21 st Century Security Convergence Collaboration and Competition
21 st Century Security: Convergence Collaboration and Competition? ? April 5, 2005 Bill. Boni @ Motorola. com Vice President and Chief Information Security Officer Page 1
• • • IT Governance Agenda The “Warring Tribes” of Security Convergence Collaboration Competition Conclusions 2
Warring Tribes? • Badges • Bytes • Beans IT Governance 3

Badges – Corporate Security /Physical Security • Typically drawn from law enforcement or military • Reports Administration, Facilities, Human Resources • Frames the issue as protection of people, facilities, operations • Values authority and command • Contributes prevention skillsets IT Governance 4
Bytes – IT or Information Security • Typically drawn from technologist ranks • Reports to CIO or IT Operations • Frames the issue as availability, integrity, confidentiality of information and systems • Values creativity and technology innovation • Contribution is continuity and availability of IT capacity IT Governance 5
Beans – The Financial Wizards • • • IT Governance Typically drawn from financial community Reports to Chief Financial Officer or Frames the issue as “Risk Management” Values financial efficiency and loss avoidance Contribution is quantitative rigor 6

Convergence? • What challenges are generally the same ? 1. 2. 3. 4. 5. 6. 7. IT Governance Extended enterprise risks Diverse operational risks Increased legal and regulatory scrutiny Complexity Common approach Common philosophy Mobility and choices 7
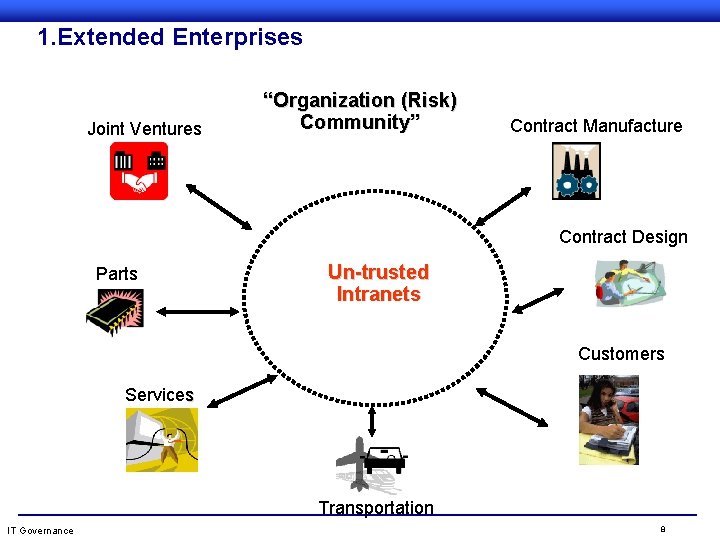
1. Extended Enterprises Dissolution of Perimeter Security Joint Ventures “Organization (Risk) Community” Contract Manufacture Contract Design Parts Un-trusted Intranets Customers Services Transportation IT Governance 8
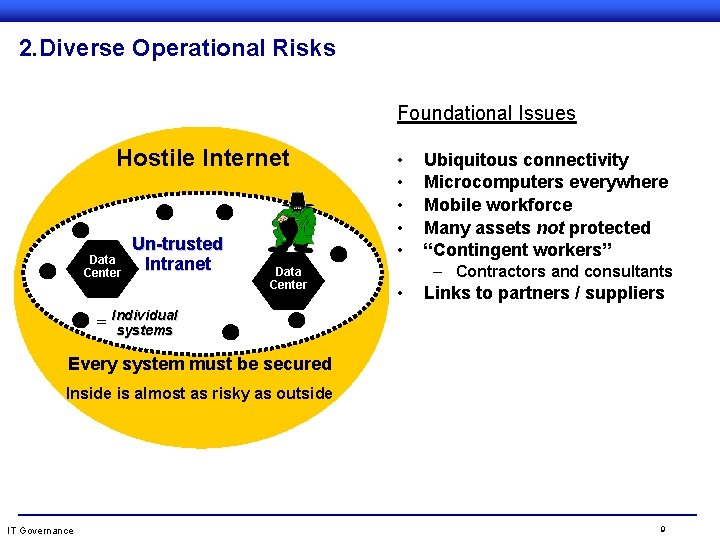
2. Diverse Operational Risks Foundational Issues Hostile Internet Data Center Un-trusted Intranet b Data Center • • • Ubiquitous connectivity Microcomputers everywhere Mobile workforce Many assets not protected “Contingent workers” – Contractors and consultants • Links to partners / suppliers = Individual systems Every system must be secured Inside is almost as risky as outside IT Governance 9
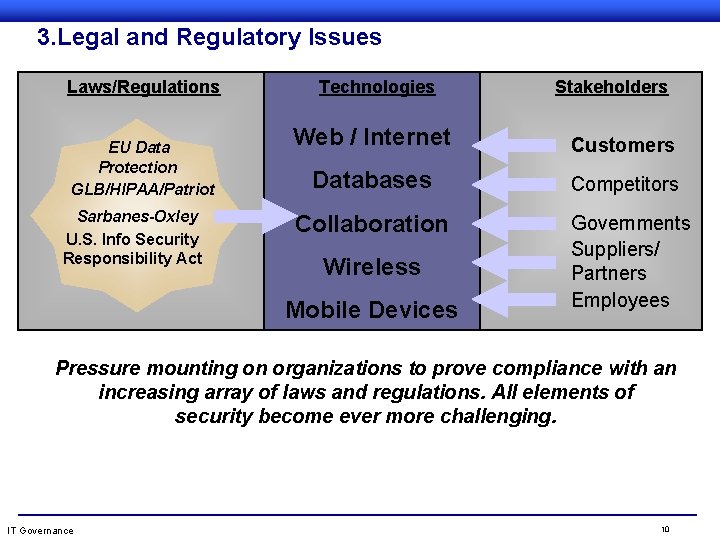
3. Legal and Regulatory Issues Laws/Regulations EU Data Protection GLB/HIPAA/Patriot Sarbanes-Oxley U. S. Info Security Responsibility Act Technologies Stakeholders Web / Internet Customers Databases Competitors Collaboration Wireless Mobile Devices Governments Suppliers/ Partners Employees Pressure mounting on organizations to prove compliance with an increasing array of laws and regulations. All elements of security become ever more challenging. IT Governance 10
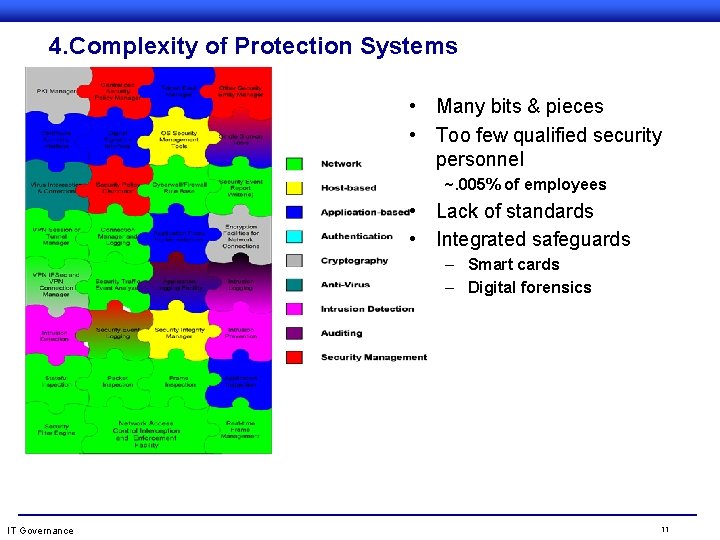
4. Complexity of Protection Systems • Many bits & pieces • Too few qualified security personnel ~. 005% of employees • Lack of standards • Integrated safeguards – Smart cards – Digital forensics IT Governance 11
5. A Common Approach to Strategy? • PROTECT – Key assets and capabilities • DETECT – Attacks and malicious actions • RESPOND – Rapid notification and reaction • Recover – Disaster / business continuity planning IT Governance 12

6. Common Philosophy : Security Must Be Rational OPTIMAL LEVEL OF SECURITY AT MINIMUM COST ($) SECURITY LEVEL COST OF SECURITY COUNTERMEASURES TOTAL COST 0% IT Governance COST OF SECURITY BREACHES 100% 13
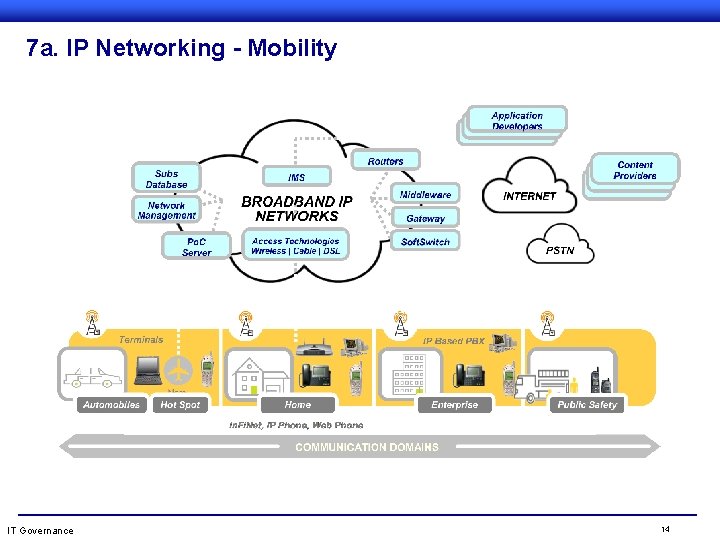
7 a. IP Networking - Mobility IT Governance 14
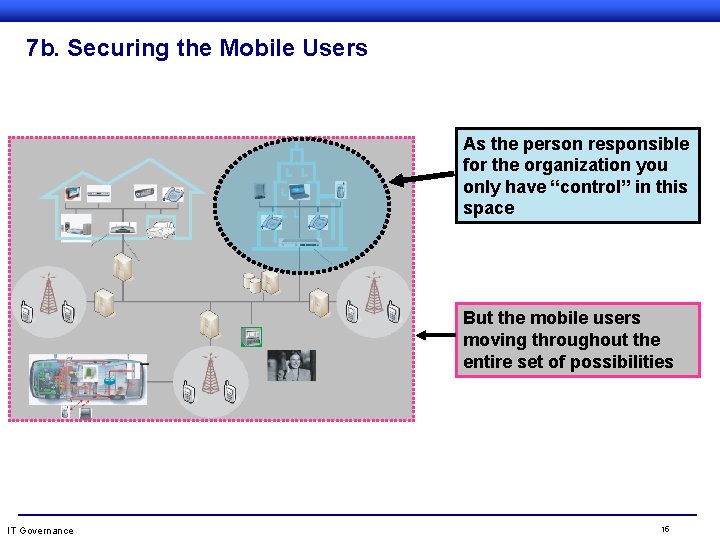
7 b. Securing the Mobile Users As the person responsible for the organization you only have “control” in this space But the mobile users moving throughout the entire set of possibilities IT Governance 15
Competition • • IT Governance Overall leadership Staffing Budget Access to leadership 16
State of the Security Profession? • Corporate – Physical security - CSO • IT – Information Security - CISO • The Security Alliance Initiative – ASIS – ISSA – ISACA • CRO • ERM : Revenge of the “bean counters” ? IT Governance 17
Enterprise Risk Management • Top Down - comprehensive risk management – – Insurance Financial Strategic Operational • Operational Risks Security Professionals • Financial Expertise benefits from metrics/data IT Governance 18
Risk Management The board should manage enterprise risk by: l Ascertaining that there is transparency about the significant risks to the organization l Being aware that the final responsibility for risk management rests with the board l Considering that a proactive risk management approach creates competitive advantage l Insisting that risk management is embedded in the operation of the enterprise l Obtaining assurance that management has put processes and technology in place for (information) security IT Governance Source: IT Governance Institute 19
3 Generic Approaches to Organization Security • Silo’s of independence – Little or no communication and coordination • Councils of collaboration – Periodic, ad hoc, often incident focused • Unified organization – Formal, structured, aligned IT Governance 20
Protection Program Focus Areas • Security Governance – Organization operations and partners • Network Defense – Security strategy and architecture • Protection Management – Projects and continuity program IT Governance 21
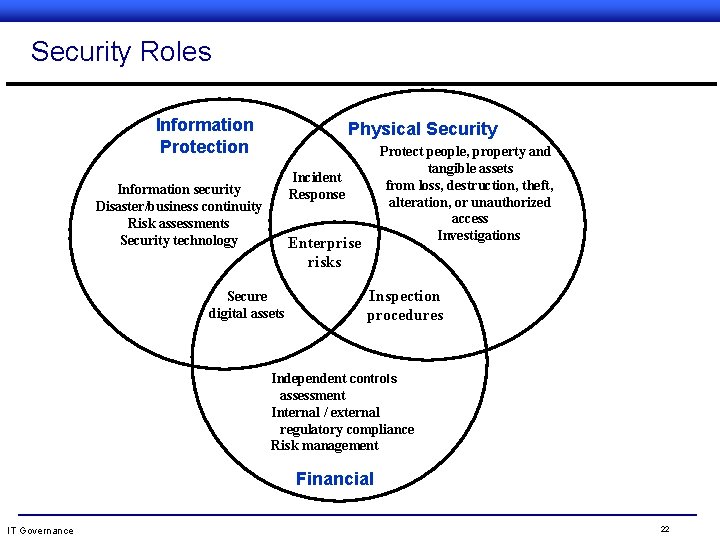
Security Roles Information Protection Physical Security Protect people, property and tangible assets from loss, destruction, theft, alteration, or unauthorized access Investigations Incident Response Information security Disaster/business continuity Risk assessments Security technology Enterprise risks Secure digital assets Inspection procedures Independent controls assessment Internal / external regulatory compliance Risk management Financial IT Governance 22
Changes Ahead for Security Professionals • Cybercrime failures will result in major liability judgments • Public / Private Sector formally share infrastructure protection roles – Certification / licensing for (all? ) security professionals • CSO’s assume responsibility for operational risks • Security is subsumed into ERM and Finance/CRO’s predominate IT Governance 23
A Security Professional for All Seasons…. • • IT Governance Grounded in multiple protection disciplines Capable project/program manager Life long passion to learn Business acumen Diplomatic and adaptable Adept at framing issues as risk management Professional training / certifications 24
A Security Mantra • Vision without Action is Imagination • Action without Vision creates Chaos ü Vision with Right Action is Transformation See the Future and Plan Backwards IT Governance 25
- Slides: 25