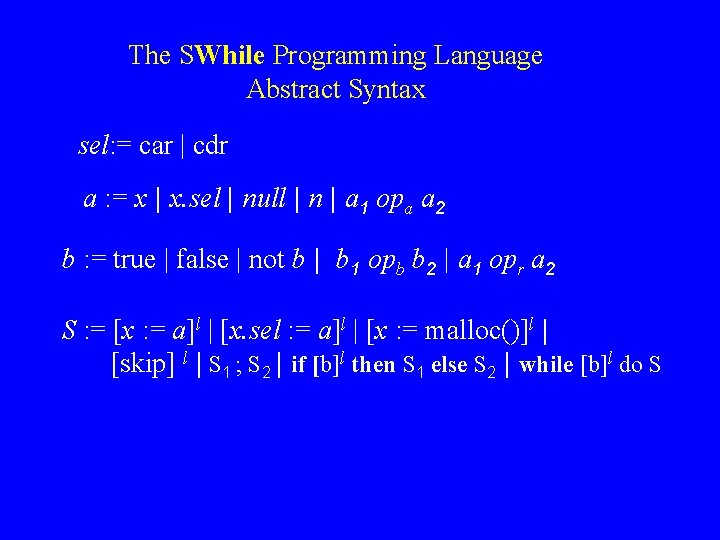
The SWhile Programming Language Abstract Syntax sel: = car | cdr a : = x | x. sel | null | n | a 1 opa a 2 b : = true | false | not b | b 1 opb b 2 | a 1 opr a 2 S : = [x : = a]l | [x. sel : = a]l | [x : = malloc()]l | [skip] l | S 1 ; S 2 | if [b]l then S 1 else S 2 | while [b]l do S
![Dereference of NULL pointers elem c 1 found false 2 Dereference of NULL pointers ]elem : = c; ]1 ]found : = false; ]2](https://slidetodoc.com/presentation_image_h2/0e03ca33185dfafc6cc51f600f4f4e1d/image-7.jpg)
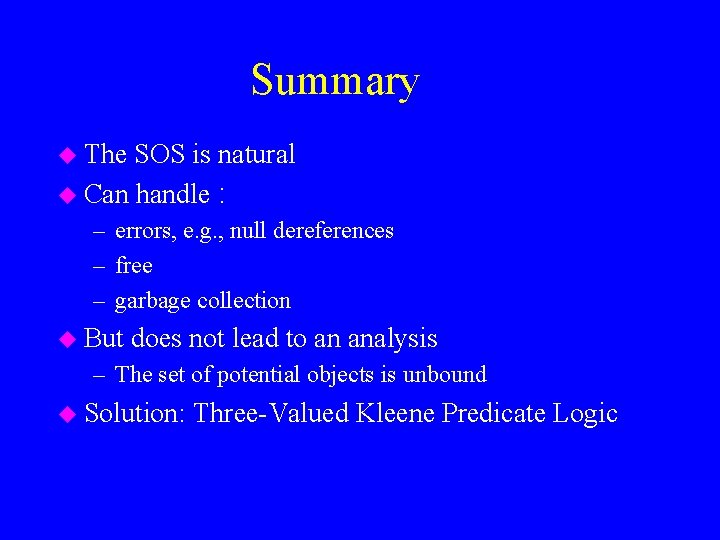
Dereference of NULL pointers ]elem : = c; ]1 ]found : = false; ]2 while ([c != null]3 && [!found]4) ( if ([elem->car= value]5( then [found : = true]6 else [elem = elem->cdr]7 ( NULL dereference
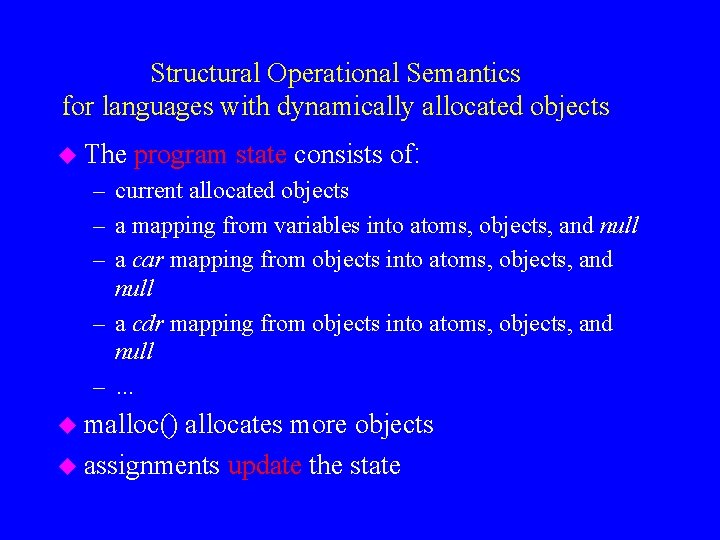
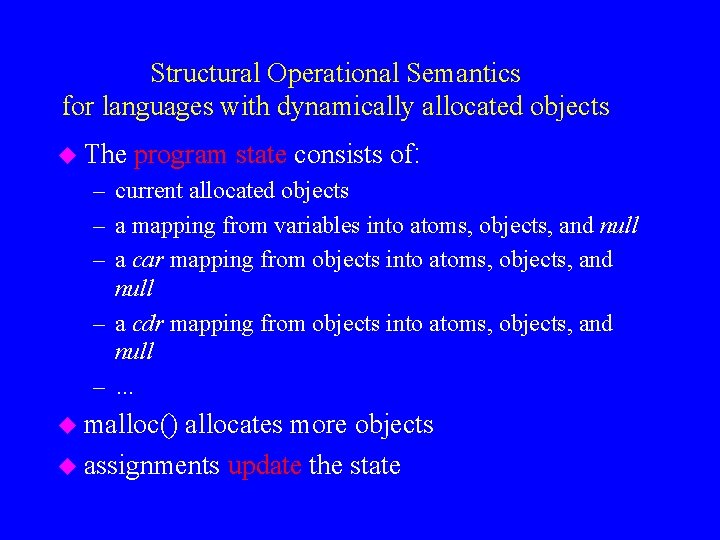
Structural Operational Semantics for languages with dynamically allocated objects u The program state consists of: – current allocated objects – a mapping from variables into atoms, objects, and null – a car mapping from objects into atoms, objects, and null – a cdr mapping from objects into atoms, objects, and null – … u malloc() allocates more objects u assignments update the state
Structural Operational Semantics u The – – – program state S=(O, env, car, cdr: ( current allocated objects O atoms (integers, Booleans) A env: Var* A O {null{ car: A A O {null{ cdr: A A O {null{ u The meaning of expressions A a : S A O {null{ – – A at (s) = at A x ((O, env, car, cdr)) = env(x( A x. car ((O, env, car, cdr)) = car(env(x(( A x. cdr ((O, env, car, cdr)) = cdr(env(x((
![Structural Semantics for SWhile axioms assvsos x a sO e car cdr Structural Semantics for SWhile axioms ]assvsos] <x : = a, s=(O, e, car, cdr)>](https://slidetodoc.com/presentation_image_h2/0e03ca33185dfafc6cc51f600f4f4e1d/image-10.jpg)
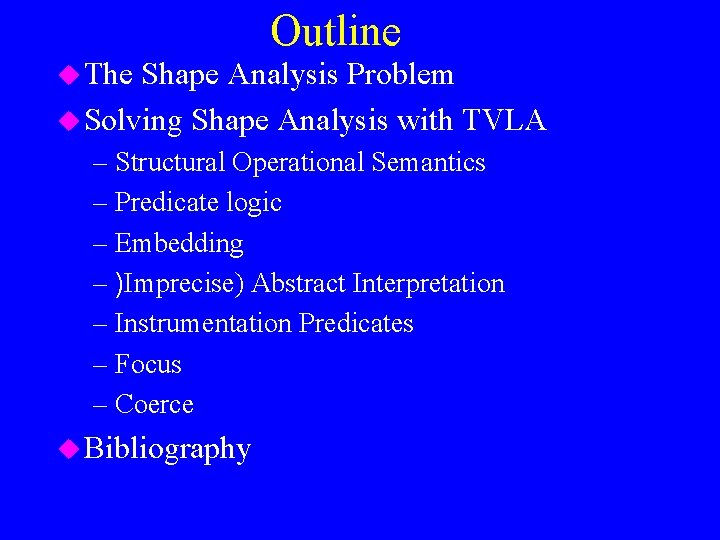
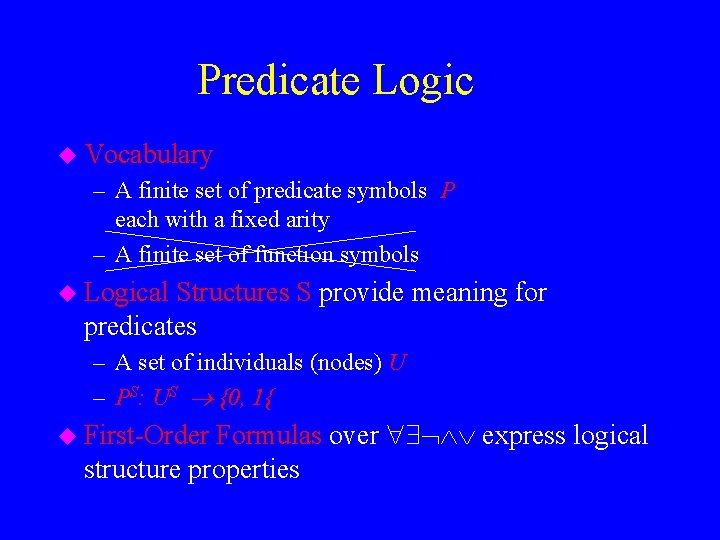
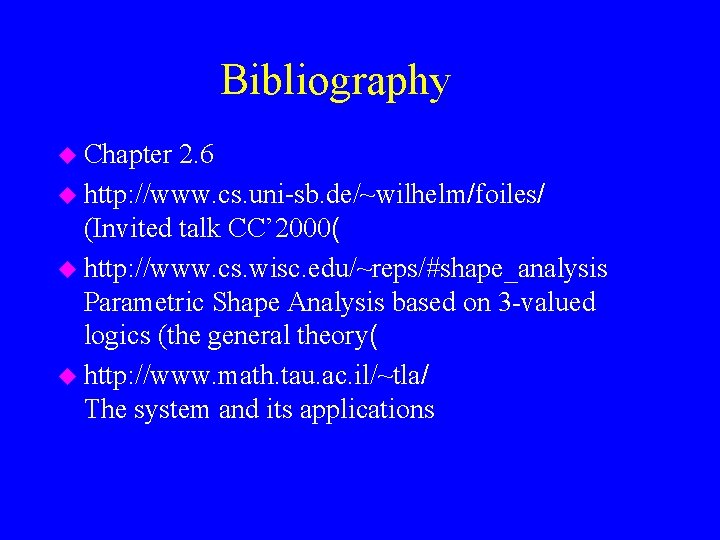
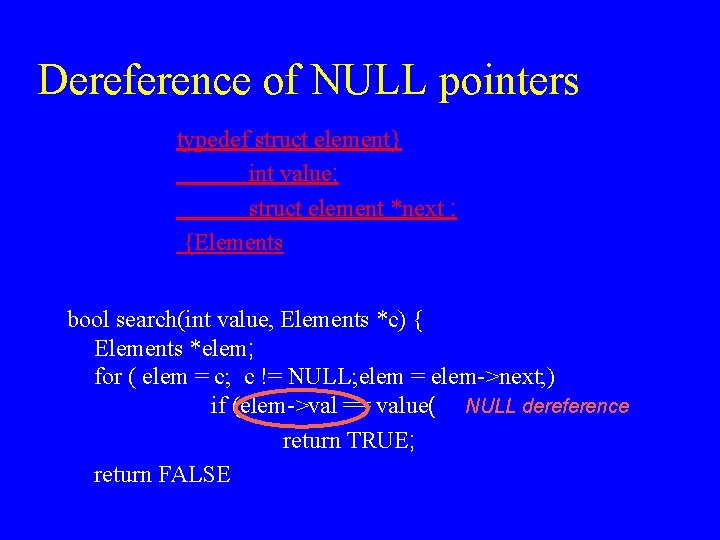
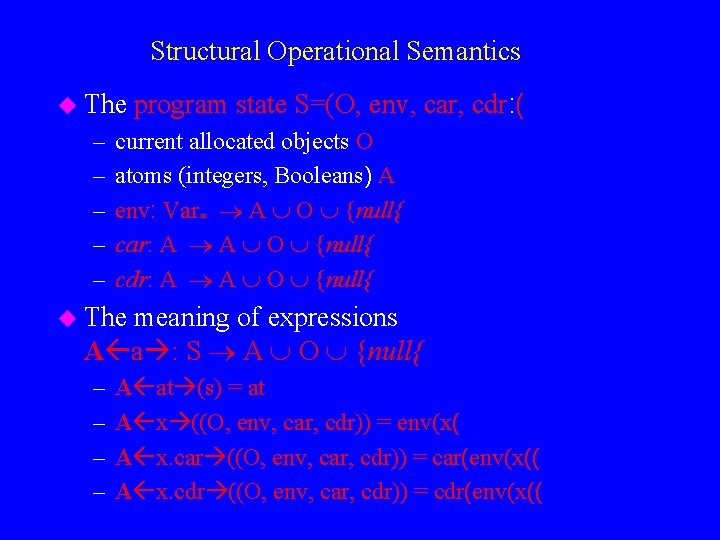
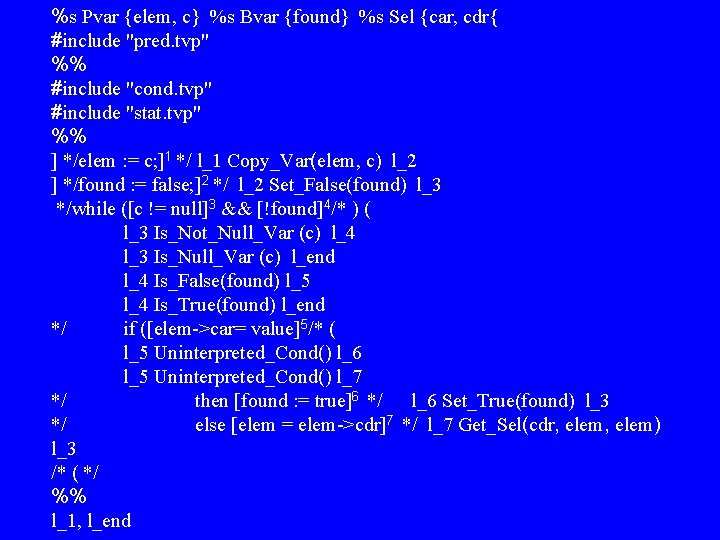
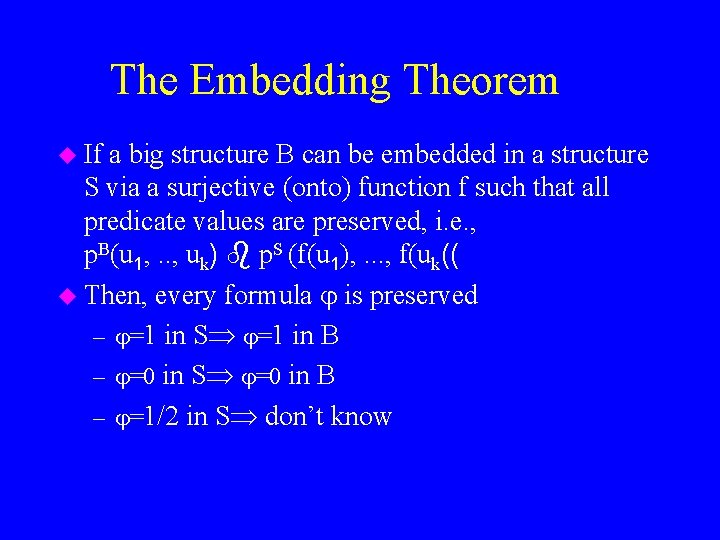
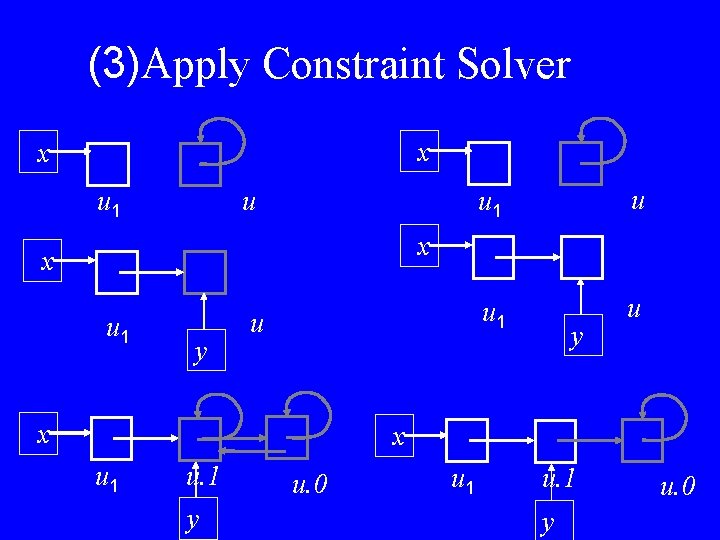
Structural Semantics for SWhile axioms ]assvsos] <x : = a, s=(O, e, car, cdr)> (O, e[x A a s], car, cdr( ]asscarsos] <x. car : = a, (O, e, car, cdr)> (O, e, car[e(x) A a s], cdr( ]asscdrsos] <x. cdr : = a, (O, e, car, cdr)> (O, e, car, cdr[e(x) A a s([ ]assmsos] <x : = malloc(), (O, e, car, cdr)> (O {n}, e[x n], car, cdr( ]skipsos] <skip, s> s where n O
![Structural Semantics for SWhile rules comp 1 sos S 1 s S 1 Structural Semantics for SWhile rules ]comp 1 sos] <S 1 , s> <S’ 1,](https://slidetodoc.com/presentation_image_h2/0e03ca33185dfafc6cc51f600f4f4e1d/image-11.jpg)
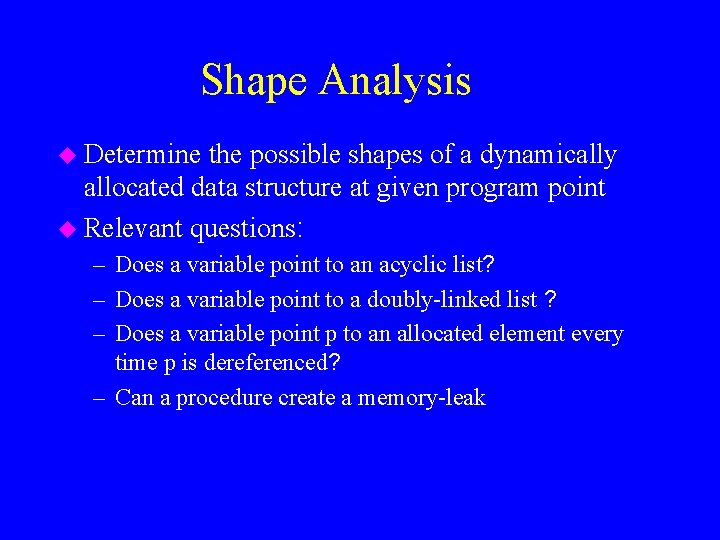
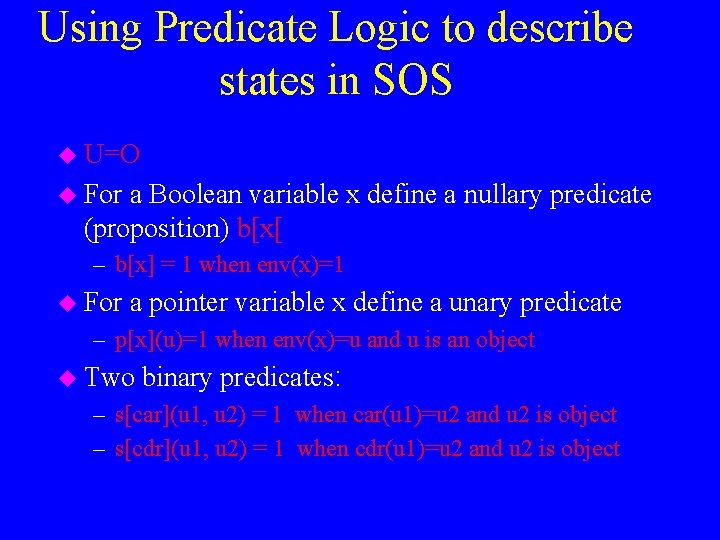
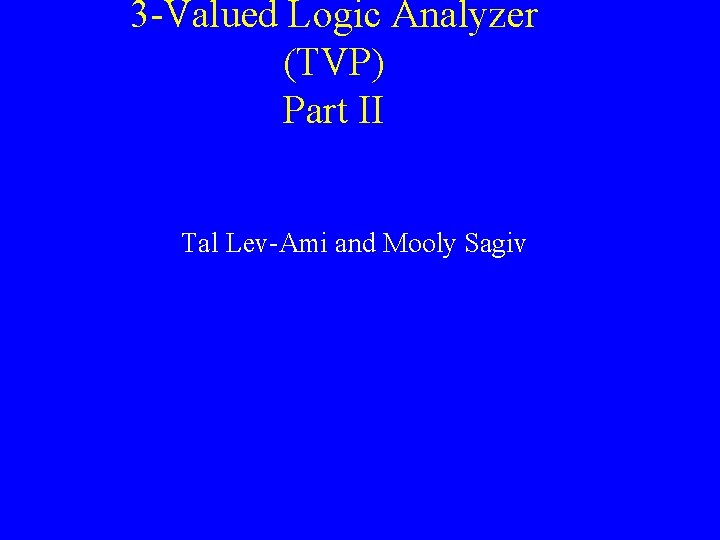
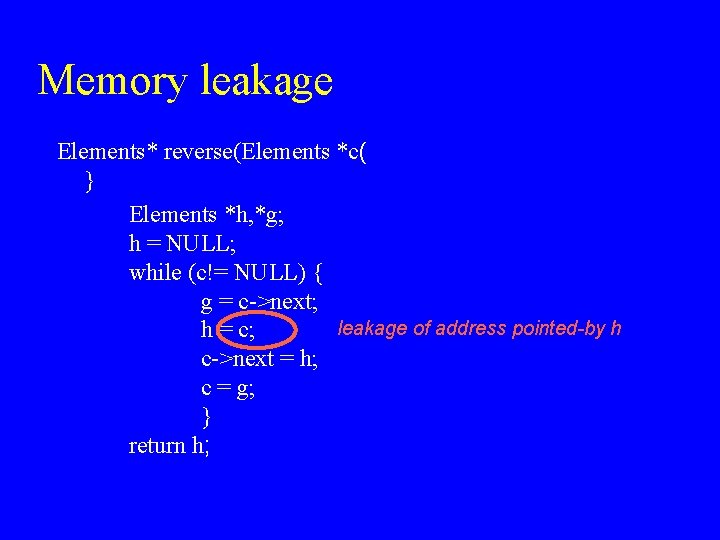
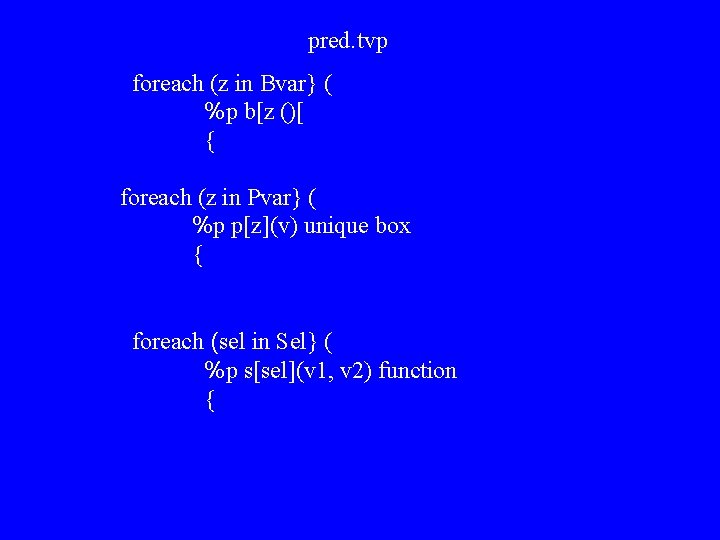
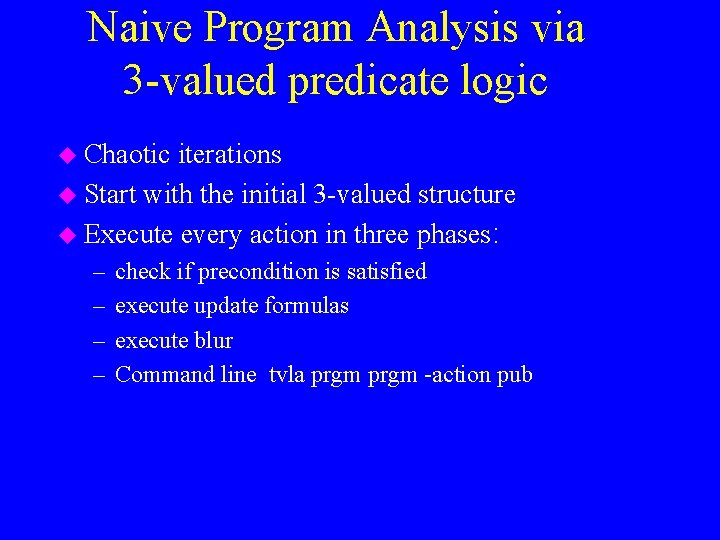
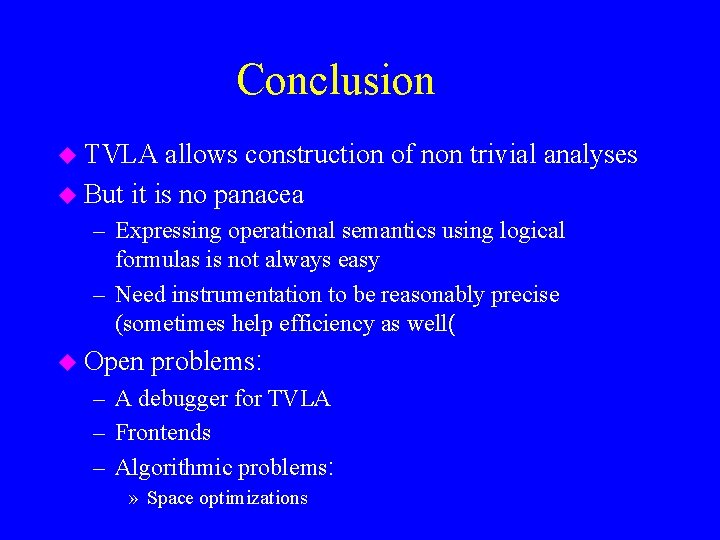
Structural Semantics for SWhile rules ]comp 1 sos] <S 1 , s> <S’ 1, s<’ > S 1; S 2, s> < S’ 1; S 2, s <’ ]comp 2 sos] <S 1 , s> s’ > S 1; S 2, s> < S 2, s <’ ]ifttsos] <if b then S 1 else S 2, s> <S 1, s < ]ifff if B b s=tt if sos] <if b then S 1 else S 2, s> <S 2, s < B b s=ff
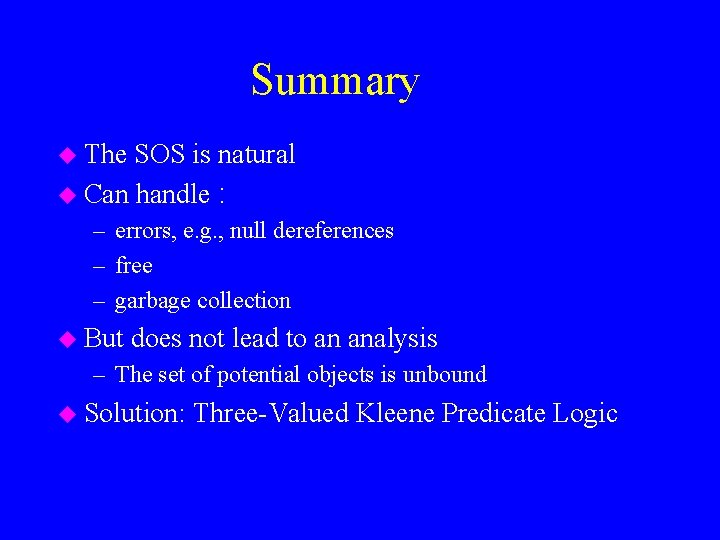
Summary u The SOS is natural u Can handle : – errors, e. g. , null dereferences – free – garbage collection u But does not lead to an analysis – The set of potential objects is unbound u Solution: Three-Valued Kleene Predicate Logic
Predicate Logic u Vocabulary – A finite set of predicate symbols P each with a fixed arity – A finite set of function symbols u Logical Structures S provide meaning for predicates – A set of individuals (nodes) U – PS: US {0, 1{ Formulas over express logical structure properties u First-Order
Using Predicate Logic to describe states in SOS u U=O u For a Boolean variable x define a nullary predicate (proposition) b[x[ – b[x] = 1 when env(x)=1 u For a pointer variable x define a unary predicate – p[x](u)=1 when env(x)=u and u is an object u Two binary predicates: – s[car](u 1, u 2) = 1 when car(u 1)=u 2 and u 2 is object – s[cdr](u 1, u 2) = 1 when cdr(u 1)=u 2 and u 2 is object
![Running Example elem c 1 found false 2 while c Running Example ]elem : = c; ]1 ]found : = false; ]2 while ([c](https://slidetodoc.com/presentation_image_h2/0e03ca33185dfafc6cc51f600f4f4e1d/image-15.jpg)
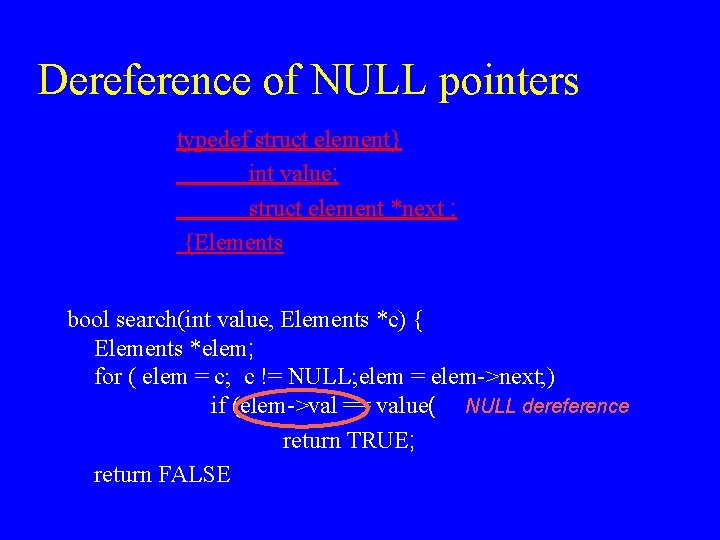
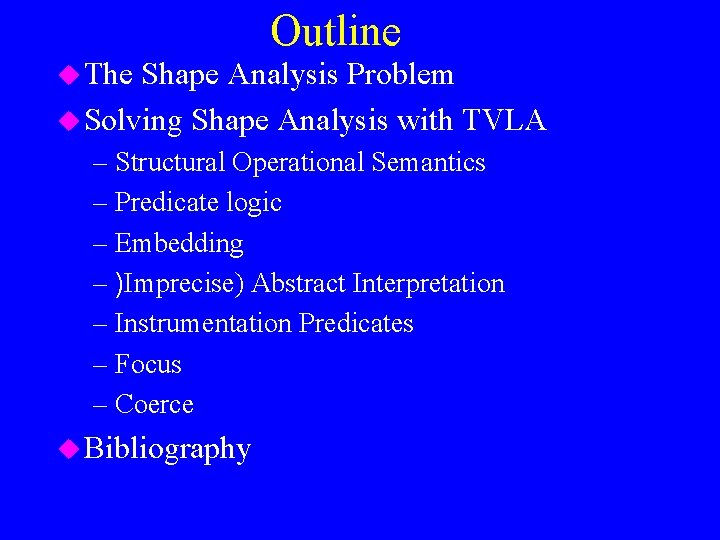
Running Example ]elem : = c; ]1 ]found : = false; ]2 while ([c != null]3 && [!found]4) ( if ([elem->car= value]5( then [found : = true]6 else [elem = elem->cdr]7 (
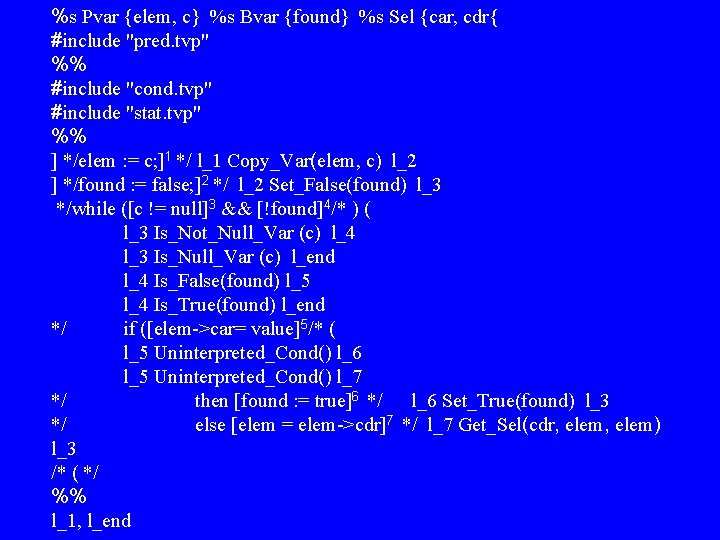
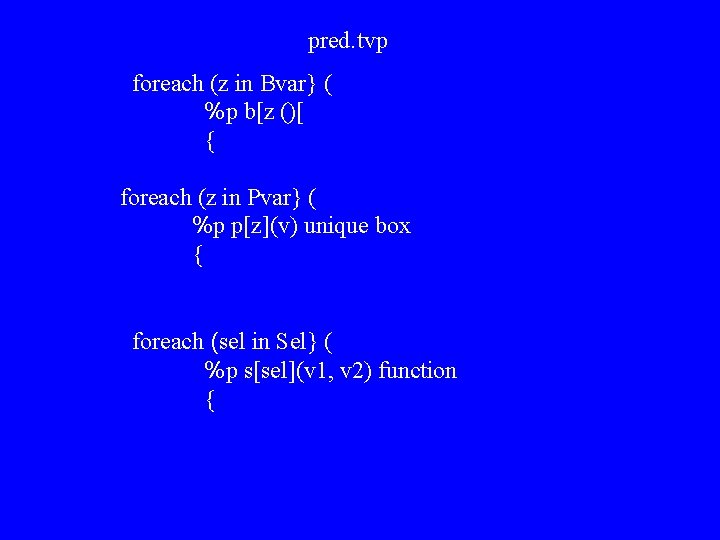
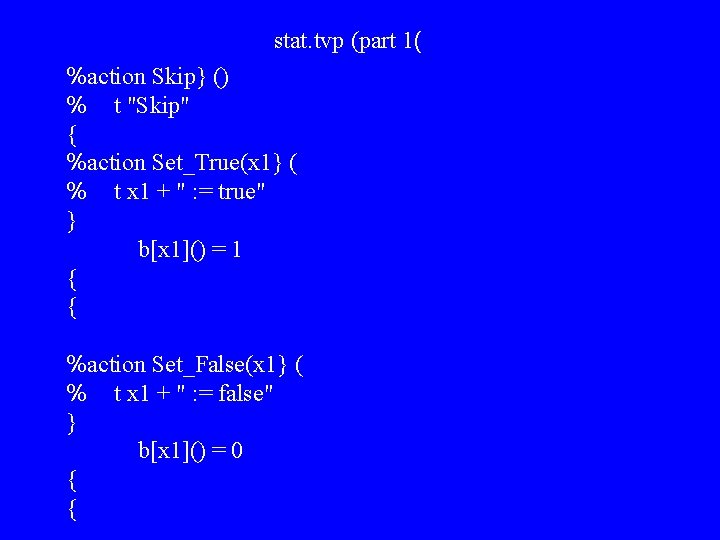
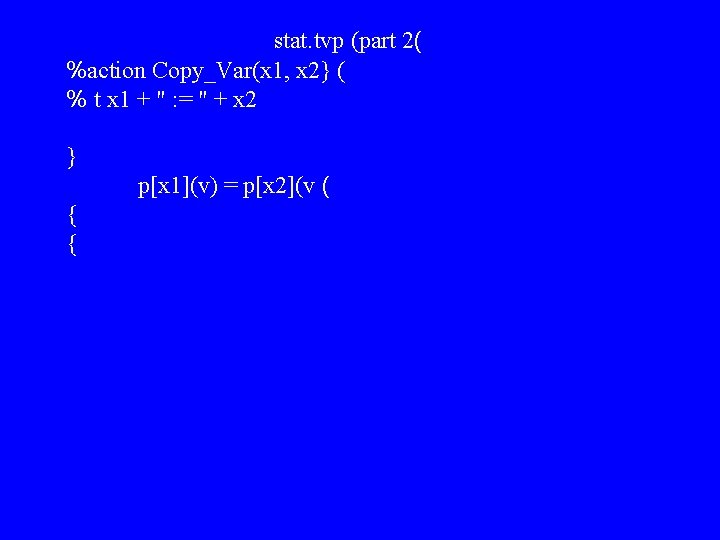
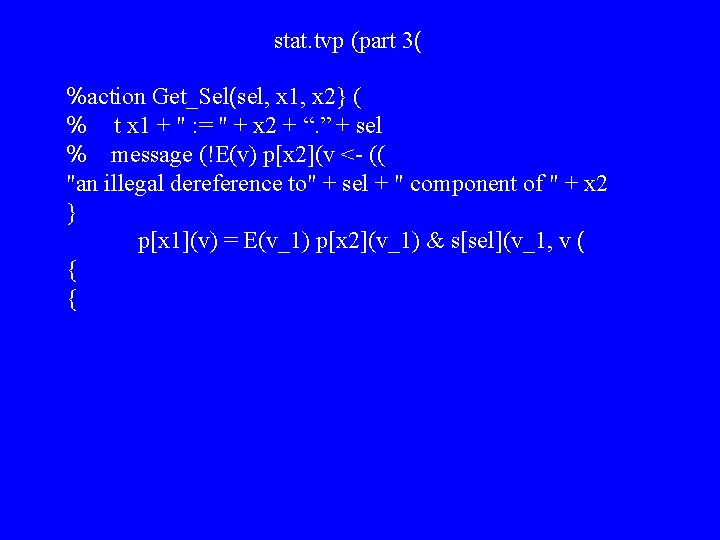
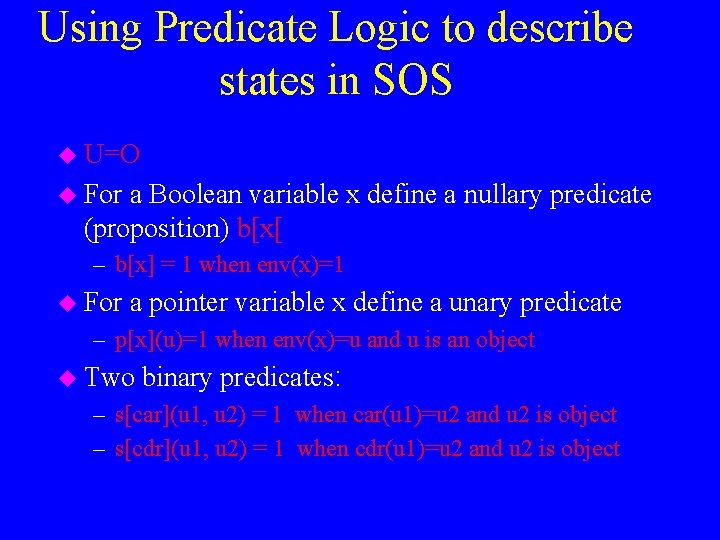
%s Pvar {elem, c} %s Bvar {found} %s Sel {car, cdr{ #include "pred. tvp" %% #include "cond. tvp" #include "stat. tvp" %% ] */elem : = c; ]1 */ l_1 Copy_Var(elem, c) l_2 ] */found : = false; ]2 */ l_2 Set_False(found) l_3 */while ([c != null]3 && [!found]4/* ) ( l_3 Is_Not_Null_Var (c) l_4 l_3 Is_Null_Var (c) l_end l_4 Is_False(found) l_5 l_4 Is_True(found) l_end */ if ([elem->car= value]5/* ( l_5 Uninterpreted_Cond() l_6 l_5 Uninterpreted_Cond() l_7 */ then [found : = true]6 */ l_6 Set_True(found) l_3 */ else [elem = elem->cdr]7 */ l_7 Get_Sel(cdr, elem) l_3 /* ( */ %% l_1, l_end
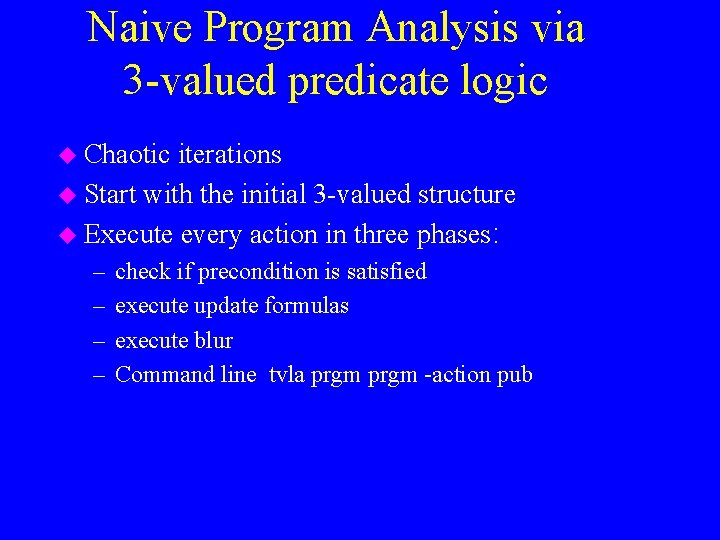
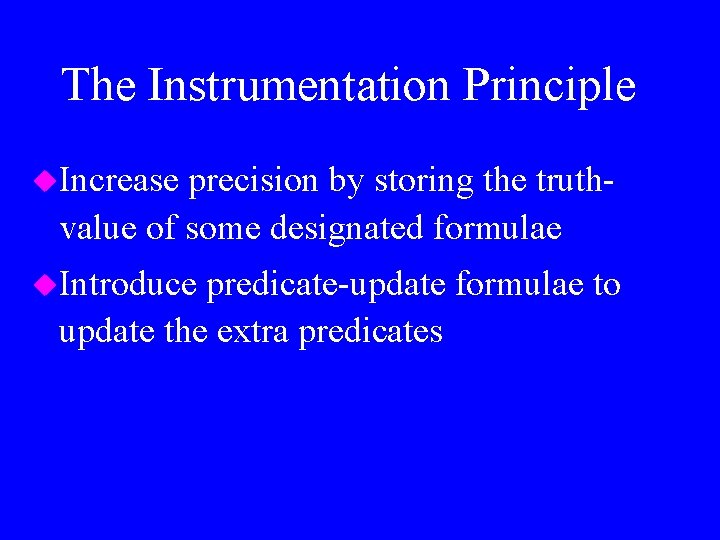
pred. tvp foreach (z in Bvar} ( %p b[z ()[ { foreach (z in Pvar} ( %p p[z](v) unique box { foreach (sel in Sel} ( %p s[sel](v 1, v 2) function {
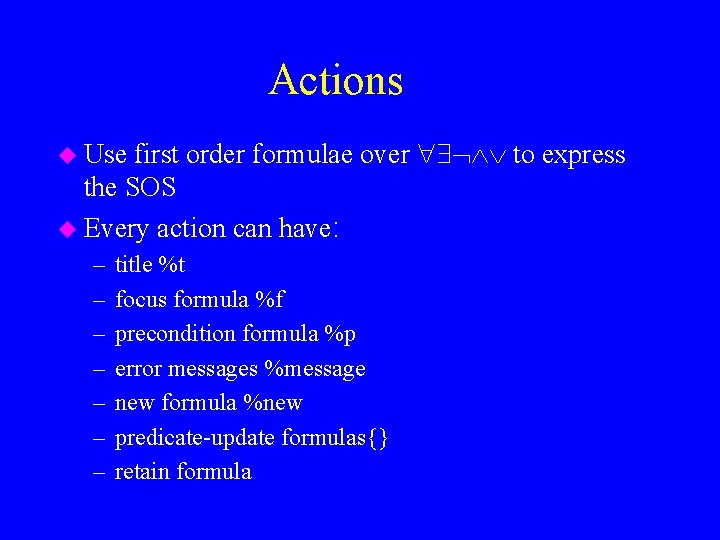
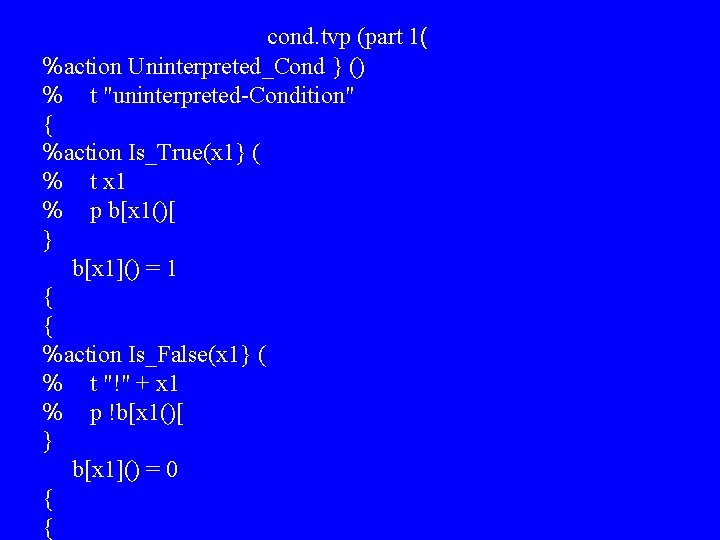
Actions first order formulae over to express the SOS u Every action can have: u Use – – – – title %t focus formula %f precondition formula %p error messages %message new formula %new predicate-update formulas{} retain formula
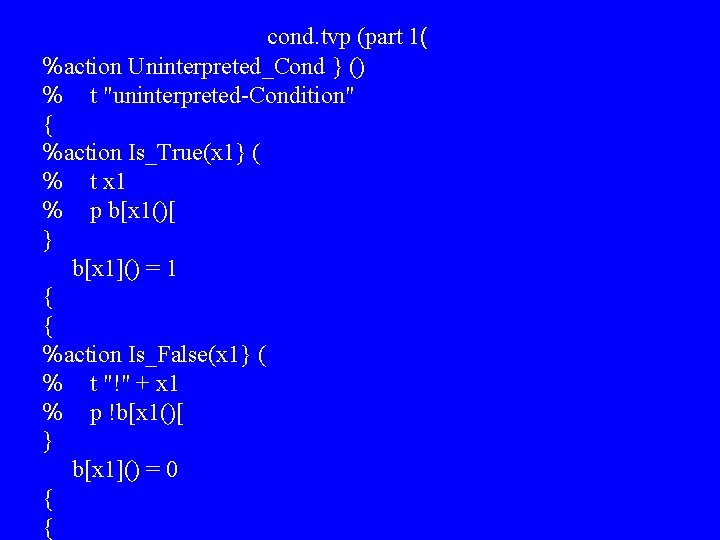
cond. tvp (part 1( %action Uninterpreted_Cond } () % t "uninterpreted-Condition" { %action Is_True(x 1} ( % t x 1 % p b[x 1()[ } b[x 1]() = 1 { { %action Is_False(x 1} ( % t "!" + x 1 % p !b[x 1()[ } b[x 1]() = 0 { {
cond. tvp (part 2( %action Is_Not_Null_Var(x 1} ( % t x 1 + " != null" % p E(v) p[x 1](v( { %action Is_Null_Var(x 1} ( % t x 1 + " = null" % p !(E(v) p[x 1](v(( {
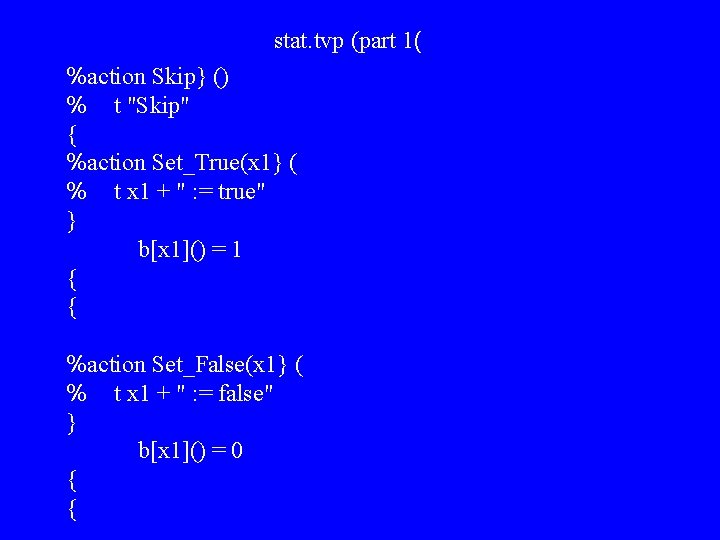
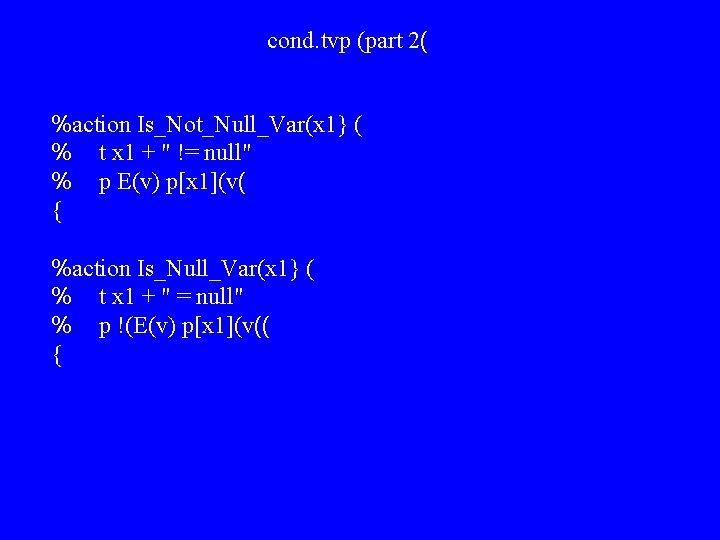
stat. tvp (part 1( %action Skip} () % t "Skip" { %action Set_True(x 1} ( % t x 1 + " : = true" } b[x 1]() = 1 { { %action Set_False(x 1} ( % t x 1 + " : = false" } b[x 1]() = 0 { {
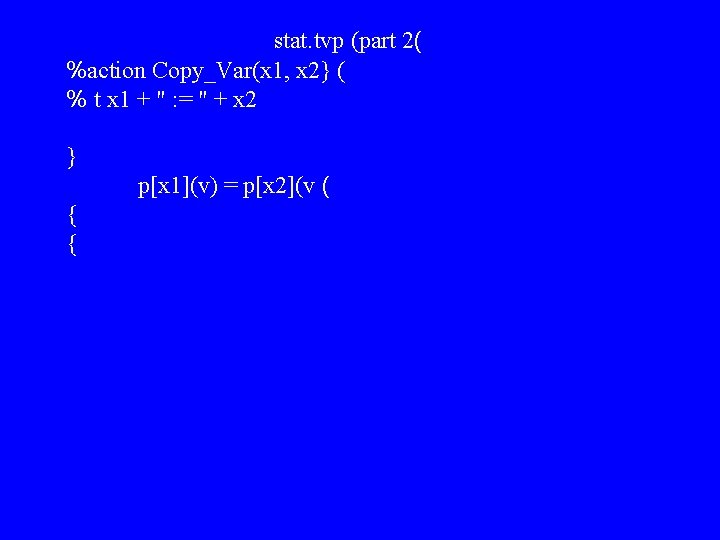
stat. tvp (part 2( %action Copy_Var(x 1, x 2} ( % t x 1 + " : = " + x 2 } p[x 1](v) = p[x 2](v ( { {
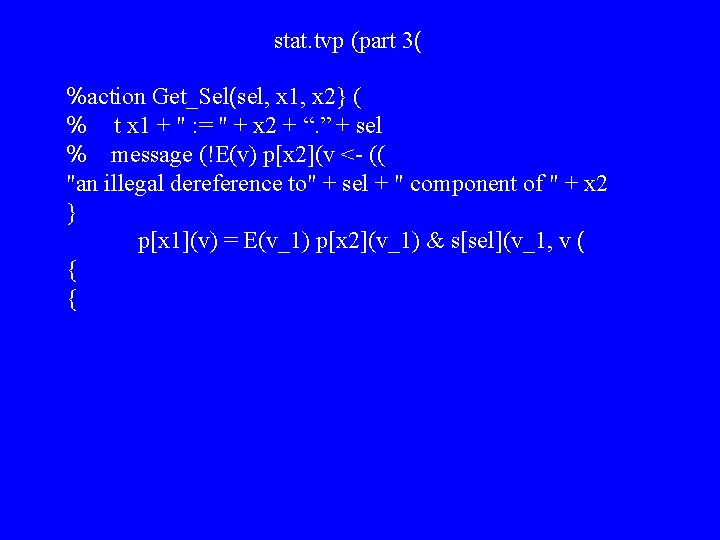
stat. tvp (part 3( %action Get_Sel(sel, x 1, x 2} ( % t x 1 + " : = " + x 2 + “. ” + sel % message (!E(v) p[x 2](v <- (( "an illegal dereference to" + sel + " component of " + x 2 } p[x 1](v) = E(v_1) p[x 2](v_1) & s[sel](v_1, v ( { {
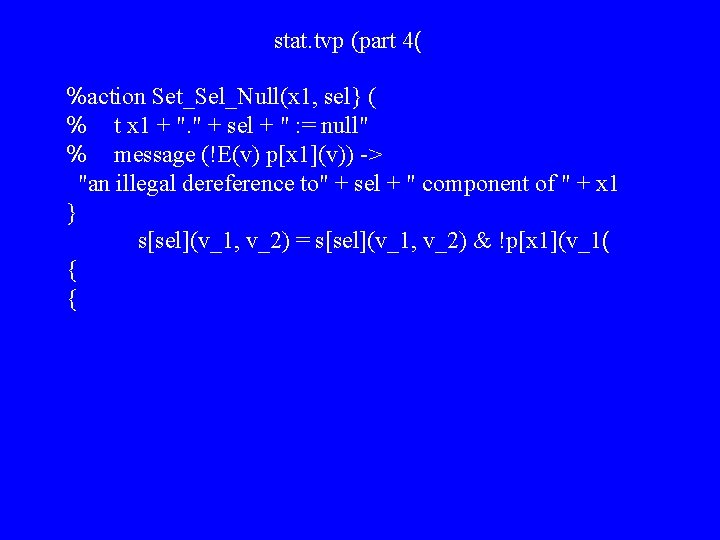
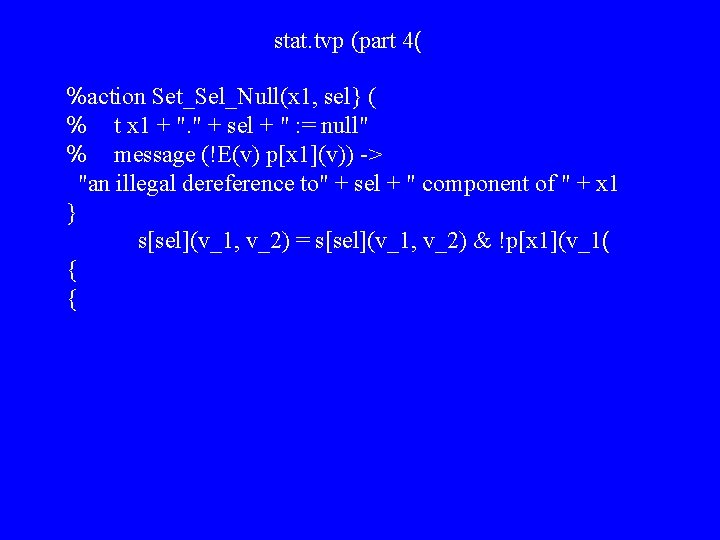
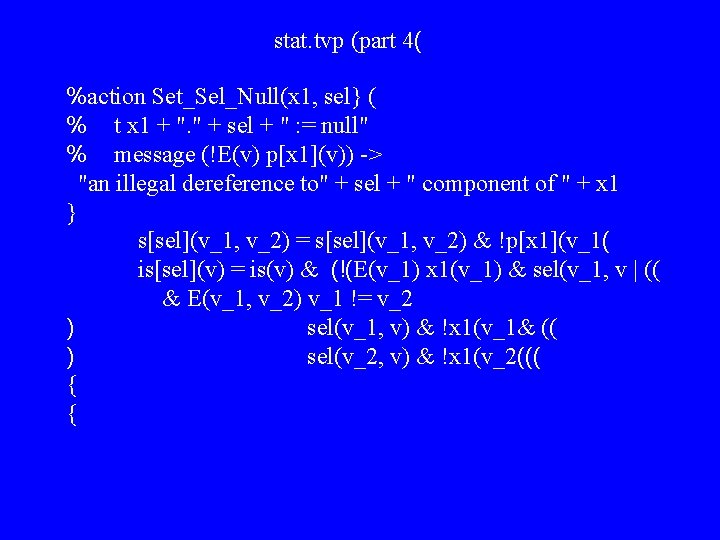
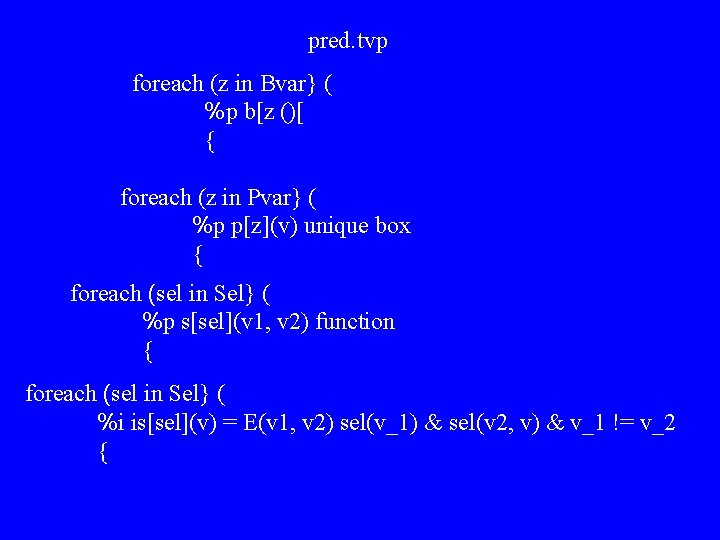
stat. tvp (part 4( %action Set_Sel_Null(x 1, sel} ( % t x 1 + ". " + sel + " : = null" % message (!E(v) p[x 1](v)) -> "an illegal dereference to" + sel + " component of " + x 1 } s[sel](v_1, v_2) = s[sel](v_1, v_2) & !p[x 1](v_1( { {
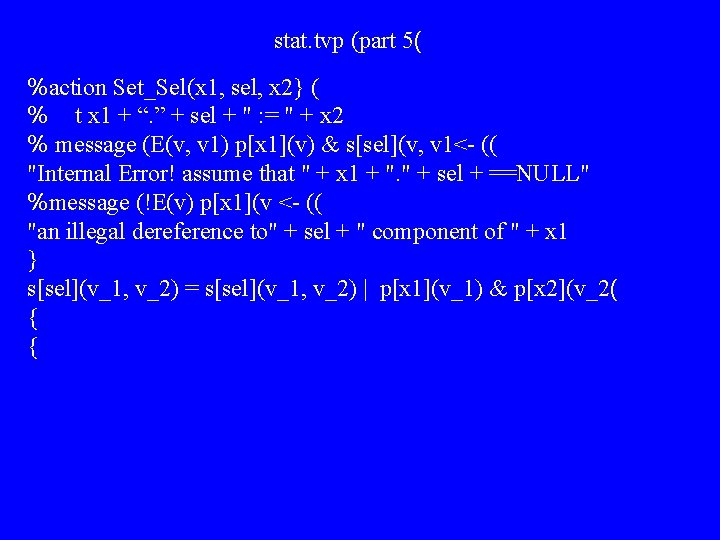
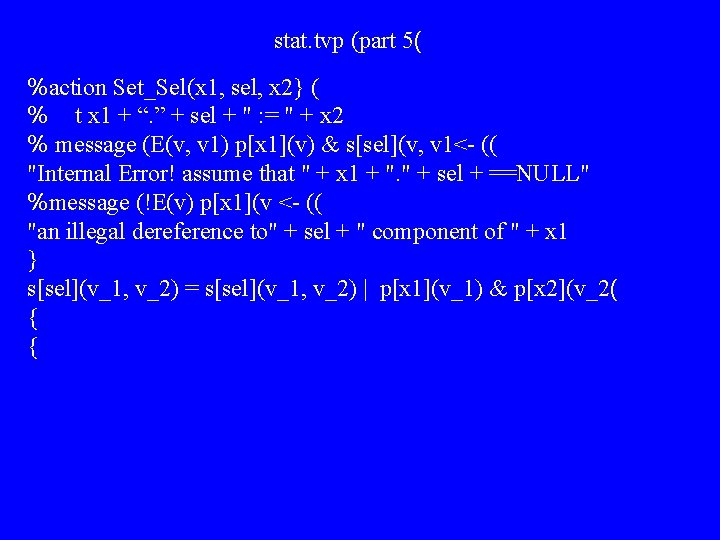
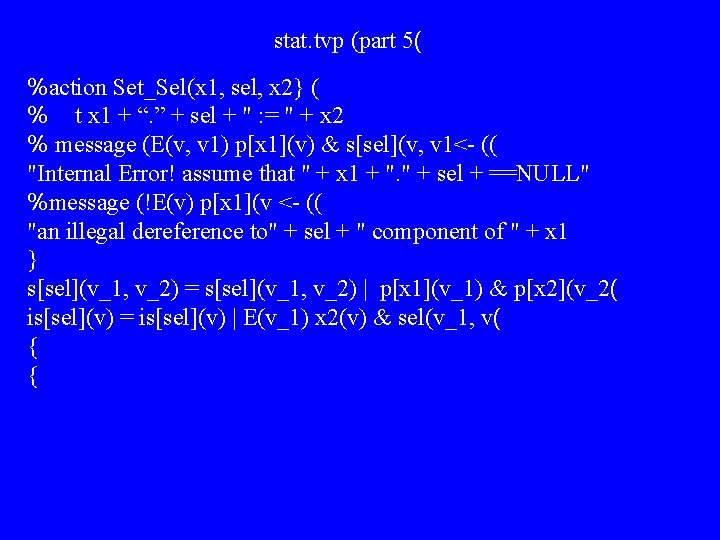
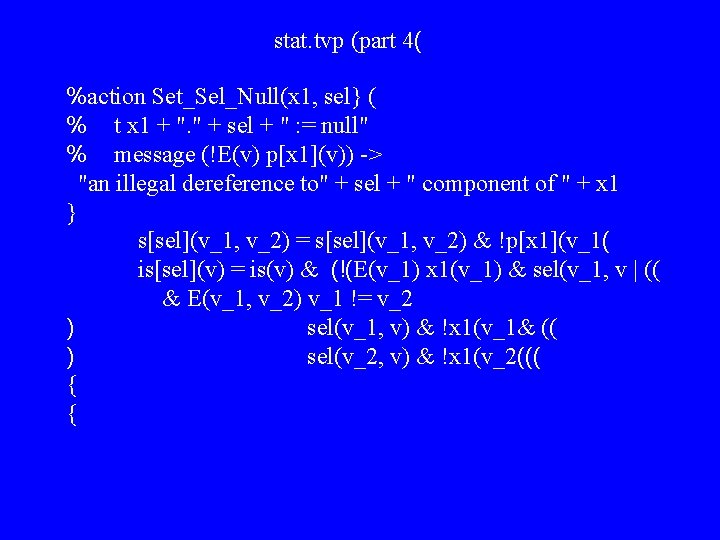
stat. tvp (part 5( %action Set_Sel(x 1, sel, x 2} ( % t x 1 + “. ” + sel + " : = " + x 2 % message (E(v, v 1) p[x 1](v) & s[sel](v, v 1<- (( "Internal Error! assume that " + x 1 + ". " + sel + ==NULL" %message (!E(v) p[x 1](v <- (( "an illegal dereference to" + sel + " component of " + x 1 } s[sel](v_1, v_2) = s[sel](v_1, v_2) | p[x 1](v_1) & p[x 2](v_2( { {
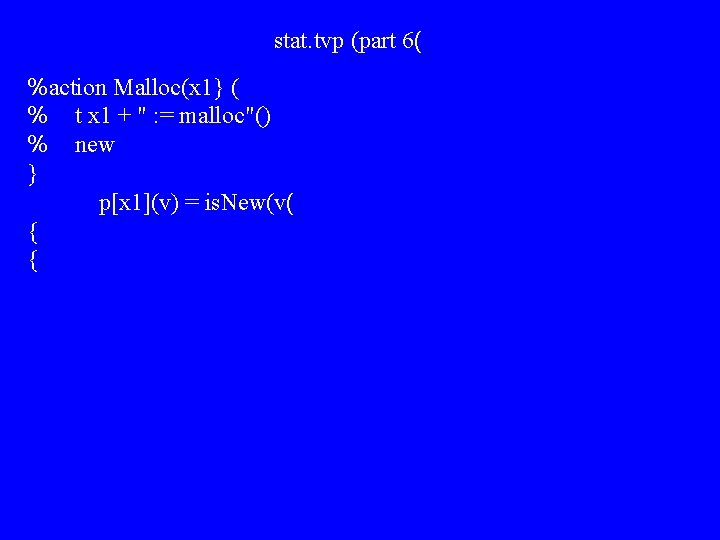
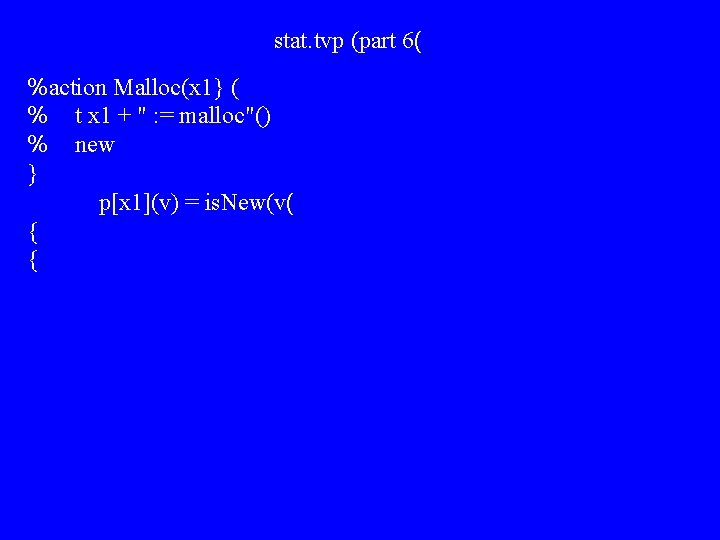
stat. tvp (part 6( %action Malloc(x 1} ( % t x 1 + " : = malloc"() % new } p[x 1](v) = is. New(v( { {
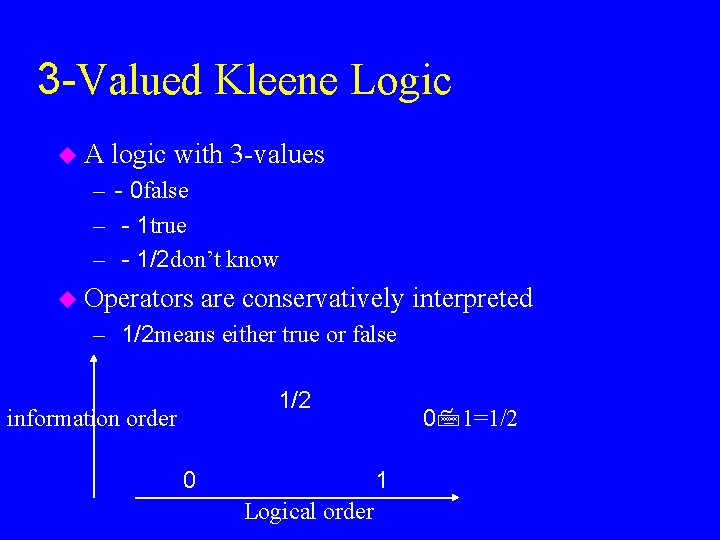
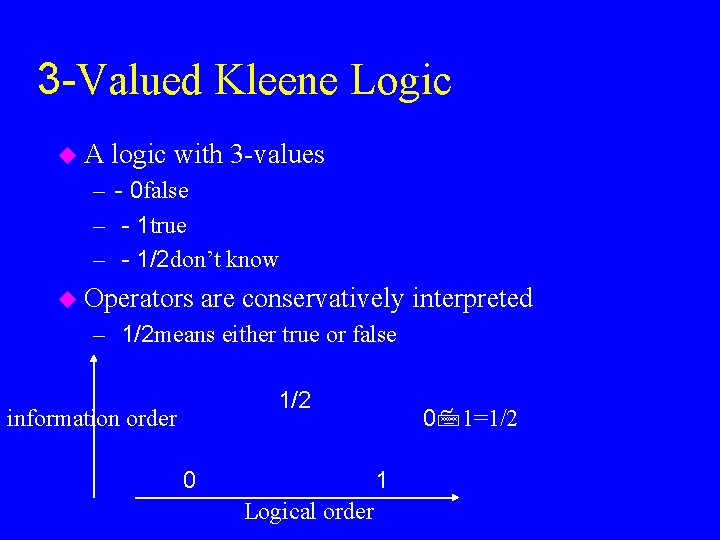
3 -Valued Kleene Logic u. A logic with 3 -values – - 0 false – - 1 true – - 1/2 don’t know u Operators are conservatively interpreted – 1/2 means either true or false 1/2 information order 0 0 1=1/2 1 Logical order
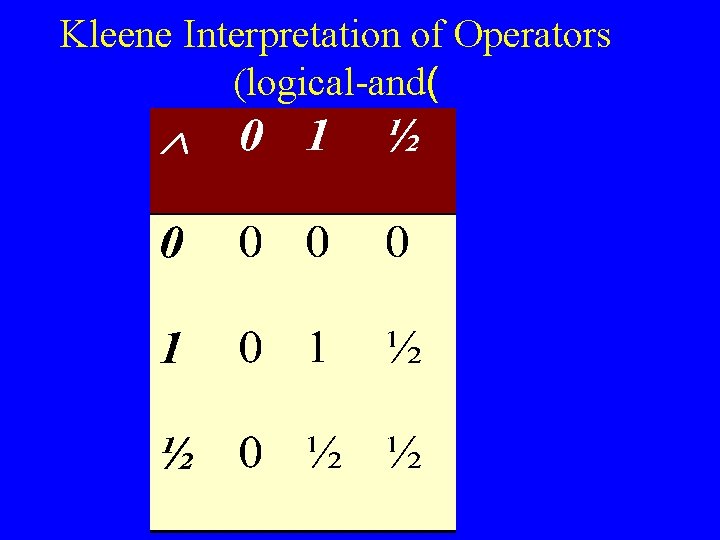
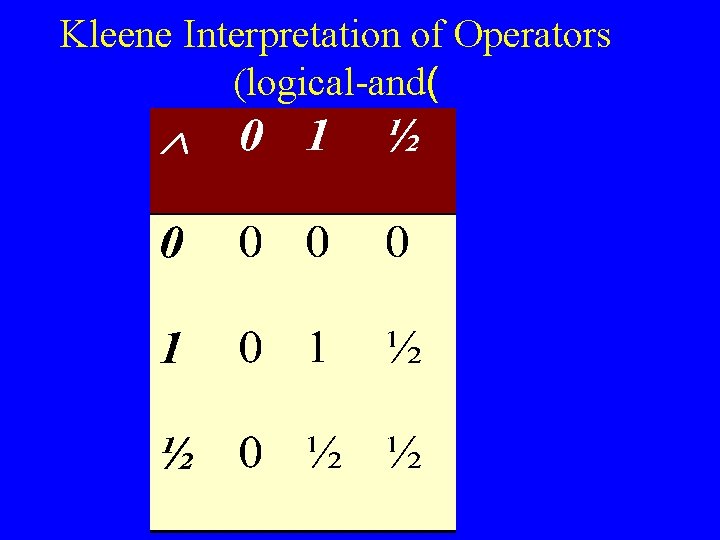
Kleene Interpretation of Operators (logical-and(
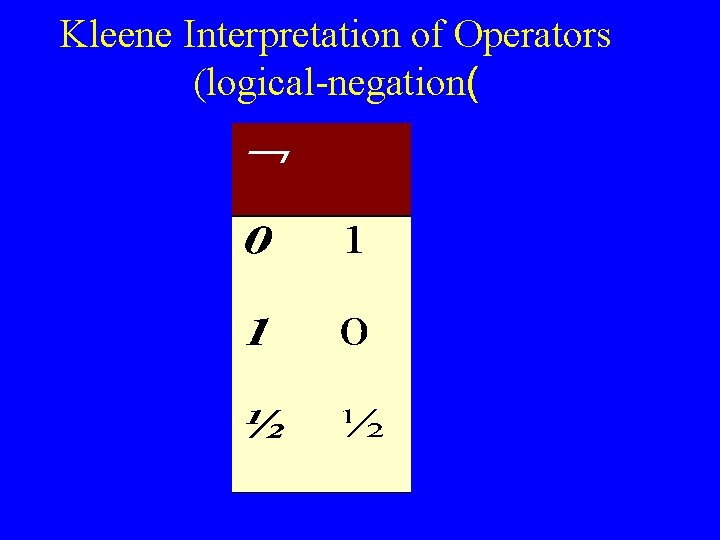
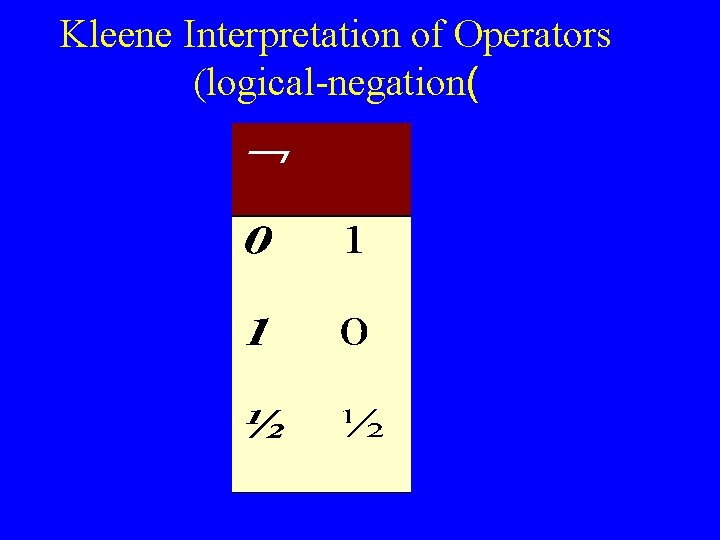
Kleene Interpretation of Operators (logical-negation(
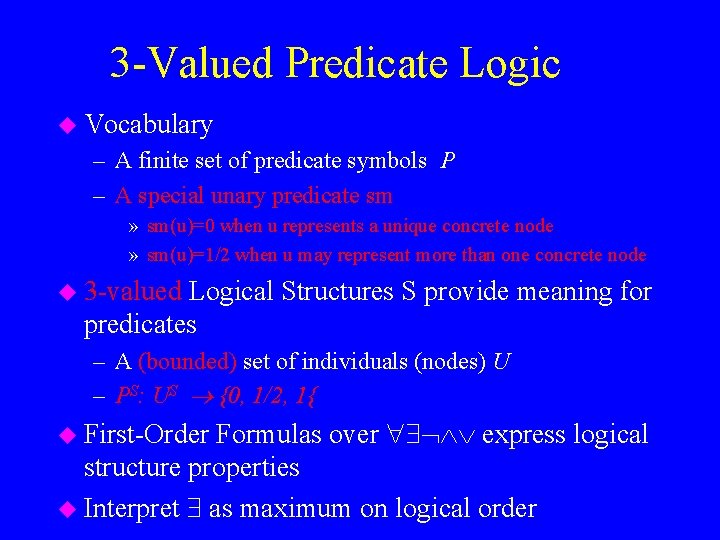
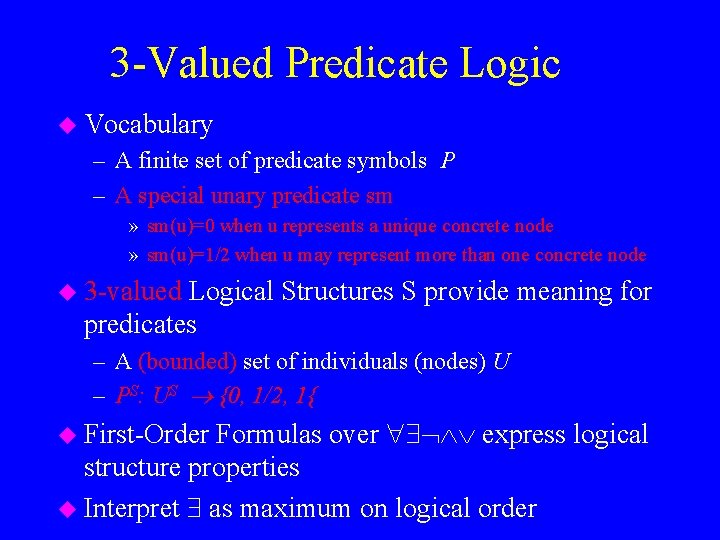
3 -Valued Predicate Logic u Vocabulary – A finite set of predicate symbols P – A special unary predicate sm » sm(u)=0 when u represents a unique concrete node » sm(u)=1/2 when u may represent more than one concrete node u 3 -valued Logical Structures S provide meaning for predicates – A (bounded) set of individuals (nodes) U – PS: US {0, 1/2, 1{ Formulas over express logical structure properties u Interpret as maximum on logical order u First-Order
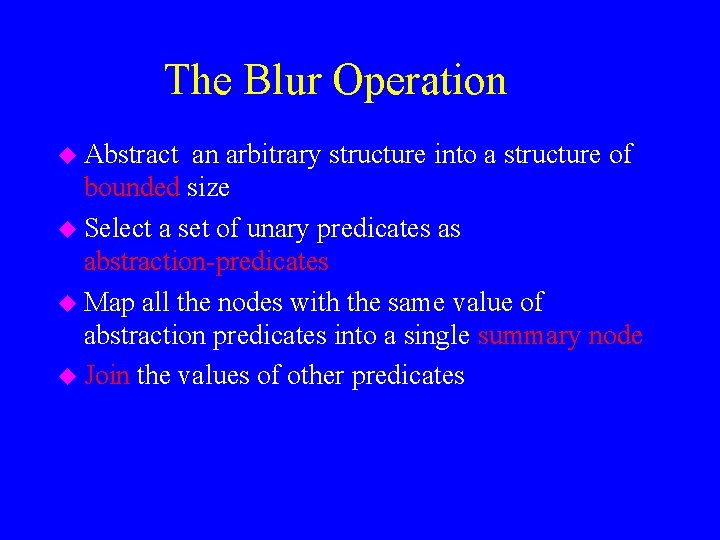
The Blur Operation u Abstract an arbitrary structure into a structure of bounded size u Select a set of unary predicates as abstraction-predicates u Map all the nodes with the same value of abstraction predicates into a single summary node u Join the values of other predicates
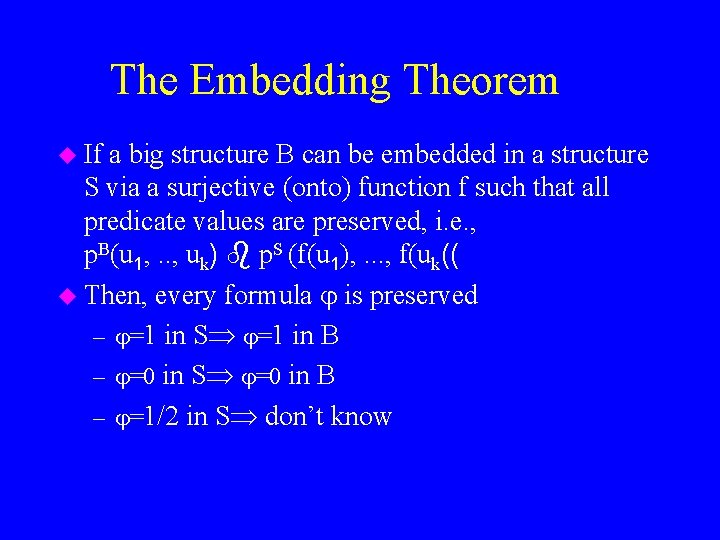
The Embedding Theorem u If a big structure B can be embedded in a structure S via a surjective (onto) function f such that all predicate values are preserved, i. e. , p. B(u 1, . . , uk) p. S (f(u 1), . . . , f(uk(( u Then, every formula is preserved – =1 in S =1 in B – =0 in S =0 in B – =1/2 in S don’t know
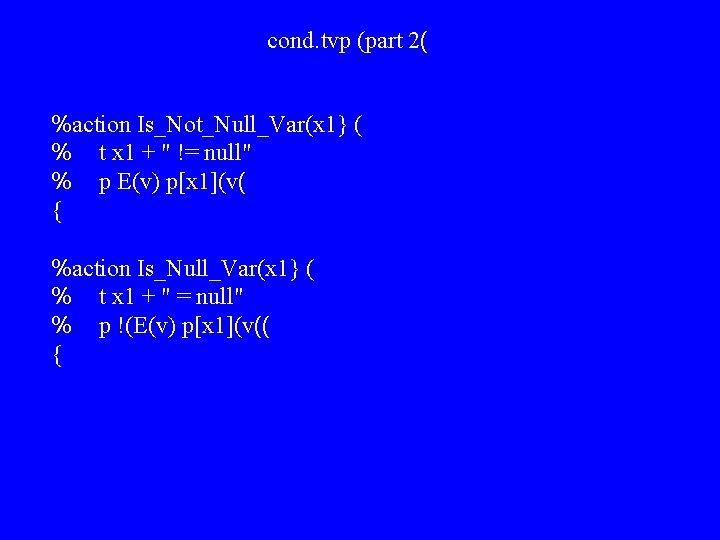
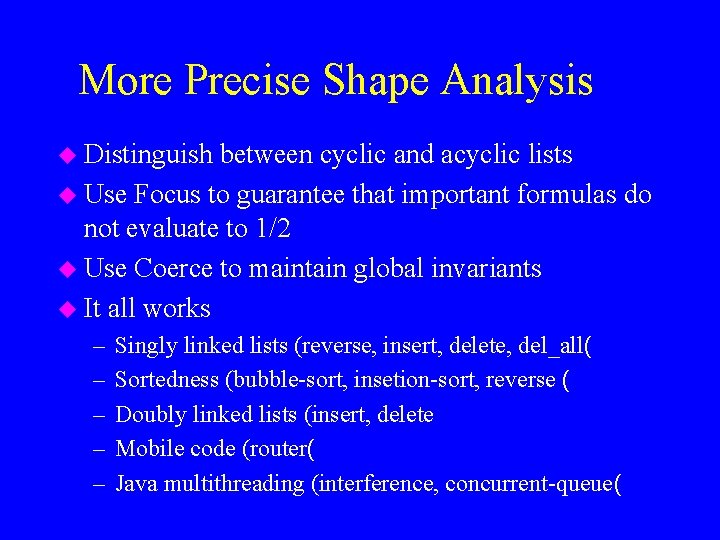
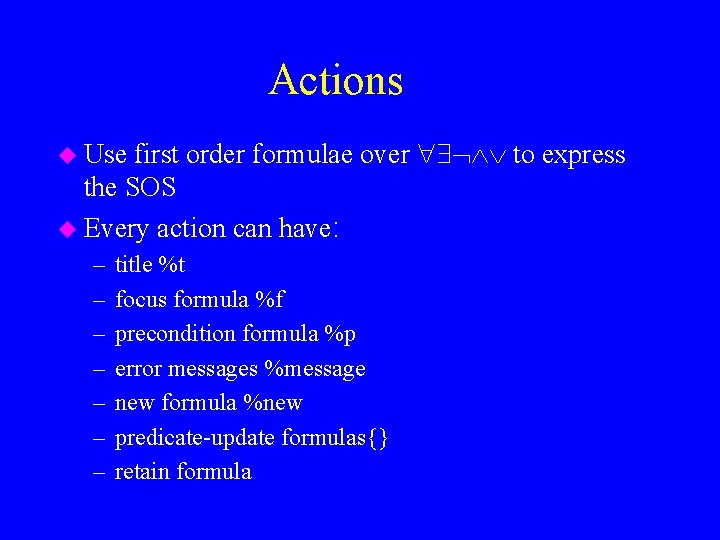
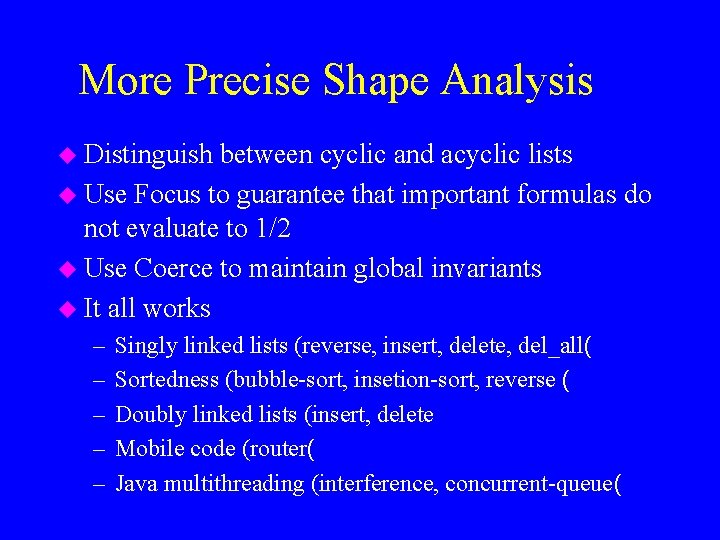
Naive Program Analysis via 3 -valued predicate logic u Chaotic iterations u Start with the initial 3 -valued structure u Execute every action in three phases: – – check if precondition is satisfied execute update formulas execute blur Command line tvla prgm -action pub
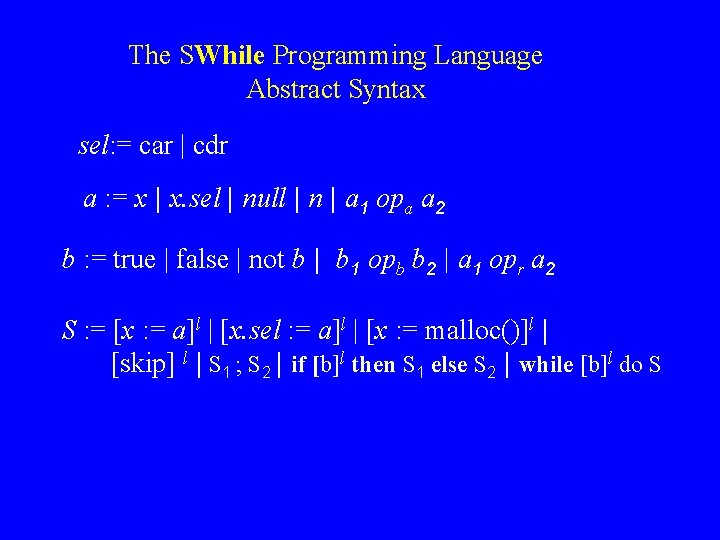
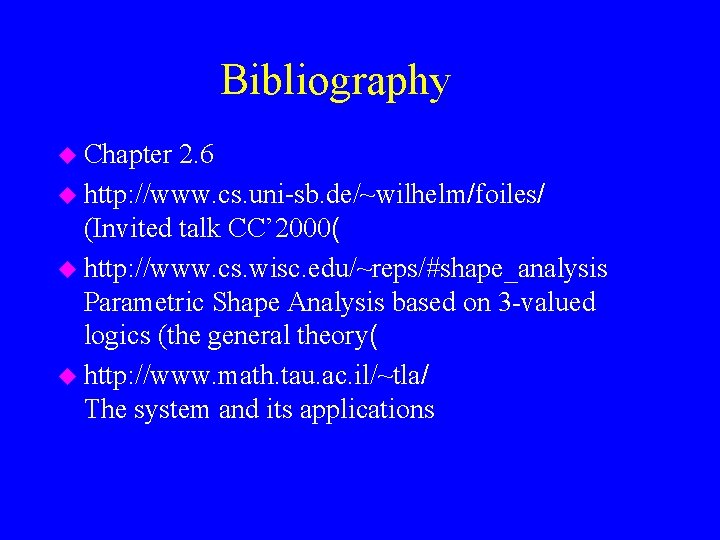
![prgm tvs n u u 0 p sm u 12 scdr prgm. tvs %n = {u, u 0{ %p} = sm = {u: 1/2{ s[cdr]](https://slidetodoc.com/presentation_image_h2/0e03ca33185dfafc6cc51f600f4f4e1d/image-34.jpg)
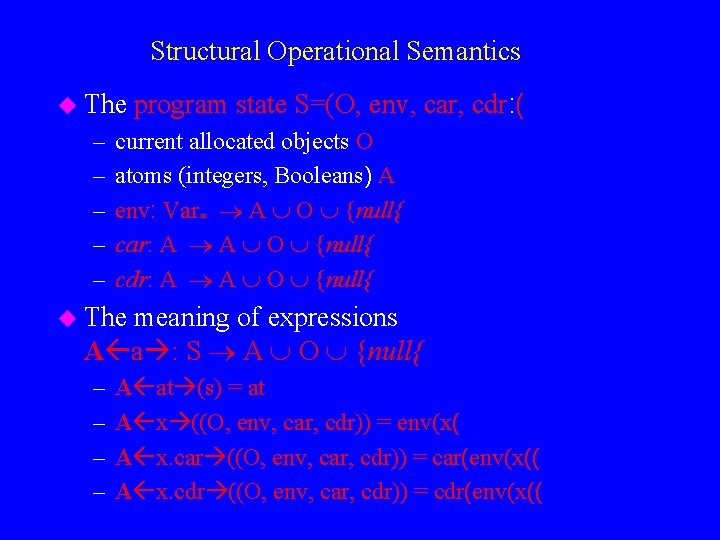
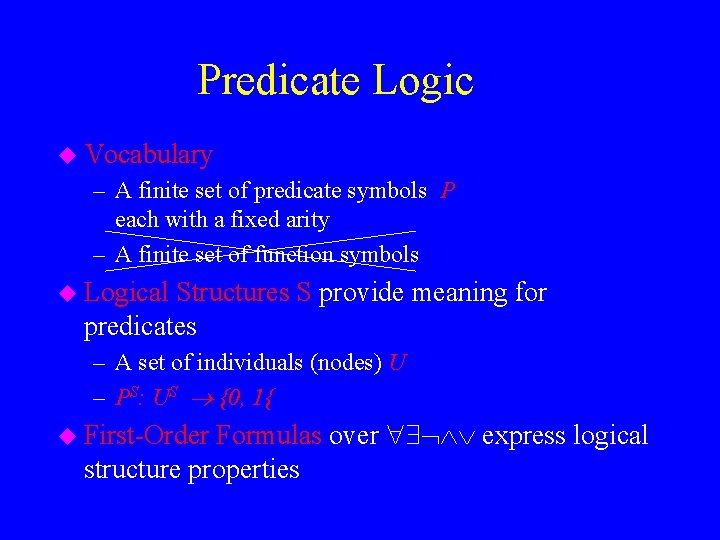
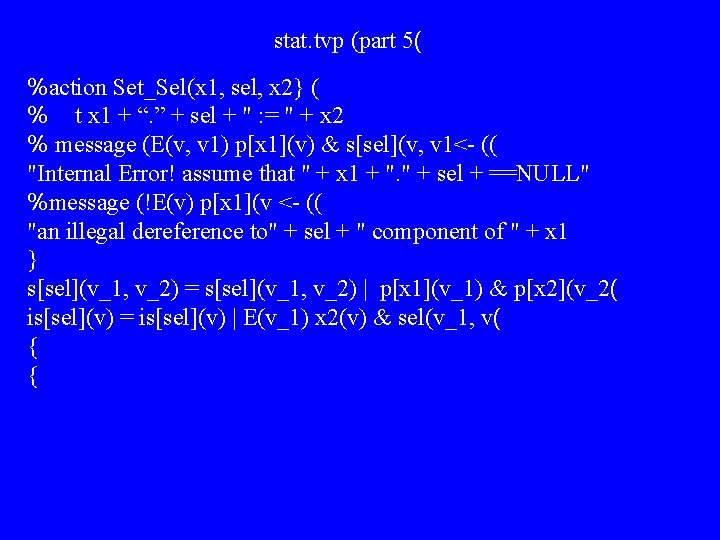
prgm. tvs %n = {u, u 0{ %p} = sm = {u: 1/2{ s[cdr] = {u->u: 1/2, u 0 ->u: 1/2{ p[c] = {u 0{ {
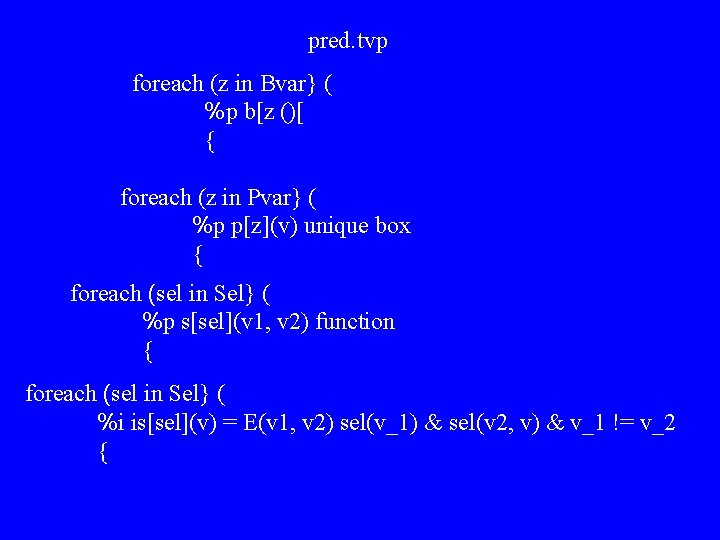
More Precise Shape Analysis u Distinguish between cyclic and acyclic lists u Use Focus to guarantee that important formulas do not evaluate to 1/2 u Use Coerce to maintain global invariants u It all works – – – Singly linked lists (reverse, insert, delete, del_all( Sortedness (bubble-sort, insetion-sort, reverse ( Doubly linked lists (insert, delete Mobile code (router( Java multithreading (interference, concurrent-queue(
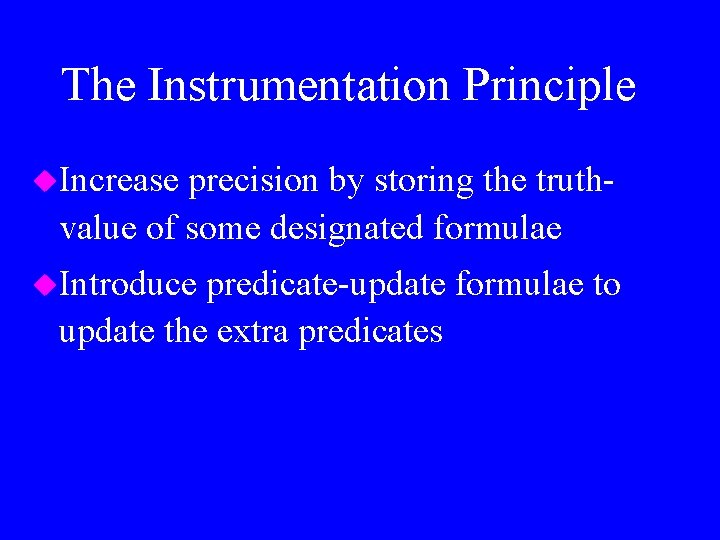
The Instrumentation Principle u. Increase precision by storing the truthvalue of some designated formulae u. Introduce predicate-update formulae to update the extra predicates
 = v 1, v 2: cdr(v 1, v) cdr(v 2,](https://slidetodoc.com/presentation_image_h2/0e03ca33185dfafc6cc51f600f4f4e1d/image-37.jpg)
Example: Heap Sharing is[cdr](v) = v 1, v 2: cdr(v 1, v) cdr(v 2, v) v 1 v 2 x 31 is = 0 71 is = 0 x u 1 is = 0 u is = 0 91 is = 0
 = v 1, v 2: cdr(v 1, v) cdr(v 2,](https://slidetodoc.com/presentation_image_h2/0e03ca33185dfafc6cc51f600f4f4e1d/image-38.jpg)
Example: Heap Sharing is[cdr](v) = v 1, v 2: cdr(v 1, v) cdr(v 2, v) v 1 v 2 x 31 71 is = 0 is = 10 x u 1 91 is = 0 u is = 0 is = 1 is = 0
pred. tvp foreach (z in Bvar} ( %p b[z ()[ { foreach (z in Pvar} ( %p p[z](v) unique box { foreach (sel in Sel} ( %p s[sel](v 1, v 2) function { foreach (sel in Sel} ( %i is[sel](v) = E(v 1, v 2) sel(v_1) & sel(v 2, v) & v_1 != v_2 {
stat. tvp (part 4( %action Set_Sel_Null(x 1, sel} ( % t x 1 + ". " + sel + " : = null" % message (!E(v) p[x 1](v)) -> "an illegal dereference to" + sel + " component of " + x 1 } s[sel](v_1, v_2) = s[sel](v_1, v_2) & !p[x 1](v_1( is[sel](v) = is(v) & (!(E(v_1) x 1(v_1) & sel(v_1, v | (( & E(v_1, v_2) v_1 != v_2 ) sel(v_1, v) & !x 1(v_1& (( ) sel(v_2, v) & !x 1(v_2((( { {
stat. tvp (part 5( %action Set_Sel(x 1, sel, x 2} ( % t x 1 + “. ” + sel + " : = " + x 2 % message (E(v, v 1) p[x 1](v) & s[sel](v, v 1<- (( "Internal Error! assume that " + x 1 + ". " + sel + ==NULL" %message (!E(v) p[x 1](v <- (( "an illegal dereference to" + sel + " component of " + x 1 } s[sel](v_1, v_2) = s[sel](v_1, v_2) | p[x 1](v_1) & p[x 2](v_2( is[sel](v) = is[sel](v) | E(v_1) x 2(v) & sel(v_1, v( { {
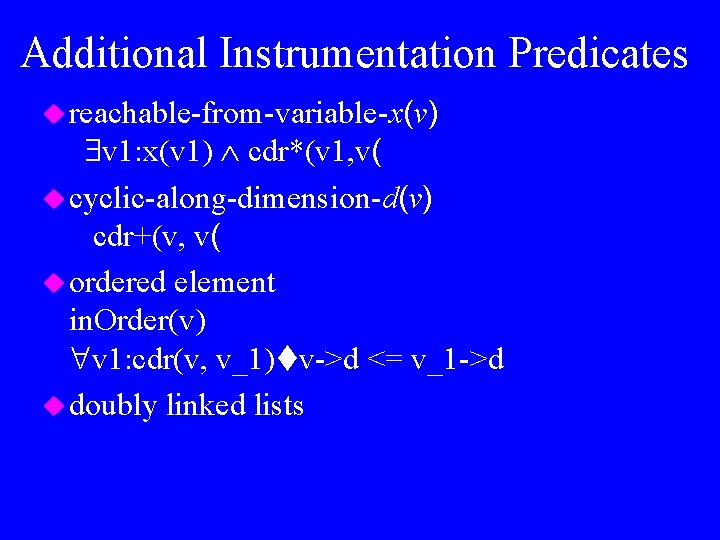
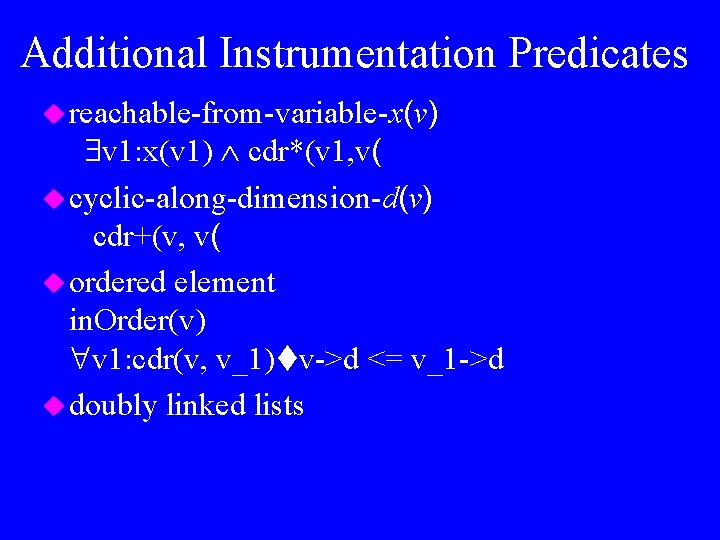
Additional Instrumentation Predicates u reachable-from-variable-x(v) v 1: x(v 1) cdr*(v 1, v( u cyclic-along-dimension-d(v) cdr+(v, v( u ordered element in. Order(v) v 1: cdr(v, v_1) v->d <= v_1 ->d u doubly linked lists
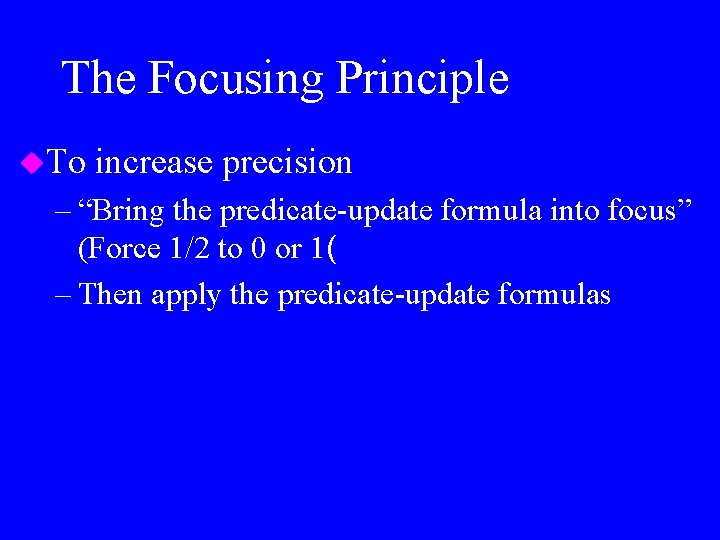
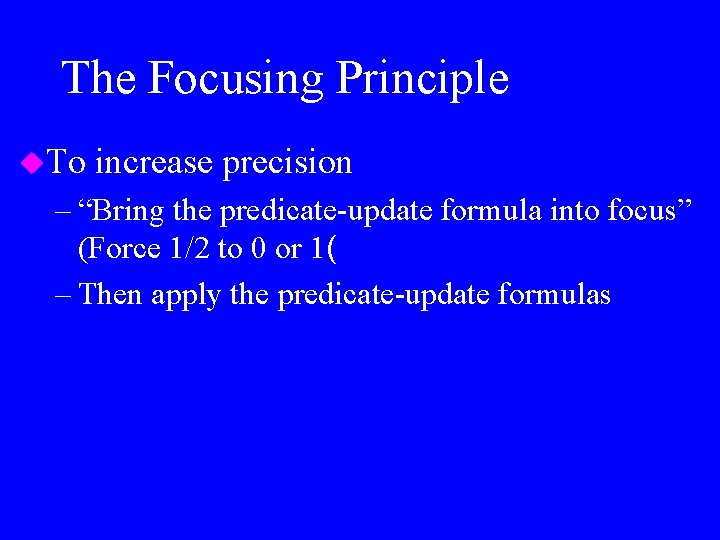
The Focusing Principle u. To increase precision – “Bring the predicate-update formula into focus” (Force 1/2 to 0 or 1( – Then apply the predicate-update formulas
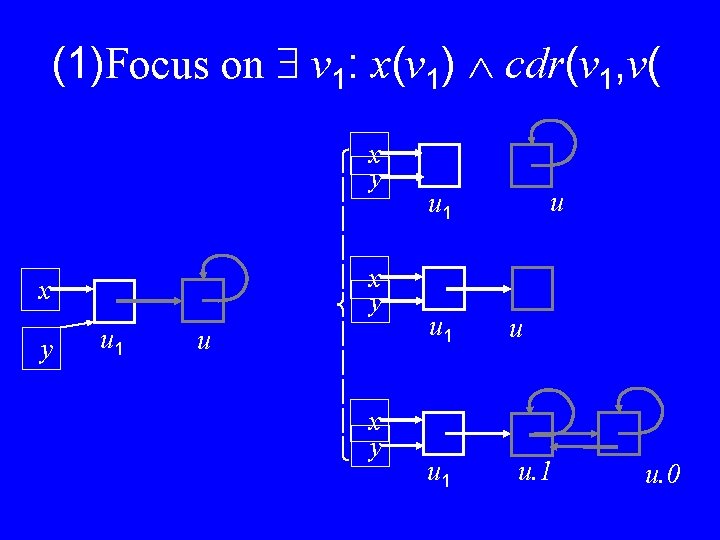
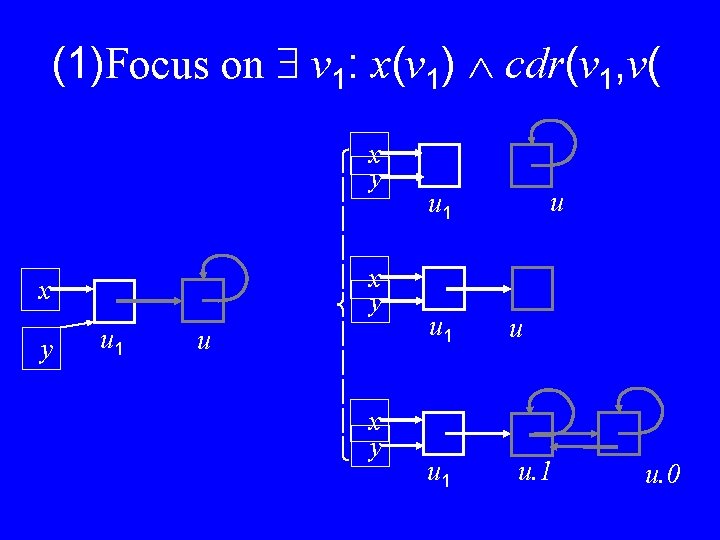
(1)Focus on v 1: x(v 1) cdr(v 1, v( x y u 1 u x y x y u u 1 u 1 u u. 1 u. 0
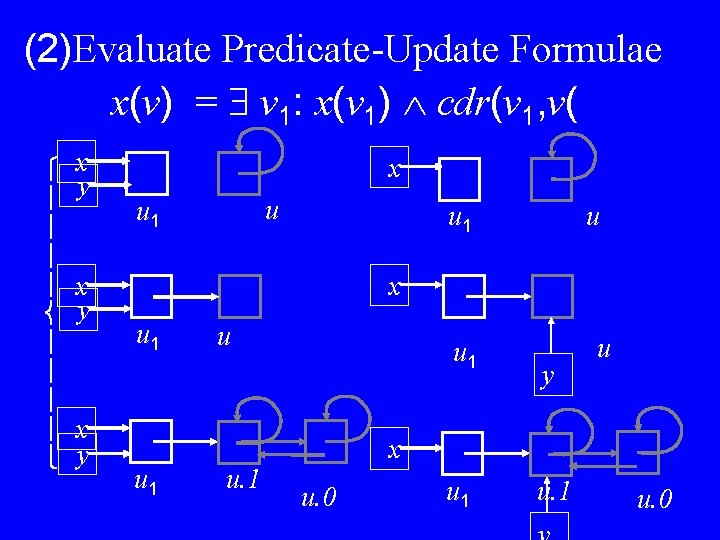
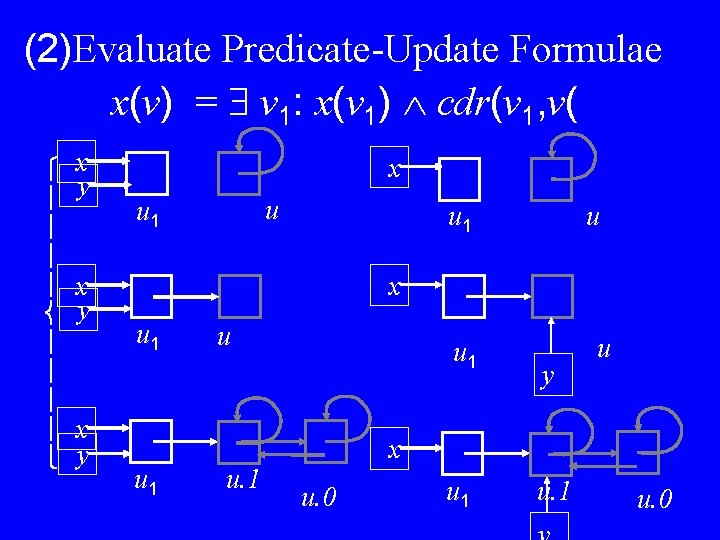
(2)Evaluate Predicate-Update Formulae x(v) = v 1: x(v 1) cdr(v 1, v( x y x y x u u 1 x u 1 u u. 1 u 1 y u x u. 0 u 1 u. 0
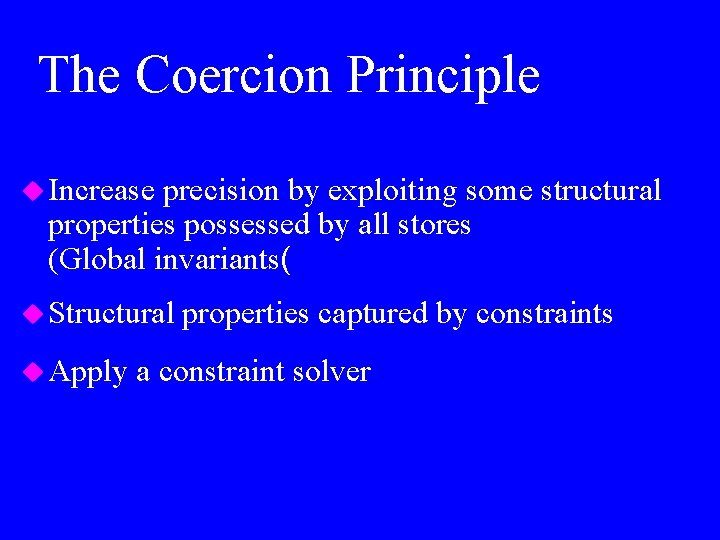
The Coercion Principle u Increase precision by exploiting some structural properties possessed by all stores (Global invariants( u Structural u Apply properties captured by constraints a constraint solver
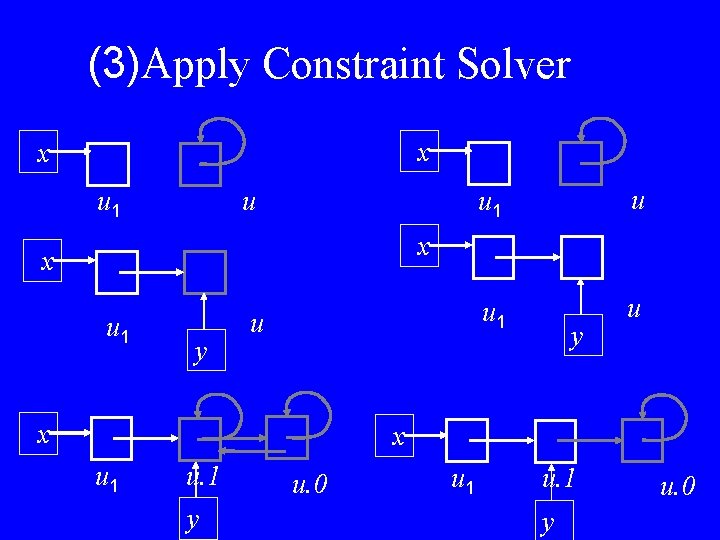
(3)Apply Constraint Solver x x u u 1 u x x u 1 y u x y x u 1 u. 1 y u. 0
Conclusion u TVLA allows construction of non trivial analyses u But it is no panacea – Expressing operational semantics using logical formulas is not always easy – Need instrumentation to be reasonably precise (sometimes help efficiency as well( u Open problems: – A debugger for TVLA – Frontends – Algorithmic problems: » Space optimizations
Bibliography u Chapter 2. 6 u http: //www. cs. uni-sb. de/~wilhelm/foiles/ (Invited talk CC’ 2000( u http: //www. cs. wisc. edu/~reps/#shape_analysis Parametric Shape Analysis based on 3 -valued logics (the general theory( u http: //www. math. tau. ac. il/~tla/ The system and its applications